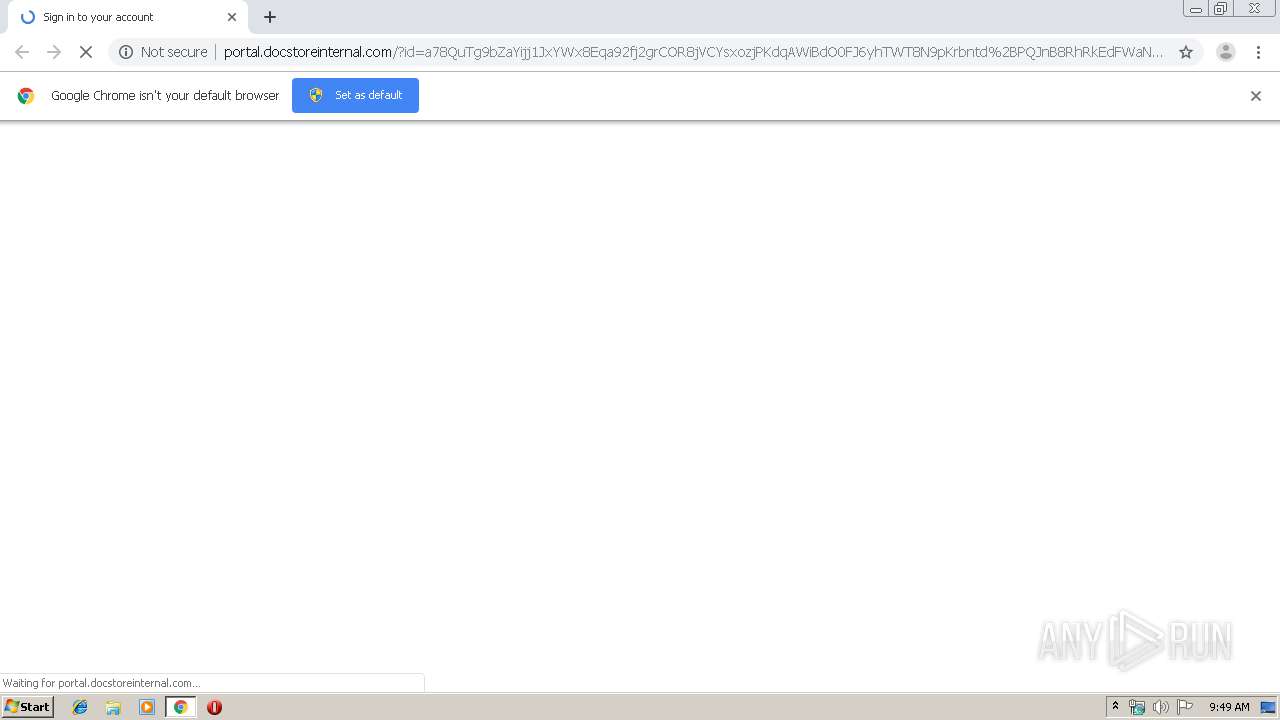
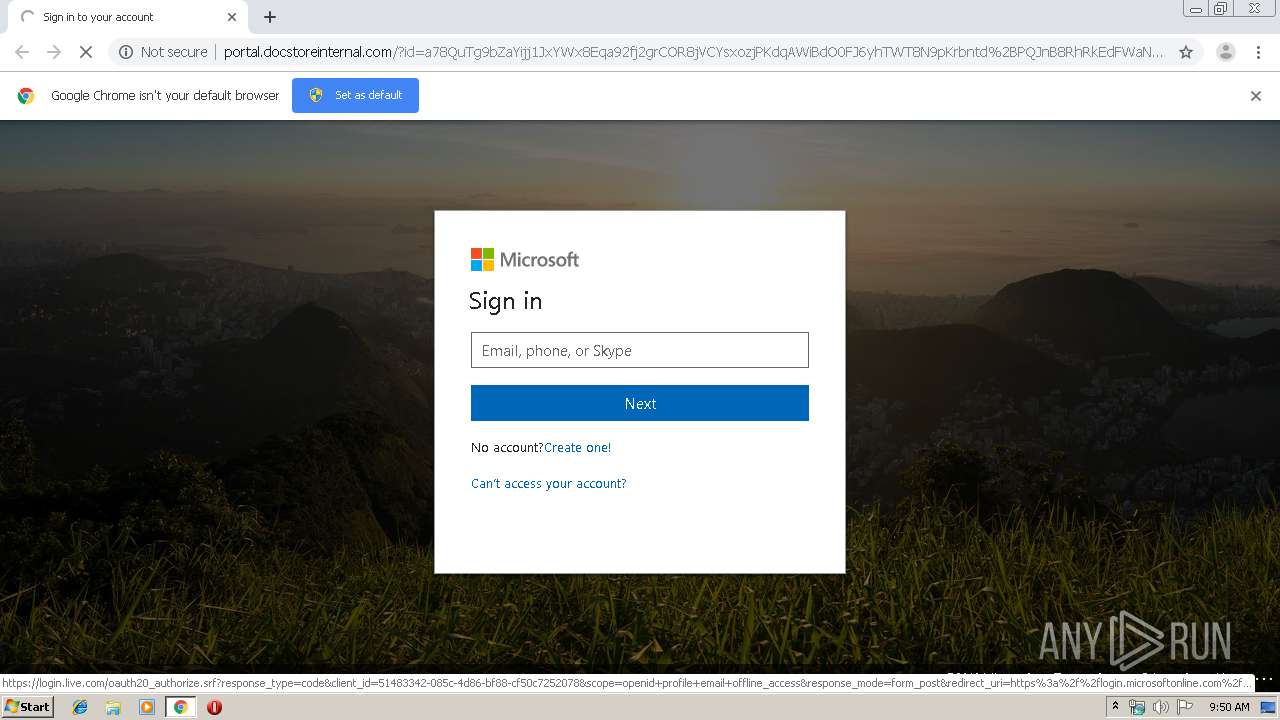
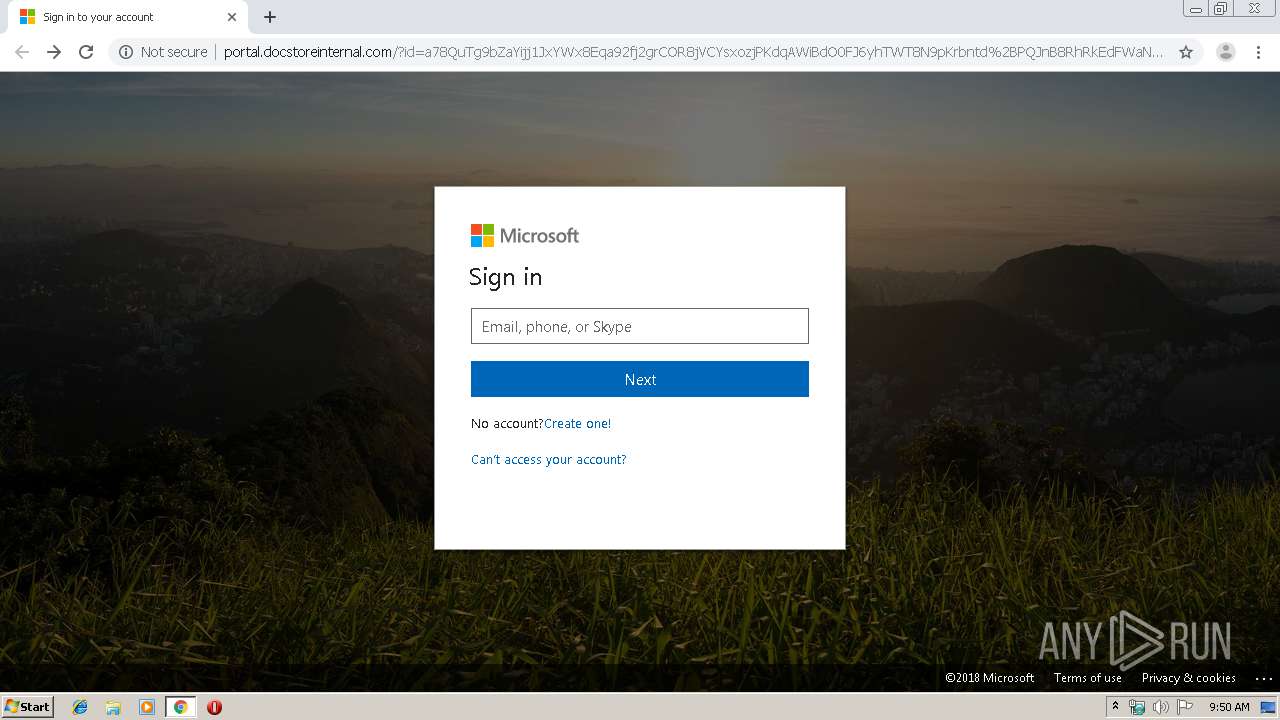
| URL: | http://portal.docstoreinternal.com/?id=a78QuTg9bZaYijj1JxYWx8Eqa92fj2grCOR8jVCYsxozjPKdqAWiBdO0FJ6yhTWT8N9pKrbntd%2BPQJnB8RhRkEdFWaNiDX40%2FlMZg8CUSL%2BBLi6ZWUN1gBmgF7V2VWSZEqsnX5AbTduTn8xI3opzWg7OkRPlHEPNDzOoXH%2B9N0MvmqDHuMISX4rP1dJqU7DJmqyomJ0O8x6jO4uSQF%2BLdEorgSvfiT2qjXD2o0tGYZMXmS4ExW%2BOmyT5Zfx%2B8bto4%2BwPJrEMmLH6ytyLbBvKDZ7gTzwk62subvLt4wRg7Xg%3D |
| Full analysis: | https://app.any.run/tasks/39e1832c-5abd-4c4a-a523-9795dc85b82c |
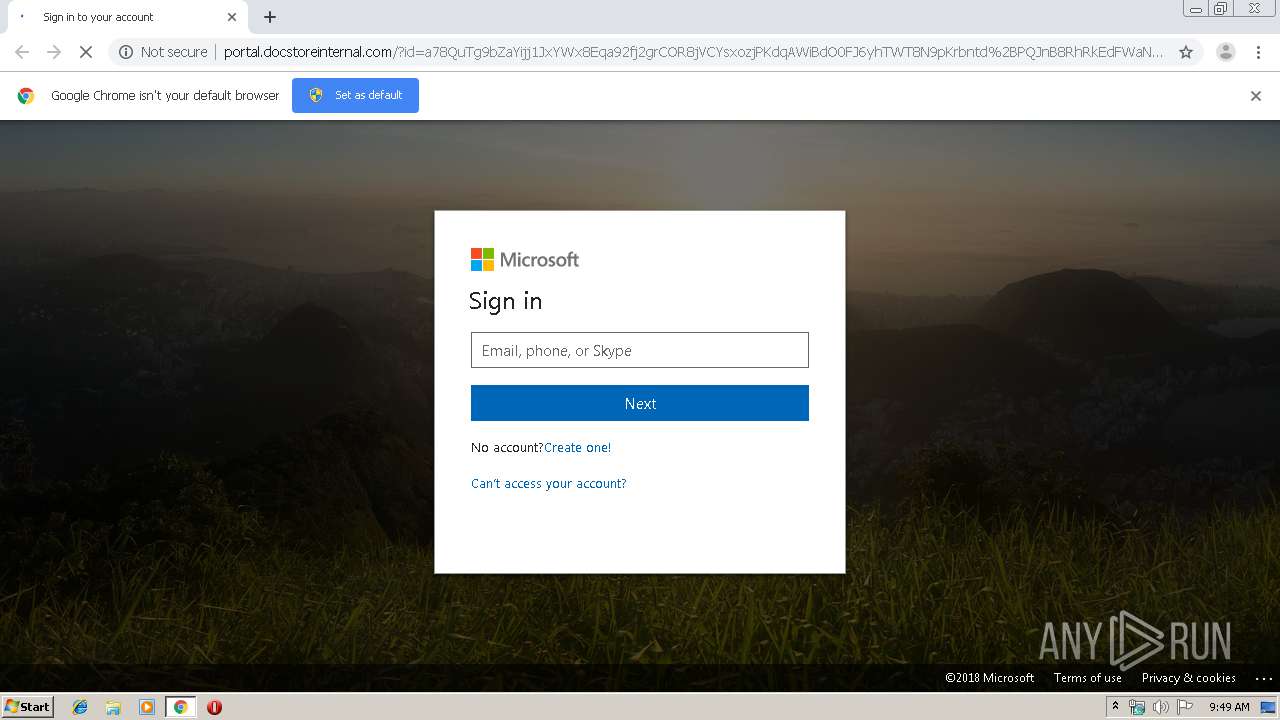
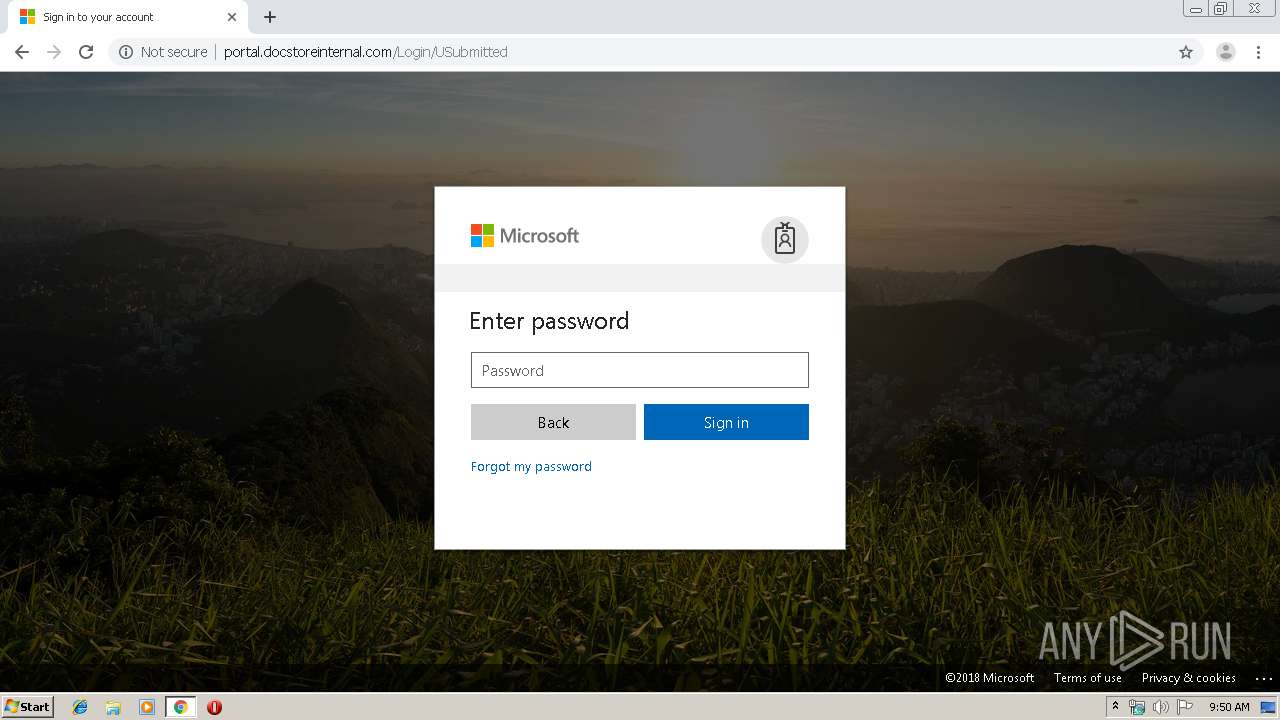
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 08:49:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0F3DAD8434DBF5EEBE4AF61F8F48B136 |
| SHA1: | 3740D473B69241C8F6CB7E2A3CDC49206C3124F8 |
| SHA256: | EE6059B48072165AC2AD8E0C49F2147C4DEC1E8ADDCCE5E7452D9DFD6AD9B19D |
| SSDEEP: | 6:COvL8GFEOKfdqvI1wR8ixJvvIWy+KX0yY+9xTZt0ambJ5INQKlthdgdVDXu10/0m:jAME5NI8i3wWy+G0yYoTZHmb3IQ8TdgP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2908)
INFO
Application launched itself
- chrome.exe (PID: 2908)
Reads the hosts file
- chrome.exe (PID: 2300)
- chrome.exe (PID: 2908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,6166223317441539846,18256257701750743084,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1842711853932012030 --mojo-platform-channel-handle=3308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,6166223317441539846,18256257701750743084,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17900335959200979081 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,6166223317441539846,18256257701750743084,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4408737655695276523 --mojo-platform-channel-handle=3332 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,6166223317441539846,18256257701750743084,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=377569240606658183 --mojo-platform-channel-handle=2764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2912 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,6166223317441539846,18256257701750743084,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13603178869486081022 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://portal.docstoreinternal.com/?id=a78QuTg9bZaYijj1JxYWx8Eqa92fj2grCOR8jVCYsxozjPKdqAWiBdO0FJ6yhTWT8N9pKrbntd%2BPQJnB8RhRkEdFWaNiDX40%2FlMZg8CUSL%2BBLi6ZWUN1gBmgF7V2VWSZEqsnX5AbTduTn8xI3opzWg7OkRPlHEPNDzOoXH%2B9N0MvmqDHuMISX4rP1dJqU7DJmqyomJ0O8x6jO4uSQF%2BLdEorgSvfiT2qjXD2o0tGYZMXmS4ExW%2BOmyT5Zfx%2B8bto4%2BwPJrEMmLH6ytyLbBvKDZ7gTzwk62subvLt4wRg7Xg%3D" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,6166223317441539846,18256257701750743084,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10148174442859939089 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,6166223317441539846,18256257701750743084,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1059766988373908344 --mojo-platform-channel-handle=2780 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,6166223317441539846,18256257701750743084,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7679041632995960148 --mojo-platform-channel-handle=3460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
598
Read events
512
Write events
81
Delete events
5
Modification events
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2908-13213356591189750 |
Value: 259 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
57
Text files
192
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9b00bbf5-d87a-4f0e-887c-c6747a18db40.tmp | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF16ac90.TMP | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF16accf.TMP | text | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF16ad2d.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
42
DNS requests
27
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/?id=a78QuTg9bZaYijj1JxYWx8Eqa92fj2grCOR8jVCYsxozjPKdqAWiBdO0FJ6yhTWT8N9pKrbntd%2BPQJnB8RhRkEdFWaNiDX40%2FlMZg8CUSL%2BBLi6ZWUN1gBmgF7V2VWSZEqsnX5AbTduTn8xI3opzWg7OkRPlHEPNDzOoXH%2B9N0MvmqDHuMISX4rP1dJqU7DJmqyomJ0O8x6jO4uSQF%2BLdEorgSvfiT2qjXD2o0tGYZMXmS4ExW%2BOmyT5Zfx%2B8bto4%2BwPJrEMmLH6ytyLbBvKDZ7gTzwk62subvLt4wRg7Xg%3D | US | html | 9.98 Kb | suspicious |
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/Content/newSignInFiles/prefetch.html | US | html | 704 b | suspicious |
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/Content/newSignInFiles/converged.login.min.css | US | text | 22.1 Kb | suspicious |
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/Content/newSignInFiles/firstScript.js | US | text | 19.1 Kb | suspicious |
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/Content/newSignInFiles/convergedlogin_pcore.min.js | US | text | 117 Kb | suspicious |
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/Content/newSignInFiles/jsonjs.js | US | text | 3.71 Kb | suspicious |
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/Content/newSignInFiles/morescript.js | US | text | 390 b | suspicious |
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/Content/newSignInFiles/0.jpg | US | image | 291 Kb | suspicious |
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/Content/newSignInFiles/microsoft_logo.svg | US | image | 3.57 Kb | suspicious |
2300 | chrome.exe | GET | 200 | 52.168.52.134:80 | http://portal.docstoreinternal.com/Content/newSignInFiles/convergedloginpaginatedstrings-en.min.js | US | text | 4.06 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2300 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2300 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2300 | chrome.exe | 52.168.52.134:80 | portal.docstoreinternal.com | Microsoft Corporation | US | suspicious |
2300 | chrome.exe | 184.31.91.84:443 | secure.aadcdn.microsoftonline-p.com | Akamai International B.V. | NL | whitelisted |
2300 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
2300 | chrome.exe | 2.18.232.217:443 | wusofficehome.msocdn.com | Akamai International B.V. | — | whitelisted |
2300 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
2300 | chrome.exe | 2.18.232.137:443 | r4.res.office365.com | Akamai International B.V. | — | whitelisted |
2300 | chrome.exe | 172.217.22.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2300 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
portal.docstoreinternal.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
secure.aadcdn.microsoftonline-p.com |
| whitelisted |
clients1.google.com |
| whitelisted |
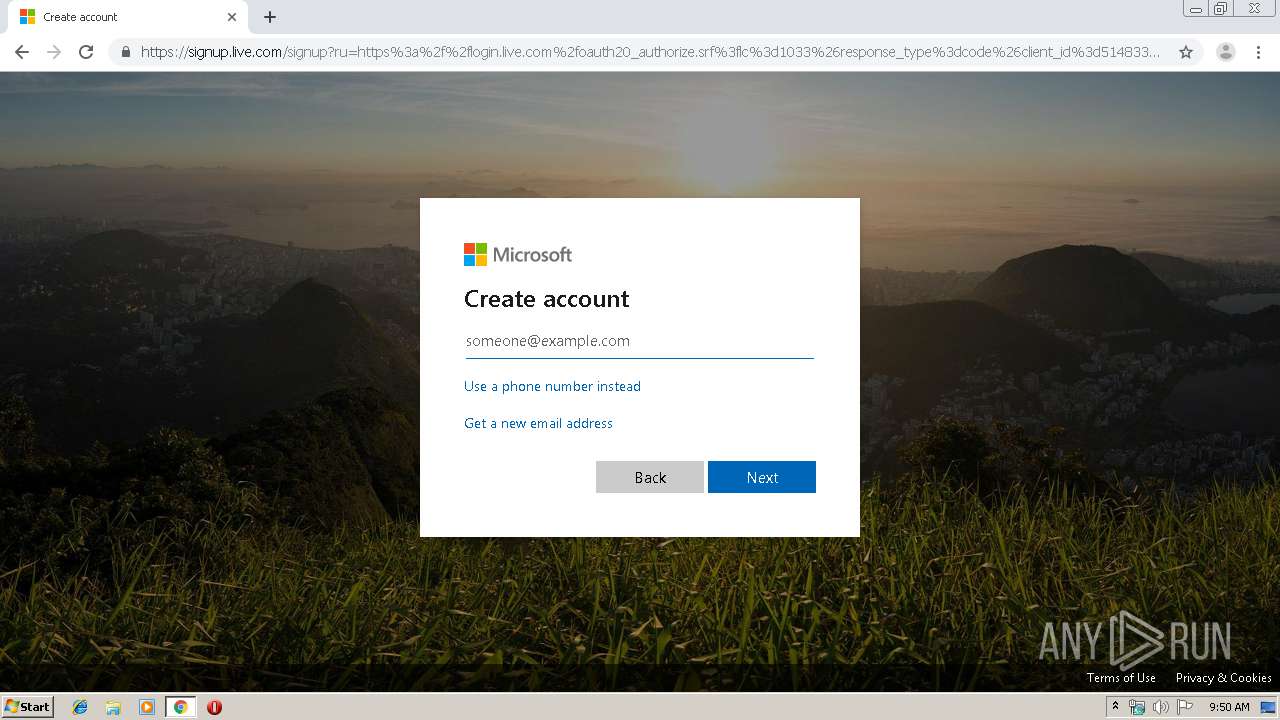
login.live.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
privacy.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
wusofficehome.msocdn.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2300 | chrome.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |
2300 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Cloned Website Phishing Landing - Saved Website Comment Observed |
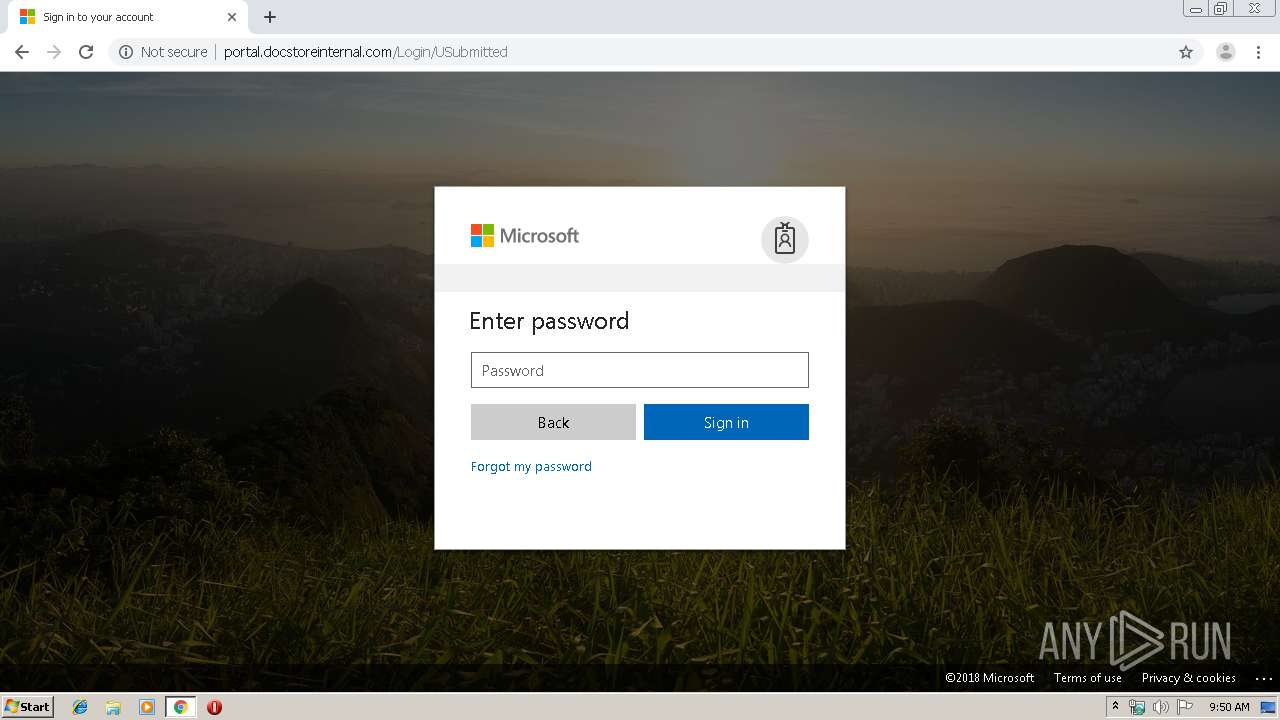
2300 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
1 ETPRO signatures available at the full report