| File name: | Remote Desktop Software Ammyy Admin_AA_v3.9.exe |
| Full analysis: | https://app.any.run/tasks/122e8abd-5aa8-4de5-8c15-7b50fd75a306 |
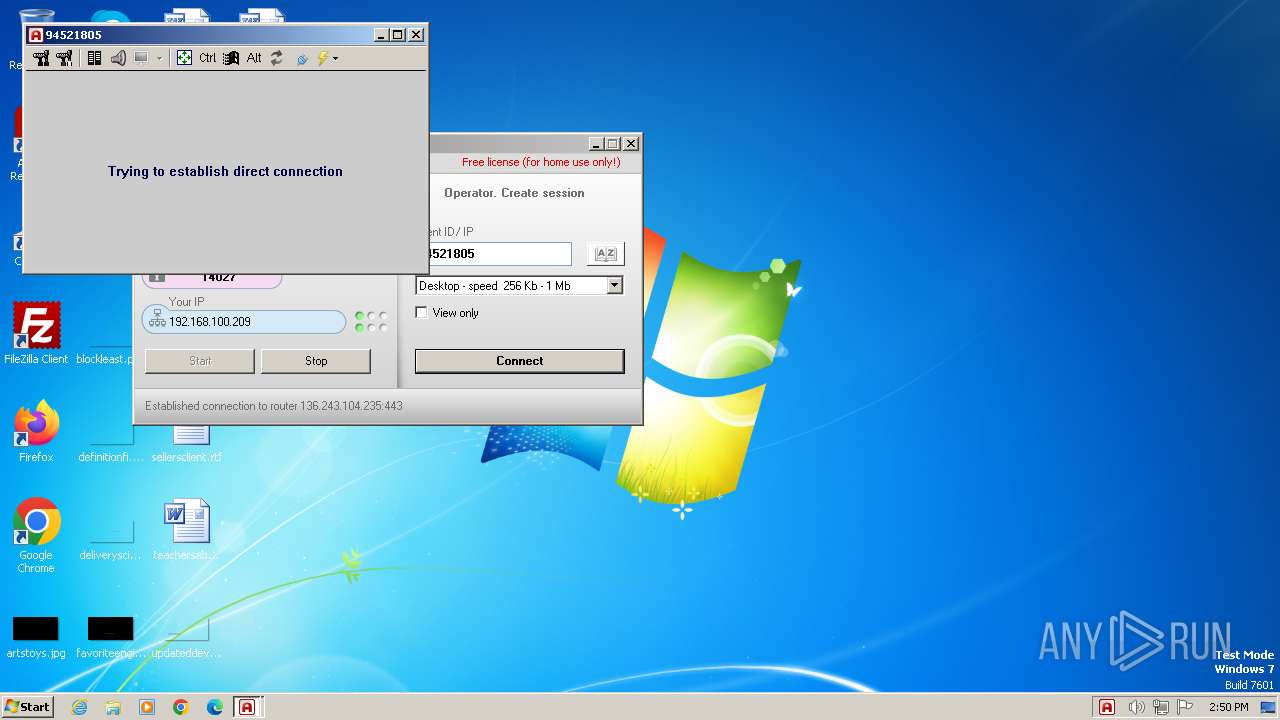
| Verdict: | Malicious activity |
| Analysis date: | March 28, 2024, 14:49:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 90AADF2247149996AE443E2C82AF3730 |
| SHA1: | 050B7EBA825412B24E3F02D76D7DA5AE97E10502 |
| SHA256: | EE573647477339784DCEF81024DE1BE1762833A20E5CC2B89A93E47D05B86B6A |
| SSDEEP: | 24576:Uj0JJ4p/A4npt3XojeQG5EtzRtO7GvmDguXd:UjoJ4u4zojegylDN |
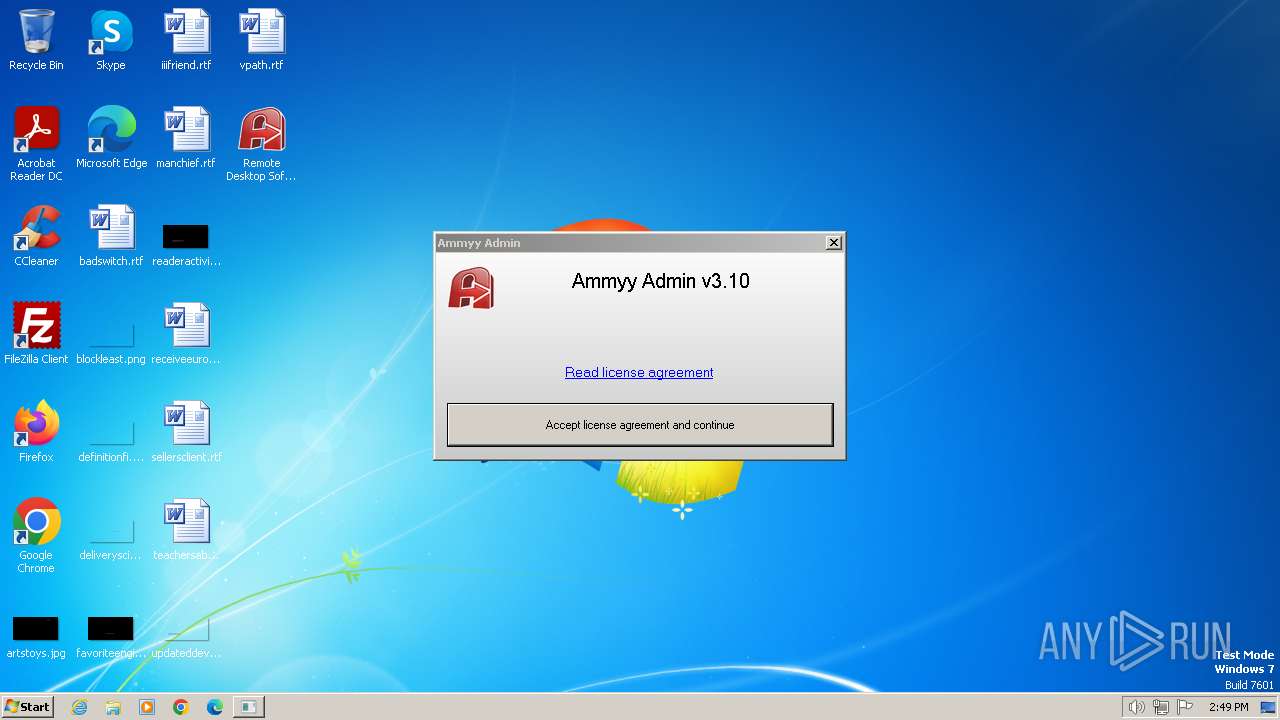
MALICIOUS
Drops the executable file immediately after the start
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1696)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Deletes the SafeBoot registry key
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1348)
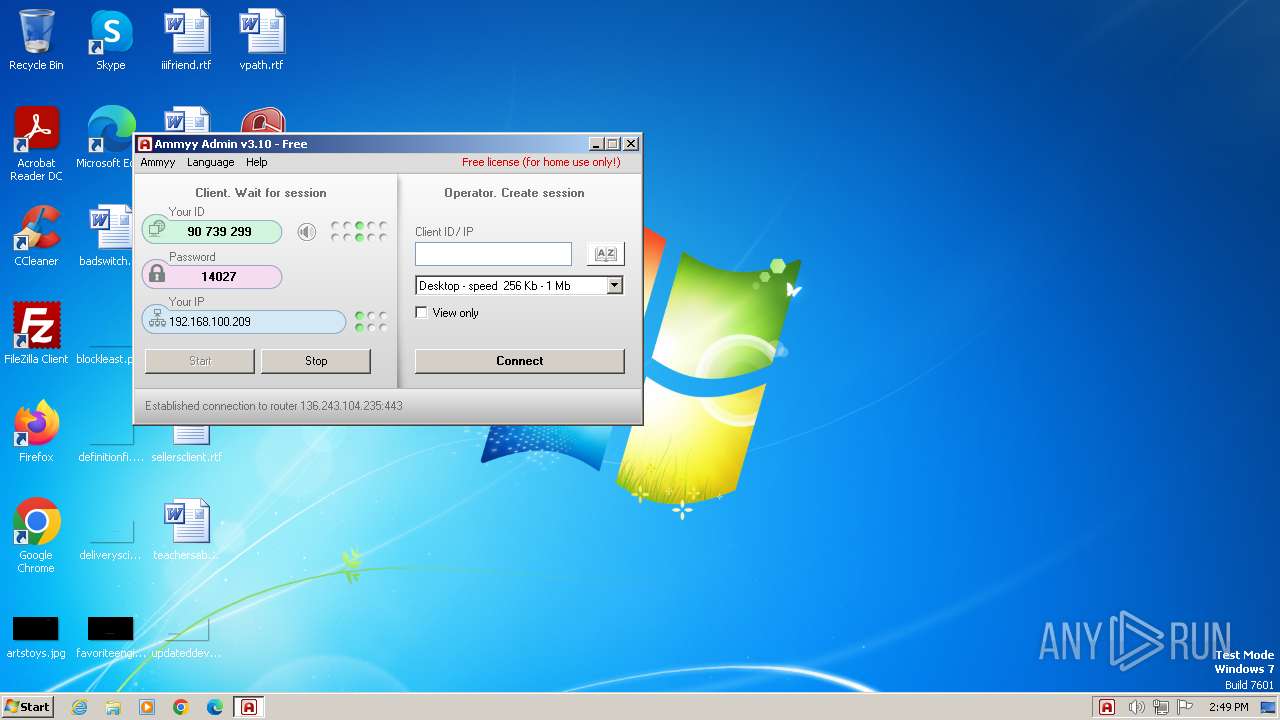
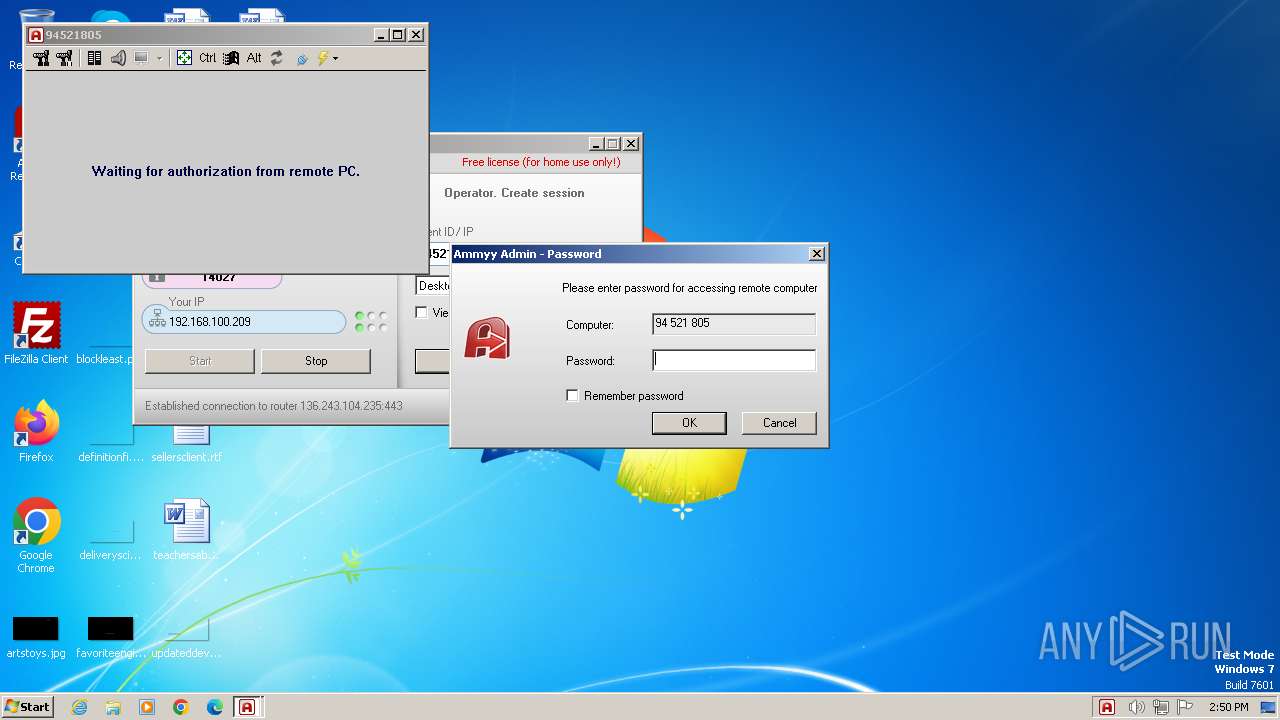
AMMYY has been detected (SURICATA)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Creates a writable file in the system directory
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
SUSPICIOUS
Executes as Windows Service
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 2064)
Reads security settings of Internet Explorer
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1696)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Application launched itself
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1696)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 2064)
Reads the Internet Settings
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1696)
Checks for external IP
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Uses RUNDLL32.EXE to load library
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Adds/modifies Windows certificates
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Checks Windows Trust Settings
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
INFO
Checks proxy server information
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1696)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Checks supported languages
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1696)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1348)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 2064)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
- wmpnscfg.exe (PID: 2728)
Reads the computer name
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1696)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1348)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 2064)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
- wmpnscfg.exe (PID: 2728)
Creates files in the program directory
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 1696)
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Process checks computer location settings
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Reads the software policy settings
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Manual execution by a user
- wmpnscfg.exe (PID: 2728)
Reads the machine GUID from the registry
- Remote Desktop Software Ammyy Admin_AA_v3.9.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:09:15 16:09:42+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 581632 |
| InitializedDataSize: | 258048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x86db8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.10.0.0 |
| ProductVersionNumber: | 3.10.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Ammyy LLC |
| FileDescription: | Ammyy Admin |
| FileVersion: | 3.1 |
| InternalName: | Ammyy Admin |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| PrivateBuild: | - |
| ProductName: | Ammyy Admin |
| ProductVersion: | 3.1 |
| SpecialBuild: | - |
Total processes
46
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | "C:\Users\admin\Desktop\Remote Desktop Software Ammyy Admin_AA_v3.9.exe" -elevated | C:\Users\admin\Desktop\Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | ||||||||||||
User: admin Company: Ammyy LLC Integrity Level: HIGH Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\Desktop\Remote Desktop Software Ammyy Admin_AA_v3.9.exe" | C:\Users\admin\Desktop\Remote Desktop Software Ammyy Admin_AA_v3.9.exe | — | explorer.exe | |||||||||||
