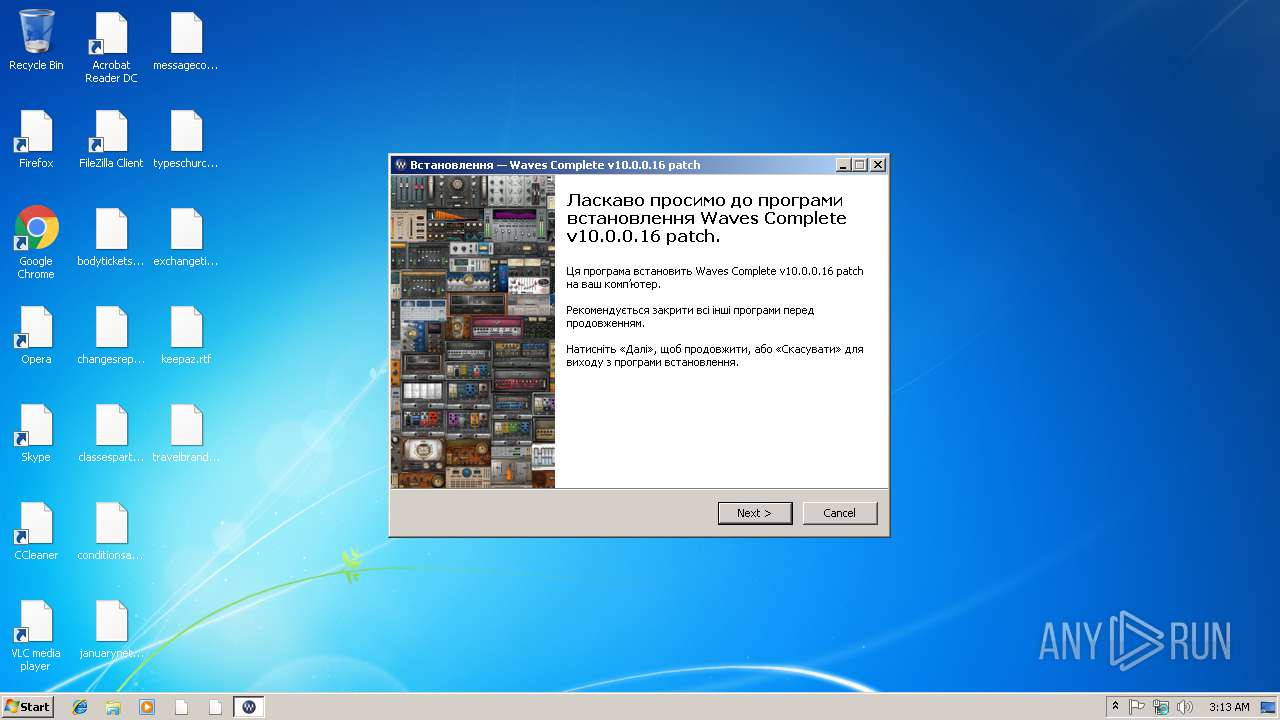
| File name: | Waves_Complete_10.0.0.16_patch.exe |
| Full analysis: | https://app.any.run/tasks/b44d95e9-128c-4ec3-b27b-7292d8825b9f |
| Verdict: | Malicious activity |
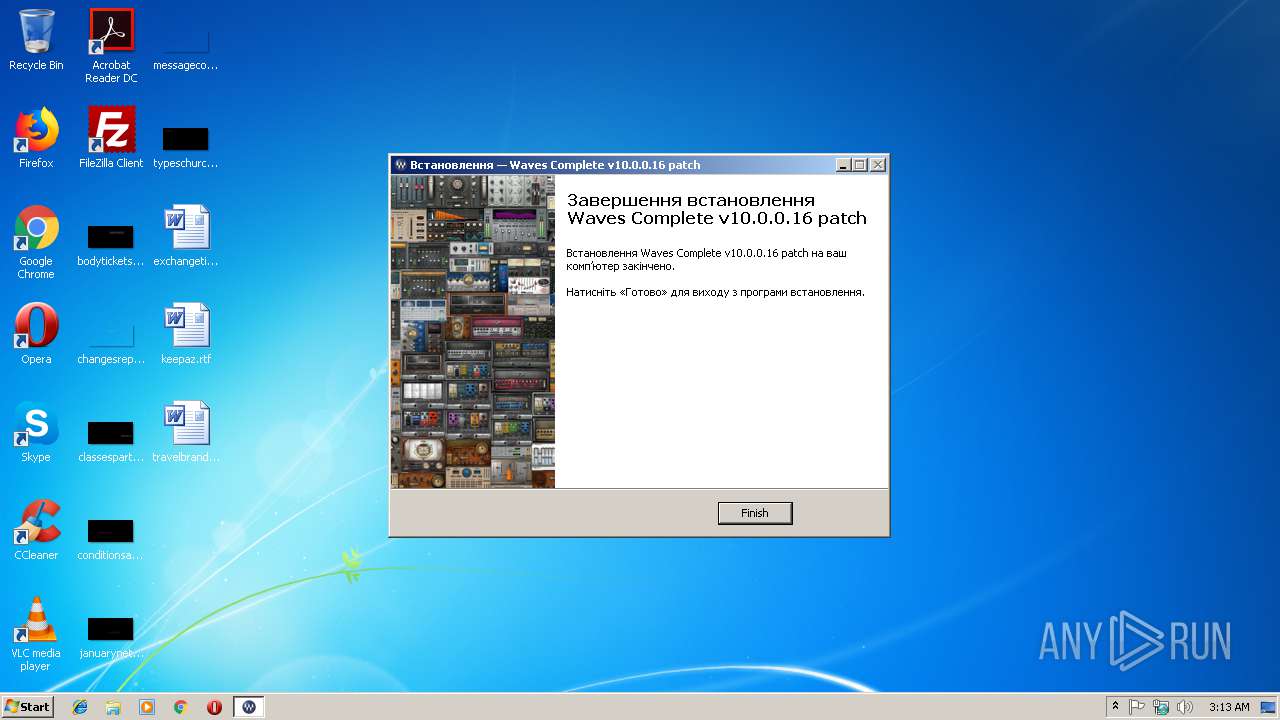
| Analysis date: | March 08, 2019, 03:13:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BCADDEFD316784C45D631AC6DFA656A9 |
| SHA1: | 39D5E47332508562D3B1312E6C9328DFD34AA603 |
| SHA256: | EEDC76C561874D0B54ED3CA58DE88D39AD8D26904C5B613D19D1B33D87A13BC1 |
| SSDEEP: | 98304:/Xz+EI4K955Mf7OERIjWguHsOuuOJtCA501m40JM4JAI4K9jkmhdvohjY5FK:PKF955Mf7OERjgws3uitp50Y40vJh9jy |
MALICIOUS
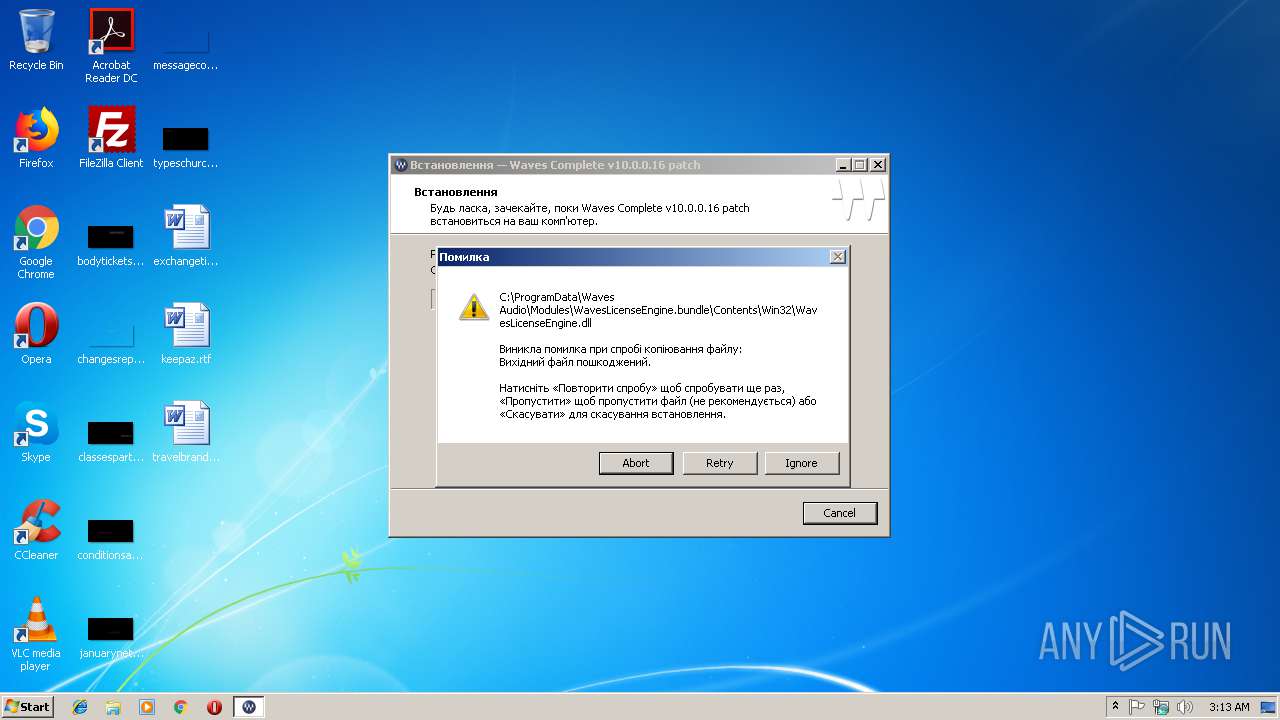
Application was dropped or rewritten from another process
- Waves_Complete_10.0.0.16_patch.exe (PID: 2632)
SUSPICIOUS
Creates or modifies windows services
- Waves_Complete_10.0.0.16_patch.exe (PID: 3636)
Creates files in the program directory
- Waves_Complete_10.0.0.16_patch.exe (PID: 3636)
Creates files in the Windows directory
- Waves_Complete_10.0.0.16_patch.exe (PID: 3636)
Reads Windows owner or organization settings
- Waves_Complete_10.0.0.16_patch.tmp (PID: 3556)
Creates a software uninstall entry
- Waves_Complete_10.0.0.16_patch.exe (PID: 3636)
Executable content was dropped or overwritten
- Waves_Complete_10.0.0.16_patch.exe (PID: 2632)
- Waves_Complete_10.0.0.16_patch.exe (PID: 3636)
- Waves_Complete_10.0.0.16_patch.tmp (PID: 3556)
Reads the Windows organization settings
- Waves_Complete_10.0.0.16_patch.tmp (PID: 3556)
INFO
Application was dropped or rewritten from another process
- Waves_Complete_10.0.0.16_patch.tmp (PID: 3556)
Loads dropped or rewritten executable
- Waves_Complete_10.0.0.16_patch.tmp (PID: 3556)
Creates files in the program directory
- Waves_Complete_10.0.0.16_patch.tmp (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 148992 |
| InitializedDataSize: | 397312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25468 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.0.0.16 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
| CompanyName: | Patch |
| FileDescription: | Waves 10.0.0.16 Installation |
| FileVersion: | 10.0.0.16 |
| LegalCopyright: | Patch |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Patch |
| FileDescription: | Waves 10.0.0.16 Installation |
| FileVersion: | 10.0.0.16 |
| LegalCopyright: | Patch |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59438 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88549 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x0005B068 | 0x0005B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.93294 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 3.71769 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.16444 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 4.57078 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 4.72664 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 5.30274 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
55 | 5.70579 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.86826 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2632 | "C:\Program Files\Patch\Waves\Waves_Complete_10.0.0.16_patch.exe" | C:\Program Files\Patch\Waves\Waves_Complete_10.0.0.16_patch.exe | Waves_Complete_10.0.0.16_patch.exe | ||||||||||||
User: admin Company: Waves Audio Integrity Level: HIGH Description: Waves Complete Exit code: 0 Version: 10.0.0.16 Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\AppData\Local\Temp\Waves_Complete_10.0.0.16_patch.exe" | C:\Users\admin\AppData\Local\Temp\Waves_Complete_10.0.0.16_patch.exe | — | explorer.exe | |||||||||||
User: admin Company: Patch Integrity Level: MEDIUM Description: Waves 10.0.0.16 Installation Exit code: 3221226540 Version: 10.0.0.16 Modules
| |||||||||||||||
| 3556 | "C:\Users\admin\AppData\Local\Temp\is-KESF3.tmp\Waves_Complete_10.0.0.16_patch.tmp" /SL5="$30112,1093626,486912,C:\Program Files\Patch\Waves\Waves_Complete_10.0.0.16_patch.exe" | C:\Users\admin\AppData\Local\Temp\is-KESF3.tmp\Waves_Complete_10.0.0.16_patch.tmp | Waves_Complete_10.0.0.16_patch.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3636 | "C:\Users\admin\AppData\Local\Temp\Waves_Complete_10.0.0.16_patch.exe" | C:\Users\admin\AppData\Local\Temp\Waves_Complete_10.0.0.16_patch.exe | explorer.exe | ||||||||||||
User: admin Company: Patch Integrity Level: HIGH Description: Waves 10.0.0.16 Installation Exit code: 0 Version: 10.0.0.16 Modules
| |||||||||||||||
Total events
128
Read events
50
Write events
72
Delete events
6
Modification events
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | Type |
Value: 16 | |||
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | Start |
Value: 2 | |||
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | ErrorControl |
Value: 1 | |||
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | ImagePath |
Value: C:\Windows\wmu2\wnetmonitor.exe | |||
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | Description |
Value: WMI Providers | |||
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | DisplayName |
Value: WMIs | |||
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | ObjectName |
Value: LocalSystem | |||
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | DelayedAutostart |
Value: 0 | |||
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | FailureActionsOnNonCrashFailures |
Value: 1 | |||
| (PID) Process: | (3636) Waves_Complete_10.0.0.16_patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WMS |
| Operation: | write | Name: | FailureActions |
Value: 00000000000000000000000003000000140000000100000060EA00000100000060EA00000100000060EA0000 | |||
Executable files
5
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | Waves_Complete_10.0.0.16_patch.tmp | C:\ProgramData\Waves Audio\Modules\WavesLicenseEngine.bundle\Contents\Win32\is-QUQKO.tmp | — | |
MD5:— | SHA256:— | |||
| 3636 | Waves_Complete_10.0.0.16_patch.exe | C:\Windows\wmu2\wnetmonitor.exe | executable | |
MD5:— | SHA256:— | |||
| 3636 | Waves_Complete_10.0.0.16_patch.exe | C:\Program Files\Patch\Waves\Waves_Complete_10.0.0.16_patch.exe | executable | |
MD5:— | SHA256:— | |||
| 3636 | Waves_Complete_10.0.0.16_patch.exe | C:\Windows\wmu2\wininit.exe | executable | |
MD5:— | SHA256:— | |||
| 2632 | Waves_Complete_10.0.0.16_patch.exe | C:\Users\admin\AppData\Local\Temp\is-KESF3.tmp\Waves_Complete_10.0.0.16_patch.tmp | executable | |
MD5:— | SHA256:— | |||
| 3556 | Waves_Complete_10.0.0.16_patch.tmp | C:\Users\admin\AppData\Local\Temp\is-JOFE4.tmp\_isetup\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report