| File name: | AA_v3.exe |
| Full analysis: | https://app.any.run/tasks/b876d04f-8512-446f-b197-fdd1cdadae4a |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2022, 12:35:48 |
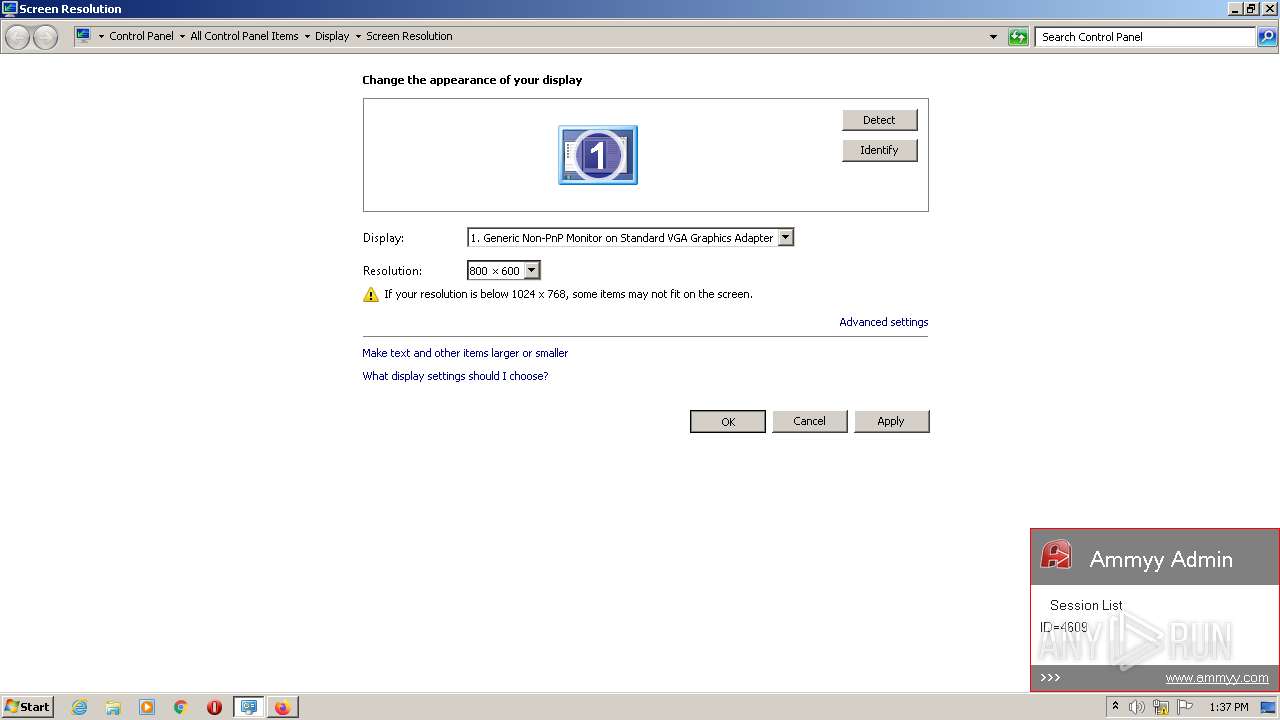
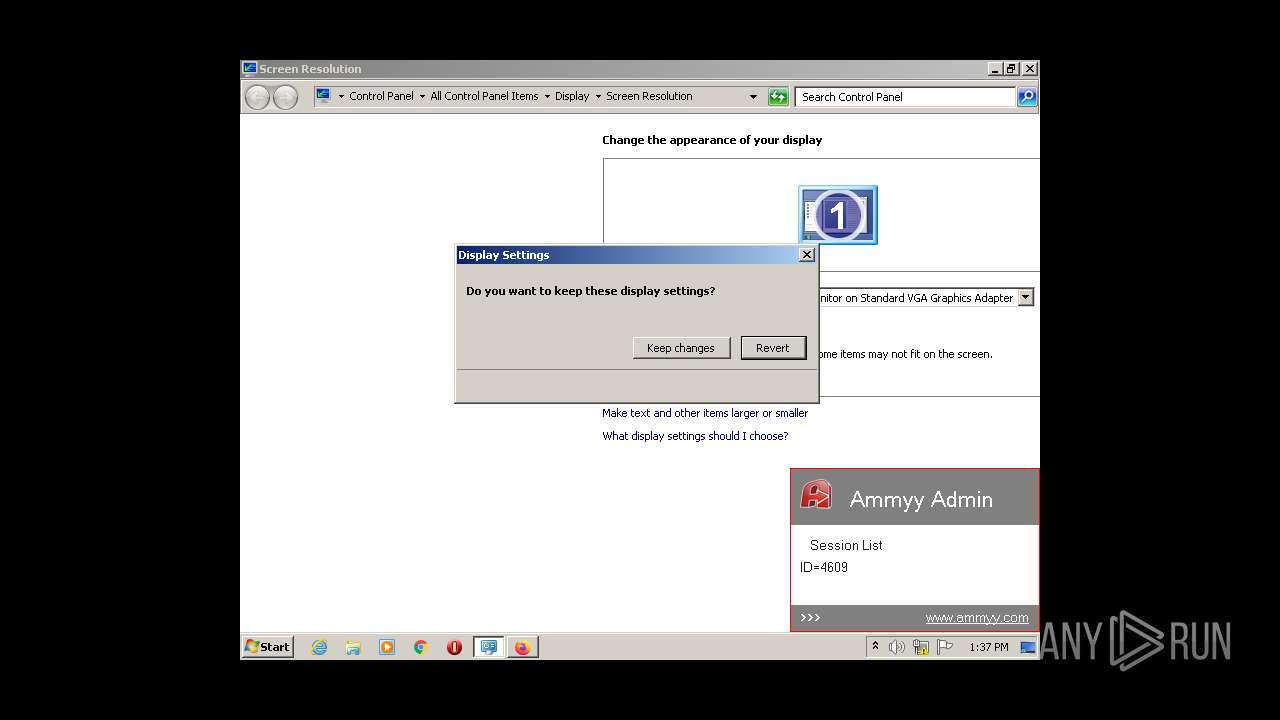
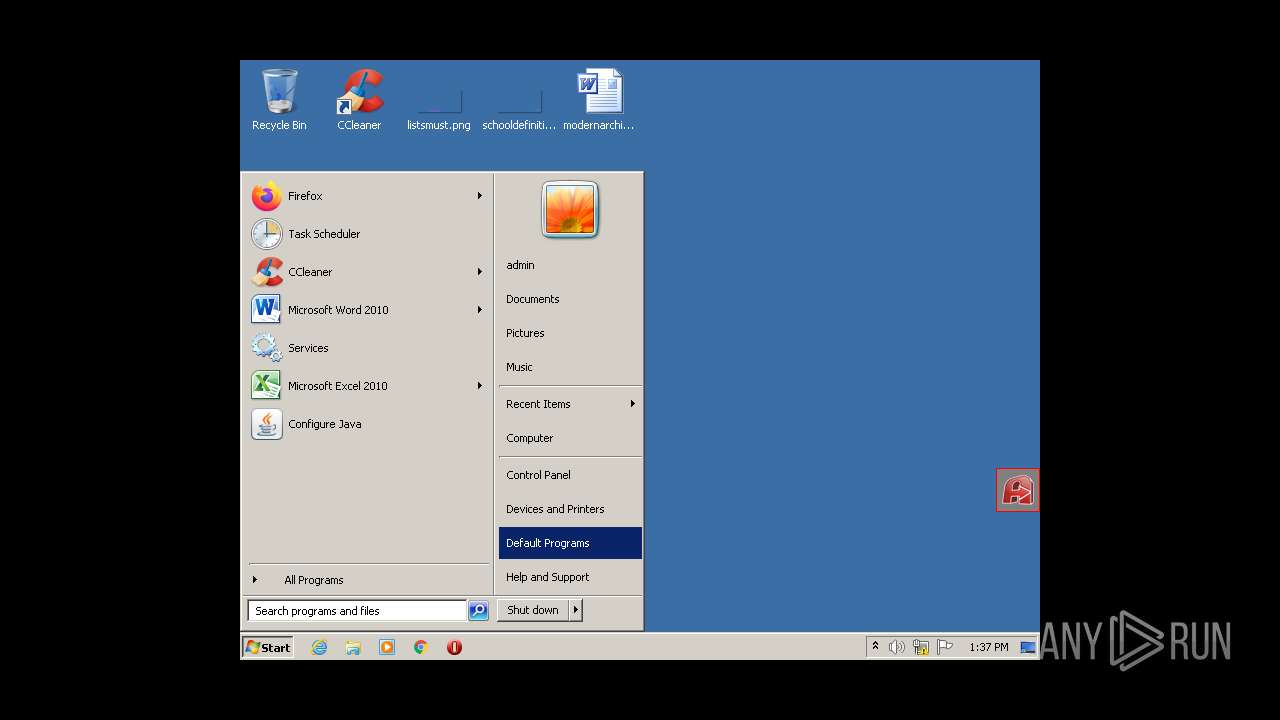
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 90AADF2247149996AE443E2C82AF3730 |
| SHA1: | 050B7EBA825412B24E3F02D76D7DA5AE97E10502 |
| SHA256: | EE573647477339784DCEF81024DE1BE1762833A20E5CC2B89A93E47D05B86B6A |
| SSDEEP: | 24576:Uj0JJ4p/A4npt3XojeQG5EtzRtO7GvmDguXd:UjoJ4u4zojegylDN |
MALICIOUS
Deletes the SafeBoot registry key
- AA_v3.exe (PID: 664)
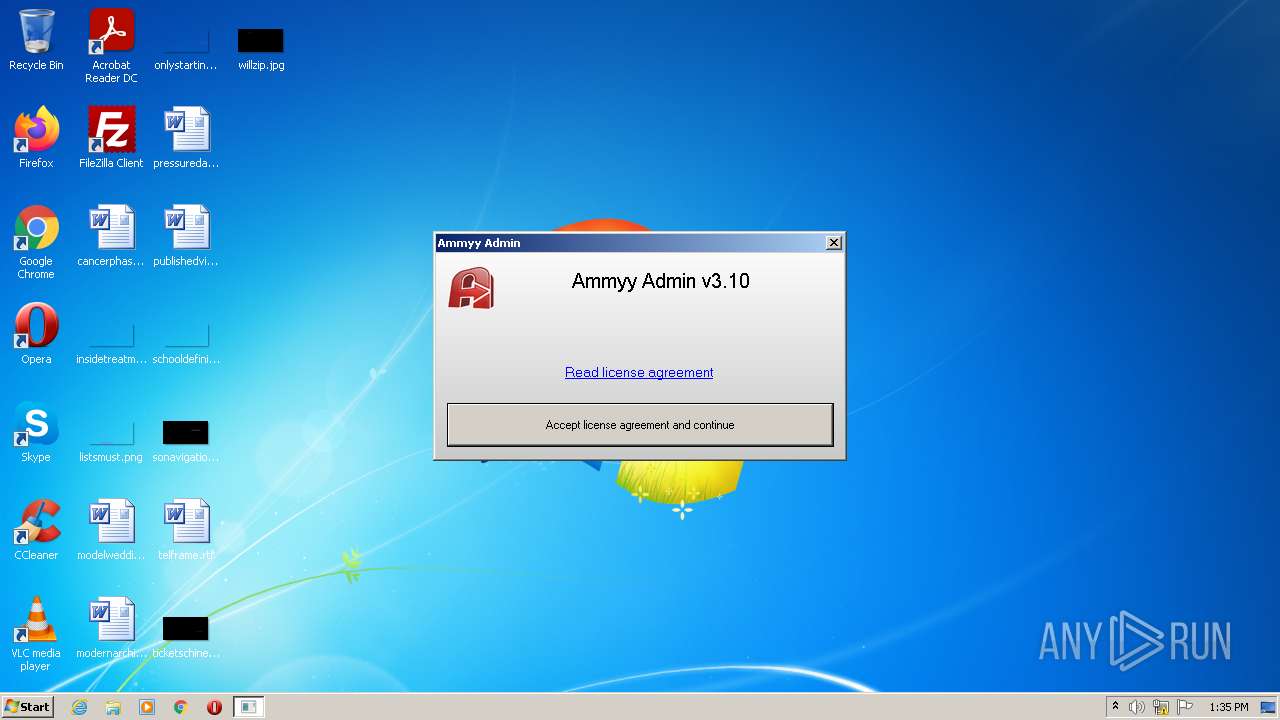
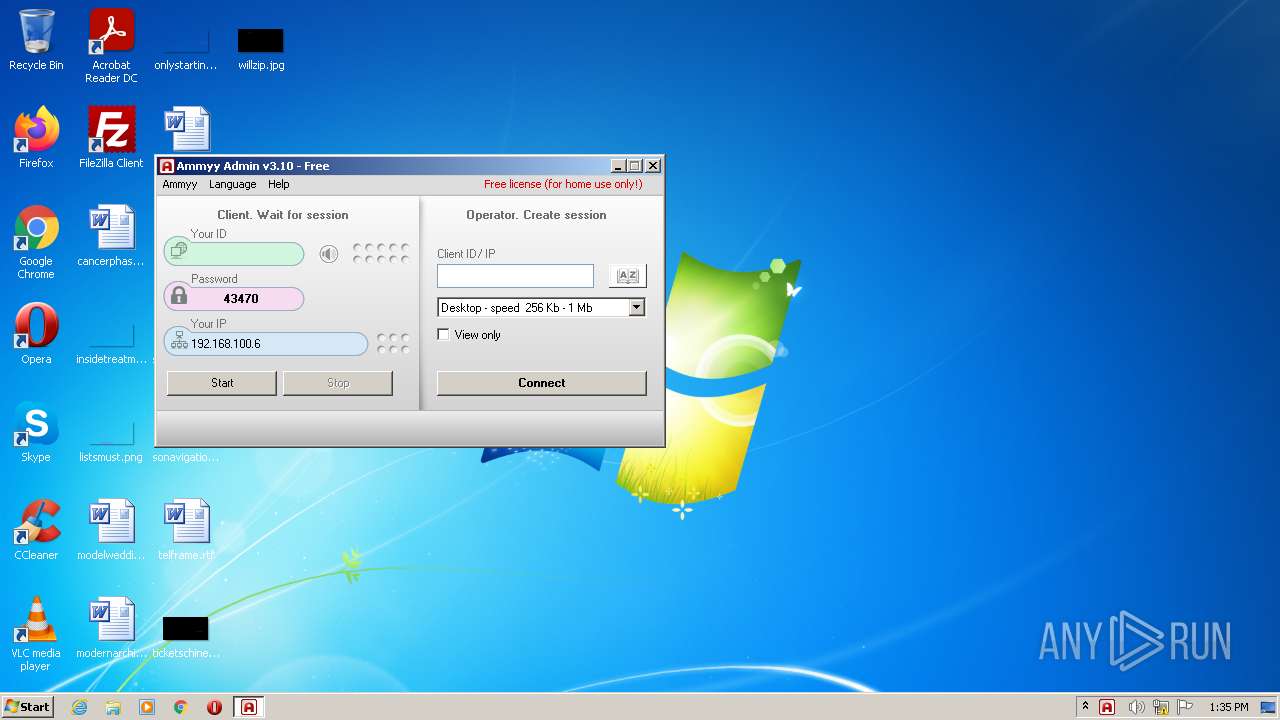
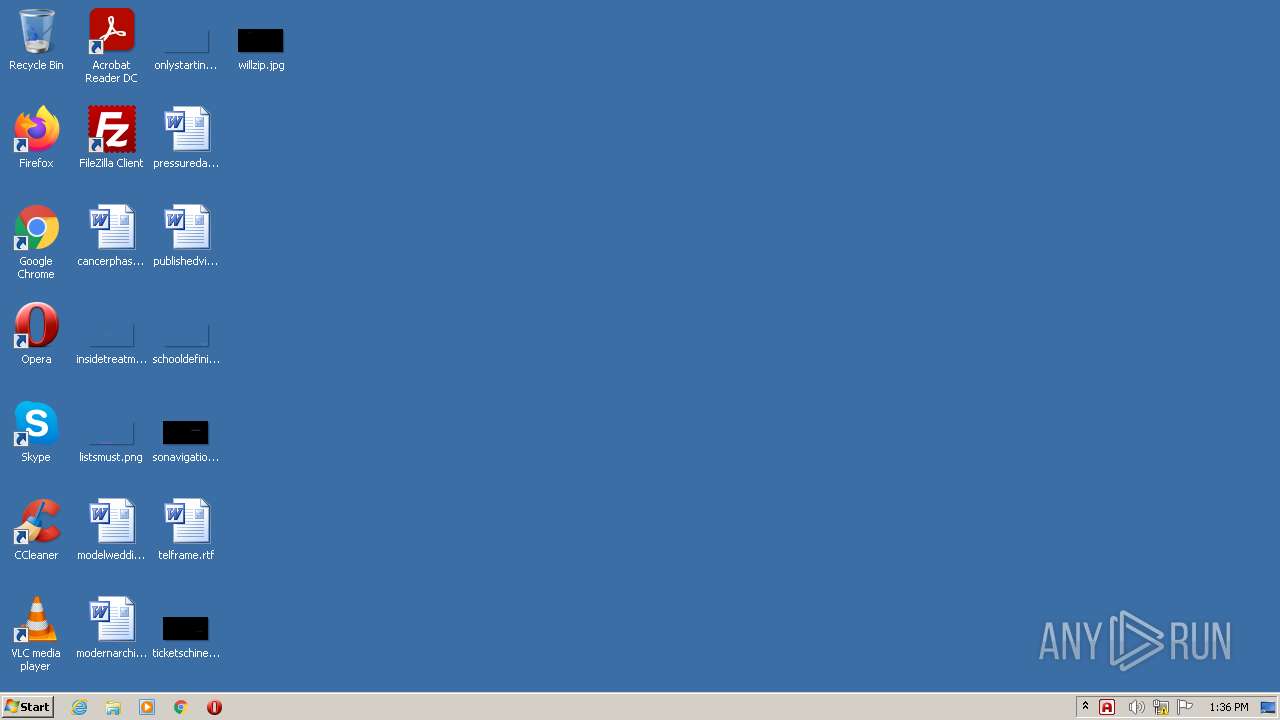
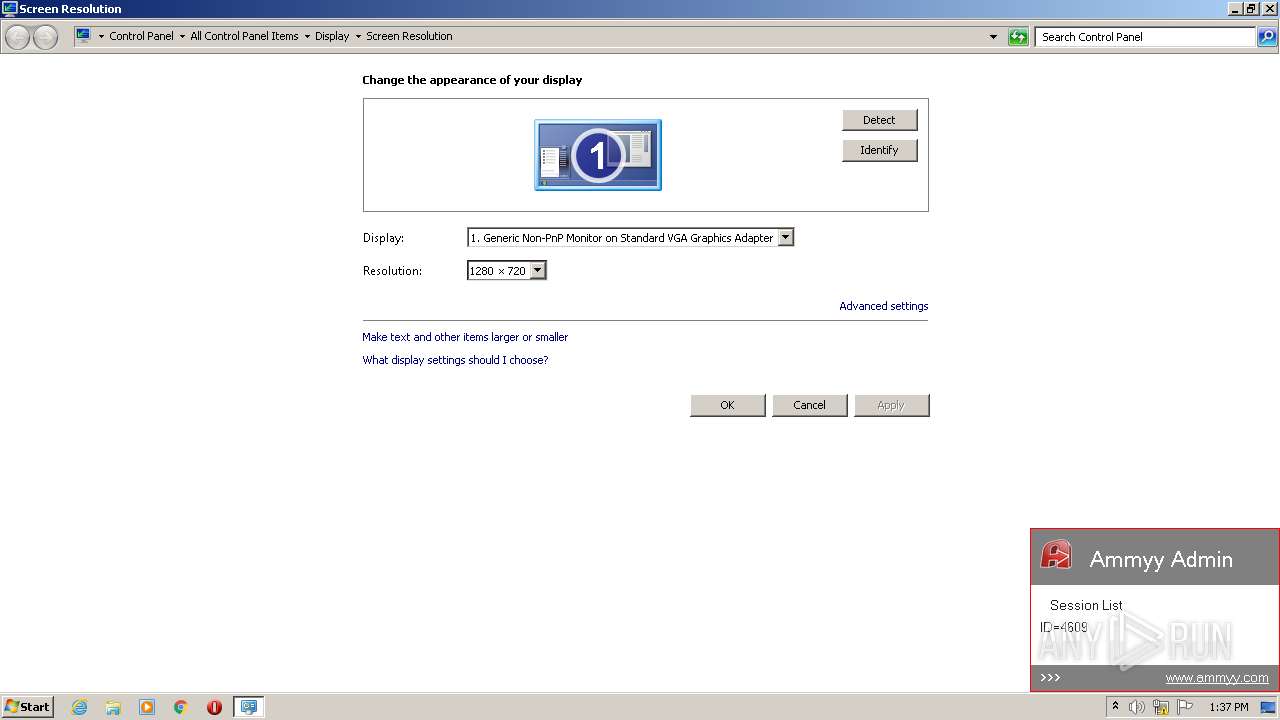
AMMYY was detected
- AA_v3.exe (PID: 3120)
Drops executable file immediately after starts
- AA_v3.exe (PID: 3120)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3108)
Changes settings of System certificates
- AA_v3.exe (PID: 3120)
SUSPICIOUS
Reads the computer name
- AA_v3.exe (PID: 3120)
- AA_v3.exe (PID: 2700)
- AA_v3.exe (PID: 664)
- AA_v3.exe (PID: 568)
Checks supported languages
- AA_v3.exe (PID: 664)
- AA_v3.exe (PID: 568)
- AA_v3.exe (PID: 2700)
- AA_v3.exe (PID: 3120)
Application launched itself
- AA_v3.exe (PID: 568)
- AA_v3.exe (PID: 2700)
Executed as Windows Service
- AA_v3.exe (PID: 2700)
Creates files in the program directory
- AA_v3.exe (PID: 568)
- AA_v3.exe (PID: 3120)
Checks for external IP
- AA_v3.exe (PID: 3120)
Drops a file with a compile date too recent
- AA_v3.exe (PID: 3120)
Removes files from Windows directory
- AA_v3.exe (PID: 3120)
Adds / modifies Windows certificates
- AA_v3.exe (PID: 3120)
Uses RUNDLL32.EXE to load library
- AA_v3.exe (PID: 3120)
Executable content was dropped or overwritten
- AA_v3.exe (PID: 3120)
Creates files in the Windows directory
- AA_v3.exe (PID: 3120)
INFO
Application launched itself
- firefox.exe (PID: 3760)
- firefox.exe (PID: 2936)
Checks supported languages
- firefox.exe (PID: 2936)
- firefox.exe (PID: 3760)
- firefox.exe (PID: 3656)
- firefox.exe (PID: 628)
- firefox.exe (PID: 2484)
- rundll32.exe (PID: 3108)
- firefox.exe (PID: 3060)
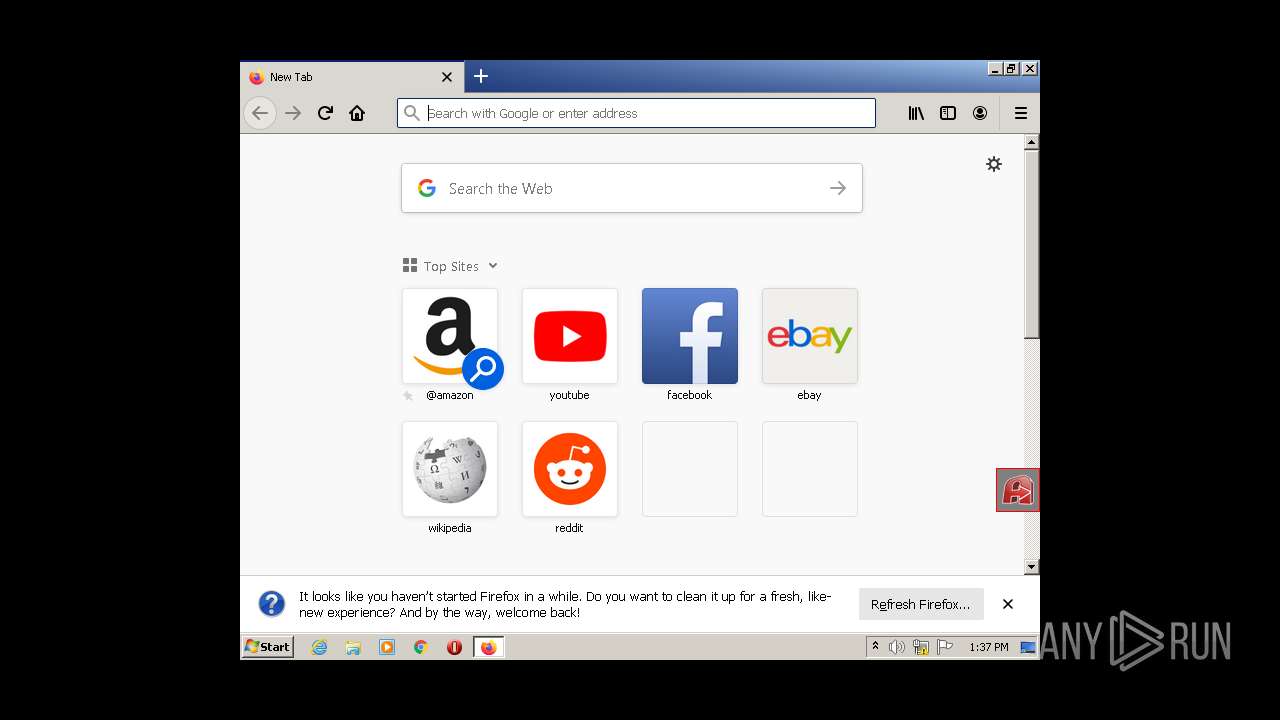
Manual execution by user
- firefox.exe (PID: 3760)
Reads CPU info
- firefox.exe (PID: 2936)
Creates files in the user directory
- firefox.exe (PID: 2936)
Reads the computer name
- firefox.exe (PID: 2484)
- firefox.exe (PID: 3656)
- firefox.exe (PID: 628)
- firefox.exe (PID: 2936)
- firefox.exe (PID: 3060)
Creates files in the program directory
- firefox.exe (PID: 2936)
Reads the date of Windows installation
- firefox.exe (PID: 2936)
Checks Windows Trust Settings
- AA_v3.exe (PID: 3120)
Reads settings of System Certificates
- AA_v3.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| SpecialBuild: | - |
|---|---|
| ProductVersion: | 3.1 |
| ProductName: | Ammyy Admin |
| PrivateBuild: | - |
| OriginalFileName: | - |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | Ammyy Admin |
| FileVersion: | 3.1 |
| FileDescription: | Ammyy Admin |
| CompanyName: | Ammyy LLC |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.10.0.0 |
| FileVersionNumber: | 3.10.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x86db8 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 258048 |
| CodeSize: | 581632 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2020:09:15 18:09:42+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Sep-2020 16:09:42 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Ammyy LLC |
| FileDescription: | Ammyy Admin |
| FileVersion: | 3.10 |
| InternalName: | Ammyy Admin |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| PrivateBuild: | - |
| ProductName: | Ammyy Admin |
| ProductVersion: | 3.10 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-Sep-2020 16:09:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DBBA | 0x0008E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70222 |
.rdata | 0x0008F000 | 0x0001A5A6 | 0x0001B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16793 |
.data | 0x000AA000 | 0x0001EBB8 | 0x00017000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.21636 |
.rsrc | 0x000C9000 | 0x00004490 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.41822 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29974 | 1474 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.72434 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 6.13946 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
128 | 2.4763 | 48 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
150 | 0 | 1 | UNKNOWN | UNKNOWN | BINARY |
Imports
ADVAPI32.dll |
COMCTL32.dll |
DSOUND.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
Secur32.dll |
Total processes
48
Monitored processes
11
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Users\admin\AppData\Local\Temp\AA_v3.exe" | C:\Users\admin\AppData\Local\Temp\AA_v3.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Ammyy LLC Integrity Level: MEDIUM Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2936.13.1144045479\871315463" -childID 2 -isForBrowser -prefsHandle 3188 -prefMapHandle 3184 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2936 "\\.\pipe\gecko-crash-server-pipe.2936" 3200 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 664 | "C:\Users\admin\AppData\Local\Temp\AA_v3.exe" -elevated | C:\Users\admin\AppData\Local\Temp\AA_v3.exe | AA_v3.exe | ||||||||||||
User: admin Company: Ammyy LLC Integrity Level: HIGH Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2936.0.309084442\502701682" -parentBuildID 20201112153044 -prefsHandle 1128 -prefMapHandle 1120 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2936 "\\.\pipe\gecko-crash-server-pipe.2936" 1212 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 83.0 Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\Temp\AA_v3.exe" -service -lunch | C:\Users\admin\AppData\Local\Temp\AA_v3.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2936.20.607930043\89348110" -childID 3 -isForBrowser -prefsHandle 3516 -prefMapHandle 3292 -prefsLen 7399 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2936 "\\.\pipe\gecko-crash-server-pipe.2936" 3540 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3108 | rundll32.exe "C:\ProgramData\AMMYY\aa_nts.dll",run | C:\Windows\system32\rundll32.exe | — | AA_v3.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3120 | "C:\Users\admin\AppData\Local\Temp\AA_v3.exe" -elevated | C:\Users\admin\AppData\Local\Temp\AA_v3.exe | AA_v3.exe | ||||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 3656 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2936.6.1593744660\1371038397" -childID 1 -isForBrowser -prefsHandle 2504 -prefMapHandle 2500 -prefsLen 245 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2936 "\\.\pipe\gecko-crash-server-pipe.2936" 2516 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
12 869
Read events
12 801
Write events
67
Delete events
1
Modification events
| (PID) Process: | (568) AA_v3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (568) AA_v3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (568) AA_v3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (568) AA_v3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (664) AA_v3.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\AmmyyAdmin_298 |
| Operation: | write | Name: | (default) |
Value: Service | |||
| (PID) Process: | (664) AA_v3.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\AmmyyAdmin_298 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3120) AA_v3.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3120) AA_v3.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3120) AA_v3.exe | Key: | HKEY_USERS\.DEFAULT\Software\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: 5E8E65D7BCD29EBFA27EF07EE0F856471AA6B18D83E0C40627919C06AA257A12D751783814D5BFD55BE8041DD84B7F941DAFFE996C9CEE271E7FFDD10946EAAF98D1834B | |||
| (PID) Process: | (3120) AA_v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: 5E8E65D7BCD29EBFA27EF07EE0F856471AA6B18D83E0C40627919C06AA257A12D751783814D5BFD55BE8041DD84B7F941DAFFE996C9CEE271E7FFDD10946EAAF98D1834B | |||
Executable files
1
Suspicious files
120
Text files
32
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3120 | AA_v3.exe | C:\ProgramData\AMMYY\hr3 | binary | |
MD5:2E6E2B2F465F6925912081538F208F9A | SHA256:2875224FAED9463320B5F8A9C4316485F13FE5635CA18497E1D61FF19465E0E9 | |||
| 568 | AA_v3.exe | C:\ProgramData\AMMYY\settings3.bin | binary | |
MD5:4655A2FD572F21586221B7ECE461038A | SHA256:42DD1272A2A552EA1819CFB3AB314AEDCBBB2A91B526EFD41752203499B62CF8 | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:994A33896BB41A278A315D0D796422B6 | SHA256:54EC50A20FFF8CC016710E49437CF6A11D3FE5EE7B28C185E4A9AAFEE2908B63 | |||
| 2936 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:F47A84BADD5A50E42E4EE5AA331D2B34 | SHA256:C2CBBDCB2402784DE1DF943A8034FAA2D52F7ABE6DEF8D447A26C5C9C2AF6388 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
24
DNS requests
59
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3120 | AA_v3.exe | POST | 200 | 188.42.129.148:80 | http://rl.ammyy.com/ | NL | text | 246 b | suspicious |
2936 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2936 | firefox.exe | POST | 200 | 142.250.179.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3120 | AA_v3.exe | GET | 301 | 136.243.18.118:80 | http://www.ammyy.com/files/v7/aans32.gz | DE | html | 326 b | suspicious |
2936 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3120 | AA_v3.exe | GET | 200 | 8.241.79.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?4b3c15353a53fa92 | US | compressed | 59.5 Kb | whitelisted |
3120 | AA_v3.exe | GET | 200 | 8.241.79.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3e0e31088d596e66 | US | compressed | 4.70 Kb | whitelisted |
3120 | AA_v3.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
3120 | AA_v3.exe | GET | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPXbW1rz02JXT71f9%2BJ8jRndQ%3D%3D | US | der | 503 b | shared |
2936 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3120 | AA_v3.exe | 184.24.77.48:80 | r3.o.lencr.org | Time Warner Cable Internet LLC | US | unknown |
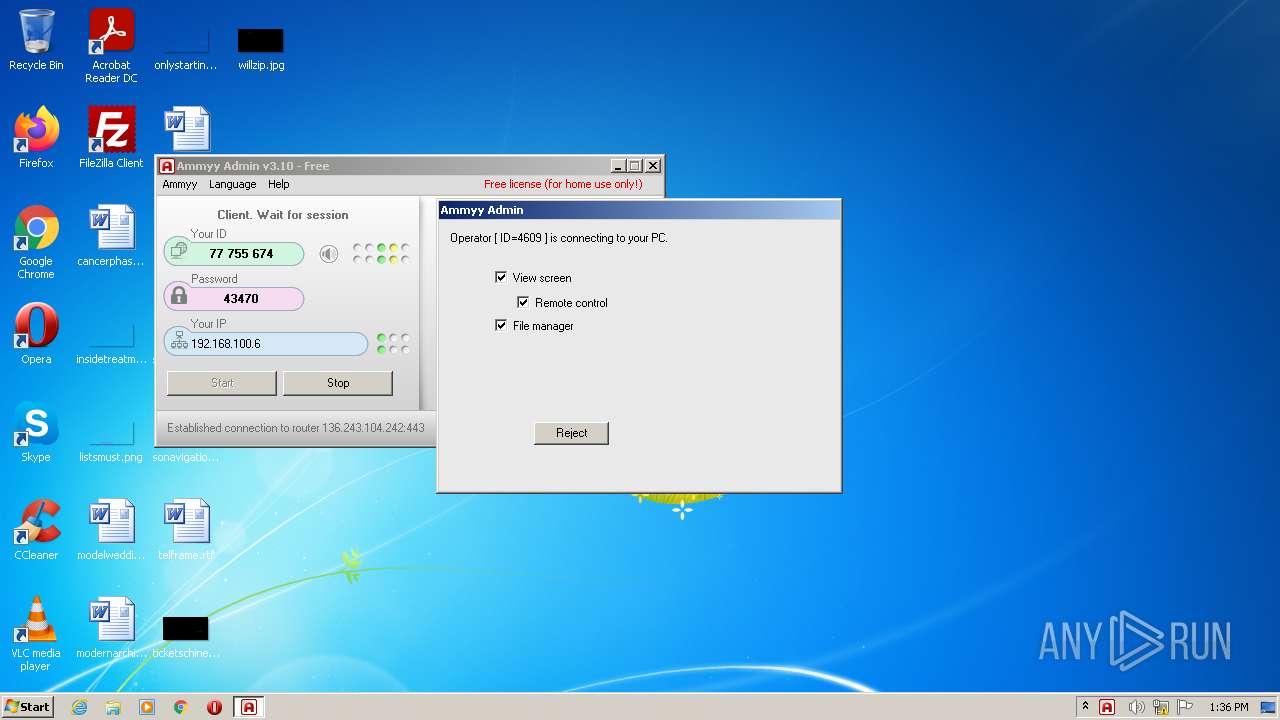
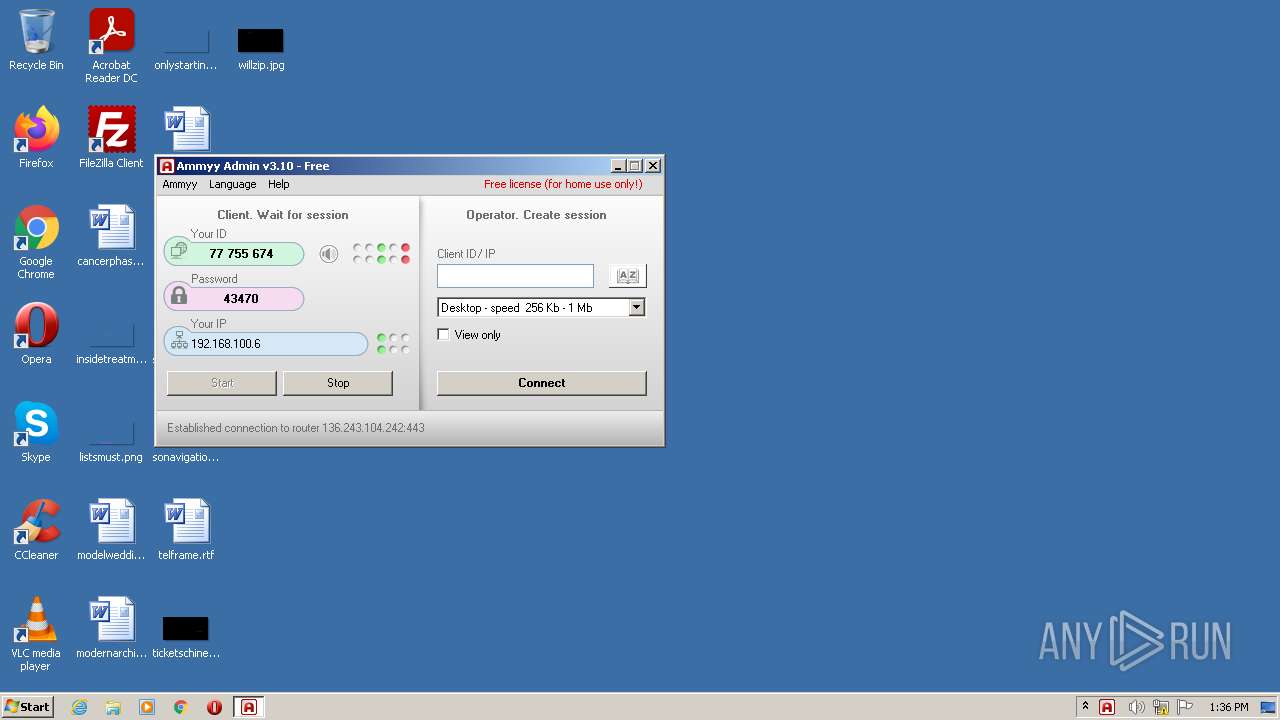
3120 | AA_v3.exe | 188.42.129.148:80 | rl.ammyy.com | Servers.com, Inc. | NL | malicious |
3120 | AA_v3.exe | 136.243.104.242:443 | — | Hetzner Online GmbH | DE | malicious |
2936 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
2936 | firefox.exe | 18.66.192.12:443 | firefox.settings.services.mozilla.com | Massachusetts Institute of Technology | US | suspicious |
2936 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2936 | firefox.exe | 18.66.192.98:443 | content-signature-2.cdn.mozilla.net | Massachusetts Institute of Technology | US | suspicious |
2936 | firefox.exe | 142.250.185.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2936 | firefox.exe | 34.223.166.69:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2936 | firefox.exe | 34.216.199.145:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rl.ammyy.com |
| suspicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3120 | AA_v3.exe | Potential Corporate Privacy Violation | ET POLICY IP Check (rl. ammyy. com) |
2936 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2936 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1 ETPRO signatures available at the full report