| File name: | DOC_89582636575US_Apr_25_2019.js |
| Full analysis: | https://app.any.run/tasks/81303ee3-8a9f-4c8c-9c6c-faac6d365dbe |
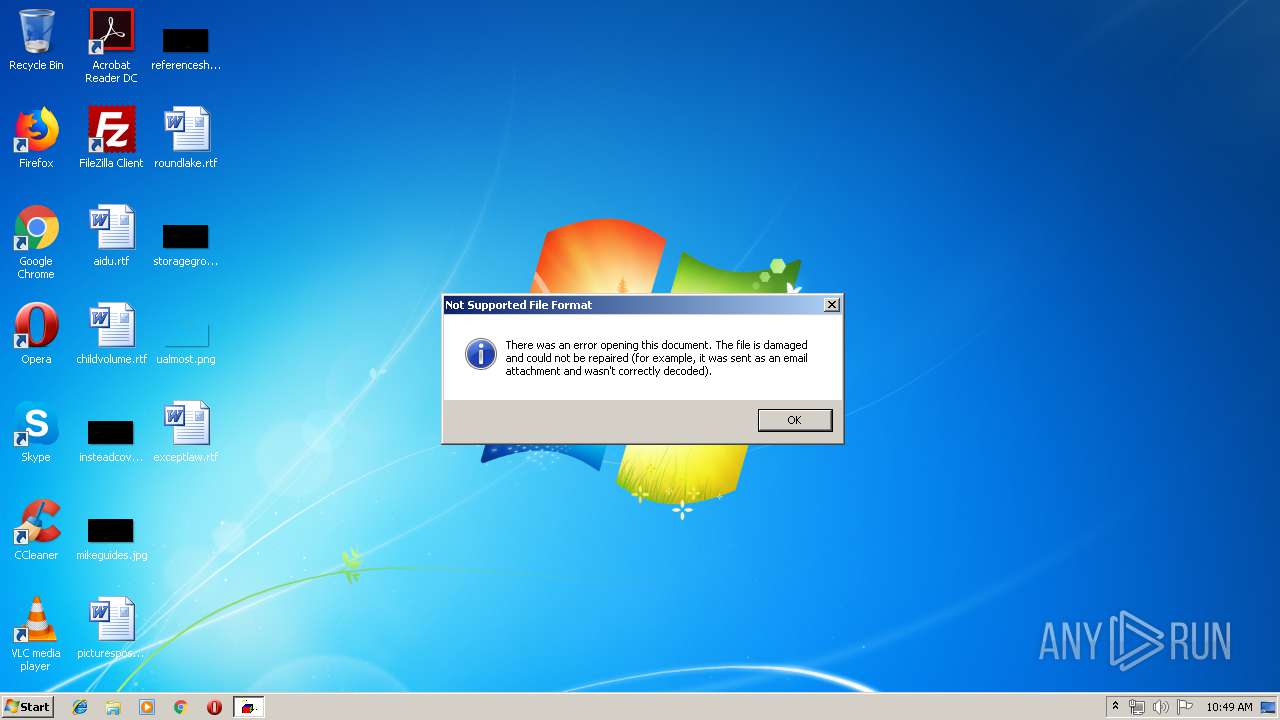
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 09:49:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | DCA68FFB6BA8C0B6F5F61C865F43DD76 |
| SHA1: | 80485DCF692CD4FC20A1597FF8EC474C3C0C4155 |
| SHA256: | EE65C61941B260403E66E0B141CD9BA307540F8BDC79375C8F4609148E5F6CEF |
| SSDEEP: | 768:tQyhL1vAcXd0A80jQ/2OfyC9cMDbHuqExzeX+tFXHAgHNoX8uy4XZ+rK6fi9CkgB:tQAL1vT0H0jQRyC9cMDbHuXxzeX/mN0o |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 2528)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
31
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2528 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\DOC_89582636575US_Apr_25_2019.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
52
Read events
34
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2528) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2528 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2528 | WScript.exe | GET | 404 | 192.254.237.246:80 | http://musicfacile.com/cgi-bin/zw_wX/ | US | xml | 345 b | suspicious |
2528 | WScript.exe | GET | 404 | 69.65.3.176:80 | http://tcmnow.com/cgi-bin/J4_5/ | US | xml | 345 b | suspicious |
2528 | WScript.exe | GET | 404 | 188.39.89.38:80 | http://teambored.co.uk/Invoice/U4_t/ | GB | xml | 345 b | malicious |
2528 | WScript.exe | GET | 404 | 54.77.80.0:80 | http://teledis.fr/updates/O_6/ | IE | xml | 345 b | unknown |
2528 | WScript.exe | GET | 404 | 65.99.237.31:80 | http://obosonews.info/wp-content/H_IP/ | US | xml | 345 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2528 | WScript.exe | 69.65.3.176:80 | tcmnow.com | GigeNET | US | malicious |
2528 | WScript.exe | 65.99.237.31:80 | obosonews.info | Colo4, LLC | US | unknown |
2528 | WScript.exe | 54.77.80.0:80 | teledis.fr | Amazon.com, Inc. | IE | unknown |
2528 | WScript.exe | 192.254.237.246:80 | musicfacile.com | Unified Layer | US | suspicious |
2528 | WScript.exe | 188.39.89.38:80 | teambored.co.uk | Entanet | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tcmnow.com |
| suspicious |
teambored.co.uk |
| malicious |
teledis.fr |
| unknown |
obosonews.info |
| unknown |
musicfacile.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2528 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2528 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2528 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2528 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2528 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |