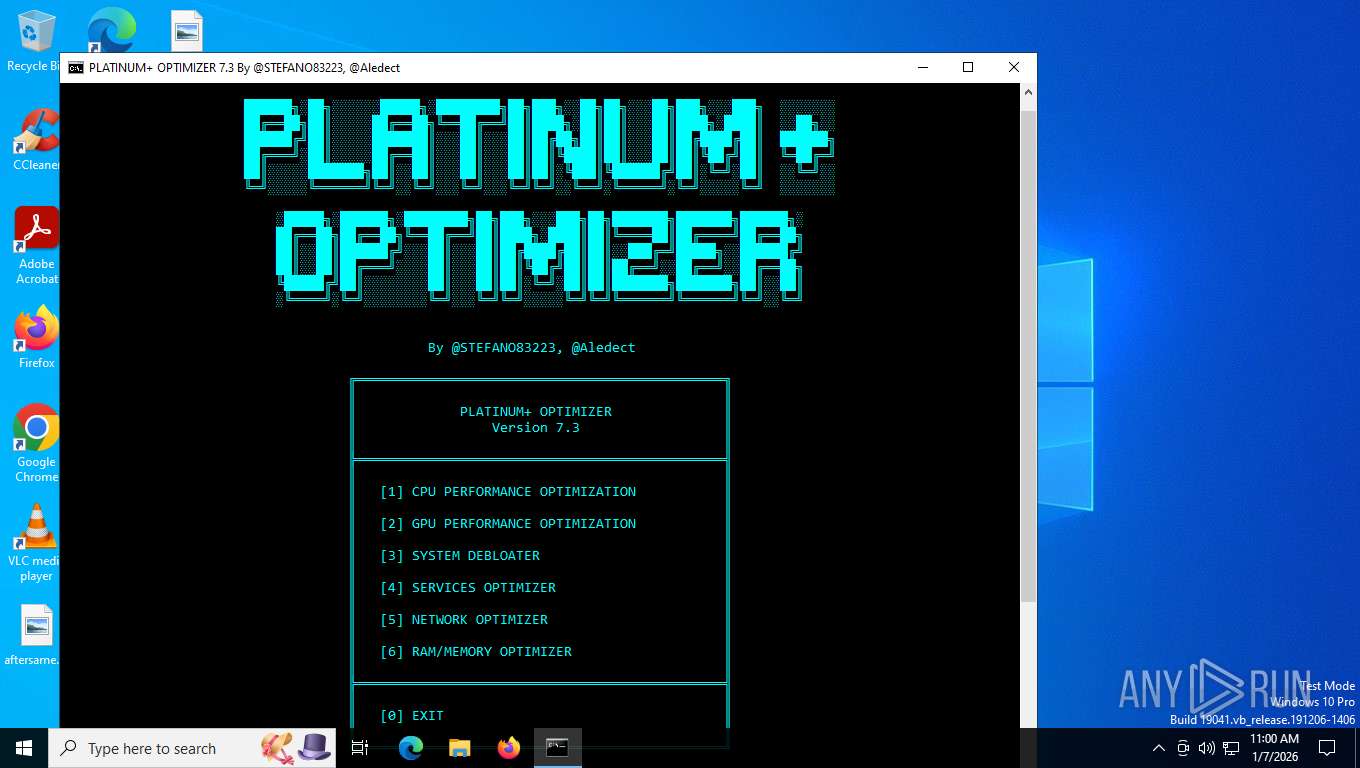
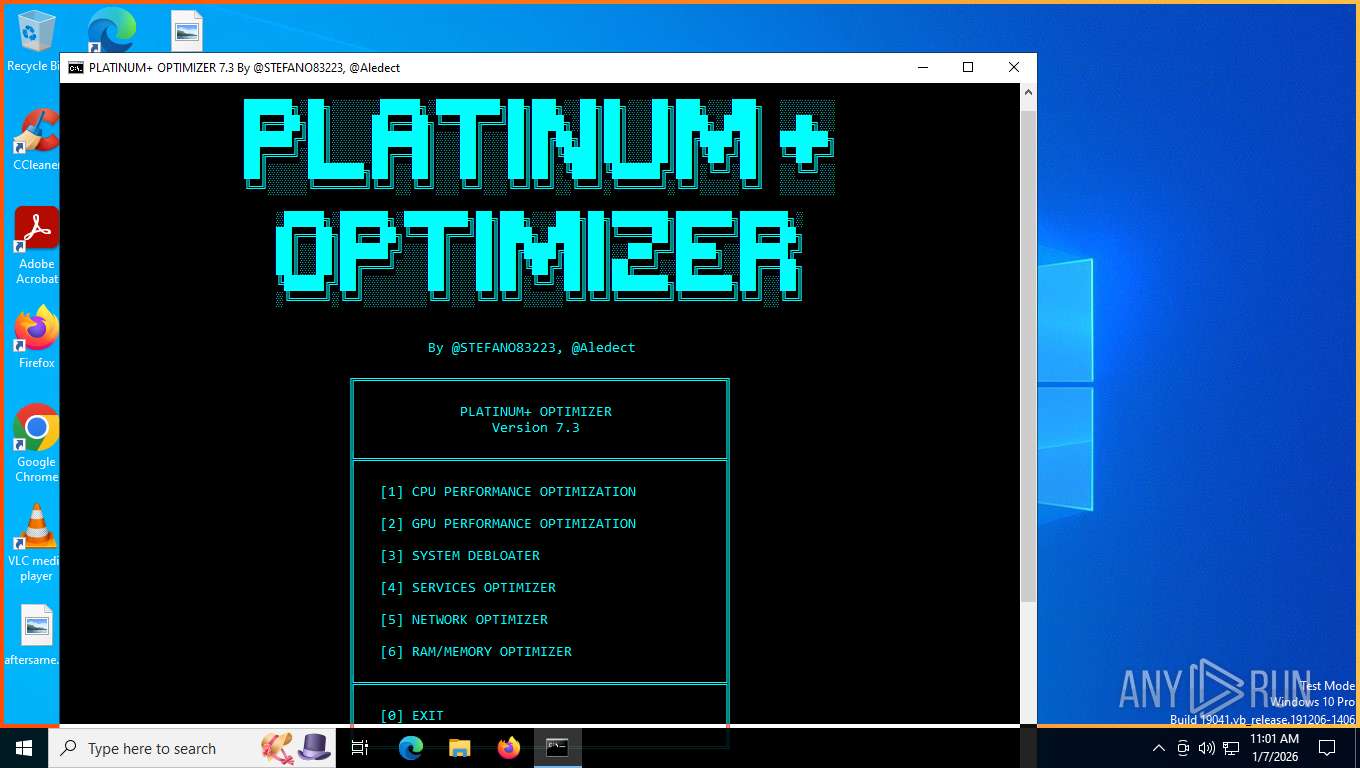
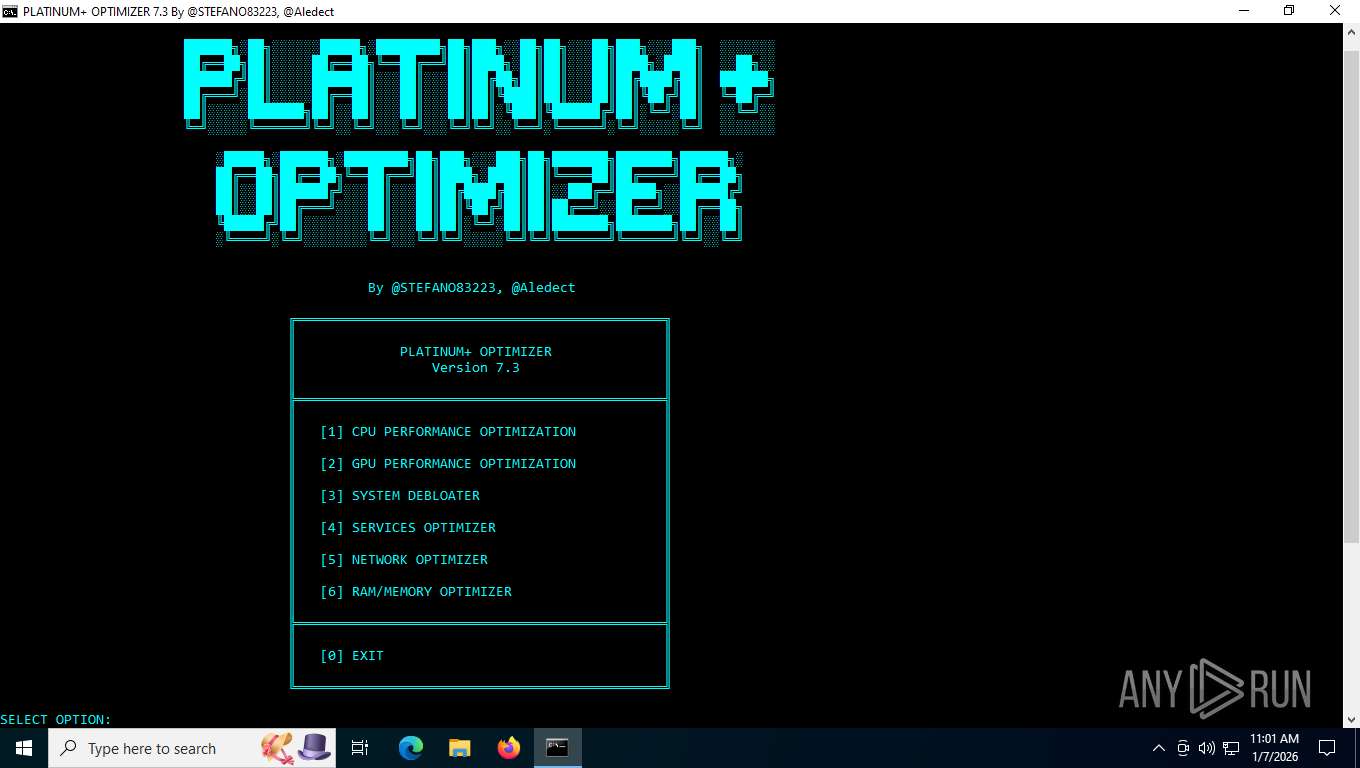
| File name: | Platinum+Optimizer.7.3.By.@STEFANO83223.@Aledect.bat |
| Full analysis: | https://app.any.run/tasks/7b3b3302-4897-441d-88f4-2e687702cc94 |
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2026, 16:00:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | DEF94DDF50DBDFA81E19A289BCC38BAD |
| SHA1: | 6F58F1B0AC6947C0C17461A49AD086D5AACF82EE |
| SHA256: | EDF1256A86286C2432FAC586D43471B643F798B63B4AB6403ECB279360546953 |
| SSDEEP: | 3072:Ht0NlFycYGN5xN59N5CN5fN5Iw0RtBWBWMWLWFW9WIWeWGWJW1WsWDW4W/WKWaWS:HtSycvN5xN59N5CN5fN5l0Rt/ |
MALICIOUS
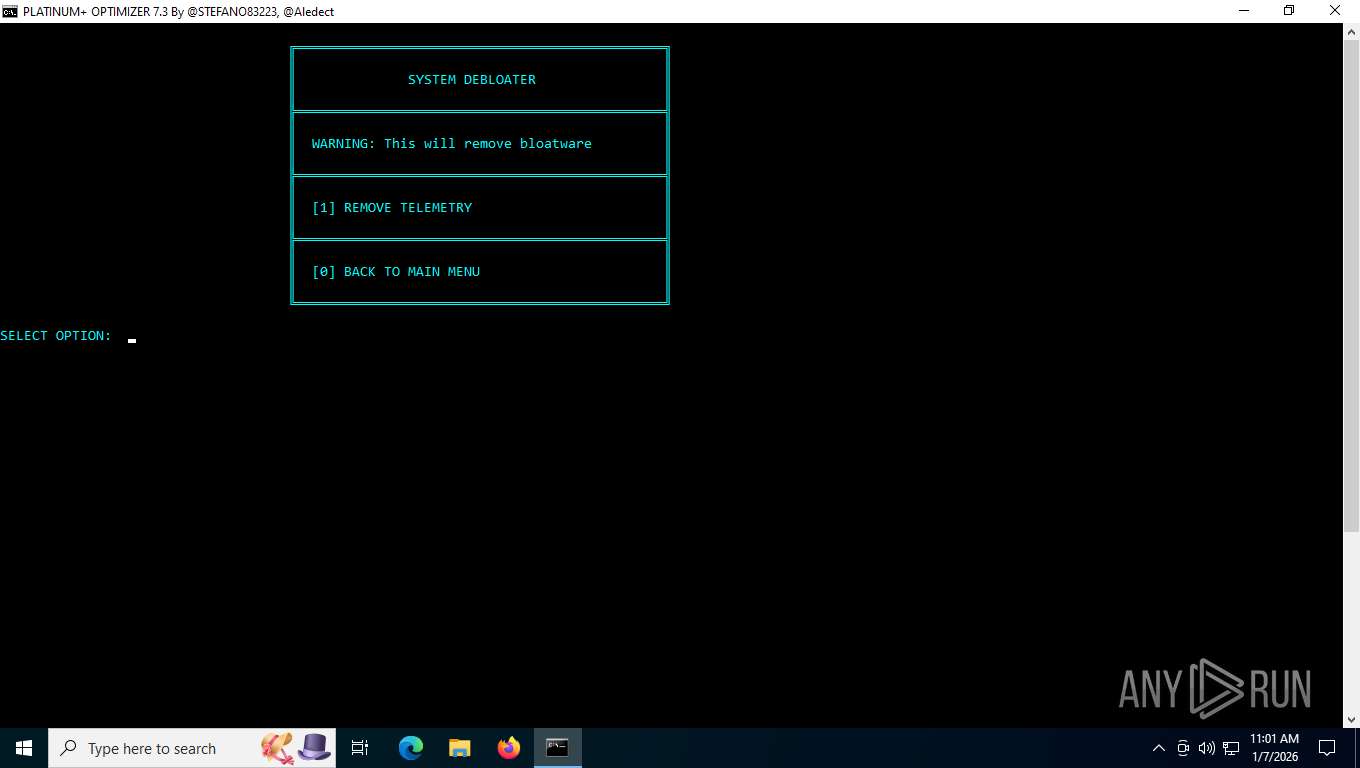
Changes powershell execution policy (Unrestricted)
- cmd.exe (PID: 7496)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 7496)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7496)
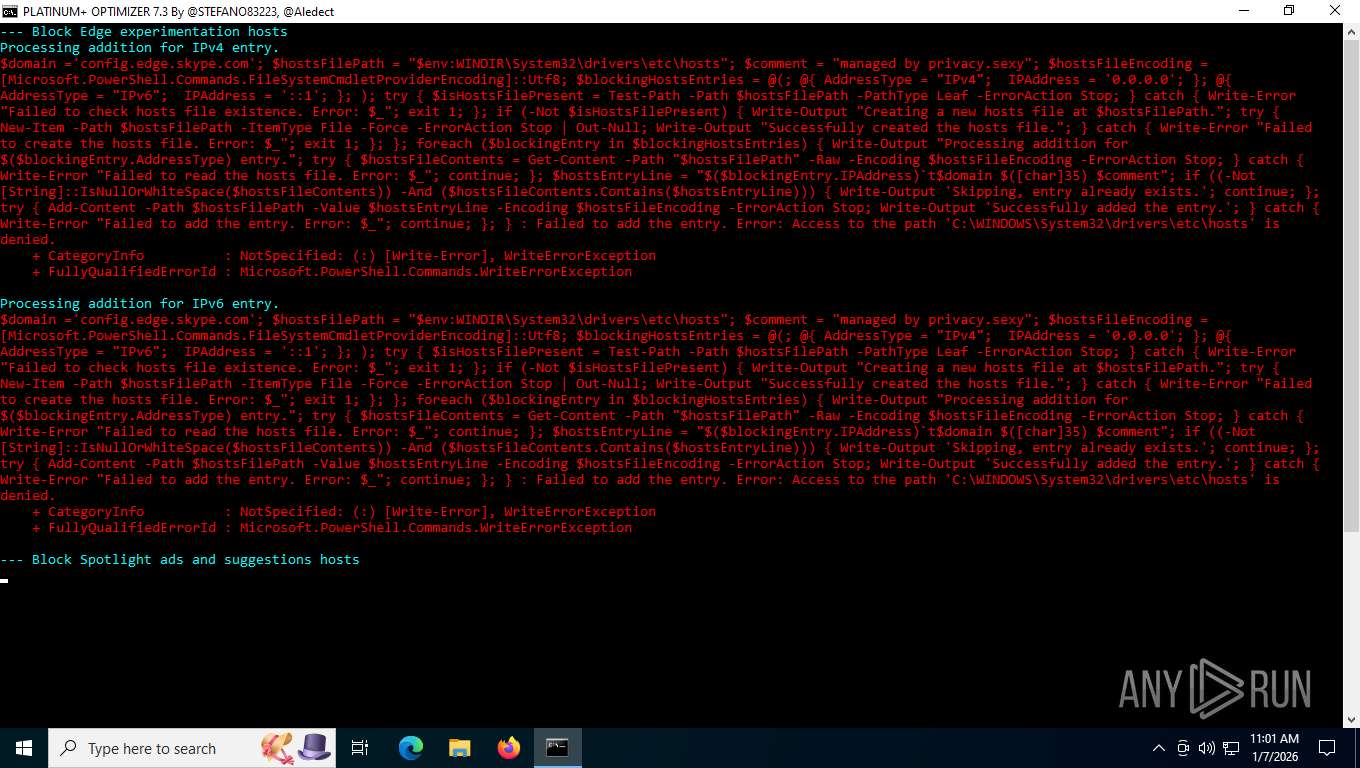
Escape characters obfuscation (POWERSHELL)
- powershell.exe (PID: 7216)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 2668)
- powershell.exe (PID: 404)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 4344)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 5104)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 1752)
- powershell.exe (PID: 4508)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 7100)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 6376)
- powershell.exe (PID: 4632)
Manipulates environment variables
