| File name: | GoogleChrome.zip |
| Full analysis: | https://app.any.run/tasks/fba83d72-9258-41c5-81d8-95729f822df8 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 02:07:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | F5EDE370FE4D82B1A9AE28575929FE38 |
| SHA1: | C6C4DDD5641774D0B937C911452E8C5BFBBBD502 |
| SHA256: | EE0A4DBC127B93572D7416405883135EE5719BB3BCC71DF334891514DF03E29C |
| SSDEEP: | 24576:MxEtYOwoidoy3SmTP6M1A+ug0Rpw/zO5K1K:MxEtYOwoidoy3SmTP6M1A+ug0Rpw/zOv |
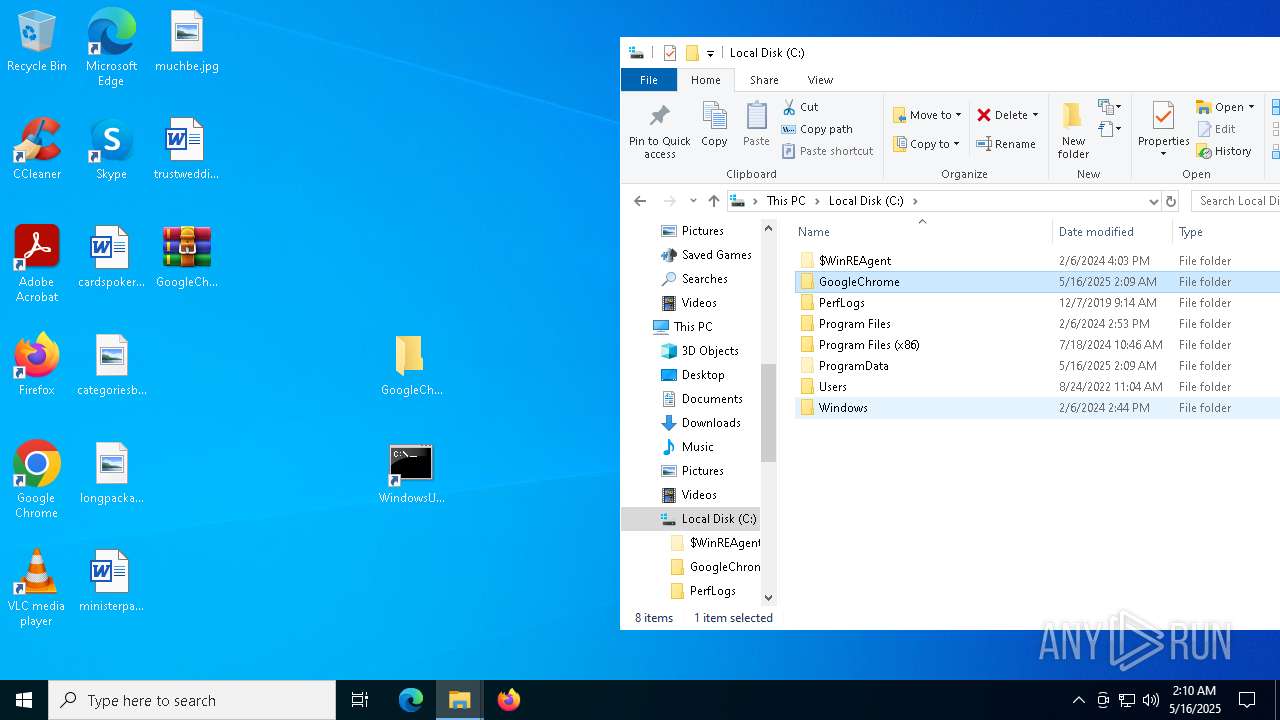
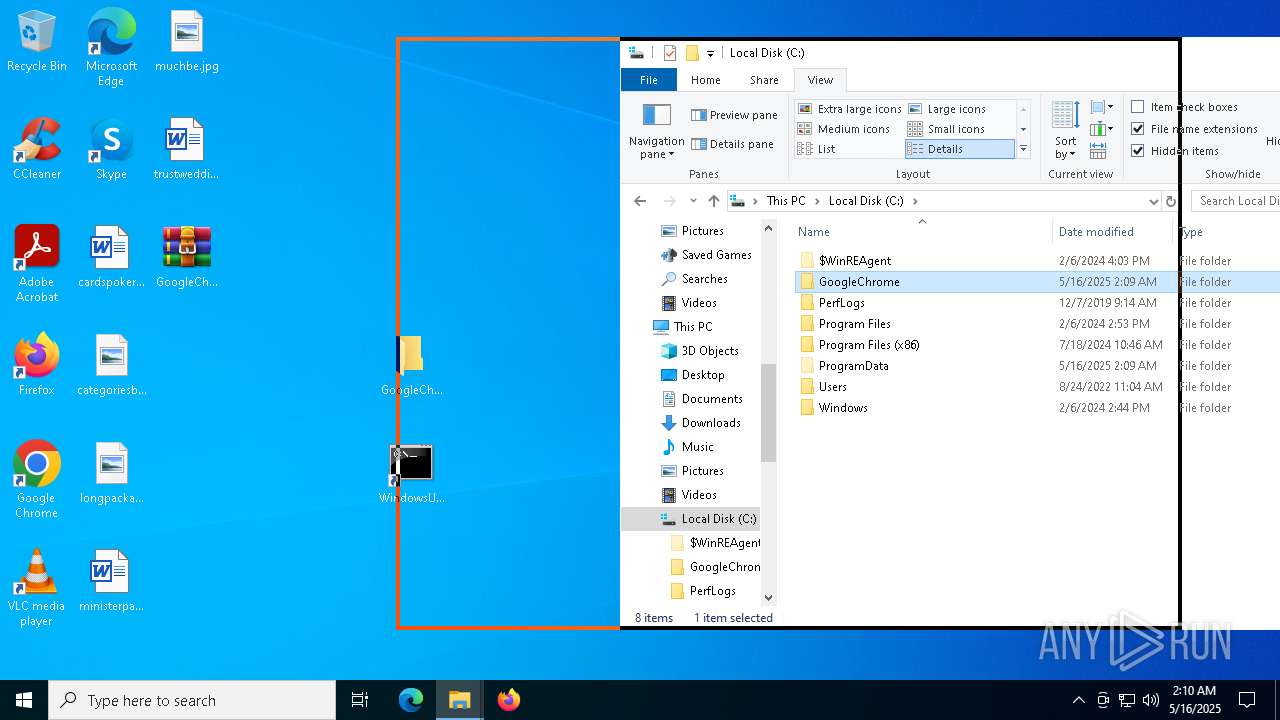
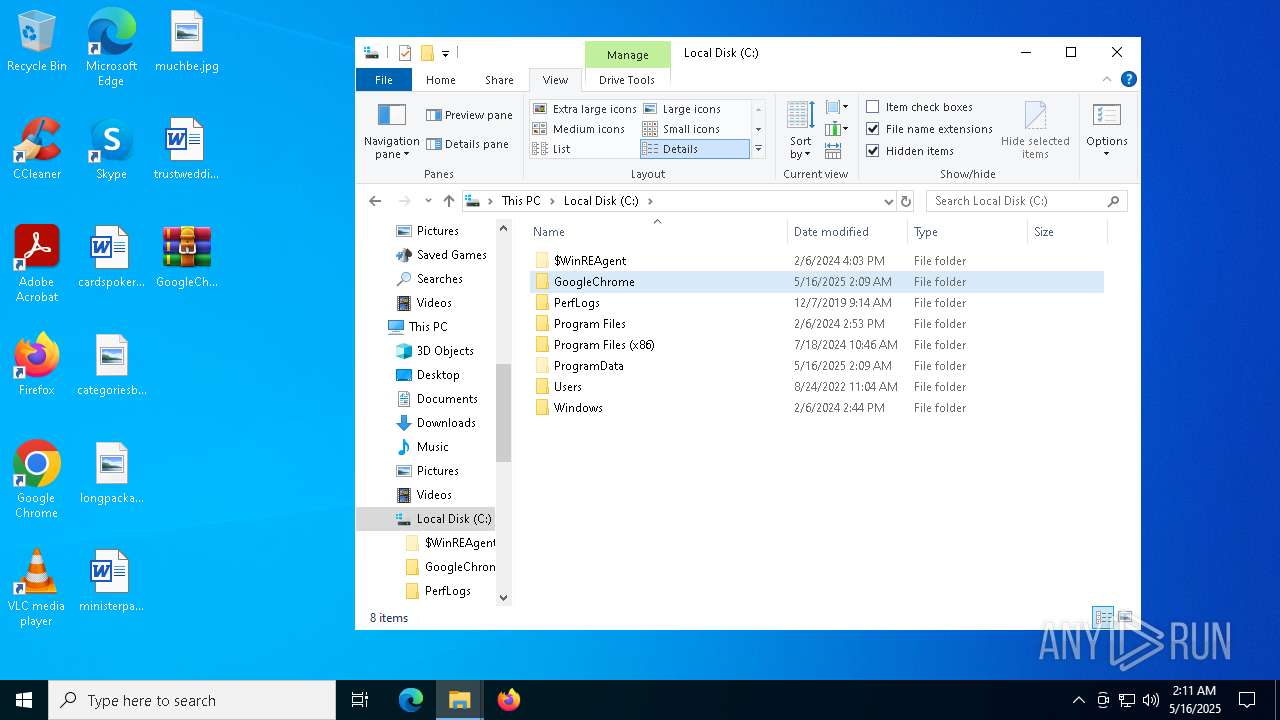
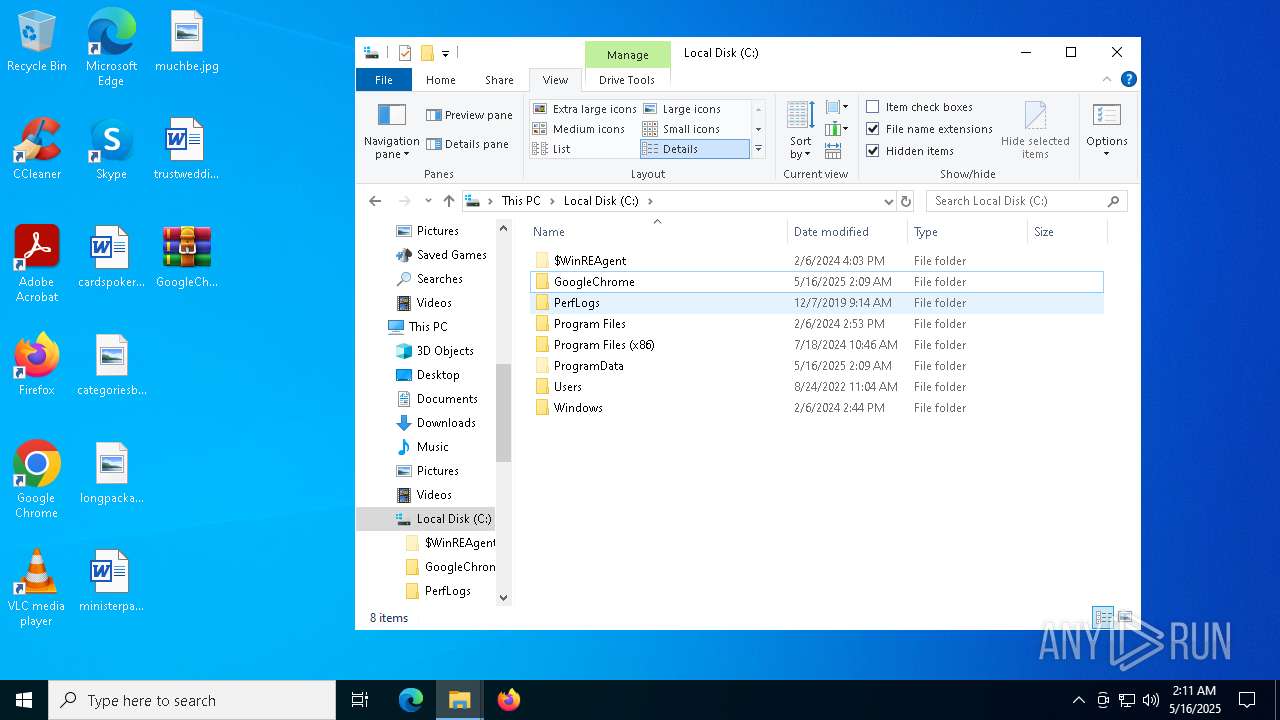
MALICIOUS
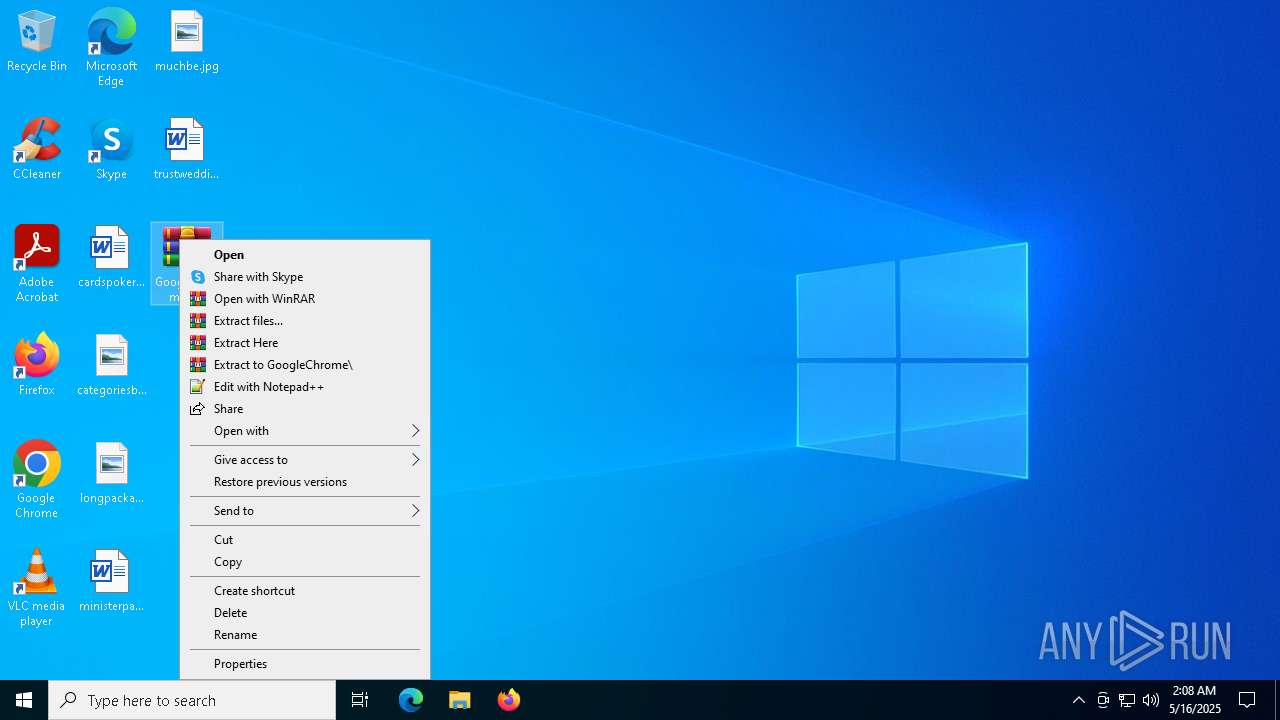
Generic archive extractor
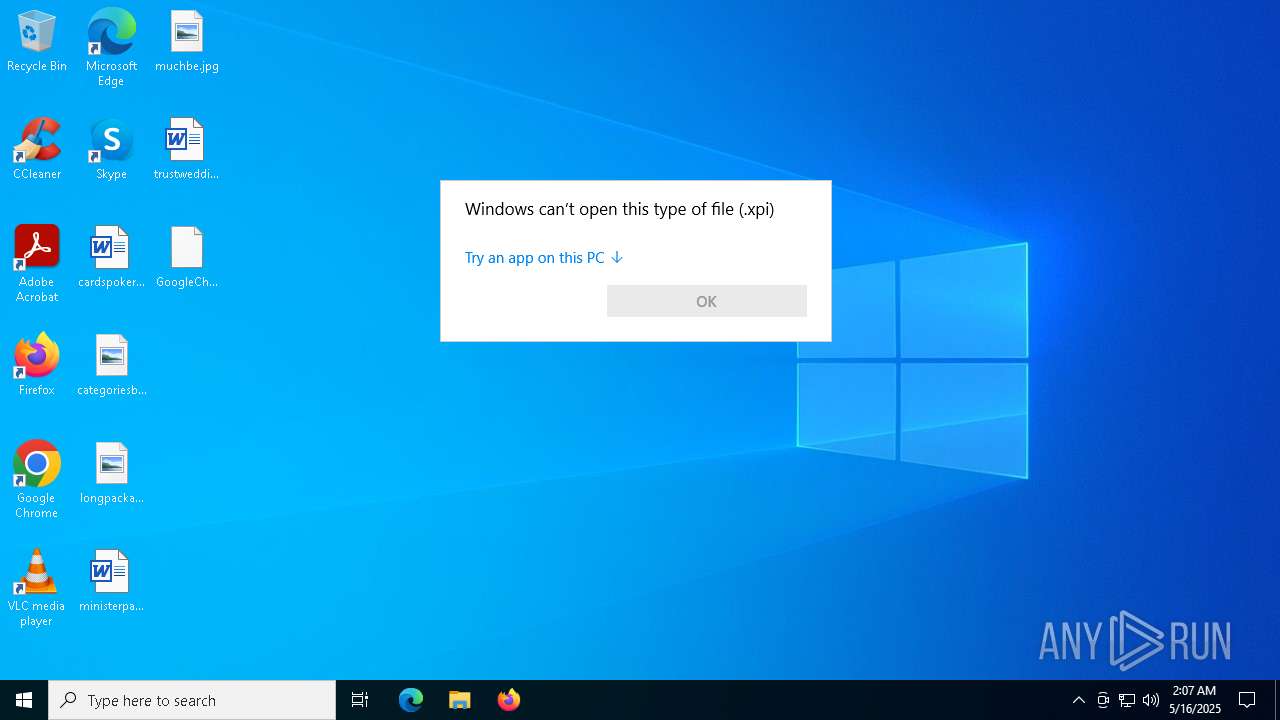
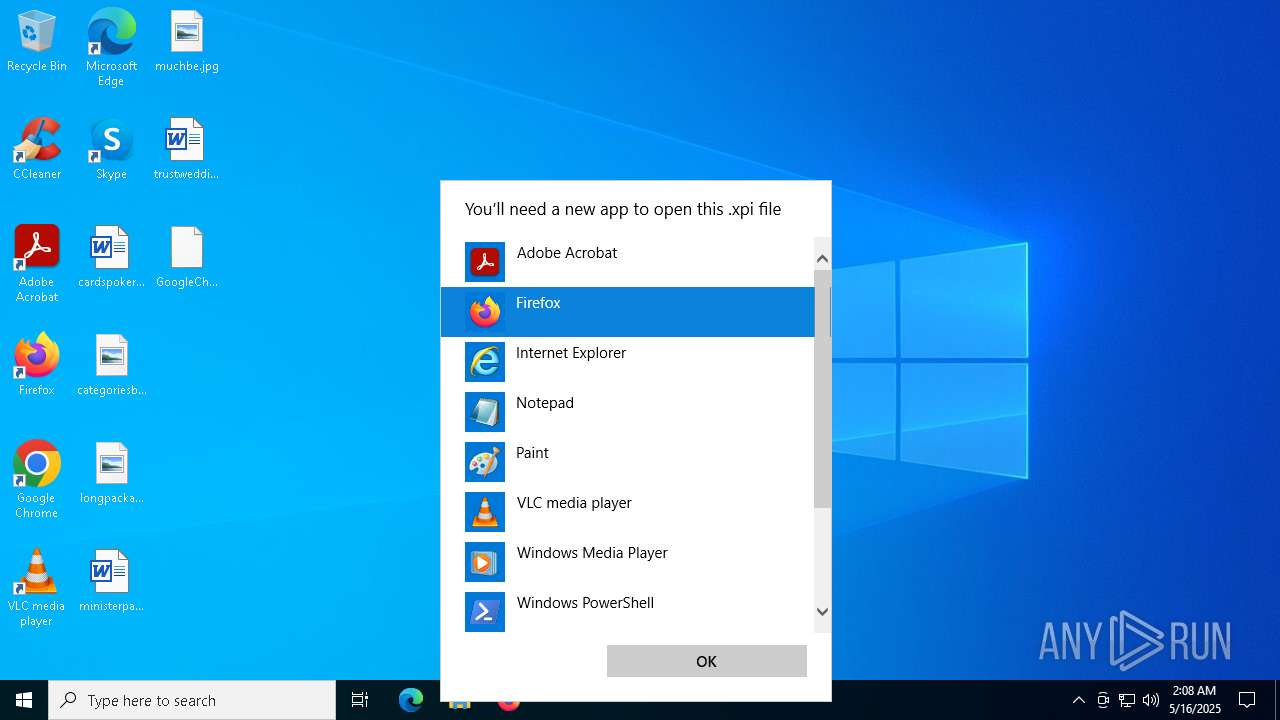
- OpenWith.exe (PID: 6708)
SUSPICIOUS
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 5680)
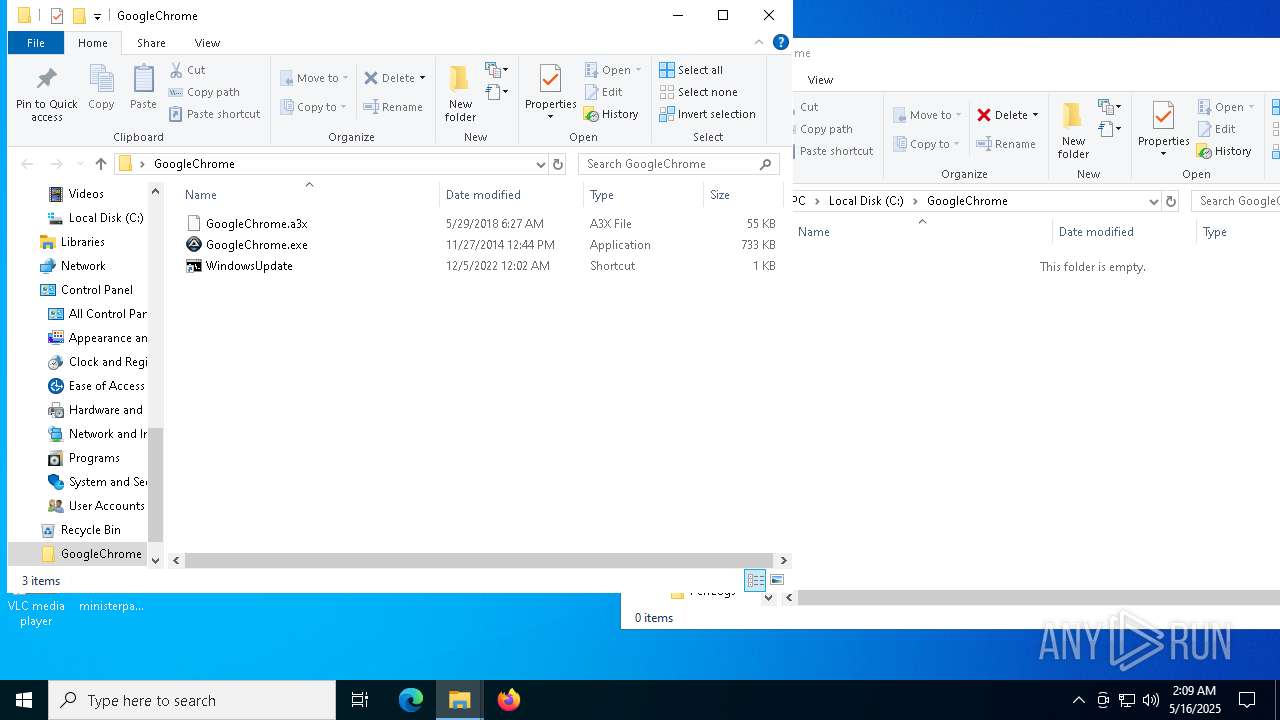
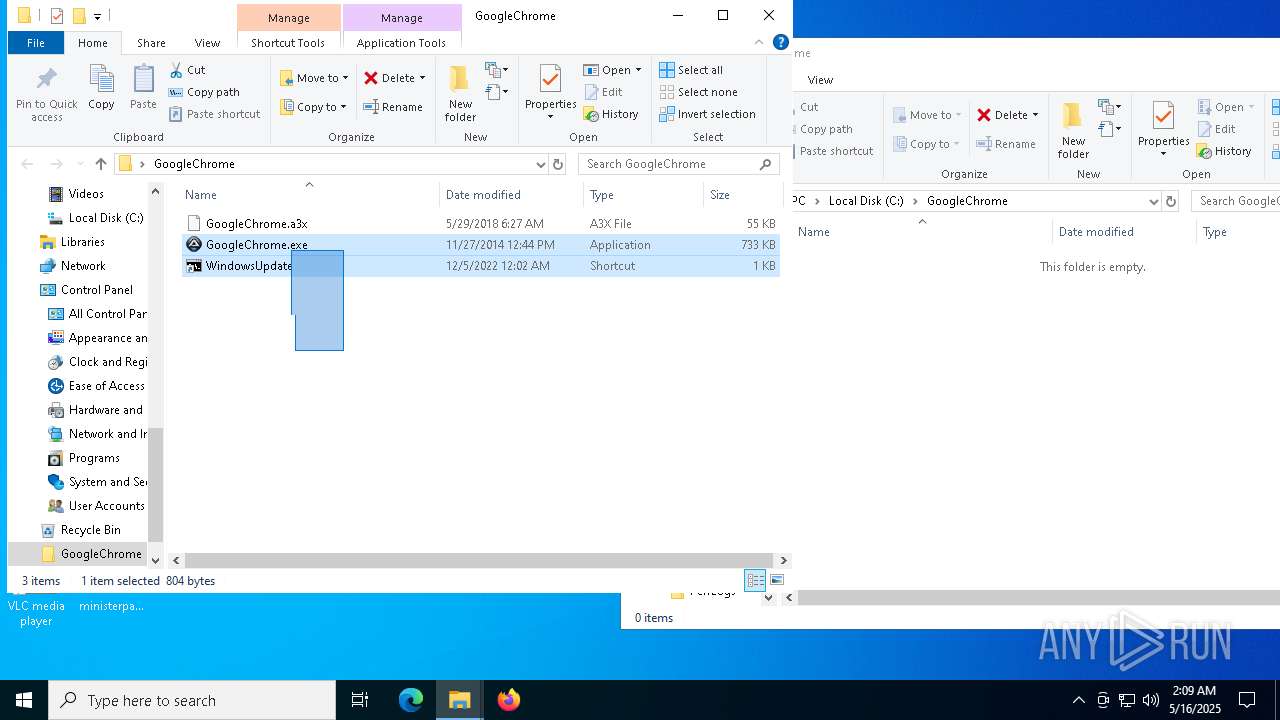
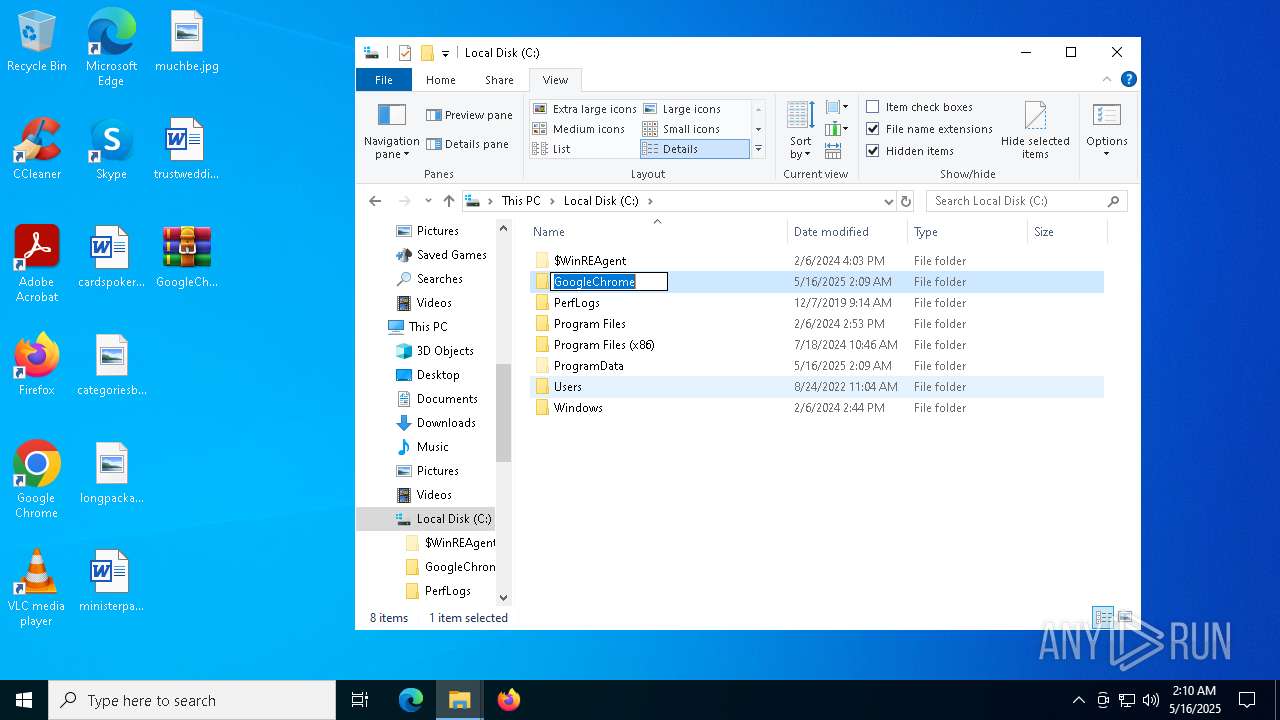
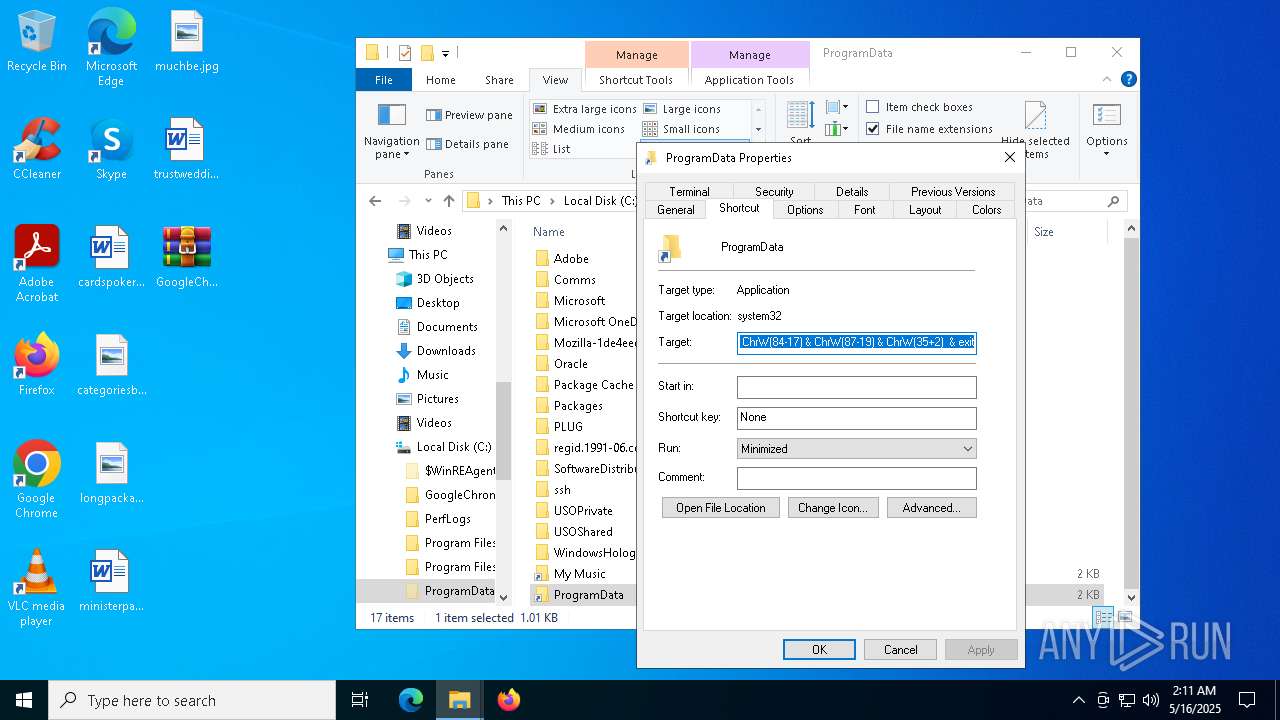
Starts the AutoIt3 executable file
- cmd.exe (PID: 4436)
Uses NETSH.EXE to add a firewall rule or allowed programs
- GoogleChrome.exe (PID: 7308)
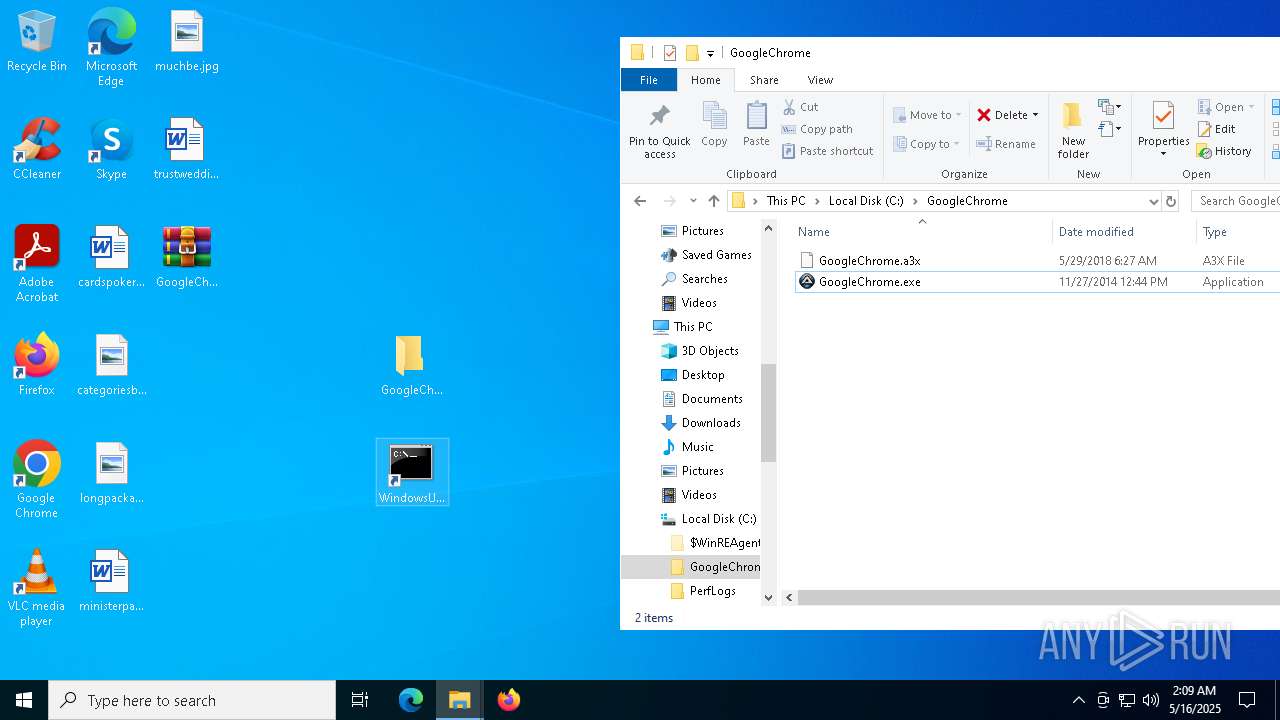
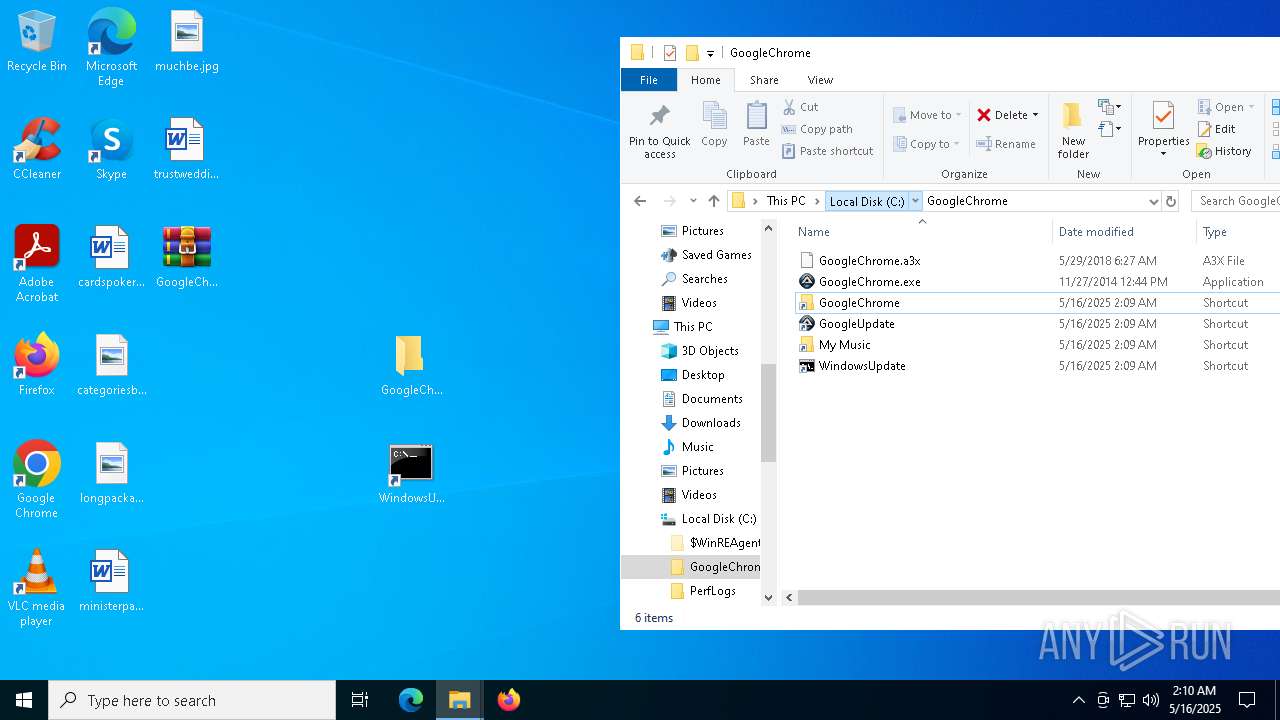
Executable content was dropped or overwritten
- GoogleChrome.exe (PID: 7308)
There is functionality for taking screenshot (YARA)
- GoogleChrome.exe (PID: 7308)
Connects to unusual port
- GoogleChrome.exe (PID: 7308)
INFO
Reads the software policy settings
- slui.exe (PID: 7240)
The sample compiled with english language support
- WinRAR.exe (PID: 7936)
- GoogleChrome.exe (PID: 7308)
Executable content was dropped or overwritten
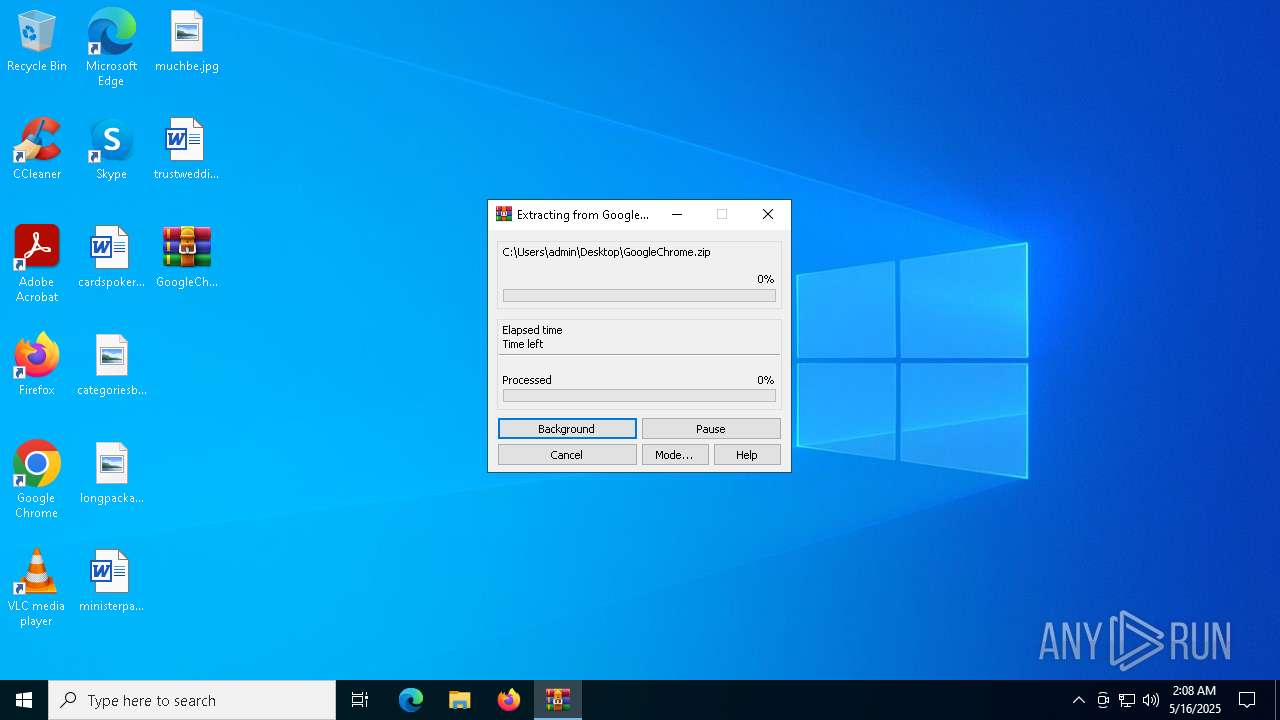
- WinRAR.exe (PID: 7936)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6708)
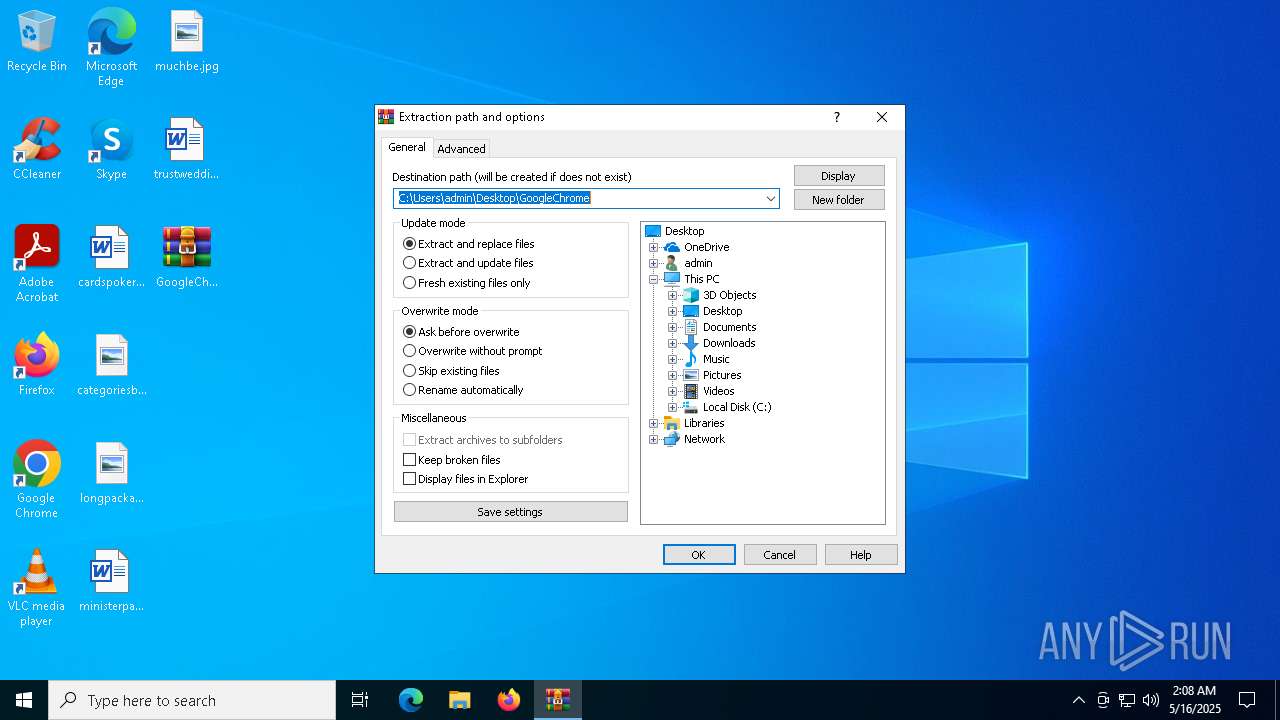
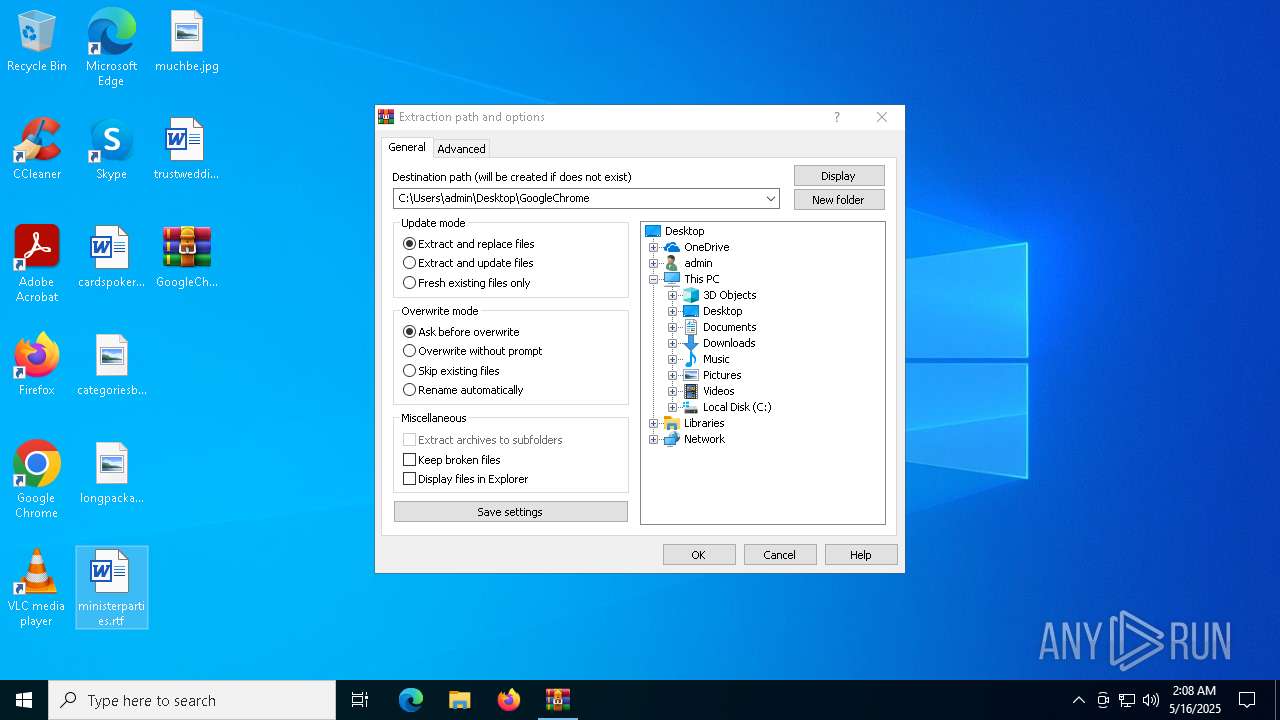
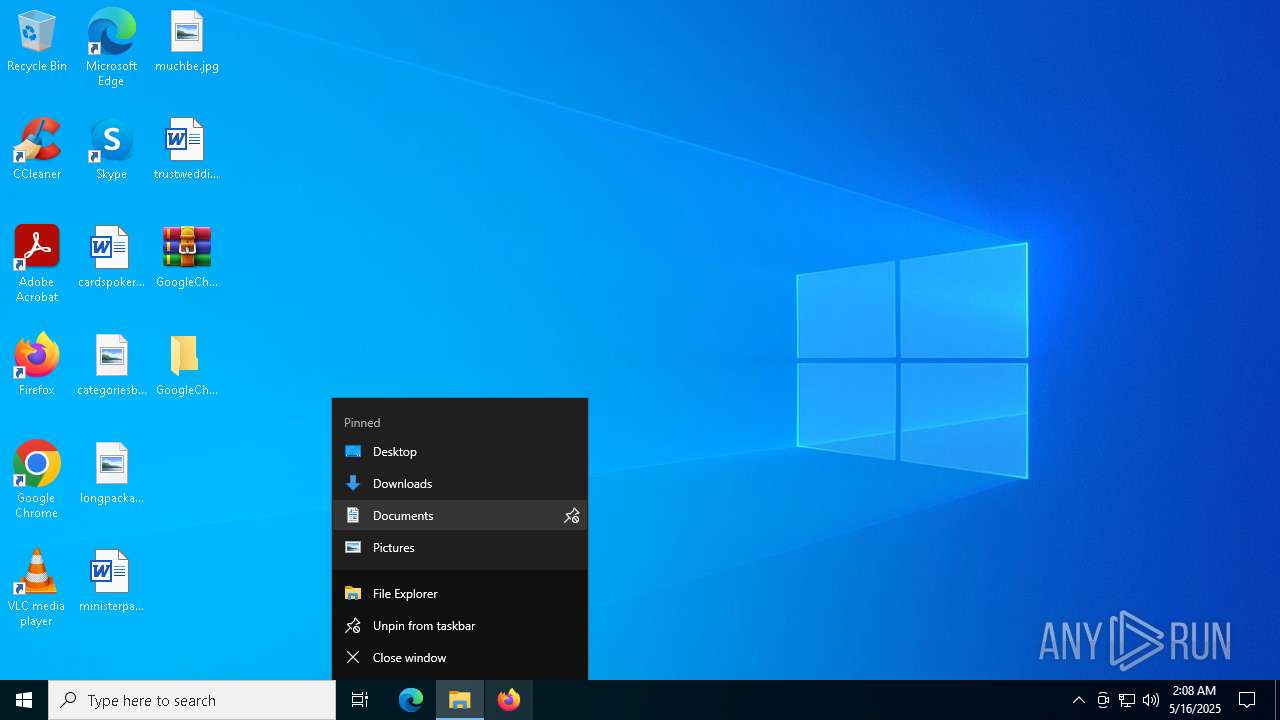
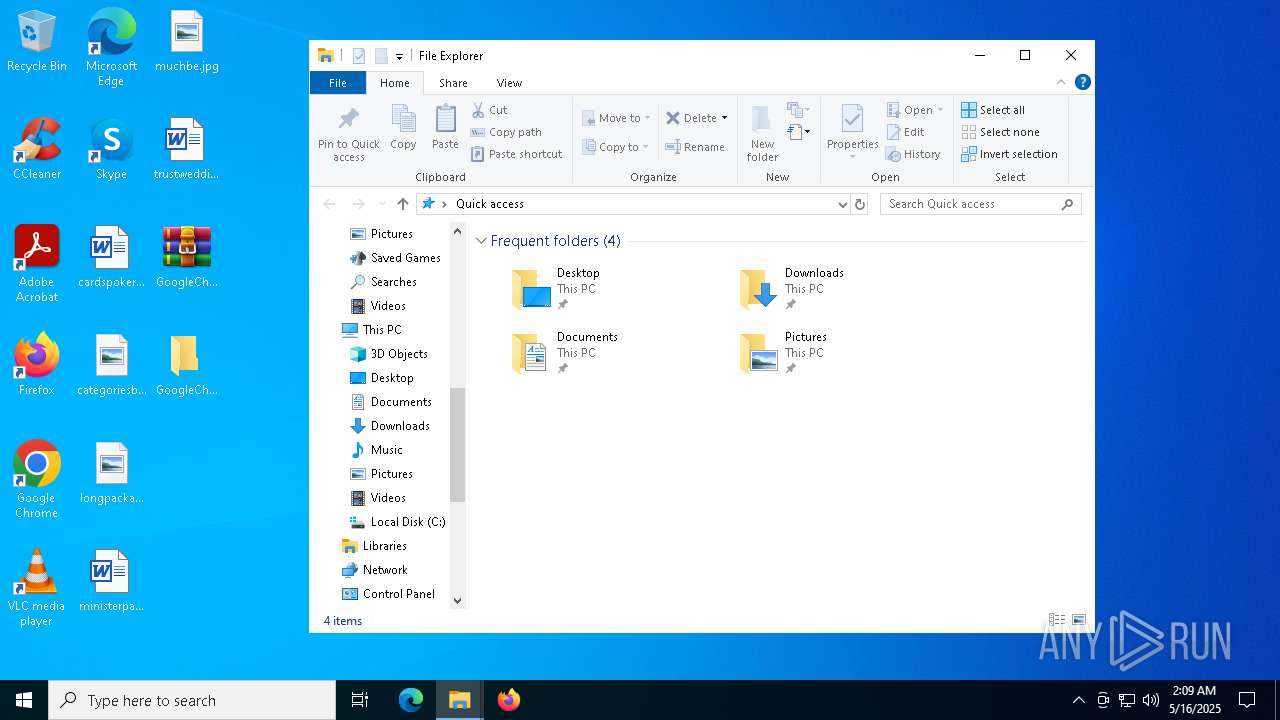
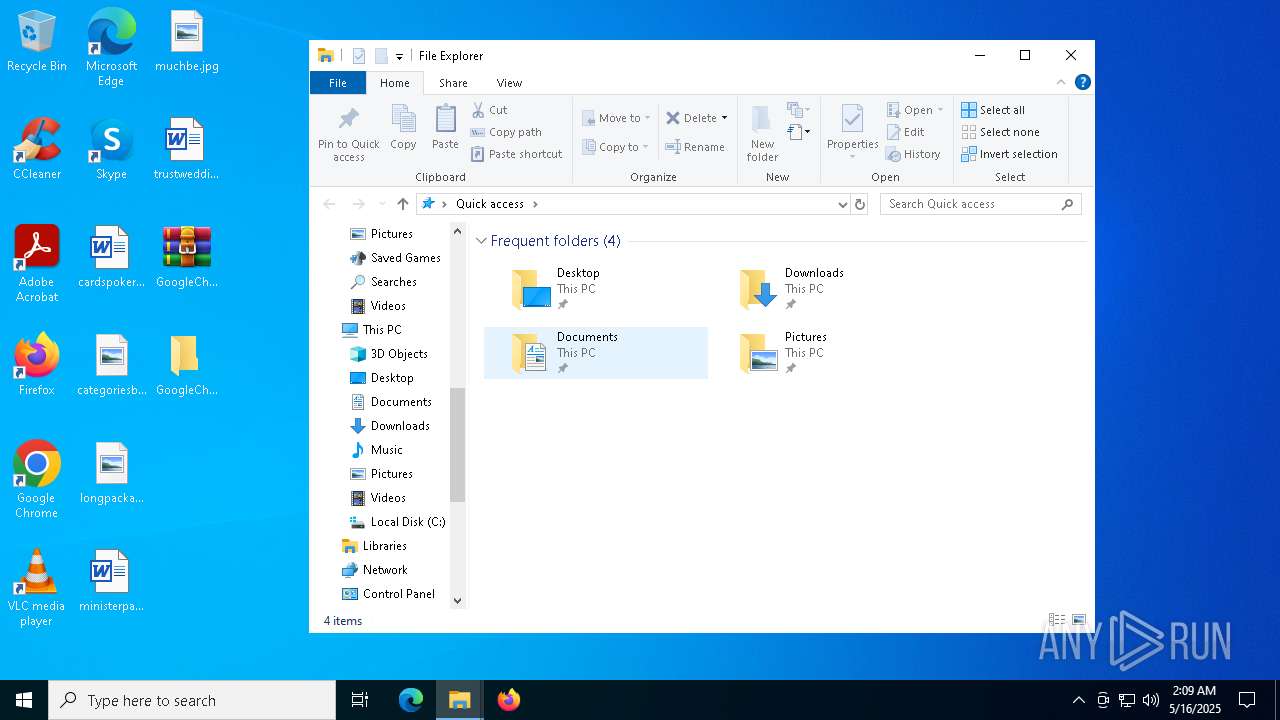
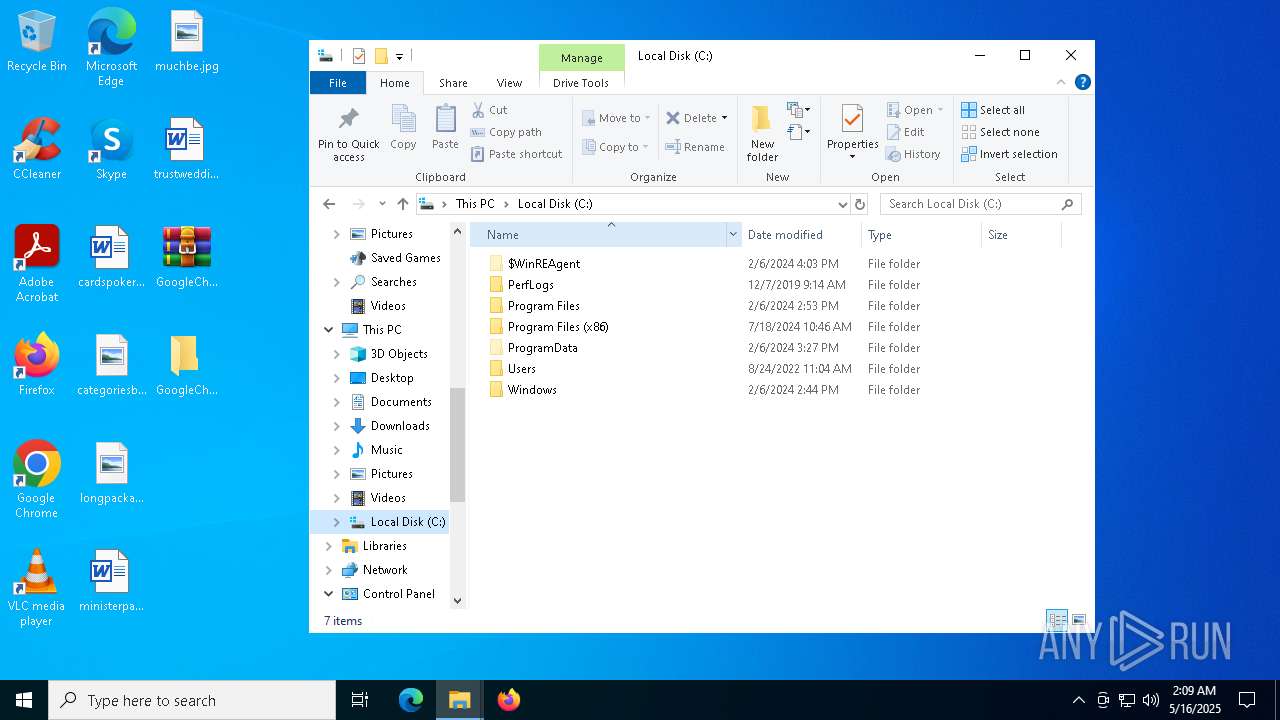
Manual execution by a user
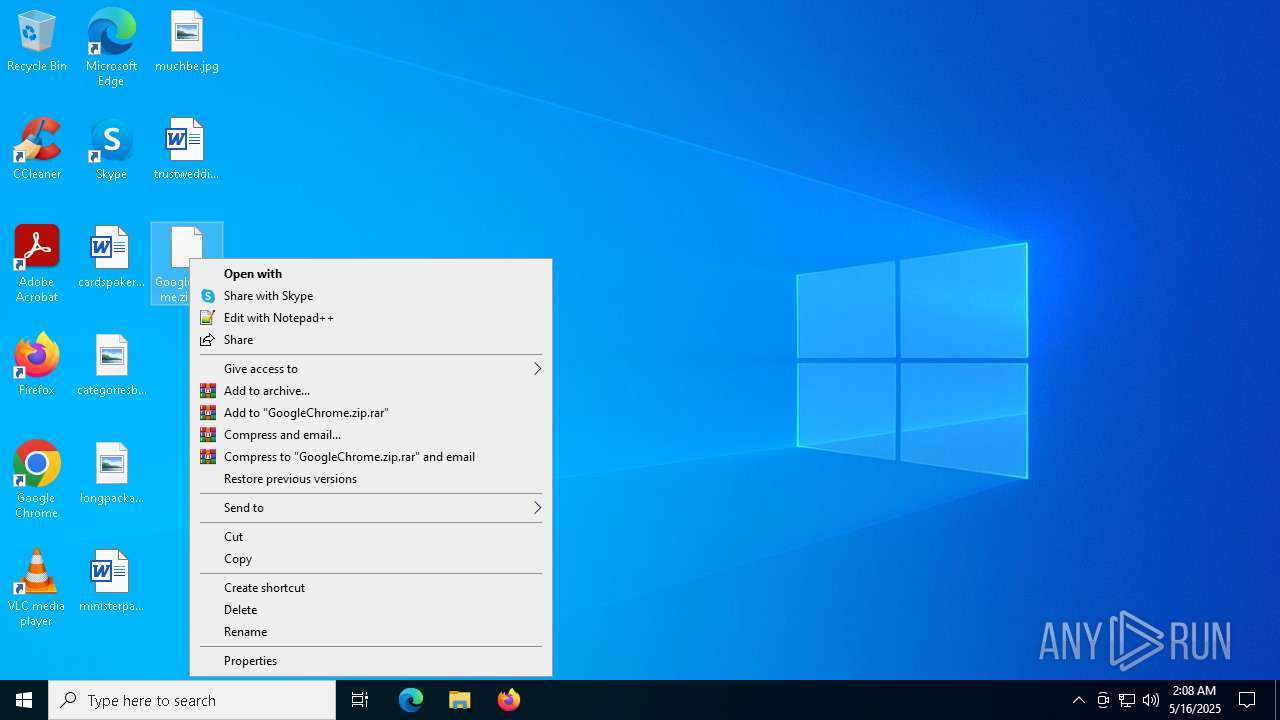
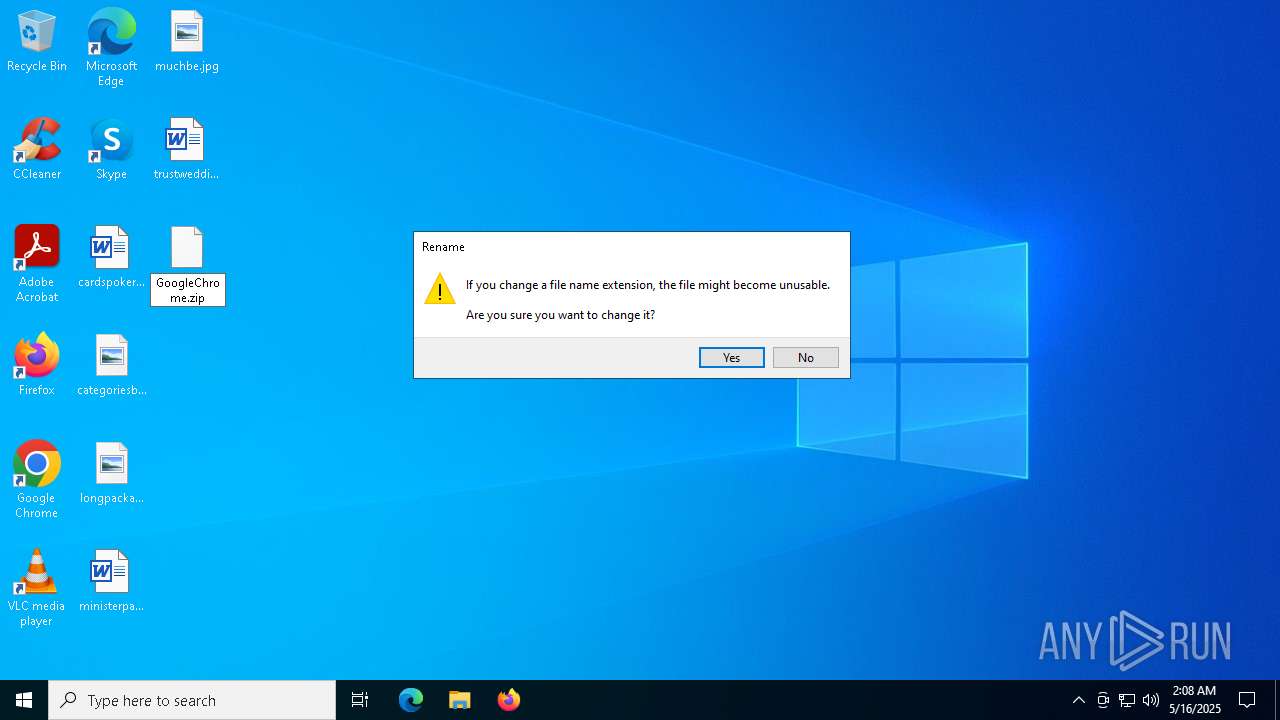
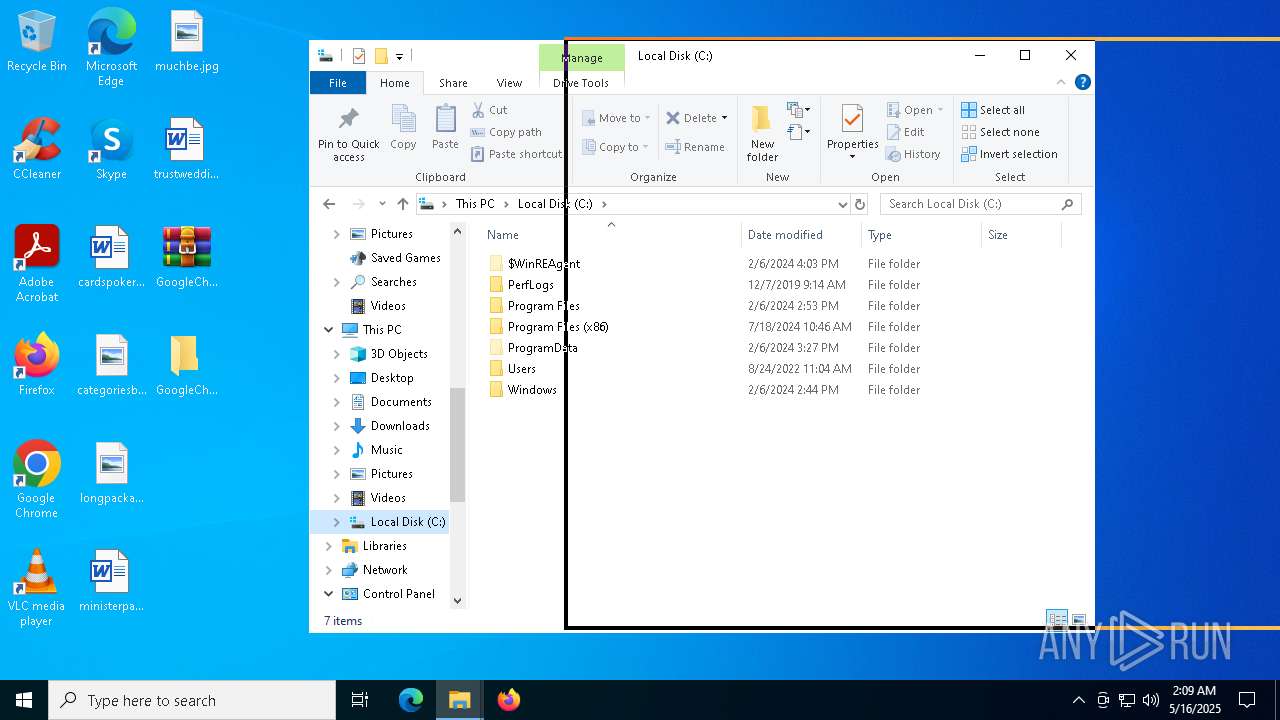
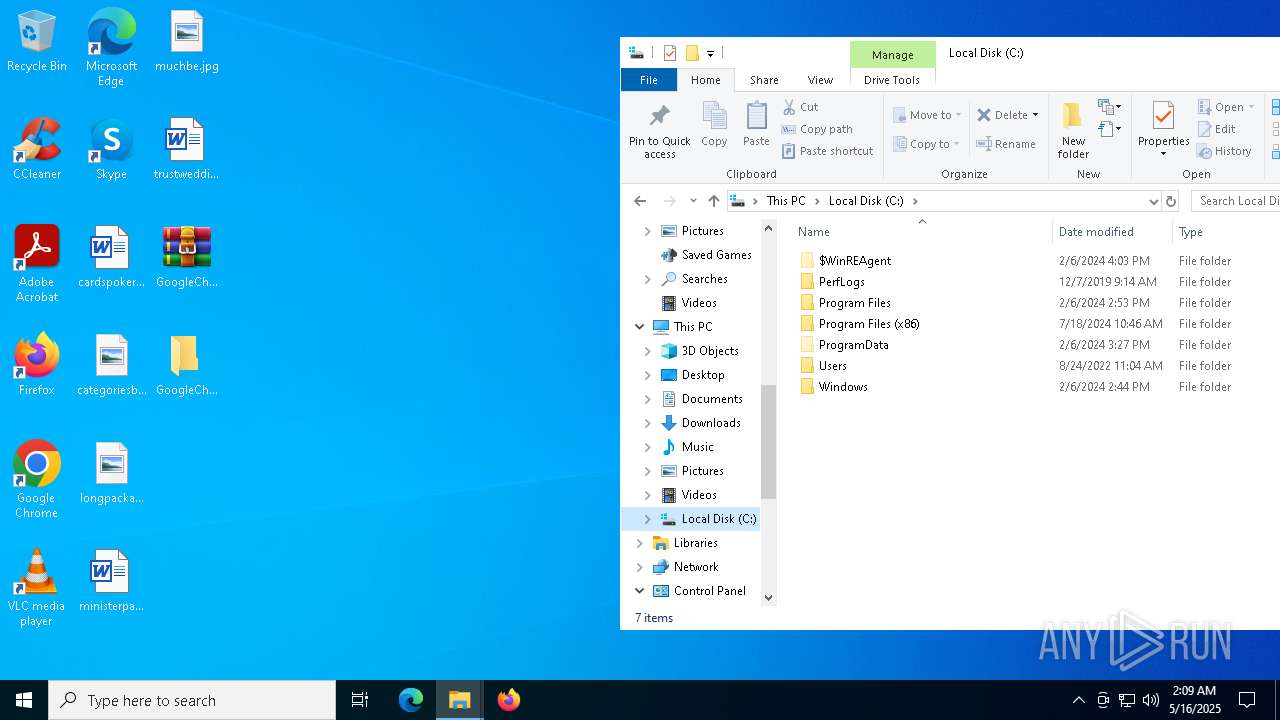
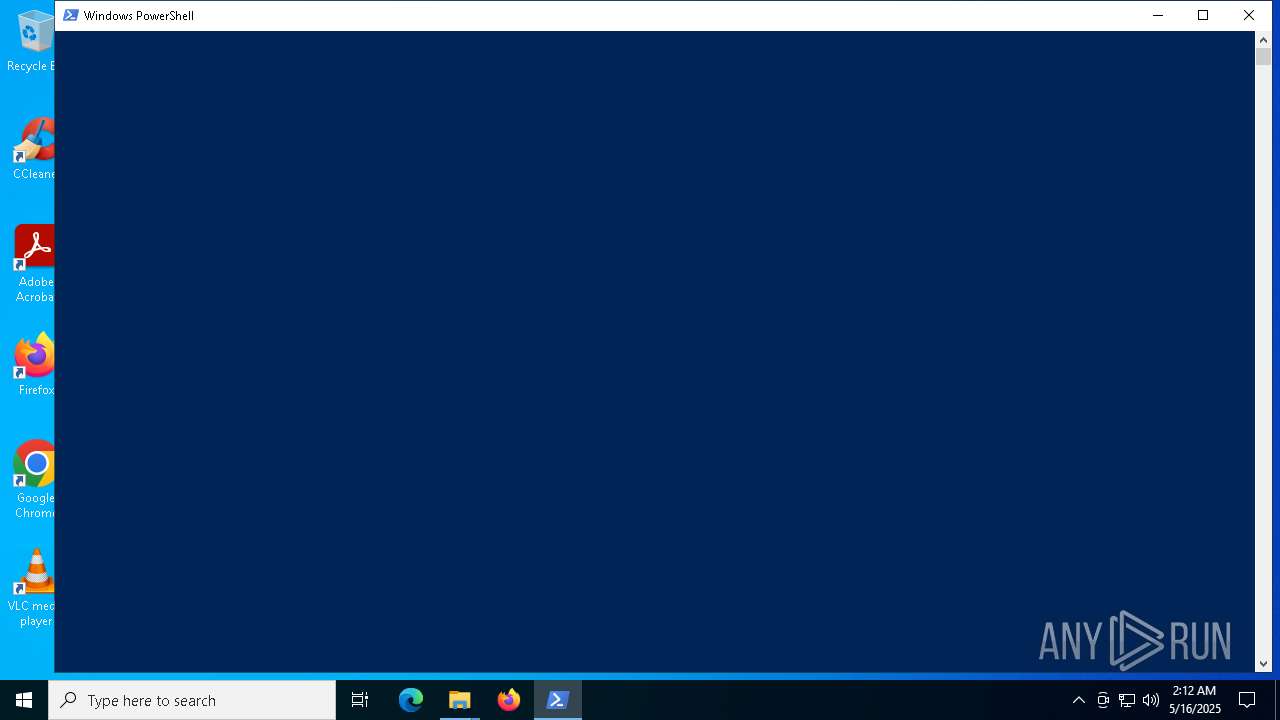
- WinRAR.exe (PID: 7936)
- cmd.exe (PID: 4436)
- powershell.exe (PID: 968)
Reads the computer name
- ShellExperienceHost.exe (PID: 5680)
Checks supported languages
- ShellExperienceHost.exe (PID: 5680)
The process uses AutoIt
- GoogleChrome.exe (PID: 7308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:16 10:06:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
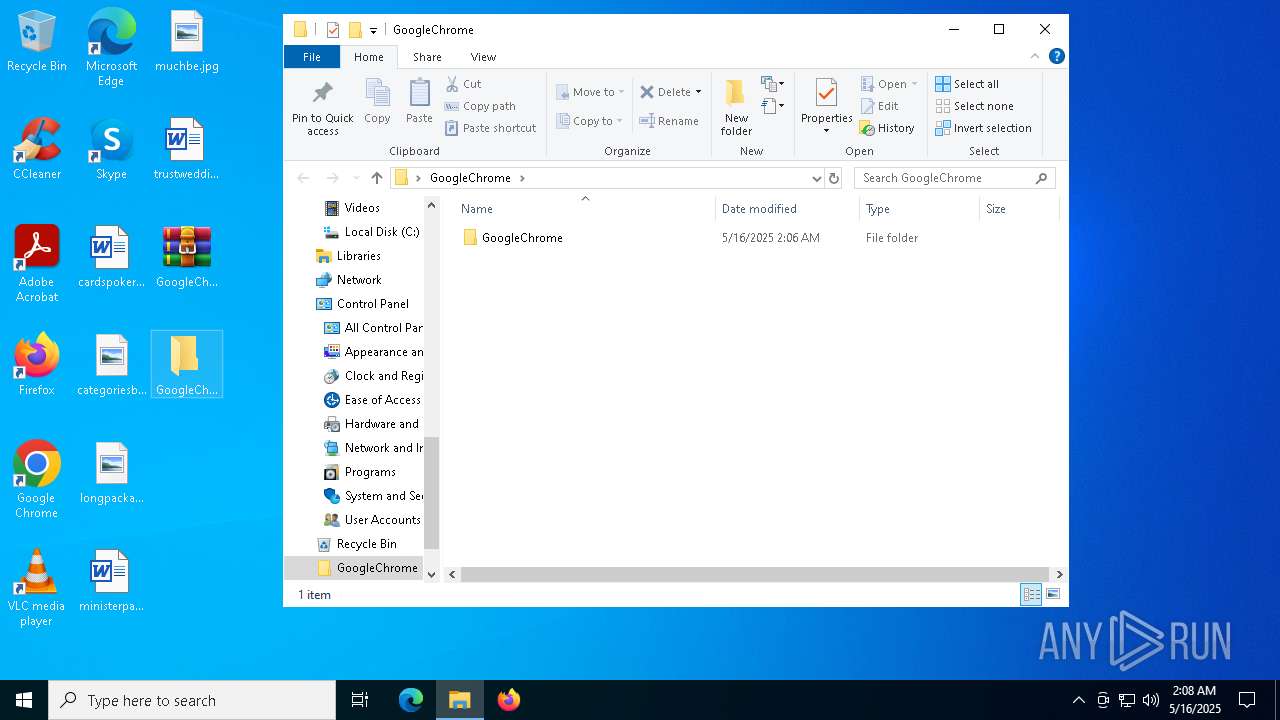
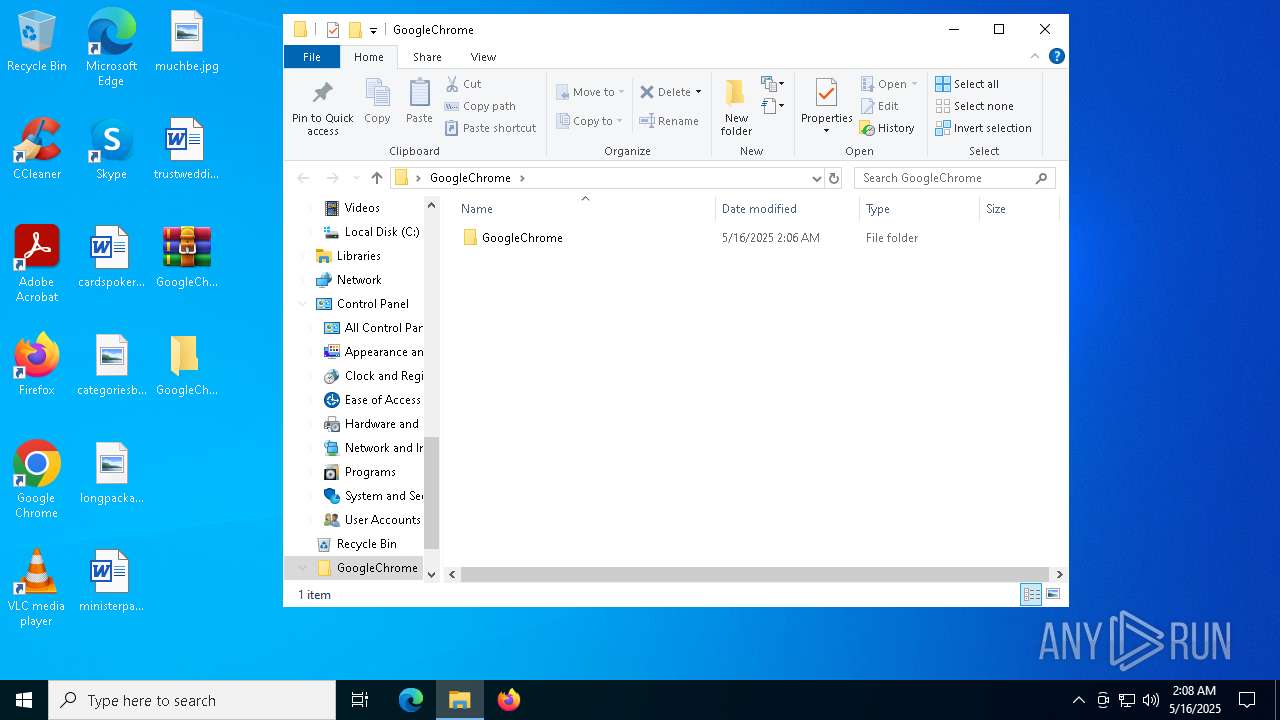
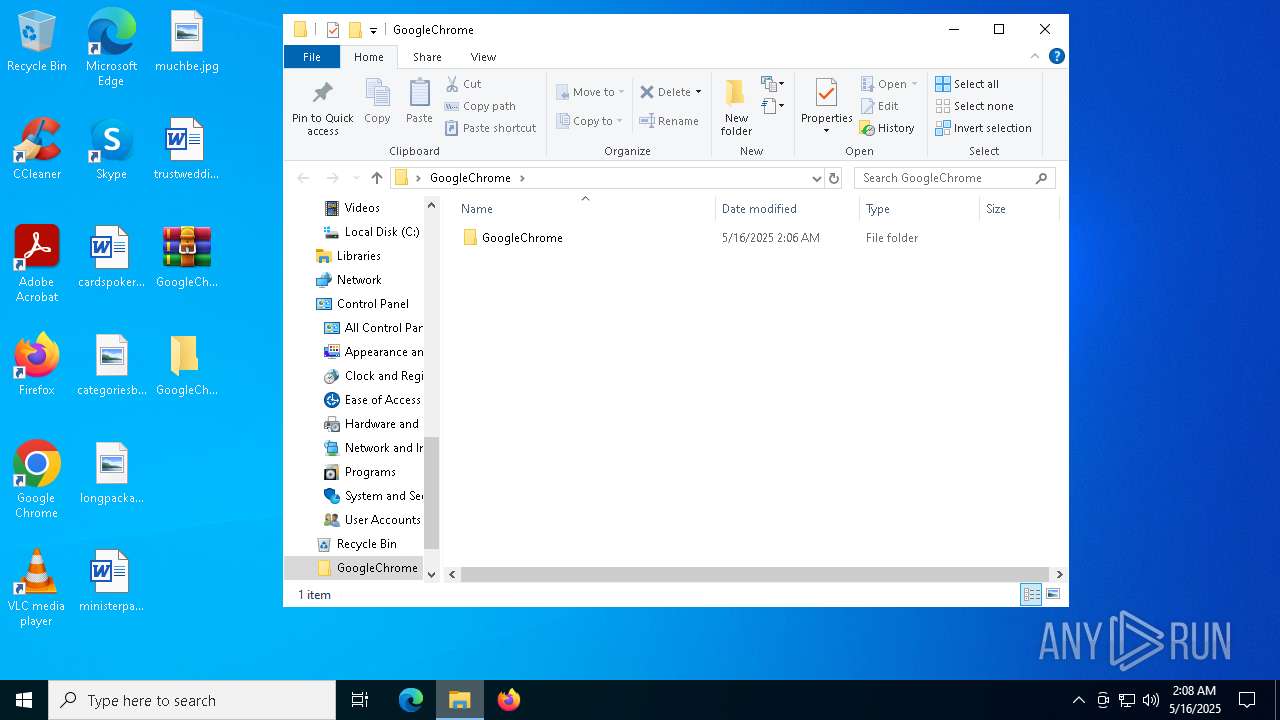
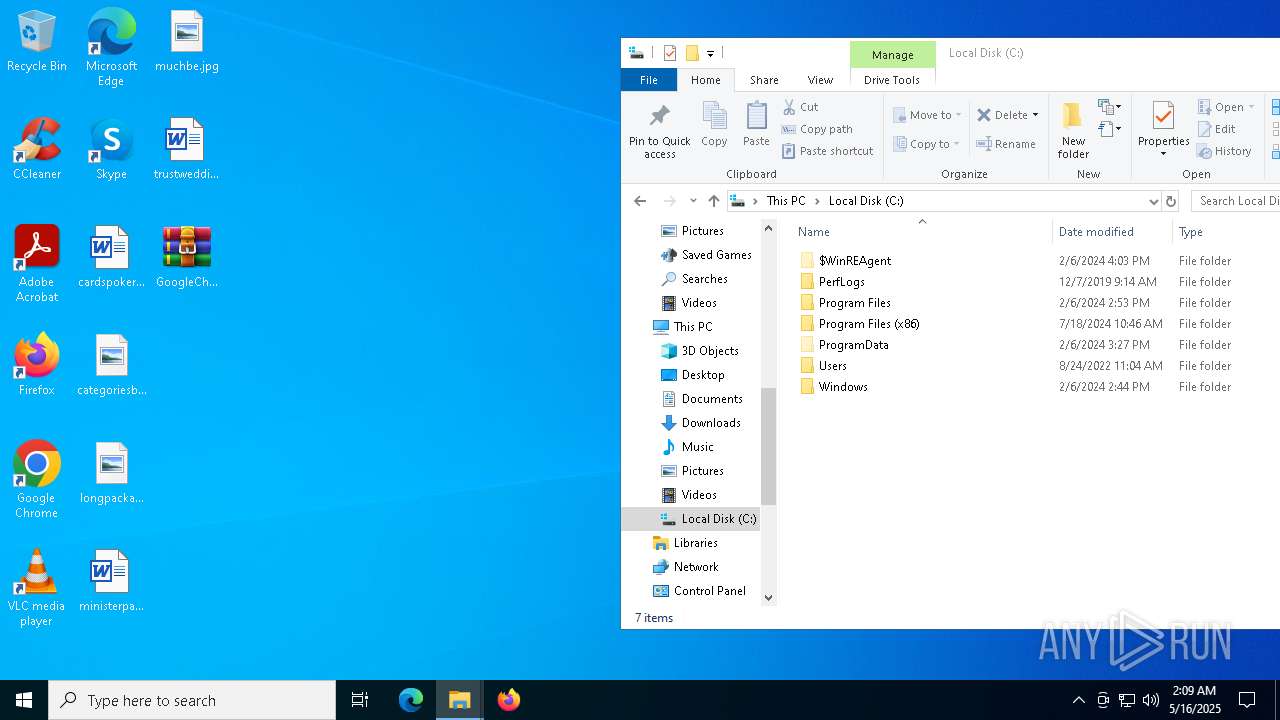
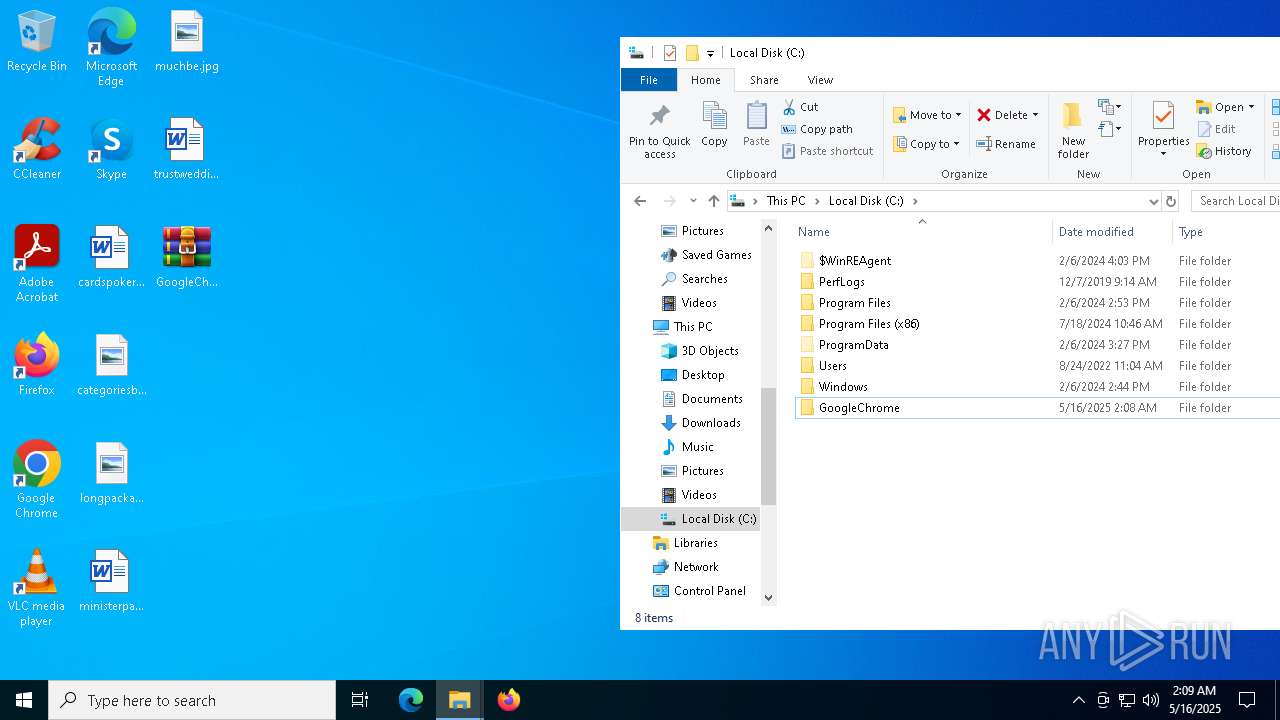
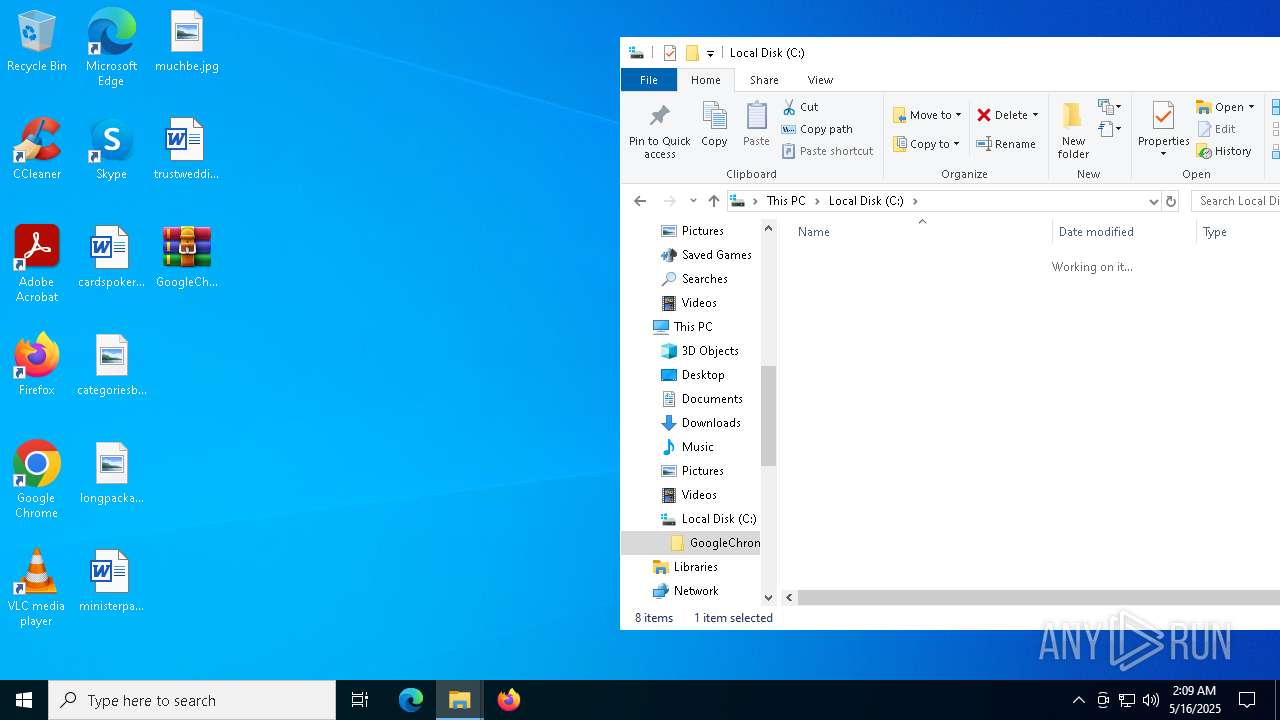
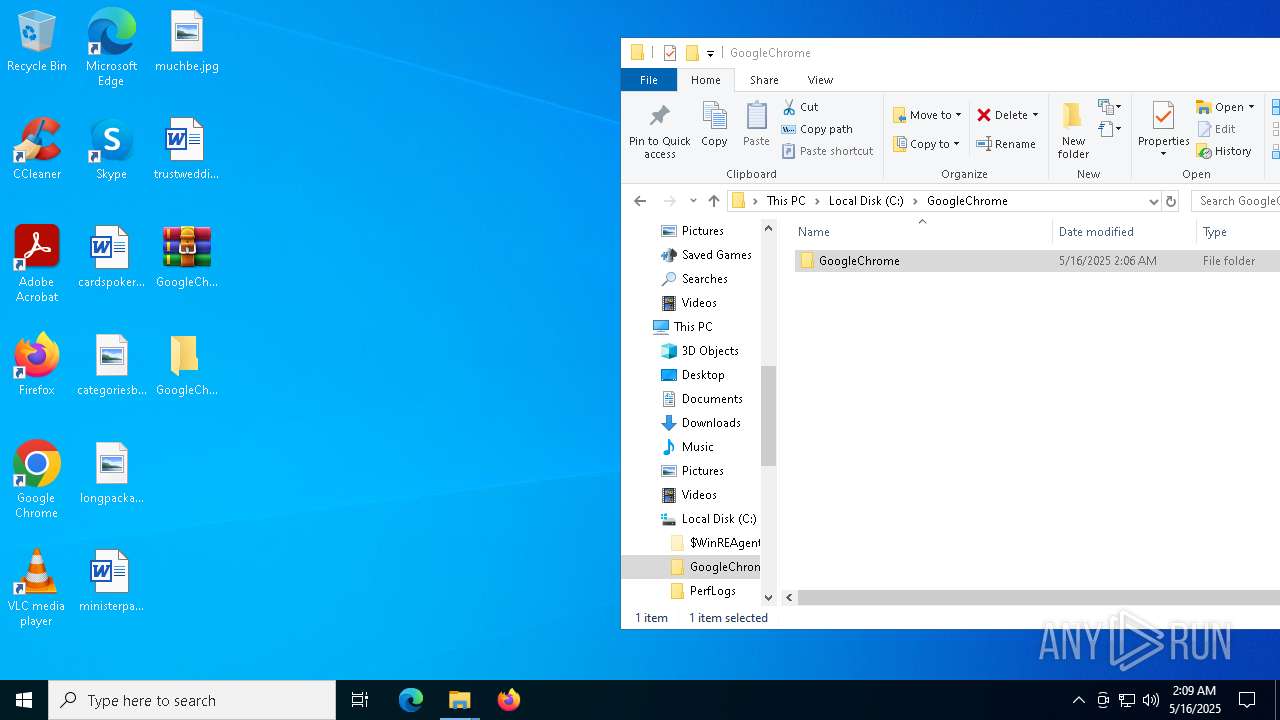
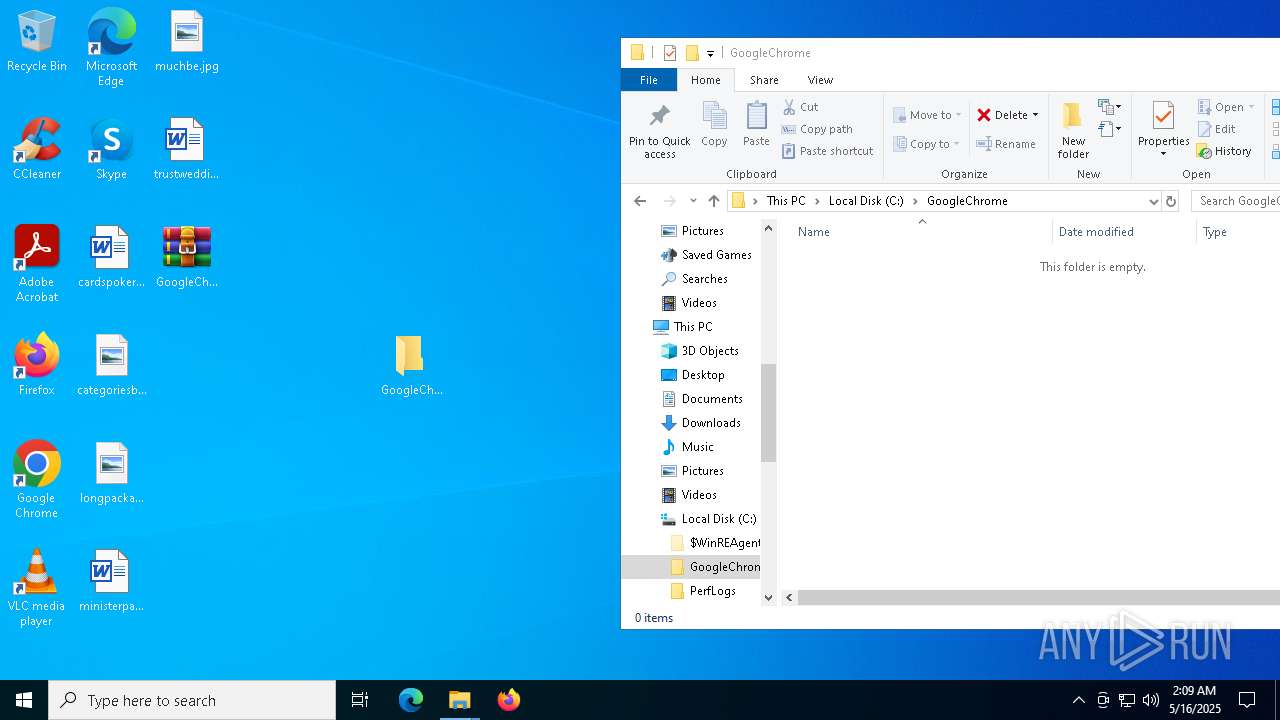
| ZipFileName: | GoogleChrome/ |
Total processes
147
Monitored processes
15
Malicious processes
2
Suspicious processes
0
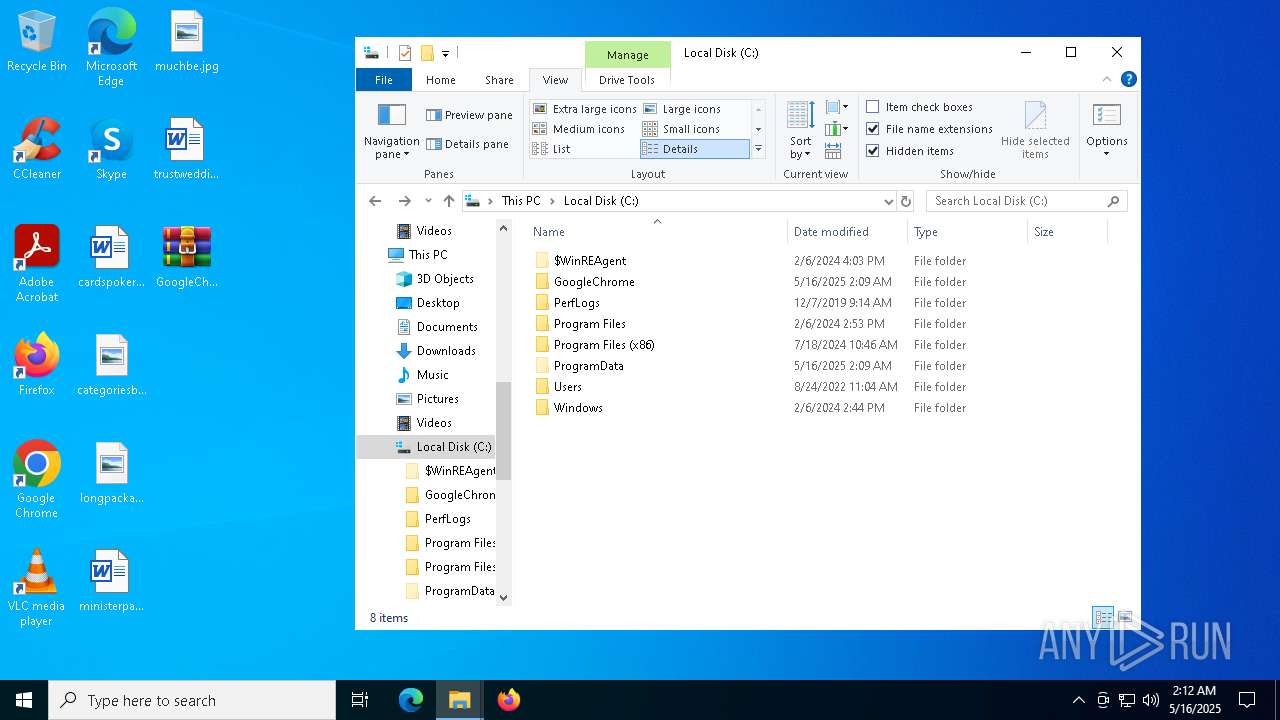
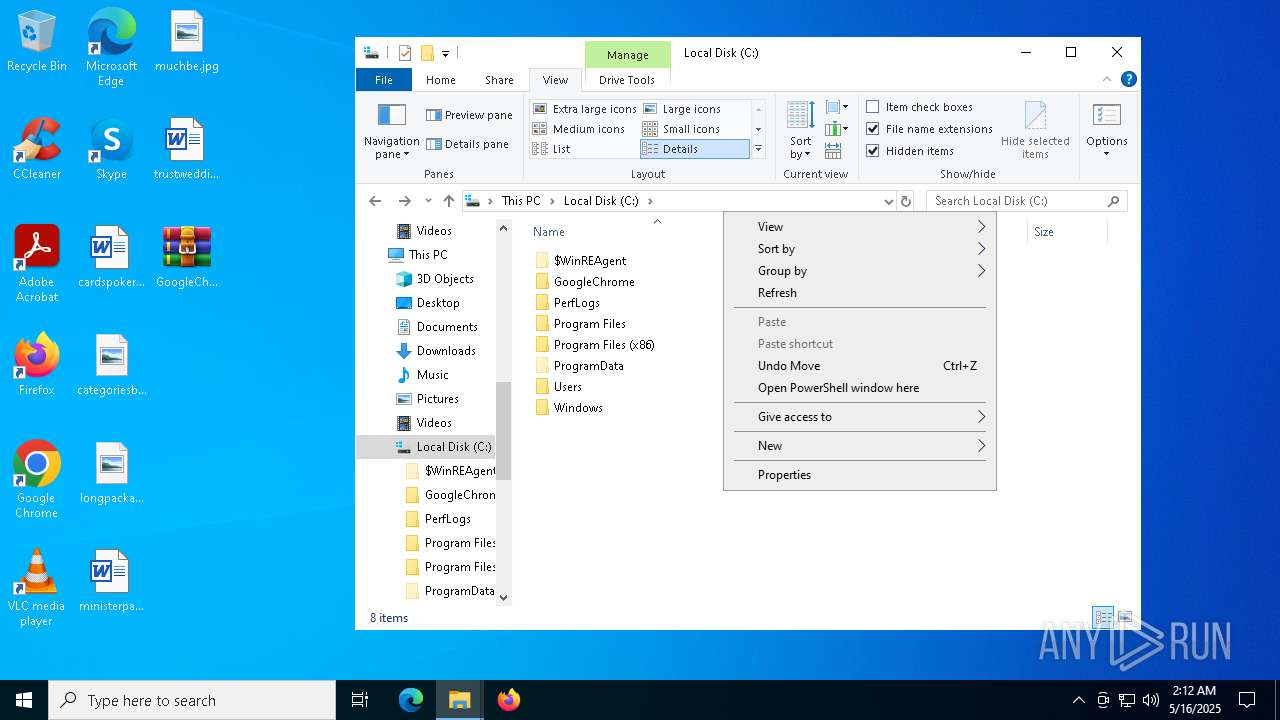
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "PowerShell.exe" -noexit -command Set-Location -literalPath 'C:\' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2980 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4436 | "C:\WINDOWS\system32\cmd.exe" /c start C:\GoogleChrome\GoogleChrome.exe C:\GoogleChrome\GoogleChrome.a3x & exit | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5680 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6068 | "C:\Windows\System32\netsh.exe" firewall add allowedprogram "C:\GoogleChrome\GoogleChrome.exe" "GoogleChrome.exe" ENABLE | C:\Windows\SysWOW64\netsh.exe | — | GoogleChrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6248 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6708 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Desktop\GoogleChrome.zip.xpi | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6988 | C:\WINDOWS\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {c82192ee-6cb5-4bc0-9ef0-fb818773790a} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7208 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7240 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 158
Read events
12 109
Write events
36
Delete events
13
Modification events
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 11 |
Value: | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 10 |
Value: | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 9 |
Value: | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 8 |
Value: | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 7 |
Value: | |||
| (PID) Process: | (7936) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 6 |
Value: | |||
Executable files
2
Suspicious files
16
Text files
2
Unknown types
0
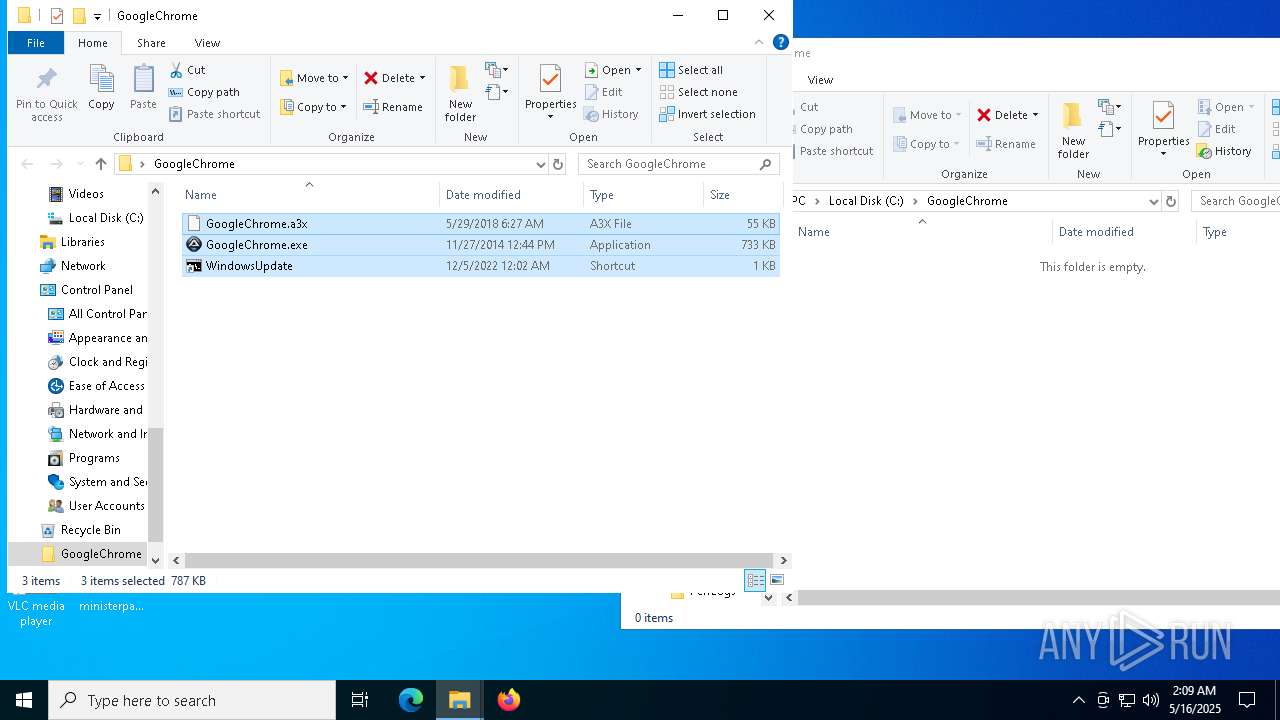
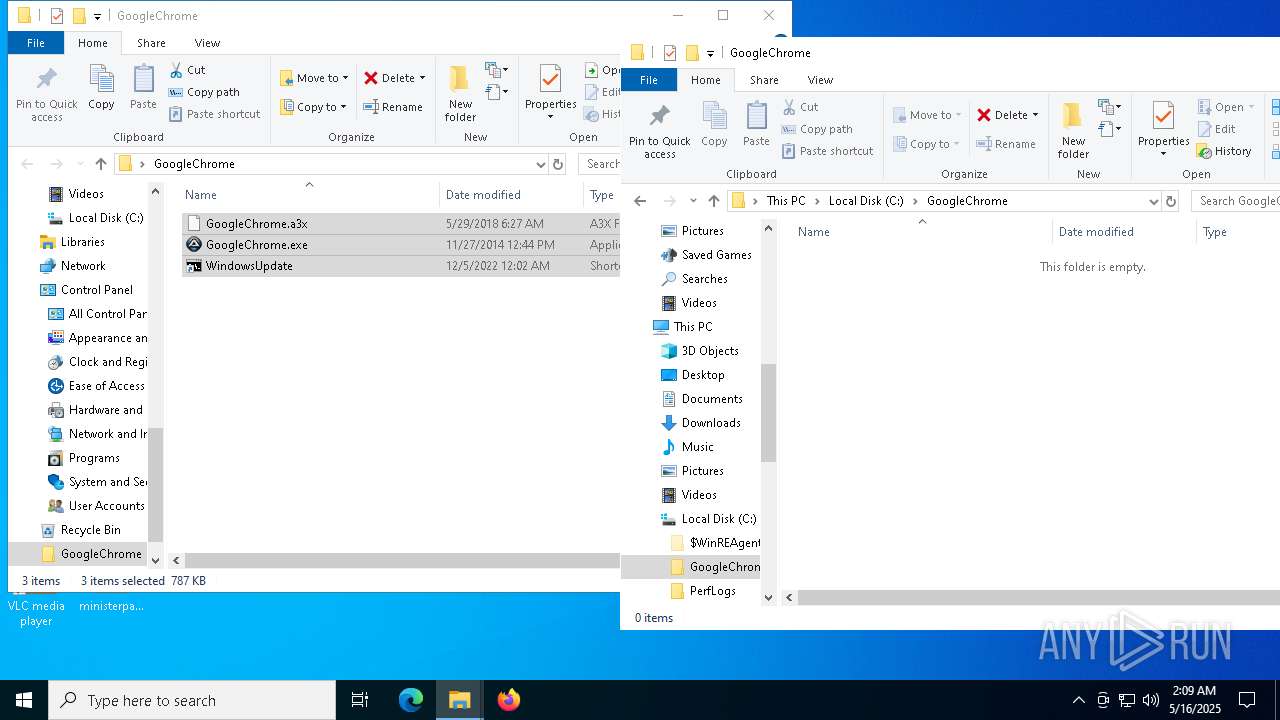
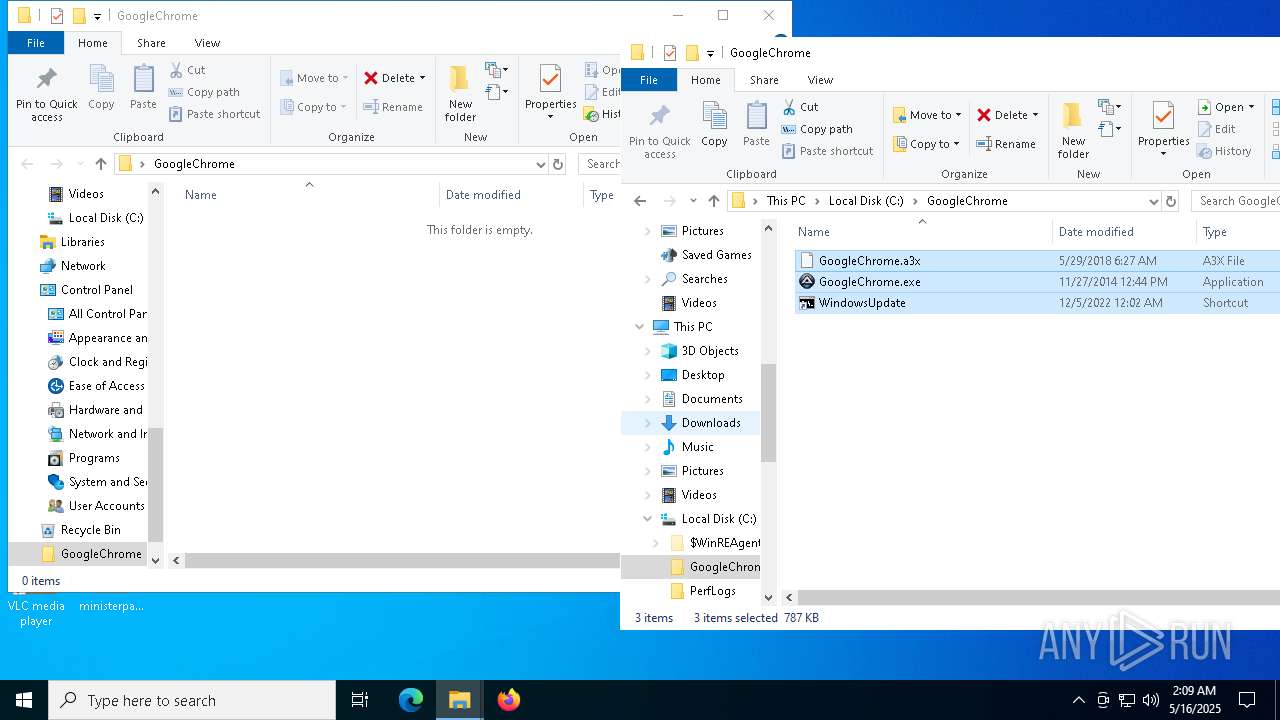
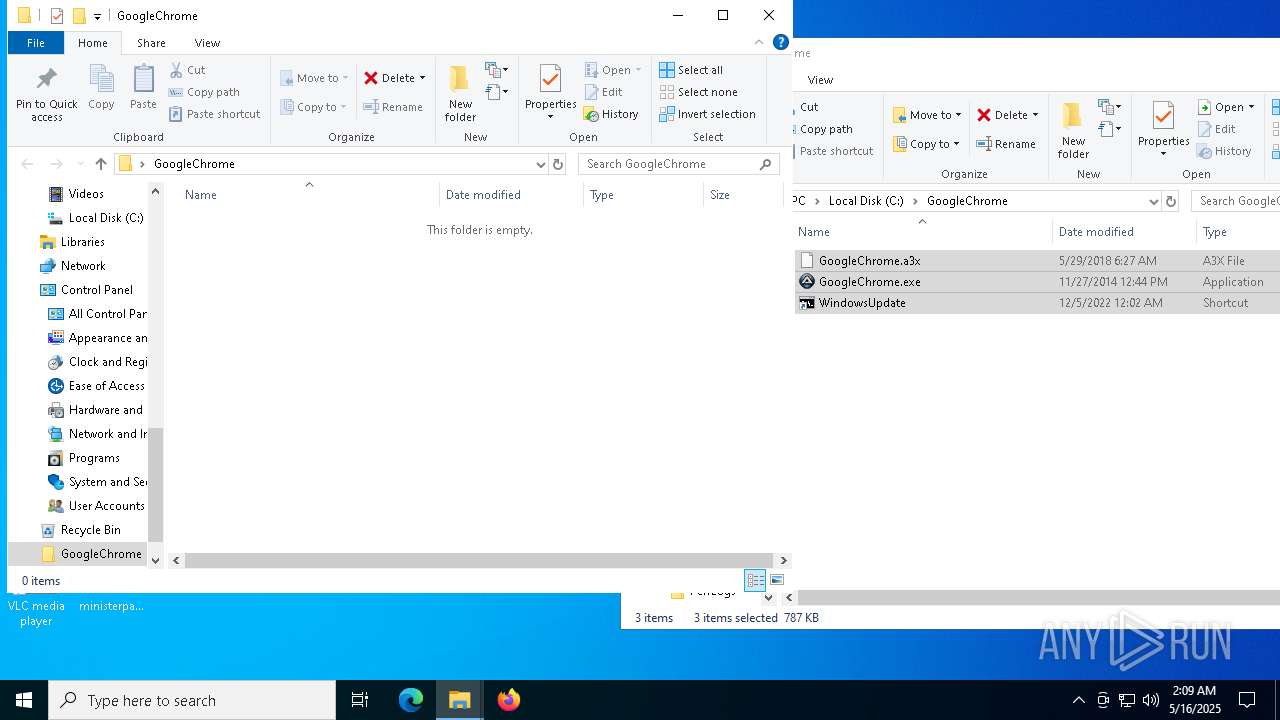
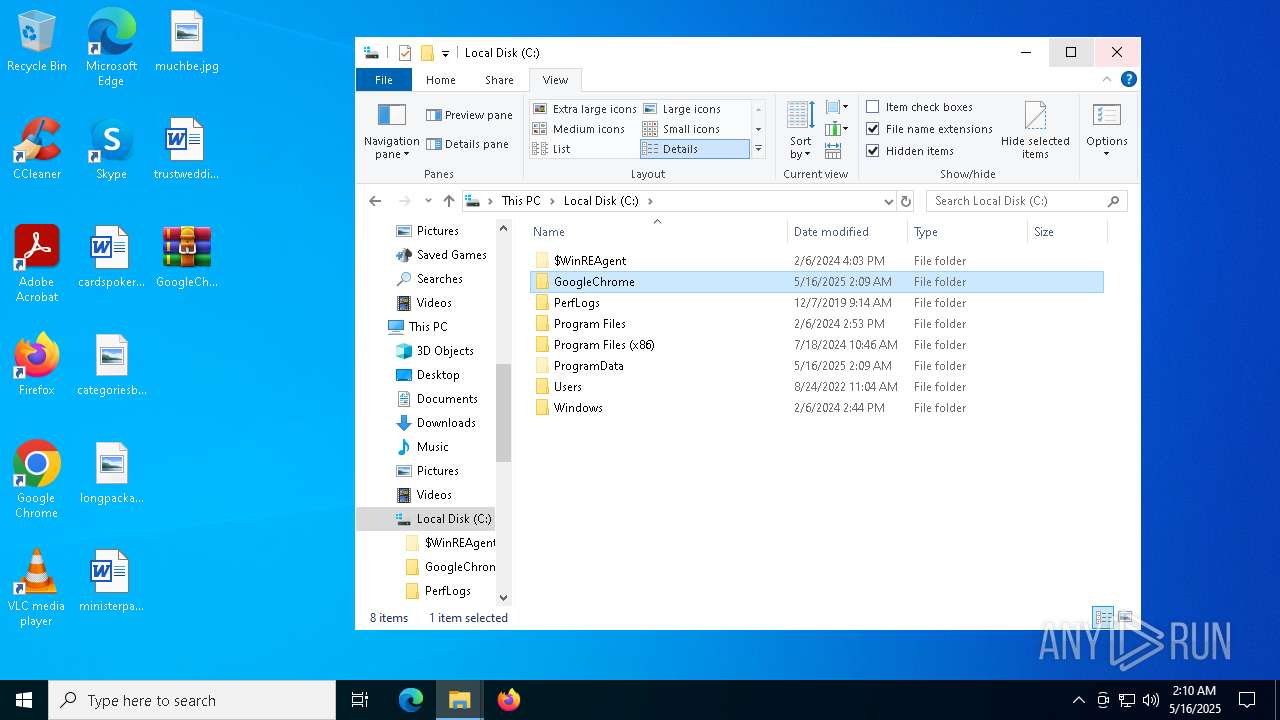
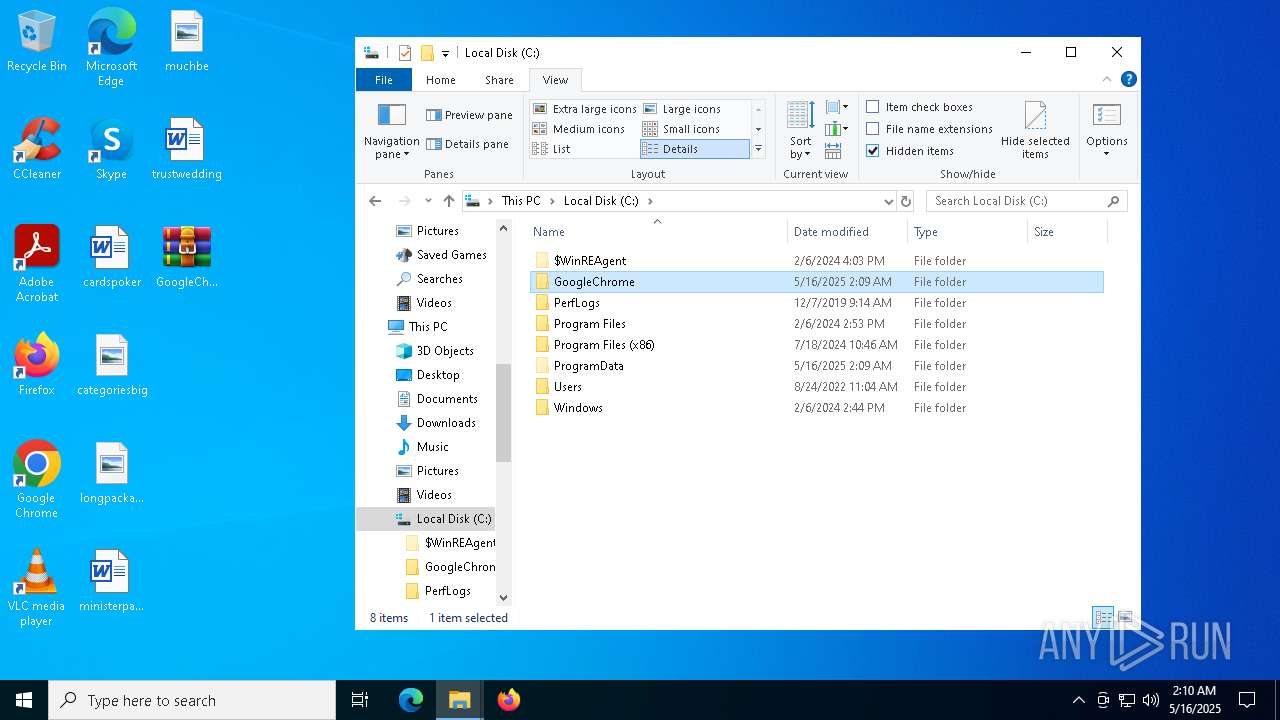
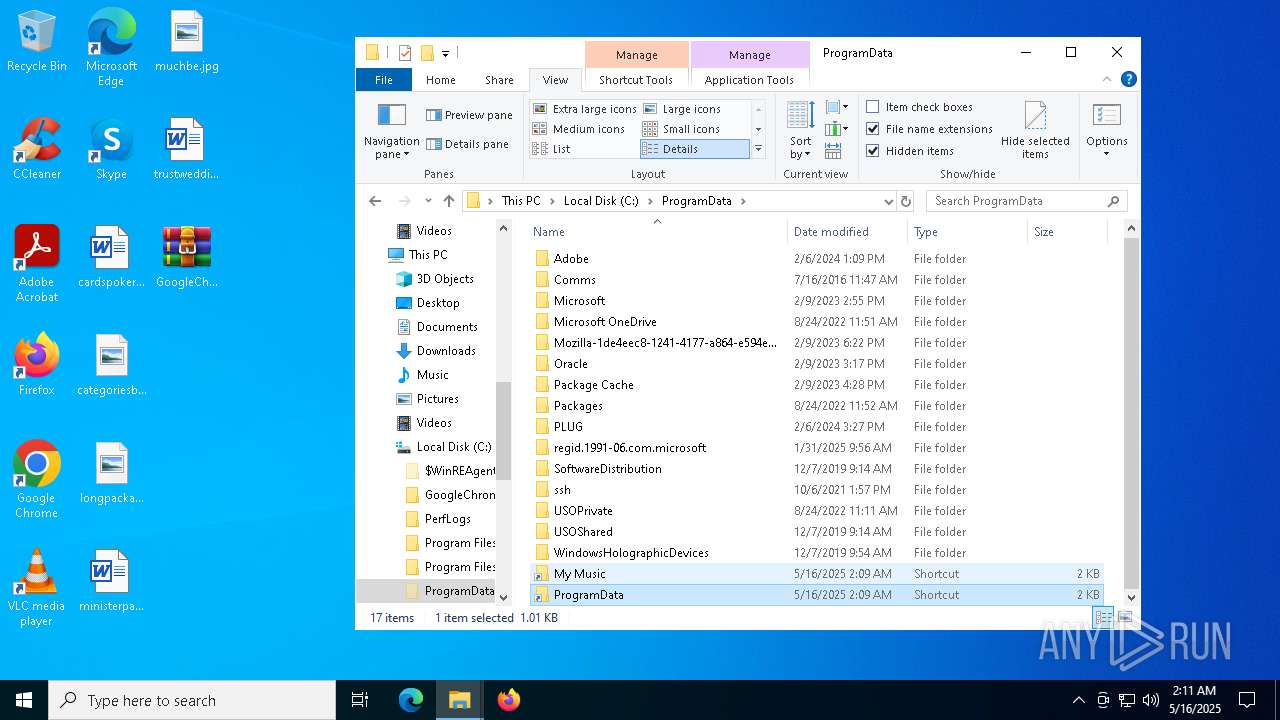
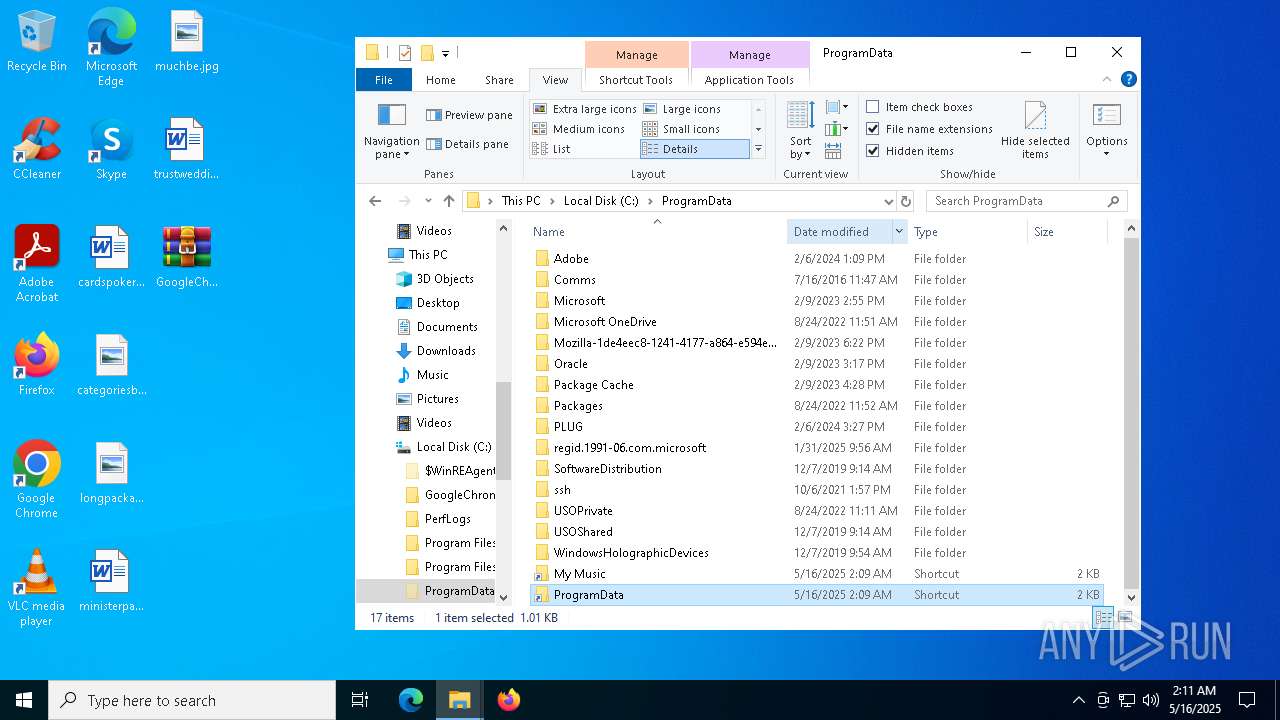
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
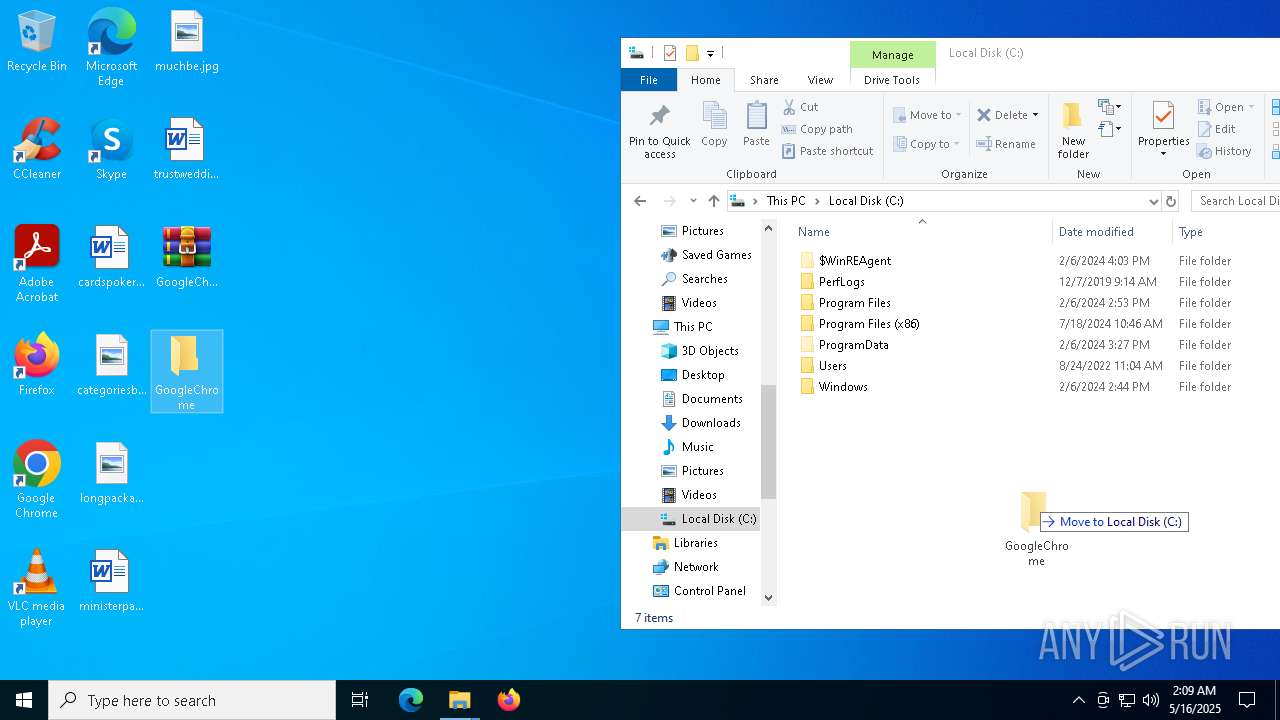
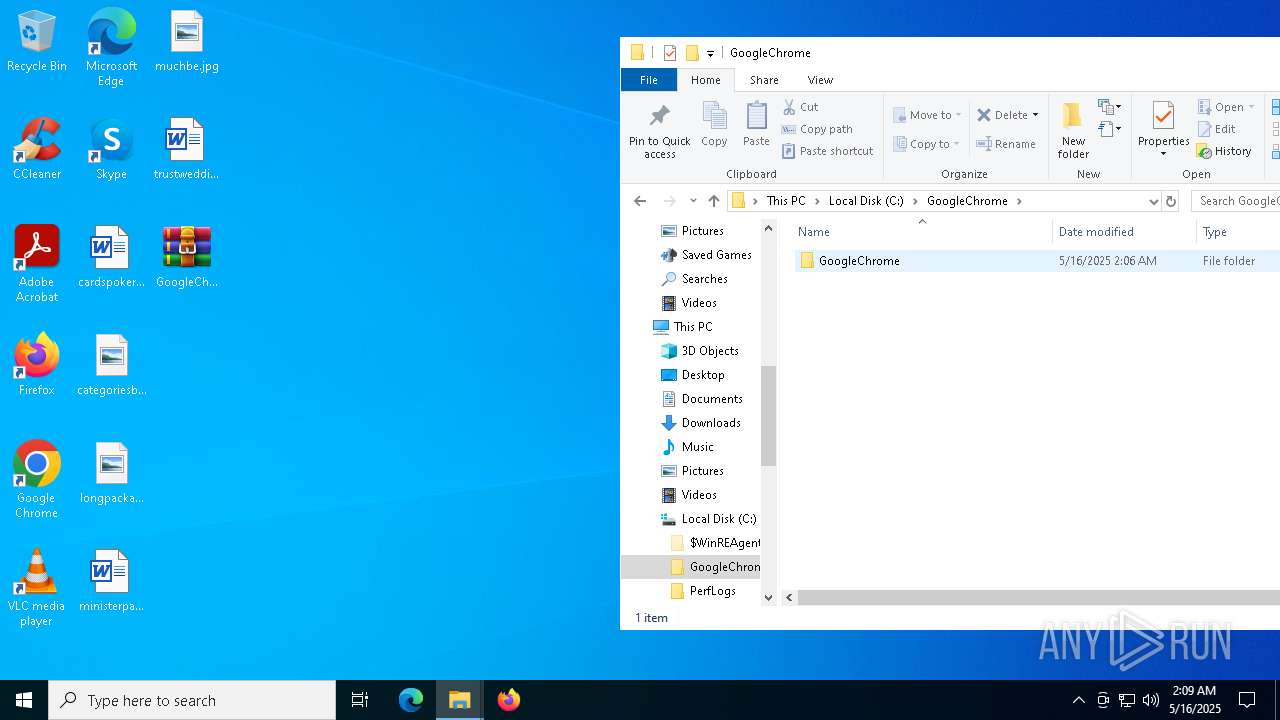
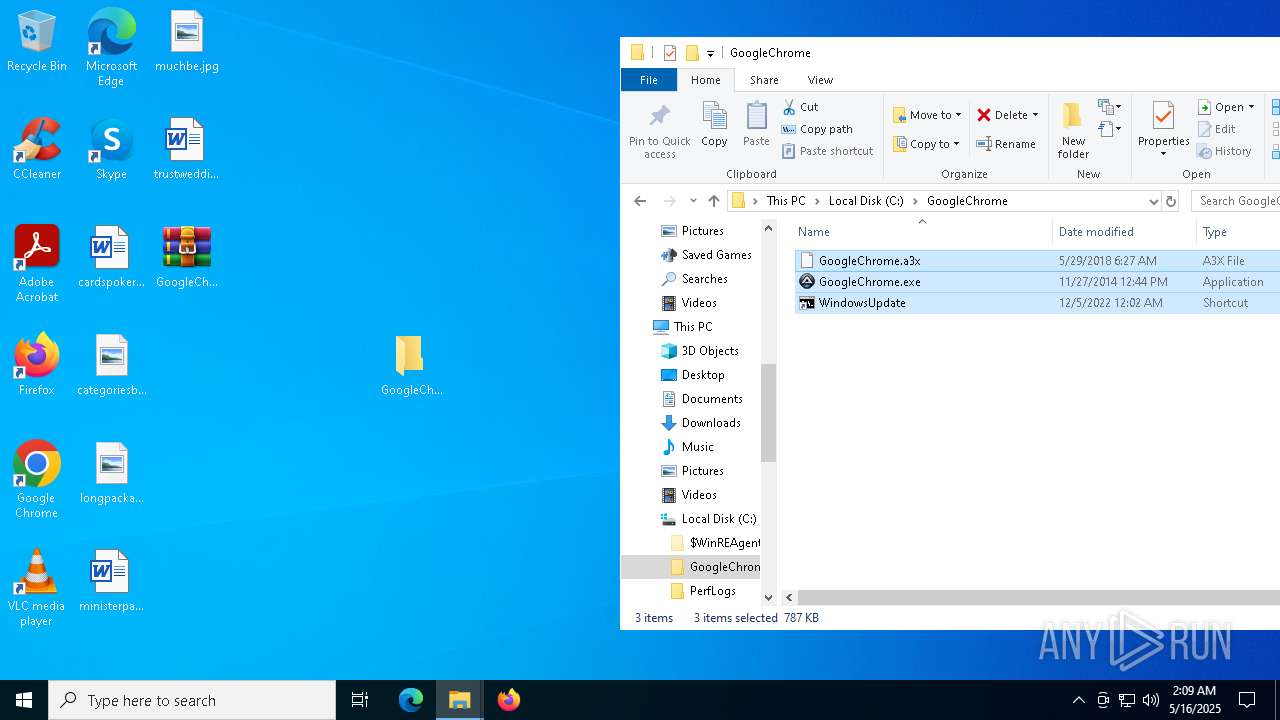
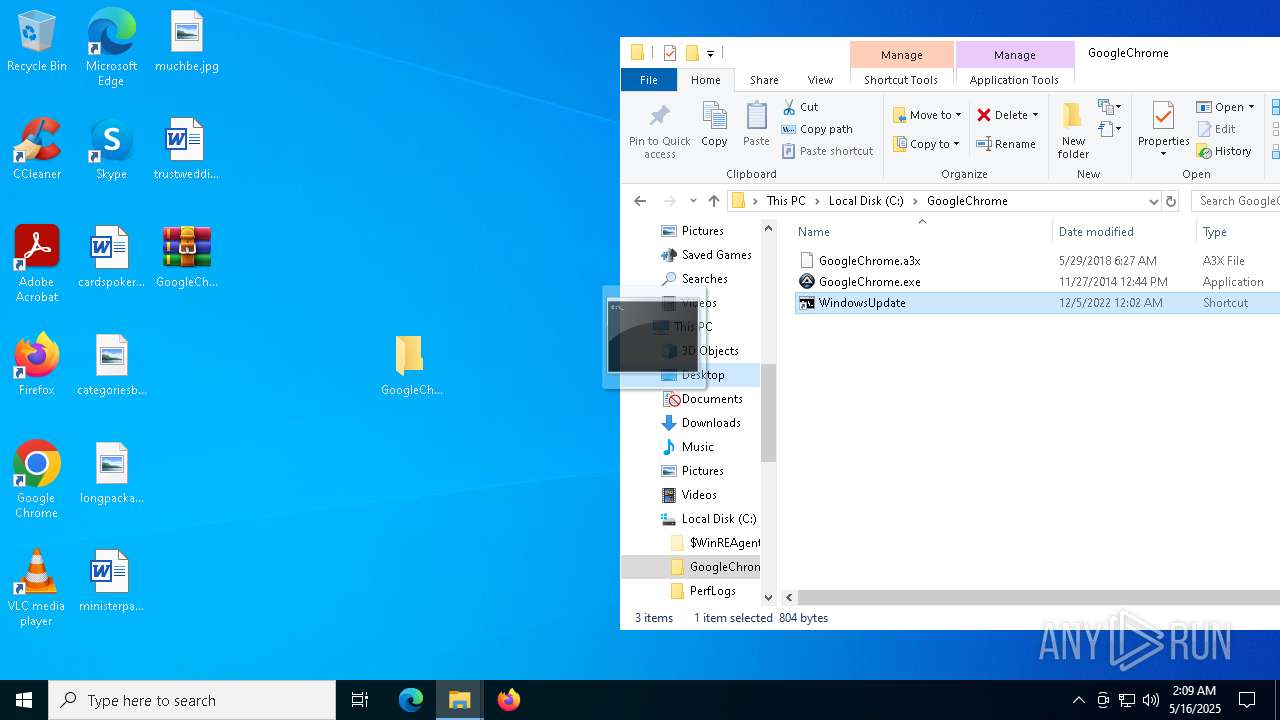
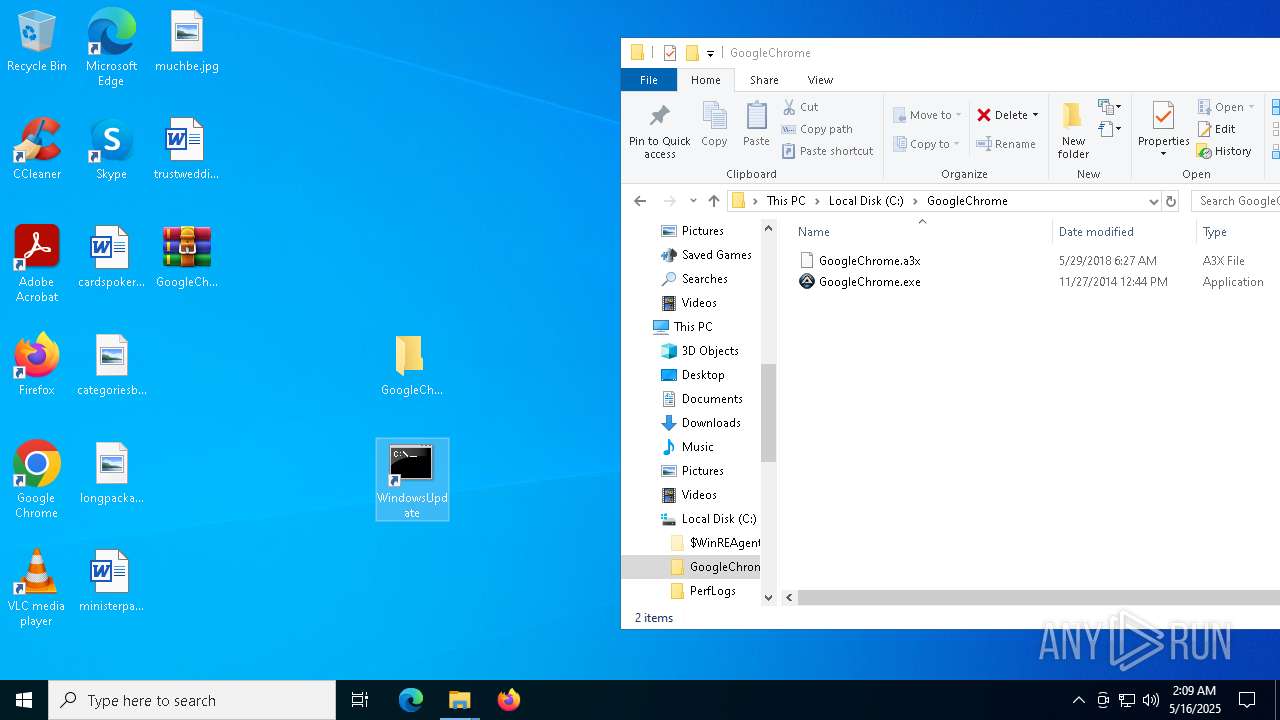
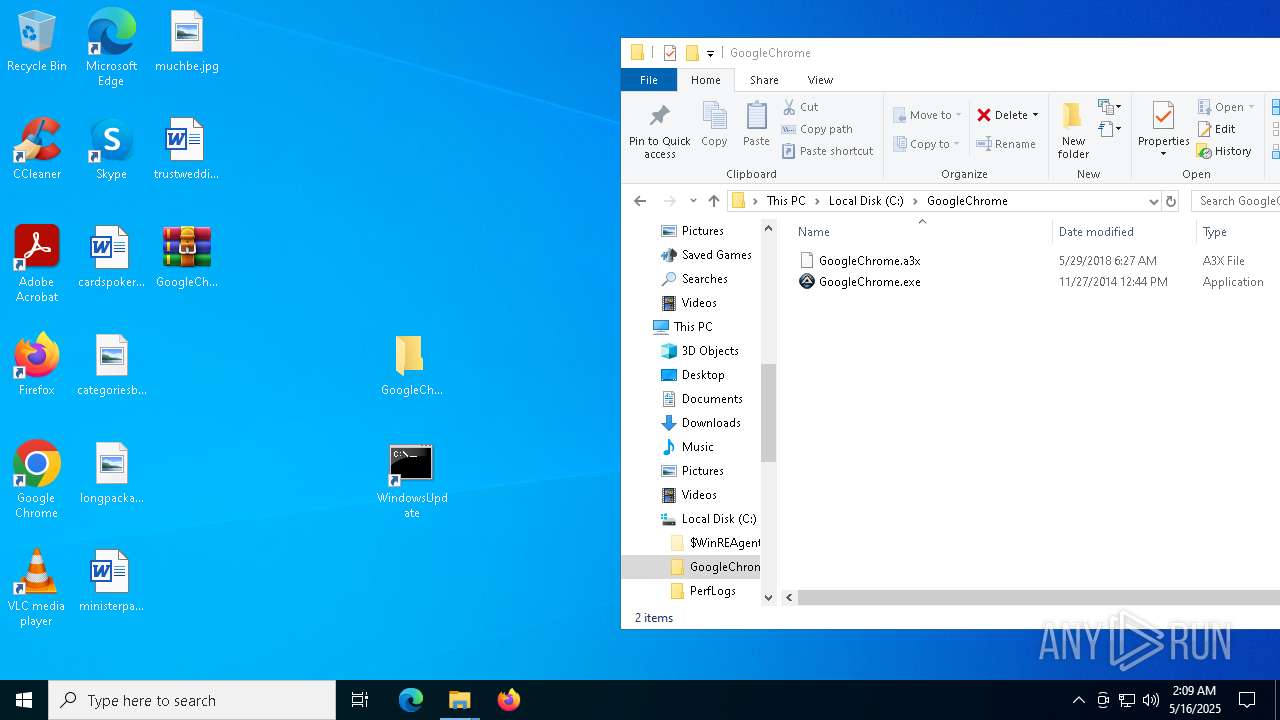
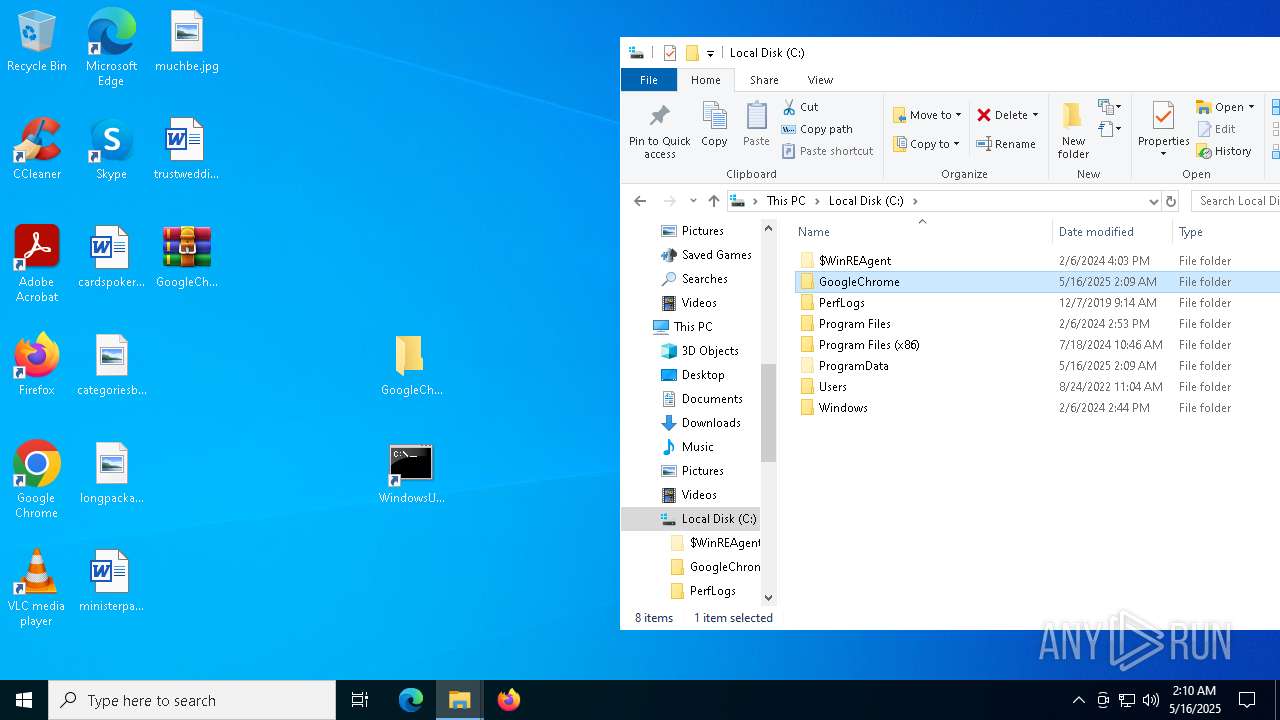
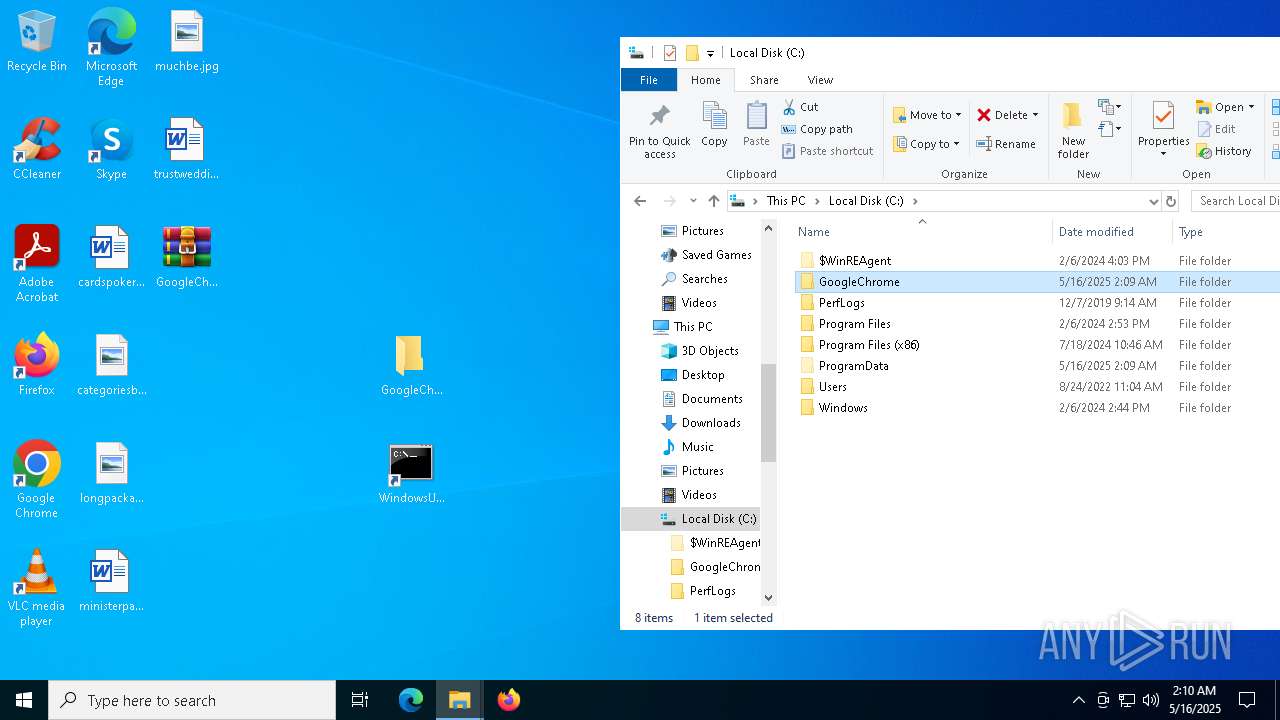
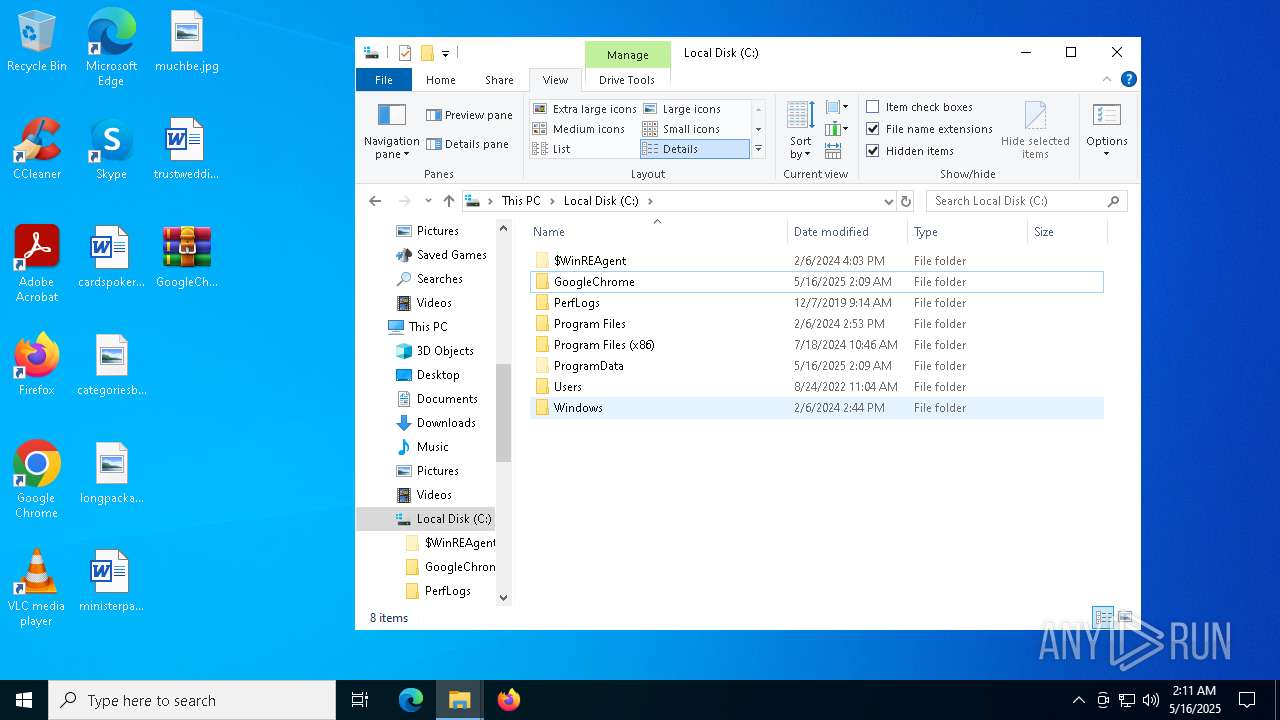
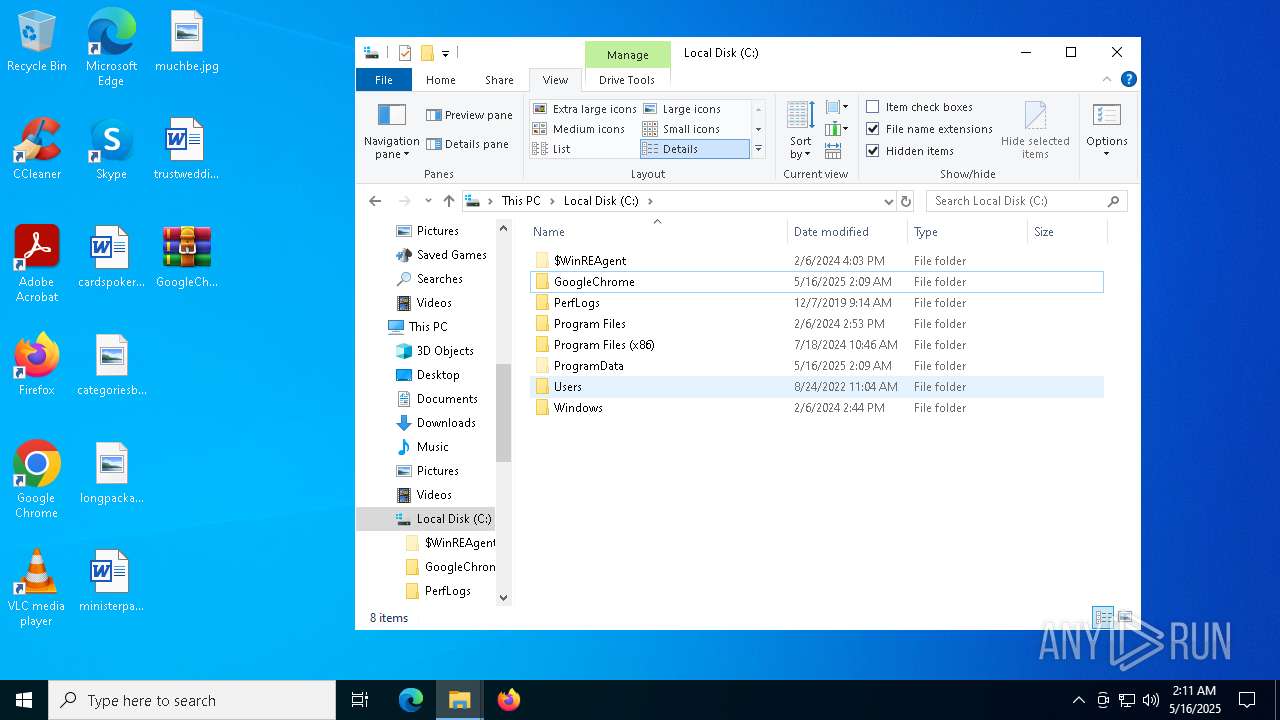
| 7308 | GoogleChrome.exe | C:\GoogleChrome\WindowsUpdate.lnk | binary | |
MD5:182C3EBC02E8139F3ECD5CF5ED474927 | SHA256:DCB57DB772AB61EF2D6FF835DC1384B0F678FE6863B7959F6D411D4CABCE20C8 | |||
| 7936 | WinRAR.exe | C:\Users\admin\Desktop\GoogleChrome\GoogleChrome\WindowsUpdate.lnk | binary | |
MD5:E28A15ED9909A894FF81060BAD872E19 | SHA256:A51AB134264A79F3E325C714F77E613541B9E613DA1ED277FC67DD3F89923694 | |||
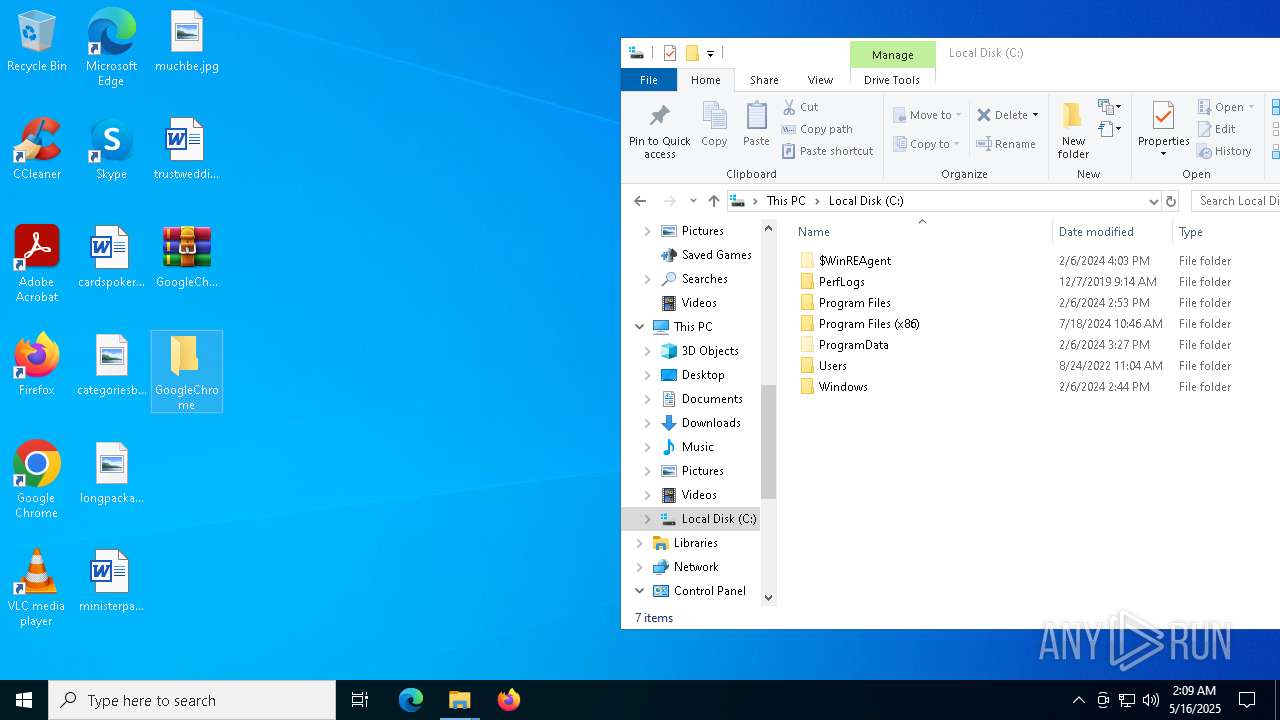
| 7936 | WinRAR.exe | C:\Users\admin\Desktop\GoogleChrome\GoogleChrome\GoogleChrome.exe | executable | |
MD5:71D8F6D5DC35517275BC38EBCC815F9F | SHA256:FB73A819B37523126C7708A1D06F3B8825FA60C926154AB2D511BA668F49DC4B | |||
| 7308 | GoogleChrome.exe | C:\GoogleChrome\GoogleChrome.lnk | binary | |
MD5:A9EE603EAC1B35084F4E7BA1D04B894A | SHA256:1B4CDC4CBC076E807A63AD731CA4233B6454B1F5FA3E3A0F224F7A30317B5B28 | |||
| 7308 | GoogleChrome.exe | C:\GoogleChrome\GoogleUpdate.lnk | binary | |
MD5:6093567B536CECCA61CA51351B561D5D | SHA256:8478EBBF52A410D7B36FAAD6E419662F748CFC0F83B346A0D249C54DF73C4177 | |||
| 7308 | GoogleChrome.exe | C:\MozillaFirefox\GoogleUpdate.lnk | binary | |
MD5:6093567B536CECCA61CA51351B561D5D | SHA256:8478EBBF52A410D7B36FAAD6E419662F748CFC0F83B346A0D249C54DF73C4177 | |||
| 7308 | GoogleChrome.exe | C:\MozillaFirefox\MozillaFirefox.lnk | binary | |
MD5:A9EE603EAC1B35084F4E7BA1D04B894A | SHA256:1B4CDC4CBC076E807A63AD731CA4233B6454B1F5FA3E3A0F224F7A30317B5B28 | |||
| 7308 | GoogleChrome.exe | C:\MozillaFirefox\WindowsUpdate.lnk | binary | |
MD5:182C3EBC02E8139F3ECD5CF5ED474927 | SHA256:DCB57DB772AB61EF2D6FF835DC1384B0F678FE6863B7959F6D411D4CABCE20C8 | |||
| 7308 | GoogleChrome.exe | C:\MozillaFirefox\GoogleChrome.exe | executable | |
MD5:71D8F6D5DC35517275BC38EBCC815F9F | SHA256:FB73A819B37523126C7708A1D06F3B8825FA60C926154AB2D511BA668F49DC4B | |||
| 968 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF15308f.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
34
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7748 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7748 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |