| URL: | http://download1494.mediafire.com/ixe53lmdxbug/15g1zjm524p2rle/phần+mềm+gõ+phiên+âm+tiếng+trung+có+dấu.rar |
| Full analysis: | https://app.any.run/tasks/a9d9daeb-9217-4836-9b3f-e659950c6c8a |
| Verdict: | Malicious activity |
| Analysis date: | May 06, 2020, 08:55:07 |
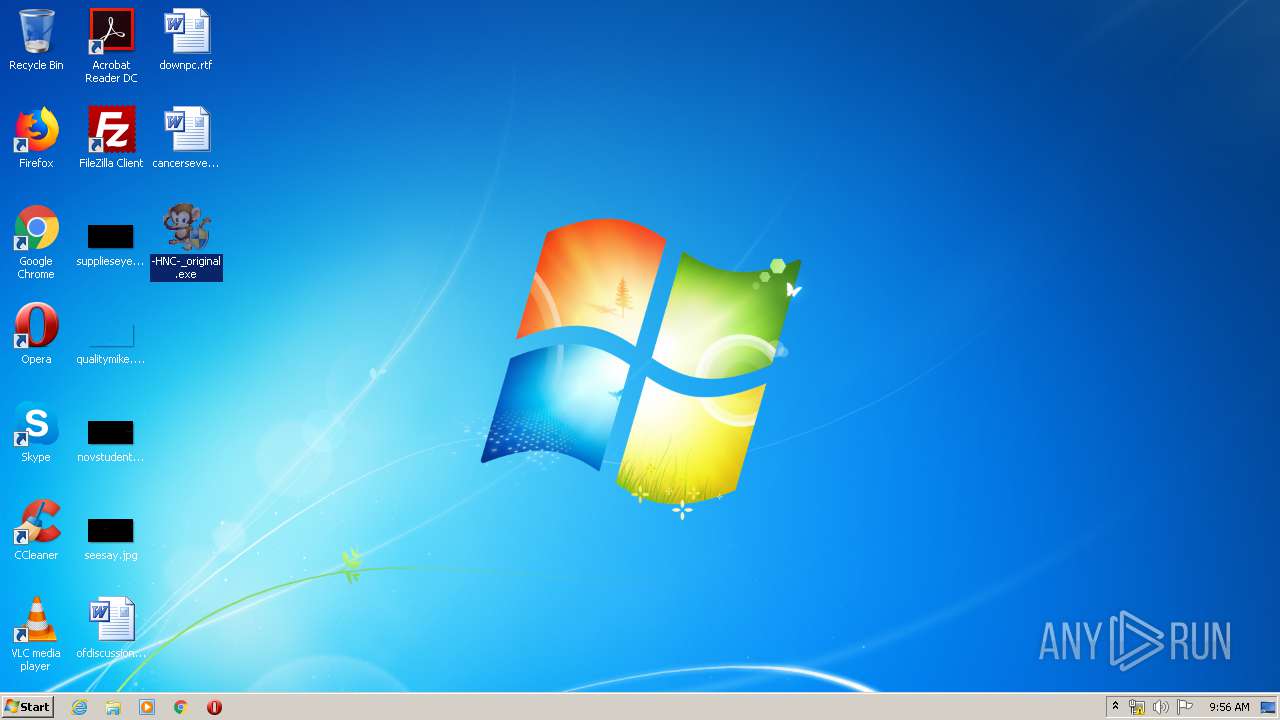
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A7E542A5E50792781B1D945531C68B11 |
| SHA1: | 32BD919173D7A8D53BB3A942F610EC88F620FEB7 |
| SHA256: | EE5FE5A25EF089006F8B375D9ED0664F602ADA1F57FA63F0FA155250DECC4A04 |
| SSDEEP: | 3:N1KaKE6ROw3eGbaGrwaQPPhHltmhOvMUn:CaAeGbaawaQPJHoON |
MALICIOUS
Application was dropped or rewritten from another process
- -HNC-_original.exe (PID: 3896)
- -HNC-_original.exe (PID: 2556)
- -HNC-_original.exe (PID: 2312)
- -HNC-_original.exe (PID: 1444)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3424)
Creates files in the user directory
- -HNC-_original.exe (PID: 1444)
Reads internet explorer settings
- -HNC-_original.exe (PID: 1444)
- -HNC-_original.exe (PID: 2312)
Reads Internet Cache Settings
- -HNC-_original.exe (PID: 1444)
- -HNC-_original.exe (PID: 2312)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 848)
- iexplore.exe (PID: 1492)
Application launched itself
- iexplore.exe (PID: 848)
Modifies the phishing filter of IE
- iexplore.exe (PID: 848)
Changes internet zones settings
- iexplore.exe (PID: 848)
Reads internet explorer settings
- iexplore.exe (PID: 1492)
Creates files in the user directory
- iexplore.exe (PID: 848)
- iexplore.exe (PID: 1492)
Manual execution by user
- -HNC-_original.exe (PID: 2556)
- -HNC-_original.exe (PID: 3896)
- -HNC-_original.exe (PID: 2312)
- -HNC-_original.exe (PID: 1444)
Reads settings of System Certificates
- iexplore.exe (PID: 848)
- iexplore.exe (PID: 1492)
Adds / modifies Windows certificates
- iexplore.exe (PID: 848)
Changes settings of System certificates
- iexplore.exe (PID: 848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://download1494.mediafire.com/ixe53lmdxbug/15g1zjm524p2rle/phần+mềm+gõ+phiên+âm+tiếng+trung+có+dấu.rar" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
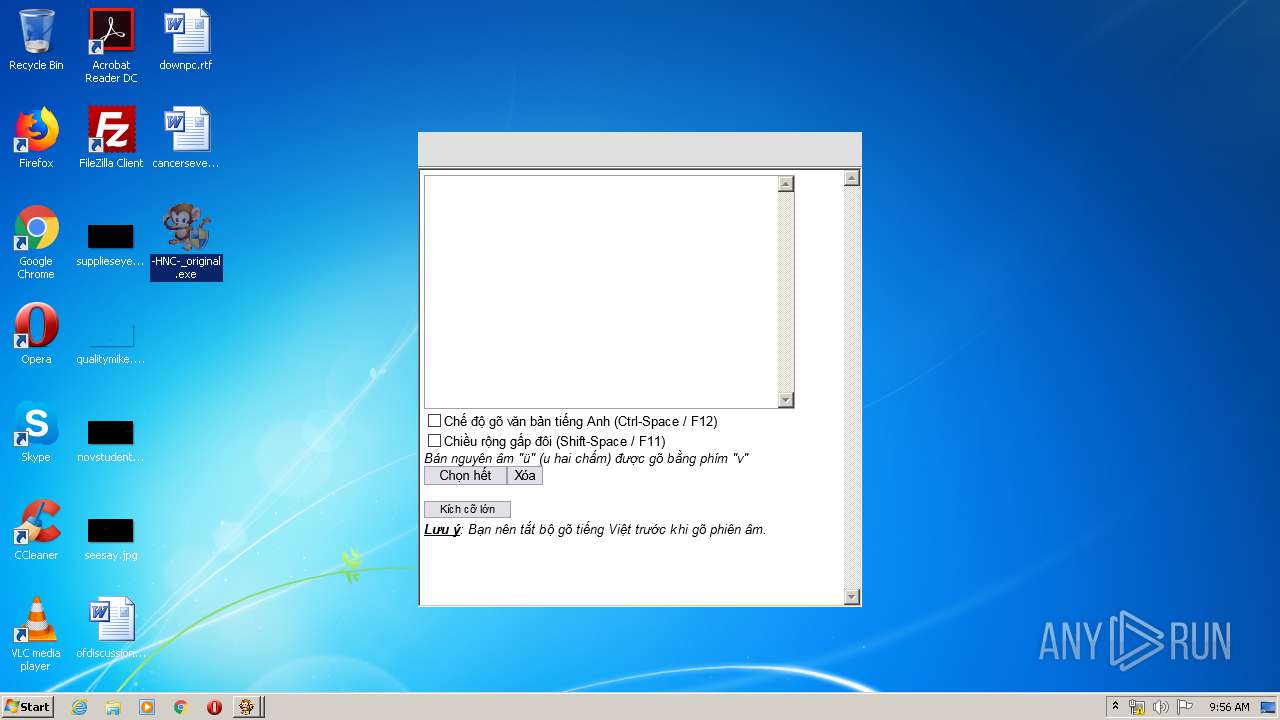
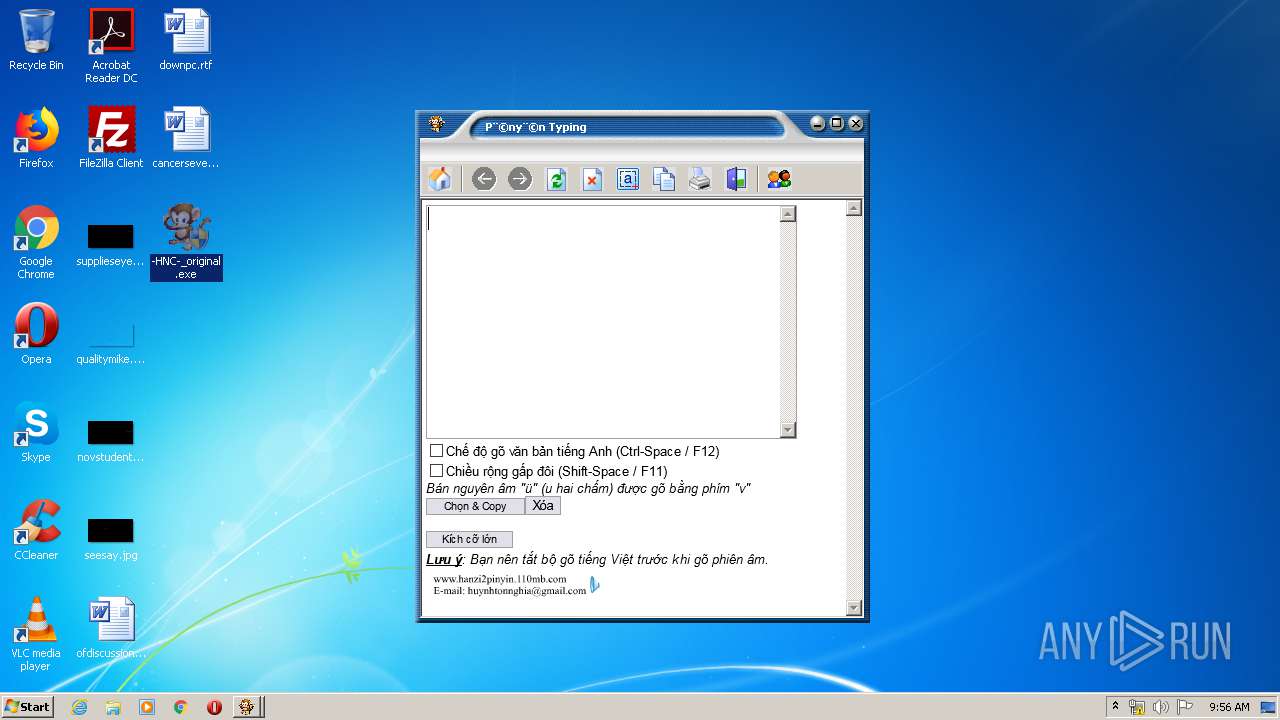
| 1444 | "C:\Users\admin\Desktop\-HNC-_original.exe" | C:\Users\admin\Desktop\-HNC-_original.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2.7.0.0 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:848 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2312 | "C:\Users\admin\Desktop\-HNC-_original.exe" | C:\Users\admin\Desktop\-HNC-_original.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2.7.0.0 Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\Desktop\-HNC-_original.exe" | C:\Users\admin\Desktop\-HNC-_original.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2.7.0.0 Modules
| |||||||||||||||
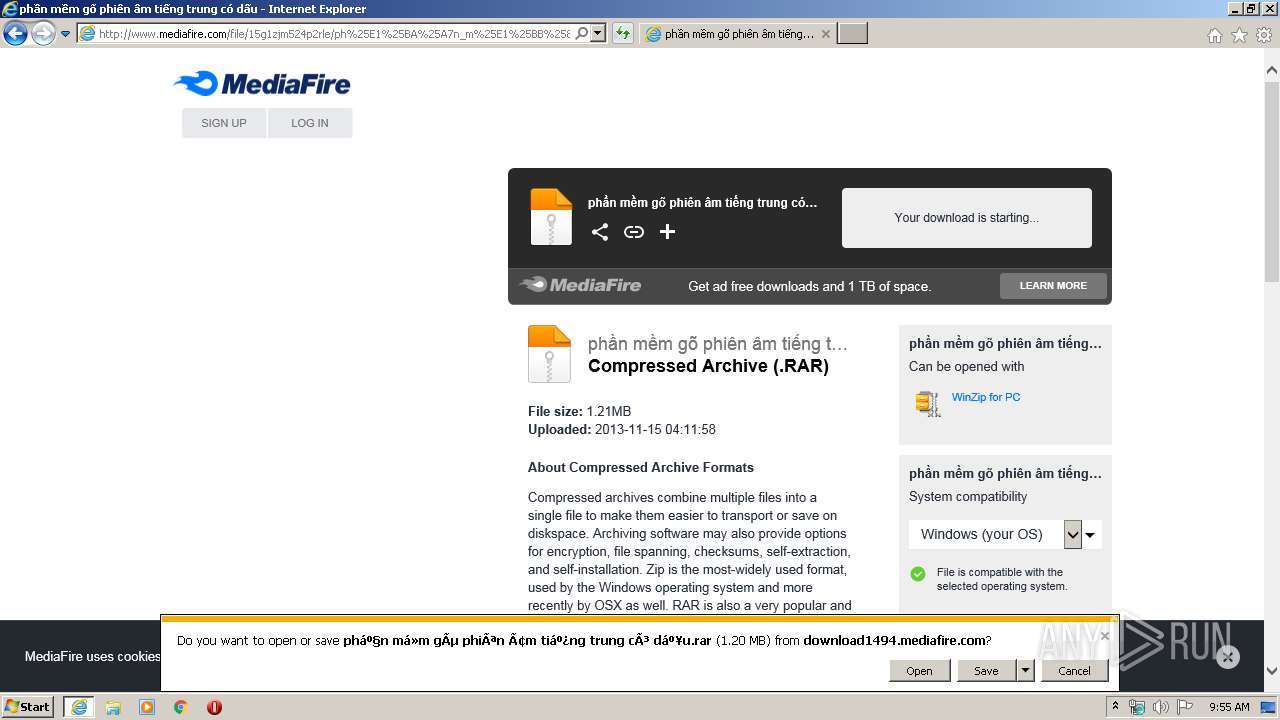
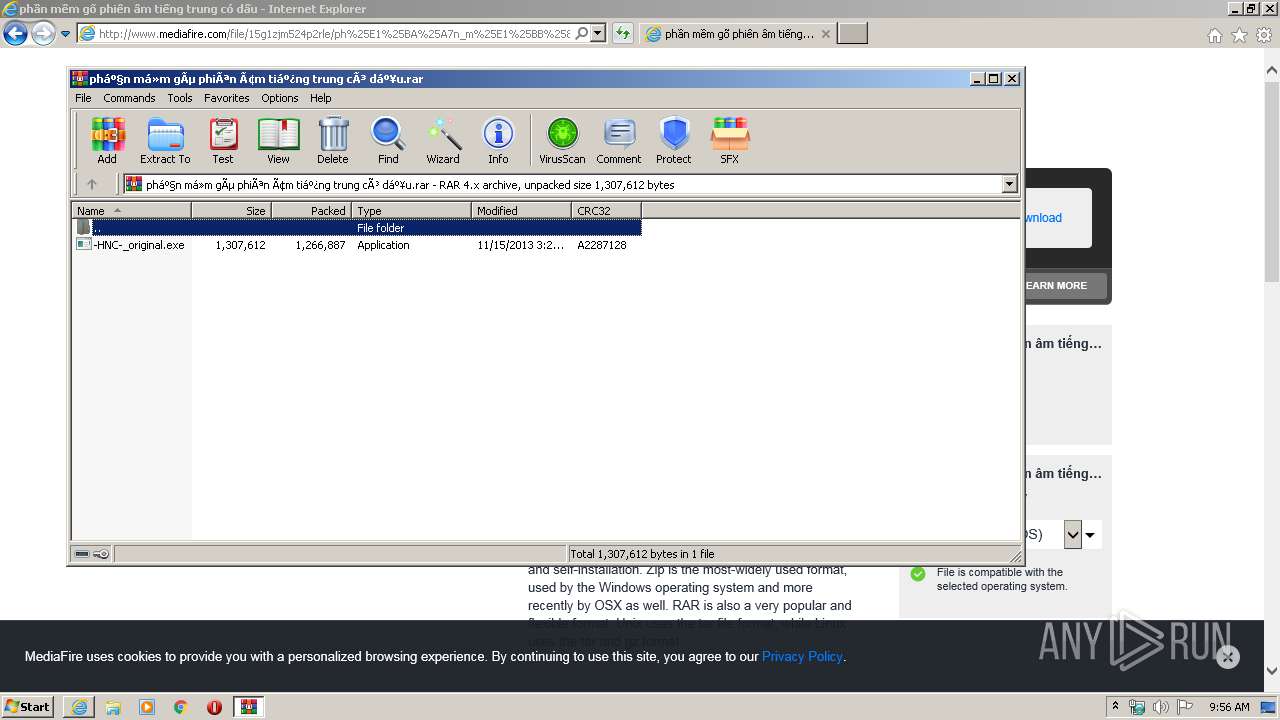
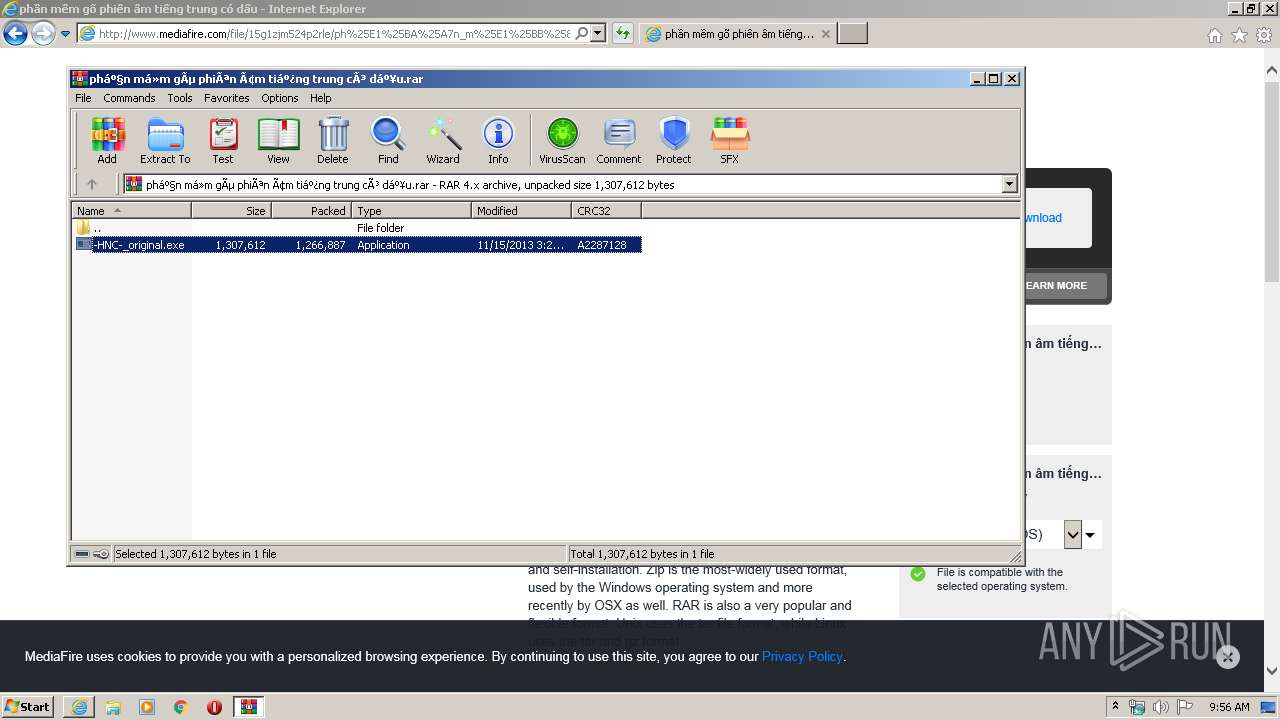
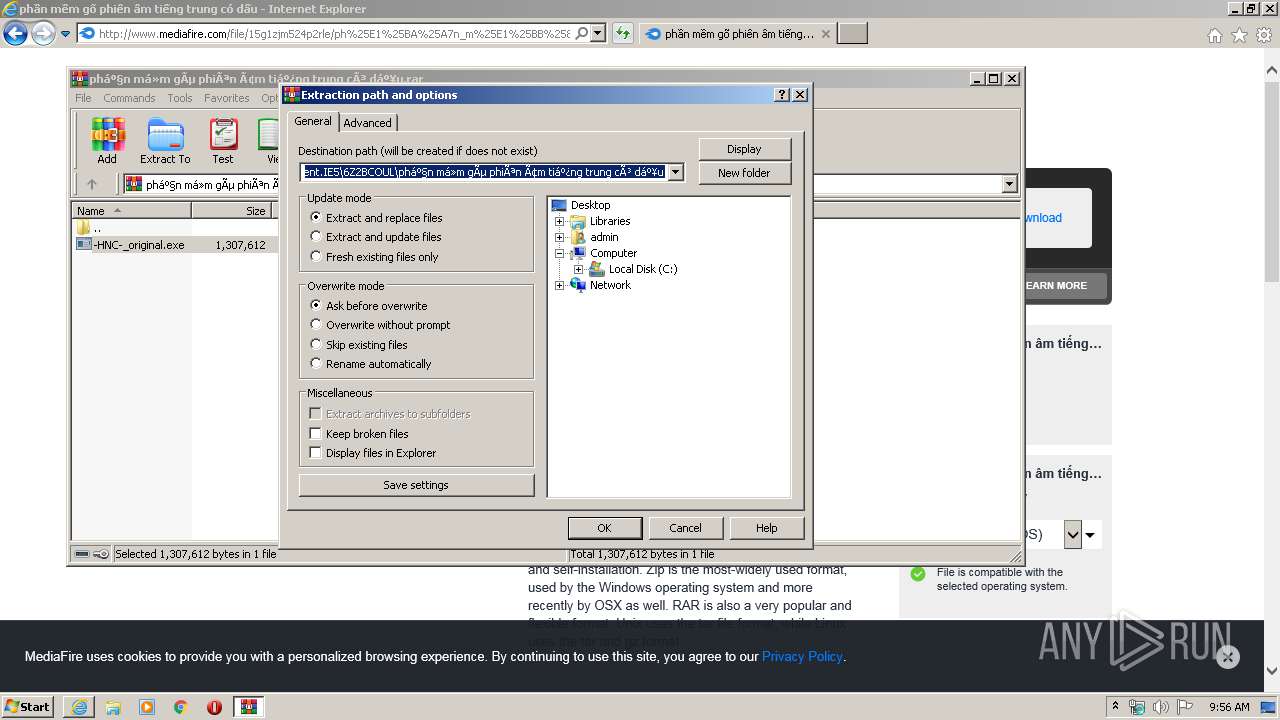
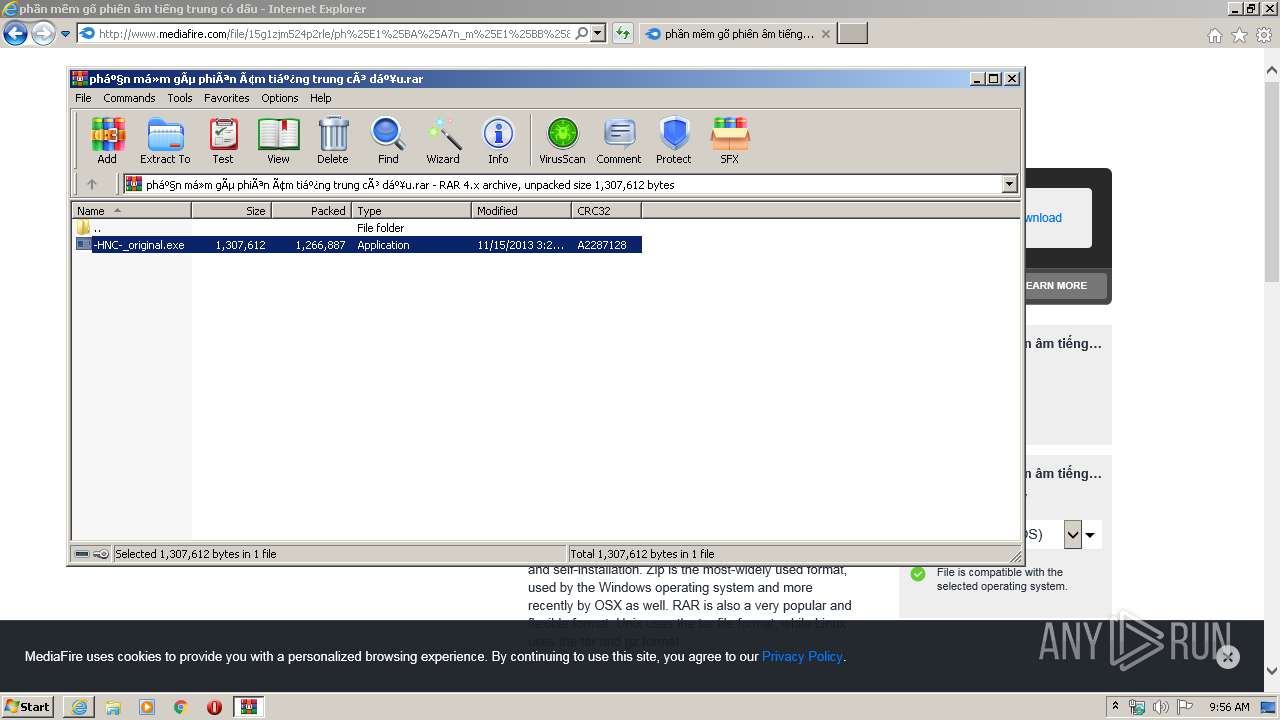
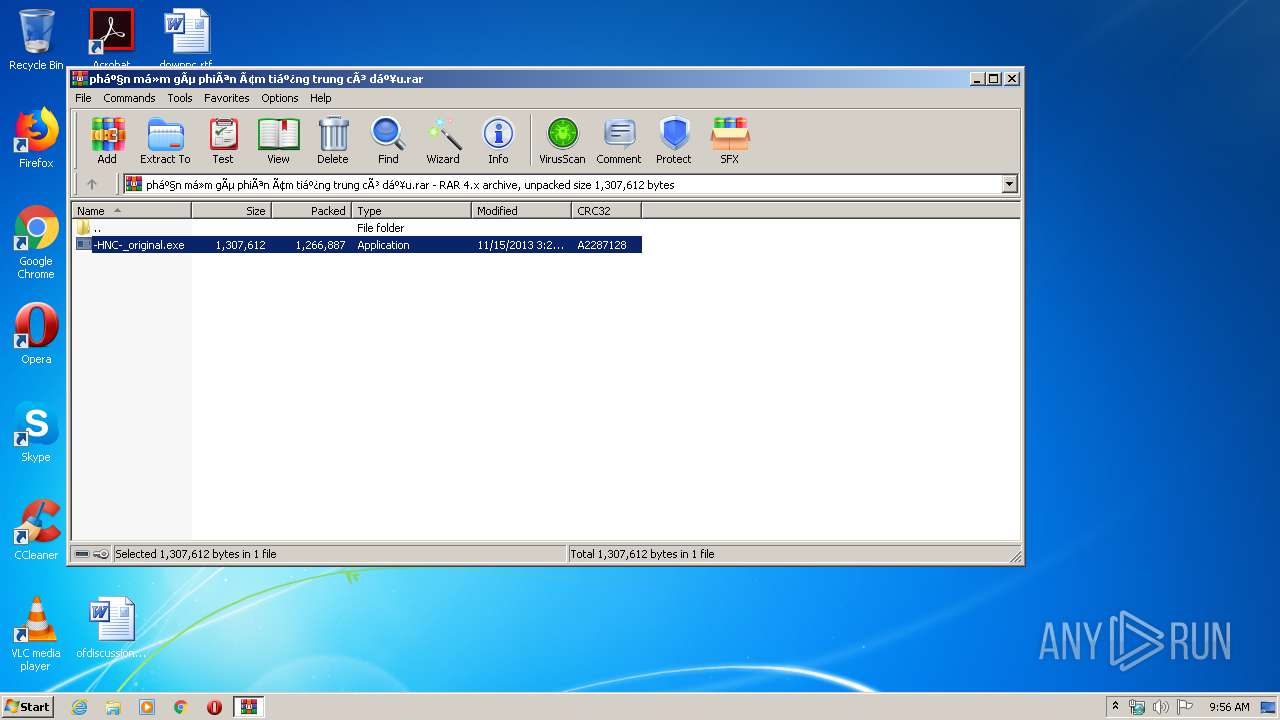
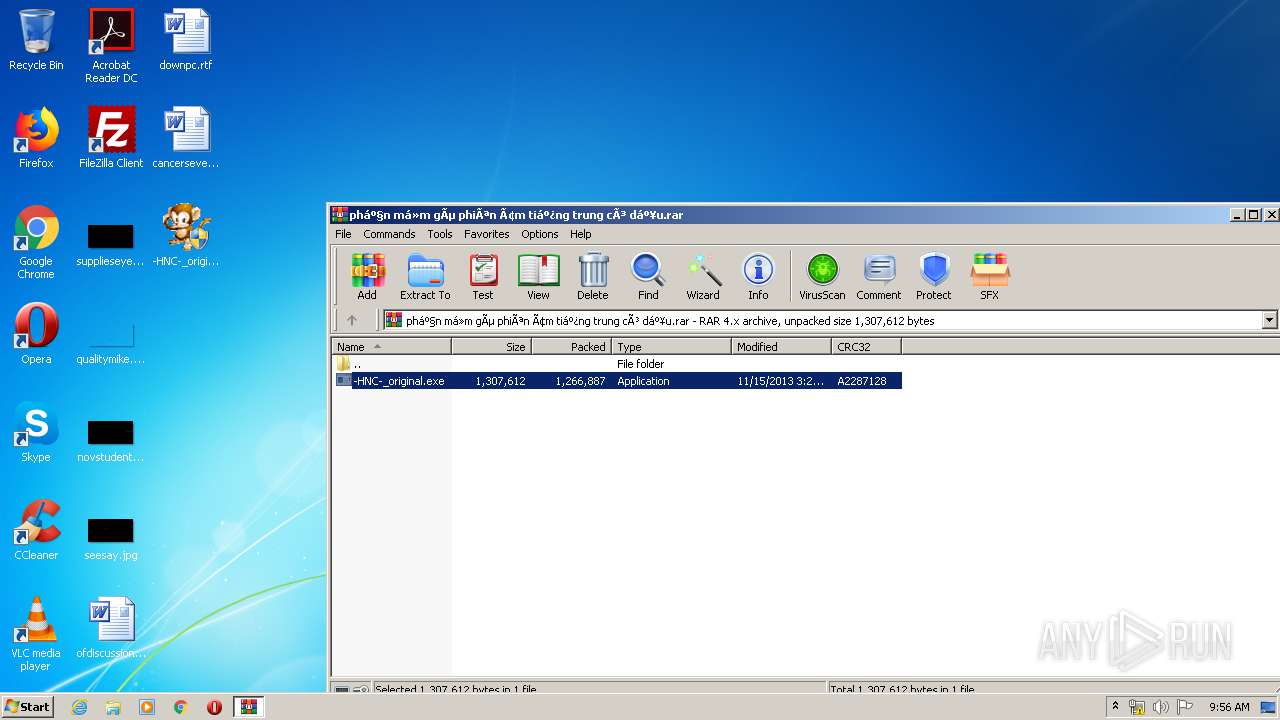
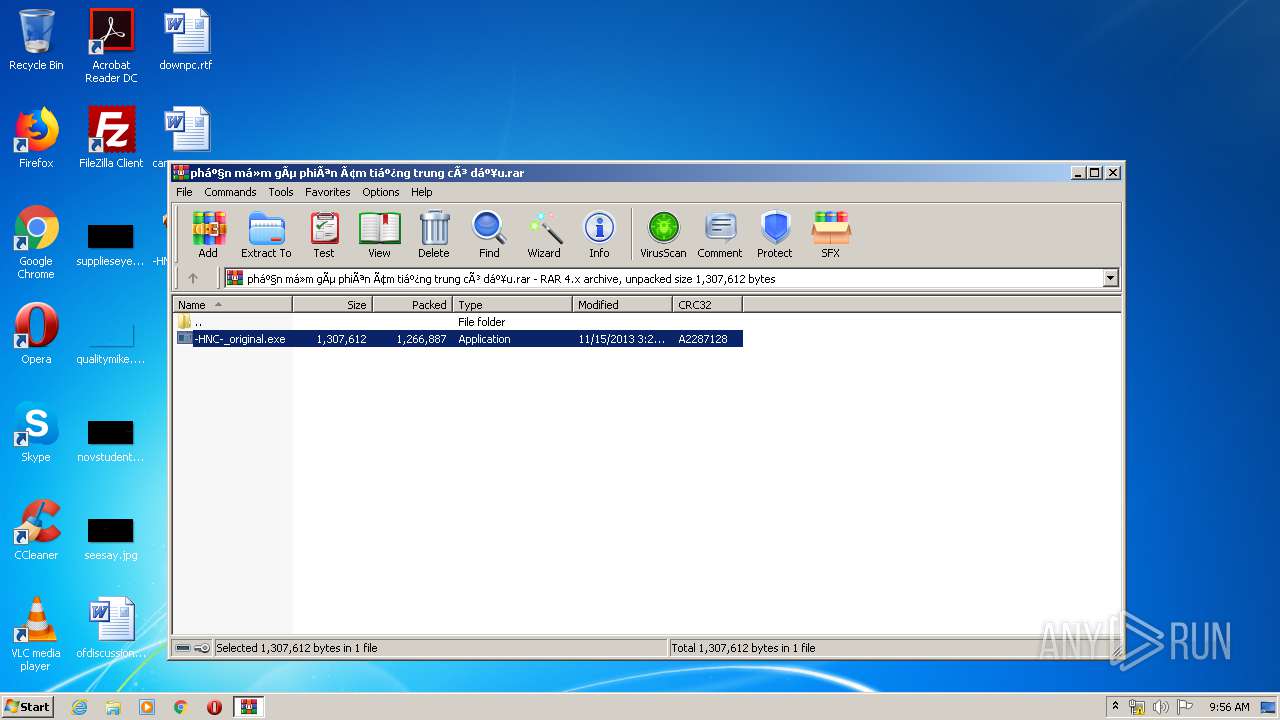
| 3424 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\phần má»m gõ phiên âm tiếng trung có dấu.rar" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\Desktop\-HNC-_original.exe" | C:\Users\admin\Desktop\-HNC-_original.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2.7.0.0 Modules
| |||||||||||||||
Total events
9 937
Read events
3 109
Write events
4 580
Delete events
2 248
Modification events
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 687973948 | |||
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30811012 | |||
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
152
Text files
135
Unknown types
88
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1492 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\K9MWBJ1S.txt | — | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\T11KJZXP.txt | — | |
MD5:— | SHA256:— | |||
| 848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9A6A.tmp | — | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9A6B.tmp | — | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download_repair[1].htm | html | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\838DLNA2.txt | text | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\master_121533[1].js | text | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\default[1].png | image | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\mfv3_121533[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
90
TCP/UDP connections
163
DNS requests
69
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
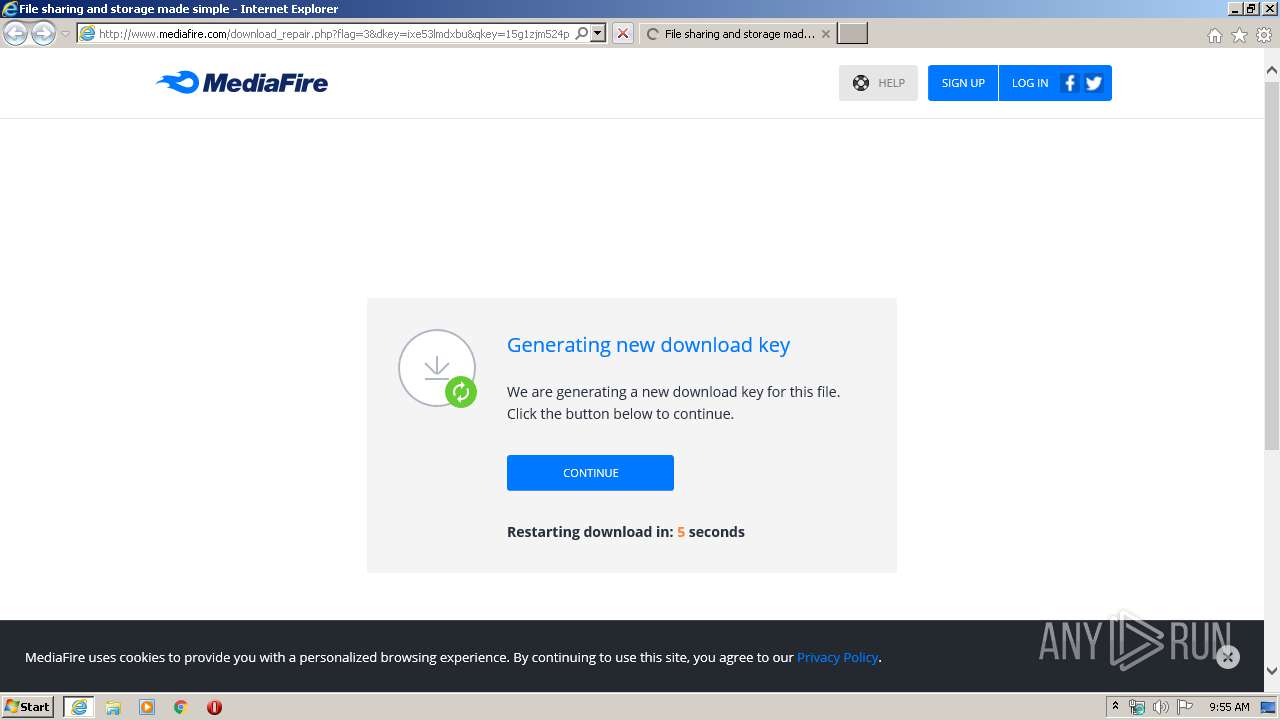
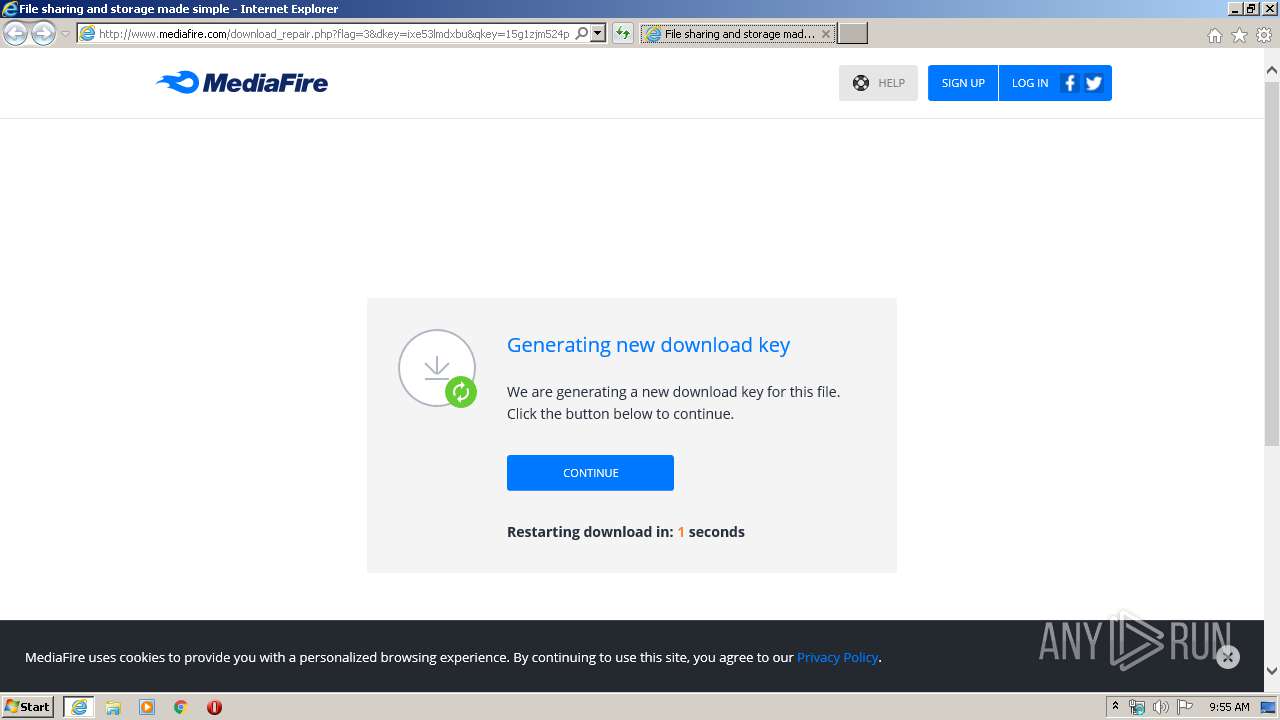
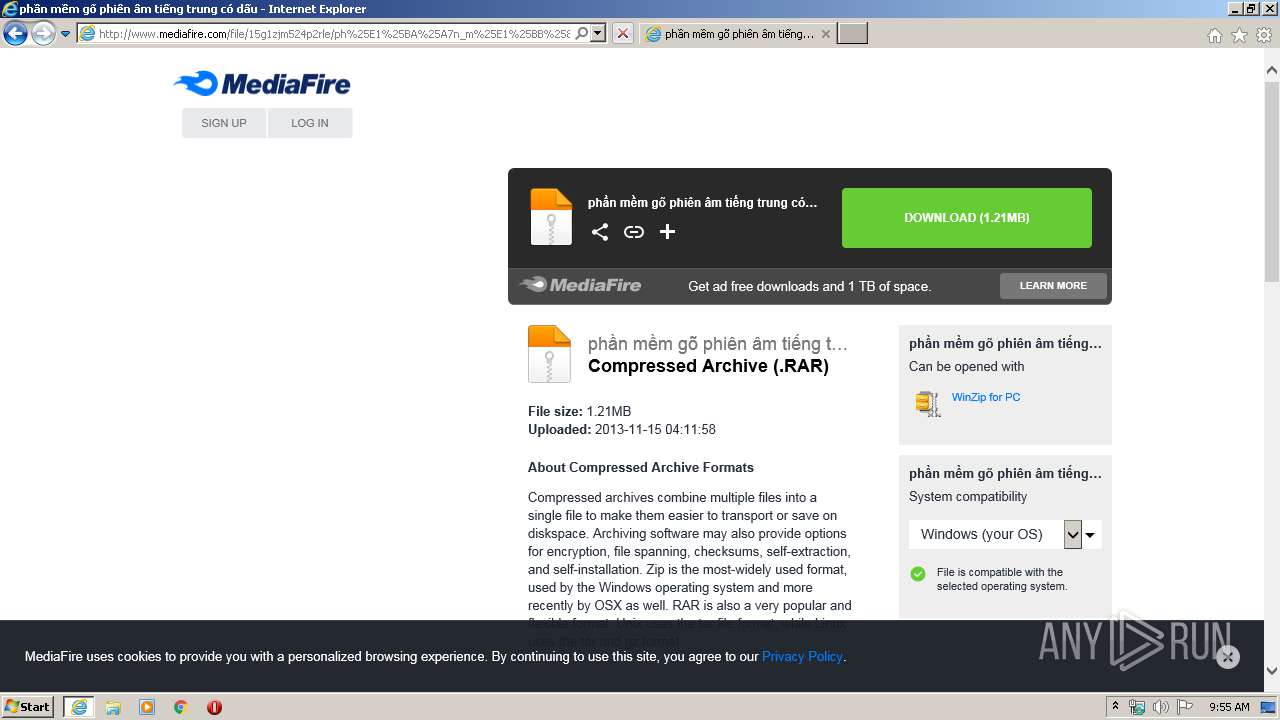
1492 | iexplore.exe | GET | 302 | 205.196.123.182:80 | http://download1494.mediafire.com/ixe53lmdxbug/15g1zjm524p2rle/ph%E1%BA%A7n+m%E1%BB%81m+g%C3%B5+phi%C3%AAn+%C3%A2m+ti%E1%BA%BFng+trung+c%C3%B3+d%E1%BA%A5u.rar | US | — | — | whitelisted |
1492 | iexplore.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/blank.html | US | html | 157 b | shared |
1492 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1492 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEApFQkhjIuntAgAAAABiB5I%3D | US | der | 471 b | whitelisted |
1492 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
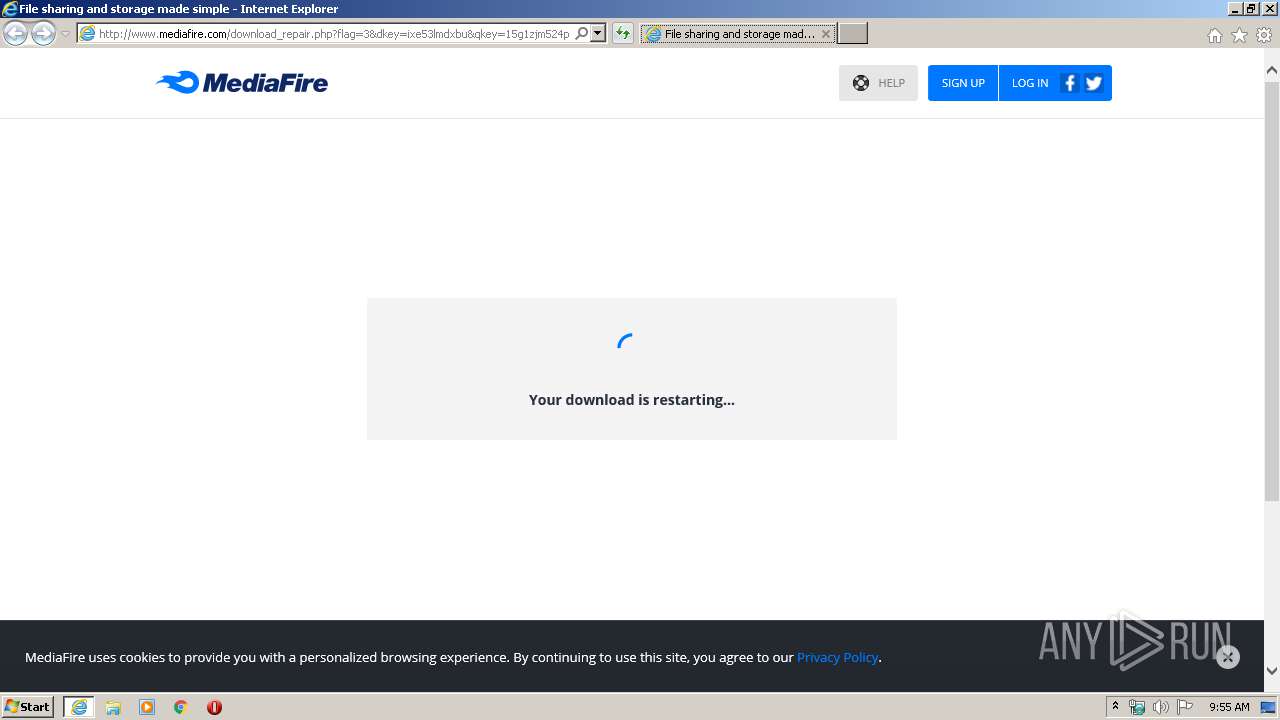
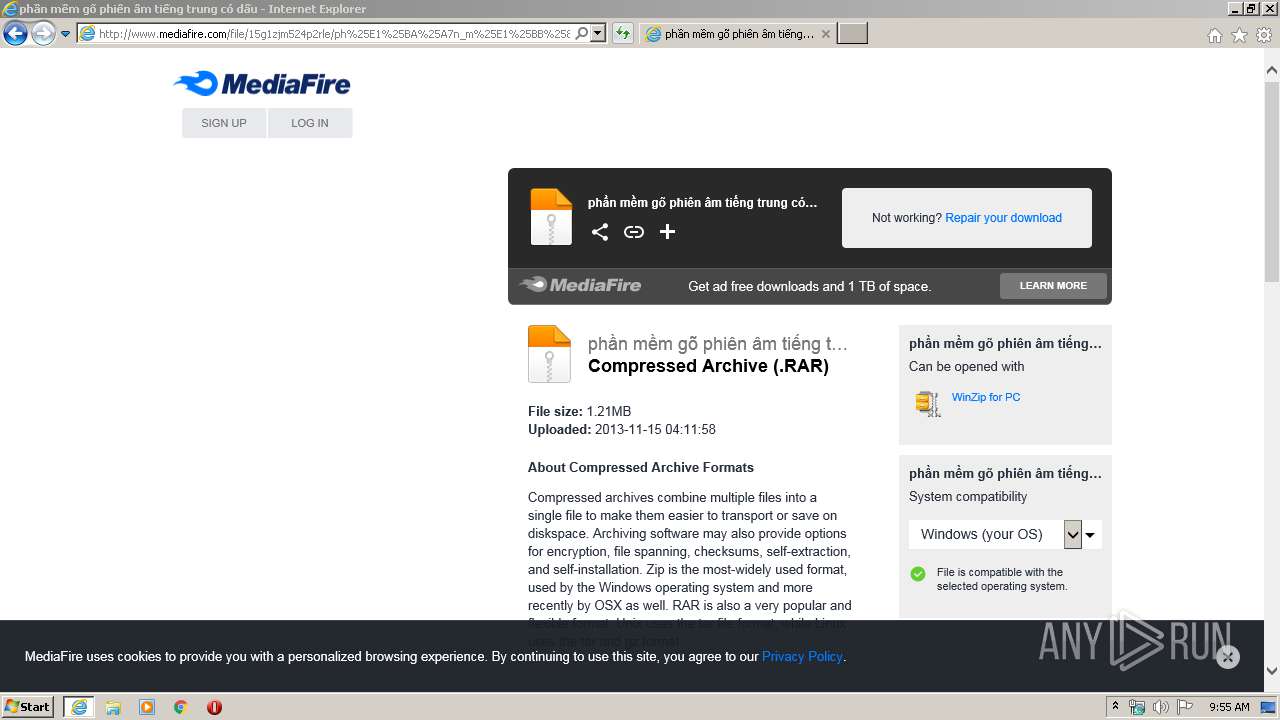
1492 | iexplore.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/download_repair.php?flag=3&dkey=ixe53lmdxbu&qkey=15g1zjm524p2rle&ip=159.148.186.246&ref=3 | US | html | 9.59 Kb | shared |
1492 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDE9U%2B0StibRggAAAAAOMpn | US | der | 472 b | whitelisted |
1492 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1492 | iexplore.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/images/icons/myfiles/default.png | US | image | 424 b | shared |
1492 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCRu%2FeBs4lAmgIAAAAAYgcP | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1492 | iexplore.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1492 | iexplore.exe | 31.13.92.14:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1492 | iexplore.exe | 172.217.23.110:80 | translate.google.com | Google Inc. | US | whitelisted |
1492 | iexplore.exe | 31.13.92.14:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1492 | iexplore.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1492 | iexplore.exe | 205.196.123.182:80 | — | MediaFire, LLC | US | suspicious |
1492 | iexplore.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
1492 | iexplore.exe | 172.217.18.4:443 | download1494.mediafire.com | Google Inc. | US | whitelisted |
1492 | iexplore.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
848 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download1494.mediafire.com |
| whitelisted |
www.mediafire.com |
| shared |
static.mediafire.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1492 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1492 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |