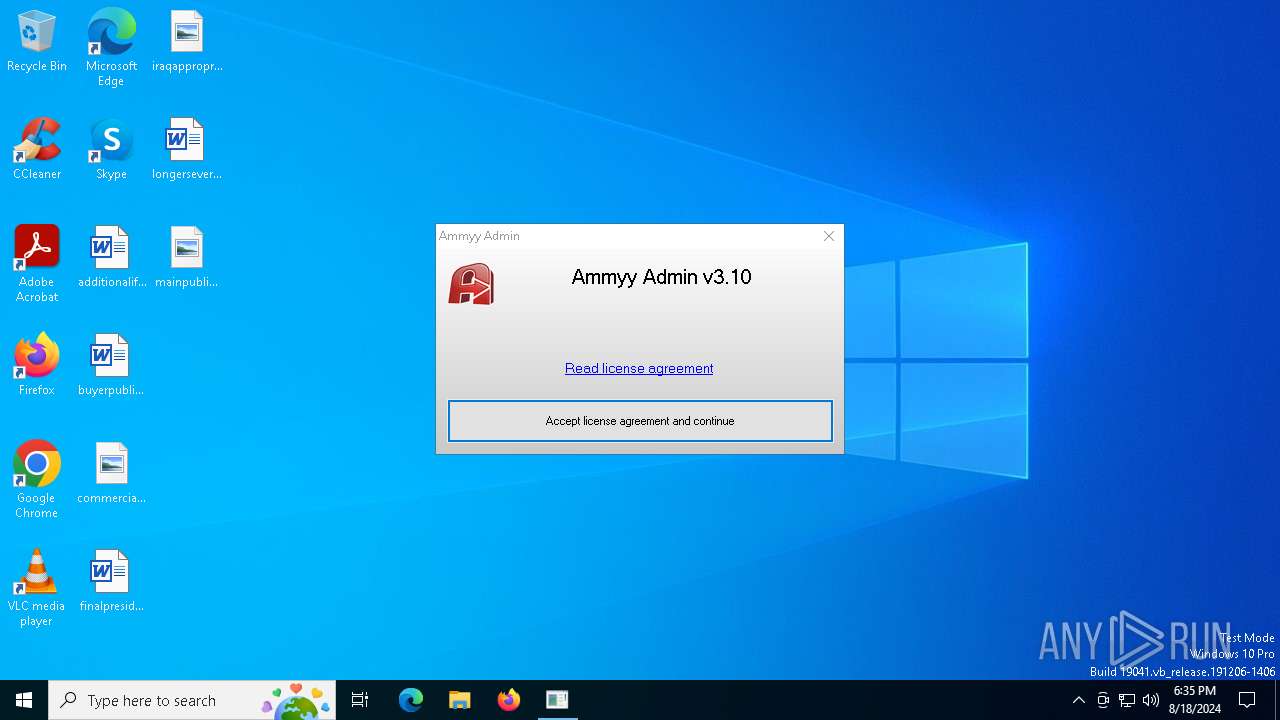
| File name: | ammyy-admin_3.10.exe |
| Full analysis: | https://app.any.run/tasks/a1bbc68f-dd17-4f54-90c2-5c85102a4b7c |
| Verdict: | Malicious activity |
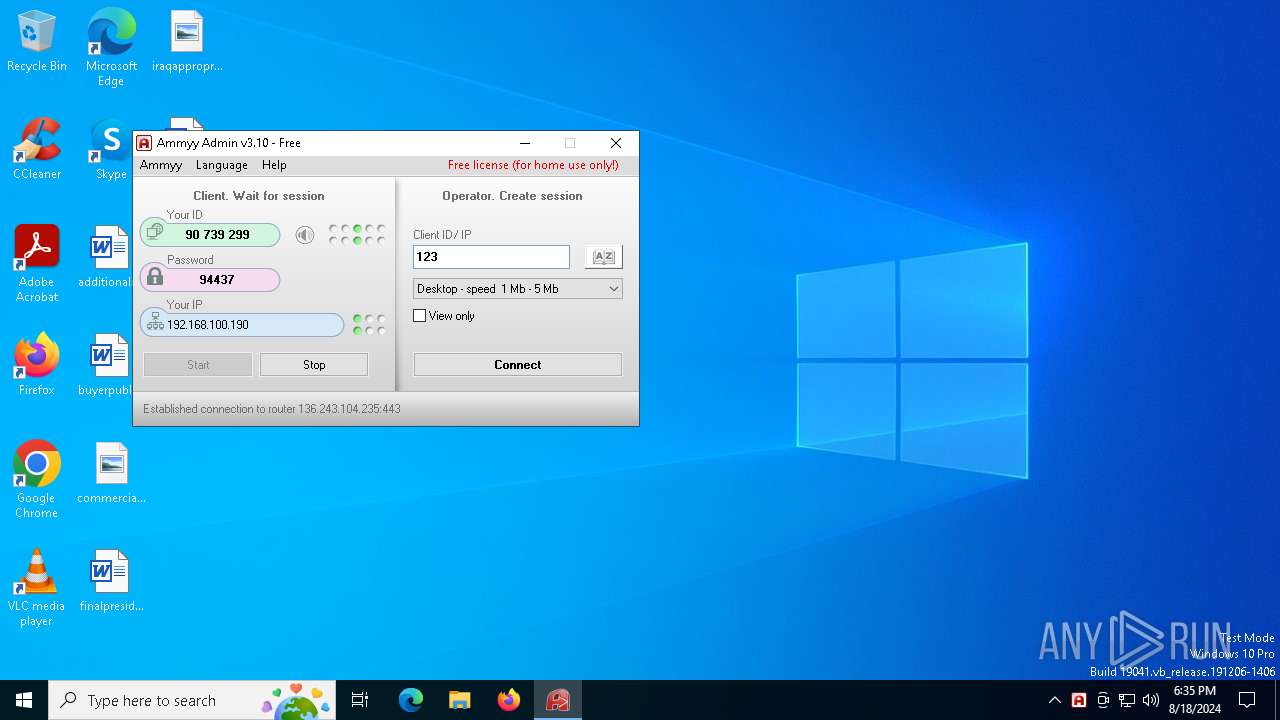
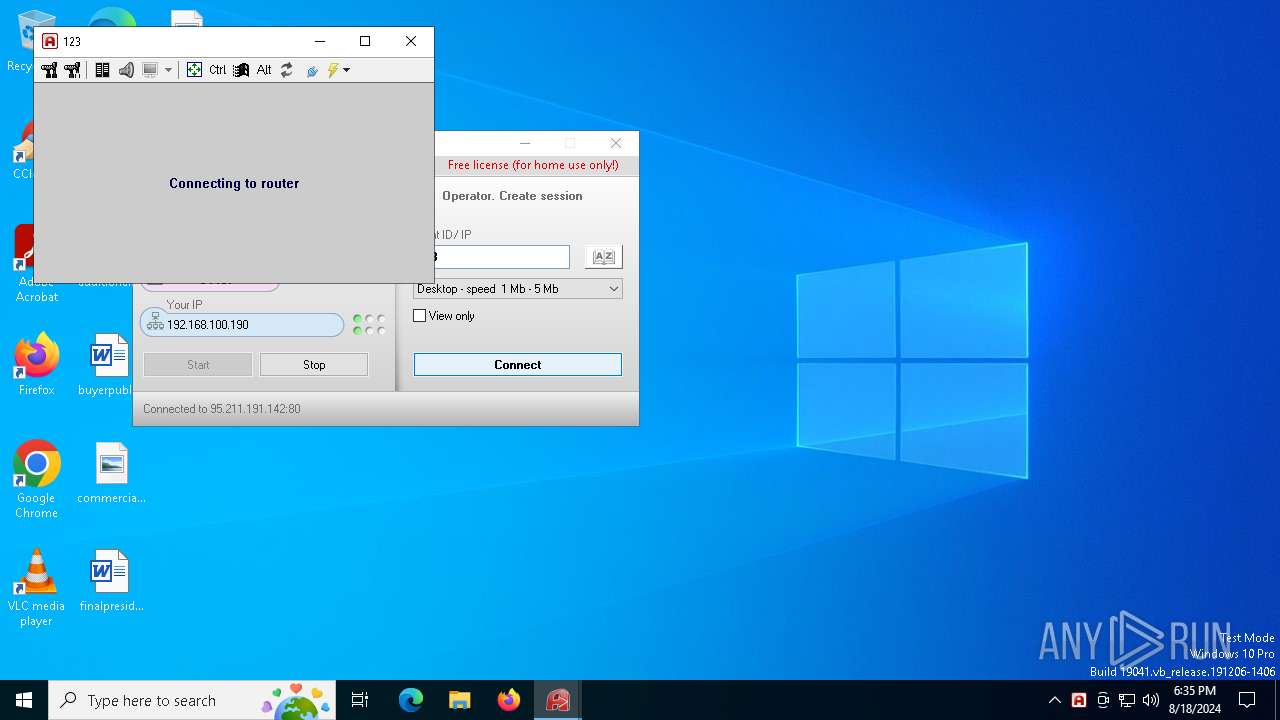
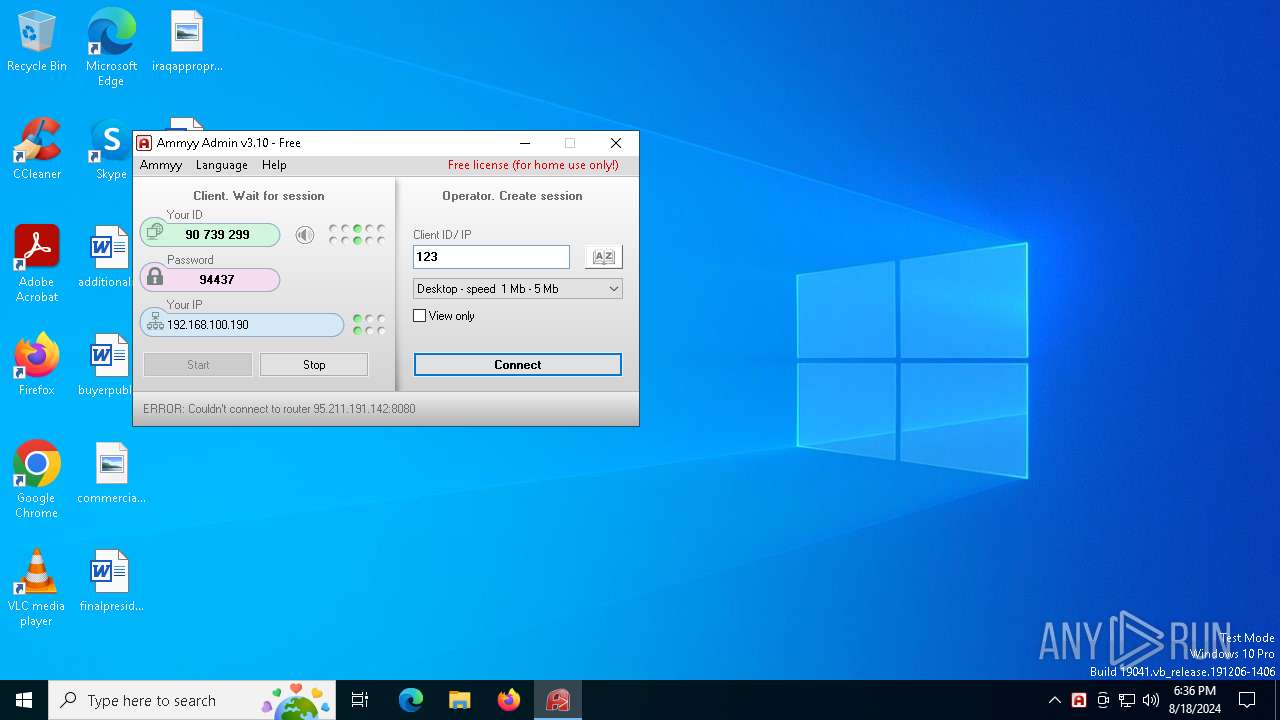
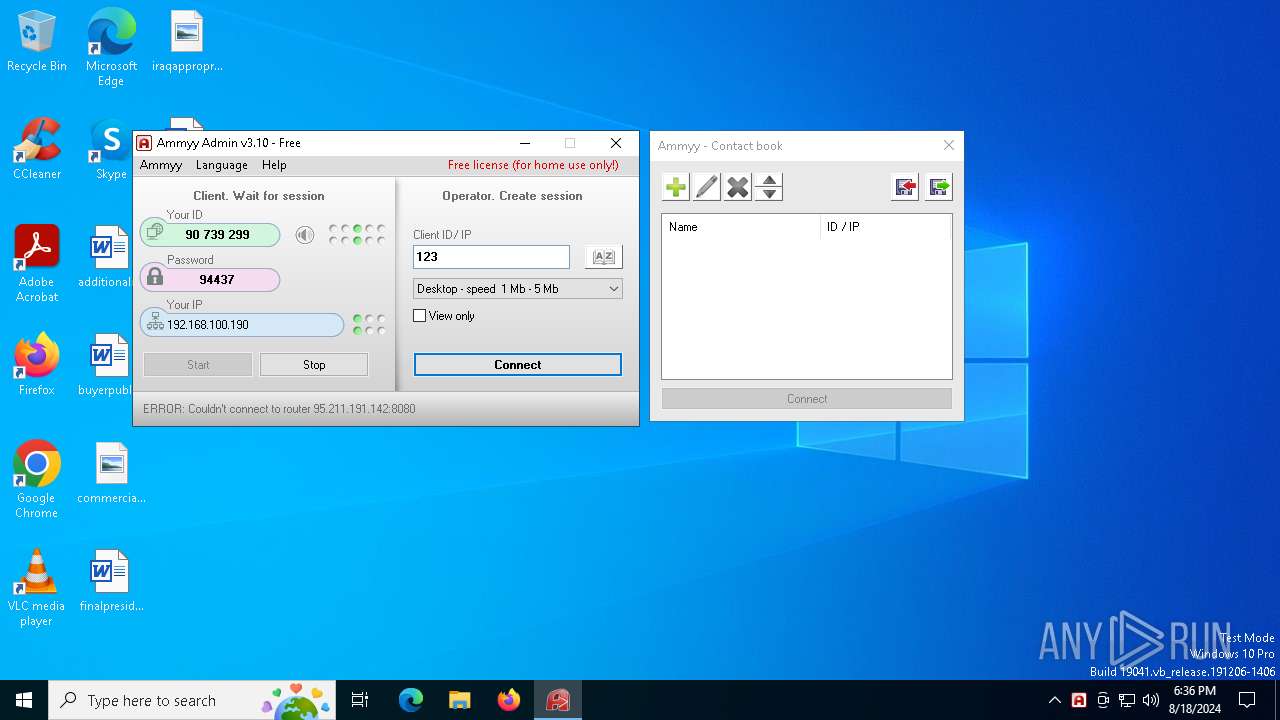
| Analysis date: | August 18, 2024, 18:35:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 90AADF2247149996AE443E2C82AF3730 |
| SHA1: | 050B7EBA825412B24E3F02D76D7DA5AE97E10502 |
| SHA256: | EE573647477339784DCEF81024DE1BE1762833A20E5CC2B89A93E47D05B86B6A |
| SSDEEP: | 24576:Uj0JJ4p/A4npt3XojeQG5EtzRtO7GvmDguXd:UjoJ4u4zojegylDN |
MALICIOUS
Deletes the SafeBoot registry key
- ammyy-admin_3.10.exe (PID: 6356)
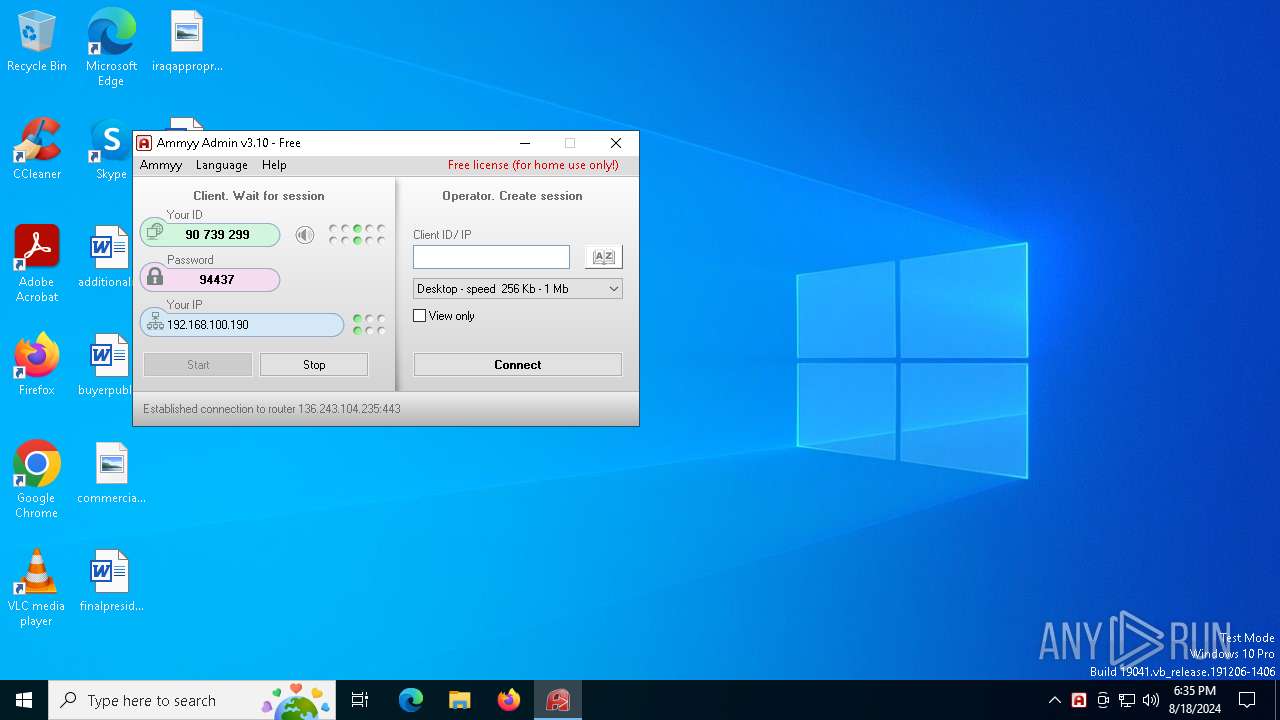
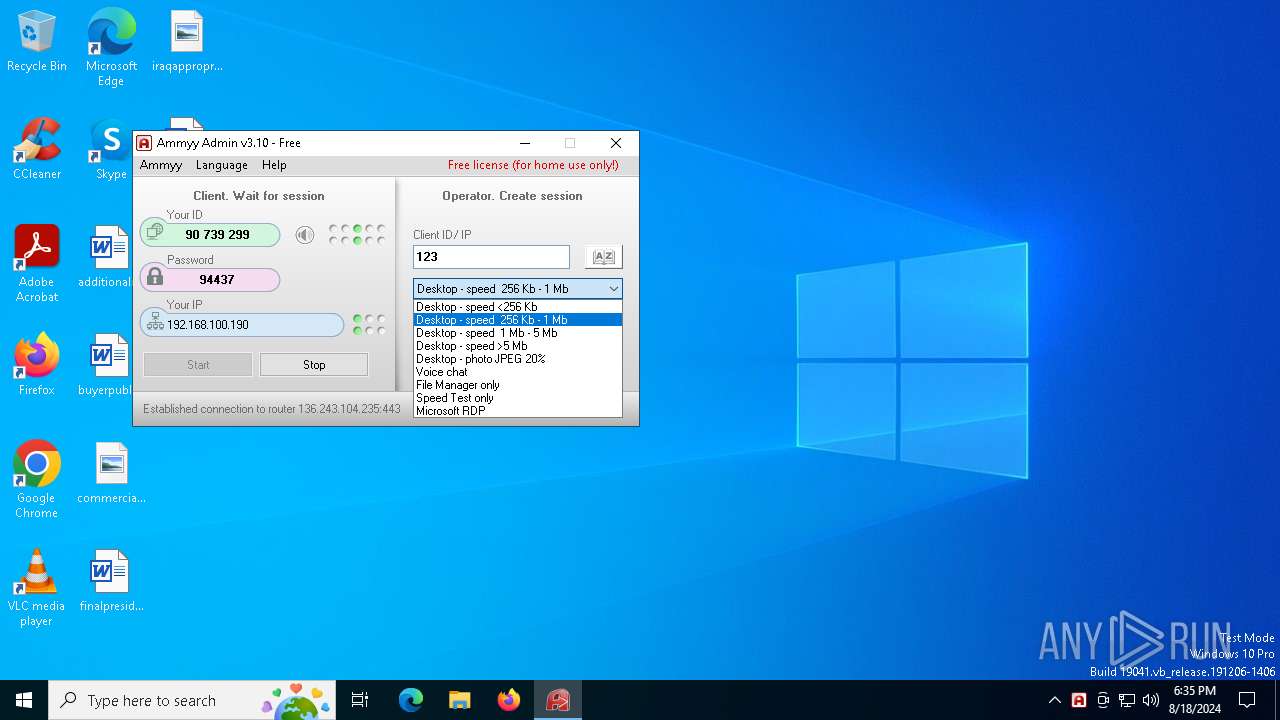
AMMYY has been detected (SURICATA)
- ammyy-admin_3.10.exe (PID: 6424)
SUSPICIOUS
Drops the executable file immediately after the start
- ammyy-admin_3.10.exe (PID: 6280)
- ammyy-admin_3.10.exe (PID: 6424)
Reads security settings of Internet Explorer
- ammyy-admin_3.10.exe (PID: 6280)
- ammyy-admin_3.10.exe (PID: 6424)
Reads the date of Windows installation
- ammyy-admin_3.10.exe (PID: 6280)
Application launched itself
- ammyy-admin_3.10.exe (PID: 6280)
- ammyy-admin_3.10.exe (PID: 6384)
Executes as Windows Service
- ammyy-admin_3.10.exe (PID: 6384)
Checks Windows Trust Settings
- ammyy-admin_3.10.exe (PID: 6424)
Potential Corporate Privacy Violation
- ammyy-admin_3.10.exe (PID: 6424)
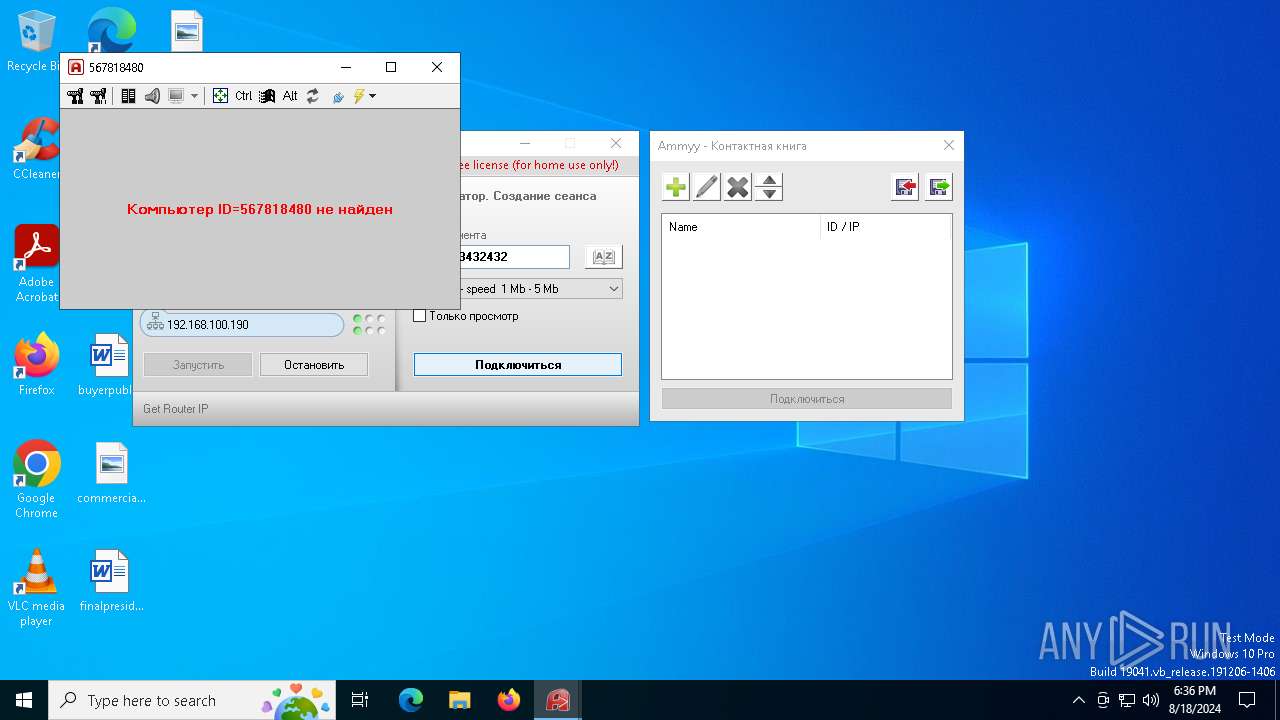
Checks for external IP
- ammyy-admin_3.10.exe (PID: 6424)
Executable content was dropped or overwritten
- ammyy-admin_3.10.exe (PID: 6424)
Uses RUNDLL32.EXE to load library
- ammyy-admin_3.10.exe (PID: 6424)
There is functionality for enable RDP (YARA)
- ammyy-admin_3.10.exe (PID: 6424)
There is functionality for taking screenshot (YARA)
- ammyy-admin_3.10.exe (PID: 6424)
INFO
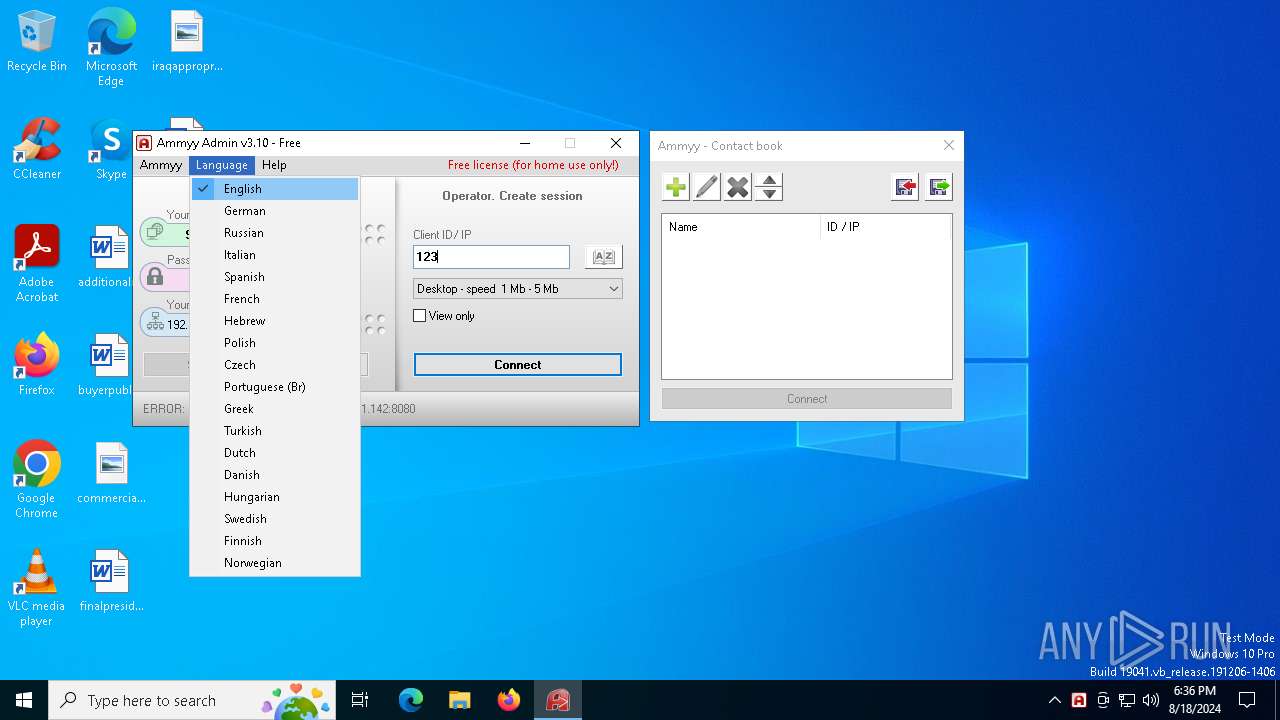
Checks supported languages
- ammyy-admin_3.10.exe (PID: 6280)
- ammyy-admin_3.10.exe (PID: 6356)
- ammyy-admin_3.10.exe (PID: 6384)
- ammyy-admin_3.10.exe (PID: 6424)
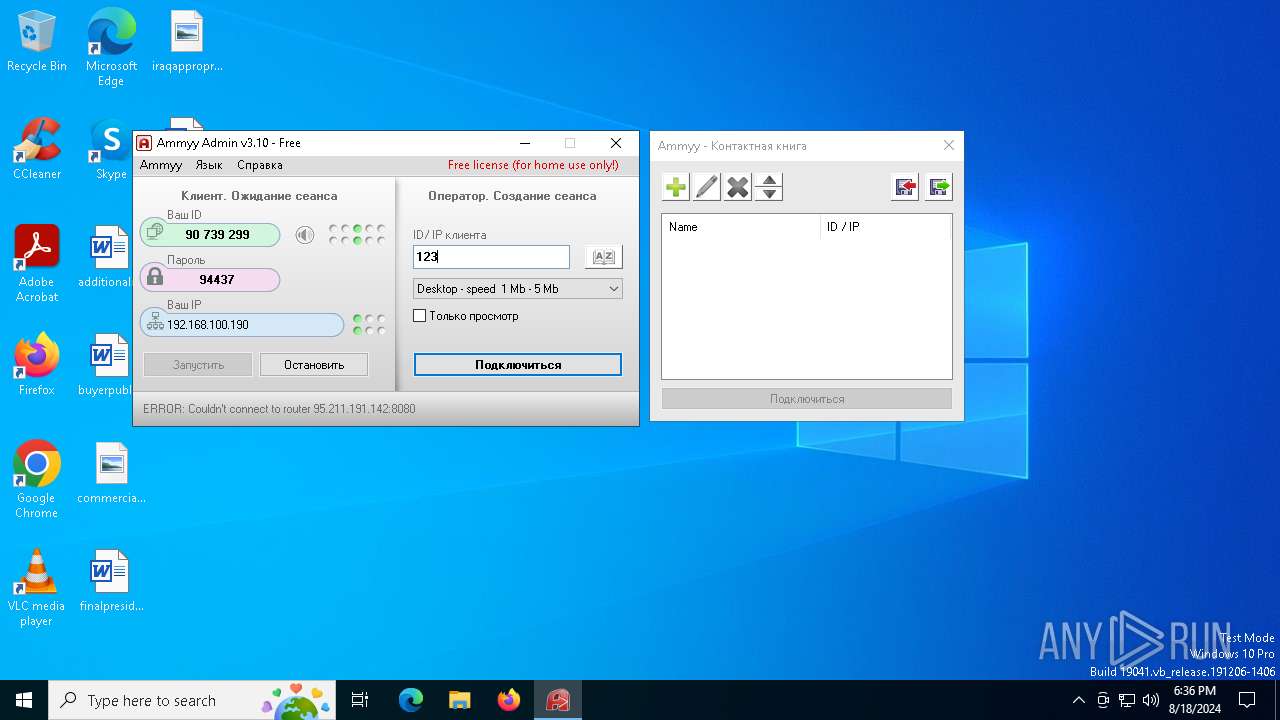
Process checks computer location settings
- ammyy-admin_3.10.exe (PID: 6280)
- ammyy-admin_3.10.exe (PID: 6424)
Creates files in the program directory
- ammyy-admin_3.10.exe (PID: 6280)
- ammyy-admin_3.10.exe (PID: 6424)
Reads the computer name
- ammyy-admin_3.10.exe (PID: 6280)
- ammyy-admin_3.10.exe (PID: 6356)
- ammyy-admin_3.10.exe (PID: 6384)
- ammyy-admin_3.10.exe (PID: 6424)
Checks proxy server information
- ammyy-admin_3.10.exe (PID: 6280)
Create files in a temporary directory
- ammyy-admin_3.10.exe (PID: 6424)
Reads the machine GUID from the registry
- ammyy-admin_3.10.exe (PID: 6424)
Reads the software policy settings
- ammyy-admin_3.10.exe (PID: 6424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:09:15 16:09:42+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 581632 |
| InitializedDataSize: | 258048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x86db8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.10.0.0 |
| ProductVersionNumber: | 3.10.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Ammyy LLC |
| FileDescription: | Ammyy Admin |
| FileVersion: | 3.1 |
| InternalName: | Ammyy Admin |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| PrivateBuild: | - |
| ProductName: | Ammyy Admin |
| ProductVersion: | 3.1 |
| SpecialBuild: | - |
Total processes
134
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6280 | "C:\Users\admin\AppData\Local\Temp\ammyy-admin_3.10.exe" | C:\Users\admin\AppData\Local\Temp\ammyy-admin_3.10.exe | — | explorer.exe | |||||||||||
User: admin Company: Ammyy LLC Integrity Level: MEDIUM Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 6356 | "C:\Users\admin\AppData\Local\Temp\ammyy-admin_3.10.exe" -elevated | C:\Users\admin\AppData\Local\Temp\ammyy-admin_3.10.exe | ammyy-admin_3.10.exe | ||||||||||||
User: admin Company: Ammyy LLC Integrity Level: HIGH Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 6384 | "C:\Users\admin\AppData\Local\Temp\ammyy-admin_3.10.exe" -service -lunch | C:\Users\admin\AppData\Local\Temp\ammyy-admin_3.10.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 6424 | "C:\Users\admin\AppData\Local\Temp\ammyy-admin_3.10.exe" -elevated | C:\Users\admin\AppData\Local\Temp\ammyy-admin_3.10.exe | ammyy-admin_3.10.exe | ||||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Version: 3.10 Modules
| |||||||||||||||
| 6764 | rundll32.exe "C:\ProgramData\AMMYY\aa_nts.dll",run | C:\Windows\System32\rundll32.exe | — | ammyy-admin_3.10.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 248
Read events
5 226
Write events
21
Delete events
1
Modification events
| (PID) Process: | (6280) ammyy-admin_3.10.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6280) ammyy-admin_3.10.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6280) ammyy-admin_3.10.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6280) ammyy-admin_3.10.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6356) ammyy-admin_3.10.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\AmmyyAdmin_18D4 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6424) ammyy-admin_3.10.exe | Key: | HKEY_USERS\.DEFAULT\Software\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: 24E2A63EAB54D3AA7BA1DFD303280478D9475F22137E41C9435BE90D83EB19A2945E30CE8229DCD53605135EE25CA52ADE4B778E054976400B1D167EFBBB1564D7C13A | |||
| (PID) Process: | (6424) ammyy-admin_3.10.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: 24E2A63EAB54D3AA7BA1DFD303280478D9475F22137E41C9435BE90D83EB19A2945E30CE8229DCD53605135EE25CA52ADE4B778E054976400B1D167EFBBB1564D7C13A | |||
| (PID) Process: | (6424) ammyy-admin_3.10.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6424) ammyy-admin_3.10.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6424) ammyy-admin_3.10.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
1
Suspicious files
7
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6424 | ammyy-admin_3.10.exe | C:\Windows\SysWOW64\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 6280 | ammyy-admin_3.10.exe | C:\ProgramData\AMMYY\settings3.bin | binary | |
MD5:B8946EDDA960DAD0F7438CD387BF1CF3 | SHA256:48149E6BED76634A06EA70DDC2CD48EA187CF4D6C98802FC31EE6291A82405B3 | |||
| 6424 | ammyy-admin_3.10.exe | C:\ProgramData\AMMYY\hr3 | binary | |
MD5:007D19EB319DF7C6819DA189BBA0CB04 | SHA256:DF992FDCF97C9E27A069CC91372216ED98731A9F8F08D009F0064AF94290C883 | |||
| 6424 | ammyy-admin_3.10.exe | C:\ProgramData\AMMYY\aa_nts.dll | executable | |
MD5:480A66902E6E7CDAFAA6711E8697FF8C | SHA256:7EAAAA6010BBCD6BB8C9AD08D4B0966C7AEDC9B2AC24758F170012AC36E508B5 | |||
| 6424 | ammyy-admin_3.10.exe | C:\Users\admin\AppData\Local\Temp\ammyy-admin_3.10.log | text | |
MD5:547C8580F4CAD1A21DFE558F543B7281 | SHA256:EB4EAA317A0A3FF0E1AFA8732A14378952F2EC03BB2E069E61E979655987B79A | |||
| 6424 | ammyy-admin_3.10.exe | C:\Windows\SysWOW64\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A82946818BB0433A7DC1AFD2189B16AF | binary | |
MD5:7E38EA74A6DCACF0B715E3BC1464B4A4 | SHA256:4F60D0B0E1067EE5E8136DFA59C597A17C79F249C96629B331DBF5131FCBED9D | |||
| 6424 | ammyy-admin_3.10.exe | C:\Windows\SysWOW64\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A82946818BB0433A7DC1AFD2189B16AF | binary | |
MD5:9834F233AD54F0D9A57474A5C83C92EB | SHA256:A59D78B204E01CEA14D60A3C0EBF4883FAD440BC837FCD5DA3A47D96E86F3CCD | |||
| 6424 | ammyy-admin_3.10.exe | C:\ProgramData\AMMYY\aa_nts.msg | binary | |
MD5:2F0D446171630FBD6B6CC8D87EC6161E | SHA256:2635277B0926D9828A3FDAB2ABA6AEE78A615B78D6115EAF05EFC01A06B752D1 | |||
| 6424 | ammyy-admin_3.10.exe | C:\Windows\SysWOW64\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:76CE31BCF3F143647E90EEE89BC1DD60 | SHA256:12E3C5536CFA42EB3442D431C81CCB420D0A6AAA77B462DBD0994D997852420B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
43
DNS requests
18
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6424 | ammyy-admin_3.10.exe | GET | 301 | 136.243.18.118:80 | http://www.ammyy.com/files/v8/aans64y2.gz | unknown | — | — | malicious |
6424 | ammyy-admin_3.10.exe | GET | 200 | 184.24.77.67:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgQEpUwbvwwxg5SLPn%2FfE87O2A%3D%3D | unknown | — | — | whitelisted |
6424 | ammyy-admin_3.10.exe | POST | 200 | 188.42.129.148:80 | http://rl.ammyy.com/ | unknown | — | — | unknown |
6424 | ammyy-admin_3.10.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
2212 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6860 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6424 | ammyy-admin_3.10.exe | POST | 200 | 188.42.129.148:80 | http://rl.ammyy.com/ | unknown | — | — | unknown |
3268 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6424 | ammyy-admin_3.10.exe | POST | 200 | 188.42.129.148:80 | http://rl.ammyy.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4576 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4664 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6424 | ammyy-admin_3.10.exe | 188.42.129.148:80 | rl.ammyy.com | SERVERS-COM | LU | unknown |
6424 | ammyy-admin_3.10.exe | 136.243.104.235:443 | — | Hetzner Online GmbH | DE | unknown |
4576 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6424 | ammyy-admin_3.10.exe | 136.243.18.118:80 | www.ammyy.com | Hetzner Online GmbH | DE | unknown |
6424 | ammyy-admin_3.10.exe | 136.243.18.118:443 | www.ammyy.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
rl.ammyy.com |
| malicious |
www.ammyy.com |
| malicious |
x1.c.lencr.org |
| whitelisted |
r11.o.lencr.org |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6424 | ammyy-admin_3.10.exe | Potential Corporate Privacy Violation | ET POLICY IP Check (rl. ammyy. com) |
6424 | ammyy-admin_3.10.exe | Potential Corporate Privacy Violation | ET POLICY IP Check (rl. ammyy. com) |
6424 | ammyy-admin_3.10.exe | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
6424 | ammyy-admin_3.10.exe | Generic Protocol Command Decode | SURICATA HTTP Request line incomplete |
6424 | ammyy-admin_3.10.exe | Potential Corporate Privacy Violation | ET POLICY IP Check (rl. ammyy. com) |
3 ETPRO signatures available at the full report