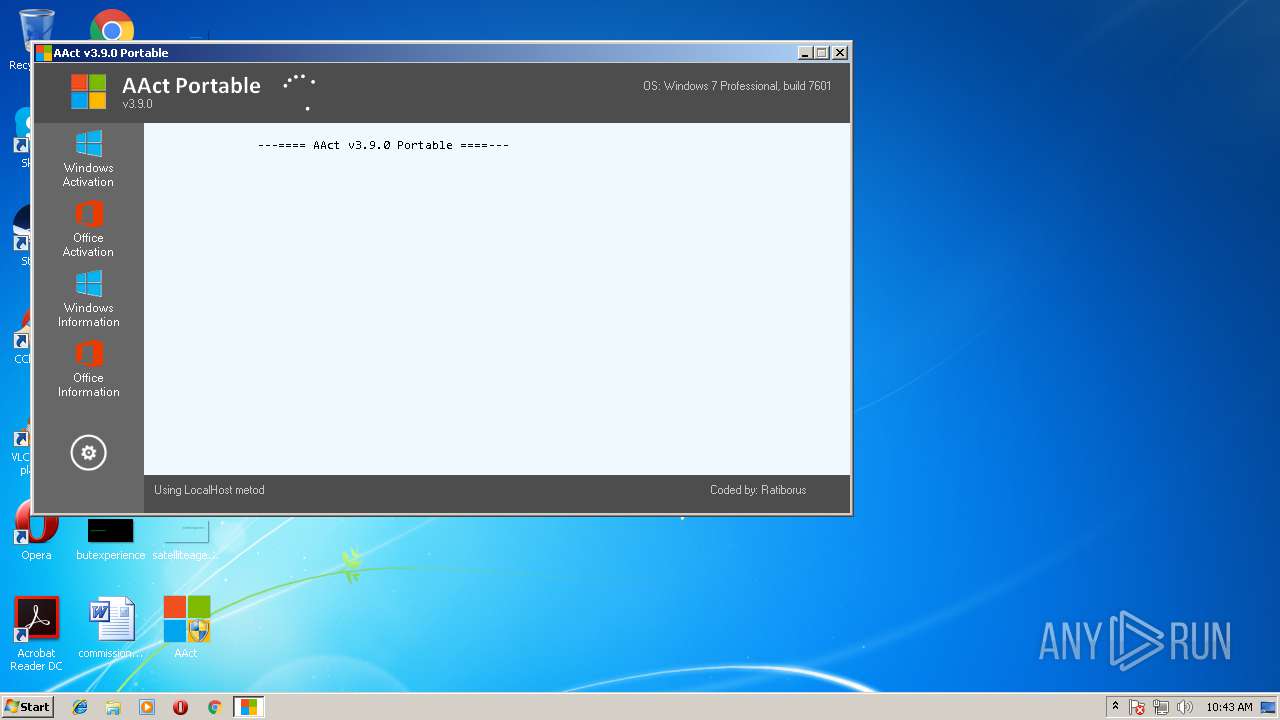
| File name: | AAct.exe |
| Full analysis: | https://app.any.run/tasks/3c30a20c-7bf4-4580-9d5e-3b0a2be9d075 |
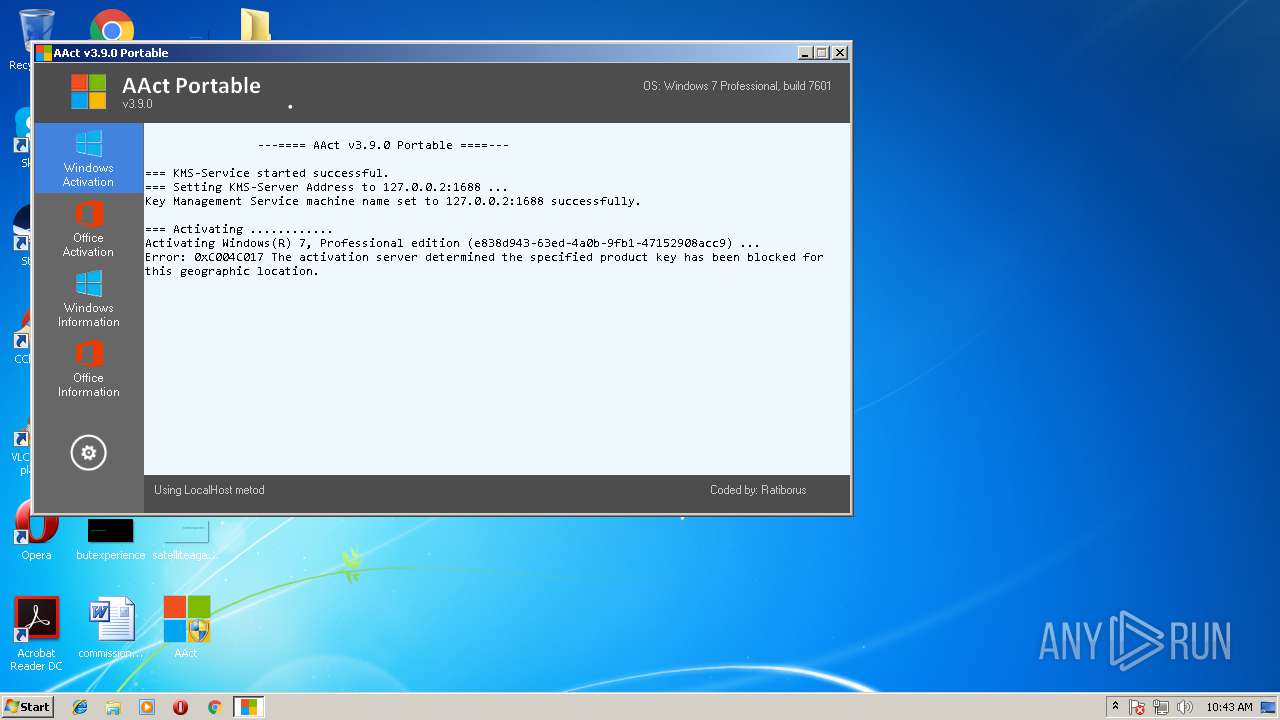
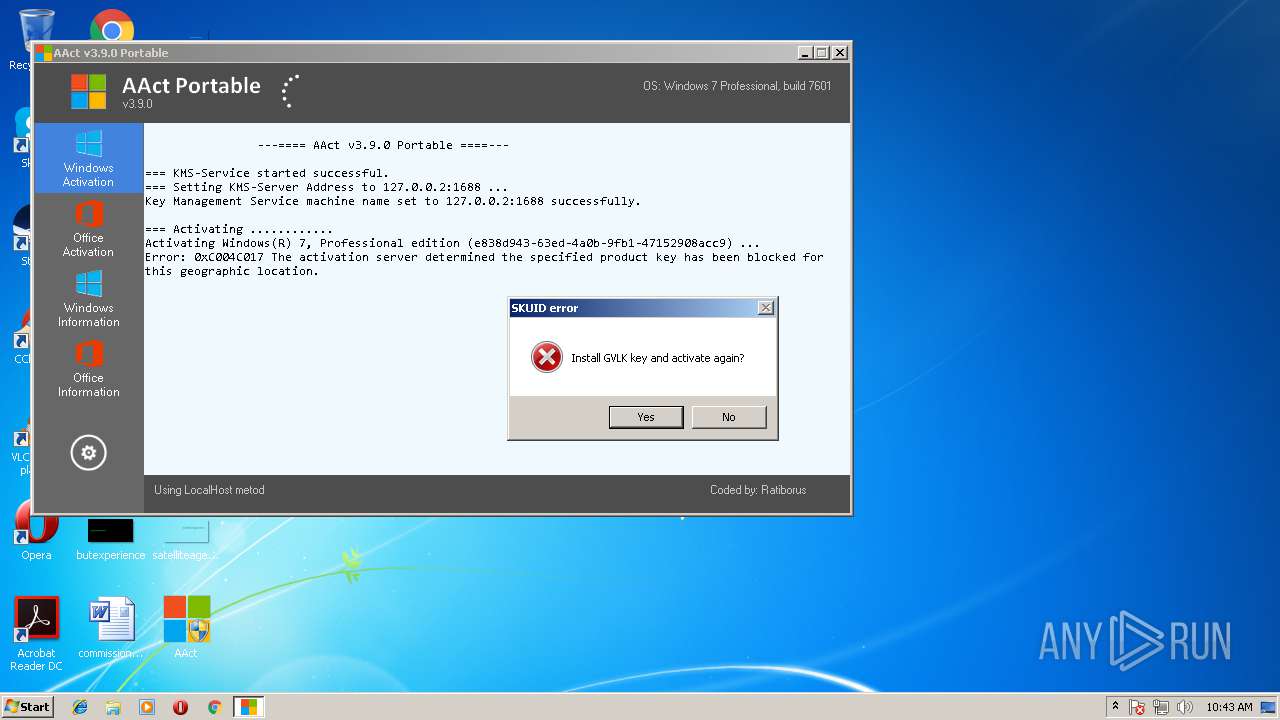
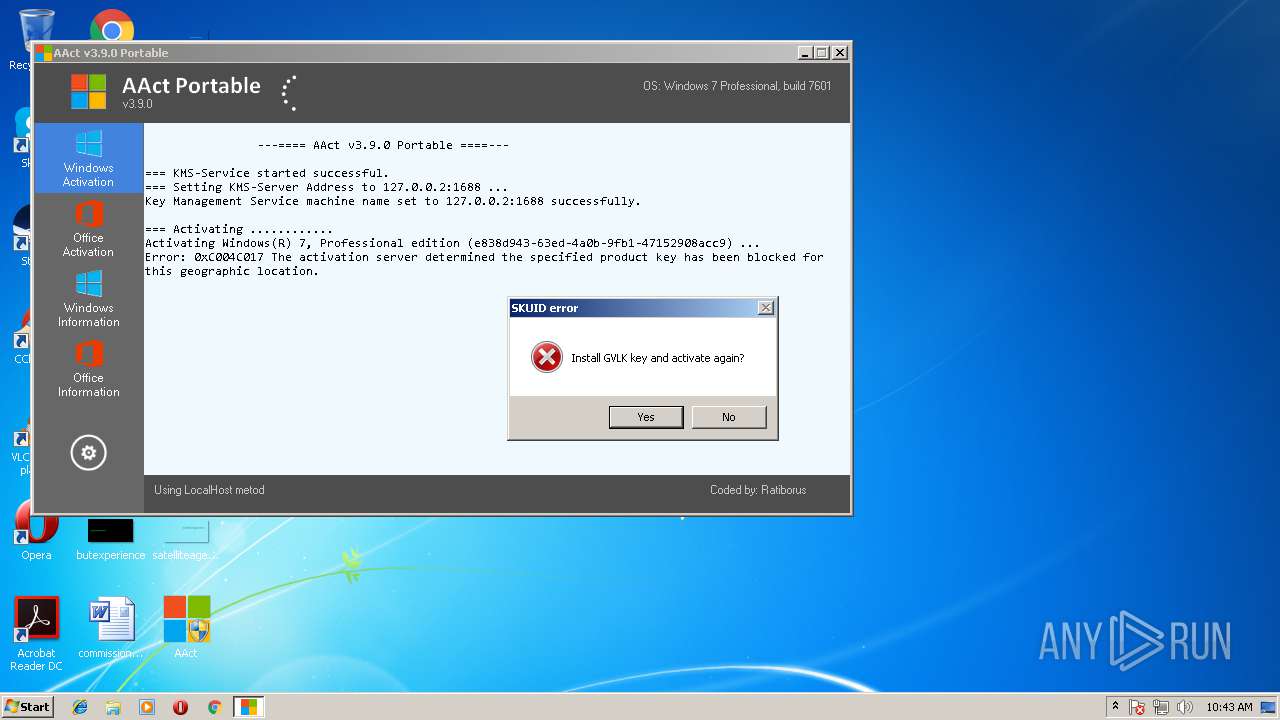
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2018, 09:42:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 23465FCDEC49D71AFB6AF505DCFBC09F |
| SHA1: | FA7F58BF05FADAC32E77DB031C354FA7608D9709 |
| SHA256: | EE3A632FF9BF3324AE854DAEB820F65D5AF939EA29B55F2E61BFB1D01B270A65 |
| SSDEEP: | 24576:M0IcWG3AQZ5DJotVEVCUNYR1KIJ/CFcYRATPQg75RJFJyAUi3qV3giuhVME9D+B9:MQVfD8UCgo1lJ/CFcoAUg75RJFMTi3qj |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1696)
- AAct.exe (PID: 1124)
- svchost.exe (PID: 880)
- conhost.exe (PID: 3648)
Application was dropped or rewritten from another process
- AAct.dll (PID: 1208)
SUSPICIOUS
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 580)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 2260)
Starts CMD.EXE for commands execution
- AAct.exe (PID: 1124)
Executable content was dropped or overwritten
- AAct.exe (PID: 1124)
Starts application with an unusual extension
- AAct.exe (PID: 1124)
Executes scripts
- cmd.exe (PID: 2532)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 3716)
- cmd.exe (PID: 2292)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 1660)
Uses REG.EXE to modify Windows registry
- AAct.exe (PID: 1124)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3832)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:07:14 11:58:47+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 1400832 |
| InitializedDataSize: | 73728 |
| UninitializedDataSize: | 1277952 |
| EntryPoint: | 0x28e040 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.9.0.0 |
| ProductVersionNumber: | 3.9.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | AAct x86 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jul-2018 09:58:47 |
| Detected languages: |
|
| FileDescription: | AAct x86 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 14-Jul-2018 09:58:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00138000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00139000 | 0x00156000 | 0x00155200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.87104 |
.rsrc | 0x0028F000 | 0x00012000 | 0x00011400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.50252 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8674 | 874 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
78
Monitored processes
30
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /ato | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 3221536791 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 344 | "C:\Windows\System32\reg.exe" DELETE "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f" /f | C:\Windows\System32\reg.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 580 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall add rule name=0pen_Port_KMS dir=in action=allow protocol=TCP localport=1688 | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 880 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1124 | "C:\Users\admin\Desktop\AAct.exe" | C:\Users\admin\Desktop\AAct.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AAct x86 Exit code: 0 Modules
| |||||||||||||||
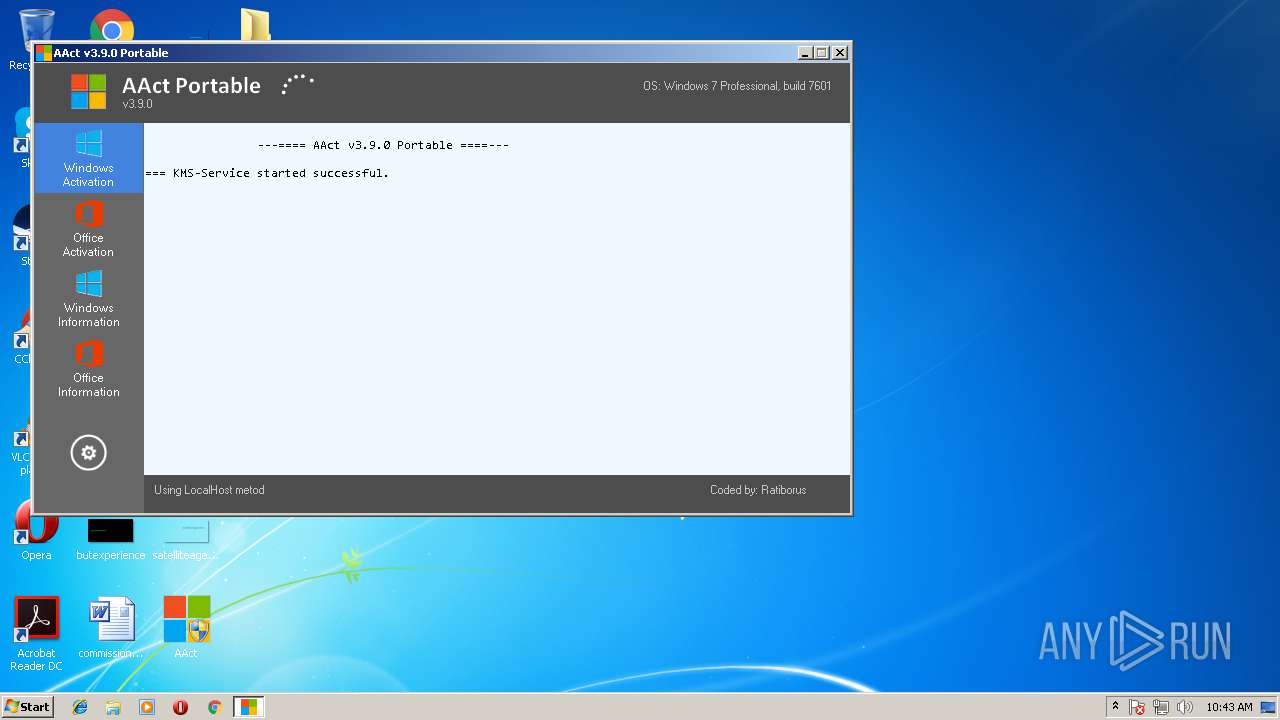
| 1208 | "C:\Users\admin\Desktop\wdvdriver\AAct.dll" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -PO16 RandomKMSPID | C:\Users\admin\Desktop\wdvdriver\AAct.dll | — | AAct.exe | |||||||||||
User: admin Company: MSFree Inc. Integrity Level: HIGH Description: KMS emulator by Ratiborus. Exit code: 1 Version: 2.0.5.0 Modules
| |||||||||||||||
| 1660 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /skms 127.0.0.2:1688 | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1696 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe8_ Global\UsGthrCtrlFltPipeMssGthrPipe8 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2144 | Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2236 | taskkill.exe /t /f /IM aact.dll | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
746
Read events
599
Write events
147
Delete events
0
Modification events
| (PID) Process: | (1124) AAct.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2144) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2144) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2144) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2144) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2144) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2144) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (2144) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (2144) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (2144) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 880 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:D67581F804CE6F5B8EFAD2D165CB7361 | SHA256:6C7DE73631A92E61E03D70E2DB6F87E4D2EE76E34E3B3ABD56412C6855E4F0CA | |||
| 1124 | AAct.exe | C:\Users\admin\Desktop\wdvdriver\AAct.dll | executable | |
MD5:124BA791D8C28151ABCD27D3D81E820B | SHA256:AFD72E00B8B6021CBD104D2CDF59FD9B58D245205D4E72E5D8BD8D75B88CCE48 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | wmiprvse.exe | POST | 302 | 23.67.133.51:80 | http://go.microsoft.com/fwlink/?LinkID=88339 | NL | — | — | whitelisted |
872 | wmiprvse.exe | POST | 302 | 23.67.133.51:80 | http://go.microsoft.com/fwlink/?LinkID=88340 | NL | — | — | whitelisted |
872 | wmiprvse.exe | POST | 302 | 23.67.133.51:80 | http://go.microsoft.com/fwlink/?LinkID=88341 | NL | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
872 | wmiprvse.exe | 23.67.133.51:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
872 | wmiprvse.exe | 65.52.98.231:443 | activation.sls.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |