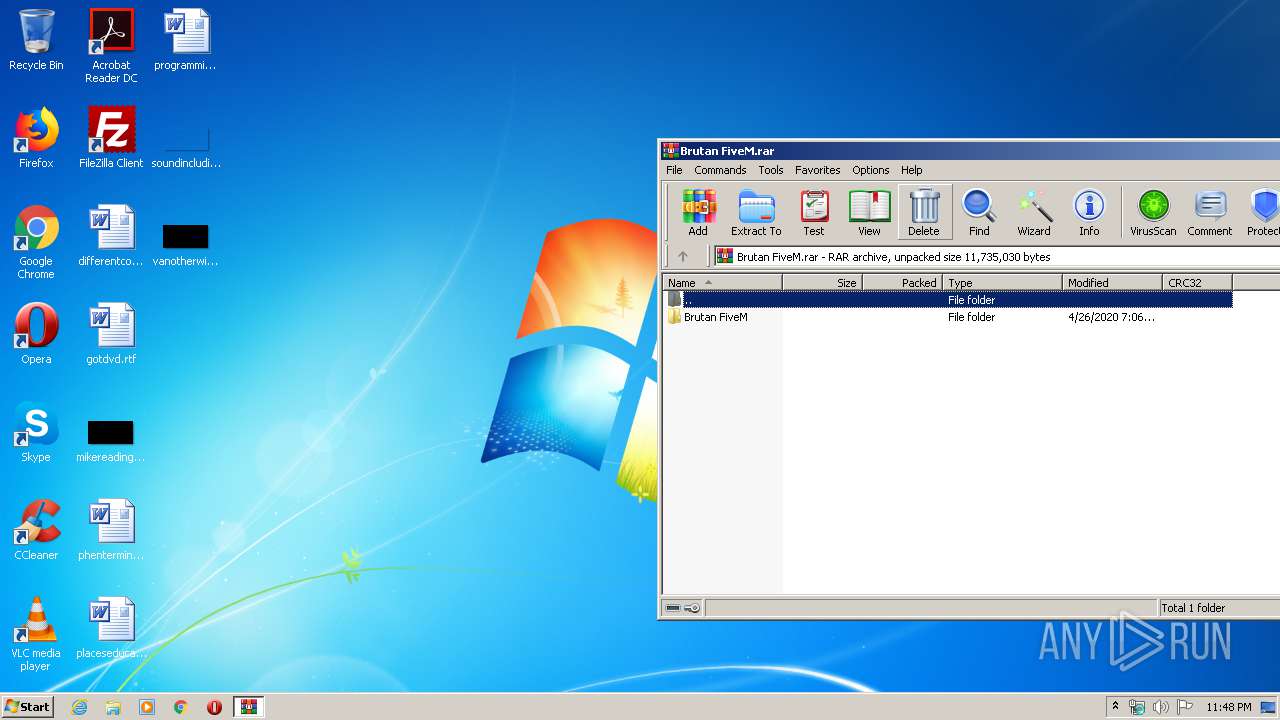
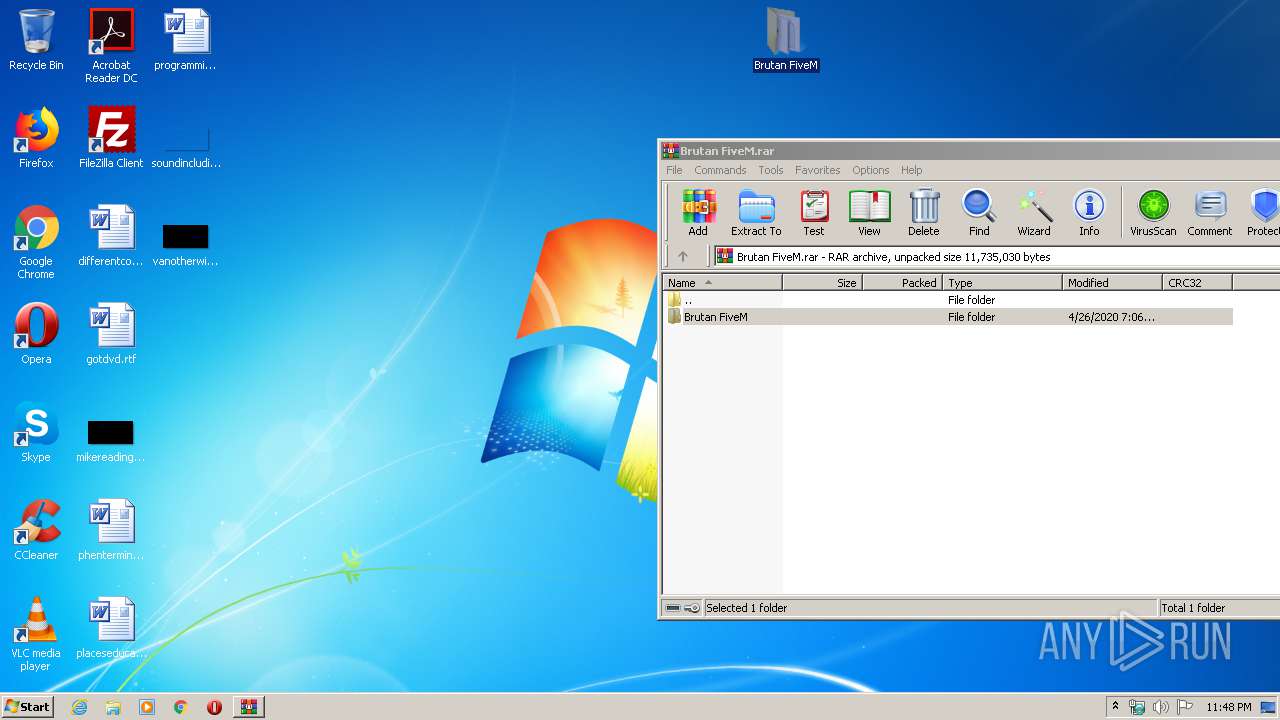
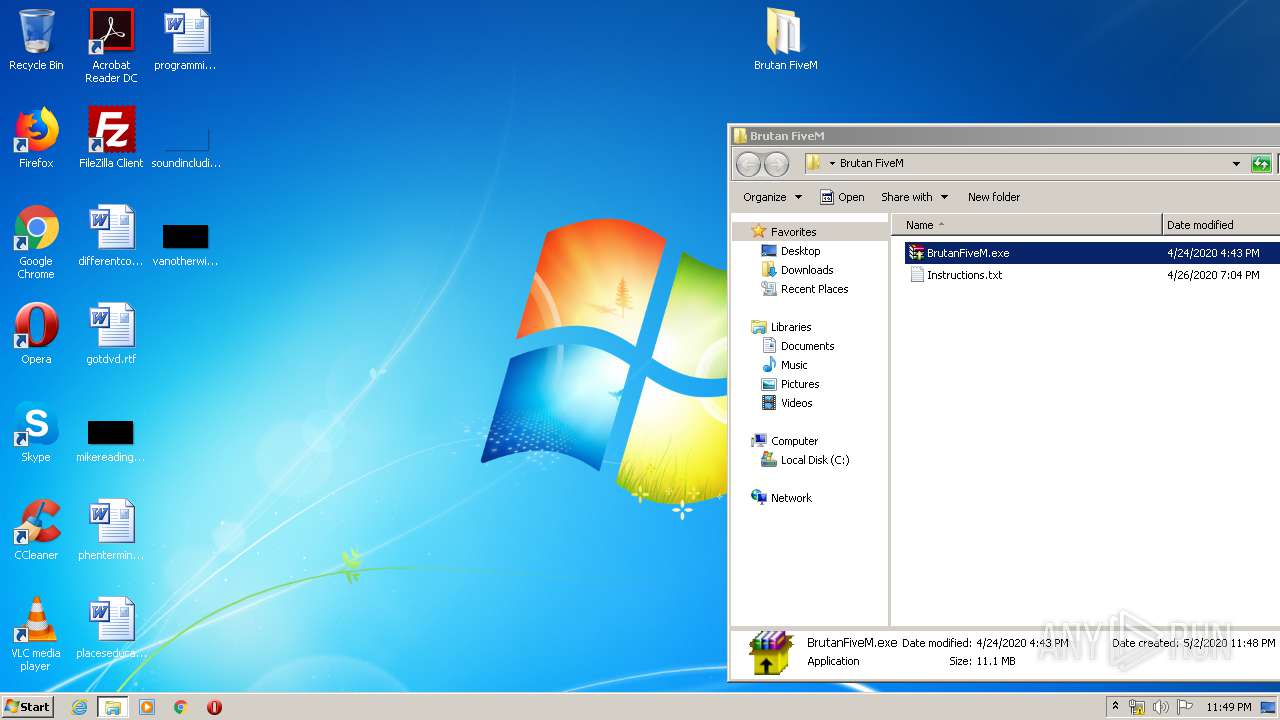
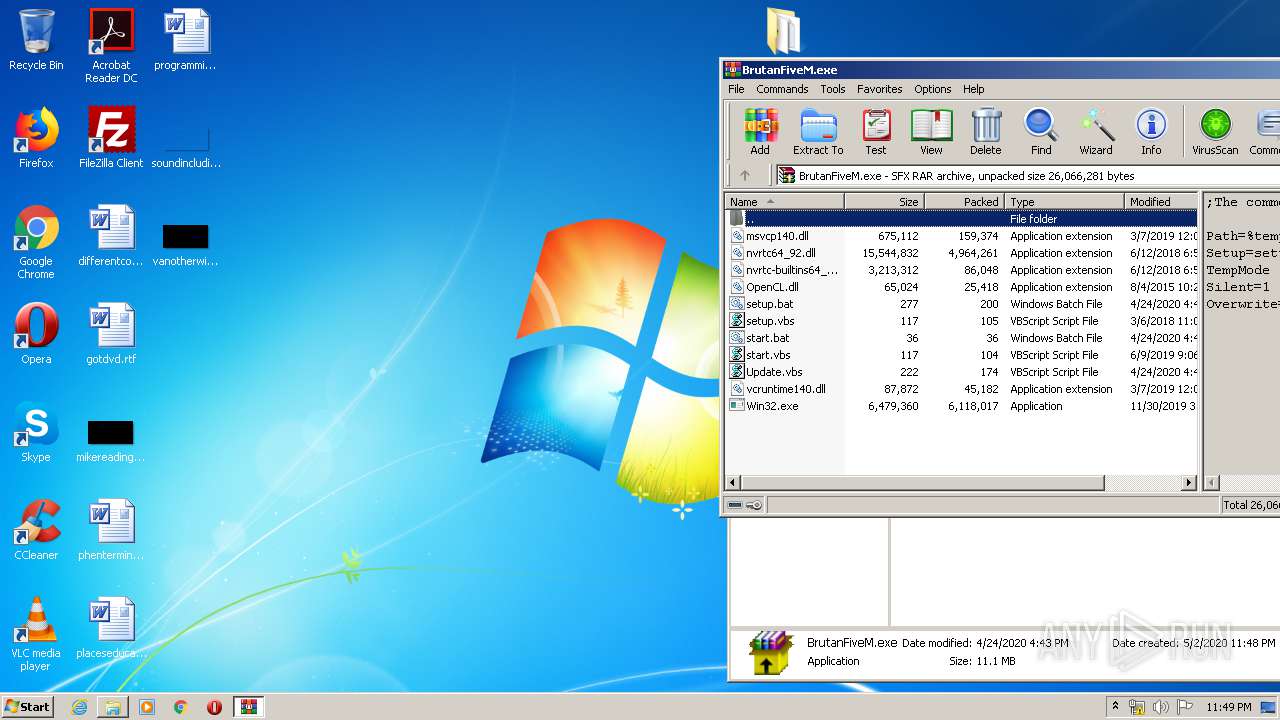
| File name: | Brutan FiveM.rar |
| Full analysis: | https://app.any.run/tasks/df763596-d511-4edc-a7e0-79ebc139f82e |
| Verdict: | Malicious activity |
| Analysis date: | May 02, 2020, 22:47:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 1C5664FC20DE5E385DF8D3EFFE33819D |
| SHA1: | 3F63D6B84528CD0FA7880833D3F76984843AF370 |
| SHA256: | EDE615DC6AE71C56B6676D50ABEDC950AABF0C76EBCFE423602F668A7E6833D8 |
| SSDEEP: | 196608:8mdTQG9Hj/HgO6JXZ6lwSEemXWswRXnxgrFV71pqjUPrdGHWFh50XtRaPHHTZEpJ:8msGTkUwdemJQnerPu0rdGHIstAPHHtG |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 1136)
- reg.exe (PID: 880)
Actions looks like stealing of personal data
- BrutanFiveM.exe (PID: 3016)
- BrutanFiveM.exe (PID: 2828)
SUSPICIOUS
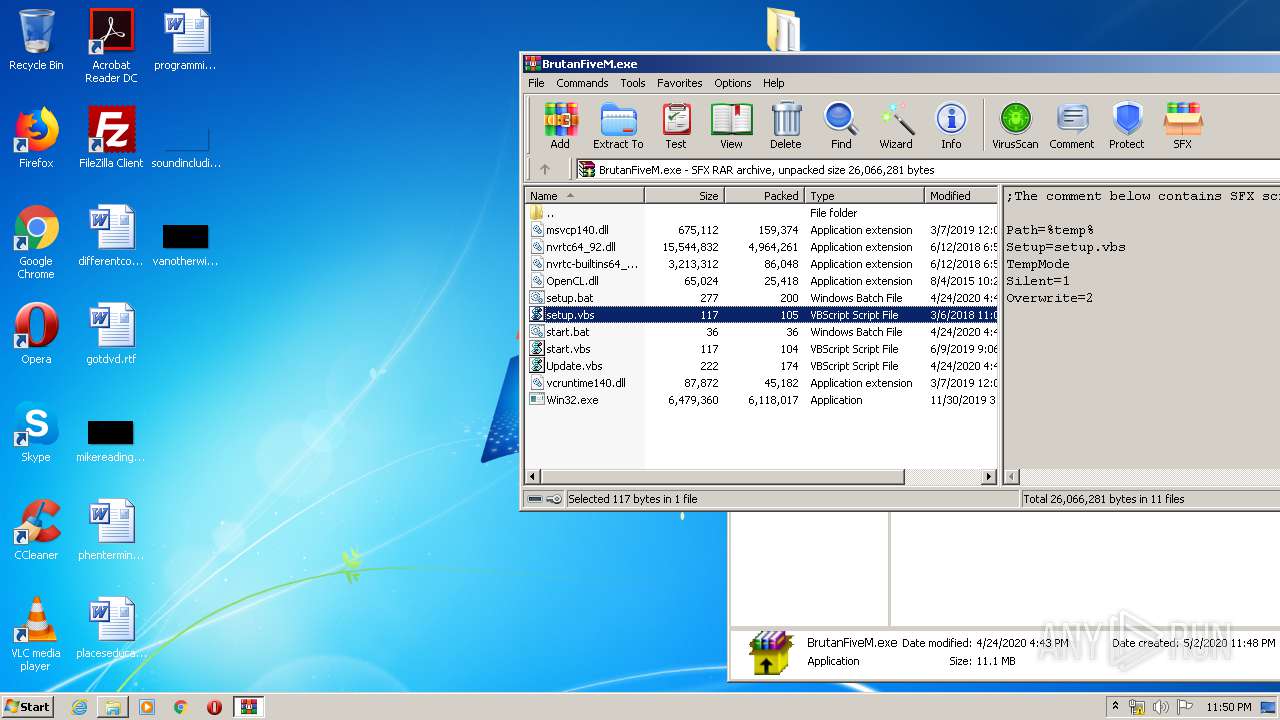
Executable content was dropped or overwritten
- BrutanFiveM.exe (PID: 3016)
- cmd.exe (PID: 3012)
- BrutanFiveM.exe (PID: 2828)
- cmd.exe (PID: 540)
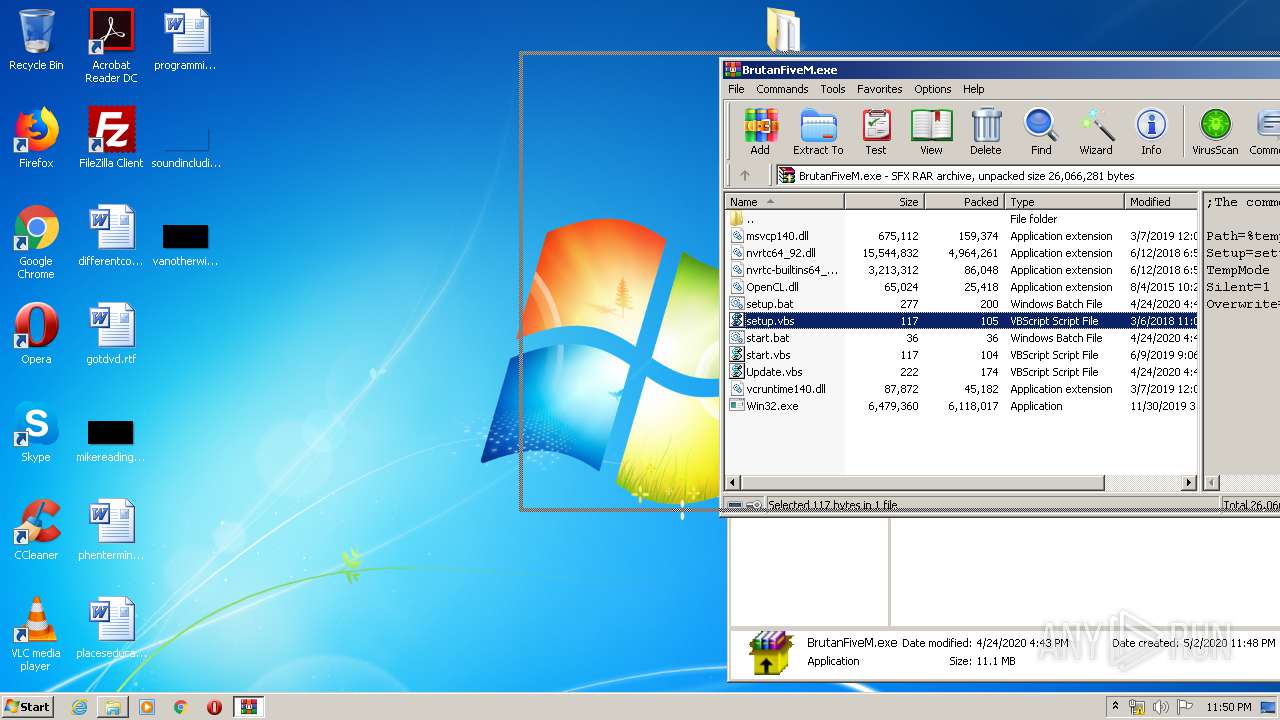
Executes scripts
- BrutanFiveM.exe (PID: 3016)
- cmd.exe (PID: 3012)
- WScript.exe (PID: 3440)
- BrutanFiveM.exe (PID: 2828)
- cmd.exe (PID: 540)
- WScript.exe (PID: 2860)
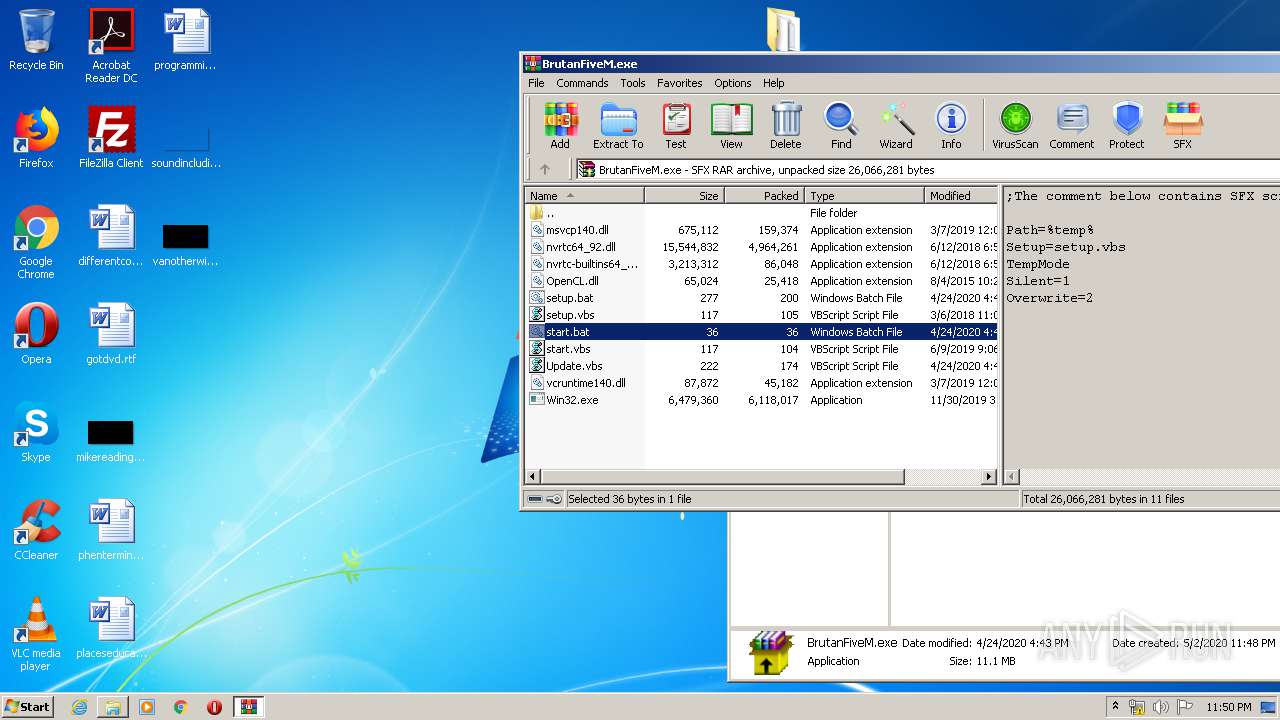
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3012)
- cmd.exe (PID: 540)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3616)
- WScript.exe (PID: 3100)
- WScript.exe (PID: 2728)
- WScript.exe (PID: 1028)
- WScript.exe (PID: 3624)
- WScript.exe (PID: 3084)
- WinRAR.exe (PID: 1828)
Creates files in the user directory
- cmd.exe (PID: 3012)
Application launched itself
- WScript.exe (PID: 3440)
- WScript.exe (PID: 2860)
INFO
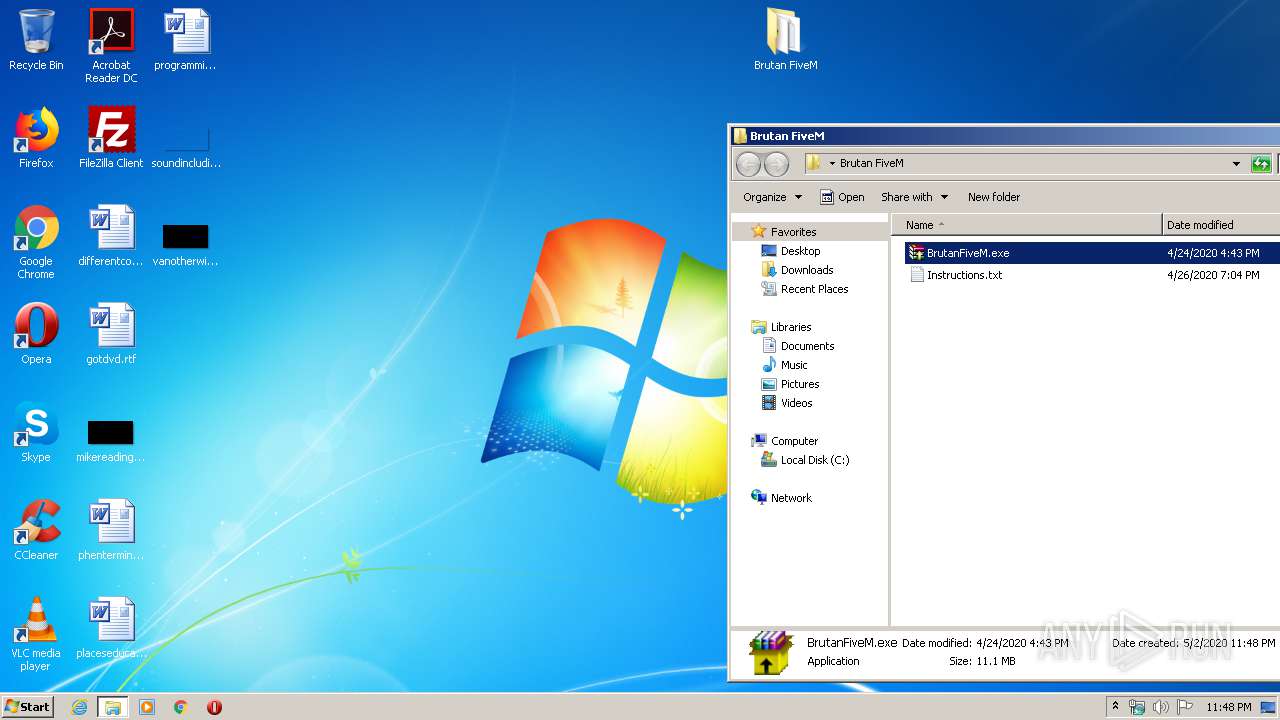
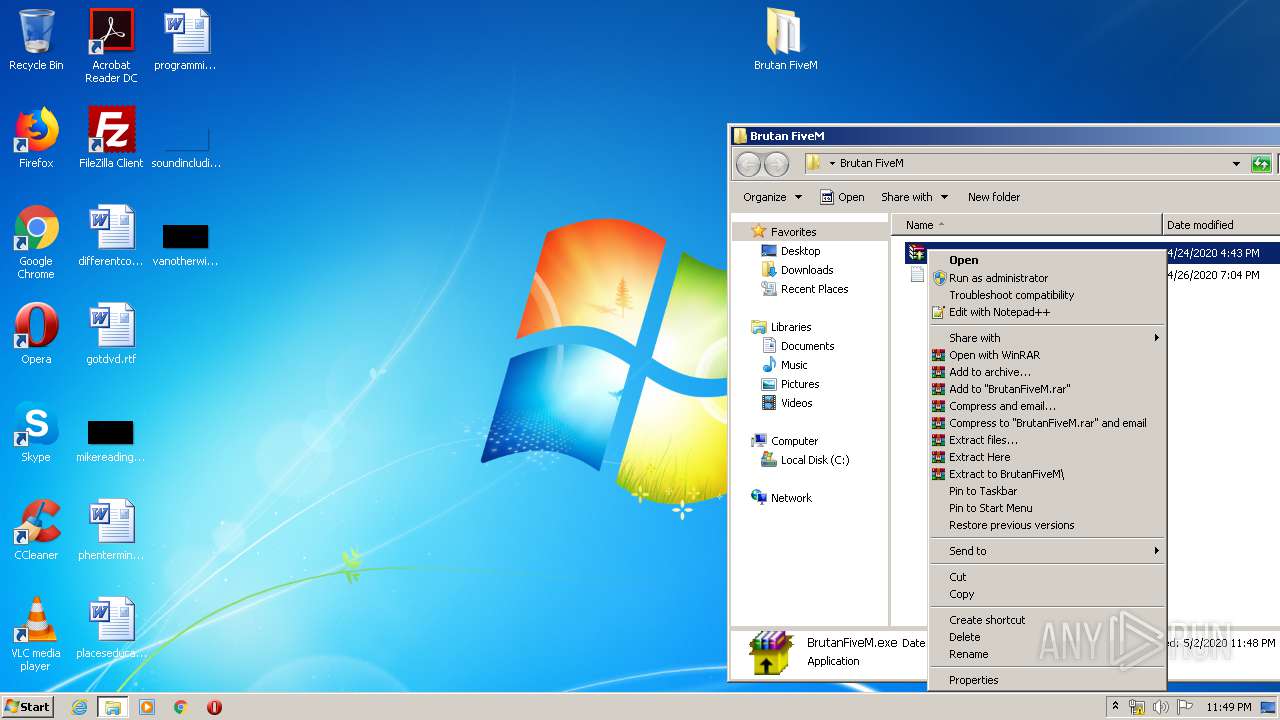
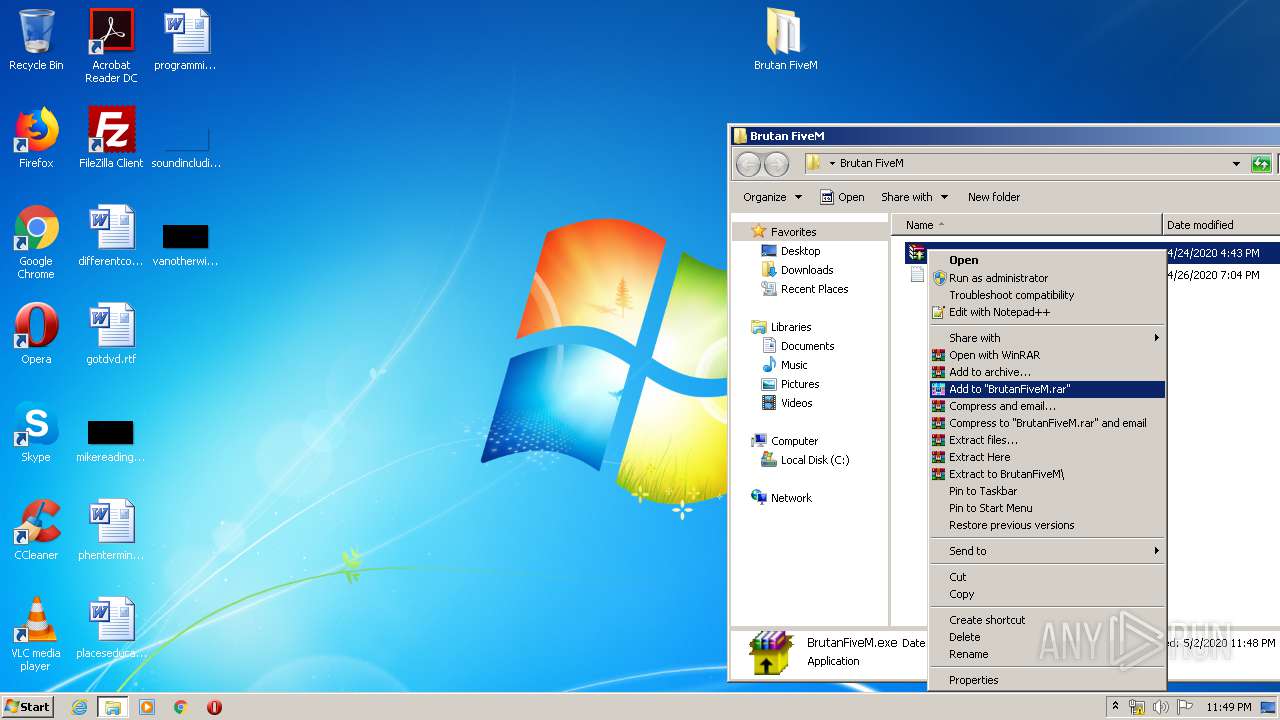
Manual execution by user
- BrutanFiveM.exe (PID: 3016)
- BrutanFiveM.exe (PID: 2828)
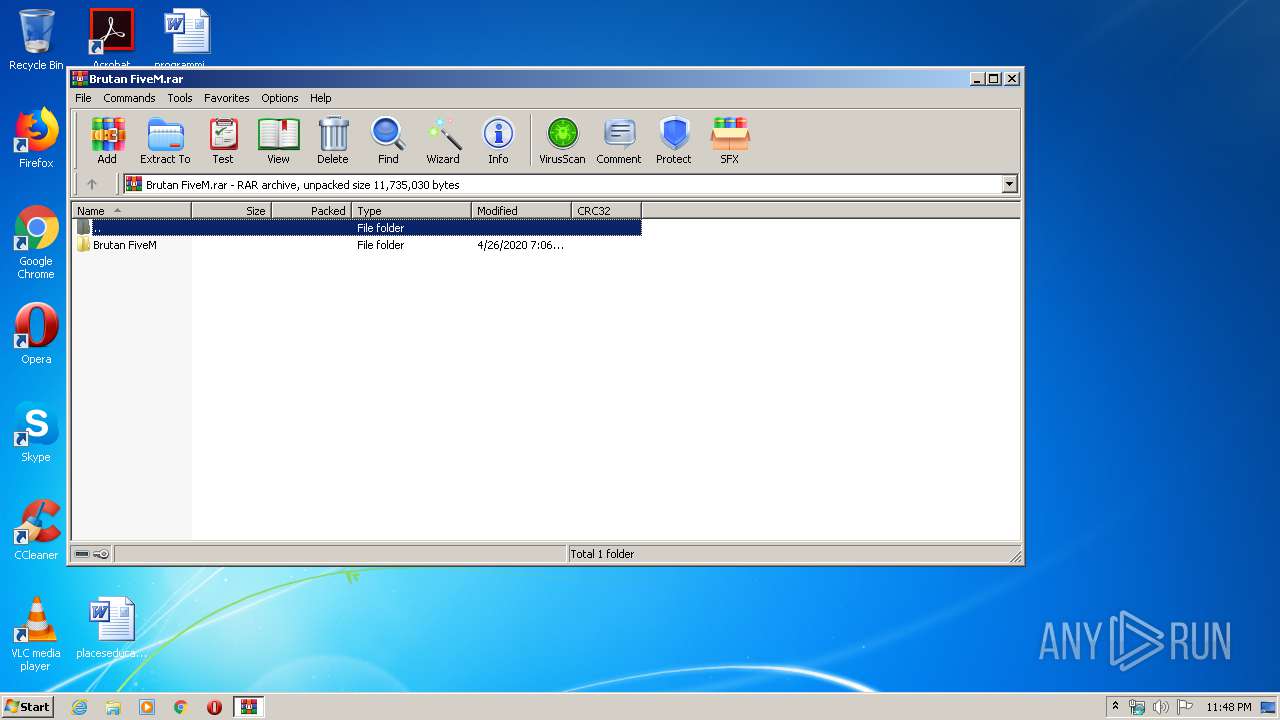
- WinRAR.exe (PID: 1828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
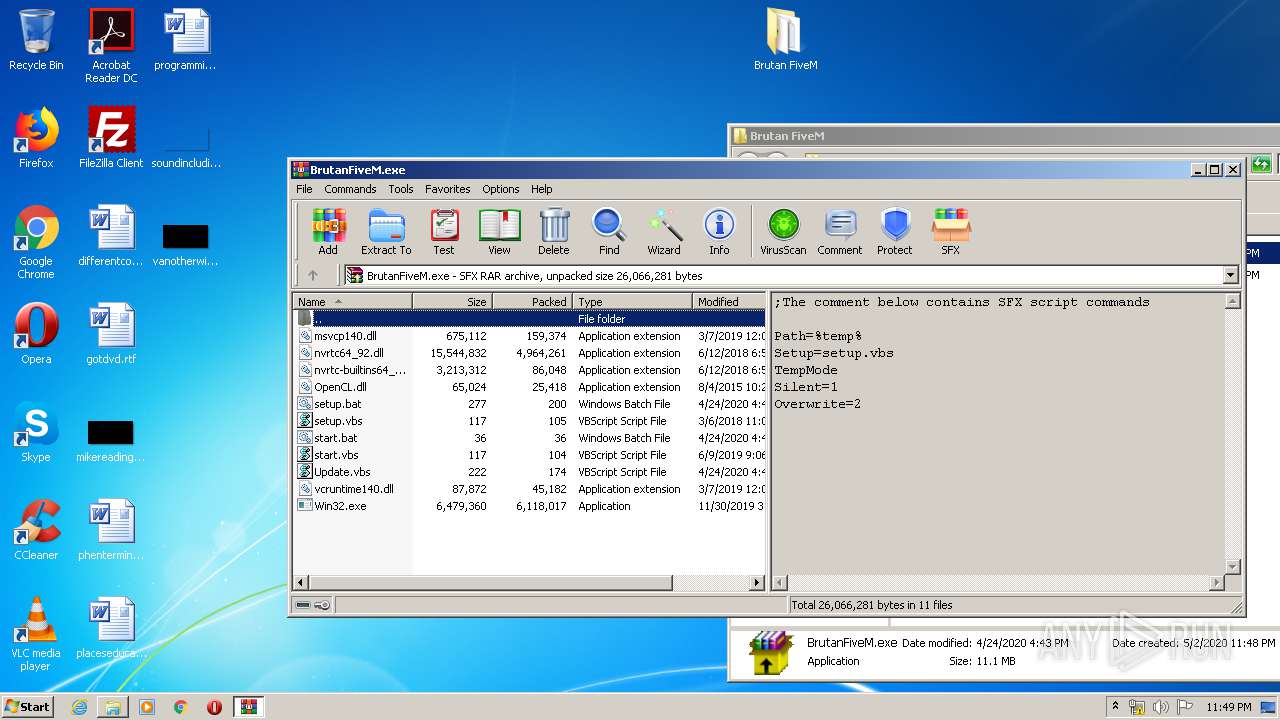
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
62
Monitored processes
21
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | cmd /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.bat" " | C:\Windows\System32\cmd.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 880 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v "SteamUpdates" /t REG_SZ /d ""C:\Users\admin\AppData\Roaming"\Win32\Update.vbs" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.vbs" | C:\Windows\System32\WScript.exe | — | BrutanFiveM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1136 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v "SteamUpdates" /t REG_SZ /d ""C:\Users\admin\AppData\Roaming"\Win32\Update.vbs" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
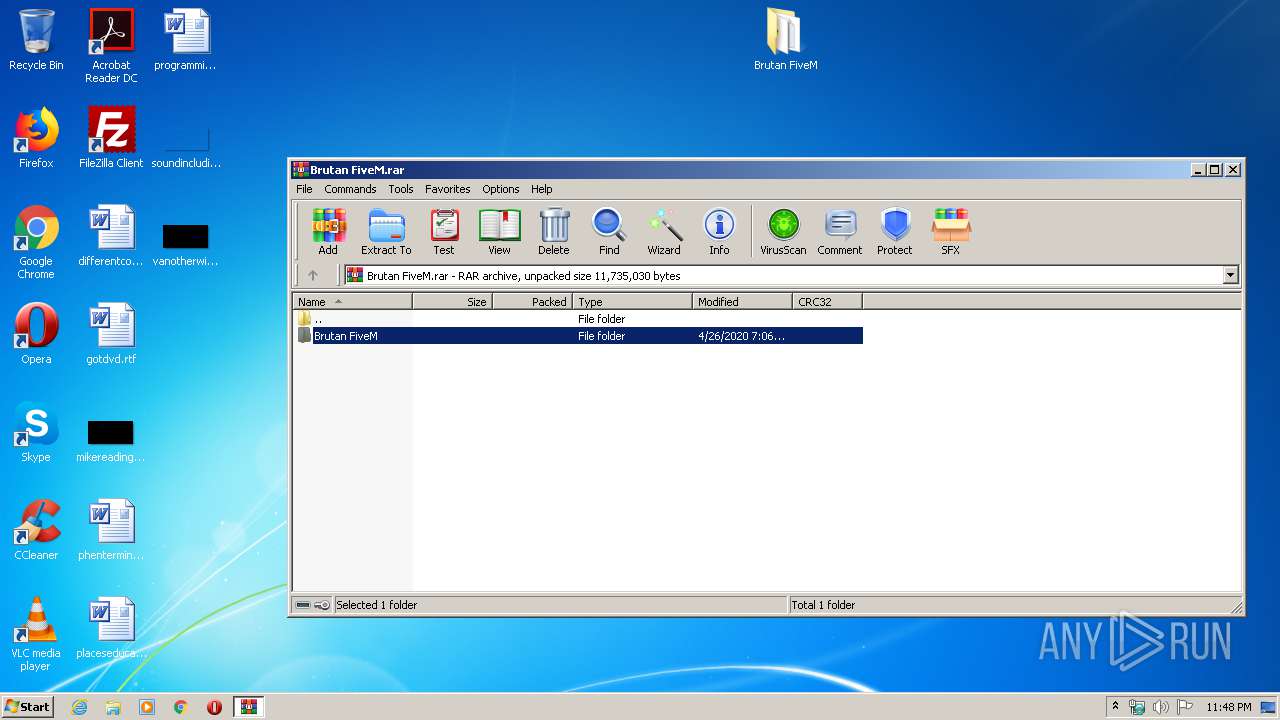
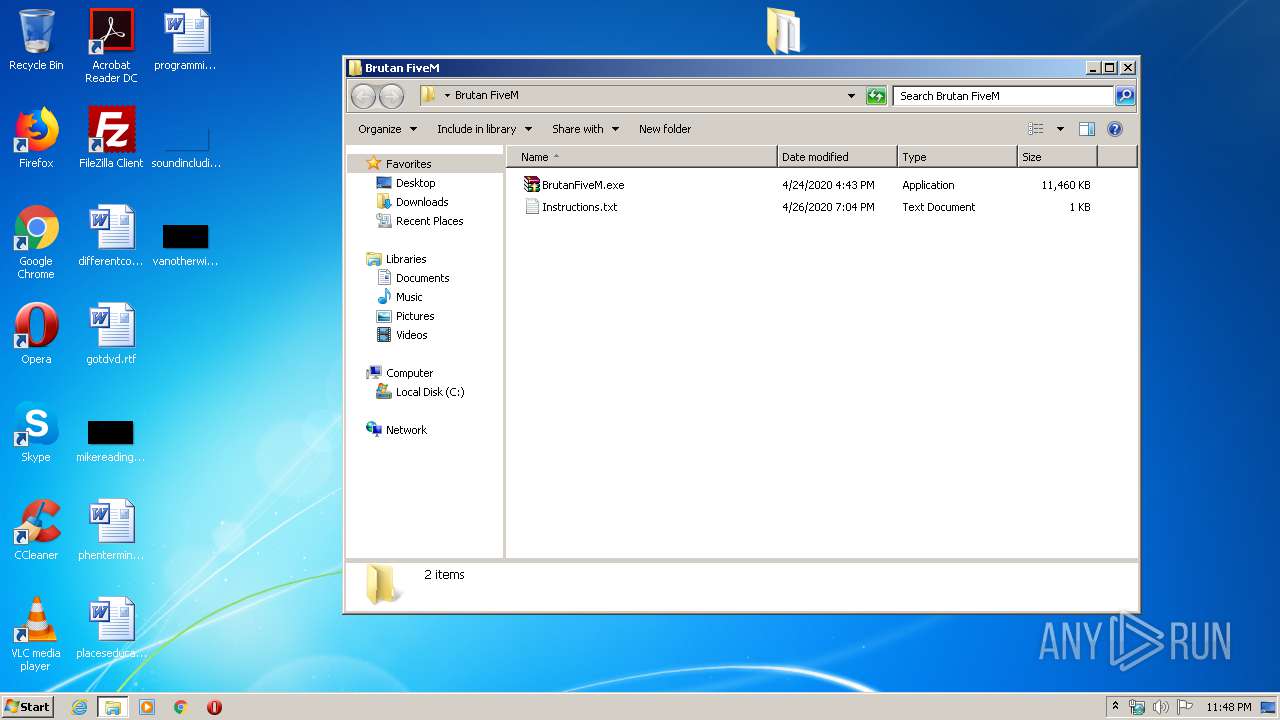
| 1828 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Brutan FiveM\BrutanFiveM.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2276 | cmd /c ""C:\Users\admin\AppData\Roaming\Win32\start.bat" " | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2672 | cmd /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\start.bat" " | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2728 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Win32\start.vbs" | C:\Windows\System32\WScript.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2784 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Brutan FiveM.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2828 | "C:\Users\admin\Desktop\Brutan FiveM\BrutanFiveM.exe" | C:\Users\admin\Desktop\Brutan FiveM\BrutanFiveM.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
5 517
Read events
5 424
Write events
93
Delete events
0
Modification events
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Brutan FiveM.rar | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF1F0100009D000000DF0400006A020000 | |||
| (PID) Process: | (2784) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
24
Suspicious files
0
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2784.1691\Brutan FiveM\BrutanFiveM.exe | — | |
MD5:— | SHA256:— | |||
| 2784 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2784.1691\Brutan FiveM\Instructions.txt | — | |
MD5:— | SHA256:— | |||
| 3016 | BrutanFiveM.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\nvrtc-builtins64_92.dll | executable | |
MD5:— | SHA256:— | |||
| 3016 | BrutanFiveM.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\vcruntime140.dll | executable | |
MD5:— | SHA256:— | |||
| 3016 | BrutanFiveM.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Win32.exe | executable | |
MD5:— | SHA256:— | |||
| 3016 | BrutanFiveM.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\start.bat | text | |
MD5:— | SHA256:— | |||
| 3016 | BrutanFiveM.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Update.vbs | text | |
MD5:— | SHA256:— | |||
| 3016 | BrutanFiveM.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\nvrtc64_92.dll | executable | |
MD5:— | SHA256:— | |||
| 3012 | cmd.exe | C:\Users\admin\AppData\Roaming\Win32\nvrtc-builtins64_92.dll | executable | |
MD5:— | SHA256:— | |||
| 3012 | cmd.exe | C:\Users\admin\AppData\Roaming\Win32\setup.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report