| File name: | PnkBstrA.exe |
| Full analysis: | https://app.any.run/tasks/cab0b639-55b1-4694-85d9-857ff3420603 |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2025, 15:03:03 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 3 sections |
| MD5: | 3A2E85F7D90D15460C337CE80C2E3B29 |
| SHA1: | 0360BE046D9C6DC2361580DE65E22409656A7A33 |
| SHA256: | EECAA20359FD2D75D6A564A3BAADACAA2CB69D061E455AA3F75055A3EAB54168 |
| SSDEEP: | 768:UObkcI6v8WBh6+o/L/V7FyYTt94w9cejnueoRzBWrg2hBHT9DOD4ytqrzRyJAv28:UGxIYhg/CSt9Lktsg2jxAeHmO/5gzYlT |
MALICIOUS
Executing a file with an untrusted certificate
- PnkBstrA.exe (PID: 3016)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- PnkBstrA.exe (PID: 3016)
Reads the computer name
- PnkBstrA.exe (PID: 3016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:12:19 20:53:20+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 49152 |
| InitializedDataSize: | 36864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x51e8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
101
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
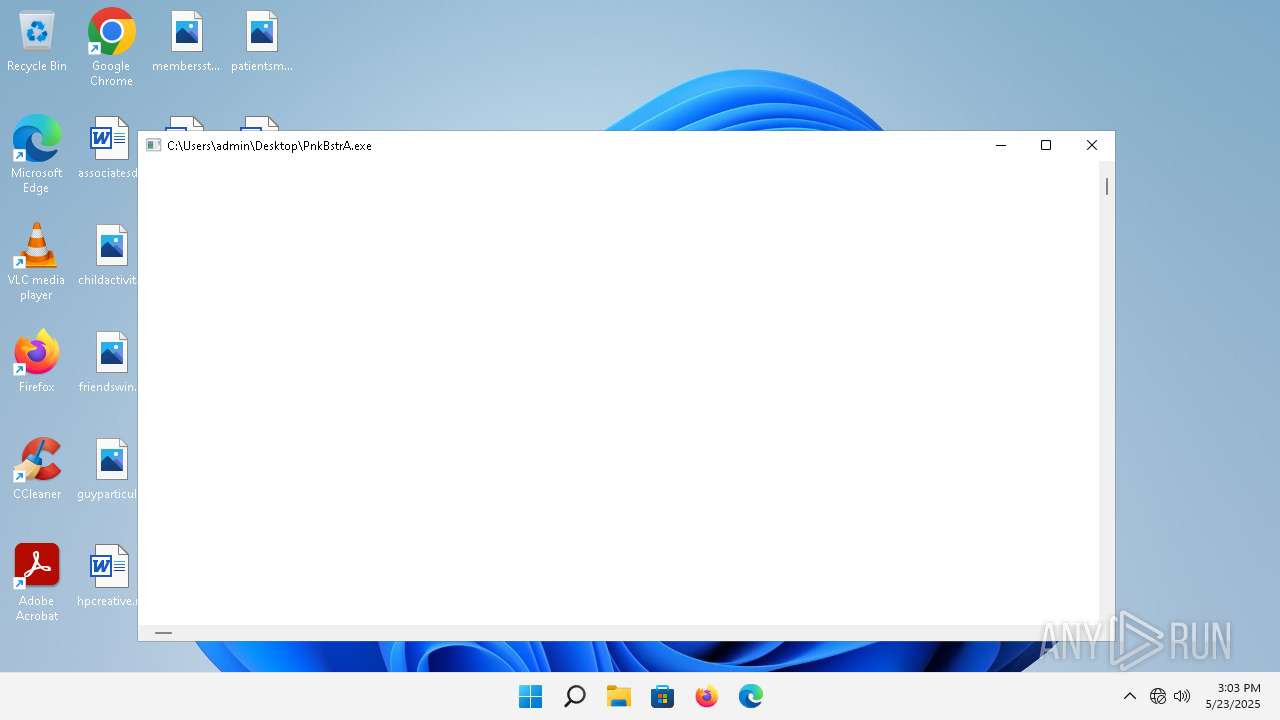
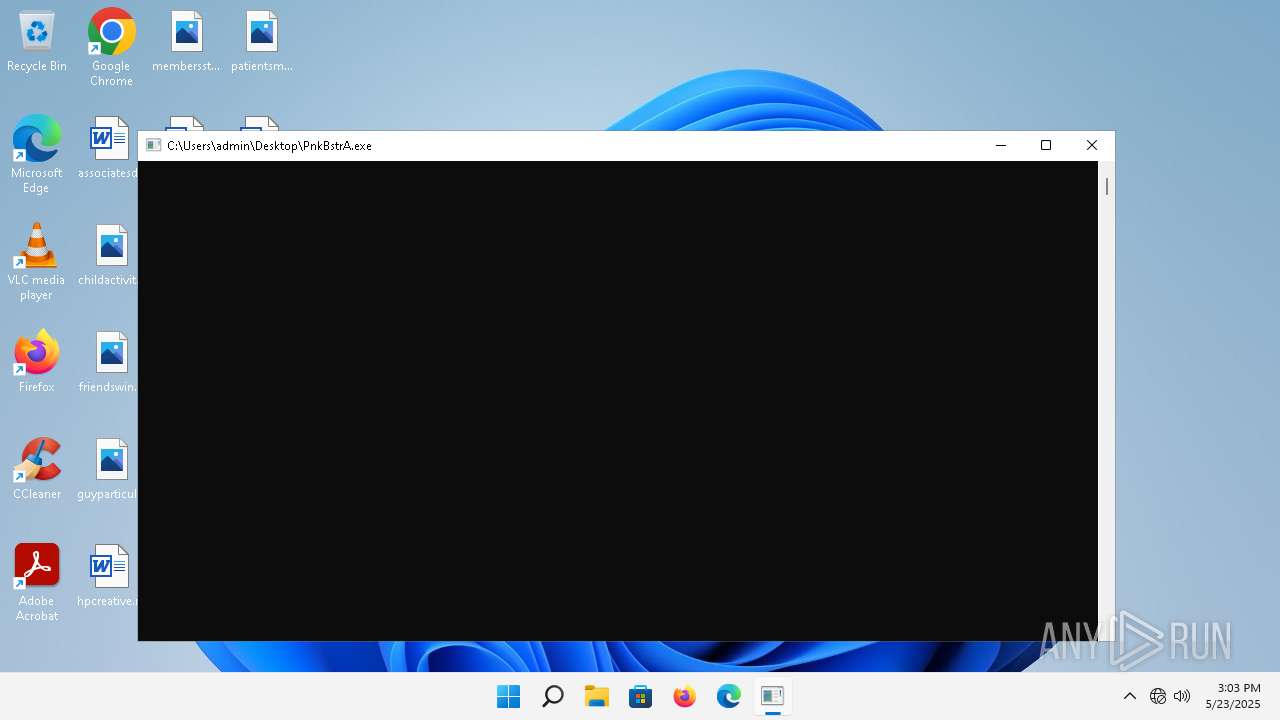
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1640 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PnkBstrA.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3016 | "C:\Users\admin\Desktop\PnkBstrA.exe" | C:\Users\admin\Desktop\PnkBstrA.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
44
Read events
44
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
12
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 20.191.45.158:443 | https://checkappexec.microsoft.com/windows/shell/actions | unknown | binary | 182 b | whitelisted |
— | — | HEAD | 200 | 23.212.222.21:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
— | — | GET | 200 | 23.212.222.21:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | binary | 55 b | whitelisted |
— | — | POST | 200 | 20.189.173.1:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | whitelisted |
1352 | svchost.exe | GET | 200 | 2.16.168.101:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
1040 | smartscreen.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?efc7c30ad38b3397 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 2.16.168.102:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2efe063e74f19306 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 2.16.168.102:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?b5c209eb39f9a373 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 2.16.168.102:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?15028c5fe99424fd | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.64:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 2.16.168.101:80 | — | Akamai International B.V. | RU | unknown |
1040 | smartscreen.exe | 48.209.164.47:443 | checkappexec.microsoft.com | — | US | whitelisted |
1040 | smartscreen.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
4432 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
384 | svchost.exe | 104.102.63.189:443 | fs.microsoft.com | AKAMAI-AS | US | whitelisted |
2988 | OfficeClickToRun.exe | 20.42.73.26:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2768 | svchost.exe | 2.16.168.102:80 | ctldl.windowsupdate.com | Akamai International B.V. | RU | whitelisted |
3640 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |