| download: | cgsetup_en.exe |
| Full analysis: | https://app.any.run/tasks/77e6e4f0-5de3-426b-8871-64ce8cc600cb |
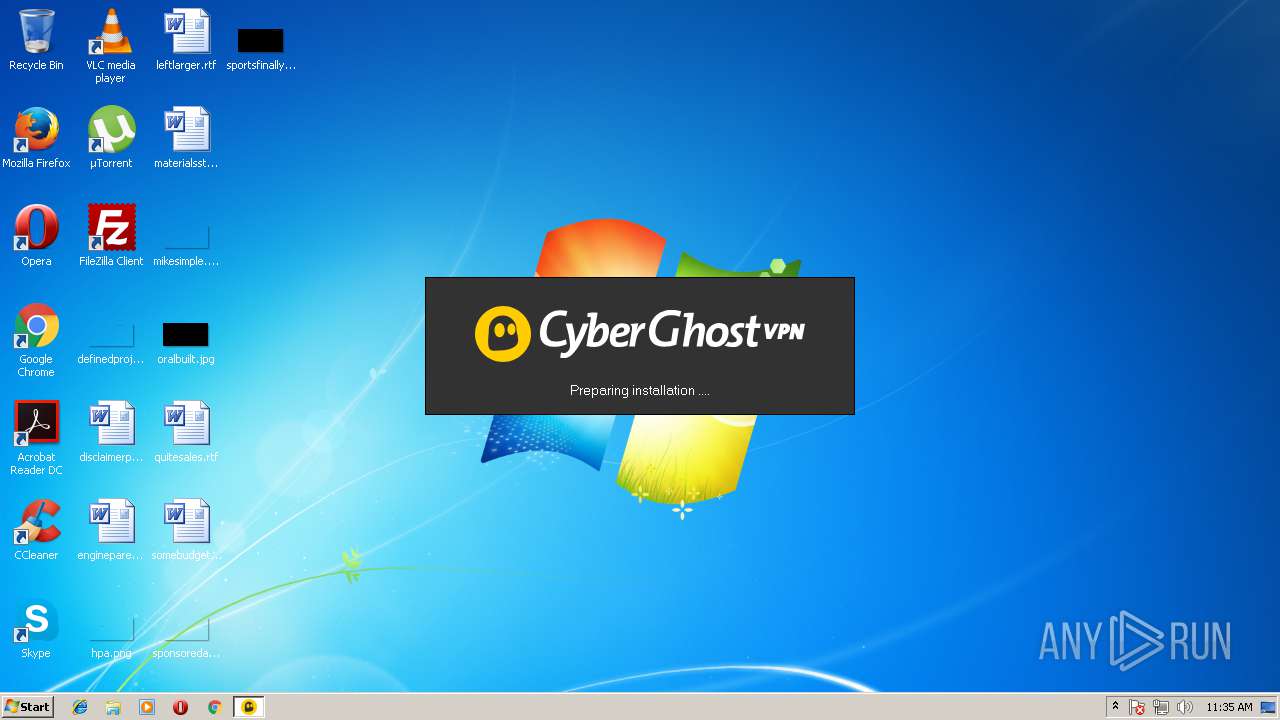
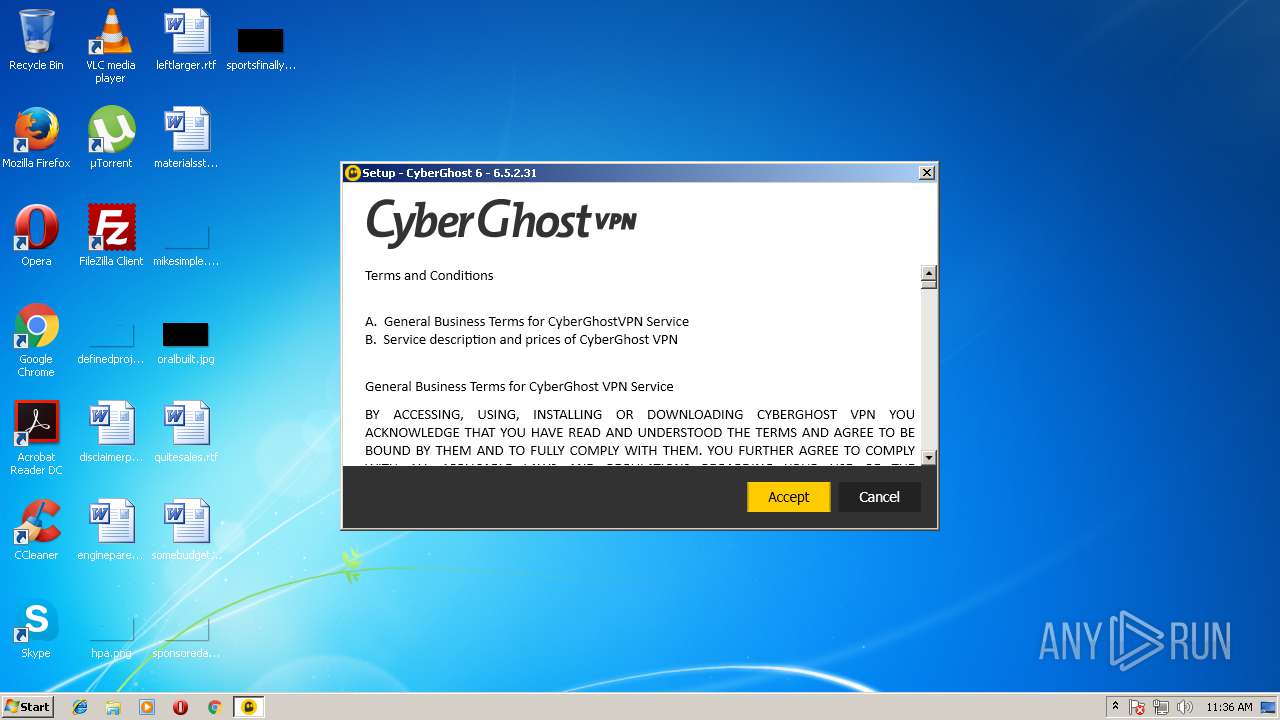
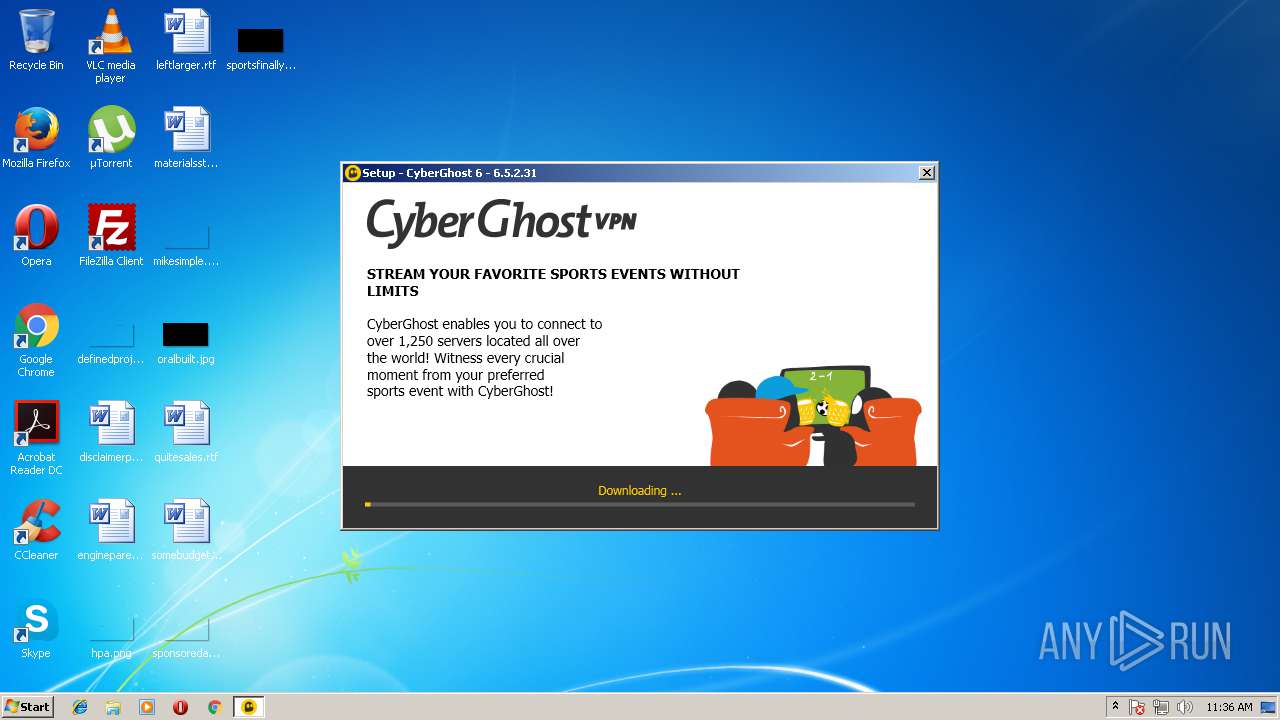
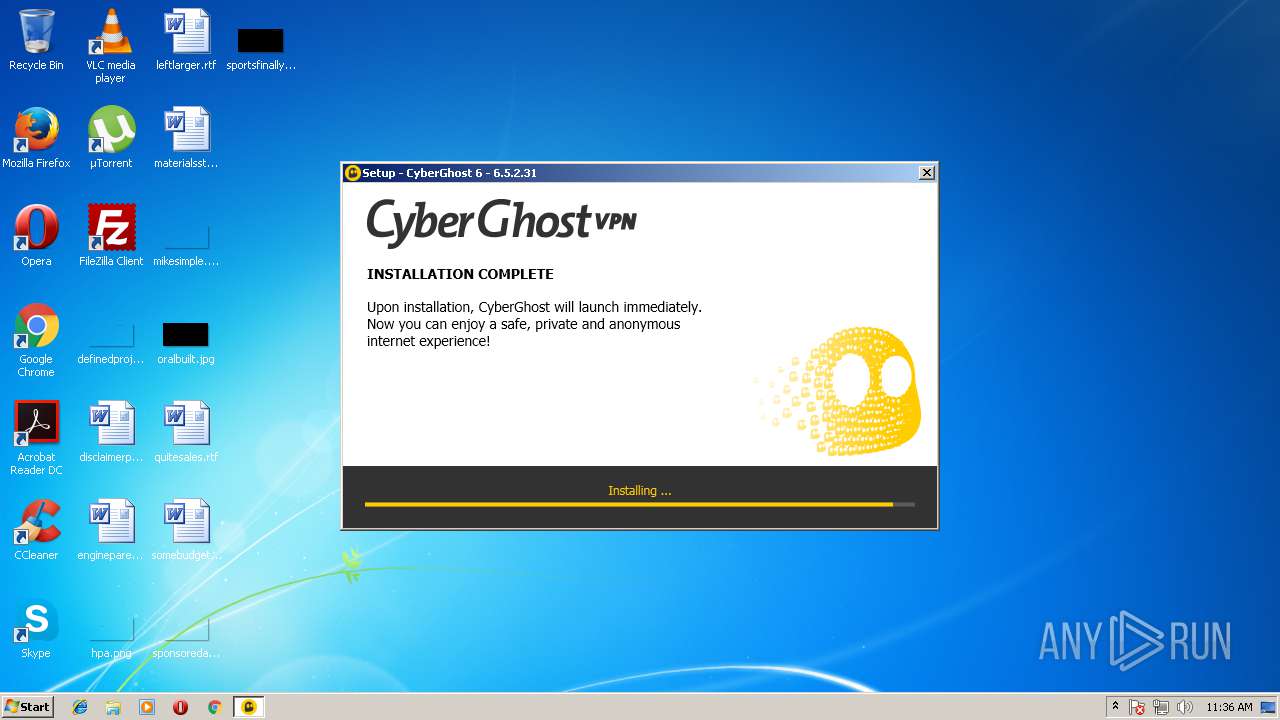
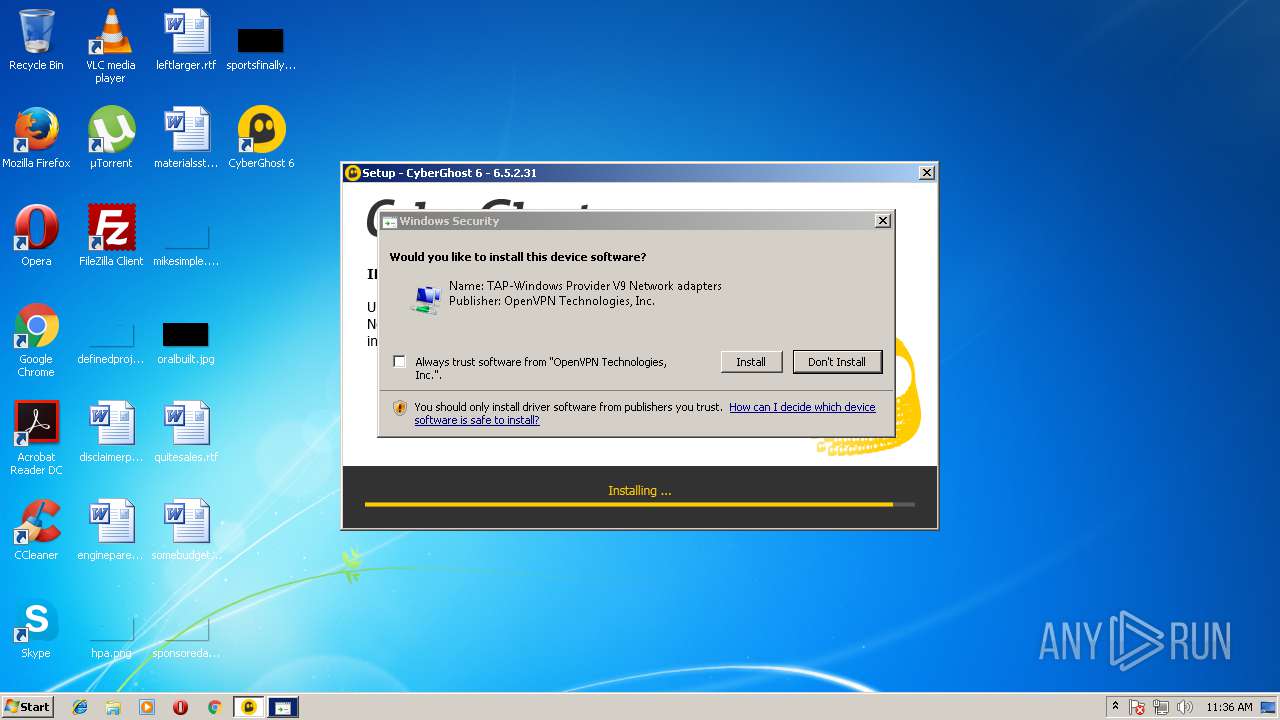
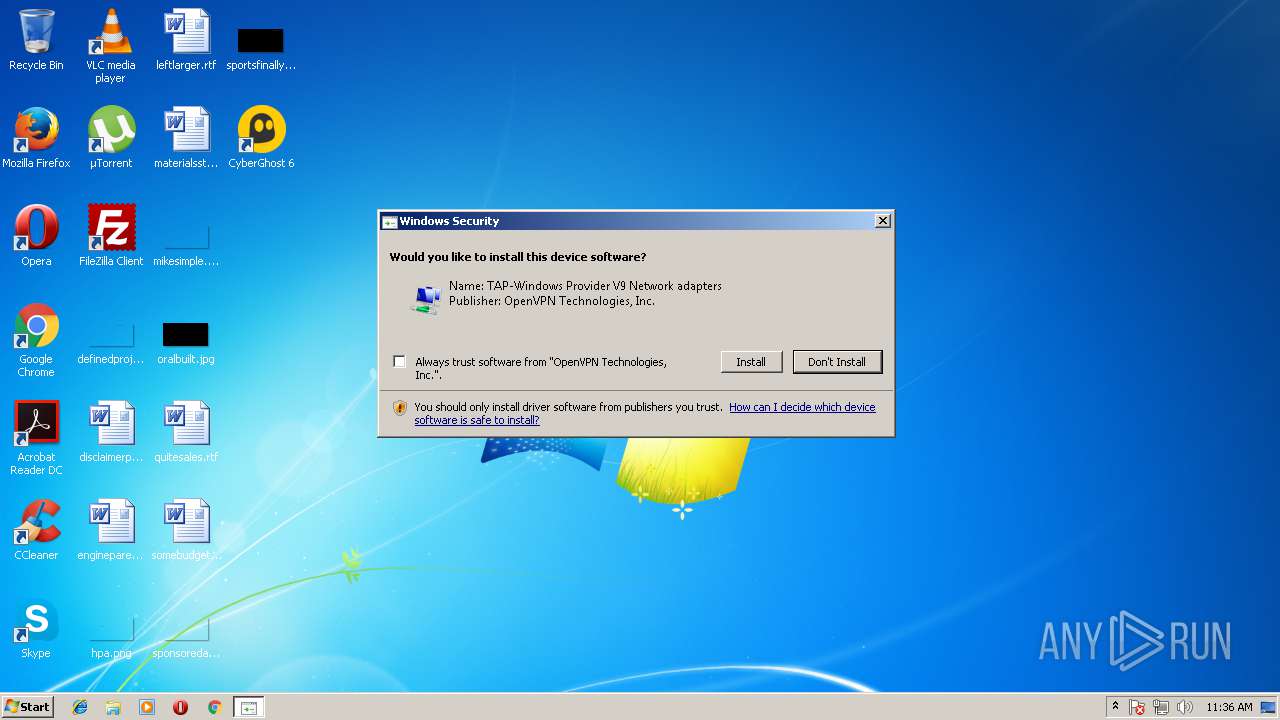
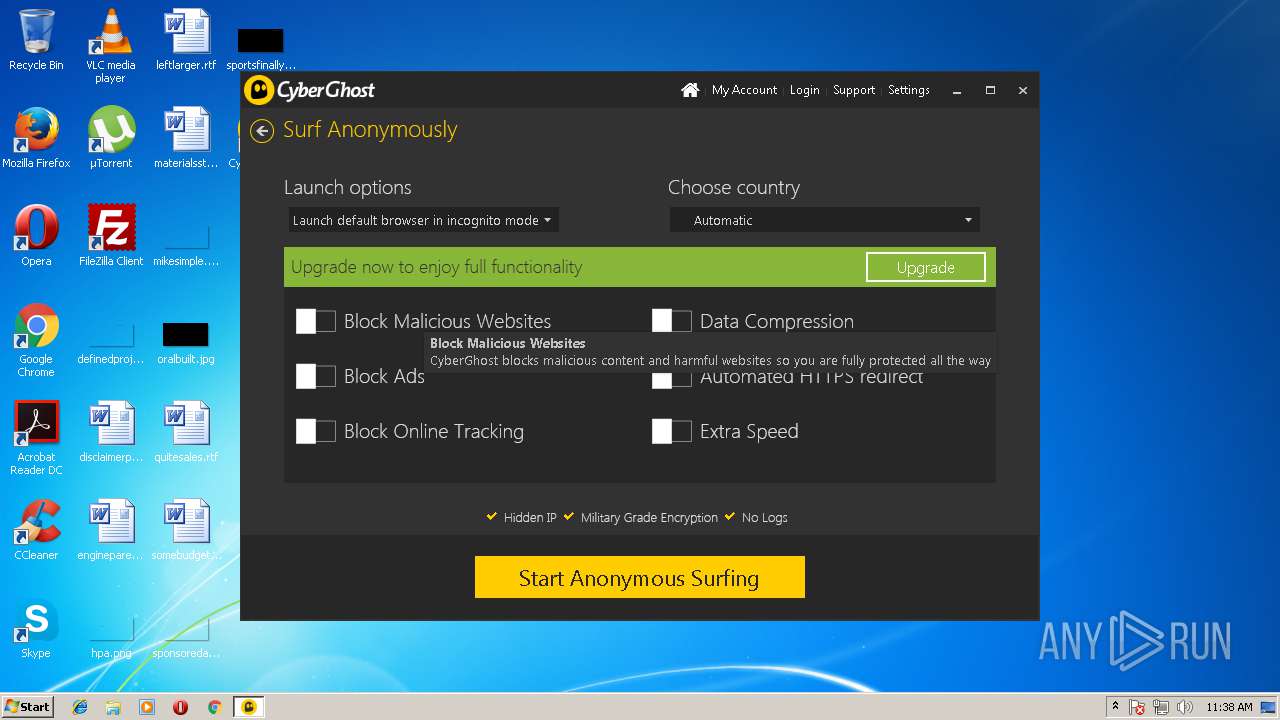
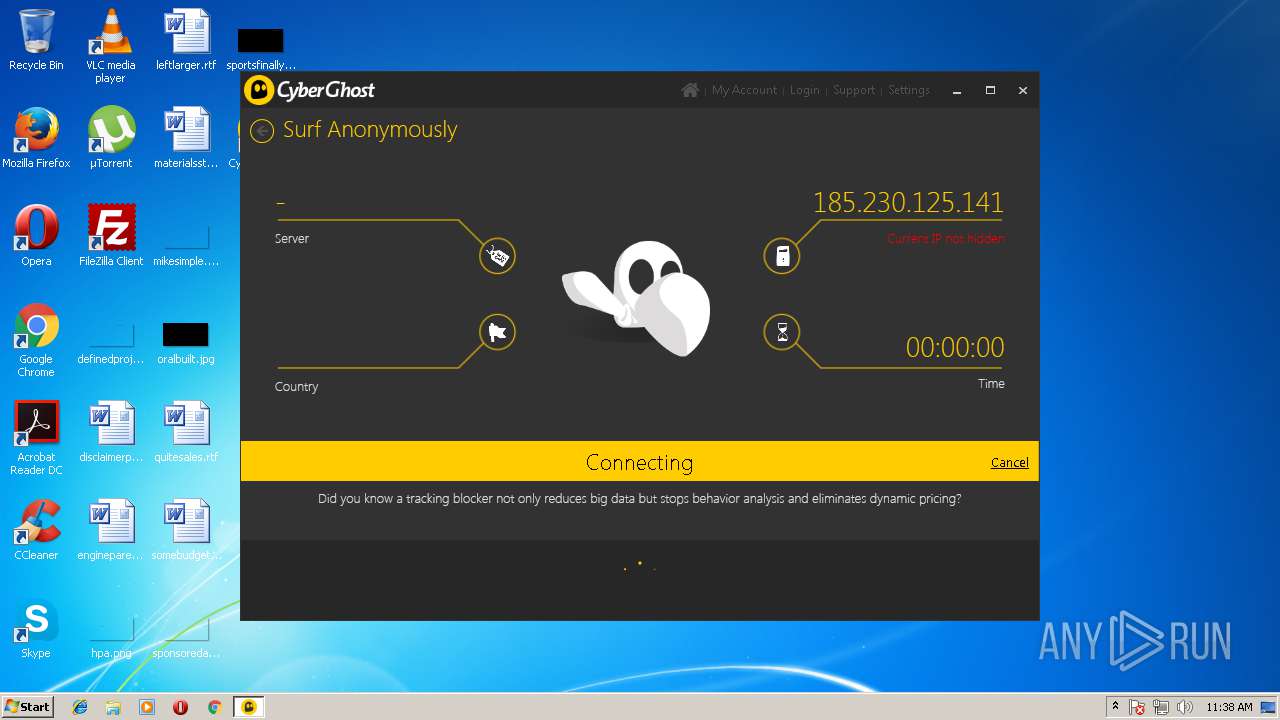
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2018, 10:35:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 420A8D37FE7C83A2D4843590972786B5 |
| SHA1: | 0A2E30ED66BB18F8E2F300C5EFD3D0DA84336667 |
| SHA256: | EE1BBA75F9EC155D41BB096CE5A6CD3BBBB00718186BFA7B56C4FF656349D5DB |
| SSDEEP: | 12288:gEVTfjuILIIYWUWDdyAR2gIGjTxjDL5tj1XUNgASK4CTfVf1WZ62dnWR++/:lVfnDdyIIwT1L5tj1XUNgASK4CTfVf1f |
MALICIOUS
Application was dropped or rewritten from another process
- cg.exe (PID: 2332)
- CyberGhost.Service.exe (PID: 2896)
- CyberGhost.exe (PID: 3636)
- CyberGhost.Service.exe (PID: 332)
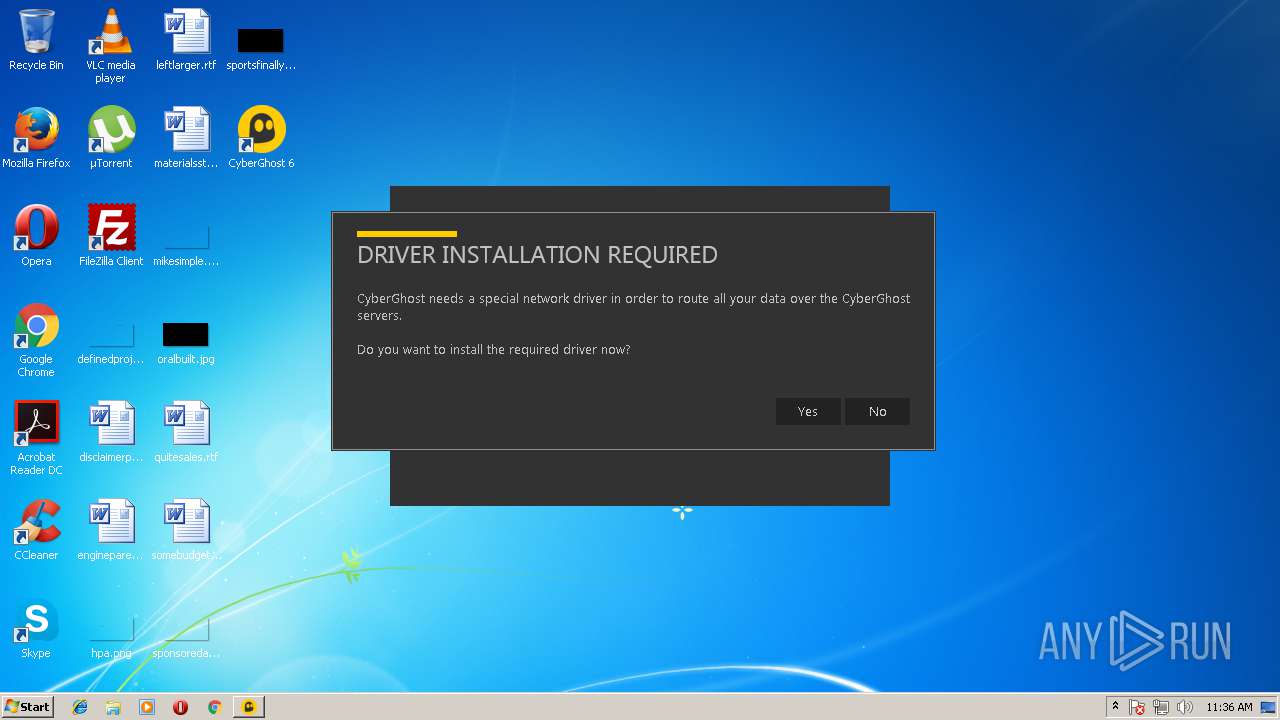
- tap-windows-9.21.2.exe (PID: 1008)
- tapinstall.exe (PID: 2392)
- ns5BC3.tmp (PID: 4052)
- ns5C9F.tmp (PID: 2808)
- CyberGhost.exe (PID: 2348)
- tapinstall.exe (PID: 2196)
- wyUpdate.exe (PID: 2404)
- nvspbind.exe (PID: 1148)
- nvspbind.exe (PID: 3908)
- nvspbind.exe (PID: 1436)
- openssl.exe (PID: 2052)
- CyberGhost.exe (PID: 3156)
- tap-windows-9.21.2.exe (PID: 2312)
- ns98AD.tmp (PID: 2776)
- tapinstall.exe (PID: 3800)
- nvspbind.exe (PID: 2564)
- nvspbind.exe (PID: 3876)
- wyUpdate.exe (PID: 2080)
- nvspbind.exe (PID: 2152)
- ns9AD1.tmp (PID: 3064)
- tapinstall.exe (PID: 2508)
- wyUpdate.exe (PID: 3356)
- wyUpdate.exe (PID: 384)
- wyUpdate.exe (PID: 2972)
Changes settings of System certificates
- cgsetup_en.exe (PID: 3744)
- tapinstall.exe (PID: 2196)
Loads dropped or rewritten executable
- CyberGhost.Service.exe (PID: 2896)
- CyberGhost.Service.exe (PID: 332)
- CyberGhost.exe (PID: 3636)
- tap-windows-9.21.2.exe (PID: 1008)
- CyberGhost.exe (PID: 2348)
- openssl.exe (PID: 2052)
- CyberGhost.exe (PID: 3156)
- tap-windows-9.21.2.exe (PID: 2312)
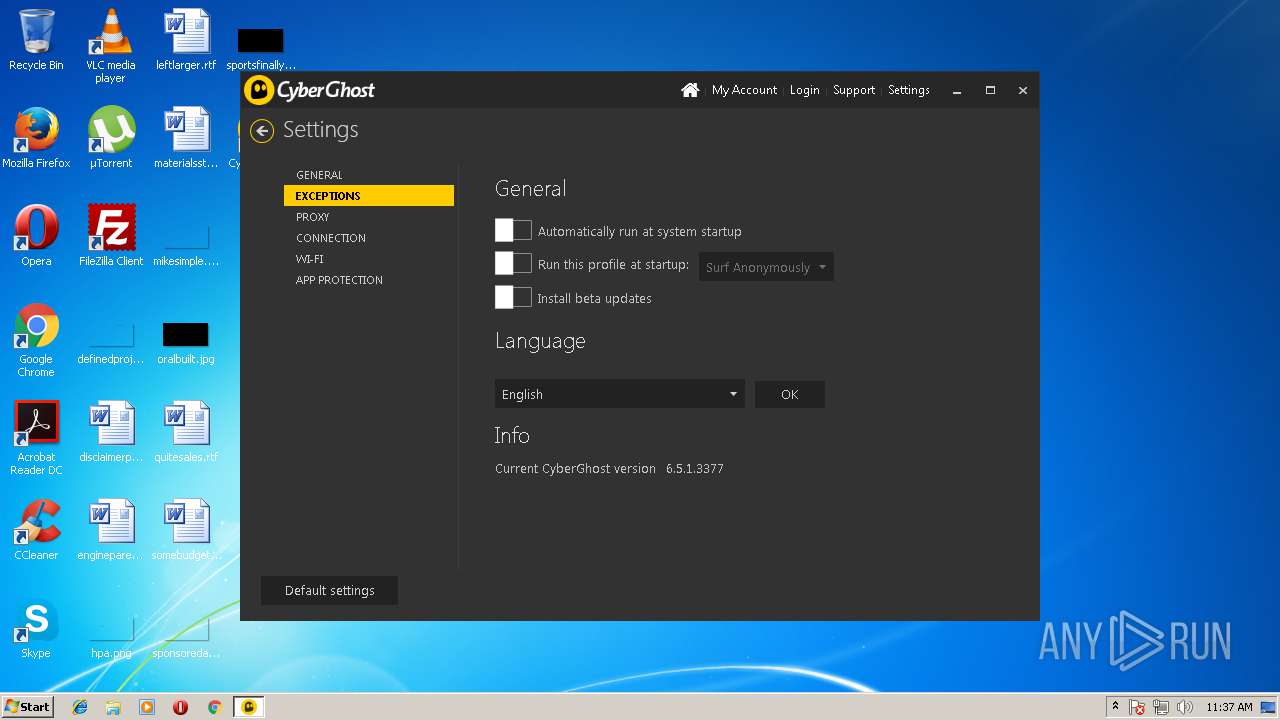
Changes the autorun value in the registry
- CyberGhost.exe (PID: 2348)
SUSPICIOUS
Adds / modifies Windows certificates
- cgsetup_en.exe (PID: 3744)
- tapinstall.exe (PID: 2196)
Creates files in the user directory
- cgsetup_en.exe (PID: 3744)
- CyberGhost.exe (PID: 2348)
Creates a software uninstall entry
- cg.exe (PID: 2332)
- tap-windows-9.21.2.exe (PID: 1008)
- tap-windows-9.21.2.exe (PID: 2312)
Executable content was dropped or overwritten
- cgsetup_en.exe (PID: 3744)
- cg.exe (PID: 2332)
- tap-windows-9.21.2.exe (PID: 1008)
- tapinstall.exe (PID: 2196)
- DrvInst.exe (PID: 2704)
- tap-windows-9.21.2.exe (PID: 2312)
- DrvInst.exe (PID: 2220)
Creates files in the program directory
- CyberGhost.Service.exe (PID: 332)
- tap-windows-9.21.2.exe (PID: 1008)
- cg.exe (PID: 2332)
- openssl.exe (PID: 2052)
Creates or modifies windows services
- CyberGhost.Service.exe (PID: 332)
- CyberGhost.Service.exe (PID: 2896)
- DrvInst.exe (PID: 2704)
- CyberGhost.exe (PID: 2348)
- netsh.exe (PID: 2696)
- DrvInst.exe (PID: 2220)
Creates files in the Windows directory
- CyberGhost.Service.exe (PID: 2896)
- tapinstall.exe (PID: 2196)
- DrvInst.exe (PID: 2704)
- wyUpdate.exe (PID: 2404)
- DrvInst.exe (PID: 2220)
- DrvInst.exe (PID: 1400)
- wyUpdate.exe (PID: 2080)
- wyUpdate.exe (PID: 3356)
- wyUpdate.exe (PID: 384)
- wyUpdate.exe (PID: 2972)
Removes files from Windows directory
- CyberGhost.Service.exe (PID: 2896)
- DrvInst.exe (PID: 2704)
- wyUpdate.exe (PID: 2404)
- DrvInst.exe (PID: 2220)
- DrvInst.exe (PID: 1400)
- wyUpdate.exe (PID: 2080)
- wyUpdate.exe (PID: 3356)
- wyUpdate.exe (PID: 384)
- wyUpdate.exe (PID: 2972)
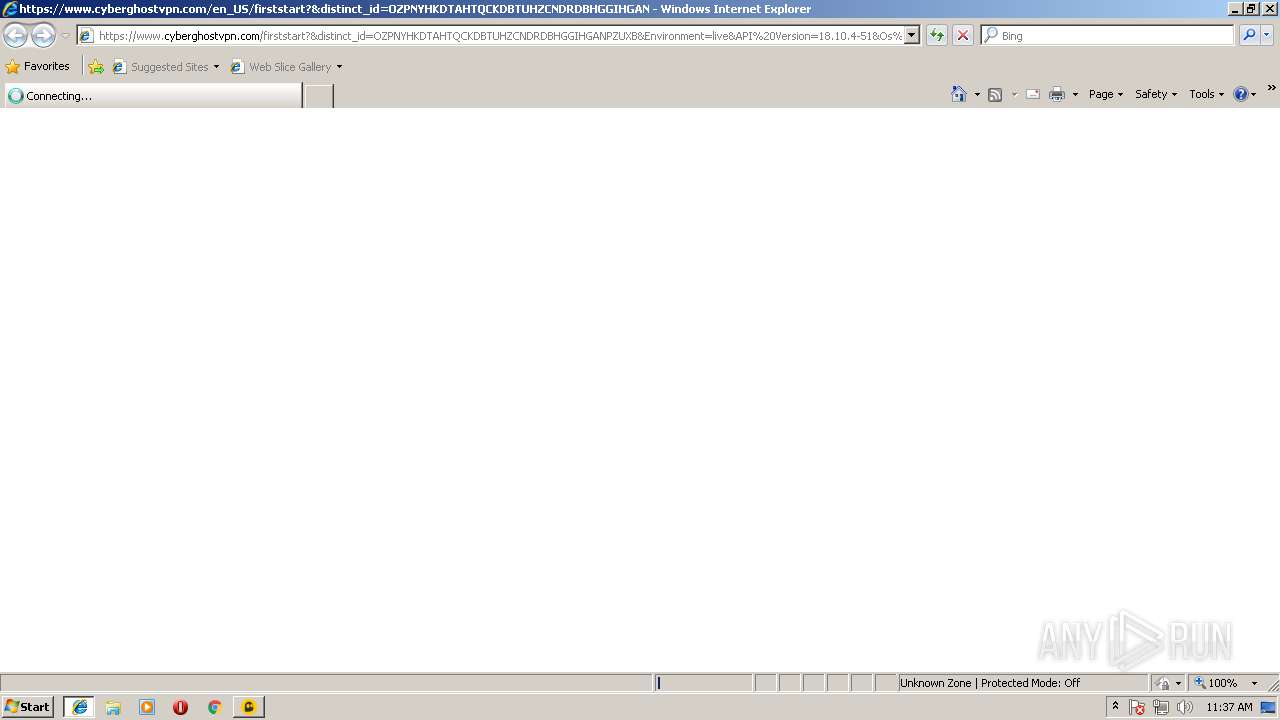
Changes IE settings (feature browser emulation)
- CyberGhost.exe (PID: 3636)
- CyberGhost.exe (PID: 2348)
Modifies the open verb of a shell class
- CyberGhost.Service.exe (PID: 2896)
Starts application with an unusual extension
- tap-windows-9.21.2.exe (PID: 1008)
- tap-windows-9.21.2.exe (PID: 2312)
Creates files in the driver directory
- DrvInst.exe (PID: 2704)
- DrvInst.exe (PID: 2220)
Uses NETSH.EXE for network configuration
- CyberGhost.Service.exe (PID: 2896)
Application launched itself
- CyberGhost.exe (PID: 2348)
Starts Internet Explorer
- CyberGhost.exe (PID: 2348)
Reads internet explorer settings
- CyberGhost.exe (PID: 2348)
INFO
Dropped object may contain URL's
- cgsetup_en.exe (PID: 3744)
- CyberGhost.Service.exe (PID: 2896)
- cg.exe (PID: 2332)
- tap-windows-9.21.2.exe (PID: 1008)
- tapinstall.exe (PID: 2196)
- DrvInst.exe (PID: 2704)
- tap-windows-9.21.2.exe (PID: 2312)
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3768)
- CyberGhost.exe (PID: 2348)
- tapinstall.exe (PID: 2508)
Reads settings of System Certificates
- cg.exe (PID: 2332)
- CyberGhost.exe (PID: 2348)
Dropped object may contain Bitcoin addresses
- cg.exe (PID: 2332)
- CyberGhost.exe (PID: 2348)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2648)
Creates files in the user directory
- iexplore.exe (PID: 3340)
Changes internet zones settings
- iexplore.exe (PID: 3768)
Application launched itself
- iexplore.exe (PID: 3768)
Creates or modifies windows services
- vssvc.exe (PID: 2648)
Reads internet explorer settings
- iexplore.exe (PID: 3340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:30 14:12:22+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 260096 |
| InitializedDataSize: | 215040 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2232 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.3 |
| ProductVersionNumber: | 1.0.0.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Process default |
| CharacterSet: | Unicode |
| CompanyName: | CyberGhost S.A. |
| FileDescription: | CyberGhost Web Installer |
| FileVersion: | 1.0.0.3 |
| InternalName: | WebBoots.exe |
| LegalCopyright: | Copyright (C) 2018 CyberGhost S.A. |
| OriginalFileName: | WebBoots.exe |
| ProductName: | CyberGhost VPN |
| ProductVersion: | 1.0.0.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Apr-2018 12:12:22 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | CyberGhost S.A. |
| FileDescription: | CyberGhost Web Installer |
| FileVersion: | 1.0.0.3 |
| InternalName: | WebBoots.exe |
| LegalCopyright: | Copyright (C) 2018 CyberGhost S.A. |
| OriginalFilename: | WebBoots.exe |
| ProductName: | CyberGhost VPN |
| ProductVersion: | 1.0.0.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 30-Apr-2018 12:12:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003F6B5 | 0x0003F800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60586 |
.rdata | 0x00041000 | 0x00008FE4 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18728 |
.data | 0x0004A000 | 0x00001B5C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.33422 |
.rsrc | 0x0004C000 | 0x00029B58 | 0x00029C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.03805 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.92969 | 4264 | UNKNOWN | German - Germany | RT_ICON |
3 | 3.56124 | 9640 | UNKNOWN | German - Germany | RT_ICON |
4 | 3.34376 | 16936 | UNKNOWN | German - Germany | RT_ICON |
5 | 2.92195 | 67624 | UNKNOWN | German - Germany | RT_ICON |
6 | 7.9517 | 13363 | UNKNOWN | German - Germany | RT_ICON |
101 | 3.1221 | 190 | UNKNOWN | Process Default Language | RT_DIALOG |
107 | 2.79908 | 90 | UNKNOWN | German - Germany | RT_GROUP_ICON |
108 | 2.48827 | 55594 | UNKNOWN | German - Germany | RT_BITMAP |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
WINTRUST.dll |
Total processes
93
Monitored processes
40
Malicious processes
12
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\CyberGhost 6\CyberGhost.Service.exe" --install | C:\Program Files\CyberGhost 6\CyberGhost.Service.exe | — | CyberGhost.exe | |||||||||||
User: admin Company: CyberGhost S.A. Integrity Level: HIGH Description: CyberGhost Service Exit code: 0 Version: 6.5.1.3377 Modules
| |||||||||||||||
| 384 | "C:\Program Files\CyberGhost 6\wyUpdate.exe" /justcheck /quickcheck /noerr -server="https://download.cyberghostvpn.com/windows/updates/6/wyserver.wys" | C:\Program Files\CyberGhost 6\wyUpdate.exe | CyberGhost.Service.exe | ||||||||||||
User: SYSTEM Company: wyDay Integrity Level: SYSTEM Description: wyUpdate Exit code: 0 Version: 2.6.18.4 Modules
| |||||||||||||||
| 584 | "C:\Users\admin\AppData\Local\Temp\cgsetup_en.exe" | C:\Users\admin\AppData\Local\Temp\cgsetup_en.exe | — | explorer.exe | |||||||||||
User: admin Company: CyberGhost S.A. Integrity Level: MEDIUM Description: CyberGhost Web Installer Exit code: 3221226540 Version: 1.0.0.3 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\CyberGhost 6\Data\OpenVPN\tap-windows-9.21.2.exe" /S | C:\Program Files\CyberGhost 6\Data\OpenVPN\tap-windows-9.21.2.exe | CyberGhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\CyberGhost 6\Data\Tools\nvspbind.exe" "TAP-Windows Adapter" /d * | C:\Program Files\CyberGhost 6\Data\Tools\nvspbind.exe | — | CyberGhost.Service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Hyper-V Network VSP Bind Application Exit code: 13 Version: 6.1.7725.0 (fbl_core1_hyp_dev(kemange).091124-1220) Modules
| |||||||||||||||
| 1400 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\Windows\INF\oem4.inf" "oemvista.inf:tap0901:tap0901.ndi:9.0.0.21:tap0901" "6d14a44ff" "00000638" "000004B0" "00000618" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1436 | "C:\Program Files\CyberGhost 6\Data\Tools\nvspbind.exe" "TAP-Windows Adapter" /e ms_tcpip6 | C:\Program Files\CyberGhost 6\Data\Tools\nvspbind.exe | — | CyberGhost.Service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Hyper-V Network VSP Bind Application Exit code: 13 Version: 6.1.7725.0 (fbl_core1_hyp_dev(kemange).091124-1220) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\CyberGhost 6\Data\OpenVPN\openssl.exe" req -days 3650 -nodes -new -keyout "C:\Users\admin\AppData\Local\CyberGhost\26998924_a48d74df3433d5e47761a90a2f395eefc54a8701.key" -out "C:\Users\admin\AppData\Local\CyberGhost\26998924_a48d74df3433d5e47761a90a2f395eefc54a8701.csr" -config "C:\Users\admin\AppData\Local\CyberGhost\openssl.txt" -batch -subj "/C=DE/O=CyberGhost VPN/OU=CyberGhost/CN=26998924_a48d74df3433d5e47761a90a2f395eefc54a8701" | C:\Program Files\CyberGhost 6\Data\OpenVPN\openssl.exe | — | CyberGhost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\CyberGhost 6\wyUpdate.exe" /justcheck /quickcheck /noerr -server="https://download.cyberghostvpn.com/windows/updates/6/wyserver.wys" | C:\Program Files\CyberGhost 6\wyUpdate.exe | CyberGhost.Service.exe | ||||||||||||
User: SYSTEM Company: wyDay Integrity Level: SYSTEM Description: wyUpdate Exit code: 0 Version: 2.6.18.4 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\CyberGhost 6\Data\Tools\nvspbind.exe" "TAP-Windows Adapter" /e ms_tcpip6 | C:\Program Files\CyberGhost 6\Data\Tools\nvspbind.exe | — | CyberGhost.Service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Hyper-V Network VSP Bind Application Exit code: 13 Version: 6.1.7725.0 (fbl_core1_hyp_dev(kemange).091124-1220) Modules
| |||||||||||||||
Total events
5 148
Read events
3 216
Write events
1 855
Delete events
77
Modification events
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3744) cgsetup_en.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\cgsetup_en_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
68
Suspicious files
64
Text files
741
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | cgsetup_en.exe | C:\Users\admin\AppData\Local\Temp\CabE5E6.tmp | — | |
MD5:— | SHA256:— | |||
| 3744 | cgsetup_en.exe | C:\Users\admin\AppData\Local\Temp\TarE5E7.tmp | — | |
MD5:— | SHA256:— | |||
| 3744 | cgsetup_en.exe | C:\Users\admin\AppData\Local\Temp\cg.exe | executable | |
MD5:— | SHA256:— | |||
| 3744 | cgsetup_en.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | der | |
MD5:— | SHA256:— | |||
| 3744 | cgsetup_en.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5080DC7A65DB6A5960ECD874088F3328_BC00434159DAE8351451CCE9C748F5D7 | der | |
MD5:— | SHA256:— | |||
| 3744 | cgsetup_en.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5457A8CE4B2A7499F8299A013B6E1C7C_CE50F893881D43DC0C815E4D80FAF2B4 | binary | |
MD5:— | SHA256:— | |||
| 3744 | cgsetup_en.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\74FBF93595CFC8459196065CE54AD928 | binary | |
MD5:— | SHA256:— | |||
| 2332 | cg.exe | C:\Users\admin\AppData\Local\Temp\6d740bcb-1c76-4fdf-a33c-1359d9ef5cc2.zip | compressed | |
MD5:— | SHA256:— | |||
| 3744 | cgsetup_en.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D2B5168CDD0EBF4C0C8EA1C3A1FAE07F_7E90E4B58528E238D78726B191FBDB4D | binary | |
MD5:— | SHA256:— | |||
| 3744 | cgsetup_en.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@cyberghostvpn[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
52
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2348 | CyberGhost.exe | GET | 304 | 178.255.83.1:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR64T7ooMQqLLQoy%2BemBUYZQOKh6QQUkK9qOpRaC9iQ6hJWc99DtDoo2ucCEFT0AaVT7qFO%2F2aJYVCRVMs%3D | GB | — | — | whitelisted |
3744 | cgsetup_en.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.trust-provider.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEENSAj%2F6qJAfE5%2Fj9OXBRE4%3D | GB | der | 471 b | whitelisted |
3744 | cgsetup_en.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEC58h8wOk0pS%2FpT9HLfNNK8%3D | GB | der | 727 b | whitelisted |
3744 | cgsetup_en.exe | GET | 200 | 2.20.188.194:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | unknown | der | 313 b | whitelisted |
3744 | cgsetup_en.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSSdxXdG447ymkRNPVViULv3rkBzQQUKZFg%2F4pN%2Buv5pmq4z%2FnmS71JzhICEHTHko7VWmc1vqjaeNBU3EQ%3D | GB | der | 471 b | whitelisted |
2896 | CyberGhost.Service.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEC58h8wOk0pS%2FpT9HLfNNK8%3D | GB | der | 727 b | whitelisted |
3744 | cgsetup_en.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | GB | der | 471 b | whitelisted |
2896 | CyberGhost.Service.exe | GET | 200 | 104.16.91.188:80 | http://crl.comodoca.com/COMODORSACodeSigningCA.crl | US | binary | 222 Kb | whitelisted |
— | — | GET | 200 | 178.255.83.1:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | GB | der | 471 b | whitelisted |
2348 | CyberGhost.exe | GET | 200 | 178.255.83.1:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | GB | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3744 | cgsetup_en.exe | 178.255.83.1:80 | ocsp.trust-provider.com | CCANET Limited | GB | unknown |
3744 | cgsetup_en.exe | 2.20.188.194:80 | ocsp.comodoca4.com | Akamai International B.V. | — | whitelisted |
3744 | cgsetup_en.exe | 104.20.27.8:443 | download.cyberghostvpn.com | Cloudflare Inc | US | shared |
3744 | cgsetup_en.exe | 104.16.89.188:80 | crt.comodoca.com | Cloudflare Inc | US | shared |
2332 | cg.exe | 104.20.27.8:443 | download.cyberghostvpn.com | Cloudflare Inc | US | shared |
2896 | CyberGhost.Service.exe | 178.255.83.1:80 | ocsp.trust-provider.com | CCANET Limited | GB | unknown |
— | — | 178.255.83.1:80 | ocsp.trust-provider.com | CCANET Limited | GB | unknown |
2348 | CyberGhost.exe | 104.20.27.8:443 | download.cyberghostvpn.com | Cloudflare Inc | US | shared |
2896 | CyberGhost.Service.exe | 104.16.91.188:80 | crt.comodoca.com | Cloudflare Inc | US | shared |
2348 | CyberGhost.exe | 104.20.26.8:443 | download.cyberghostvpn.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.cyberghostvpn.com |
| whitelisted |
ocsp.trust-provider.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
rest.cyberghostvpn.com |
| whitelisted |
www.cyberghostvpn.com |
| whitelisted |
mp-feedback.cyberghostvpn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
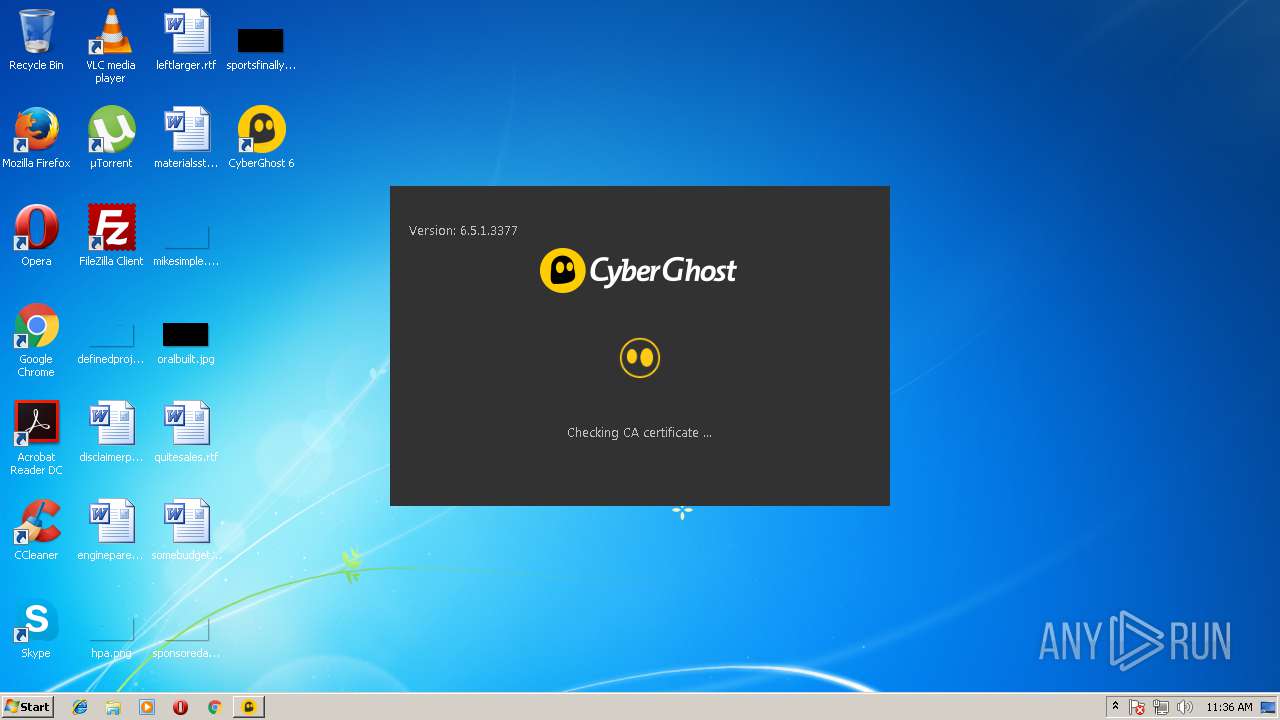
cgsetup_en.exe | Checking .NET framework ... |
cgsetup_en.exe | Downloading WebInstaller ... |
cgsetup_en.exe | Starting WebInstaller ... |
CyberGhost.exe | COULD NOT EXECUTE TAP INSTALLER A task was canceled.
|
CyberGhost.Service.exe | Checking for Update on https://download.cyberghostvpn.com/windows/updates/6/
|
CyberGhost.exe | CHECKING ADAPTER Intel(R) PRO/1000 MT Network Connection
|
CyberGhost.exe | FOUND ADAPTER Intel(R) PRO/1000 MT Network Connection WITH ms_sstpminiport
|
CyberGhost.exe | FOUND ADAPTER Intel(R) PRO/1000 MT Network Connection WITH ms_agilevpnminiport
|
CyberGhost.exe | FOUND ADAPTER Intel(R) PRO/1000 MT Network Connection WITH ms_l2tpminiport
|
CyberGhost.exe | FOUND ADAPTER Intel(R) PRO/1000 MT Network Connection WITH ms_pptpminiport
|