User: admin Company: Ammyy LLC Integrity Level: MEDIUM Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\Desktop\Remote Desktop Software Ammyy Admin_AA_v3.9.exe" -service -lunch | C:\Users\admin\Desktop\Remote Desktop Software Ammyy Admin_AA_v3.9.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Exit code: 0 Version: 3.10 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\Desktop\Remote Desktop Software Ammyy Admin_AA_v3.9.exe" -elevated | C:\Users\admin\Desktop\Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | ||||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Version: 3.10 Modules
| |||||||||||||||
| 3400 | rundll32.exe "C:\ProgramData\AMMYY\aa_nts.dll",run | C:\Windows\System32\rundll32.exe | — | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 511
Read events
7 439
Write events
48
Delete events
24
Modification events
| (PID) Process: | (1696) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1696) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1696) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1696) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1348) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\AmmyyAdmin_544 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3164) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3164) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3164) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3164) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3164) Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
Executable files
1
Suspicious files
5
Text files
1
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1696 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\ProgramData\AMMYY\settings3.bin | binary | |
MD5:— | SHA256:— | |||
| 3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\ProgramData\AMMYY\hr3 | binary | |
MD5:— | SHA256:— | |||
| 3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\Windows\TEMP\Cab435D.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\Windows\TEMP\Tar435E.tmp | binary | |
MD5:— | SHA256:— | |||
| 3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5048D75D0A7E580D041342EF64D47462 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
13
DNS requests
5
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | GET | 301 | 136.243.18.118:80 | http://www.ammyy.com/files/v7/aans32.gz | unknown | — | — | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | GET | 200 | 184.86.251.80:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPT80r3KFhxVZ5Jh2UmuA755w%3D%3D | unknown | — | — | unknown |
— | — | POST | 200 | 188.42.129.148:80 | http://rl.ammyy.com/ | unknown | — | — | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | POST | — | 188.42.129.148:80 | http://rl.ammyy.com/ | unknown | — | — | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | POST | 200 | 188.42.129.148:80 | http://rl.ammyy.com/ | unknown | — | — | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | GET | 304 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?17877333ae6fa208 | unknown | — | — | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | GET | 200 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?6cba3083cea0e54e | unknown | — | — | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | GET | 200 | 23.192.153.142:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | 188.42.129.148:80 | rl.ammyy.com | SERVERS-COM | LU | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | 136.243.104.235:443 | — | Hetzner Online GmbH | DE | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | 136.243.18.118:80 | www.ammyy.com | Hetzner Online GmbH | DE | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | 136.243.18.118:443 | www.ammyy.com | Hetzner Online GmbH | DE | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | 2.19.126.163:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | 23.192.153.142:80 | x1.c.lencr.org | AKAMAI-AS | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rl.ammyy.com |
| unknown |
www.ammyy.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Potential Corporate Privacy Violation | ET POLICY IP Check (rl. ammyy. com) |
3164 | Remote Desktop Software Ammyy Admin_AA_v3.9.exe | Potential Corporate Privacy Violation | ET POLICY IP Check (rl. ammyy. com) |
2 ETPRO signatures available at the full report