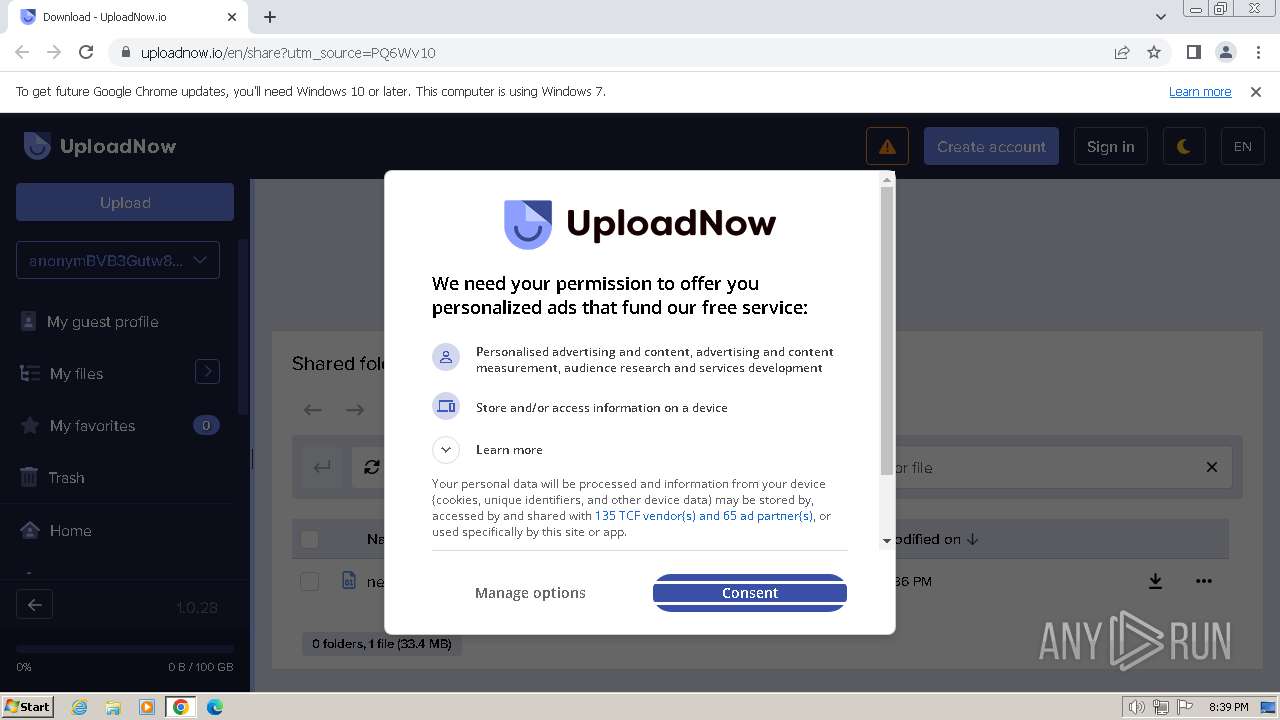
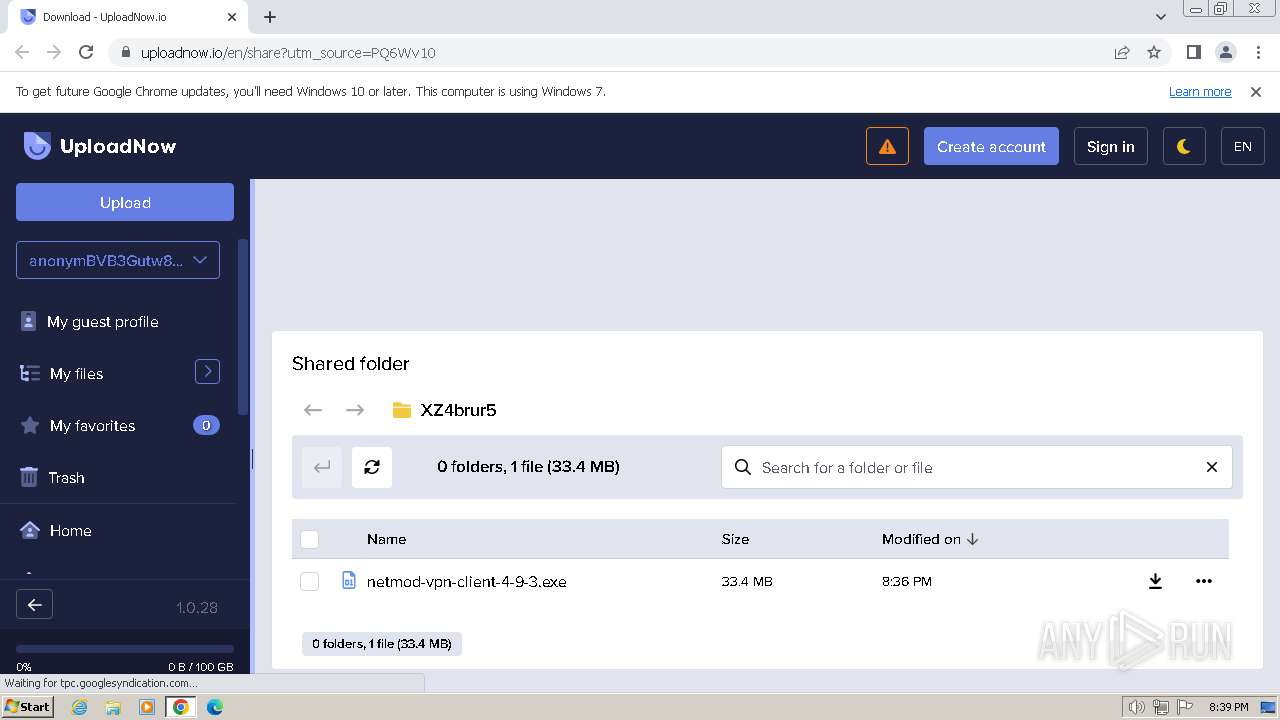
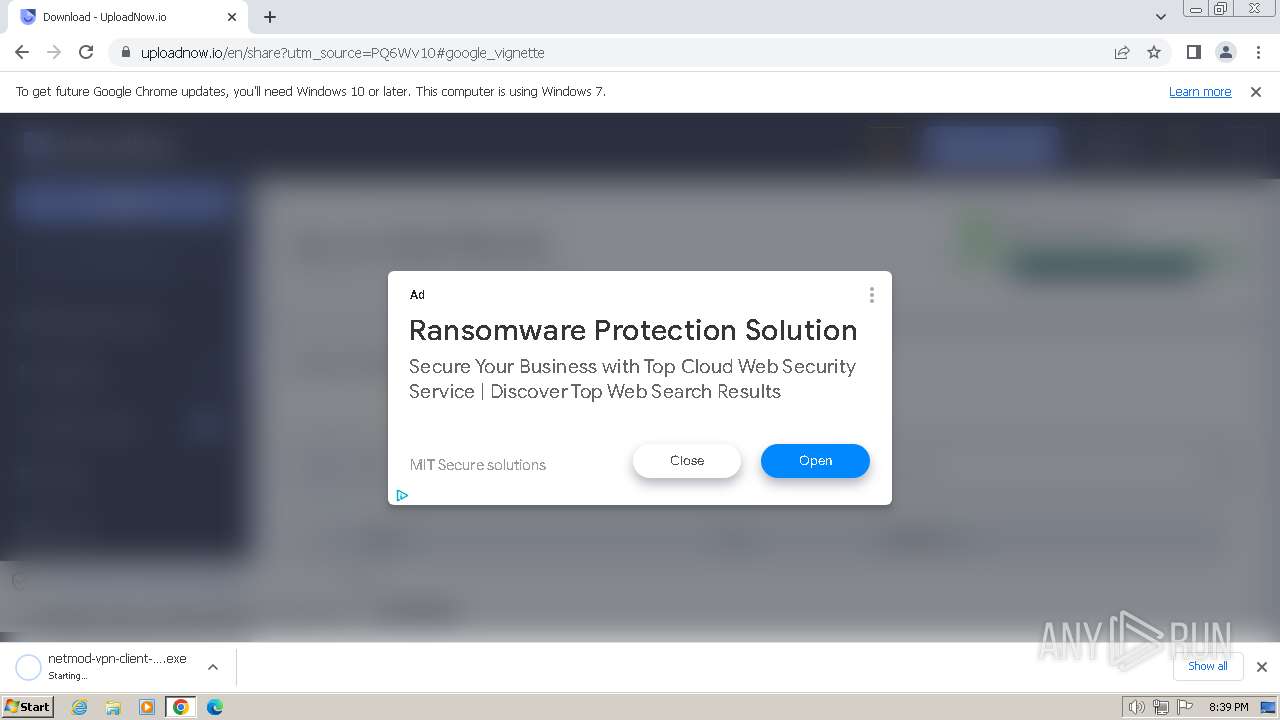
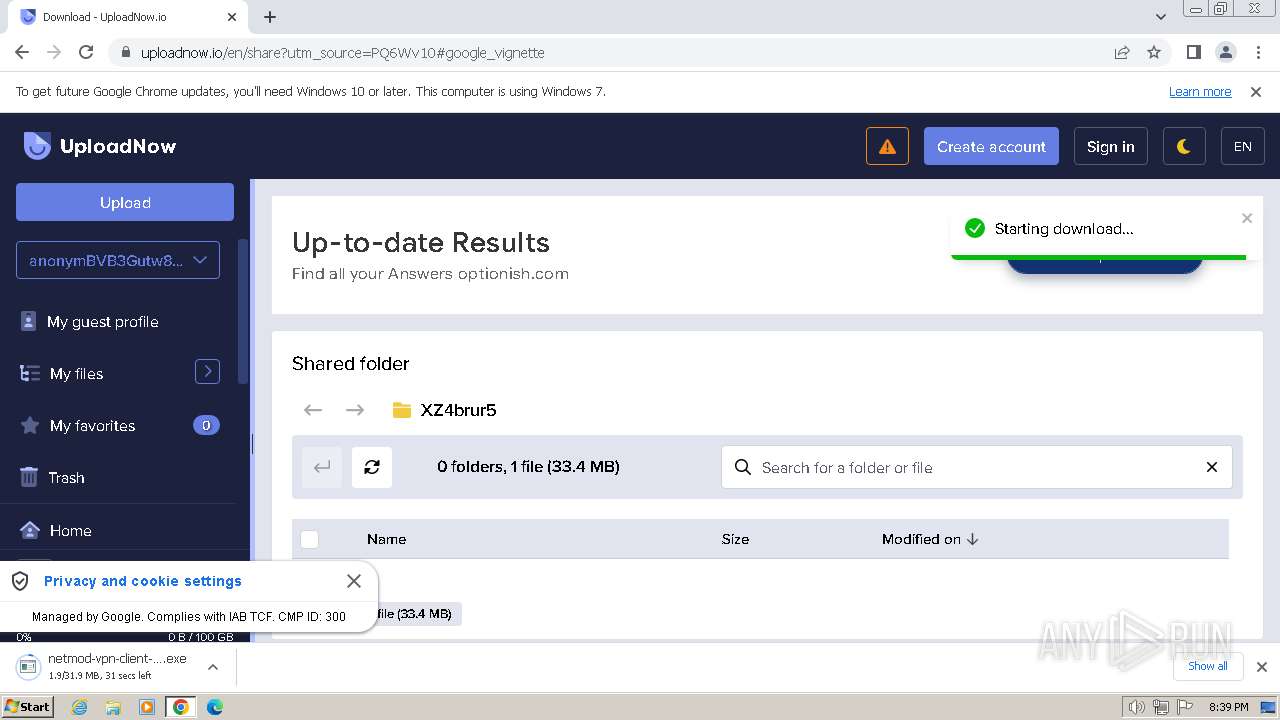
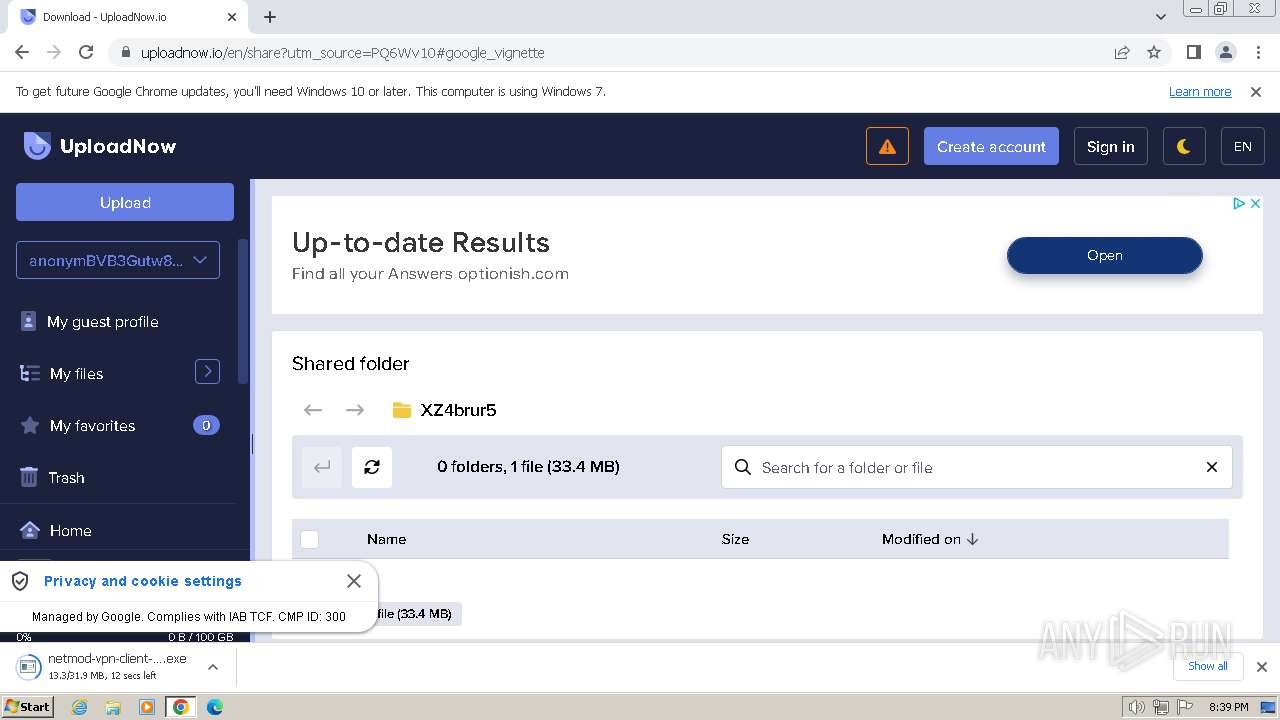
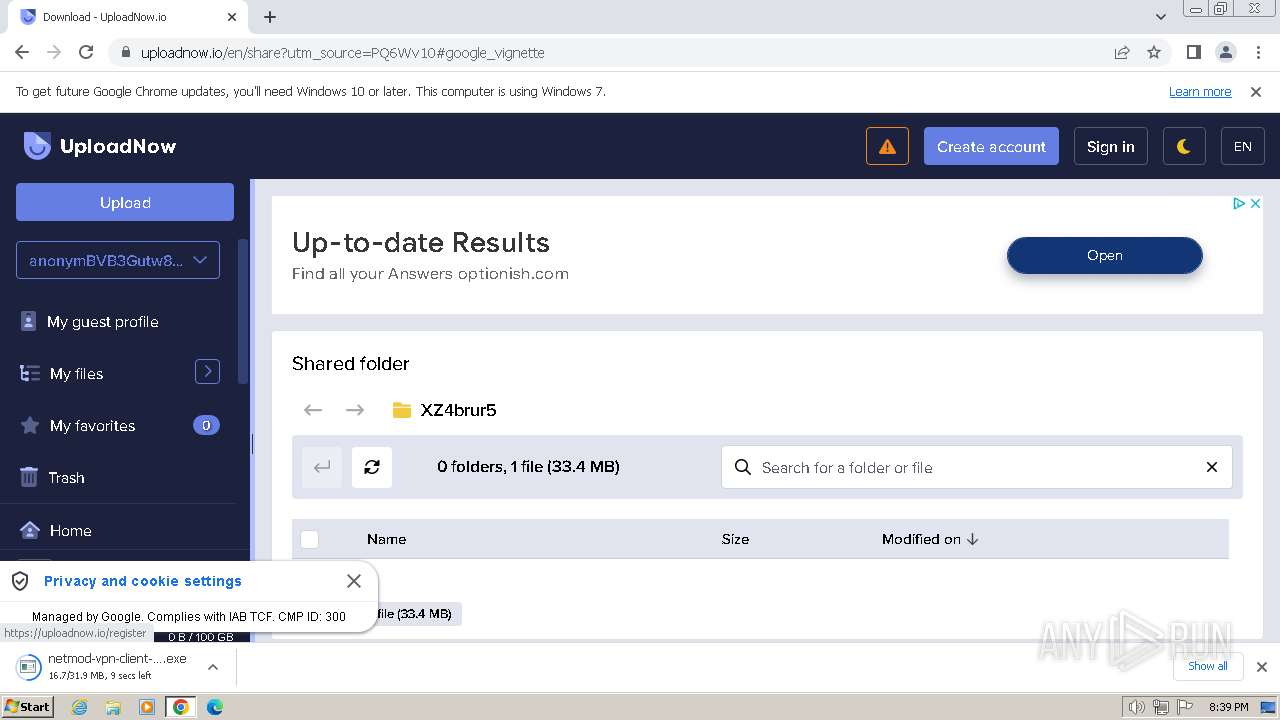
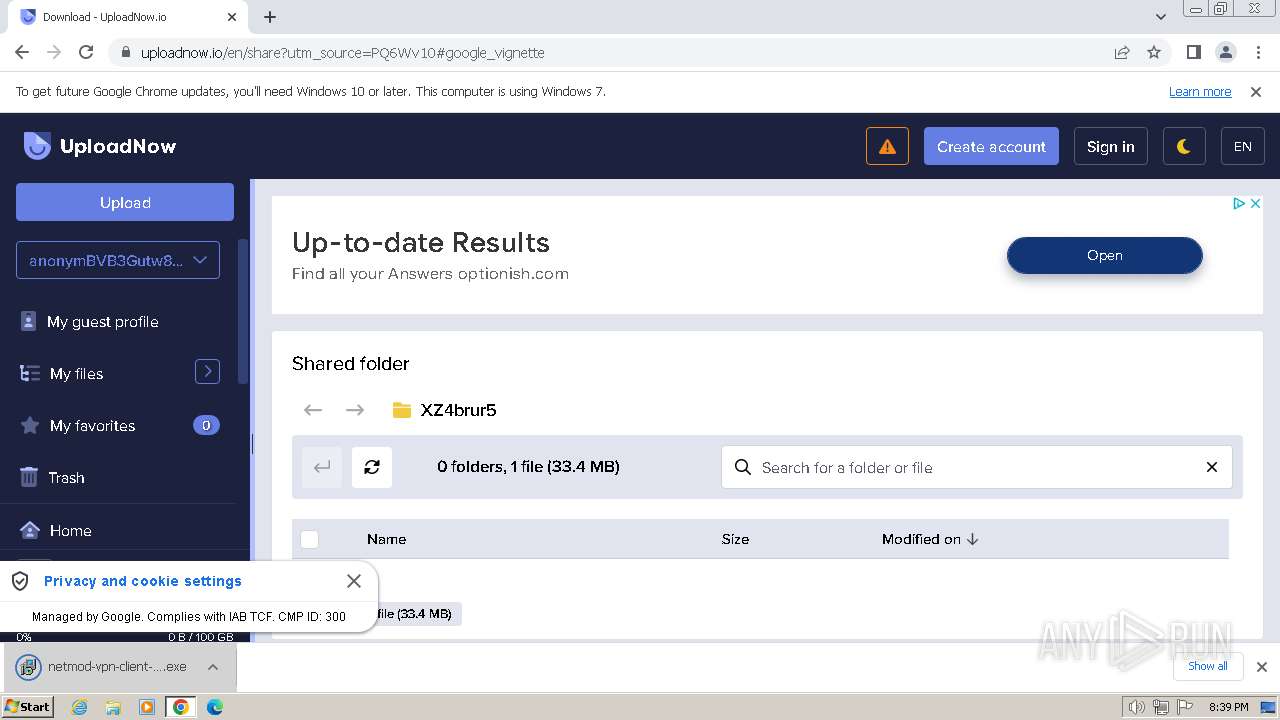
| URL: | https://uploadnow.io/f/PQ6Wv10 |
| Full analysis: | https://app.any.run/tasks/6e350b53-bbbe-4377-bb4f-20c4b22c355f |
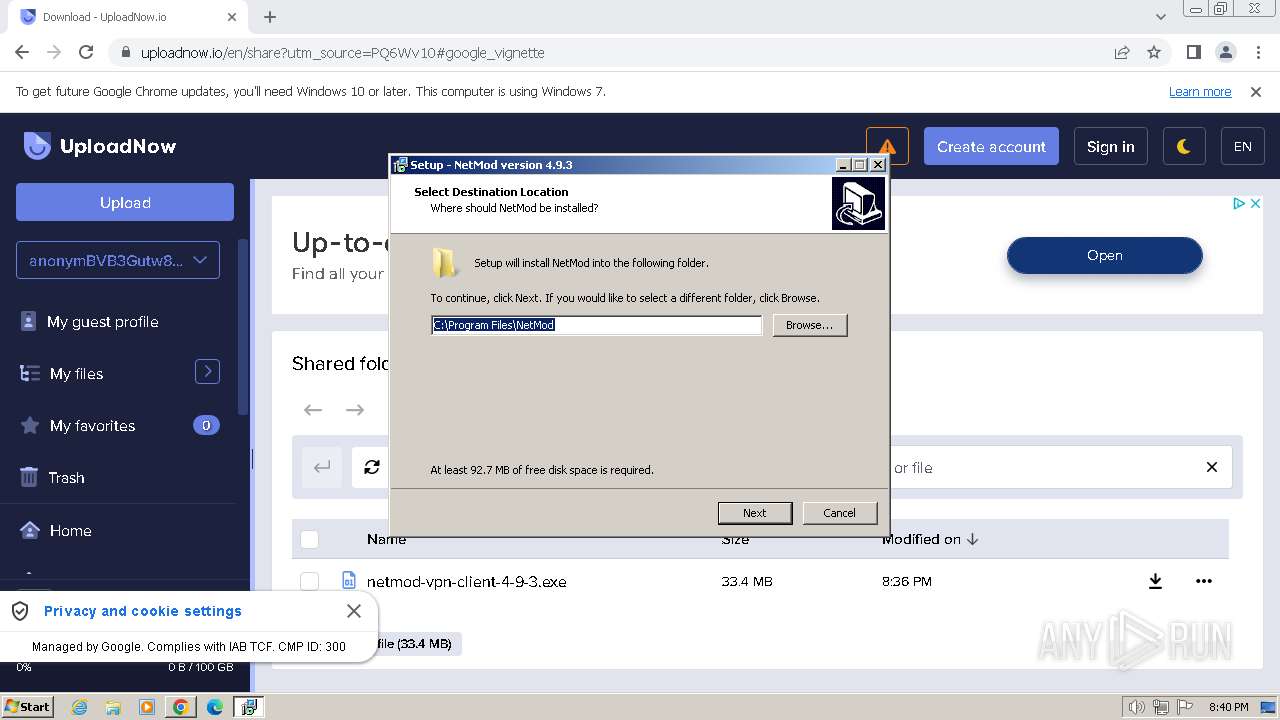
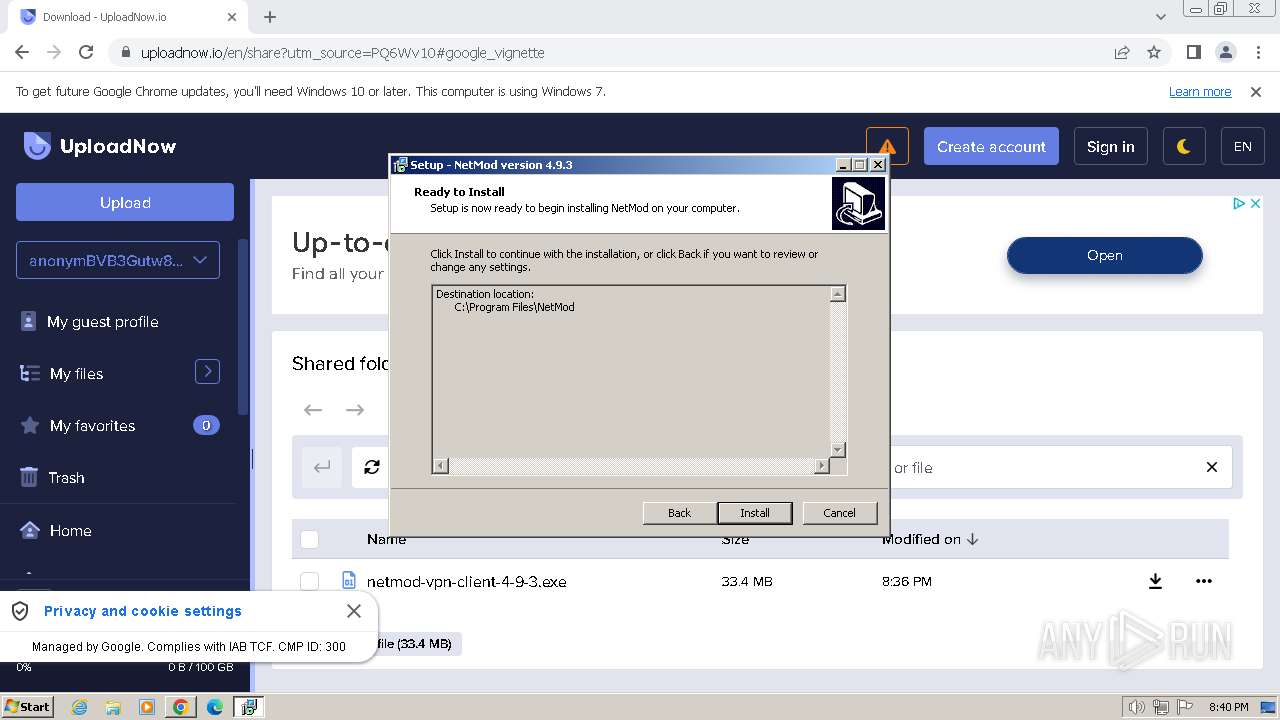
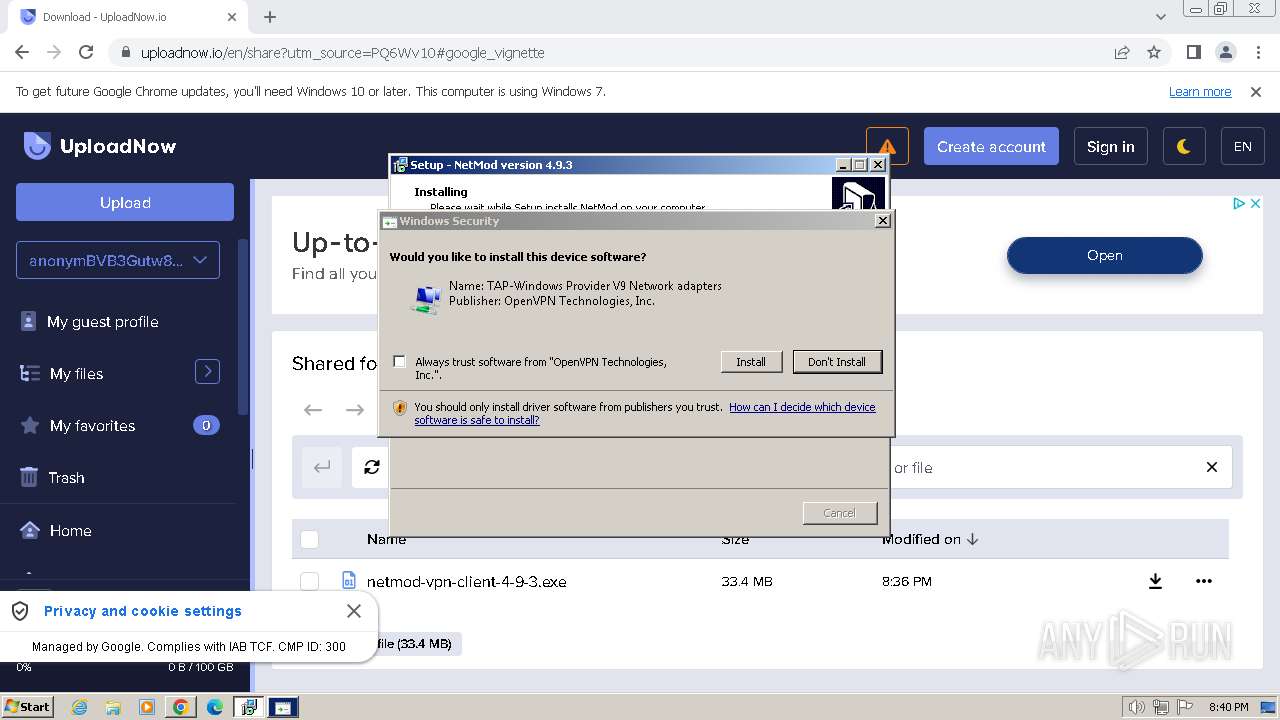
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2024, 20:39:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E6017F2423F1D7FE213B7CC7528B8214 |
| SHA1: | C08FA51AD8C86AA3C9020A1BFB0239413FCBACDA |
| SHA256: | EE165E552DA205FEBC6387F8E604126B7C8722CCBB080C7D2536118762ACDE48 |
| SSDEEP: | 3:N8ZEPL34n:2ZEPz4n |
MALICIOUS
