| File name: | Cristalix.exe |
| Full analysis: | https://app.any.run/tasks/9828f917-56bd-418f-9507-6244726d0923 |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2019, 16:32:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 50BEA11DB3540F4CE468A6DAD3301D16 |
| SHA1: | 05AAA4A38EE5B2EB7BE15E7FB6B664FD8C077221 |
| SHA256: | EEF1019B505B99B31E62B57A58AE492F9A54385708DB9E9F457FDD69AA08CED8 |
| SSDEEP: | 98304:HWoCCjByIxAb+dD5NhEB4FwAfJ1HAEHSFW:BxAb+dd/EB4FwW1g9W |
MALICIOUS
Loads dropped or rewritten executable
- java.exe (PID: 944)
- java.exe (PID: 2416)
- SearchProtocolHost.exe (PID: 3420)
SUSPICIOUS
Executable content was dropped or overwritten
- java.exe (PID: 944)
- java.exe (PID: 2416)
Creates files in the user directory
- java.exe (PID: 944)
- java.exe (PID: 2416)
Executes JAVA applets
- javaw.exe (PID: 3892)
- Cristalix.exe (PID: 2304)
- java.exe (PID: 944)
Application launched itself
- java.exe (PID: 944)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:08:24 14:23:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.26 |
| CodeSize: | 19968 |
| InitializedDataSize: | 113152 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.146.0 |
| ProductVersionNumber: | 3.0.146.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
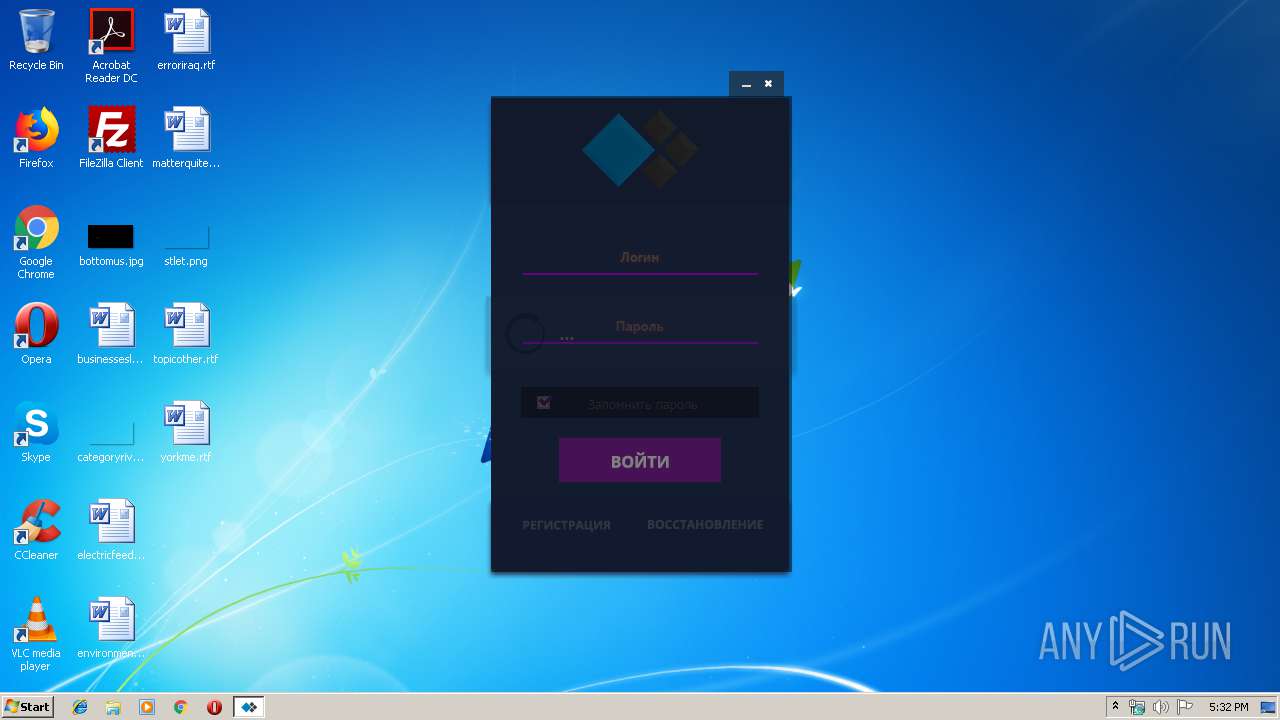
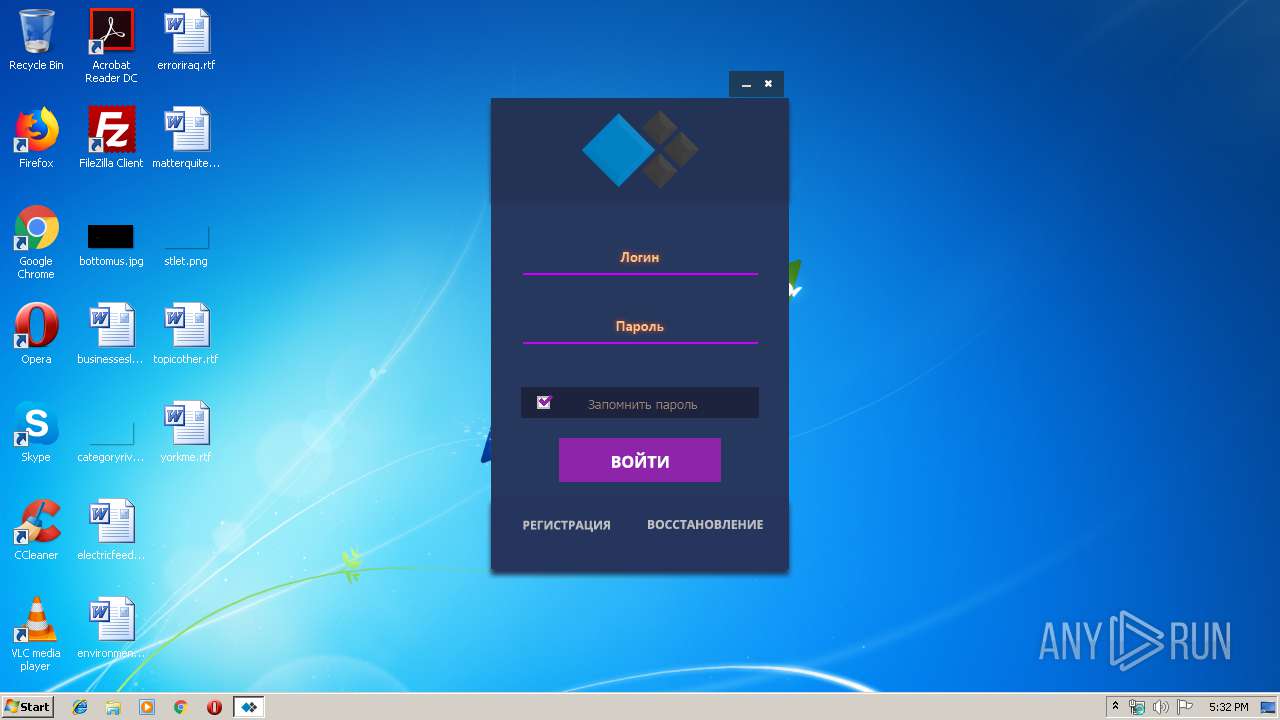
| CompanyName: | Cristalix |
| FileDescription: | launcher-client |
| FileVersion: | 3.0.146 |
| InternalName: | launcher-client-3.0.146-merged |
| LegalCopyright: | (C) 2018-2019 Cristalix |
| LegalTrademarks: | - |
| OriginalFileName: | Launcher.exe |
| ProductName: | Cristalix Launcher |
| ProductVersion: | 3.0.146 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Aug-2019 12:23:39 |
| Detected languages: |
|
| CompanyName: | Cristalix |
| FileDescription: | launcher-client |
| FileVersion: | 3.0.146 |
| InternalName: | launcher-client-3.0.146-merged |
| LegalCopyright: | (C) 2018-2019 Cristalix |
| LegalTrademarks: | - |
| OriginalFilename: | Launcher.exe |
| ProductName: | Cristalix Launcher |
| ProductVersion: | 3.0.146 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Aug-2019 12:23:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004CE0 | 0x00004E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.03203 |
.data | 0x00006000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00007000 | 0x00000680 | 0x00000800 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92317 |
.bss | 0x00008000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65099 |
.rsrc | 0x00012000 | 0x0001A230 | 0x0001A400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.32361 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.36727 | 808 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.5 | 8 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 1.80501 | 16936 | UNKNOWN | Process Default Language | RT_ICON |
4 | 1.95604 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
5 | 2.03602 | 4264 | UNKNOWN | Process Default Language | RT_ICON |
6 | 2.30185 | 1128 | UNKNOWN | Process Default Language | RT_ICON |
8 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -Djava.net.preferIPv4Stack=true -XX:-UsePerfData -XX:+DisableAttachMechanism -cp C:\Cristalix.exe ru.cristalix.launcher.o0o00000o_MOJA_oB0RoNa_SKoSHENNII_LANLISH_VaNDALNoG0_ZHIRA | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2304 | "C:\Cristalix.exe" | C:\Cristalix.exe | — | explorer.exe | |||||||||||
User: admin Company: Cristalix Integrity Level: MEDIUM Description: launcher-client Exit code: 0 Version: 3.0.146 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -Djava.net.preferIPv4Stack=true -XX:-UsePerfData -XX:+DisableAttachMechanism -cp C:\Cristalix.exe ru.cristalix.launcher.o0o00000o_MOJA_oB0RoNa_SKoSHENNII_LANLISH_VaNDALNoG0_ZHIRA | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | java.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3420 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3892 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Cristalix.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | Cristalix.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
407
Read events
400
Write events
7
Delete events
0
Modification events
| (PID) Process: | (944) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (944) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2416) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: java.exe | |||
| (PID) Process: | (3420) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3420) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
2
Suspicious files
1
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3892 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 944 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2416 | java.exe | C:\Users\admin\.cristalix\settings.bin | binary | |
MD5:— | SHA256:— | |||
| 2416 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 944 | java.exe | C:\Users\admin\.cristalix\tmp\Elevator91026546189833956.dll | executable | |
MD5:— | SHA256:— | |||
| 2416 | java.exe | C:\Users\admin\.cristalix\tmp\Elevator3406519397068297314.dll | executable | |
MD5:— | SHA256:— | |||
| 2416 | java.exe | C:\Users\admin\.cristalix\launcher.log\19-10-11\05-32-40.590\LAUNCHER.log | text | |
MD5:— | SHA256:— | |||
| 944 | java.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2416 | java.exe | 104.26.5.43:443 | cristalix.ru | Cloudflare Inc | US | unknown |
2416 | java.exe | 145.239.149.68:63071 | — | OVH SAS | DE | unknown |
— | — | 104.26.5.43:443 | cristalix.ru | Cloudflare Inc | US | unknown |
2416 | java.exe | 149.202.88.32:25565 | — | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cristalix.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2416 | java.exe | Potential Corporate Privacy Violation | ET GAMES MINECRAFT Server response inbound |
2416 | java.exe | Potential Corporate Privacy Violation | ET GAMES MINECRAFT Server response inbound |