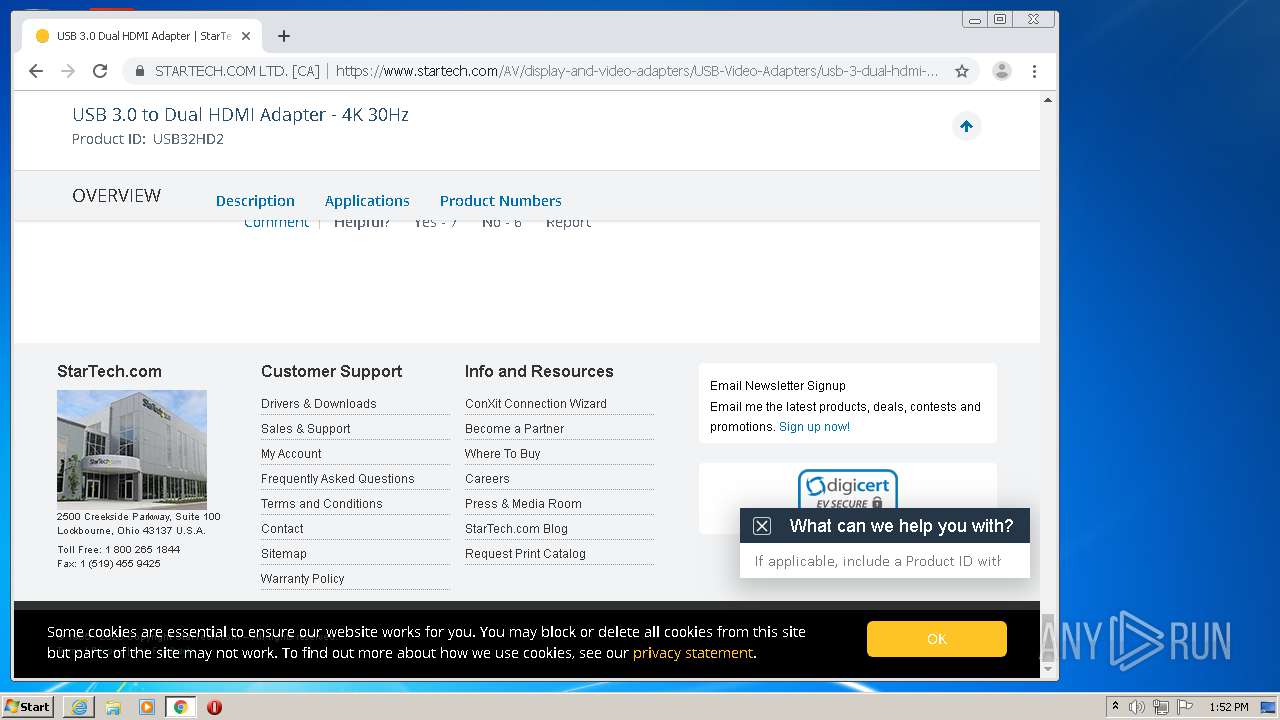
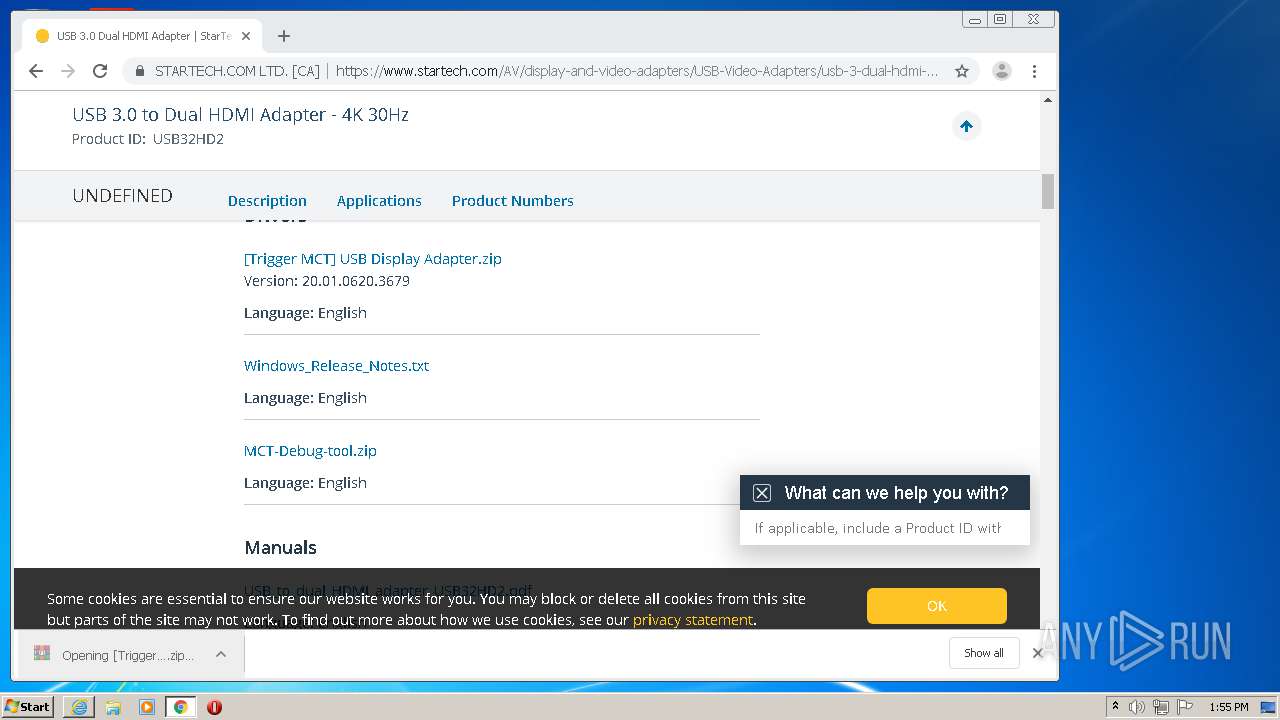
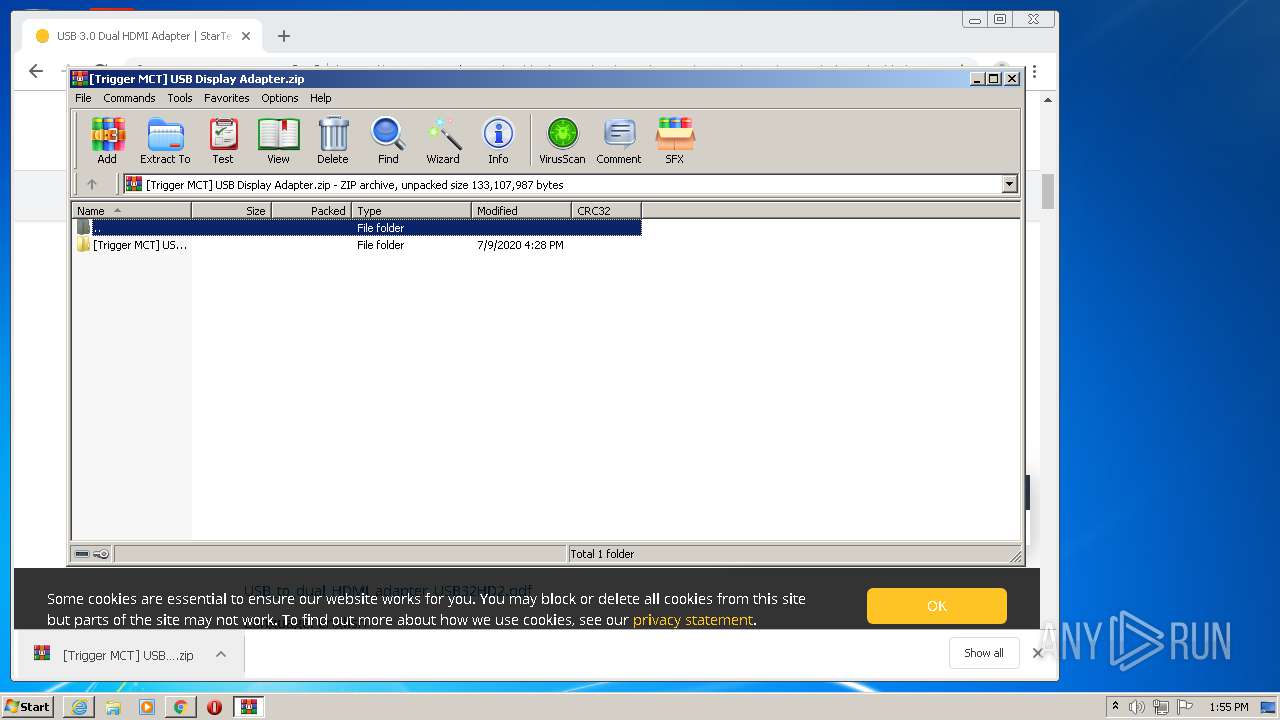
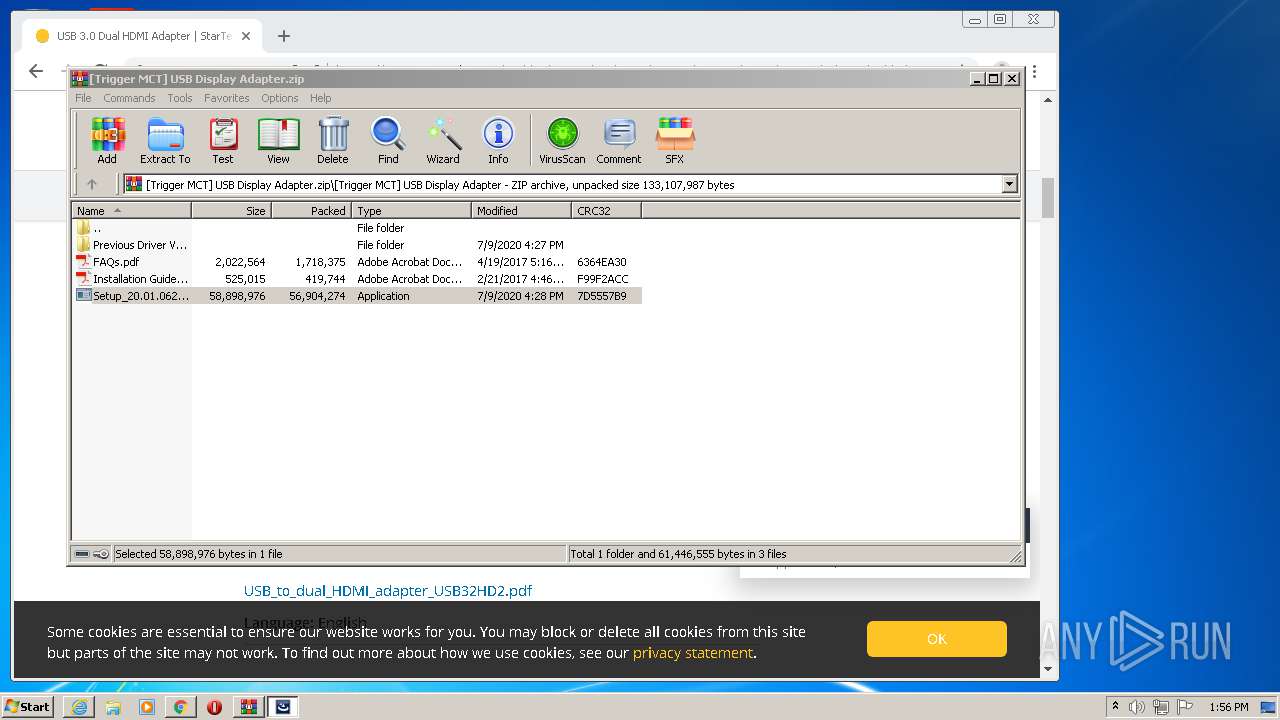
| download: | USB32HD2 |
| Full analysis: | https://app.any.run/tasks/ed3eb17e-9956-42f7-bbe3-1fad0ff15604 |
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2020, 12:51:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | F2CAB32FDAA387FA7CD2CF9934C9B35D |
| SHA1: | 2F985A9534AD12401BAF9CA7E0D10680648F001D |
| SHA256: | EDFD56535E4DD330DDA4686862D02ADBE5CFF7E68E4197F9CE77B7F570C492D5 |
| SSDEEP: | 3072:BPYkgXBk6hKOjVAOAkArAFAeAgesyfP3w8PAXuKmqlFh2iTh3i5kxvlko2G:BPYkgS6hPvlU/v4+rwXr5uoWq |
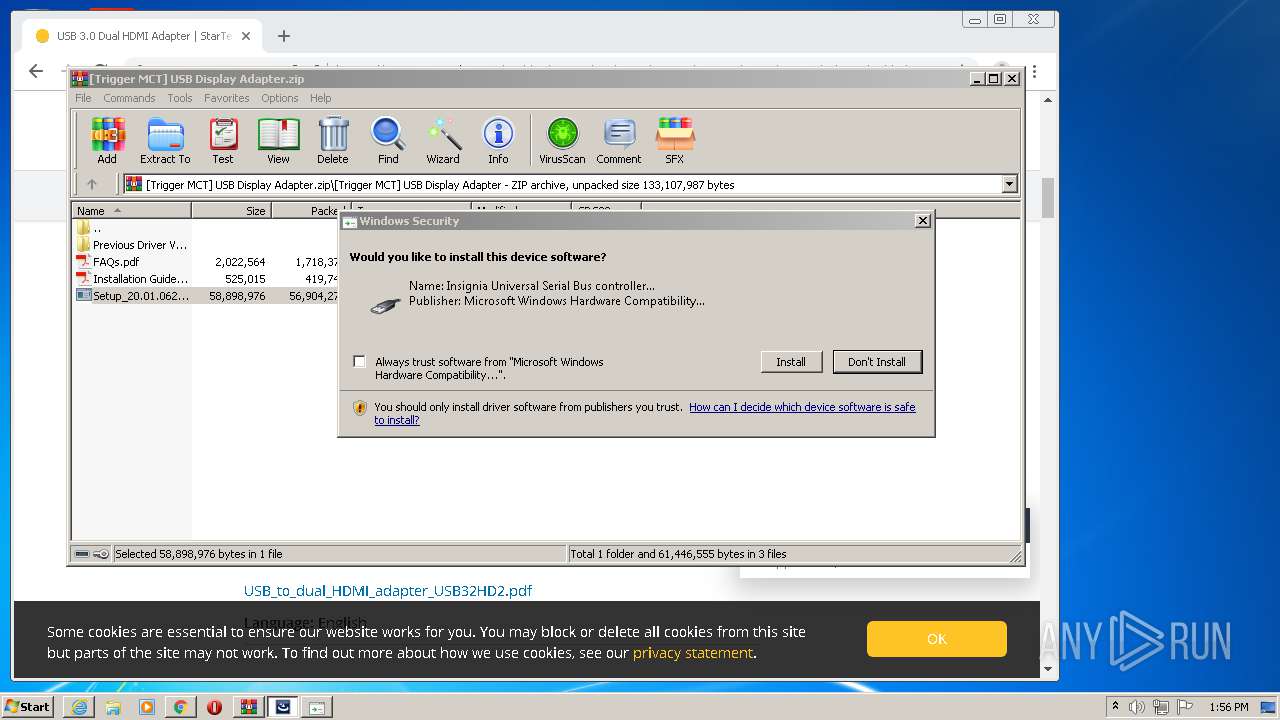
MALICIOUS
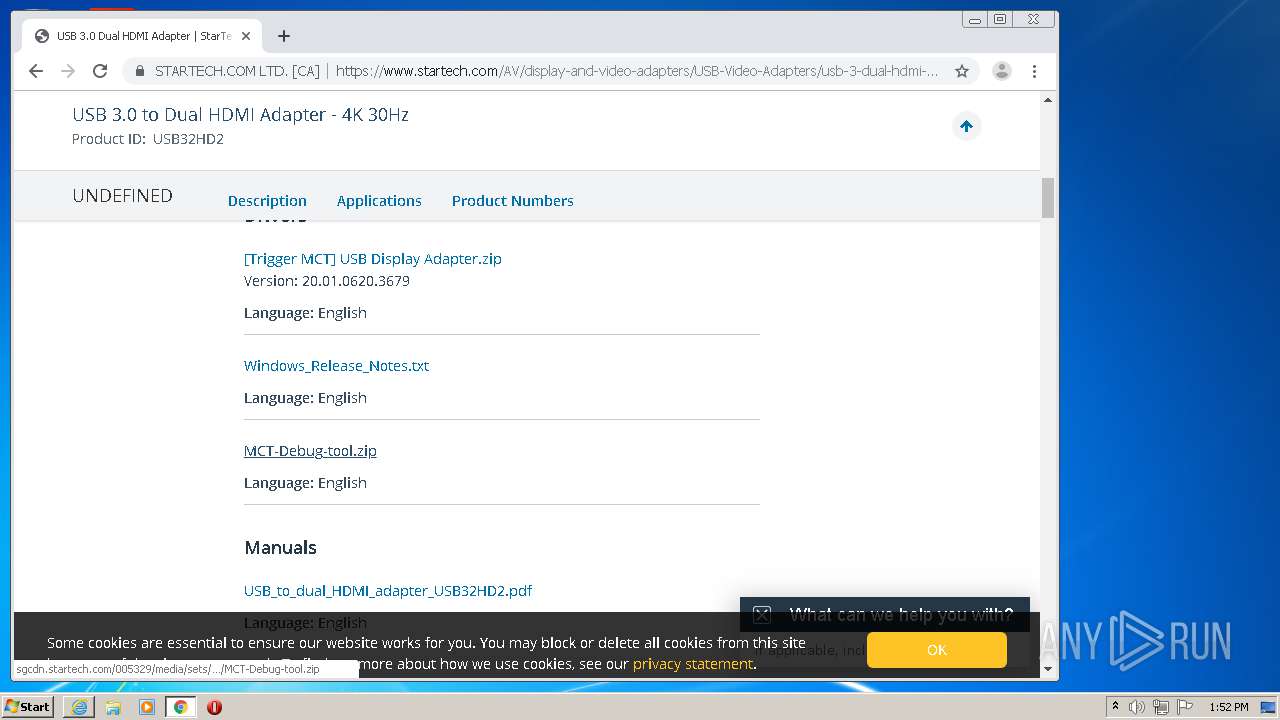
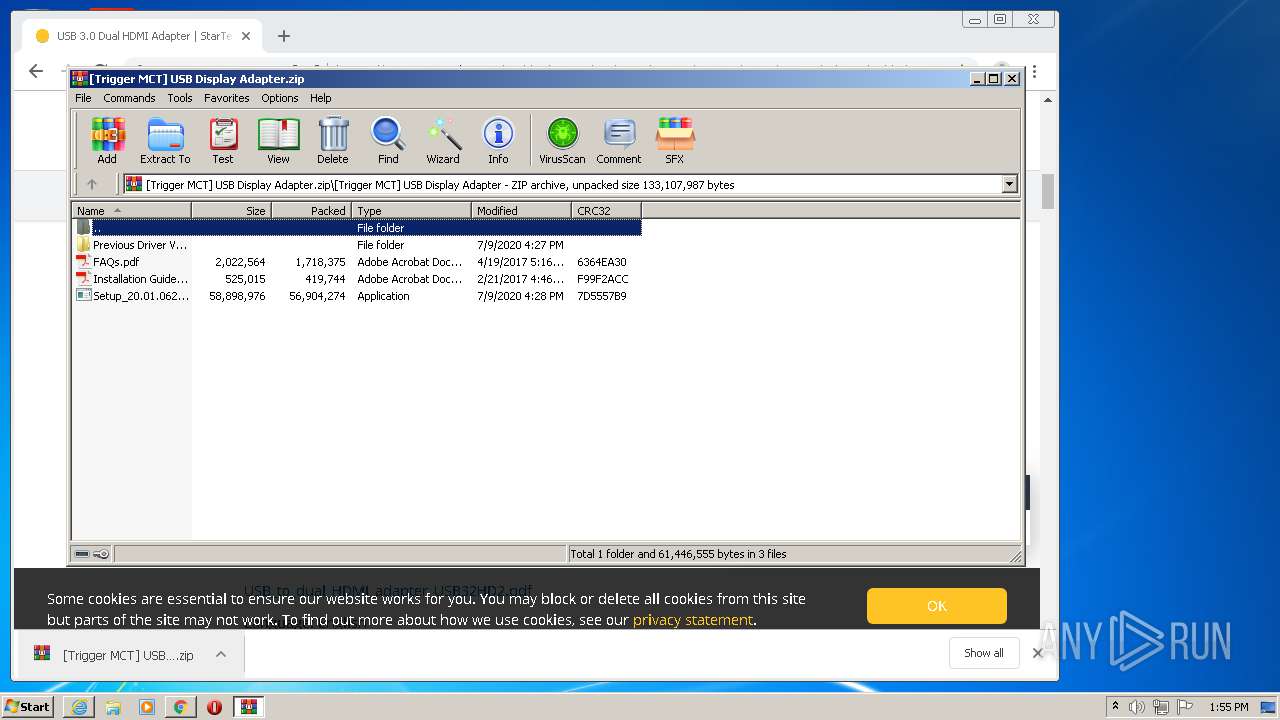
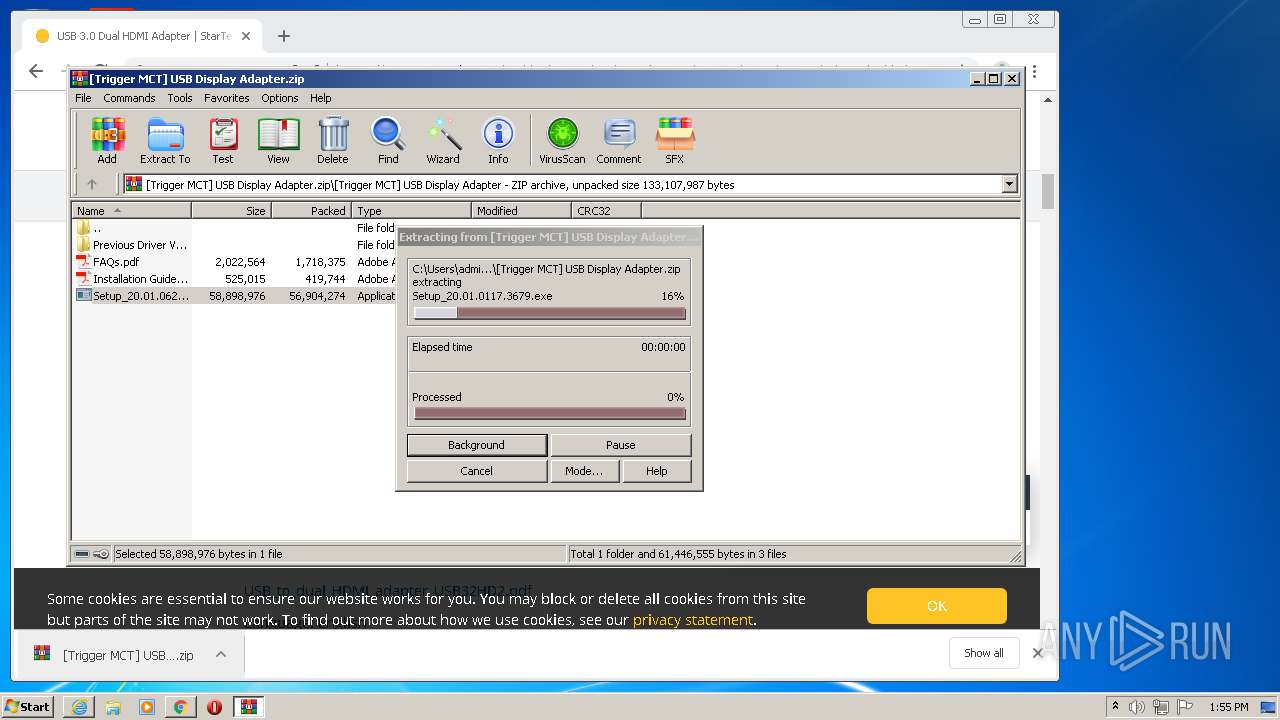
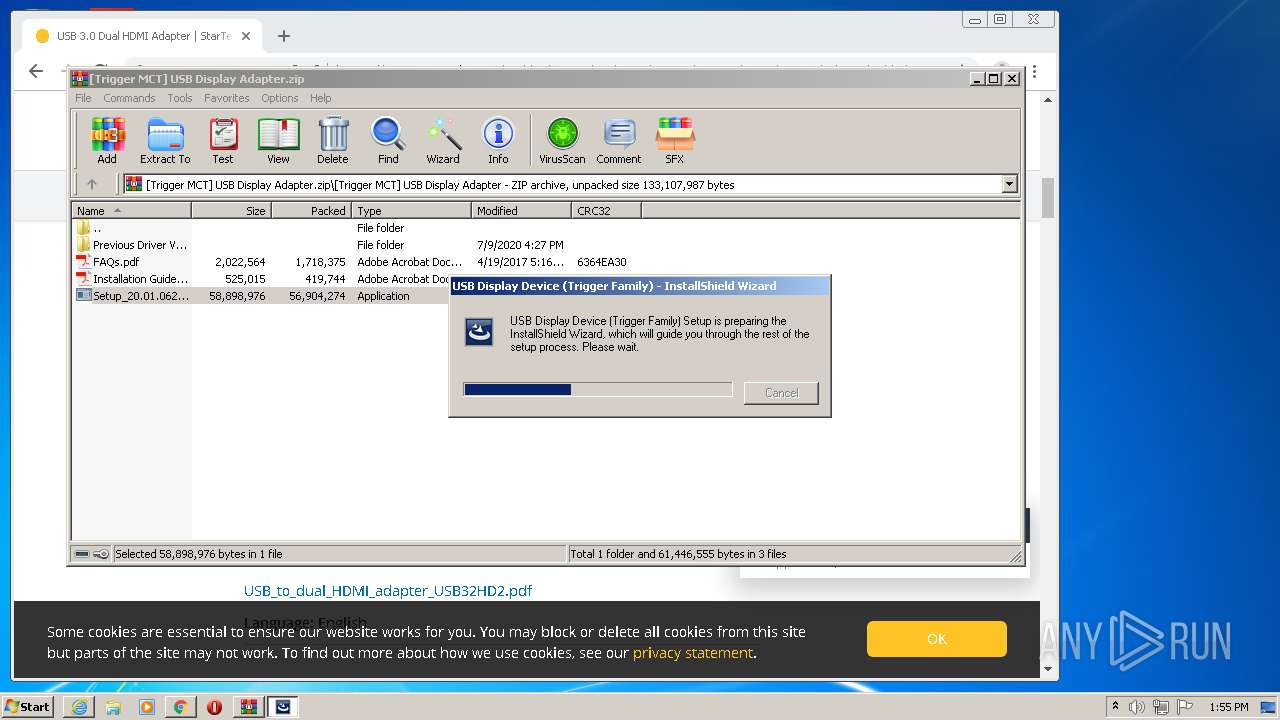
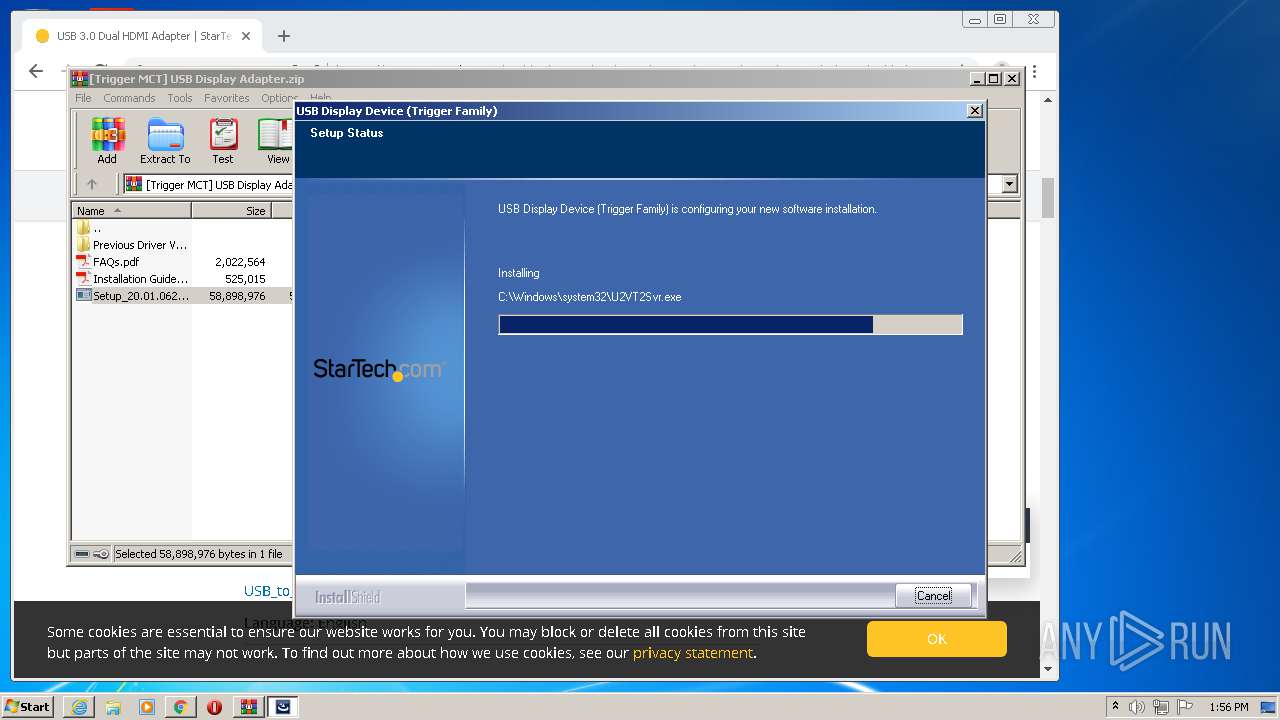
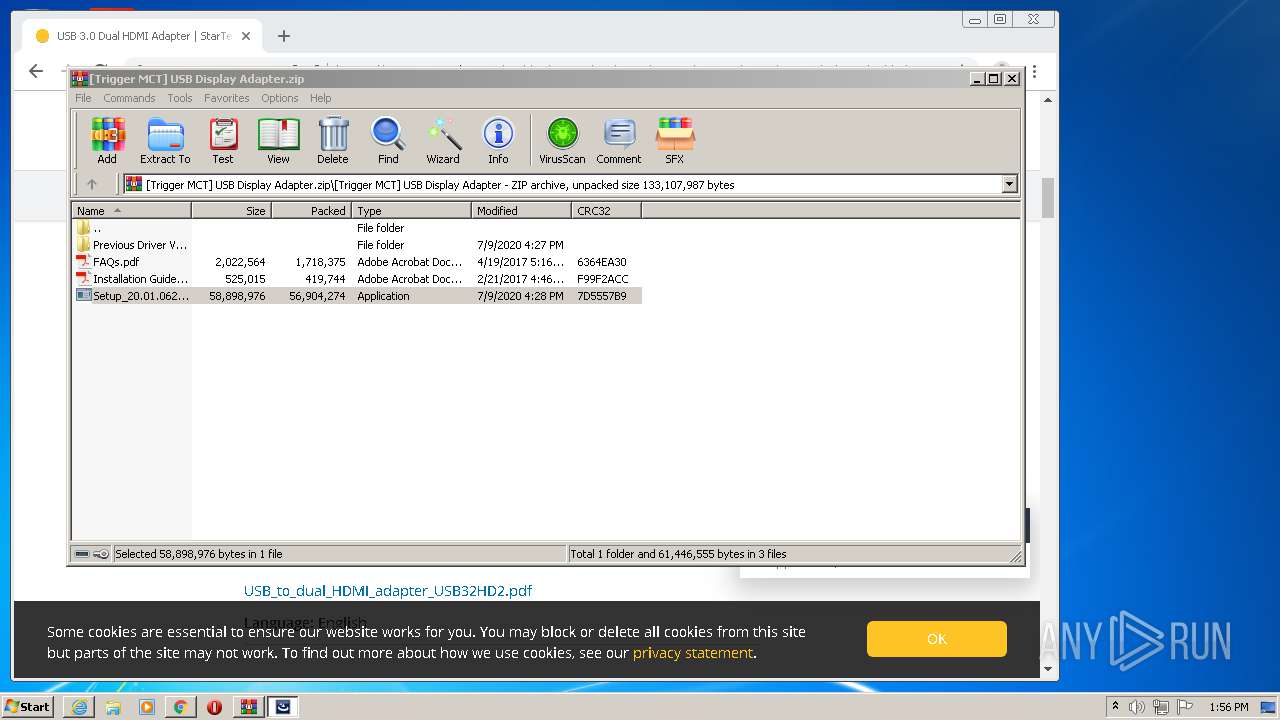
Loads dropped or rewritten executable
- Setup_20.01.0620.3679.exe (PID: 3300)
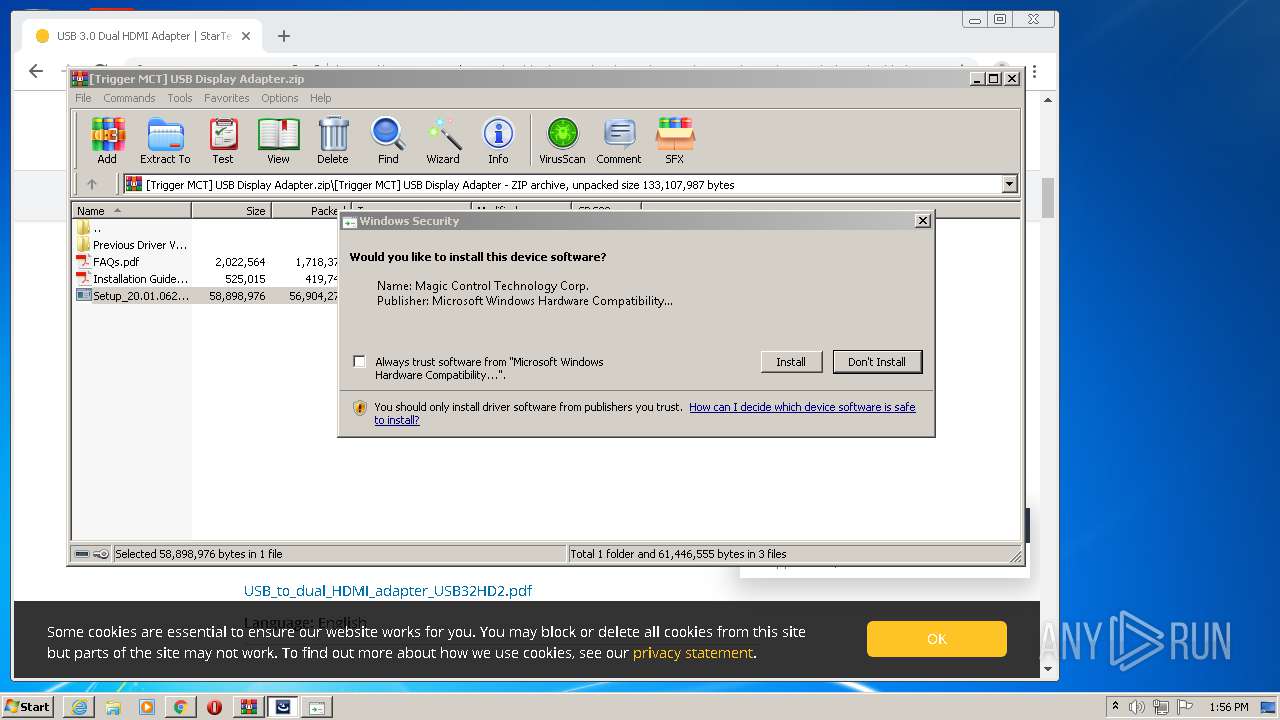
Changes settings of System certificates
- CertMgr.exe (PID: 720)
Application was dropped or rewritten from another process
- GManager.exe (PID: 2592)
- GManager.exe (PID: 1480)
- CertMgr.exe (PID: 720)
- GManager.exe (PID: 2852)
- devcon32.exe (PID: 2480)
- TUCCD.exe (PID: 3360)
- MlPatch.exe (PID: 2372)
- mlpatch.exe (PID: 1932)
- mlpatch.exe (PID: 3200)
Changes the autorun value in the registry
- Setup_20.01.0620.3679.exe (PID: 3300)
SUSPICIOUS
Reads Windows owner or organization settings
- Setup_20.01.0620.3679.exe (PID: 3300)
Reads the Windows organization settings
- Setup_20.01.0620.3679.exe (PID: 3300)
Starts CMD.EXE for commands execution
- Setup_20.01.0620.3679.exe (PID: 3300)
Executed as Windows Service
- vssvc.exe (PID: 1972)
- GManager.exe (PID: 1480)
- MlPatch.exe (PID: 2372)
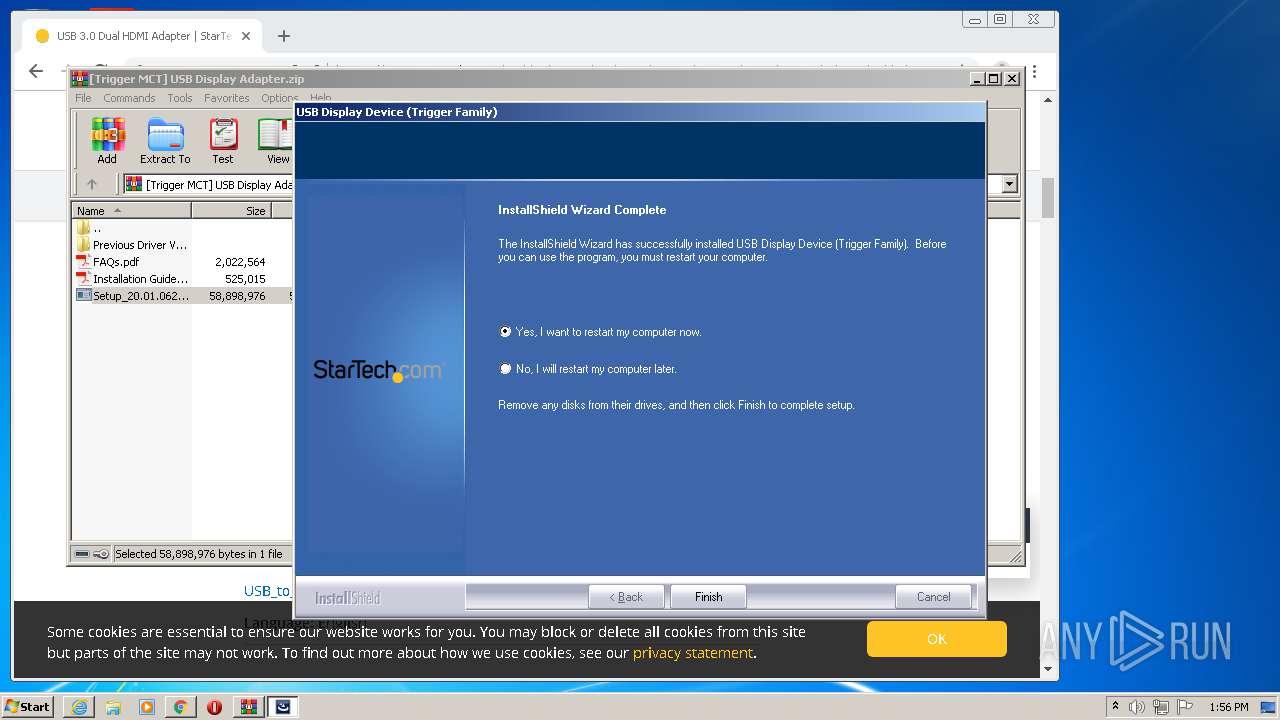
Creates a software uninstall entry
- Setup_20.01.0620.3679.exe (PID: 3300)
Creates files in the Windows directory
- GManager.exe (PID: 2852)
- Setup_20.01.0620.3679.exe (PID: 3300)
- DrvInst.exe (PID: 3084)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 1440)
Creates or modifies windows services
- Setup_20.01.0620.3679.exe (PID: 3300)
Uses TASKKILL.EXE to kill process
- Setup_20.01.0620.3679.exe (PID: 3300)
Removes files from Windows directory
- Setup_20.01.0620.3679.exe (PID: 3300)
- DrvInst.exe (PID: 3084)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 1440)
Reads Environment values
- Setup_20.01.0620.3679.exe (PID: 3300)
Starts SC.EXE for service management
- Setup_20.01.0620.3679.exe (PID: 3300)
Executable content was dropped or overwritten
- Setup_20.01.0620.3679.exe (PID: 3300)
- DrvInst.exe (PID: 3084)
- DrvInst.exe (PID: 4076)
Creates files in the driver directory
- Setup_20.01.0620.3679.exe (PID: 3300)
- DrvInst.exe (PID: 3084)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 1440)
Executed via COM
- DrvInst.exe (PID: 3084)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 1440)
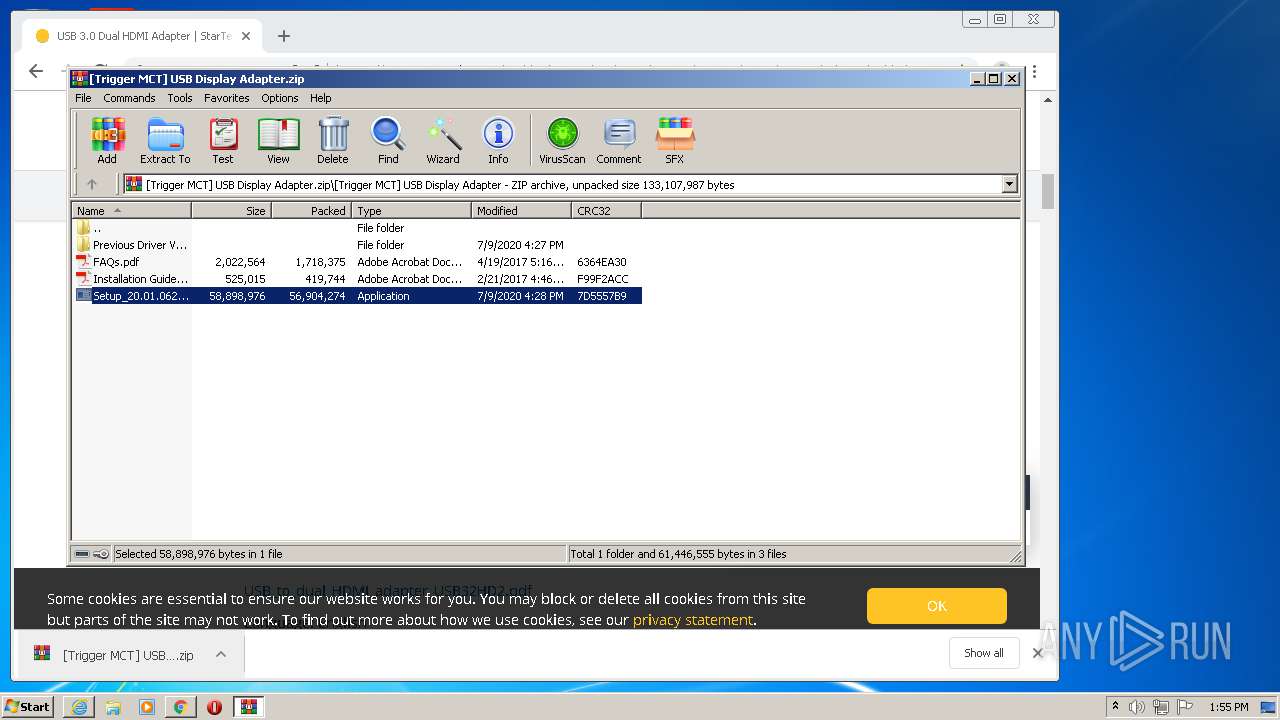
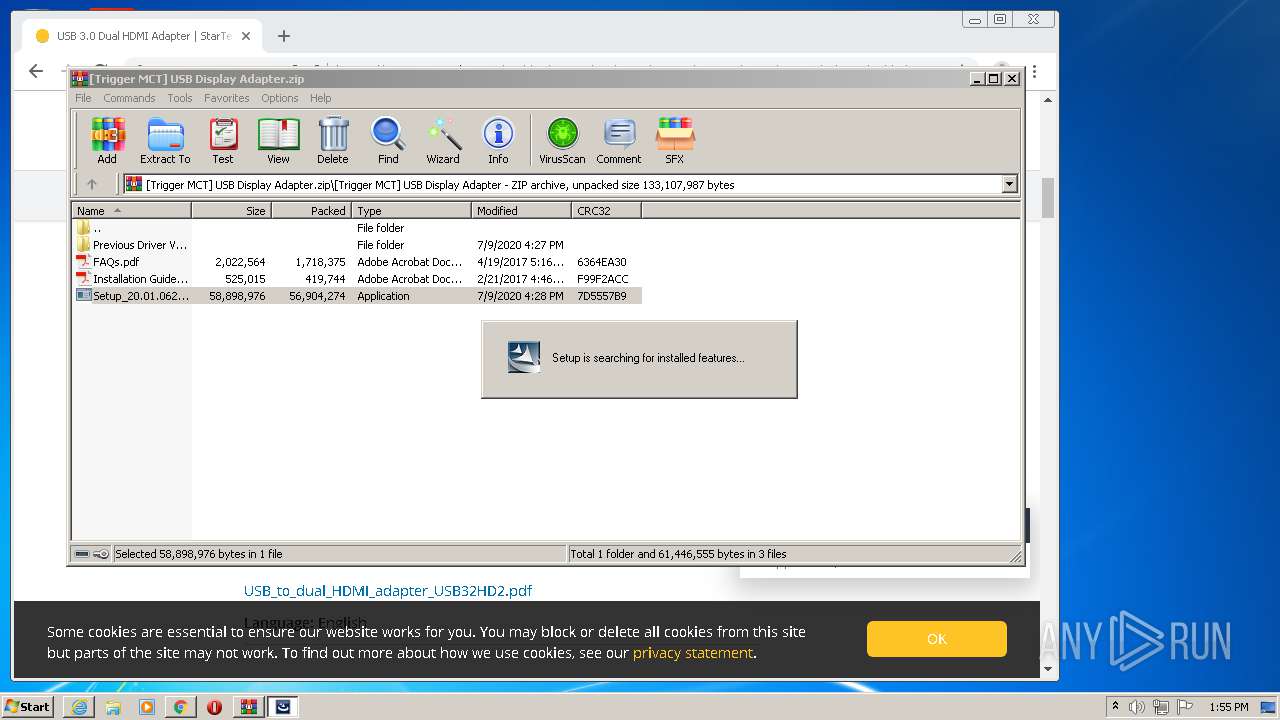
Searches for installed software
- Setup_20.01.0620.3679.exe (PID: 3300)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3084)
- DrvInst.exe (PID: 4076)
Creates files in the program directory
- Setup_20.01.0620.3679.exe (PID: 3300)
INFO
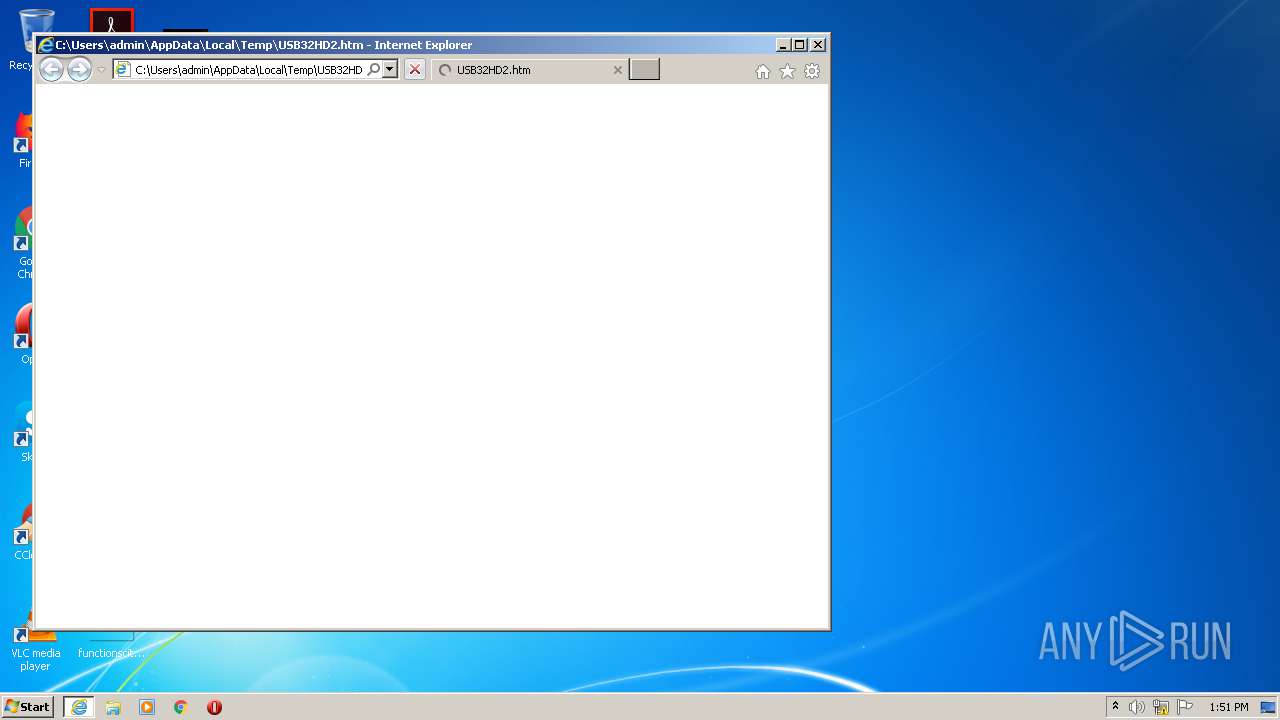
Reads Internet Cache Settings
- iexplore.exe (PID: 1624)
- chrome.exe (PID: 1496)
Changes internet zones settings
- iexplore.exe (PID: 1624)
Application launched itself
- iexplore.exe (PID: 1624)
- chrome.exe (PID: 1496)
Manual execution by user
- chrome.exe (PID: 1496)
Reads settings of System Certificates
- iexplore.exe (PID: 784)
- iexplore.exe (PID: 1624)
- chrome.exe (PID: 3688)
- DrvInst.exe (PID: 4076)
Reads internet explorer settings
- iexplore.exe (PID: 784)
Reads the hosts file
- chrome.exe (PID: 1496)
- chrome.exe (PID: 3688)
Changes settings of System certificates
- iexplore.exe (PID: 784)
- iexplore.exe (PID: 1624)
- DrvInst.exe (PID: 3084)
Creates files in the user directory
- iexplore.exe (PID: 1624)
Adds / modifies Windows certificates
- iexplore.exe (PID: 784)
- iexplore.exe (PID: 1624)
- DrvInst.exe (PID: 3084)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|---|
| HTTPEquivXUACompatible: | IE=Edge |
| viewport: | width=device-width, initial-scale=1 |
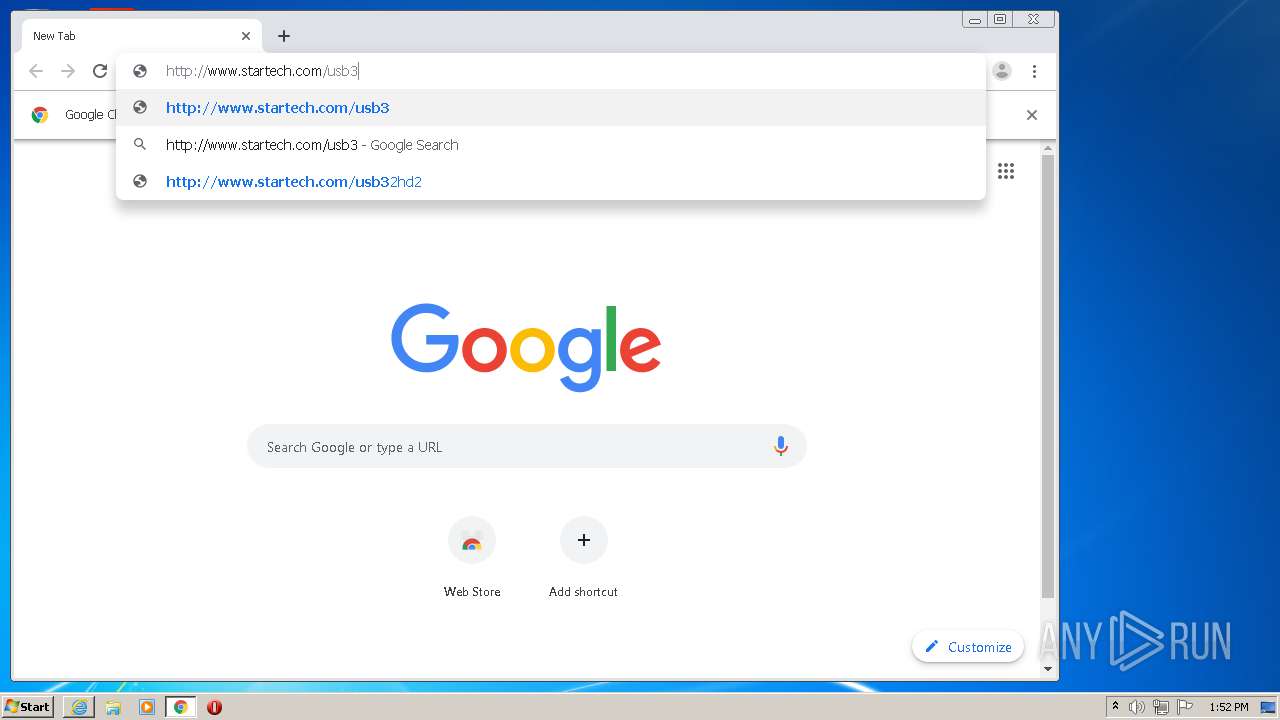
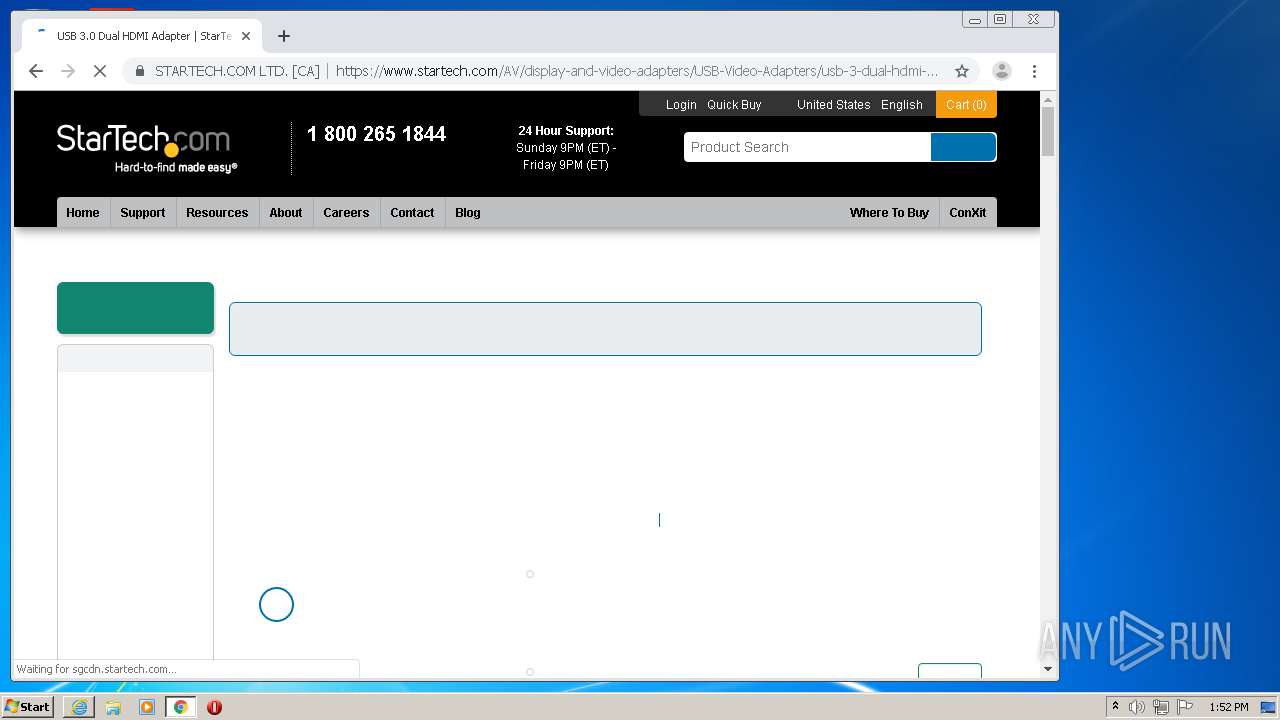
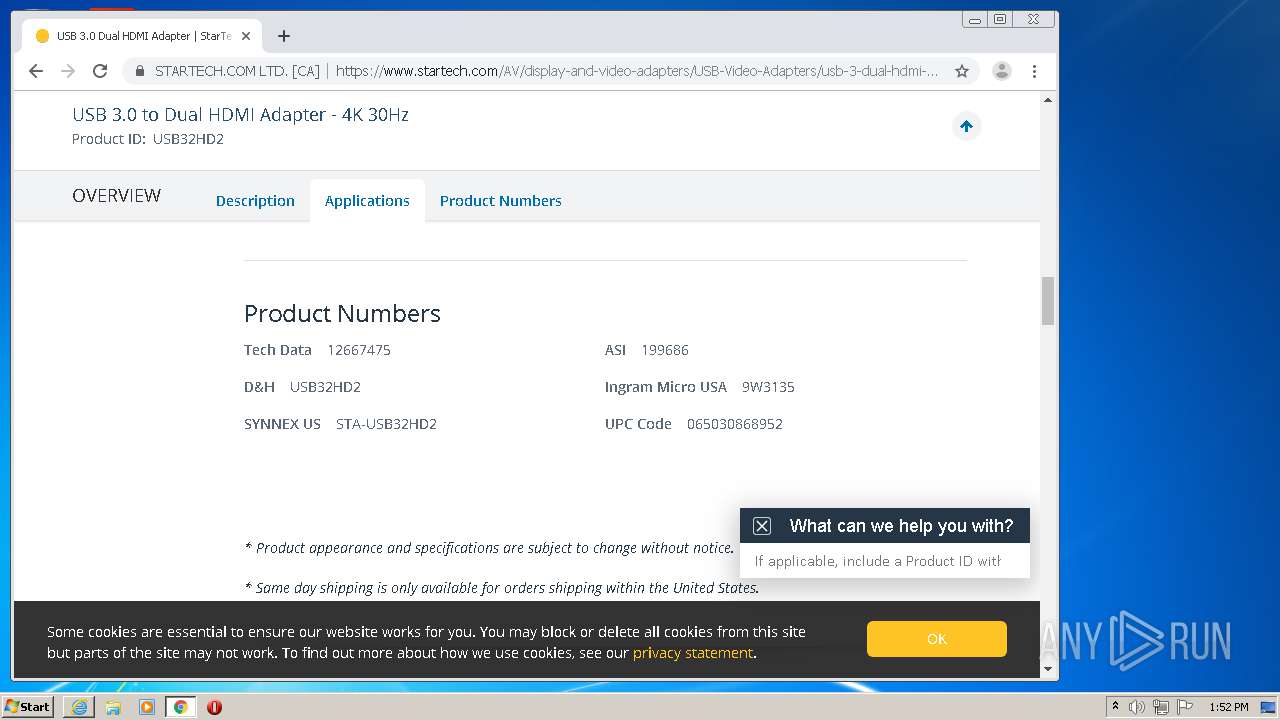
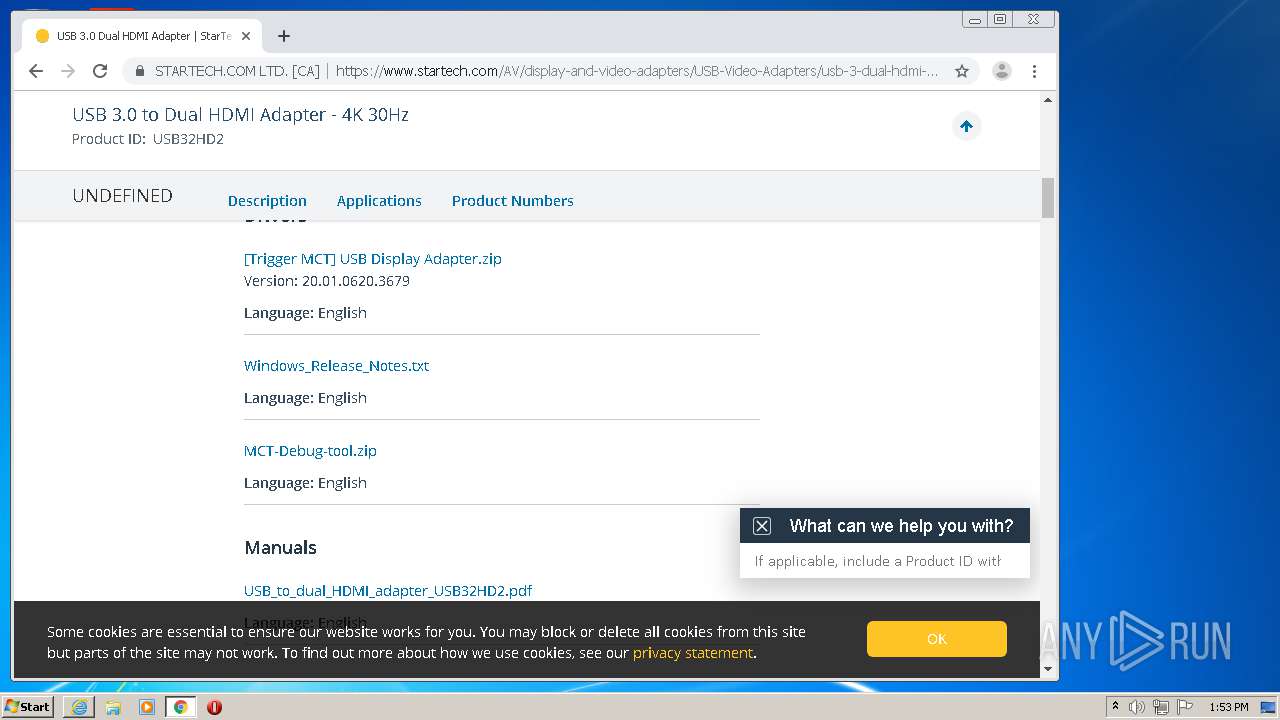
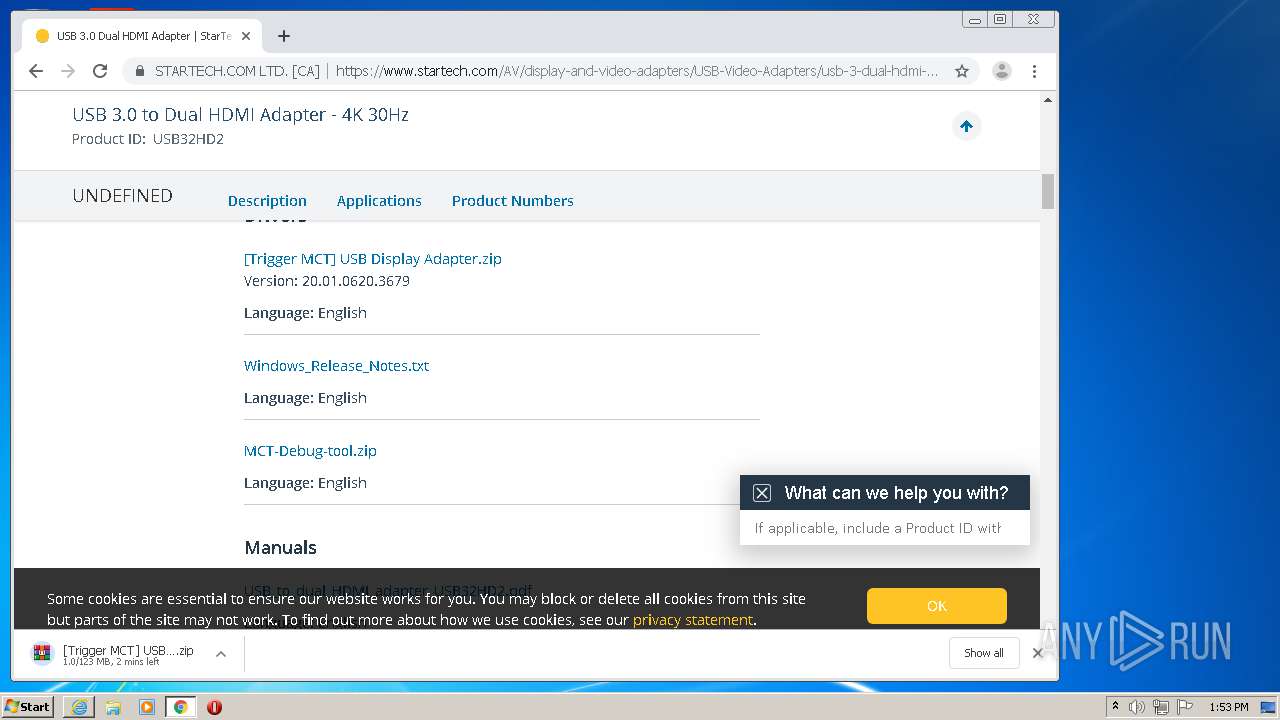
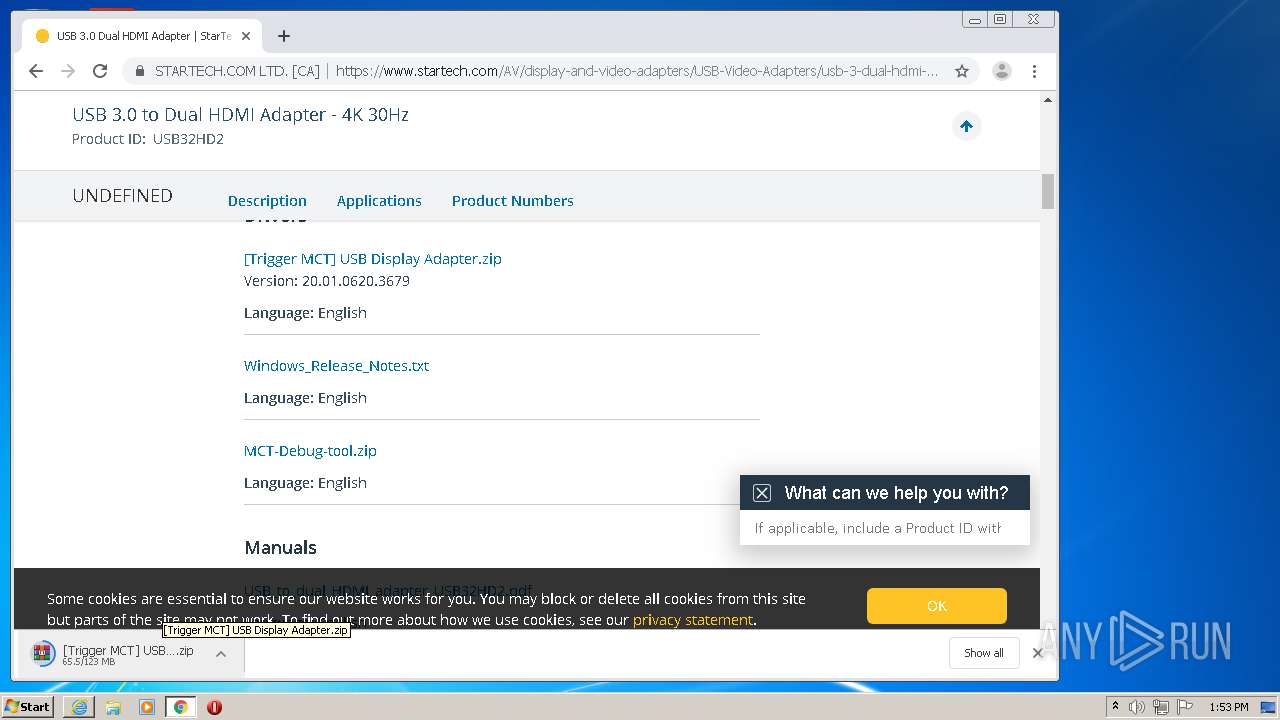
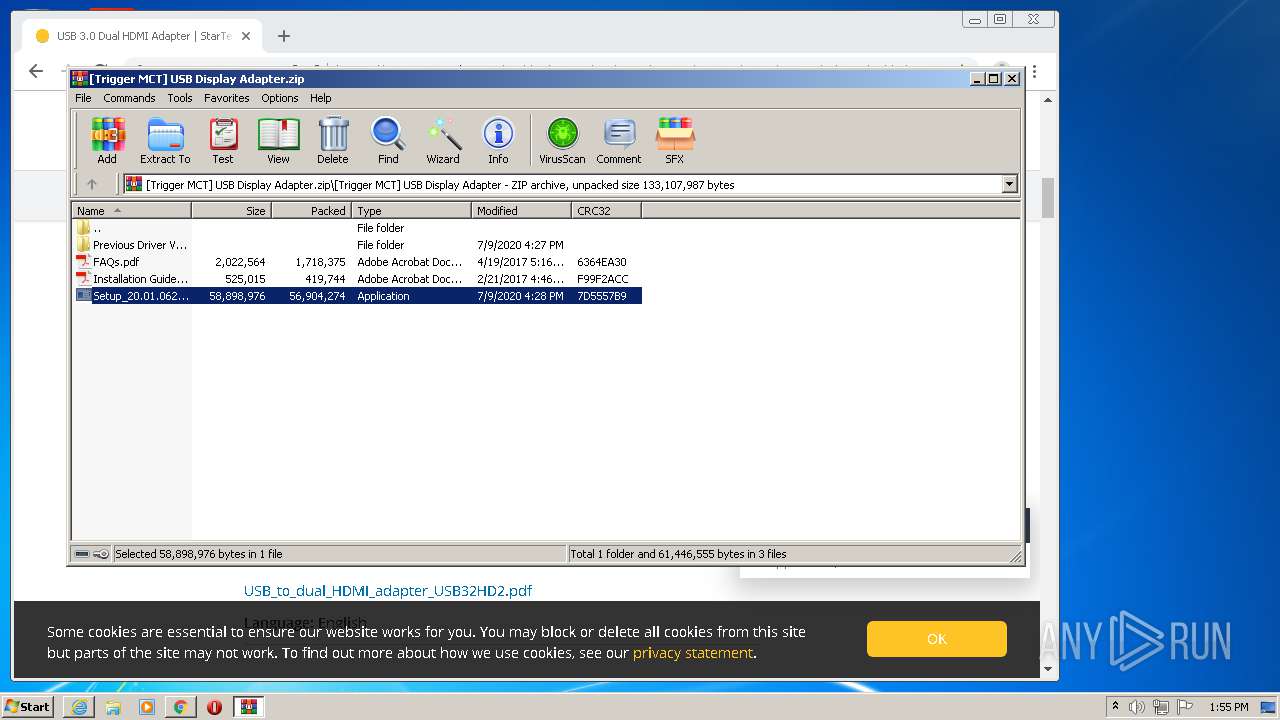
| Title: | USB 3.0 Dual HDMI Adapter | StarTech.com |
| Description: | Use this USB video adapter to connect two independent HDMI displays to a single USB port |
| formatDetection: | telephone=no |
| twitterCard: | summary_large_image |
| twitterSite: | @STARTECHdotCOM |
| twitterCreator: | @STARTECHdotCOM |
| twitterTitle: | USB 3.0 Dual HDMI Adapter | StarTech.com |
| twitterDescription: | Use this USB video adapter to connect two independent HDMI displays to a single USB port |
| twitterImage: | https://sgcdn.startech.com/005329/media/products/main/USB32HD2.Main.jpg?v=1.36 |
| msapplicationTileColor: | #2A4E6D |
| msapplicationTileImage: | https://sgcdn.startech.com/005329/media/touch-icons/apple-touch-icon-144x144-precomposed.png |
| themeColor: | #2A4E6D |
Total processes
115
Monitored processes
53
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,1959687518834645652,14229751900324614202,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10707668247046914907 --mojo-platform-channel-handle=3552 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 720 | "C:\Program Files\MCT Corp\UVTP100\Driver\CertMgr.exe" -add mct.cer -s -r localMachine -all trustedpublisher | C:\Program Files\MCT Corp\UVTP100\Driver\CertMgr.exe | — | Setup_20.01.0620.3679.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,1959687518834645652,14229751900324614202,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=34631088140979777 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1624 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 952 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{736db0f0-c2ba-0e94-6564-66350566c304} Global\{2ac8f6df-9823-530b-a476-5826f4d2e275} C:\Windows\System32\DriverStore\Temp\{292f4d42-361c-7b13-7062-4b7fbea1a879}\MctUsbVga.inf C:\Windows\System32\DriverStore\Temp\{292f4d42-361c-7b13-7062-4b7fbea1a879}\mctusbvga.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1440 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{3c67be96-329b-5e46-89d3-a77a82131d39}\T5Audio.INF" "0" "6981ccc7f" "000005CC" "WinSta0\Default" "000005AC" "208" "C:\PROGRA~1\MCTCOR~1\UVTP100\Driver\3rd\AudioFilter\Win7" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,1959687518834645652,14229751900324614202,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13535907830666306213 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1480 | C:\Windows\system32\GManager.exe | C:\Windows\system32\GManager.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: General MCT Display Service Exit code: 0 Version: 1.5.17.725 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,1959687518834645652,14229751900324614202,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=392706235299120661 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 399
Read events
2 940
Write events
453
Delete events
6
Modification events
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3969719076 | |||
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30832569 | |||
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1624) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
195
Suspicious files
232
Text files
202
Unknown types
55
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1624 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 784 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab91D9.tmp | — | |
MD5:— | SHA256:— | |||
| 784 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar91DA.tmp | — | |
MD5:— | SHA256:— | |||
| 1496 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 1496 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15b01f.TMP | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 1496 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:D11C35B3D5258F594933332C11C6F0F2 | SHA256:DC2EB16E16FA3FB258AC31A481F817208CF0C917AF4224F2832588D3A64ADD05 | |||
| 1496 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a17f8d01-c64c-4040-82a3-b71319019304.tmp | — | |
MD5:— | SHA256:— | |||
| 784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\responsive-products.min[1].css | text | |
MD5:17C42FBC50FB6130DA14978F84996848 | SHA256:DEBA2F0BB61ECD499BF9D1E3E17E6F698270C51786436F84437AA5445E0D13DC | |||
| 1496 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF15b03f.TMP | text | |
MD5:D11C35B3D5258F594933332C11C6F0F2 | SHA256:DC2EB16E16FA3FB258AC31A481F817208CF0C917AF4224F2832588D3A64ADD05 | |||
| 1496 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
91
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1624 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
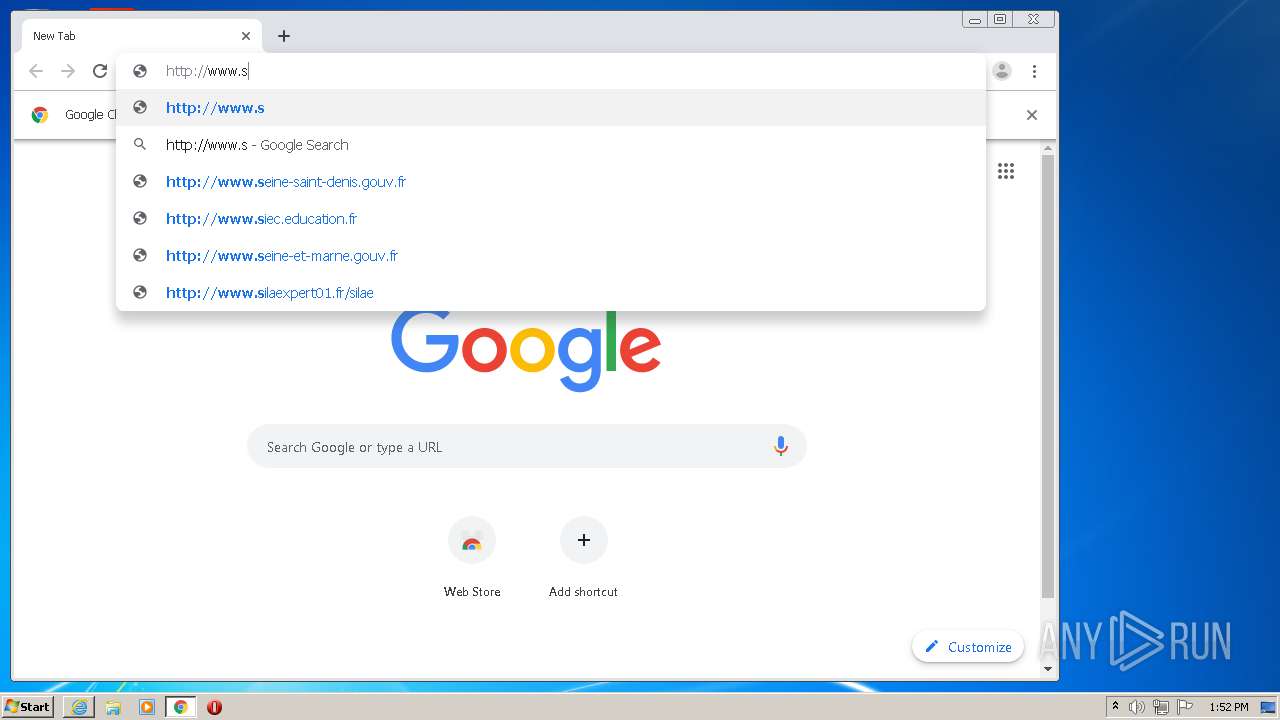
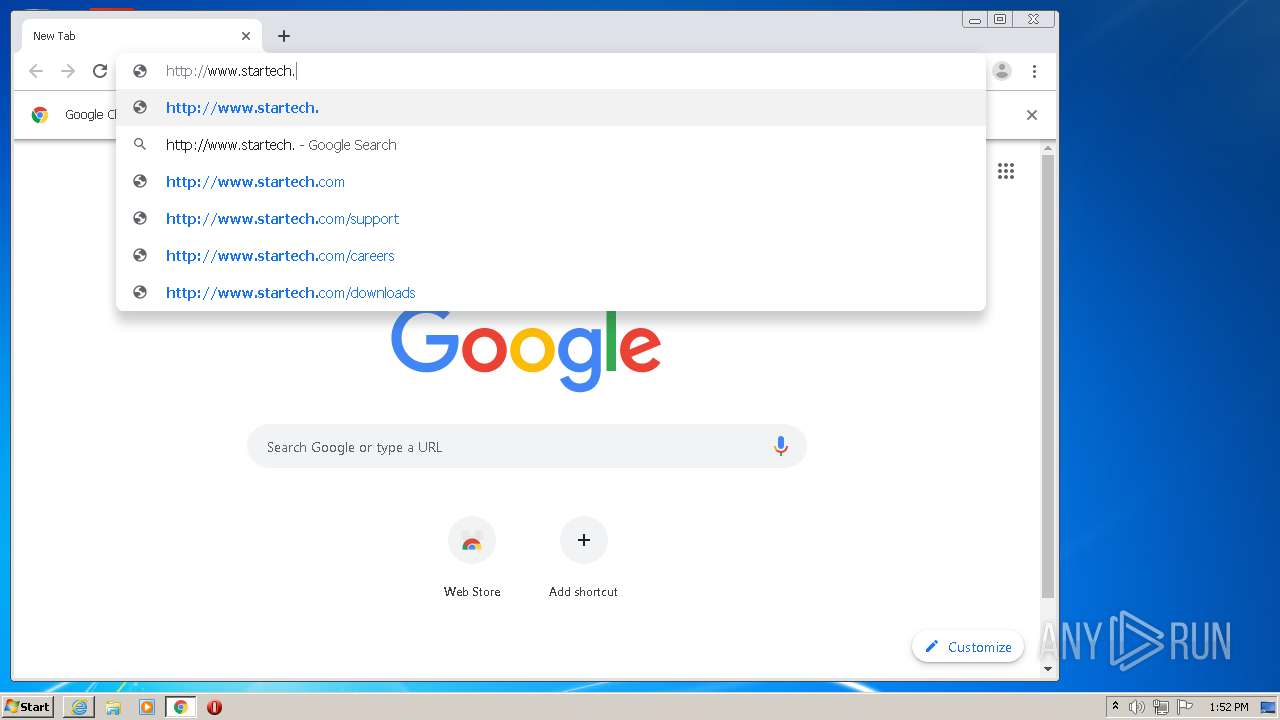
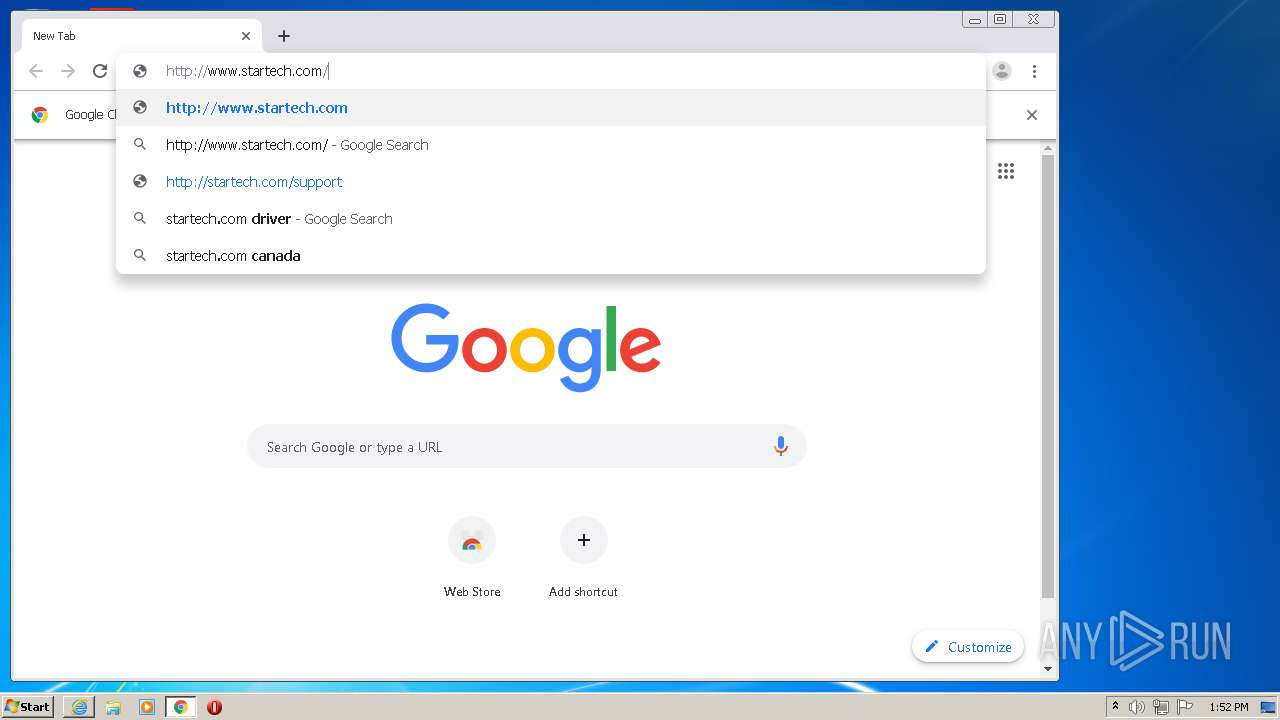
3688 | chrome.exe | GET | 301 | 54.165.34.243:80 | http://www.startech.com/usb32hd2 | US | html | 156 b | whitelisted |
784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAPSrTeI06%2B5pxhpzItJZwo%3D | US | der | 471 b | whitelisted |
784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAPSrTeI06%2B5pxhpzItJZwo%3D | US | der | 471 b | whitelisted |
784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAPSrTeI06%2B5pxhpzItJZwo%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 172.217.21.202:139 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1624 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 209.197.3.24:137 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
784 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3688 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3688 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
784 | iexplore.exe | 172.67.27.128:443 | sgcdn.startech.com | — | US | unknown |
3688 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3688 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4 | System | 172.217.21.202:445 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
netdna.bootstrapcdn.com |
| whitelisted |
seal.digicert.com |
| whitelisted |
vars.hotjar.com |
| shared |
s3.amazonaws.com |
| shared |
fonts.googleapis.com |
| whitelisted |
in.hotjar.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
script.hotjar.com |
| whitelisted |
sgcdn.startech.com |
| unknown |
code.jquery.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GManager.exe | [GManager] MCT::Service Install
|
GManager.exe | [GManager] Install service success
|
GManager.exe | [GManager] MCT::Service Run
|
GManager.exe | [GManager] DELAY_LOAD = 10000
|
GManager.exe | [GManager] DELAY_ENABLE = 0
|
GManager.exe | [GManager] Run WDDM driver mode, displayCnt = 10
|
GManager.exe | [GManager] Load C:\Windows\system32\GManager.ini file
|
GManager.exe | [GManager] loadCommon end
|
GManager.exe | [GManager] loadCommon start
|
GManager.exe | [GManager] read isAutoMapingEnable fail
|