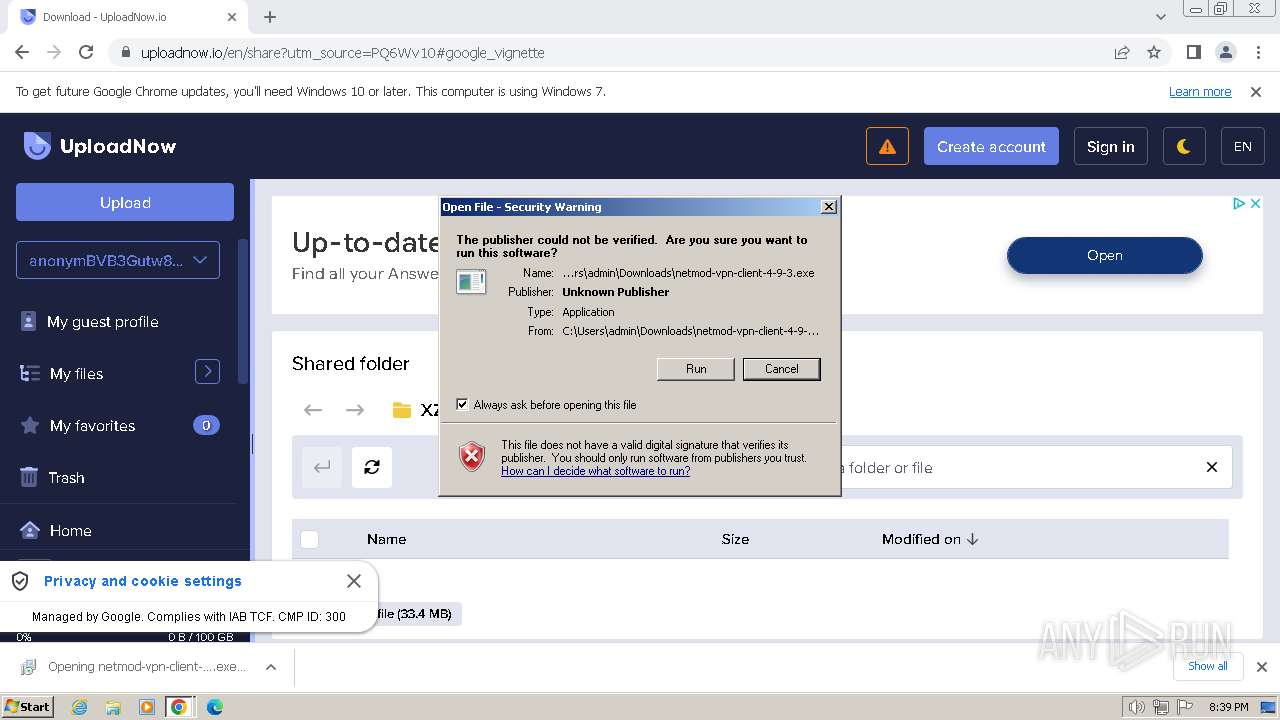
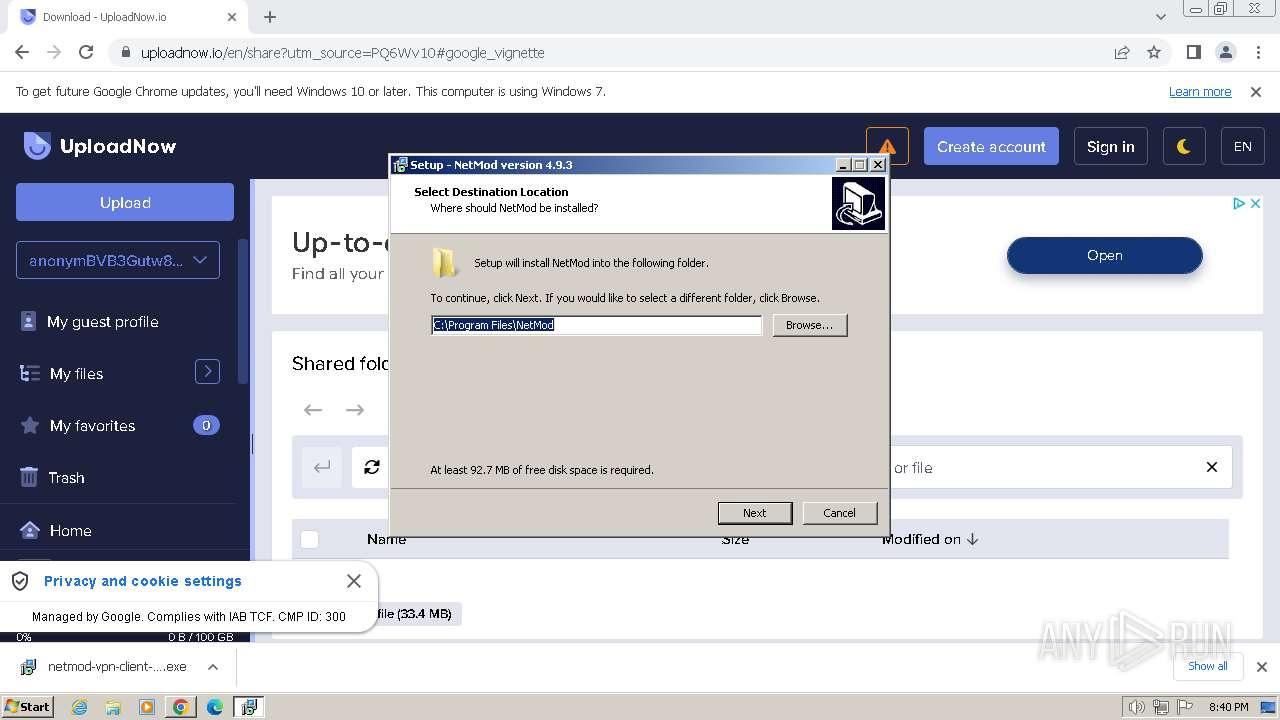
Drops the executable file immediately after the start
- netmod-vpn-client-4-9-3.exe (PID: 2268)
- netmod-vpn-client-4-9-3.exe (PID: 3588)
- tapinstall.exe (PID: 3896)
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
- drvinst.exe (PID: 2132)
Creates a writable file in the system directory
- drvinst.exe (PID: 2132)
SUSPICIOUS
Executable content was dropped or overwritten
- netmod-vpn-client-4-9-3.exe (PID: 2268)
- netmod-vpn-client-4-9-3.exe (PID: 3588)
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
- tapinstall.exe (PID: 3896)
- drvinst.exe (PID: 2132)
Reads the Windows owner or organization settings
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
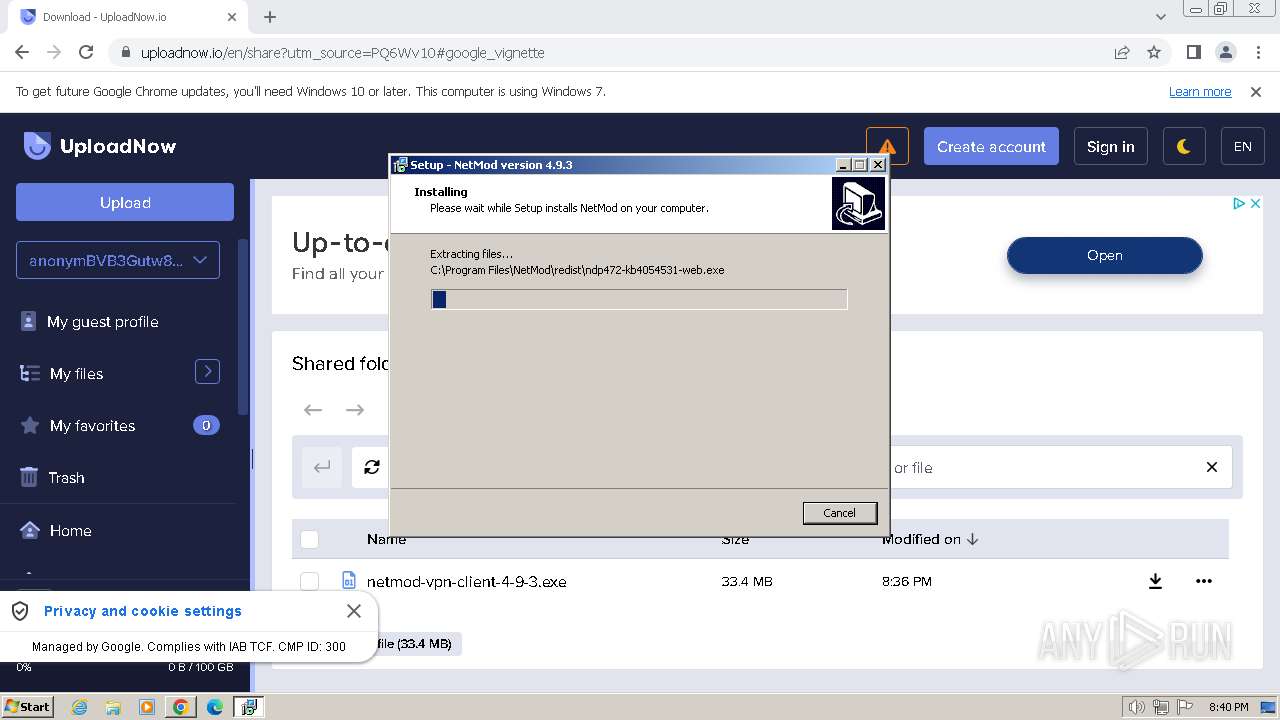
The process drops C-runtime libraries
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
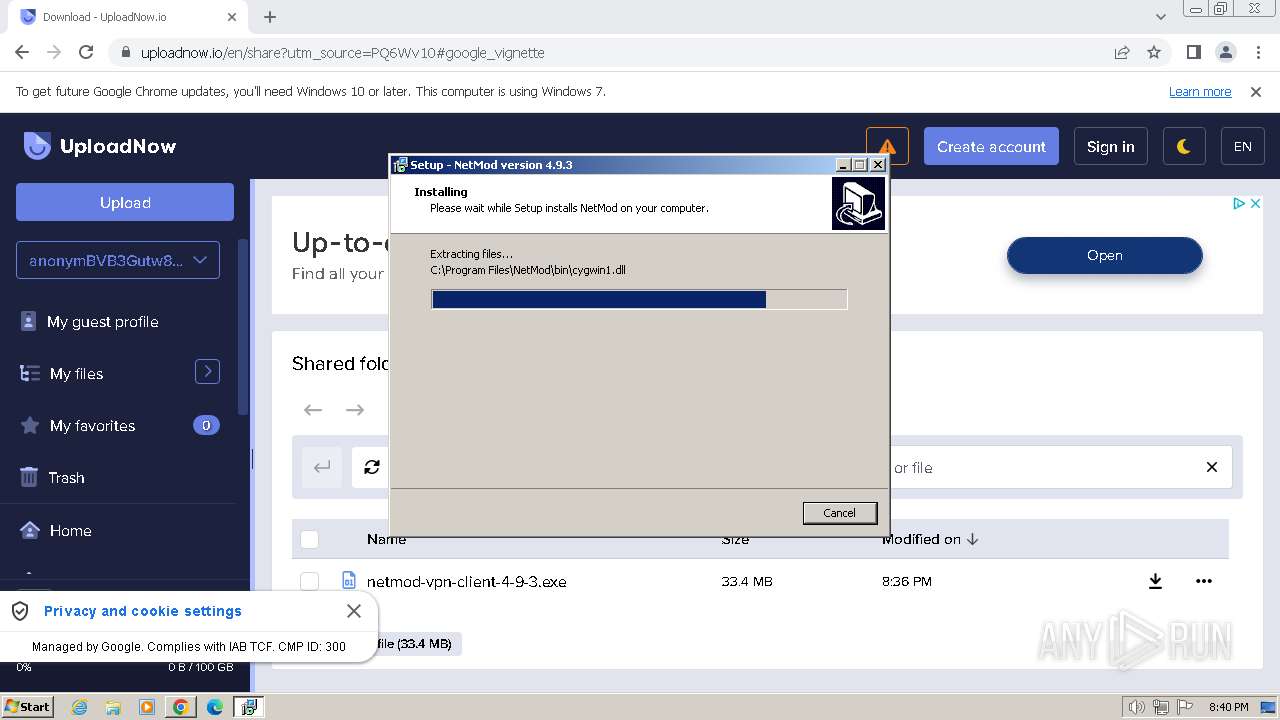
Drops a system driver (possible attempt to evade defenses)
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
- drvinst.exe (PID: 2132)
- tapinstall.exe (PID: 3896)
Checks Windows Trust Settings
- tapinstall.exe (PID: 3896)
- drvinst.exe (PID: 2132)
Reads security settings of Internet Explorer
- tapinstall.exe (PID: 3896)
Reads settings of System Certificates
- tapinstall.exe (PID: 3896)
- rundll32.exe (PID: 3008)
Process drops legitimate windows executable
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
Creates files in the driver directory
- drvinst.exe (PID: 2132)
INFO
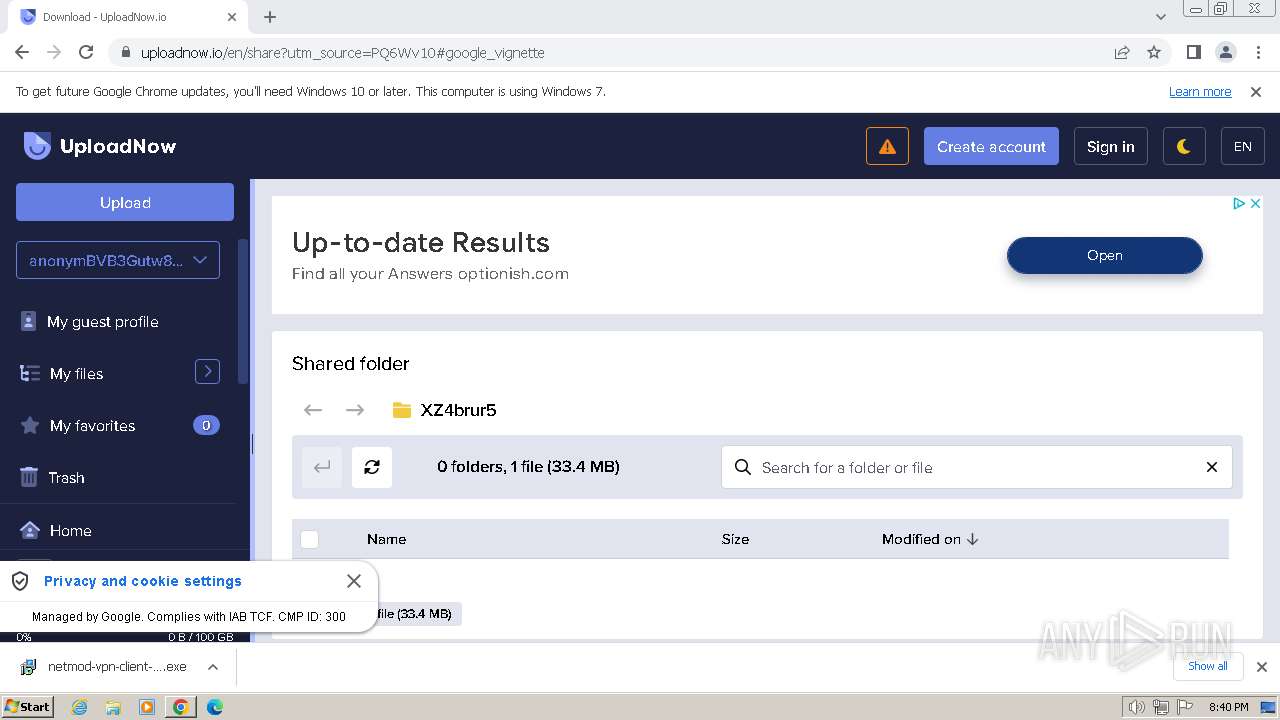
Drops the executable file immediately after the start
- chrome.exe (PID: 1432)
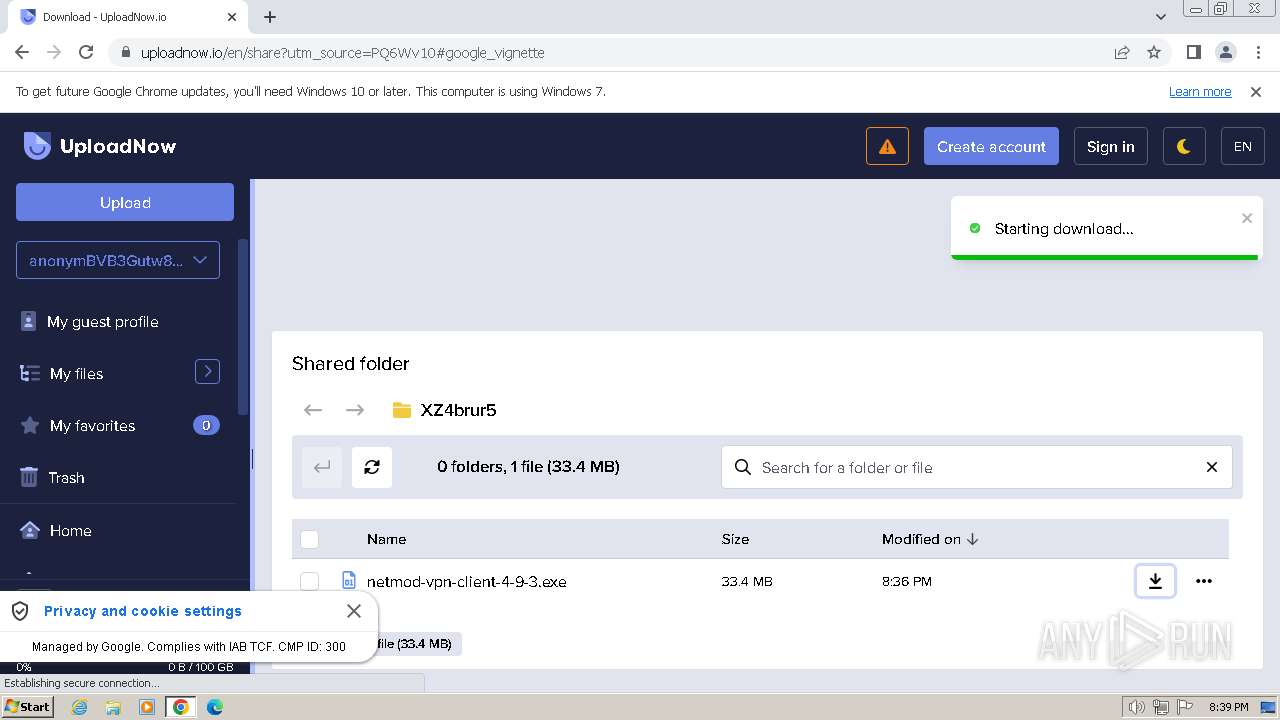
The process uses the downloaded file
- chrome.exe (PID: 1432)
- chrome.exe (PID: 3256)
Application launched itself
- chrome.exe (PID: 1432)
Checks supported languages
- netmod-vpn-client-4-9-3.exe (PID: 2268)
- netmod-vpn-client-4-9-3.tmp (PID: 3472)
- netmod-vpn-client-4-9-3.exe (PID: 3588)
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
- tapinstall.exe (PID: 3896)
- drvinst.exe (PID: 2132)
Reads the computer name
- netmod-vpn-client-4-9-3.tmp (PID: 3472)
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
- tapinstall.exe (PID: 3896)
- drvinst.exe (PID: 2132)
Create files in a temporary directory
- netmod-vpn-client-4-9-3.exe (PID: 2268)
- netmod-vpn-client-4-9-3.exe (PID: 3588)
- tapinstall.exe (PID: 3896)
Executable content was dropped or overwritten
- chrome.exe (PID: 1432)
Creates files in the program directory
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
Reads the software policy settings
- tapinstall.exe (PID: 3896)
- drvinst.exe (PID: 2132)
- rundll32.exe (PID: 3008)
Creates a software uninstall entry
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
Reads the machine GUID from the registry
- netmod-vpn-client-4-9-3.tmp (PID: 3592)
- tapinstall.exe (PID: 3896)
- drvinst.exe (PID: 2132)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
28
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3128 --field-trial-handle=1156,i,15837202369721898156,630475010152115734,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3756 --field-trial-handle=1156,i,15837202369721898156,630475010152115734,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://uploadnow.io/f/PQ6Wv10" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3904 --field-trial-handle=1156,i,15837202369721898156,630475010152115734,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2944 --field-trial-handle=1156,i,15837202369721898156,630475010152115734,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1348 --field-trial-handle=1156,i,15837202369721898156,630475010152115734,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2132 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{466a6c35-0ab0-275b-0577-73503c8f6322}\oemvista.inf" "0" "6d14a44ff" "000005D0" "WinSta0\Default" "000003BC" "208" "c:\program files\netmod\bin\tap-driver\x86" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2268 | "C:\Users\admin\Downloads\netmod-vpn-client-4-9-3.exe" | C:\Users\admin\Downloads\netmod-vpn-client-4-9-3.exe | chrome.exe | ||||||||||||
User: admin Company: Henry Gustian Integrity Level: MEDIUM Description: NetMod Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2004 --field-trial-handle=1156,i,15837202369721898156,630475010152115734,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1368 --field-trial-handle=1156,i,15837202369721898156,630475010152115734,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
25 215
Read events
25 029
Write events
177
Delete events
9
Modification events
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
181
Suspicious files
28
Text files
31
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF180923.TMP | — | |
MD5:— | SHA256:— | |||
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF180a9a.TMP | text | |
MD5:C383FD120B14BB0E98E99C1BCC9B43F6 | SHA256:56A3A5EACBD28BEE1CF8C1D0052321A5C27EE858BEF7B2FA1DE20806A0823CC1 | |||
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF181160.TMP | — | |
MD5:— | SHA256:— | |||
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
| 1432 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
43
DNS requests
54
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2304 | chrome.exe | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1432 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2304 | chrome.exe | 172.67.74.9:443 | uploadnow.io | CLOUDFLARENET | US | unknown |
2304 | chrome.exe | 142.250.186.98:443 | pagead2.googlesyndication.com | GOOGLE | US | unknown |
2304 | chrome.exe | 172.217.16.130:443 | googleads.g.doubleclick.net | GOOGLE | US | whitelisted |
2304 | chrome.exe | 142.250.185.168:443 | www.googletagmanager.com | GOOGLE | US | unknown |
2304 | chrome.exe | 172.217.16.206:443 | fundingchoicesmessages.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
uploadnow.io |
| unknown |
pagead2.googlesyndication.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
identitytoolkit.googleapis.com |
| whitelisted |
plausible.io |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |