| File name: | ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d |
| Full analysis: | https://app.any.run/tasks/1a1665b9-1fb9-40c2-821d-51ad51bd8862 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 15:12:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D236FCC8789F94F085137058311E848B |
| SHA1: | 808061052C9EFC7C7255FFEB92C77B02BBB8CFEE |
| SHA256: | EE937717EFE9A2E076B9497498B628BEB0C84A8476BD288105A59C5AEEA01F3D |
| SSDEEP: | 768:f9NJK3qZRhxXHIQBsLL16BKc+bBQZ/UMc2:ZXzXol6cc+lQZMMc2 |
MALICIOUS
Changes the autorun value in the registry
- ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe (PID: 3568)
Low-level write access rights to disk partition
- foyijtm.exe (PID: 3420)
Deletes shadow copies
- foyijtm.exe (PID: 3420)
Actions looks like stealing of personal data
- foyijtm.exe (PID: 3420)
Modifies files in Chrome extension folder
- foyijtm.exe (PID: 3420)
SUSPICIOUS
Low-level read access rights to disk partition
- foyijtm.exe (PID: 3420)
Executable content was dropped or overwritten
- ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe (PID: 3568)
Starts itself from another location
- ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe (PID: 3568)
Connects to server without host name
- ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe (PID: 3568)
- foyijtm.exe (PID: 3420)
Executed as Windows Service
- vssvc.exe (PID: 2696)
Creates files in the user directory
- foyijtm.exe (PID: 3420)
Creates files in the program directory
- foyijtm.exe (PID: 3420)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:06:25 11:56:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 22528 |
| InitializedDataSize: | 75776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5420 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jun-2016 09:56:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 25-Jun-2016 09:56:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005746 | 0x00005800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50048 |
.data | 0x00007000 | 0x00011A40 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.98346 |
.tls | 0x00019000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.reloc | 0x0001A000 | 0x00000930 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.48686 |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MPR.dll |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
WS2_32.dll |
ntdll.dll |
Total processes
43
Monitored processes
4
Malicious processes
2
Suspicious processes
0
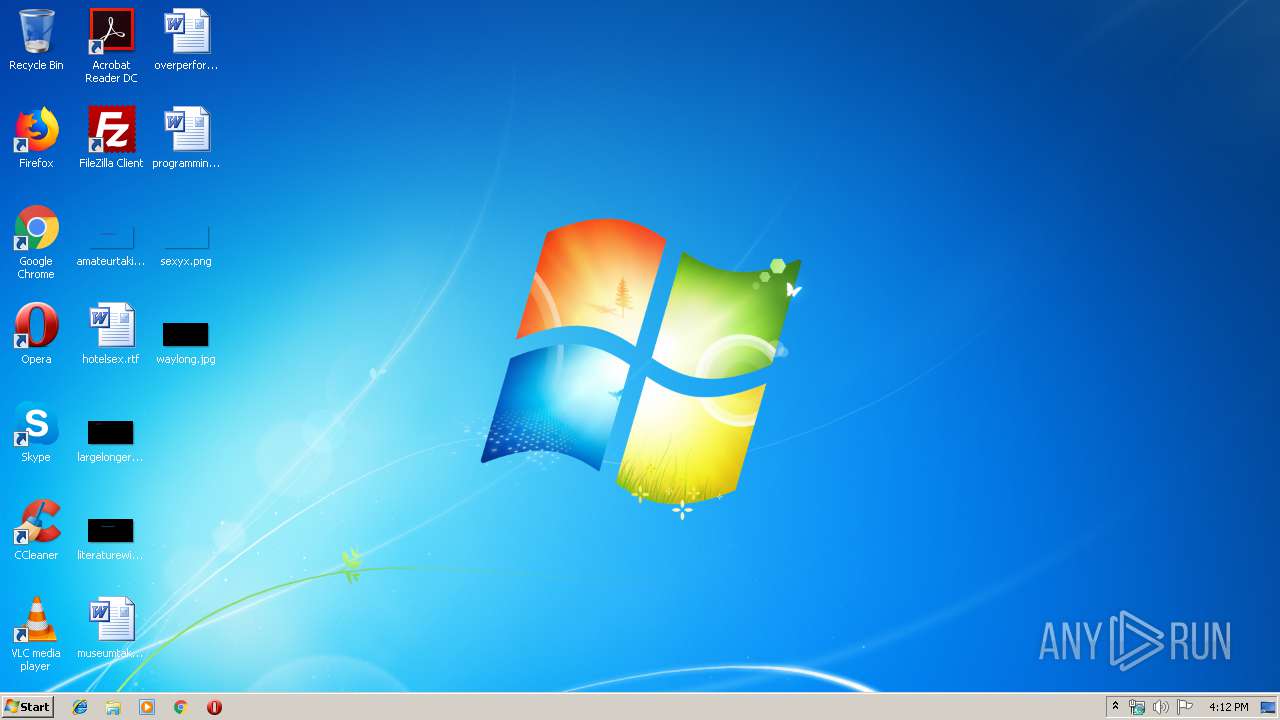
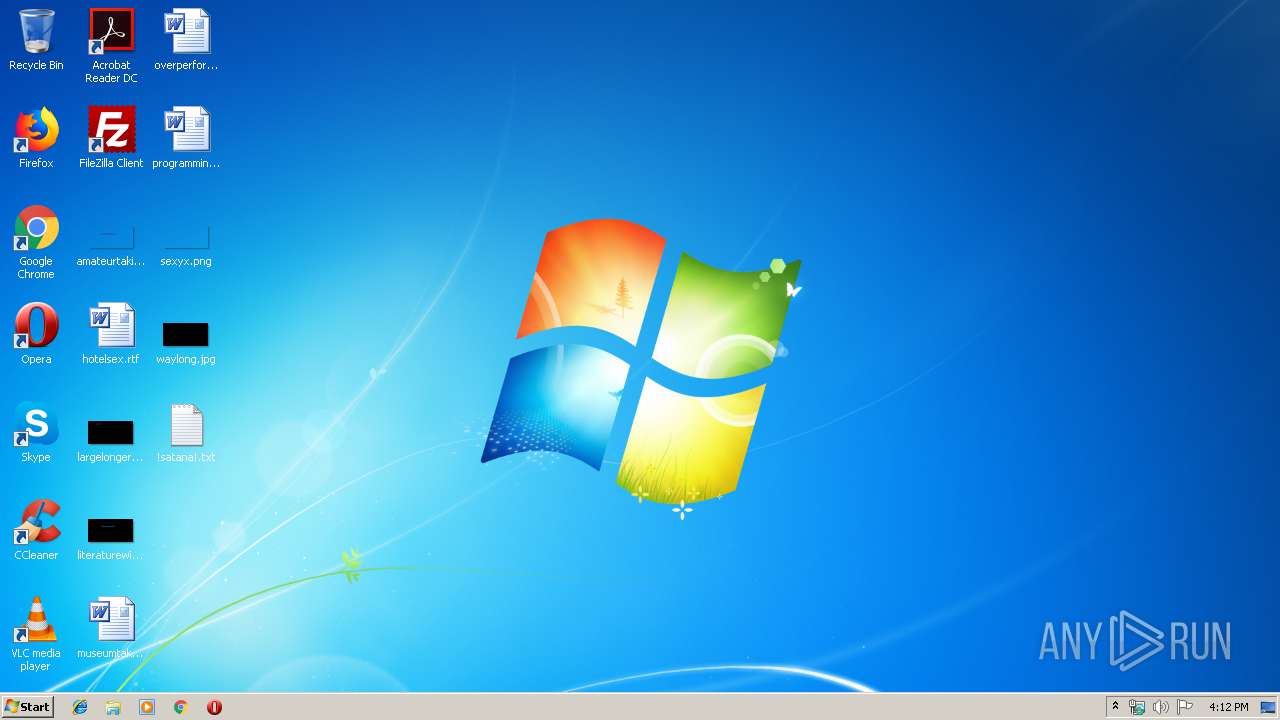
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | "C:\Windows\system32\VSSADMIN.EXE" Delete Shadows /All /Quiet | C:\Windows\system32\VSSADMIN.EXE | — | foyijtm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3420 | "C:\Users\admin\AppData\Local\Temp\foyijtm.exe" {e29ac6c0-7037-11de-816d-806e6f6e6963} "C:\Users\admin\AppData\Local\Temp\EE9377~1.EXE" | C:\Users\admin\AppData\Local\Temp\foyijtm.exe | ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\AppData\Local\Temp\ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe" | C:\Users\admin\AppData\Local\Temp\ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
Total events
402
Read events
391
Write events
11
Delete events
0
Modification events
| (PID) Process: | (3568) ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | Key: | HKEY_CURRENT_USER\14C580F9981F625C738B49834E448A14 |
| Operation: | write | Name: | |
Value: adamadam@ausi.com | |||
| (PID) Process: | (3568) ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | Key: | HKEY_CURRENT_USER\14C580F9981F625C738B49834E448A14 |
| Operation: | write | Name: | BTC |
Value: XbvKCGr8VowpBLwE8VxHNL2oL24ukKcNFw | |||
| (PID) Process: | (3568) ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | kfdn |
Value: C:\Users\admin\AppData\Local\Temp\!satana!.txt | |||
| (PID) Process: | (3568) ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3568) ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3420) foyijtm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3420) foyijtm.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
2 203
Text files
3 404
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3420 | foyijtm.exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 3420 | foyijtm.exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\ExcelMUI.xml | — | |
MD5:— | SHA256:— | |||
| 3420 | foyijtm.exe | C:\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\PowerPointMUI.xml | — | |
MD5:— | SHA256:— | |||
| 3420 | foyijtm.exe | C:\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 3420 | foyijtm.exe | C:\MSOCache\All Users\{90140000-0019-0409-0000-0000000FF1CE}-C\PublisherMUI.xml | — | |
MD5:— | SHA256:— | |||
| 3420 | foyijtm.exe | C:\MSOCache\All Users\{90140000-0019-0409-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 3420 | foyijtm.exe | C:\$Recycle.Bin\!satana!.txt | text | |
MD5:— | SHA256:— | |||
| 3568 | ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | C:\Users\admin\AppData\Local\Temp\foyijtm.exe | executable | |
MD5:— | SHA256:— | |||
| 3420 | foyijtm.exe | C:\MSOCache\All Users\{90140000-001A-0409-0000-0000000FF1CE}-C\OutlookMUI.xml | — | |
MD5:— | SHA256:— | |||
| 3568 | ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | C:\Users\admin\AppData\Local\Temp\!satana!.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3568 | ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | POST | — | 185.127.26.186:80 | http://185.127.26.186/add.php | RU | — | — | malicious |
3420 | foyijtm.exe | POST | — | 185.127.26.186:80 | http://185.127.26.186/add.php | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3568 | ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | 185.127.26.186:80 | — | Business Consulting LLC | RU | malicious |
3420 | foyijtm.exe | 185.127.26.186:80 | — | Business Consulting LLC | RU | malicious |
DNS requests
Threats
Process | Message |
|---|---|
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | "C:\Users\admin\AppData\Local\Temp\ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe" |
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | HWID: 7EA61278DFBAD65AE31E707FFE019711 |
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | hHeap = 0x250000 nSize = 8 |
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | Locale: English |
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | Size: 0x1CE7 key:0x34 |
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | Try Decrypt: uc_size = 1559, c_size = 999 |
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | DeCompressor: Ok: 1559 |
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | dwSzLending = 1559 |
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | Try Decrypt: uc_size = 540, c_size = 589 |
ee937717efe9a2e076b9497498b628beb0c84a8476bd288105a59c5aeea01f3d.exe | DeCompressor: Ok: 540 |