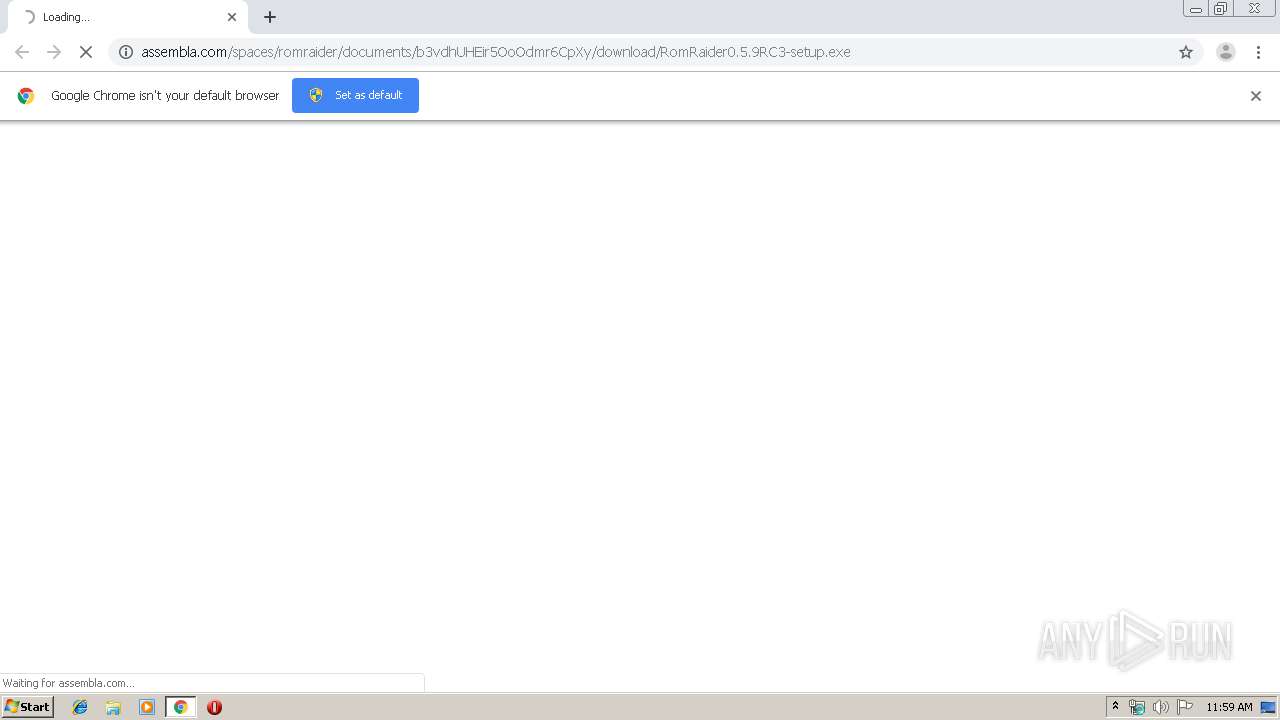
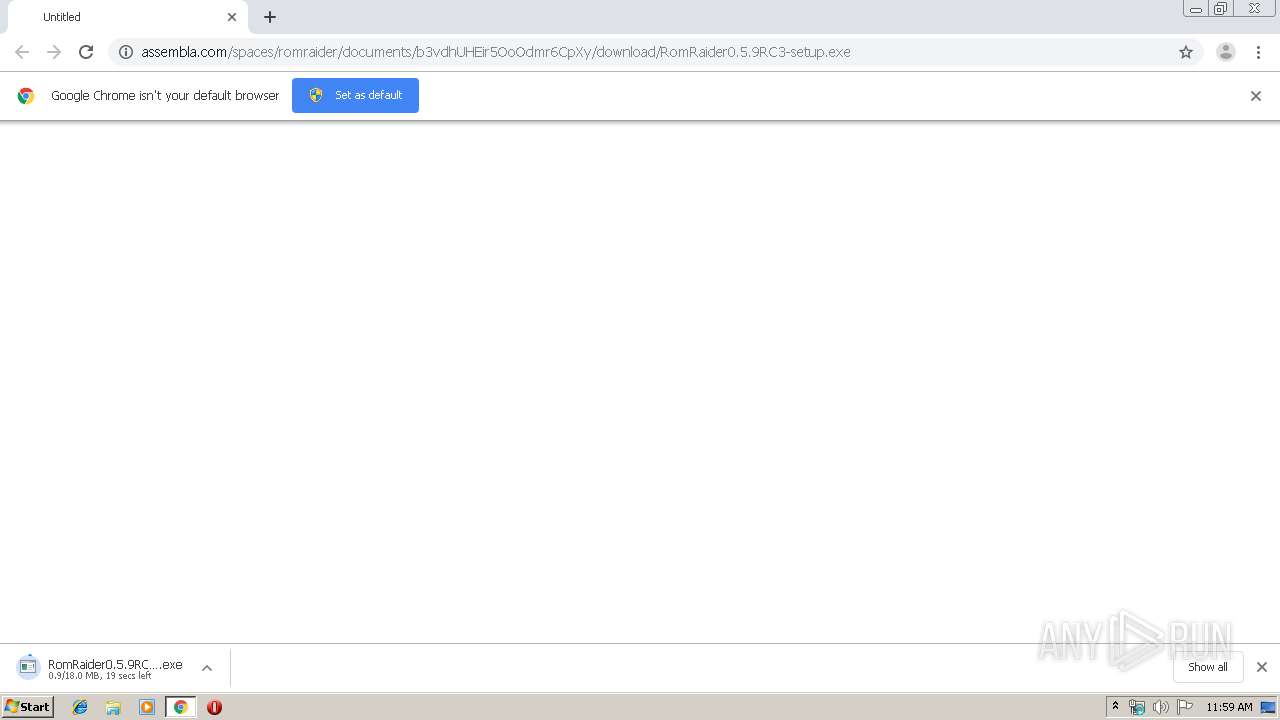
| URL: | http://assembla.com/spaces/romraider/documents/b3vdhUHEir5OoOdmr6CpXy/download/RomRaider0.5.9RC3-setup.exe |
| Full analysis: | https://app.any.run/tasks/89a527a3-56b8-4ce0-9290-4deaeeae0676 |
| Verdict: | Malicious activity |
| Analysis date: | August 28, 2019, 10:58:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 482437BA34704B2CEEF2385D9F5D063E |
| SHA1: | F650E6A2745D474968C6E1DD30E8E30D1076BD02 |
| SHA256: | EDF2EC1807133BC5DA27C5A2E922C01AD637B232485DB062884933035F58A0F2 |
| SSDEEP: | 3:N1KfHKeGQpRVWfwSWCqOecaK4mLbycQIWQA:CfDJ9SWCHe+nA |
MALICIOUS
Application was dropped or rewritten from another process
- RomRaider0.5.9RC3-setup.exe (PID: 3012)
- RomRaider0.5.9RC3-setup.exe (PID: 2676)
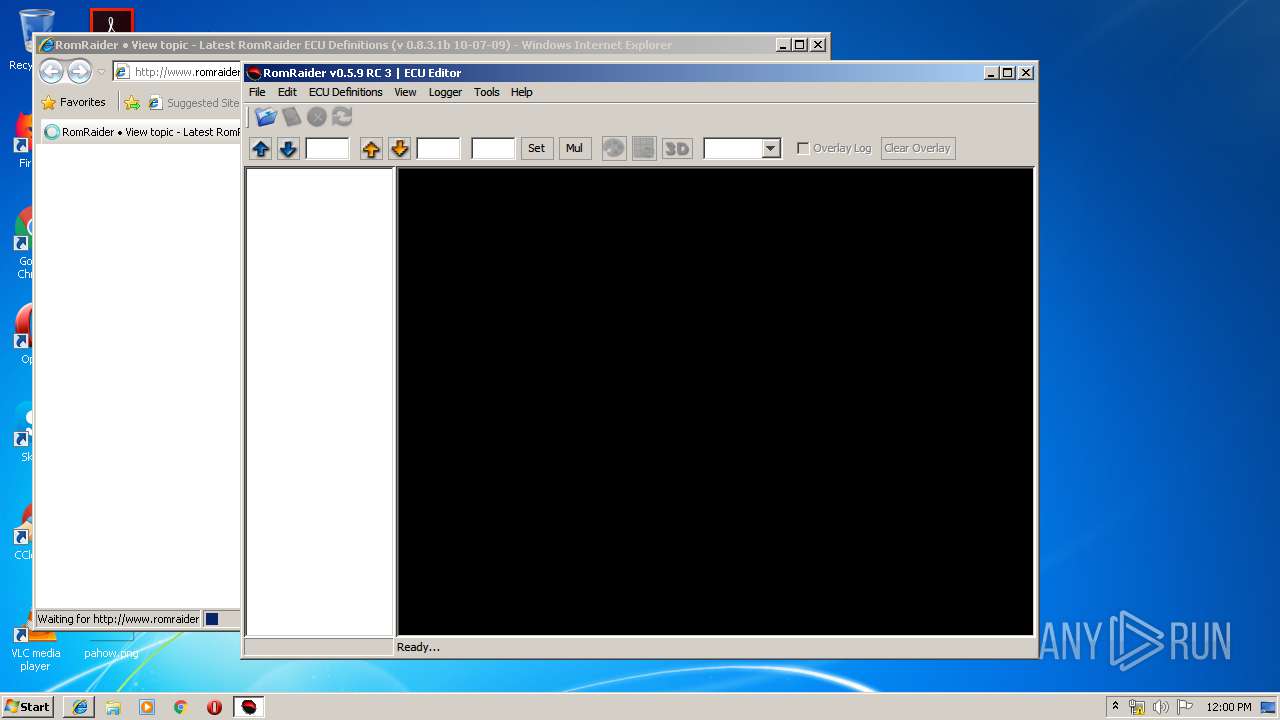
- RomRaider.exe (PID: 3356)
Loads dropped or rewritten executable
- javaw.exe (PID: 2356)
SUSPICIOUS
Starts CMD.EXE for commands execution
- javaw.exe (PID: 2356)
Executable content was dropped or overwritten
- chrome.exe (PID: 3700)
- chrome.exe (PID: 2924)
- javaw.exe (PID: 2356)
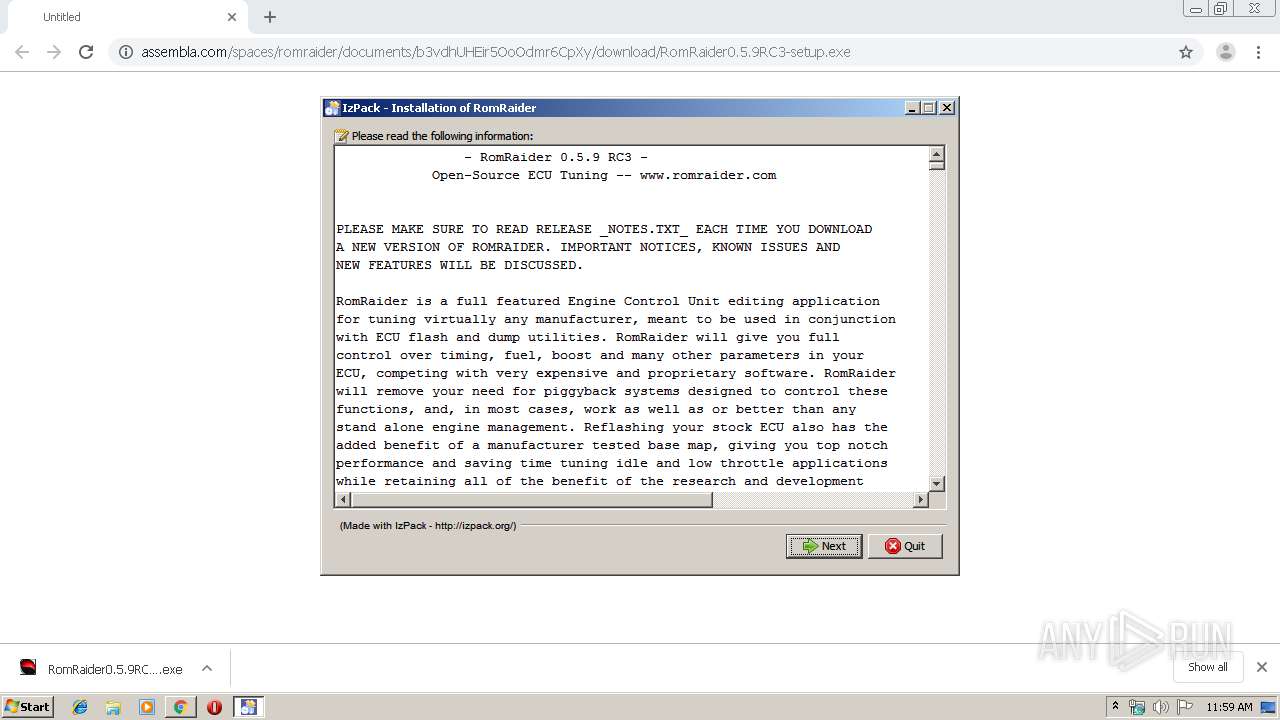
Executes JAVA applets
- RomRaider0.5.9RC3-setup.exe (PID: 2676)
- javaw.exe (PID: 2356)
- RomRaider.exe (PID: 3356)
Creates files in the user directory
- javaw.exe (PID: 2356)
Starts Internet Explorer
- javaw.exe (PID: 2076)
Creates files in the program directory
- javaw.exe (PID: 2356)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2924)
Application launched itself
- chrome.exe (PID: 3700)
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 2356)
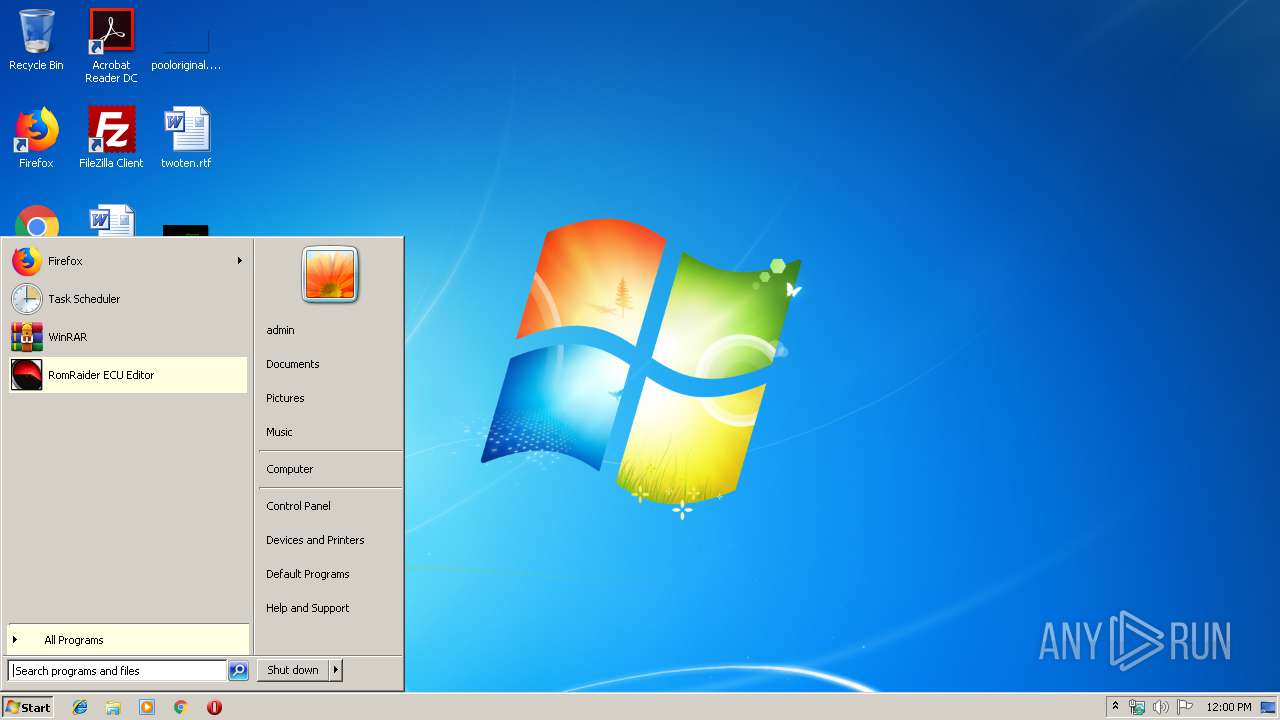
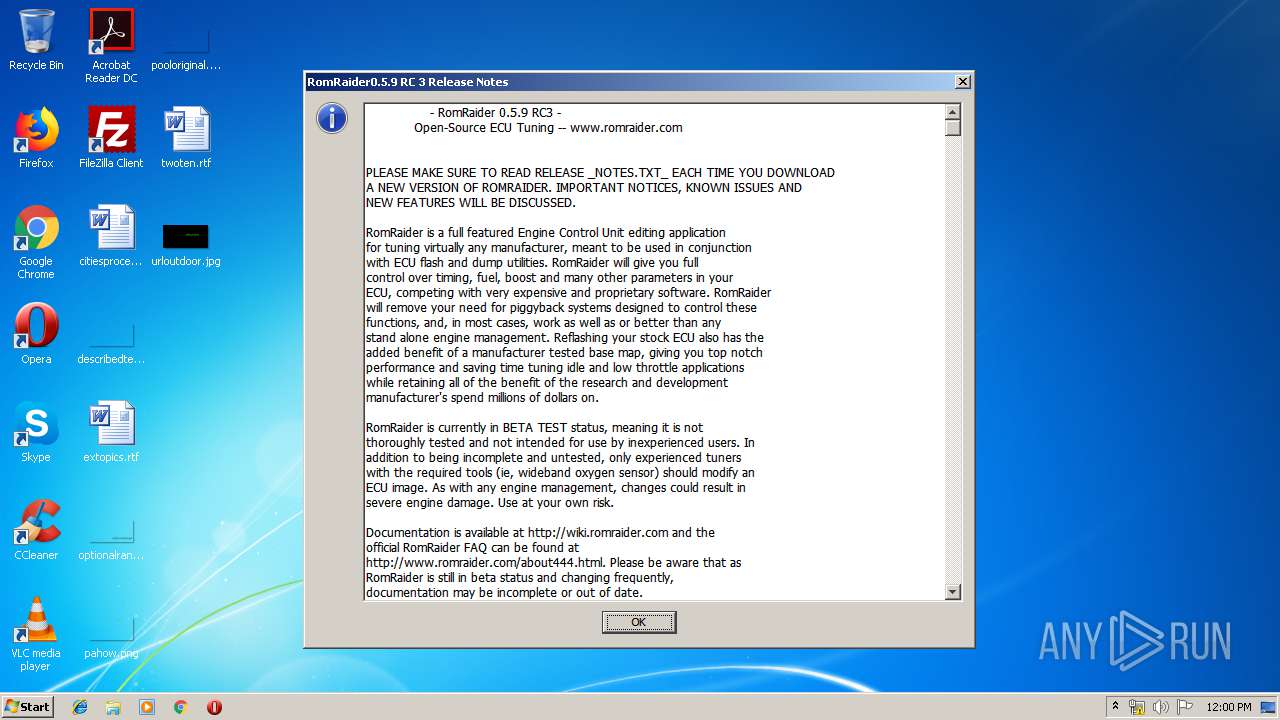
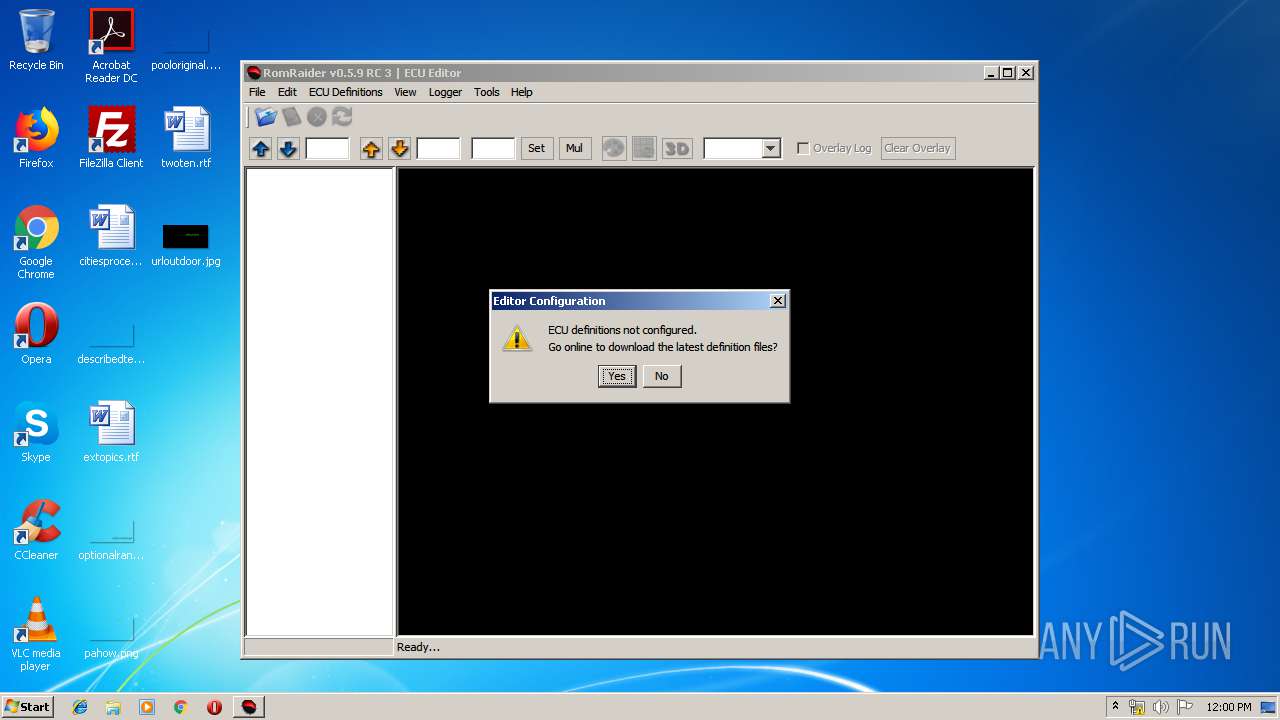
Manual execution by user
- RomRaider.exe (PID: 3356)
Reads Internet Cache Settings
- chrome.exe (PID: 3700)
- iexplore.exe (PID: 3784)
Changes internet zones settings
- iexplore.exe (PID: 2748)
Creates files in the user directory
- iexplore.exe (PID: 3784)
Reads internet explorer settings
- iexplore.exe (PID: 3784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
22
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2076 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Djava.library.path=lib/windows -Dawt.useSystemAAFontSettings=lcd -Dswing.aatext=true -Dsun.java2d.d3d=true -Xms64M -Xmx512M -jar "C:\Program Files\RomRaider\RomRaider.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | RomRaider.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Djava.library.path=lib/windows -Dawt.useSystemAAFontSettings=lcd -Dswing.aatext=true -Dsun.java2d.d3d=true -Xms64M -Xmx512M -jar "C:\Users\admin\Downloads\RomRaider0.5.9RC3-setup.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | RomRaider0.5.9RC3-setup.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6368283445346356759 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fdea9d0,0x6fdea9e0,0x6fdea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2548 | cmd.exe /C "dir /D /-C "C:\Program Files"" | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2676 | "C:\Users\admin\Downloads\RomRaider0.5.9RC3-setup.exe" | C:\Users\admin\Downloads\RomRaider0.5.9RC3-setup.exe | chrome.exe | ||||||||||||
User: admin Company: RomRaider.com Integrity Level: HIGH Description: RomRaider Exit code: 259 Version: 0.5.9 RC 3 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | javaw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14678868156050061714 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6660624486099013222 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
1 437
Read events
1 341
Write events
93
Delete events
3
Modification events
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3700-13211463554679125 |
Value: 259 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
30
Suspicious files
39
Text files
607
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\72c7eef3-af6d-40d3-89d1-e8b83be8a996.tmp | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169c73.TMP | text | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF169d6d.TMP | text | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169cc1.TMP | text | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF169cf0.TMP | text | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
16
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3784 | iexplore.exe | GET | — | 192.254.186.252:80 | http://www.romraider.com/forum/reimg/highslide/highslide.css | US | — | — | unknown |
3784 | iexplore.exe | GET | — | 192.254.186.252:80 | http://www.romraider.com/forum/reimg/reimg.js | US | — | — | unknown |
3784 | iexplore.exe | GET | — | 192.254.186.252:80 | http://www.romraider.com/forum/reimg/highslide/highslide-full.packed.js | US | — | — | unknown |
3784 | iexplore.exe | GET | — | 192.254.186.252:80 | http://www.romraider.com/forum/styles/fisubsilver2/theme/stylesheet.css | US | — | — | unknown |
3784 | iexplore.exe | GET | 200 | 192.254.186.252:80 | http://www.romraider.com/forum/topic360.html | US | html | 25.8 Kb | unknown |
2748 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2924 | chrome.exe | GET | 301 | 104.16.80.48:80 | http://assembla.com/spaces/romraider/documents/b3vdhUHEir5OoOdmr6CpXy/download/RomRaider0.5.9RC3-setup.exe | US | html | 171 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2924 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 104.16.80.48:80 | assembla.com | Cloudflare Inc | US | shared |
2924 | chrome.exe | 104.16.80.48:443 | assembla.com | Cloudflare Inc | US | shared |
2924 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
3784 | iexplore.exe | 192.254.186.252:80 | www.romraider.com | Unified Layer | US | unknown |
2924 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2924 | chrome.exe | 172.217.23.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2748 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
assembla.com |
| whitelisted |
accounts.google.com |
| shared |
www.assembla.com |
| unknown |
app.assembla.com |
| unknown |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.romraider.com |
| unknown |