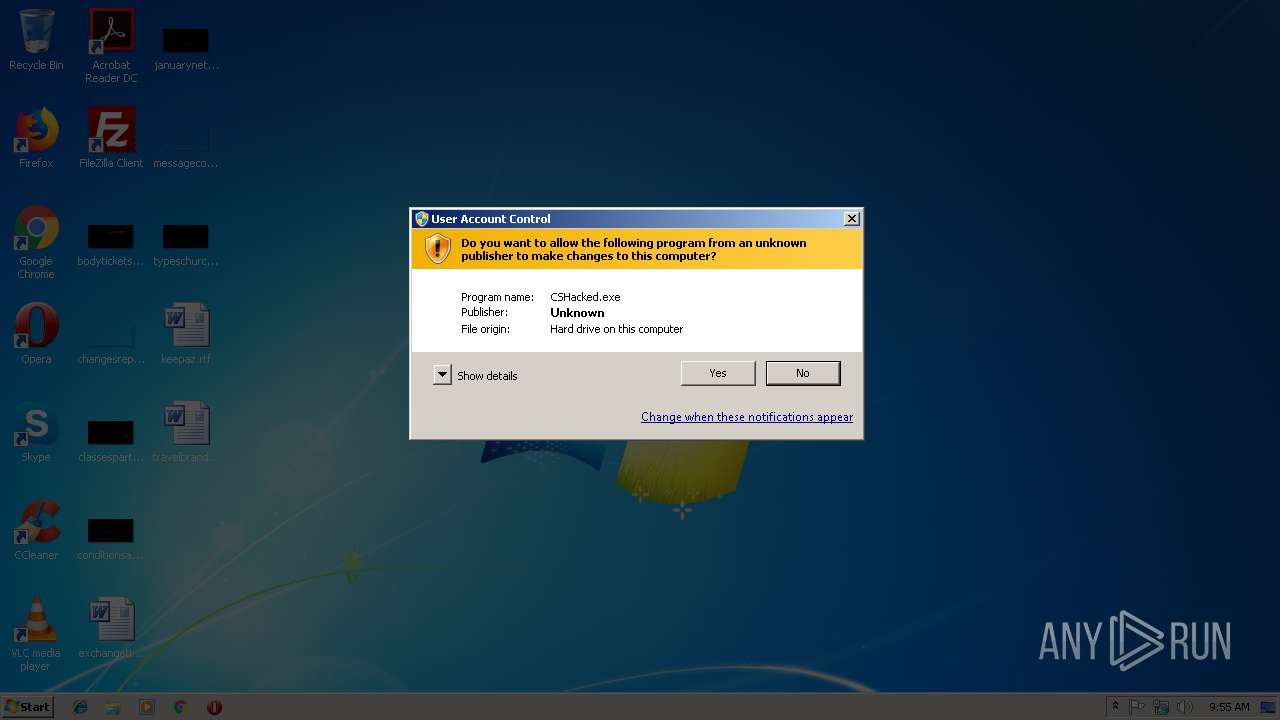
| File name: | CSHacked.exe |
| Full analysis: | https://app.any.run/tasks/75a42cd8-1d65-4f74-beae-b3139130ca53 |
| Verdict: | No threats detected |
| Analysis date: | December 10, 2018, 09:54:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5A518C818AADE52C7AD47FB04809B353 |
| SHA1: | C0DAADB74E54B6115F63E768712205D162405492 |
| SHA256: | EDF6A09082C46D9BA97358343E3B5A006E70E5033B3CEE8DEBF21DDC21B6276E |
| SSDEEP: | 98304:HvyoMlyljUTMh0Pb/aIi2hiAsjKFTWp2r25LmGAymfh3M+5X3BvMX2u1:HKNyGTnPb/ziWFxnC5CBfh3MqM1 |
MALICIOUS
Application was dropped or rewritten from another process
- CSHacked.exe (PID: 3096)
SUSPICIOUS
Executable content was dropped or overwritten
- CSHacked.exe (PID: 3548)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:28 16:45:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 36352 |
| InitializedDataSize: | 5466112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x15eb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Jun-2013 14:45:44 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 28-Jun-2013 14:45:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008D54 | 0x00008E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56215 |
.rdata | 0x0000A000 | 0x00002114 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.44357 |
.data | 0x0000D000 | 0x00002ADC | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.1026 |
.rsrc | 0x00010000 | 0x00532464 | 0x00532600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98753 |
.reloc | 0x00543000 | 0x00000EEA | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.32883 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.77792 | 357 | Latin 1 / Western European | English - United States | RT_MANIFEST |
101 | 7.92233 | 4118 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
ARCHIVE | 7.99535 | 5178419 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
DECOMPRESSOR | 6.11488 | 194048 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
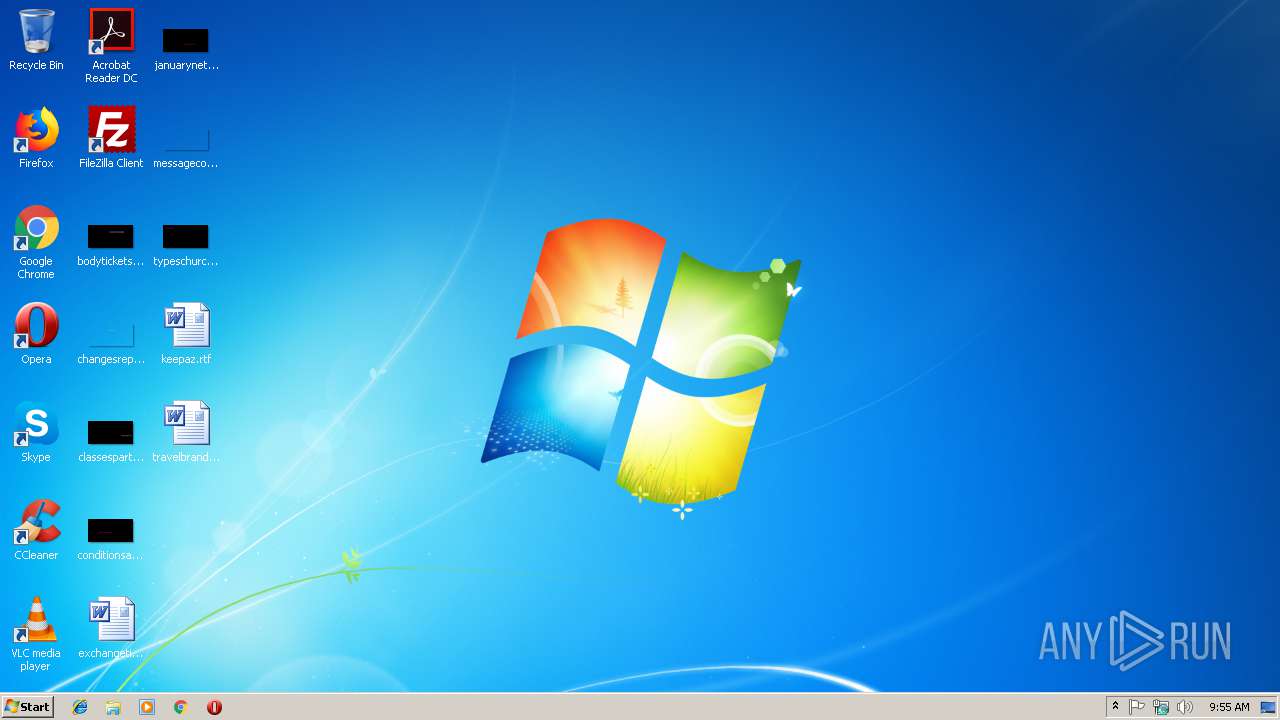
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3096 | "C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\CSHacked.exe" -ORIGIN:"C:\Users\admin\AppData\Local\Temp\" | C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\CSHacked.exe | — | CSHacked.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3220 | "C:\Users\admin\AppData\Local\Temp\CSHacked.exe" | C:\Users\admin\AppData\Local\Temp\CSHacked.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 3548 | "C:\Users\admin\AppData\Local\Temp\CSHacked.exe" | C:\Users\admin\AppData\Local\Temp\CSHacked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | CSHacked.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\CET_Archive.dat | — | |
MD5:— | SHA256:— | |||
| 3096 | CSHacked.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\extracted\CSHacked.exe | — | |
MD5:— | SHA256:— | |||
| 3096 | CSHacked.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\extracted\lua53-64.dll | — | |
MD5:— | SHA256:— | |||
| 3096 | CSHacked.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\extracted\vehdebug-x86_64.dll | — | |
MD5:— | SHA256:— | |||
| 3096 | CSHacked.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\extracted\autorun\luasymbols.lua | — | |
MD5:— | SHA256:— | |||
| 3096 | CSHacked.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\extracted\CET_TRAINER.CETRAINER | binary | |
MD5:— | SHA256:— | |||
| 3548 | CSHacked.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\CSHacked.exe | executable | |
MD5:A65C29111A4CF5A7FDD5A9D79F77BCAB | SHA256:DAB3003436B6861AE220CC5FDCB97970FC05AFDF114C2F91E46EED627CE3D6AF | |||
| 3096 | CSHacked.exe | C:\Users\admin\AppData\Local\Temp\cetrainers\CETA59C.tmp\extracted\defines.lua | text | |
MD5:11262EE8C196ED4E1E0E65C1D1CA3B9F | SHA256:9ADB8DED37012DBD1CA984F89338BA555C809272BB5456E650713532D3D9B4A1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report