- powershell.exe (PID: 7216)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 2668)
- powershell.exe (PID: 404)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 4344)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 5104)
- powershell.exe (PID: 1752)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 4508)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 7100)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 4632)
- powershell.exe (PID: 6376)
Found IP address in command line
- powershell.exe (PID: 7216)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 2668)
- powershell.exe (PID: 404)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 4344)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 5104)
- powershell.exe (PID: 1752)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 4508)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 7100)
- powershell.exe (PID: 4632)
- powershell.exe (PID: 6376)
Obfuscation pattern (POWERSHELL)
- powershell.exe (PID: 7216)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 2668)
- powershell.exe (PID: 404)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 4344)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 5104)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 1752)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 4508)
- powershell.exe (PID: 7100)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 6376)
- powershell.exe (PID: 4632)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7216)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 2668)
- powershell.exe (PID: 404)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 4344)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 5104)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 1752)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 7100)
- powershell.exe (PID: 4508)
- powershell.exe (PID: 4632)
- powershell.exe (PID: 7992)
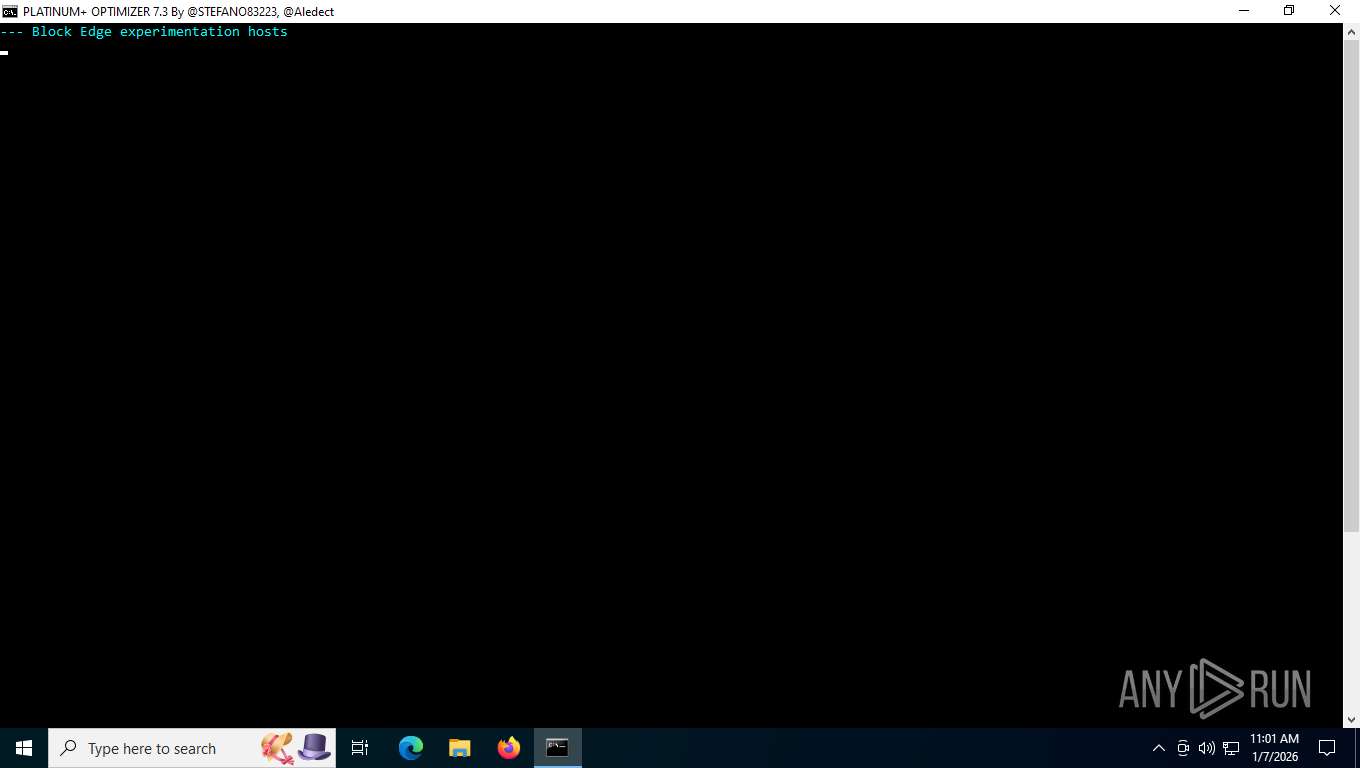
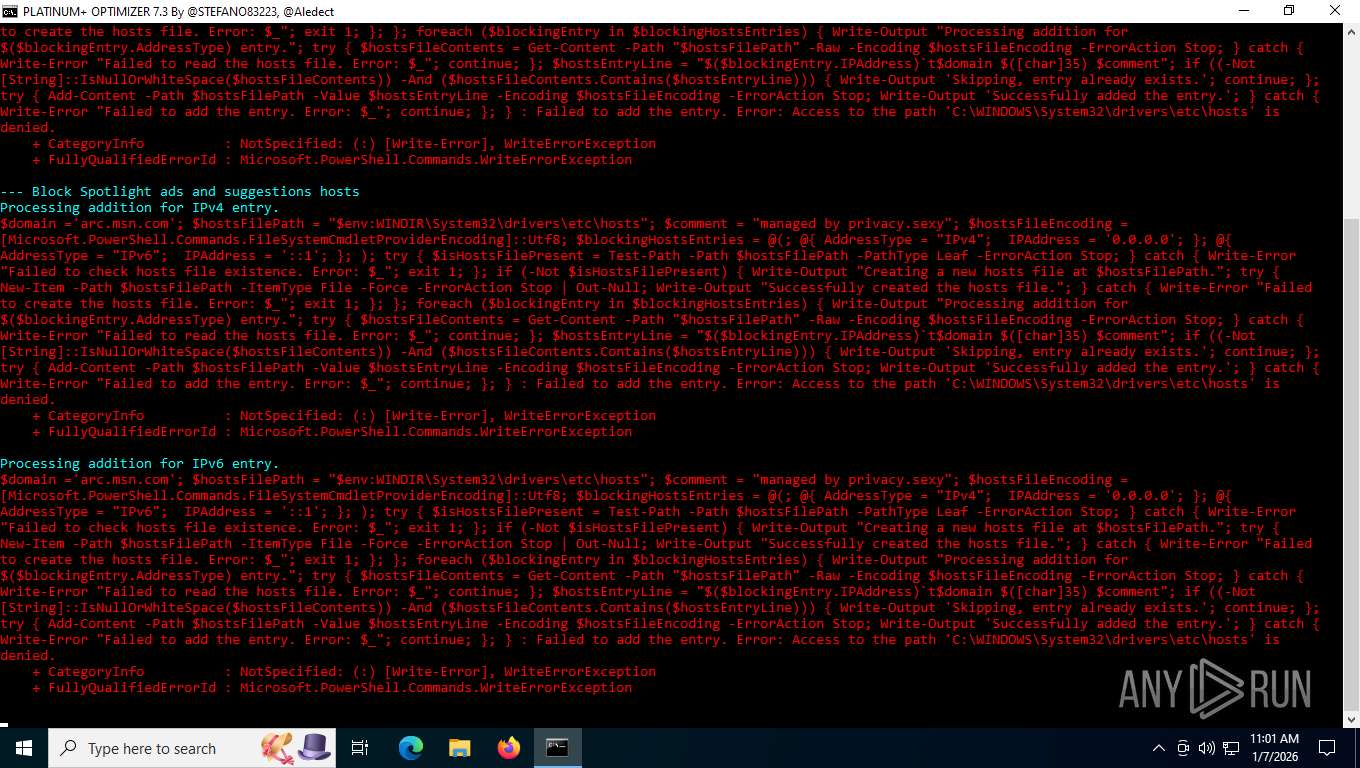
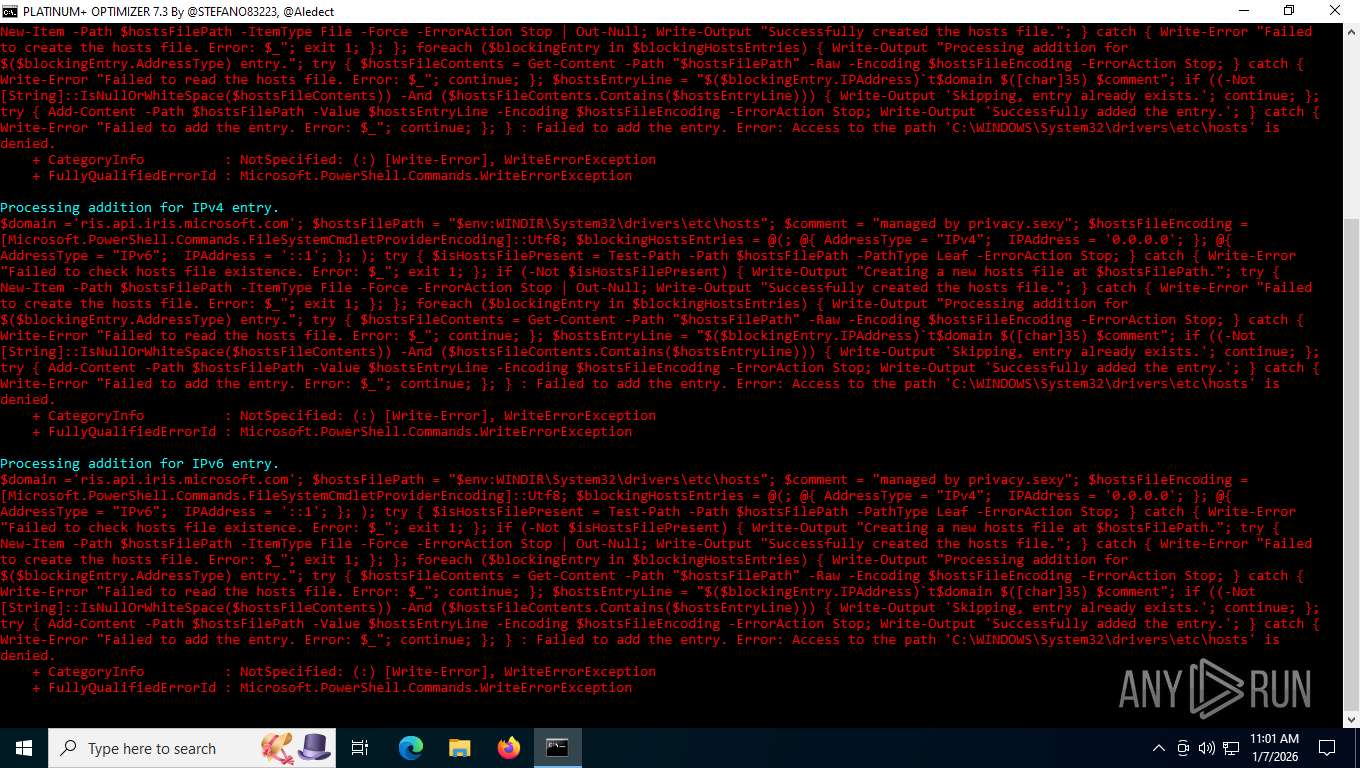
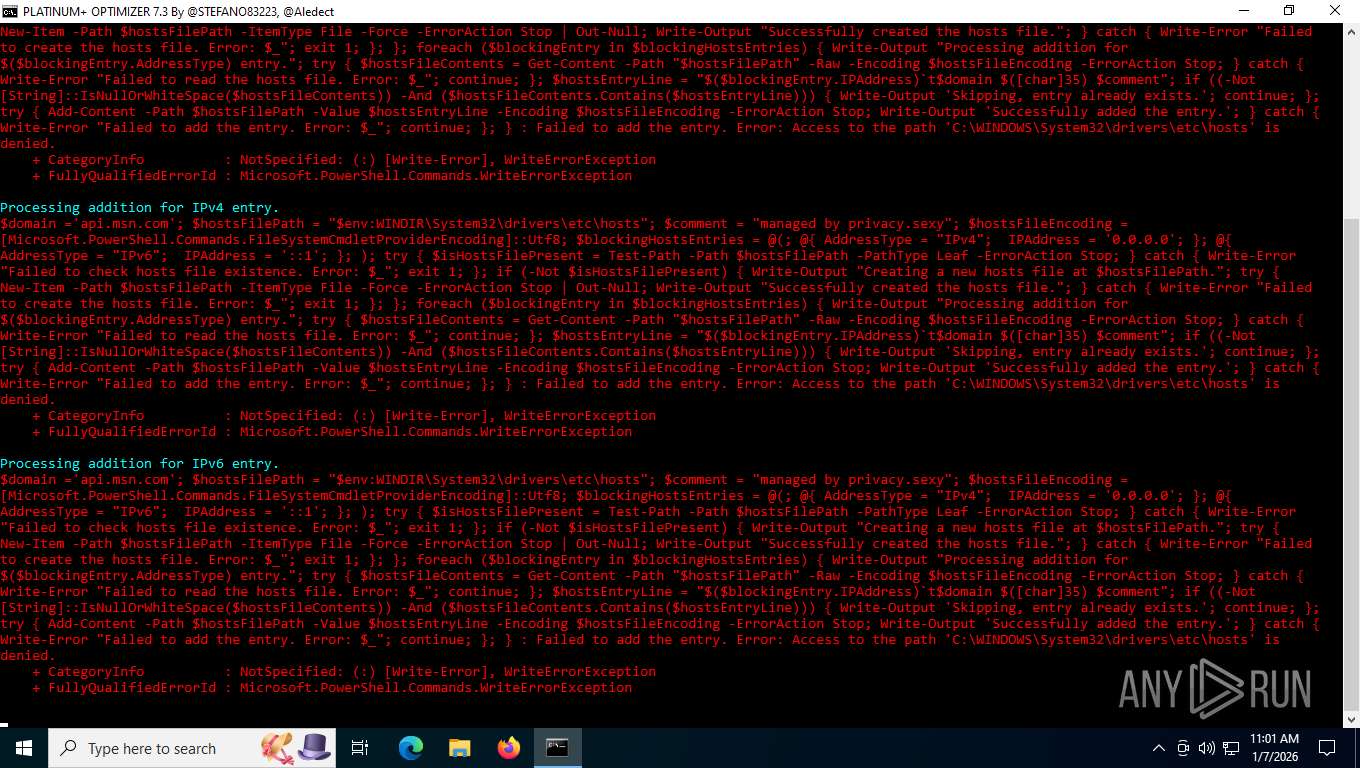
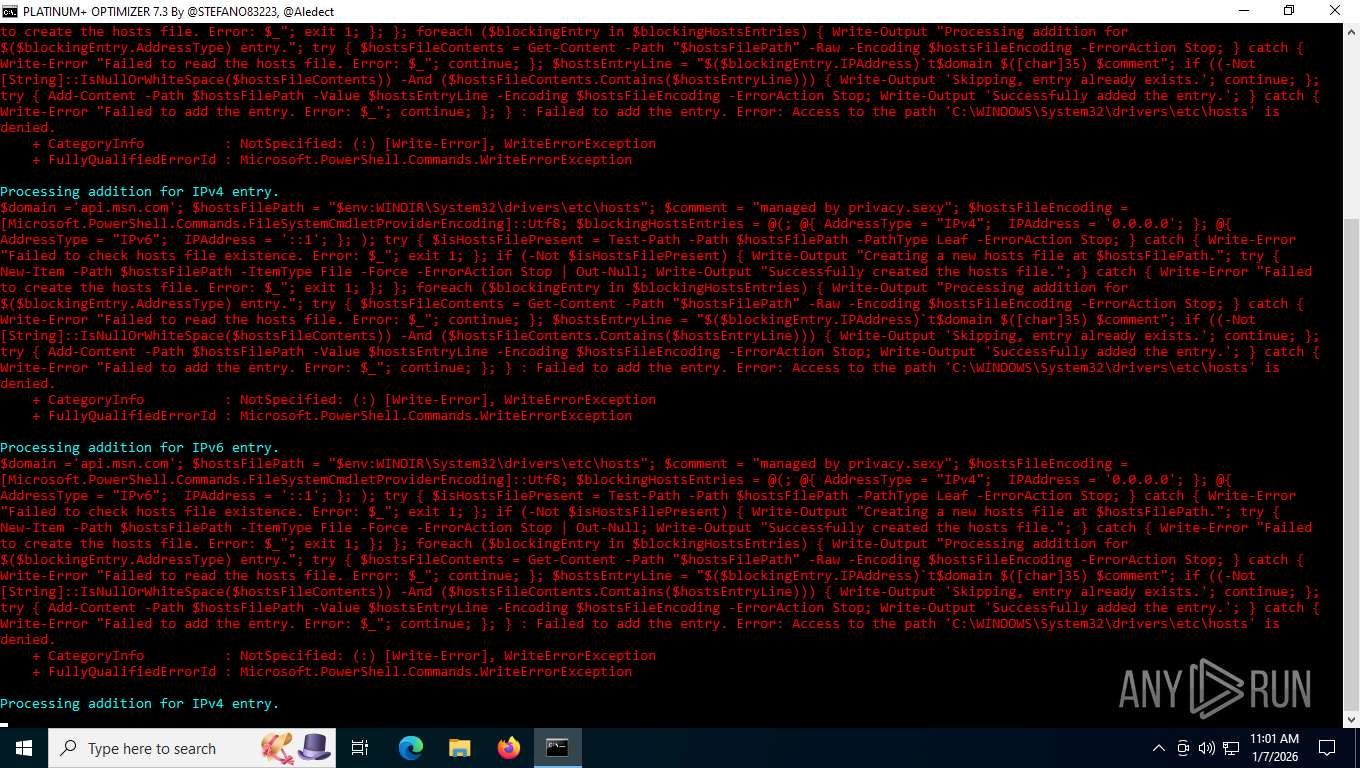
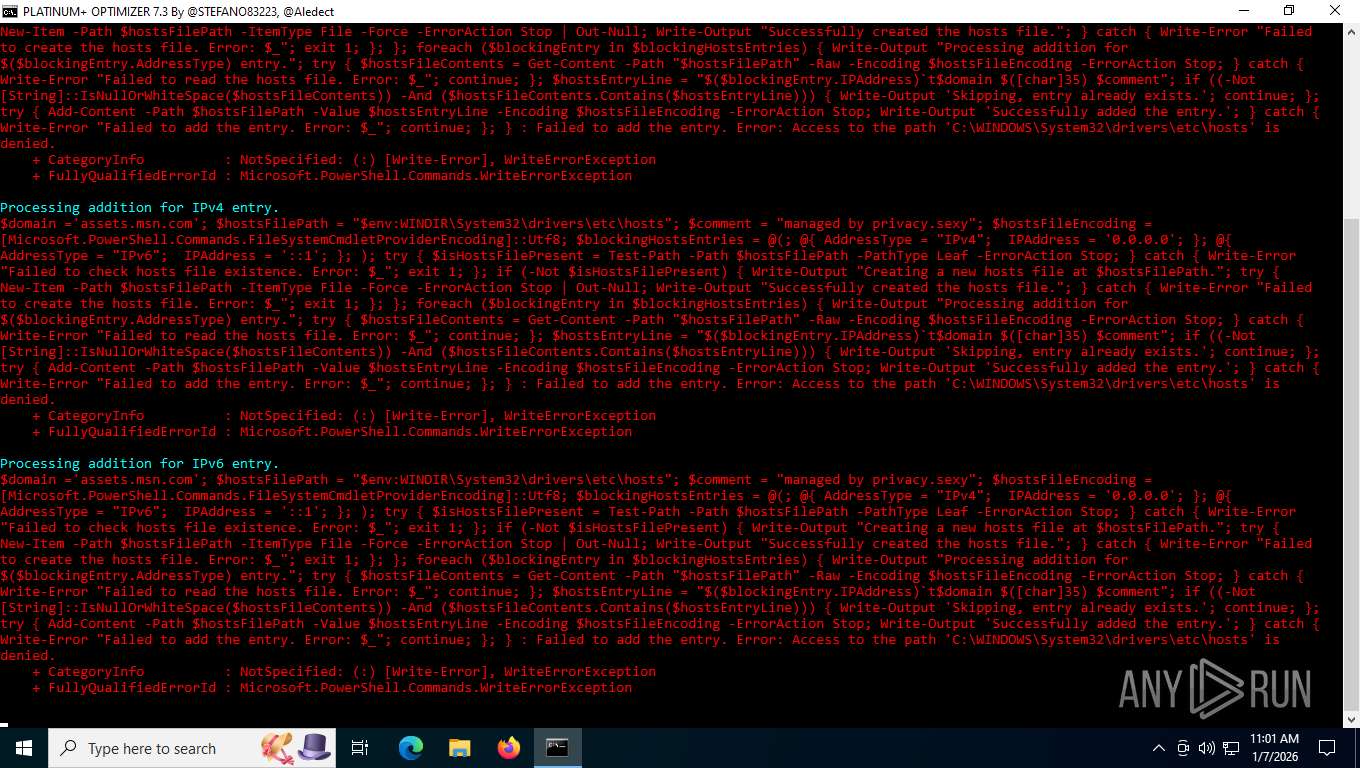
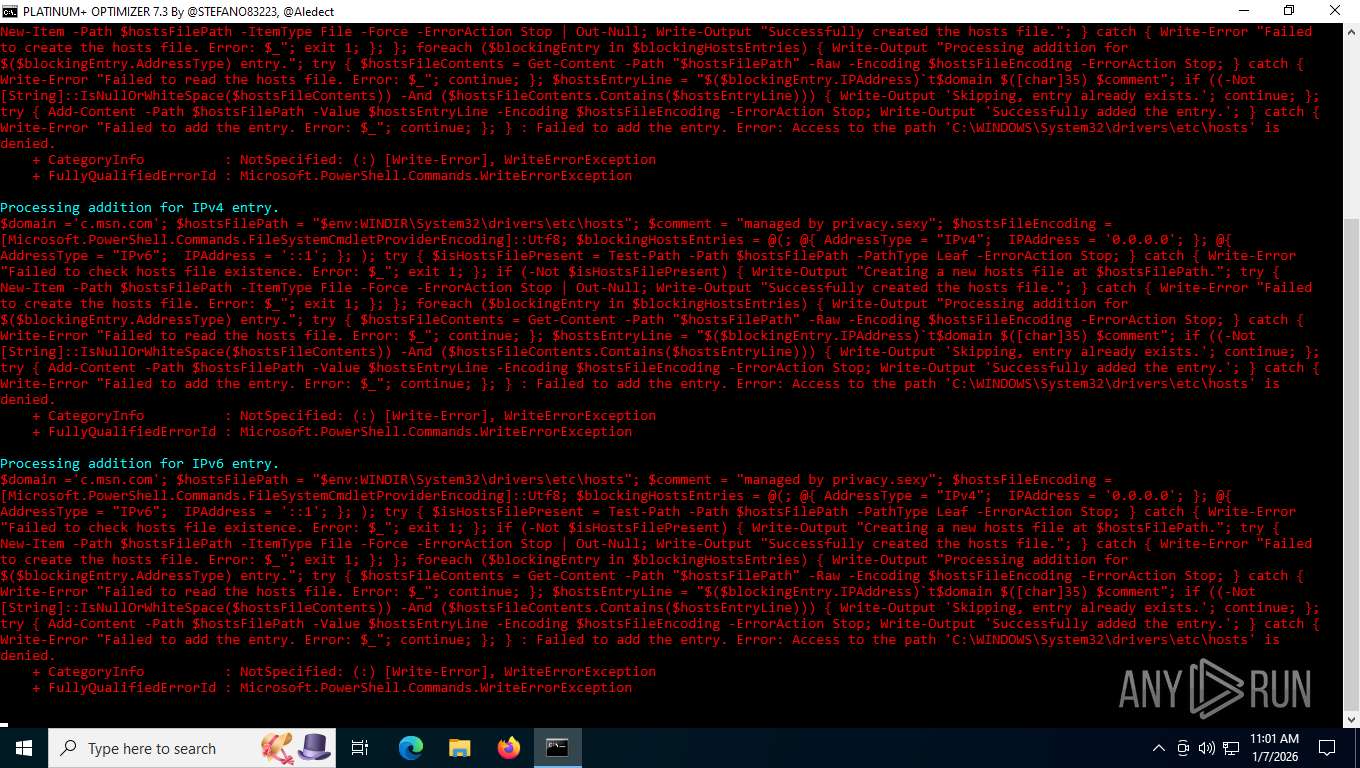
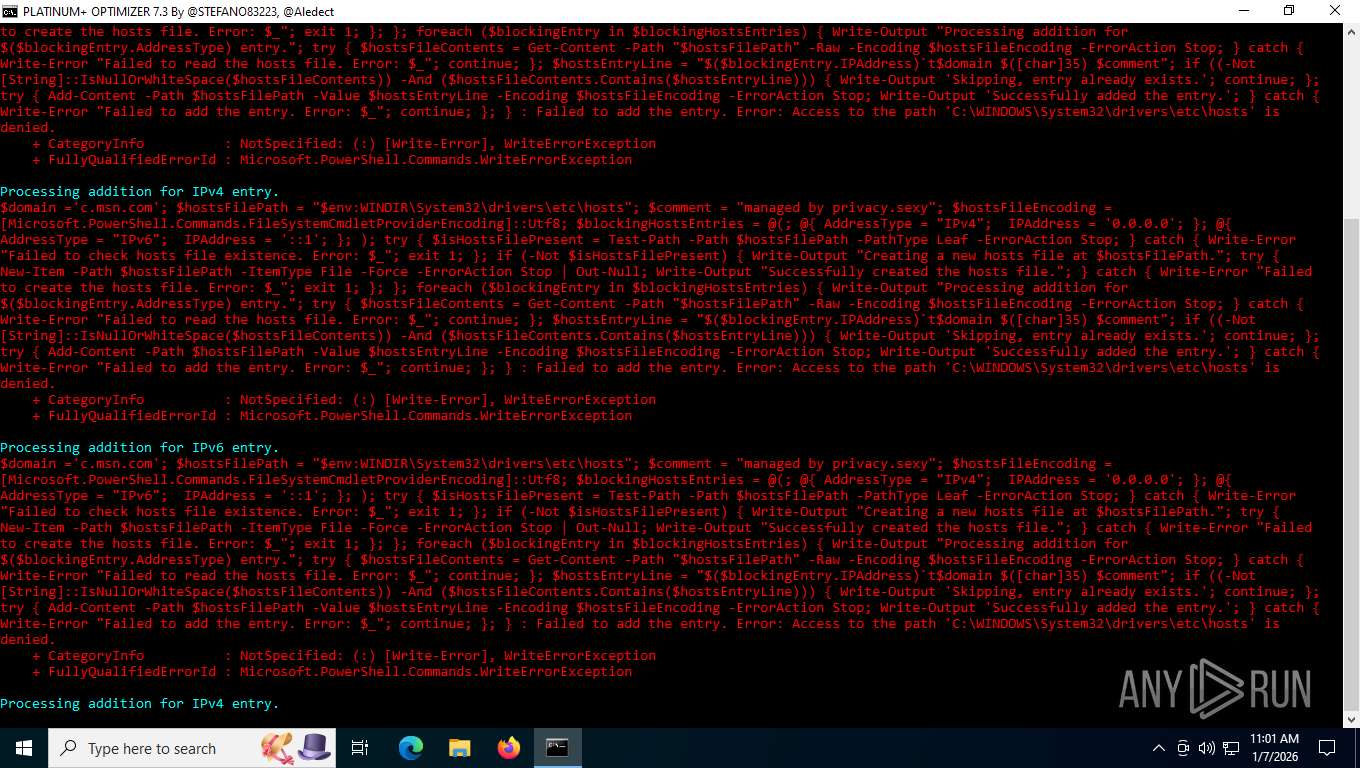
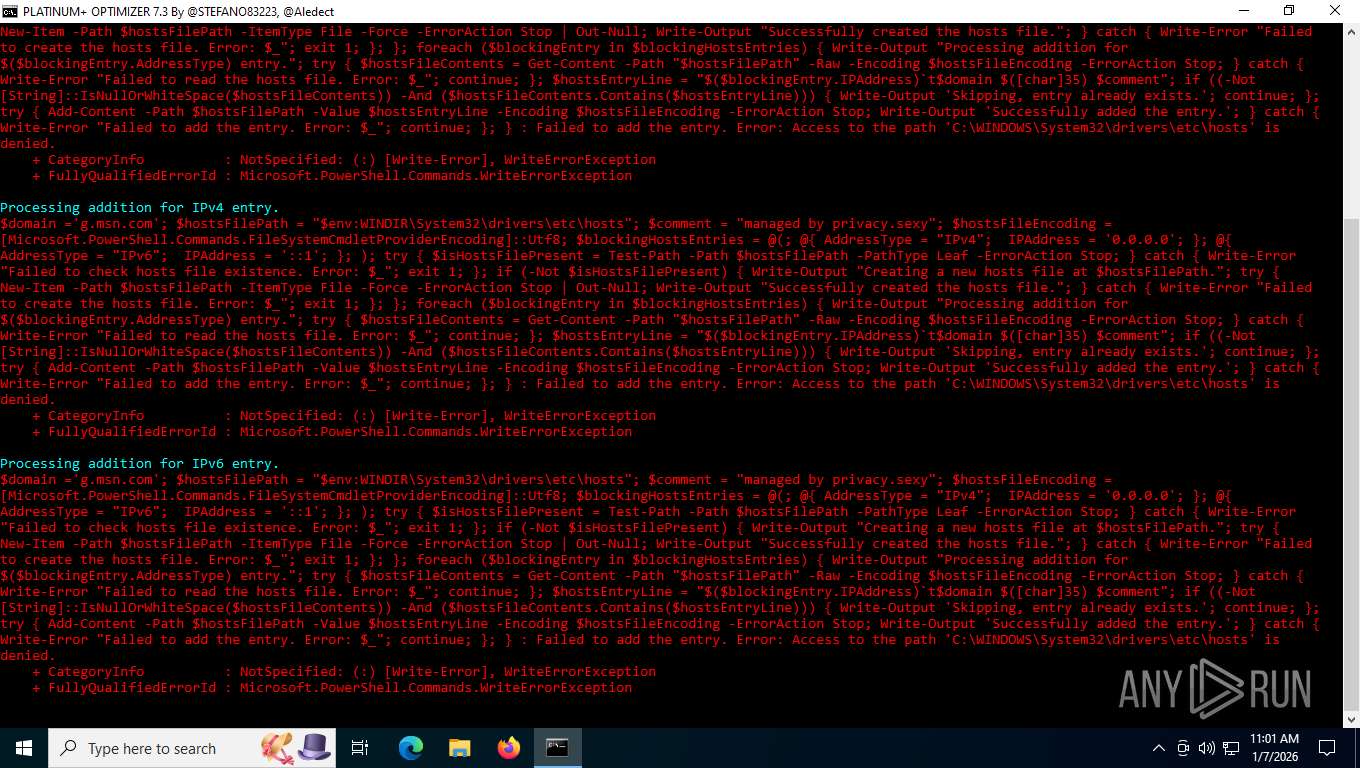
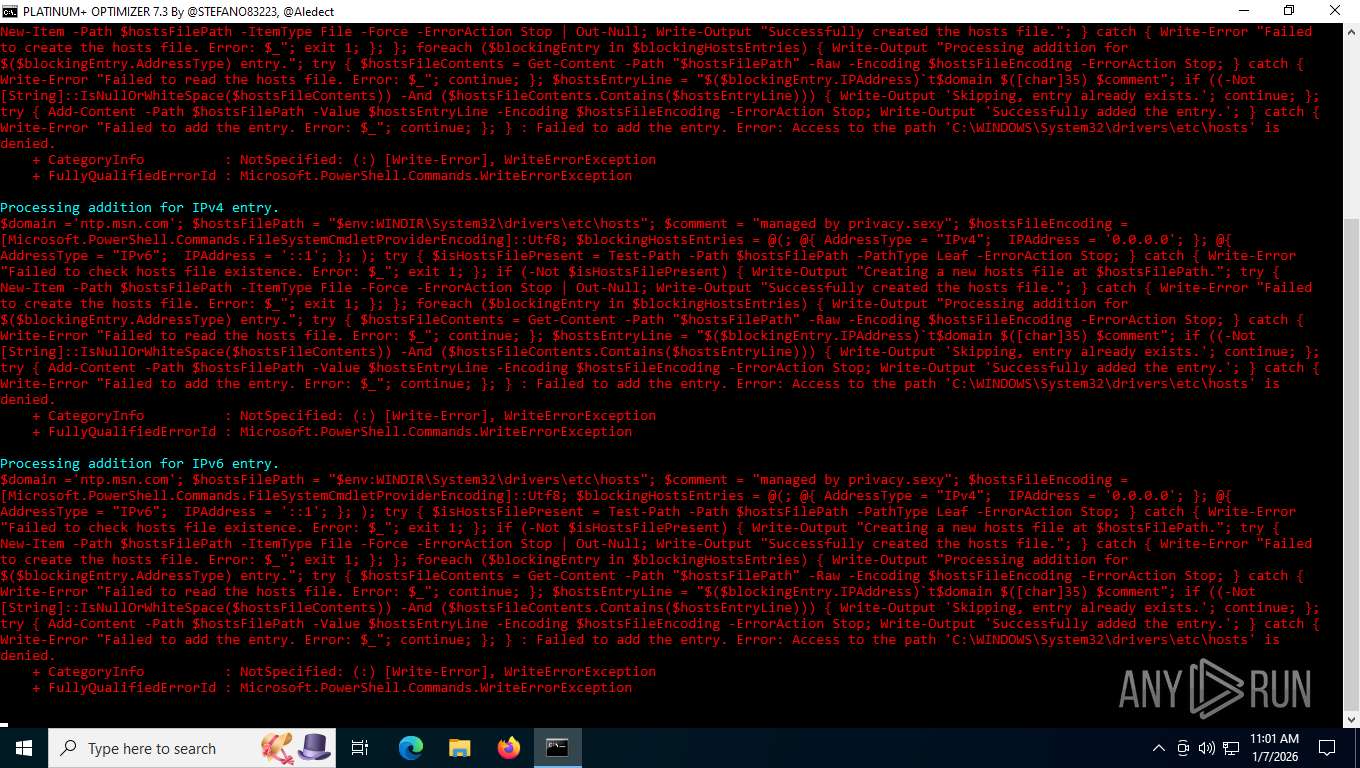
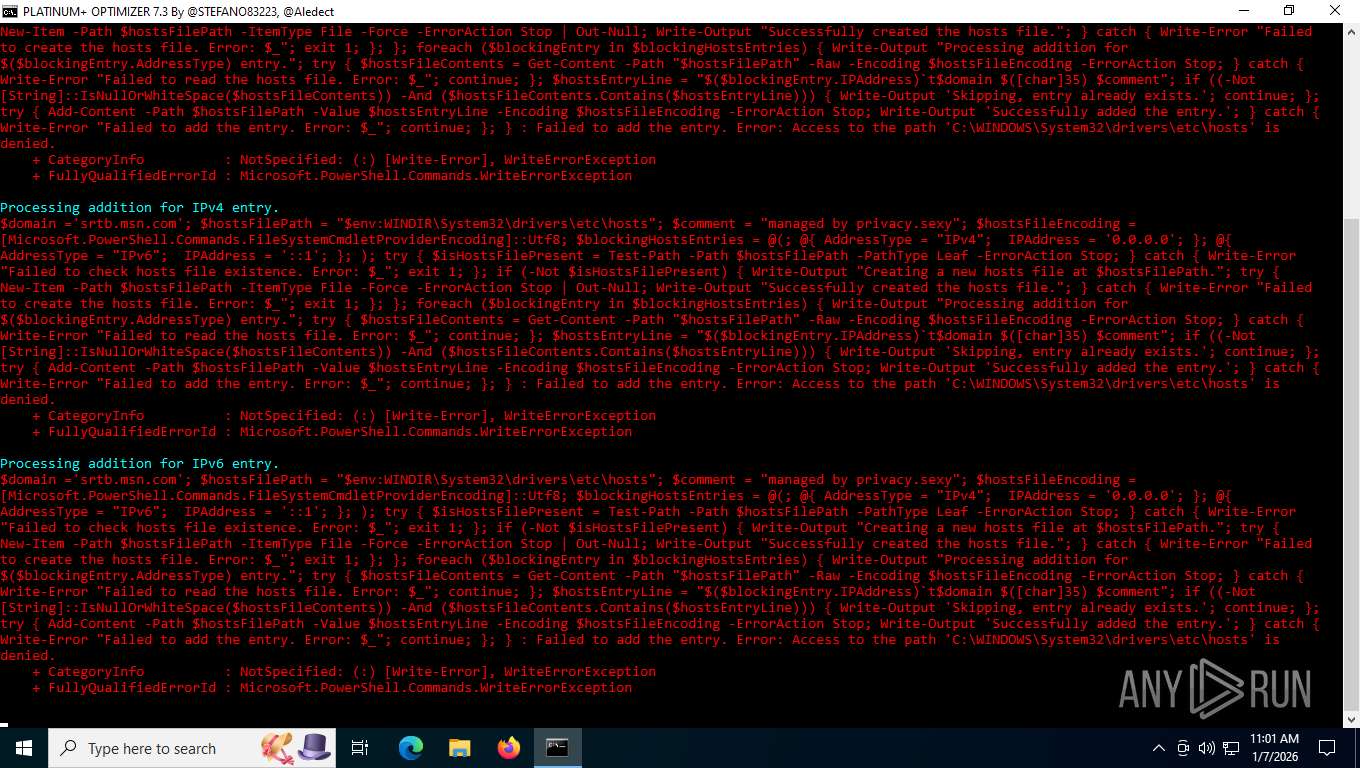
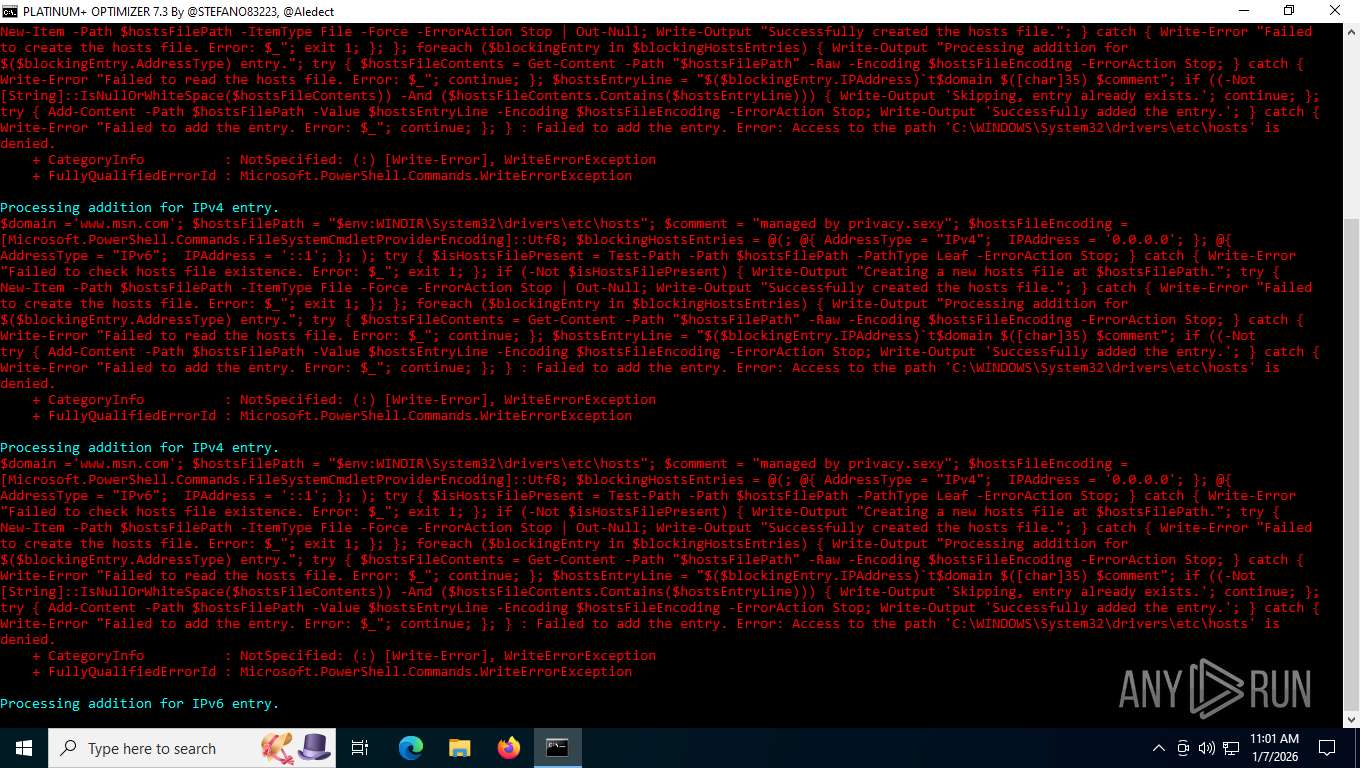
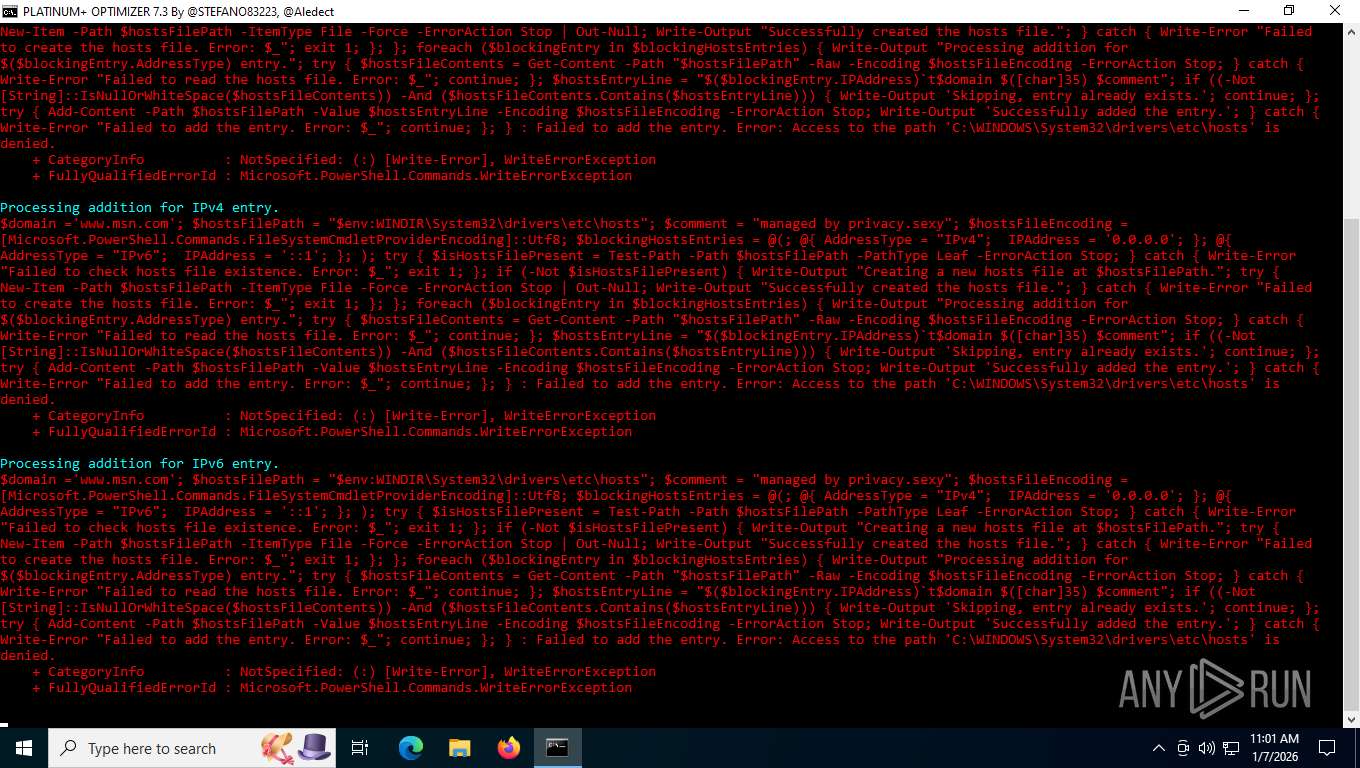
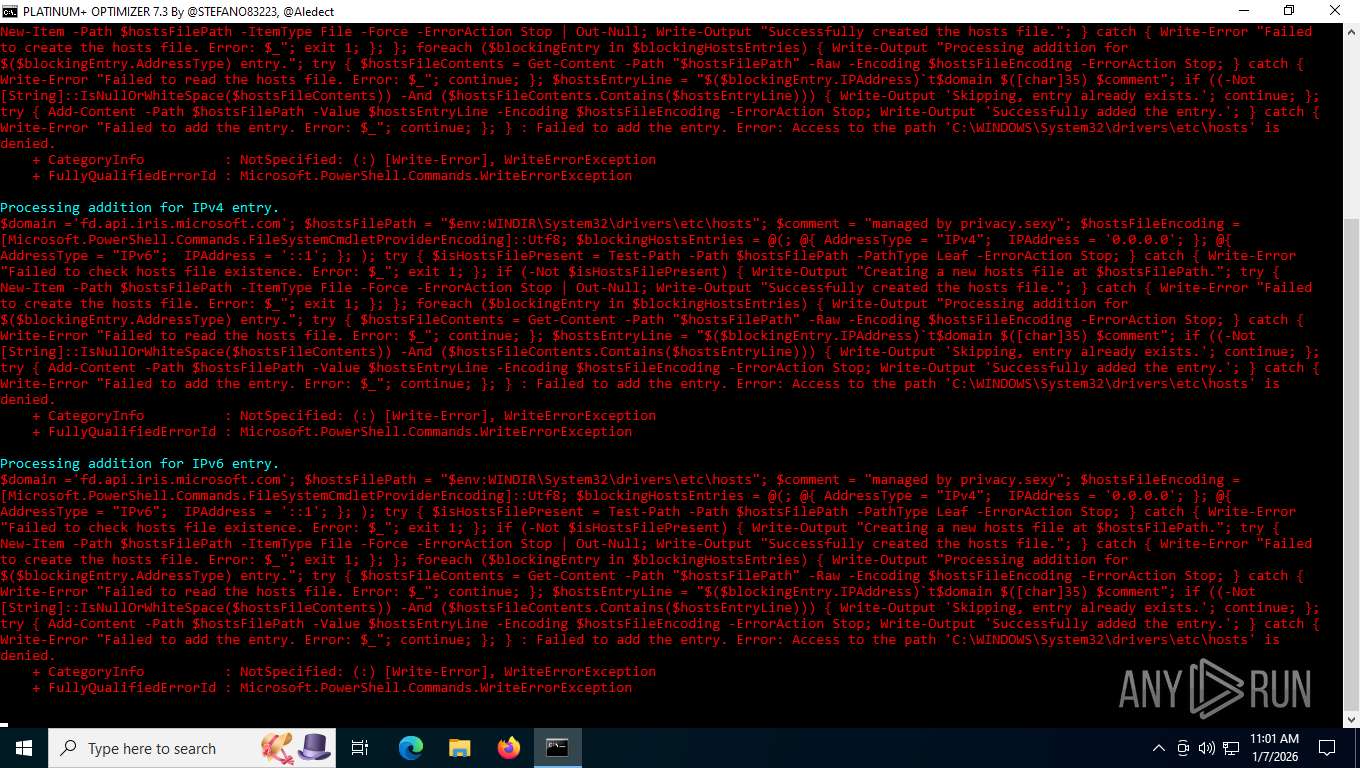
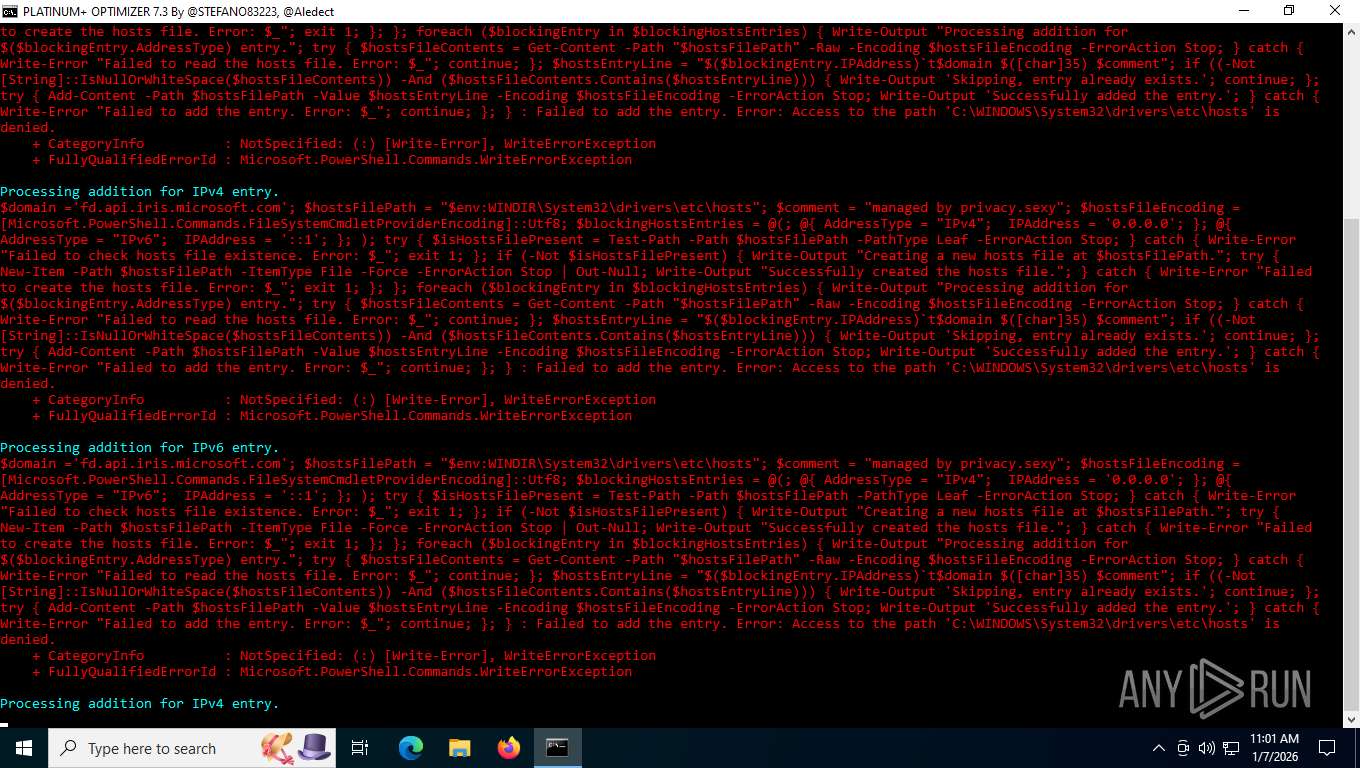
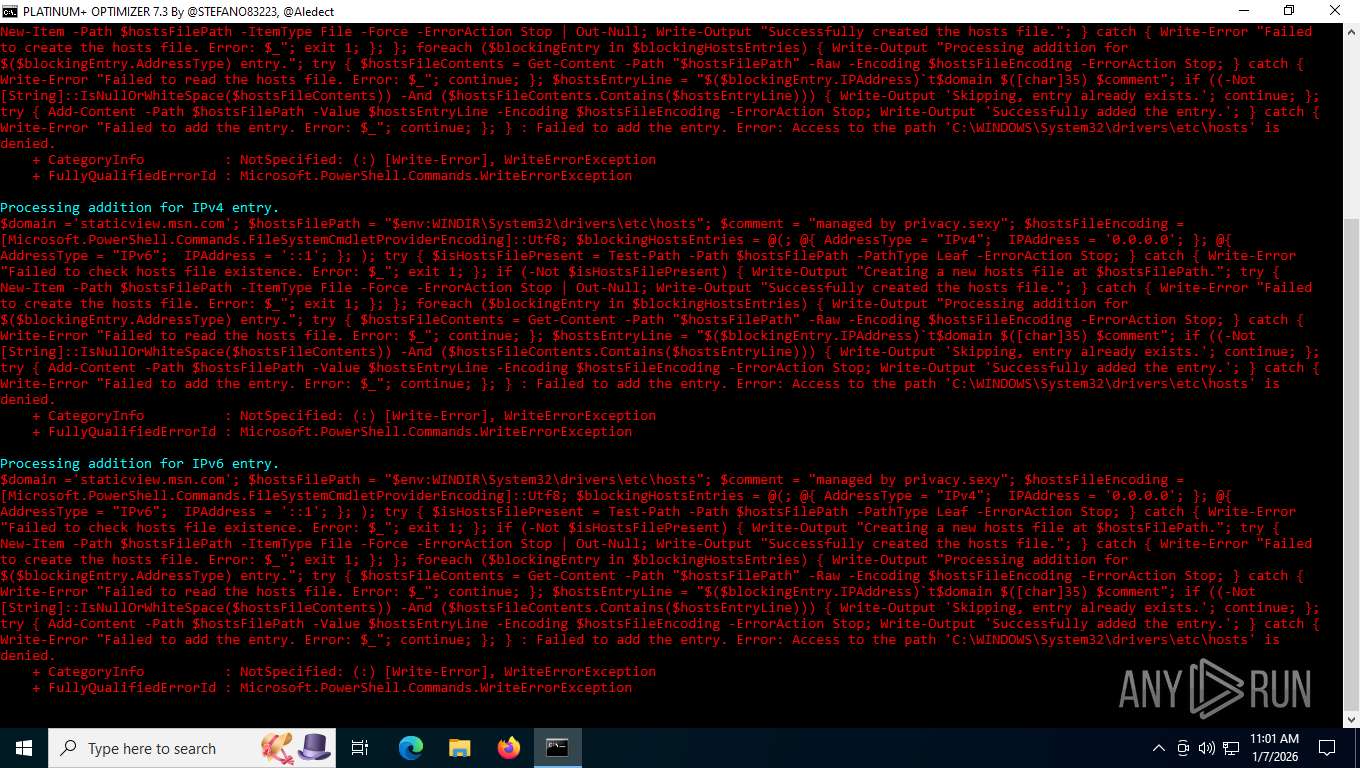
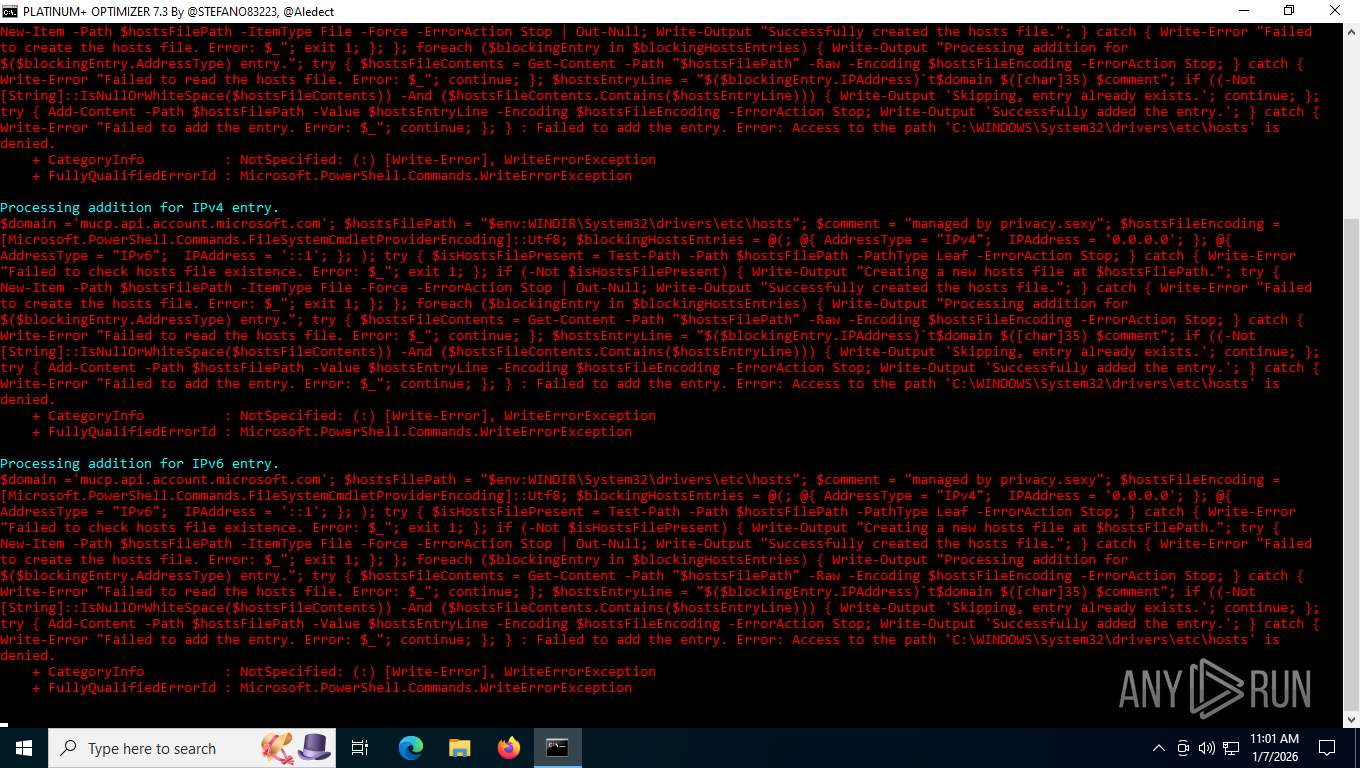
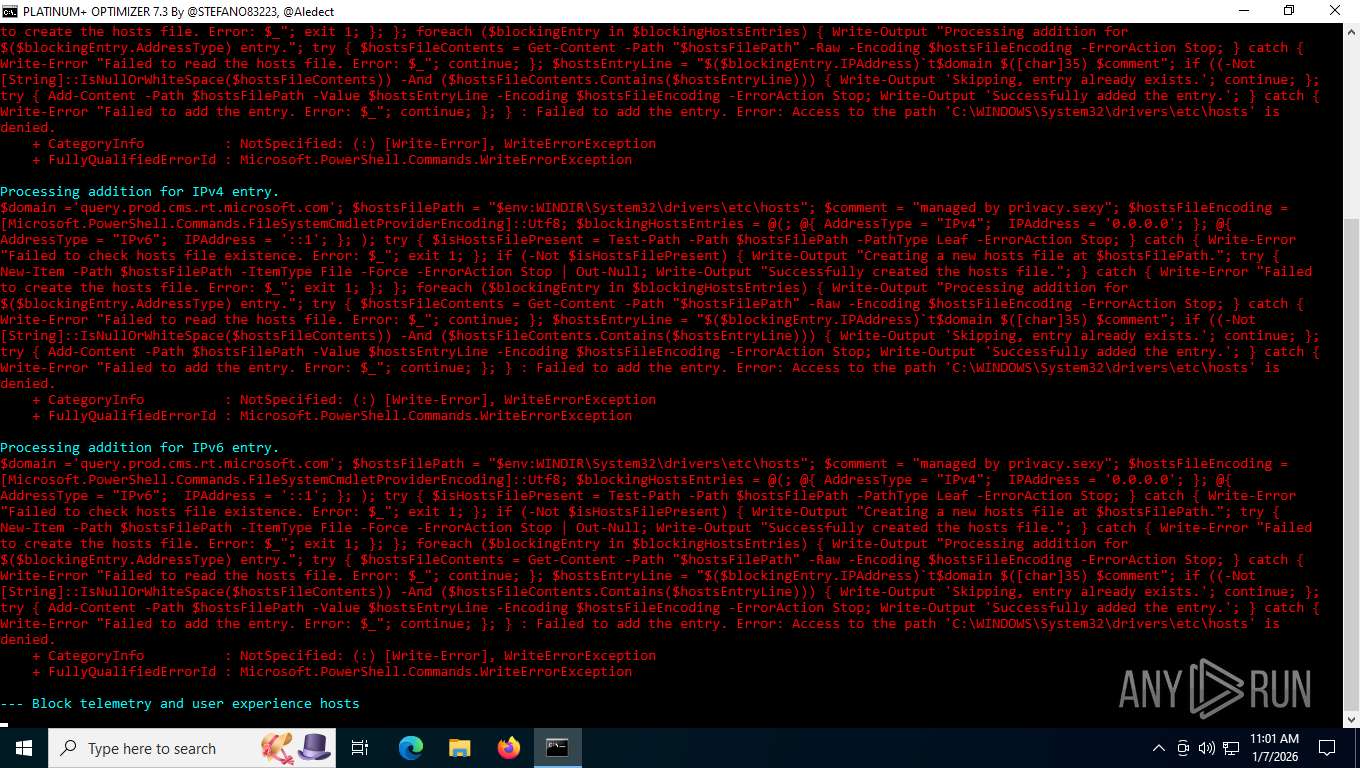
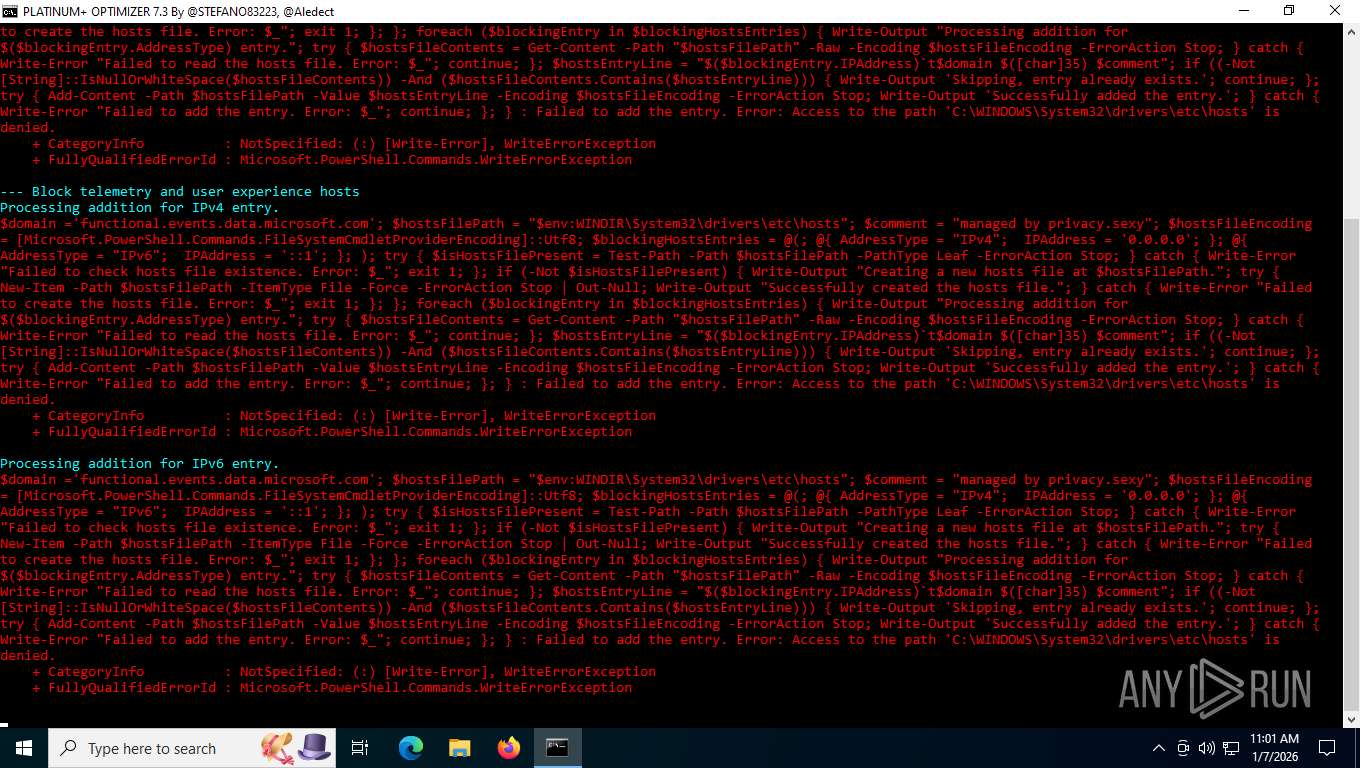
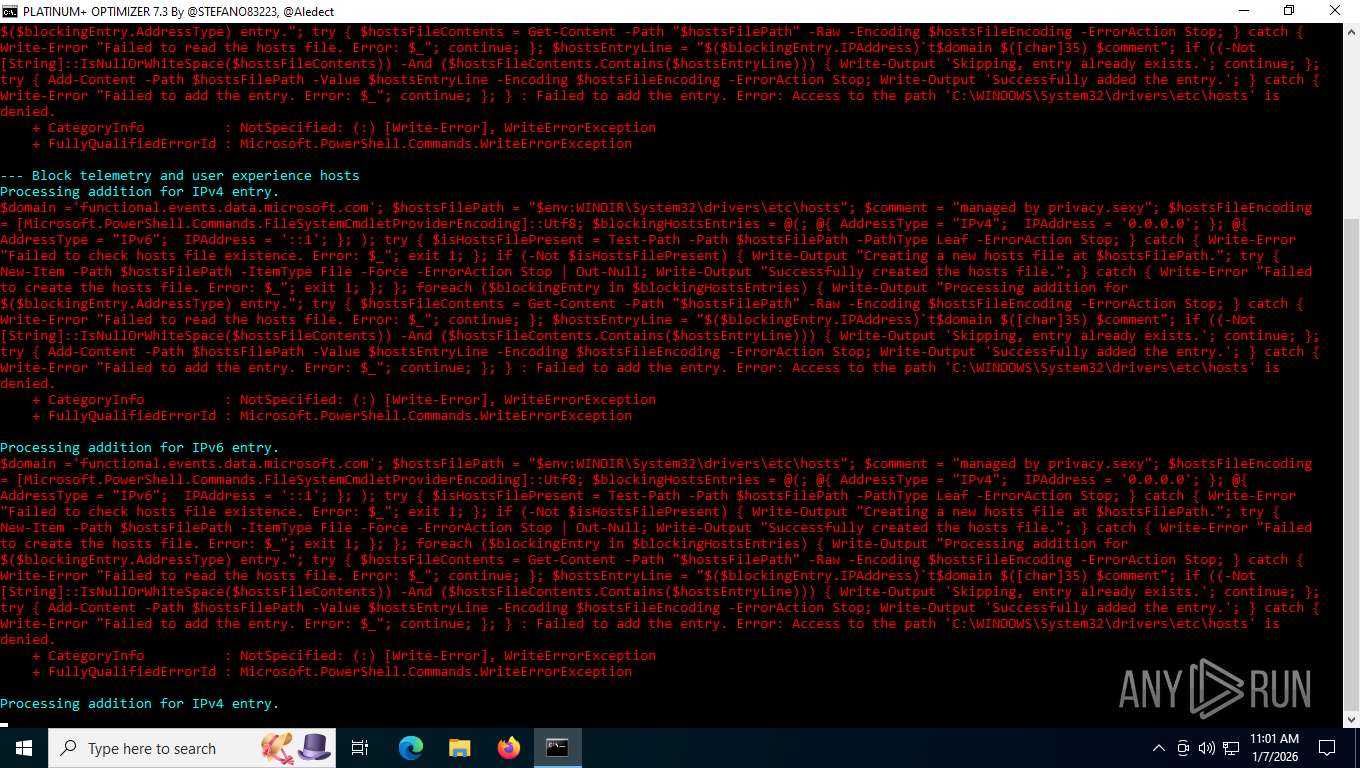
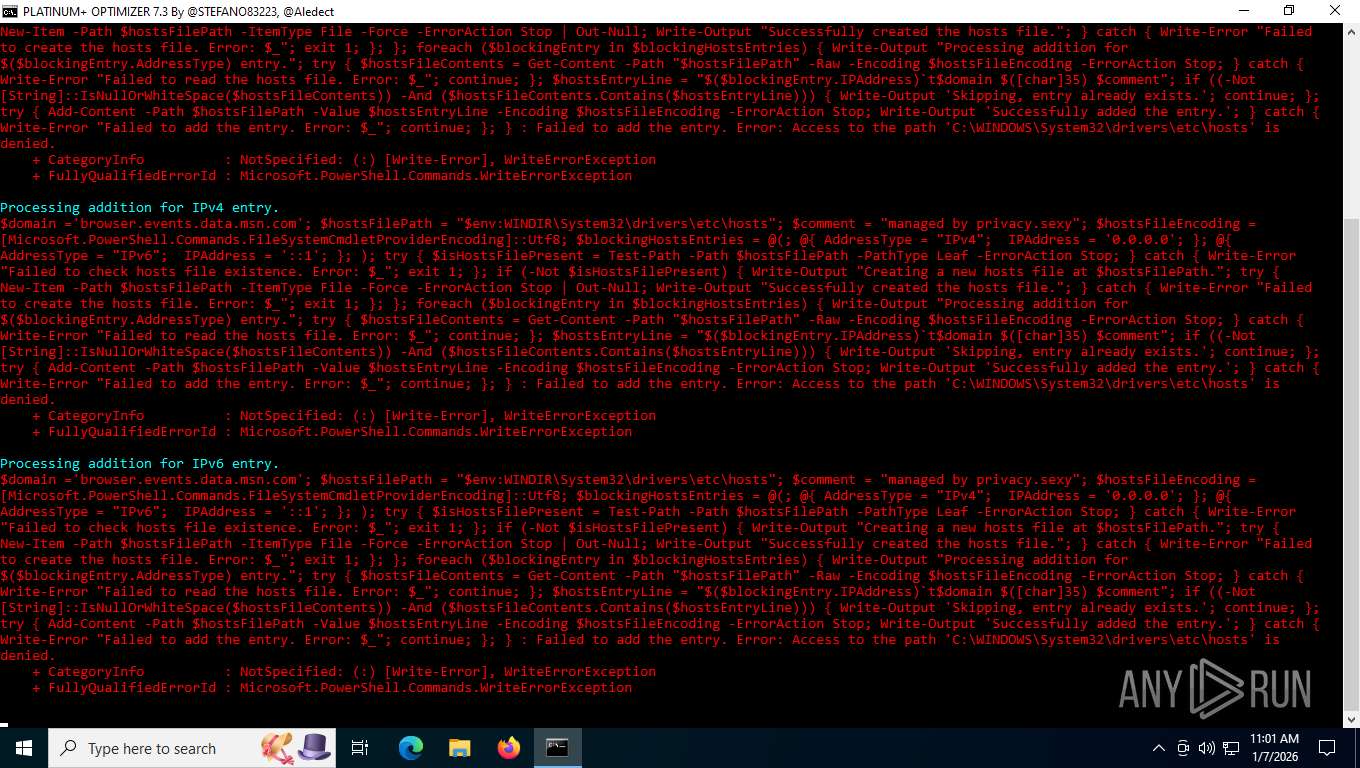
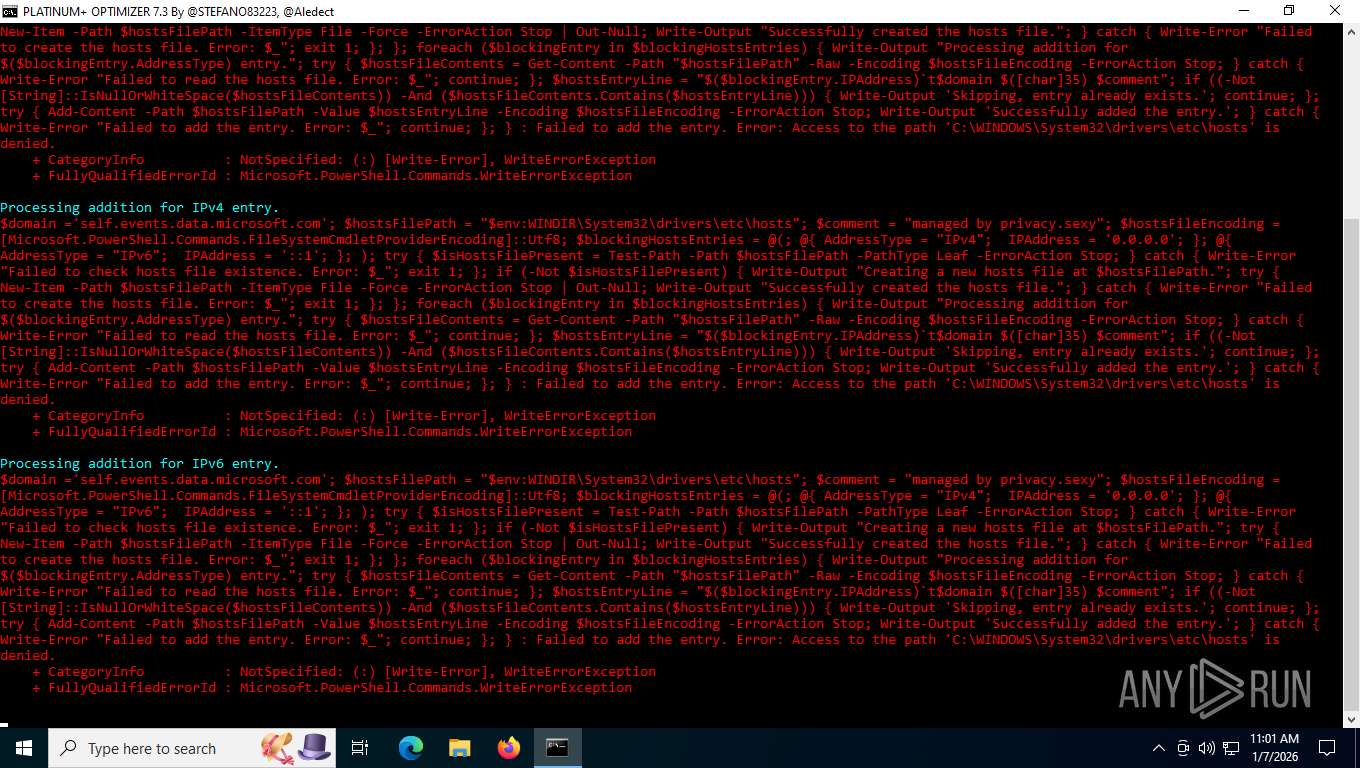
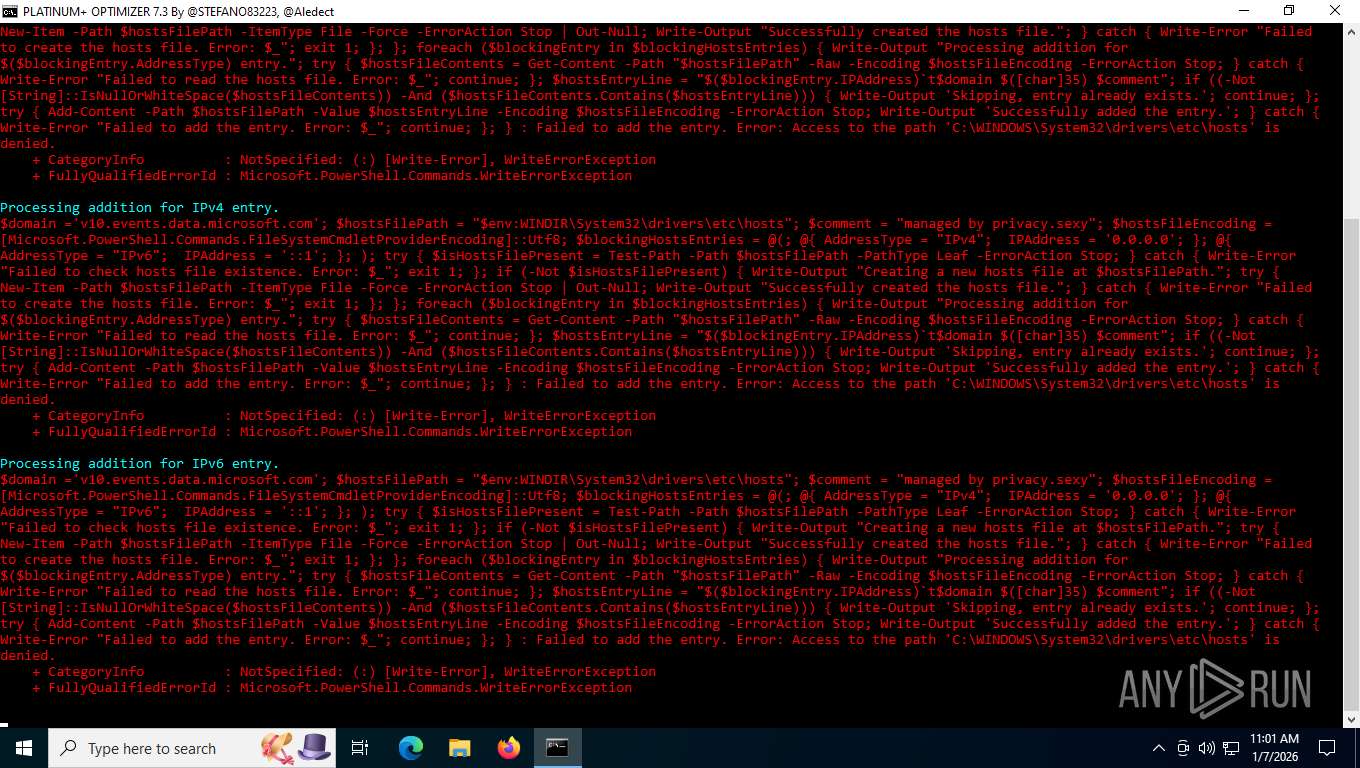
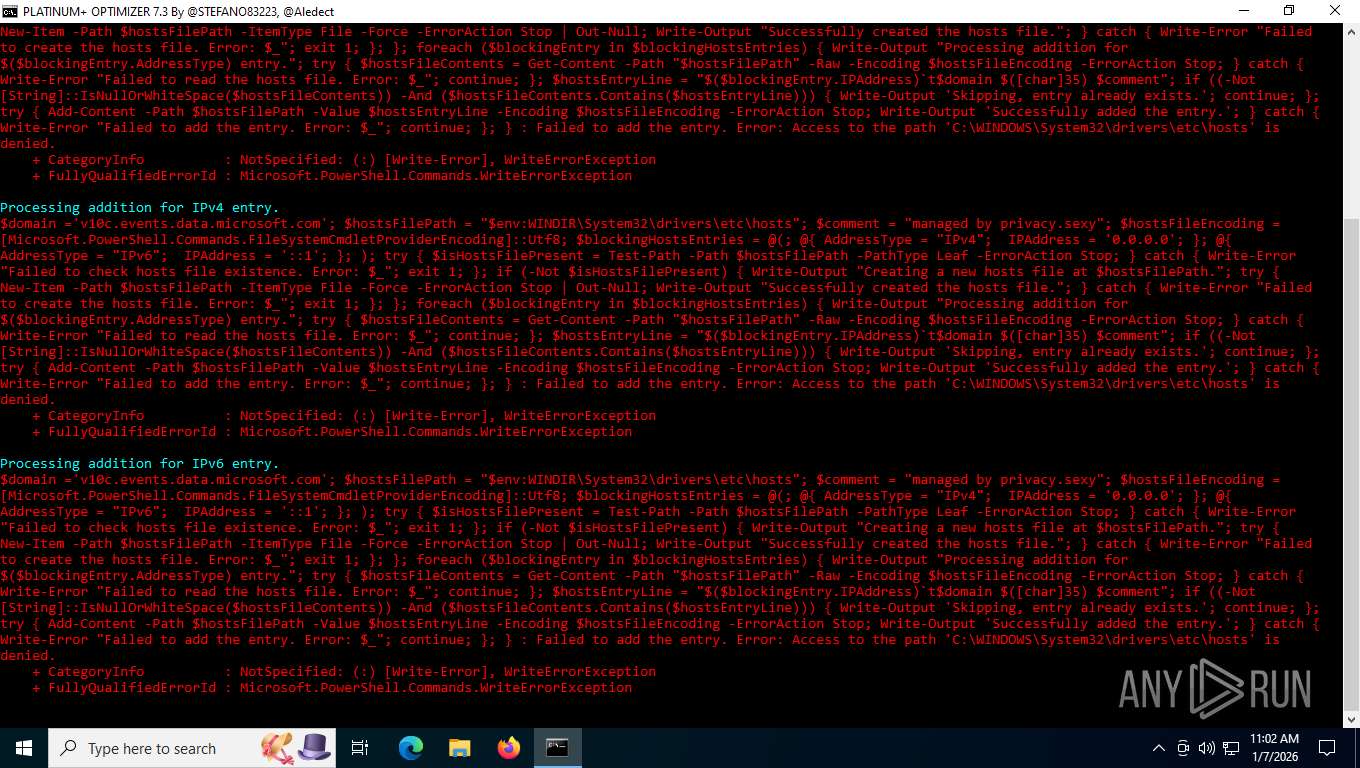
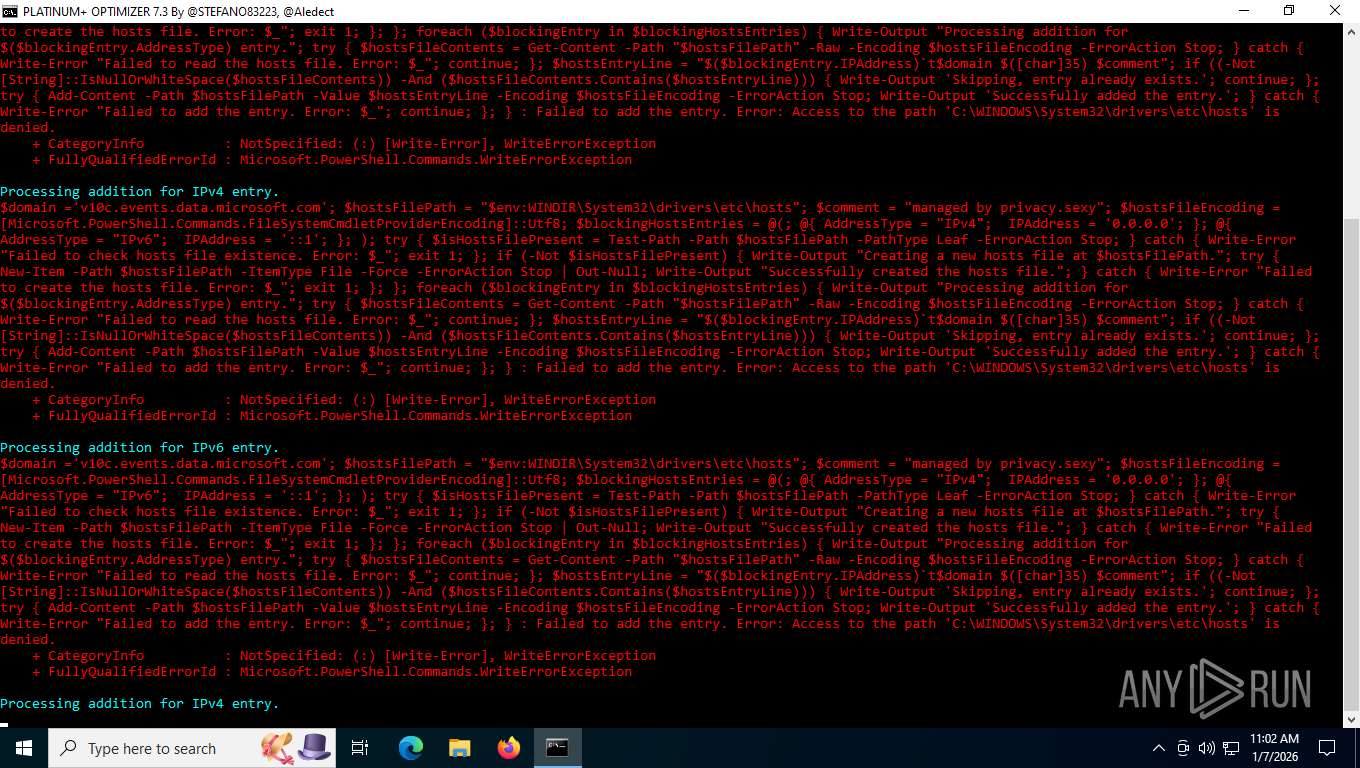
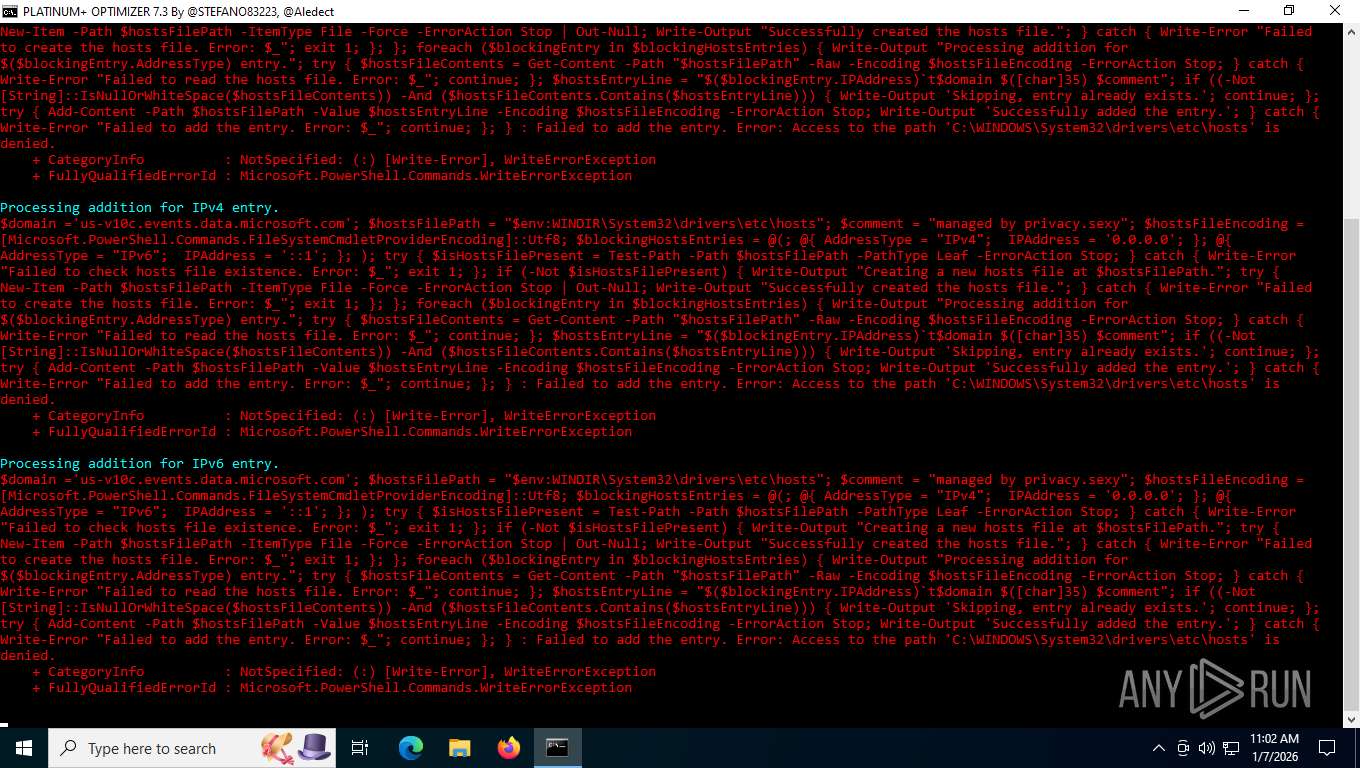
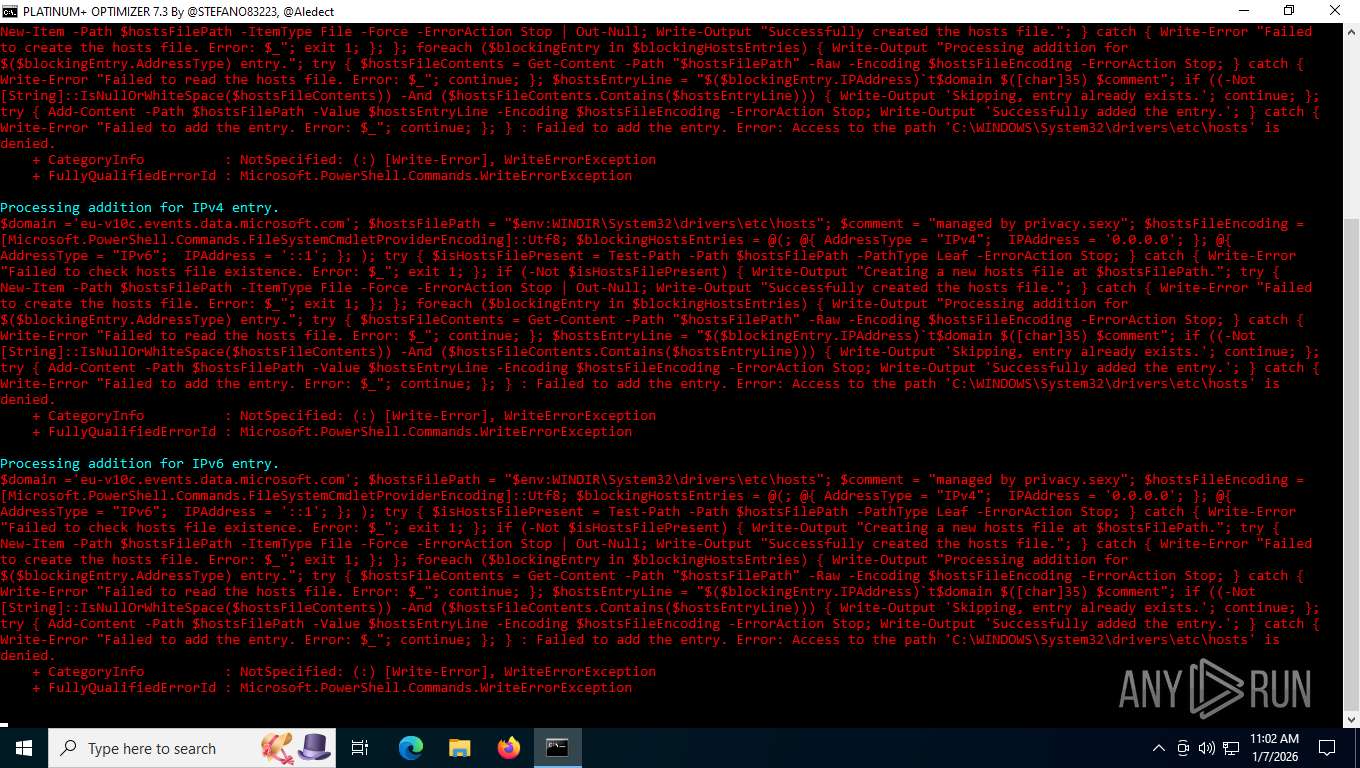
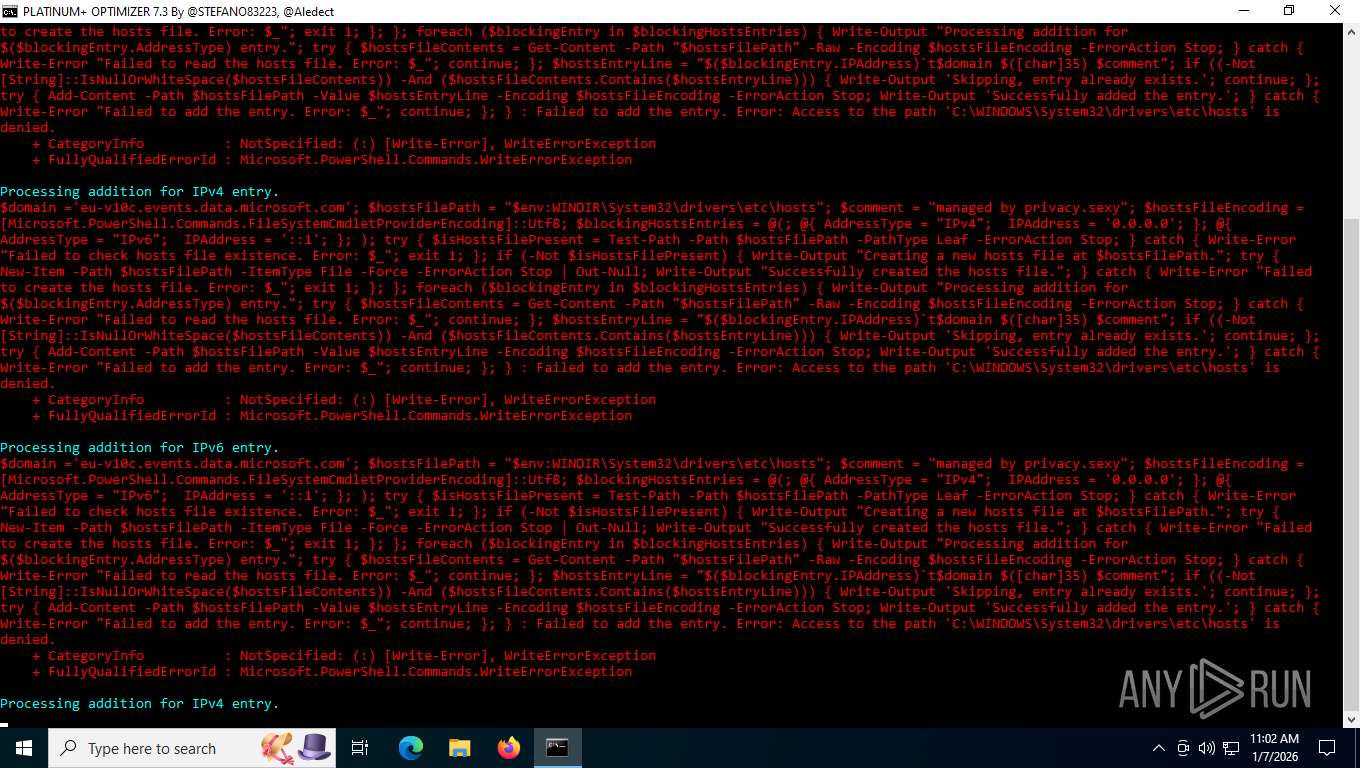
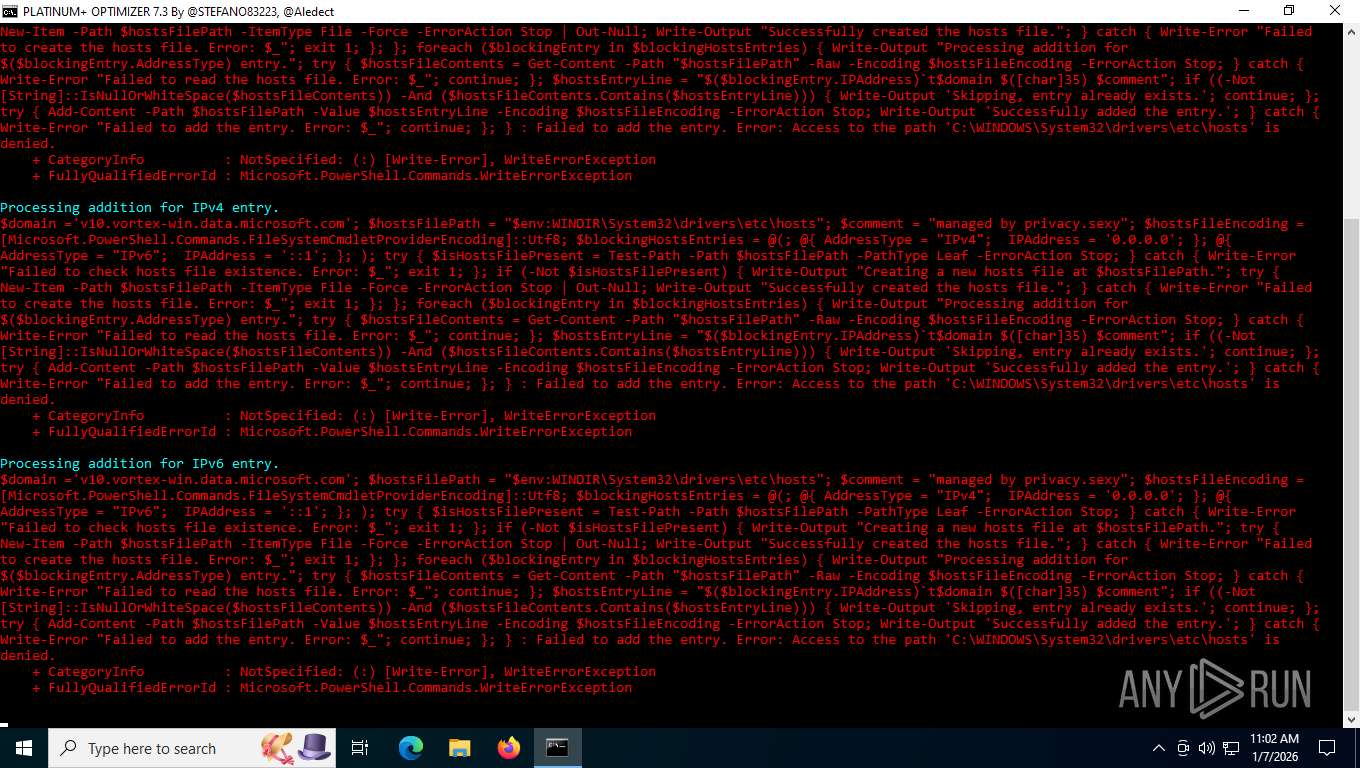
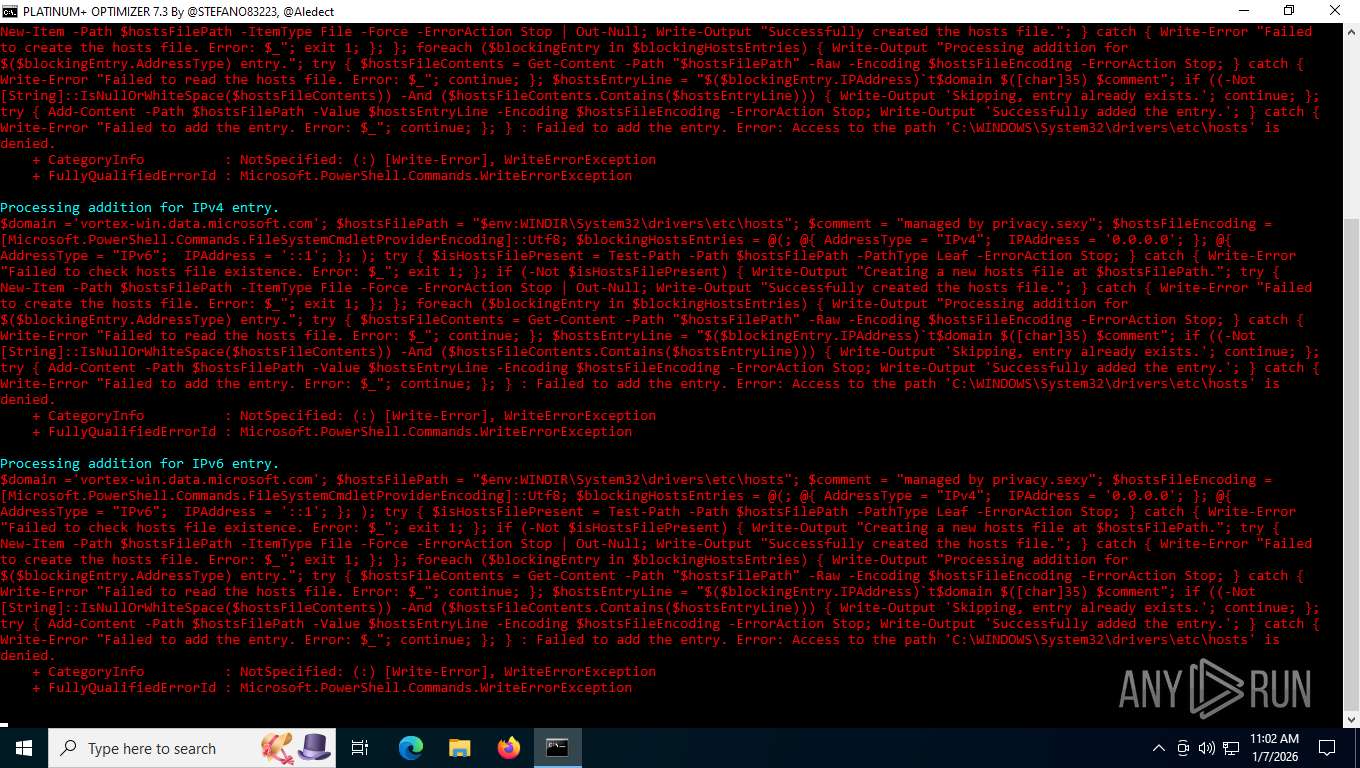
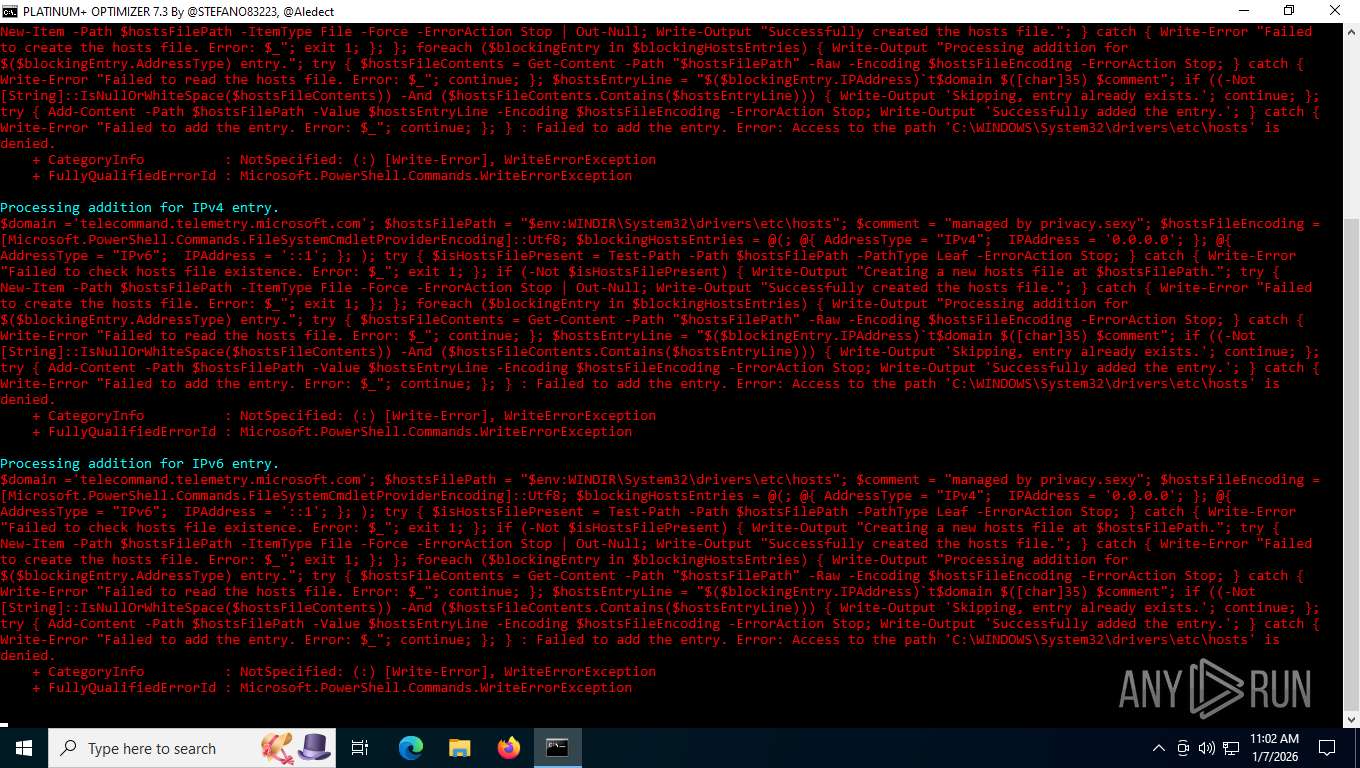
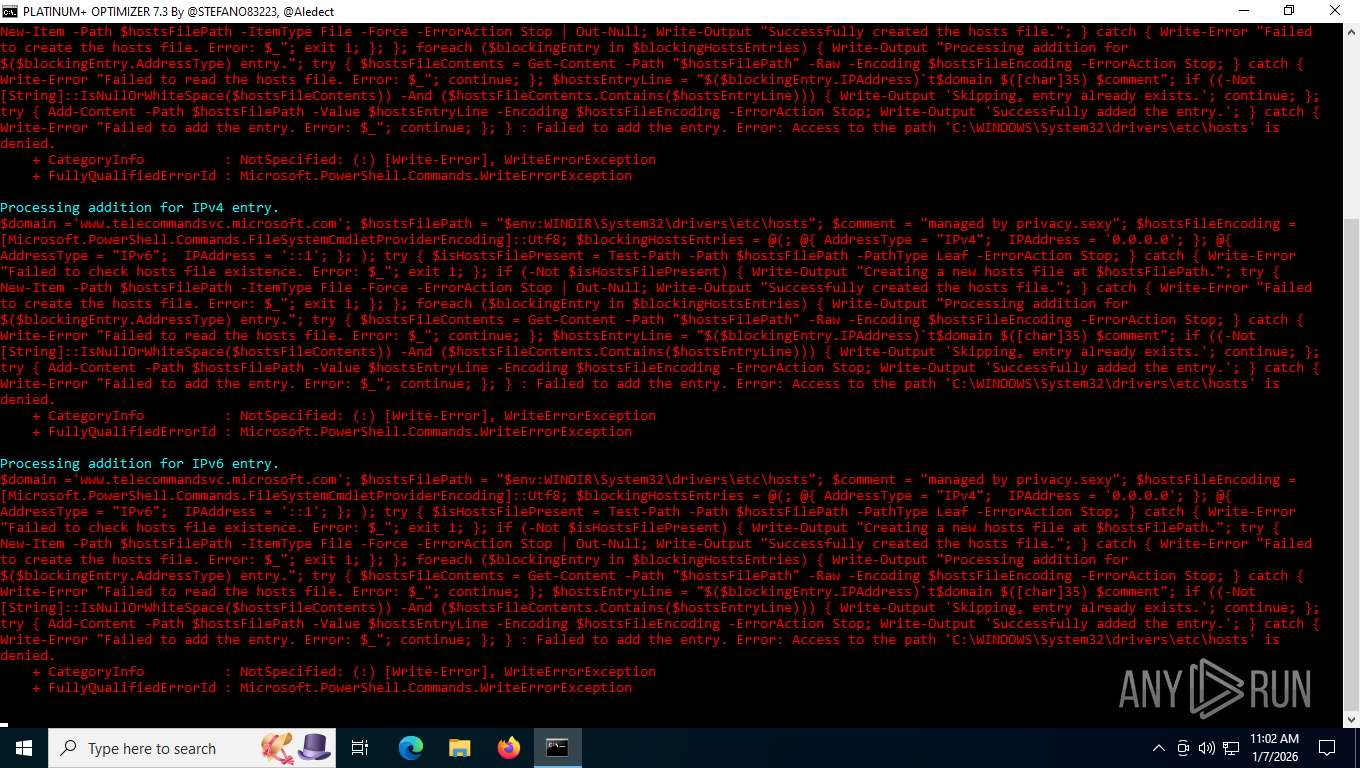
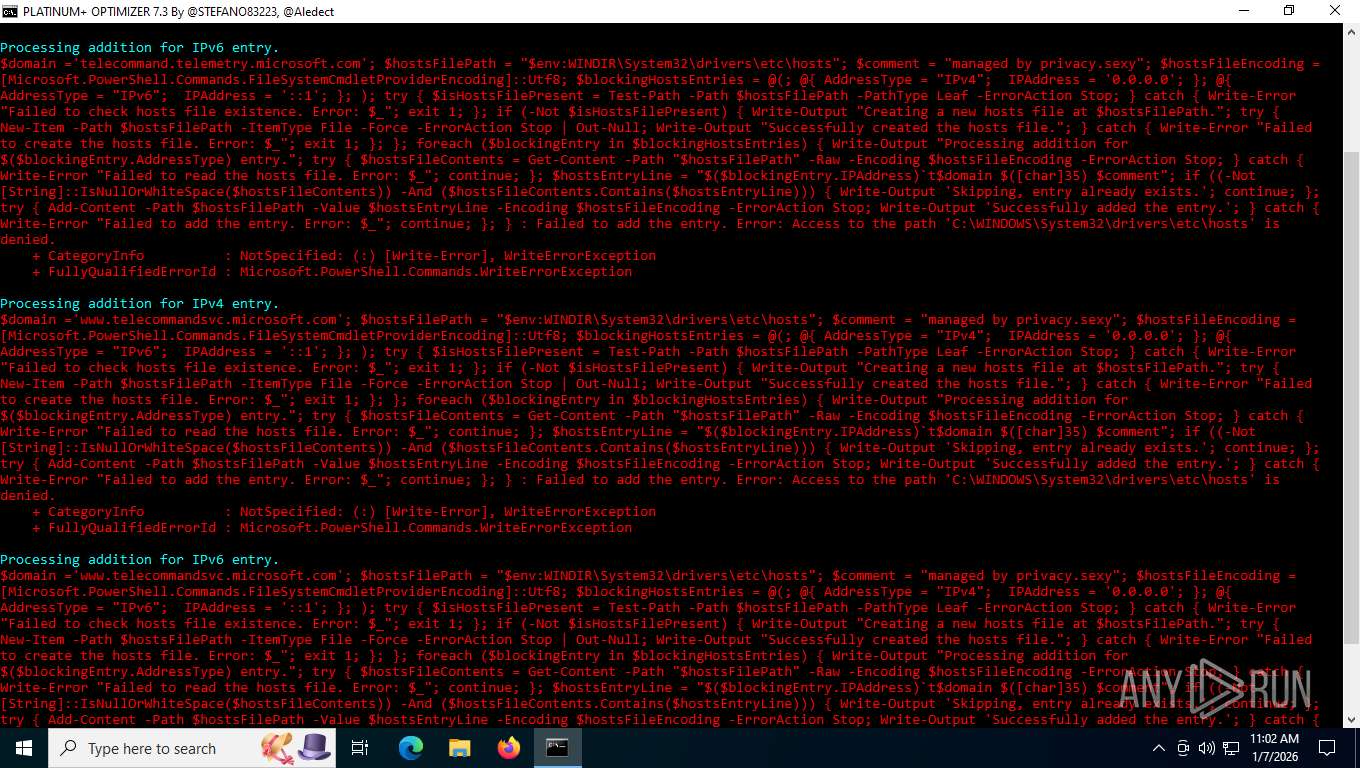
Modifies hosts file to alter network resolution
- powershell.exe (PID: 7216)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 2668)
- powershell.exe (PID: 404)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 4344)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 5104)
- powershell.exe (PID: 1752)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 4508)
- powershell.exe (PID: 7100)
- powershell.exe (PID: 4632)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7496)
INFO
Checks supported languages
- chcp.com (PID: 8144)
- mode.com (PID: 8164)
- chcp.com (PID: 7184)
Changes the display of characters in the console
- cmd.exe (PID: 7496)
Starts MODE.COM to configure console settings
- mode.com (PID: 8164)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7216)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 2668)
- powershell.exe (PID: 404)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 4344)
- powershell.exe (PID: 5104)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 1752)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 4508)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7100)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 4632)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7216)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 404)
- powershell.exe (PID: 2668)
- powershell.exe (PID: 7568)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 7956)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 7068)
- powershell.exe (PID: 6536)
- powershell.exe (PID: 7208)
- powershell.exe (PID: 4344)
- powershell.exe (PID: 7280)
- powershell.exe (PID: 5104)
- powershell.exe (PID: 7596)
- powershell.exe (PID: 1752)
- powershell.exe (PID: 3088)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7100)
- powershell.exe (PID: 4508)
- powershell.exe (PID: 4632)
- powershell.exe (PID: 7992)
Checks proxy server information
- slui.exe (PID: 8032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
178
Monitored processes
36
Malicious processes
26
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='c.msn.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='v10c.events.data.microsoft.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1840 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='arc.msn.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2668 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='assets.msn.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3088 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='eu-v10c.events.data.microsoft.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3692 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='us-v10c.events.data.microsoft.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4344 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='query.prod.cms.rt.microsoft.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4508 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='v10.vortex-win.data.microsoft.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4632 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='www.telecommandsvc.microsoft.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5104 | PowerShell -ExecutionPolicy Unrestricted -Command "$domain ='self.events.data.microsoft.com'; $hostsFilePath = """$env:WINDIR\System32\drivers\etc\hosts"""; $comment = """managed by privacy.sexy"""; $hostsFileEncoding = [Microsoft.PowerShell.Commands.FileSystemCmdletProviderEncoding]::Utf8; $blockingHostsEntries = @(; @{ AddressType = """IPv4"""; IPAddress = '0.0.0.0'; }; @{ AddressType = """IPv6"""; IPAddress = '::1'; }; ); try { $isHostsFilePresent = Test-Path -Path $hostsFilePath -PathType Leaf -ErrorAction Stop; } catch { Write-Error """Failed to check hosts file existence. Error: $_"""; exit 1; }; if (-Not $isHostsFilePresent) { Write-Output """Creating a new hosts file at $hostsFilePath."""; try { New-Item -Path $hostsFilePath -ItemType File -Force -ErrorAction Stop | Out-Null; Write-Output """Successfully created the hosts file."""; } catch { Write-Error """Failed to create the hosts file. Error: $_"""; exit 1; }; }; foreach ($blockingEntry in $blockingHostsEntries) { Write-Output """Processing addition for $($blockingEntry.AddressType) entry."""; try { $hostsFileContents = Get-Content -Path """$hostsFilePath""" -Raw -Encoding $hostsFileEncoding -ErrorAction Stop; } catch { Write-Error """Failed to read the hosts file. Error: $_"""; continue; }; $hostsEntryLine = """$($blockingEntry.IPAddress)`t$domain $([char]35) $comment"""; if ((-Not [String]::IsNullOrWhiteSpace($hostsFileContents)) -And ($hostsFileContents.Contains($hostsEntryLine))) { Write-Output 'Skipping, entry already exists.'; continue; }; try { Add-Content -Path $hostsFilePath -Value $hostsEntryLine -Encoding $hostsFileEncoding -ErrorAction Stop; Write-Output 'Successfully added the entry.'; } catch { Write-Error """Failed to add the entry. Error: $_"""; continue; }; }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
116 469
Read events
116 469
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7216 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jf3bx2mj.o0q.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vptgvnls.x5f.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jhfluzjc.1md.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7216 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:5162D7CF09AD3A9F7C99597A49154A3F | SHA256:A05A3DCEB3FC74820DE909210237434C7667EC3289DEAF1DCBC1E22DE93693AF | |||
| 7216 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uw4u2y14.h4l.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1840 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zw1hqlgb.inn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1840 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wrlvnk3w.k2s.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_exrflb5s.fc0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zvmln1l5.sbq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xhcllc3u.qvf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
26
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
4256 | svchost.exe | POST | 200 | 40.126.32.76:443 | https://login.live.com/RST2.srf | US | xml | 11.1 Kb | whitelisted |
6904 | SIHClient.exe | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
4256 | svchost.exe | POST | 200 | 40.126.32.76:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
6904 | SIHClient.exe | GET | 200 | 20.165.94.63:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
6904 | SIHClient.exe | GET | 304 | 20.165.94.63:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
4256 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
408 | svchost.exe | GET | 200 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.48 Kb | whitelisted |
408 | svchost.exe | GET | 200 | 2.16.164.88:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
408 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1784 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4256 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4256 | svchost.exe | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
408 | svchost.exe | 2.16.164.88:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
408 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |