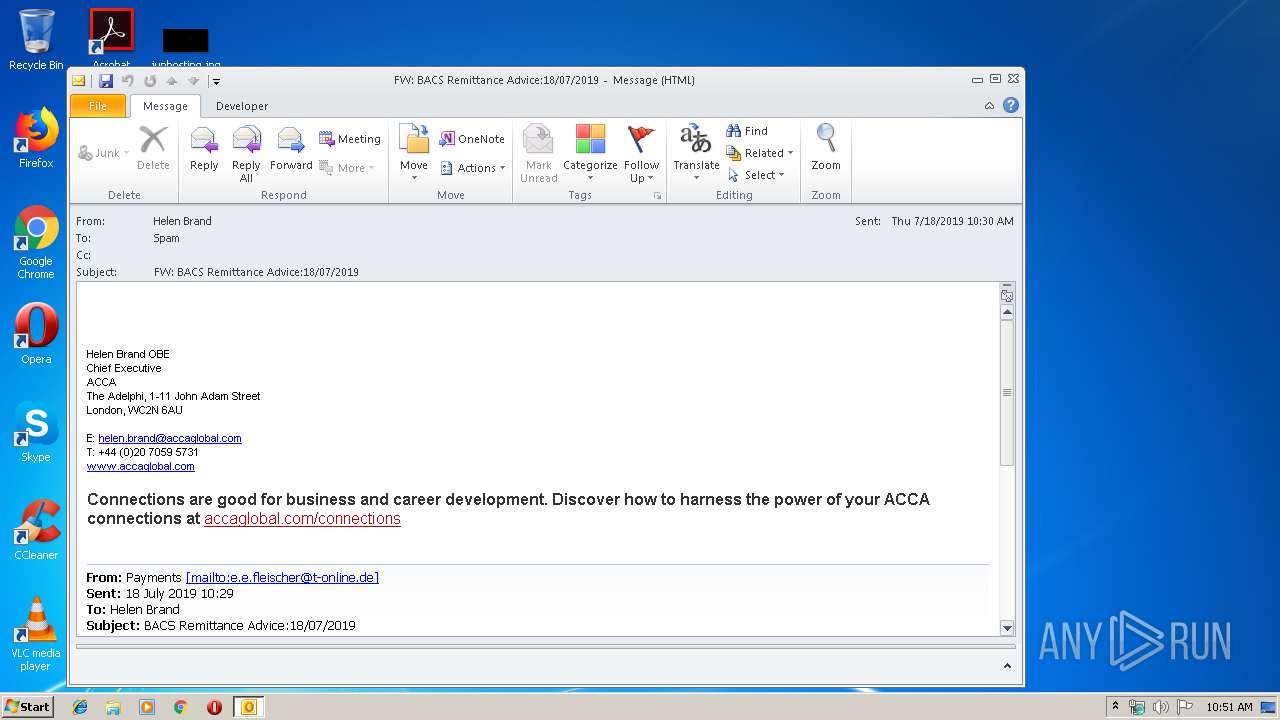
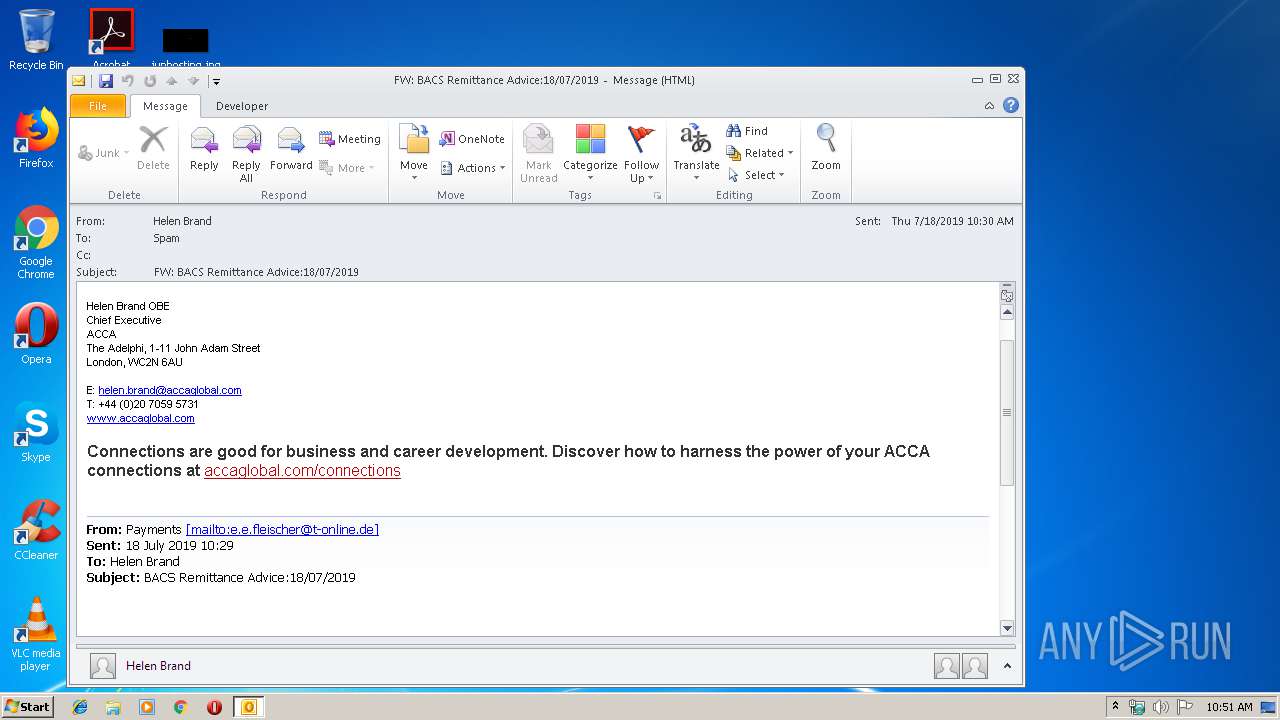
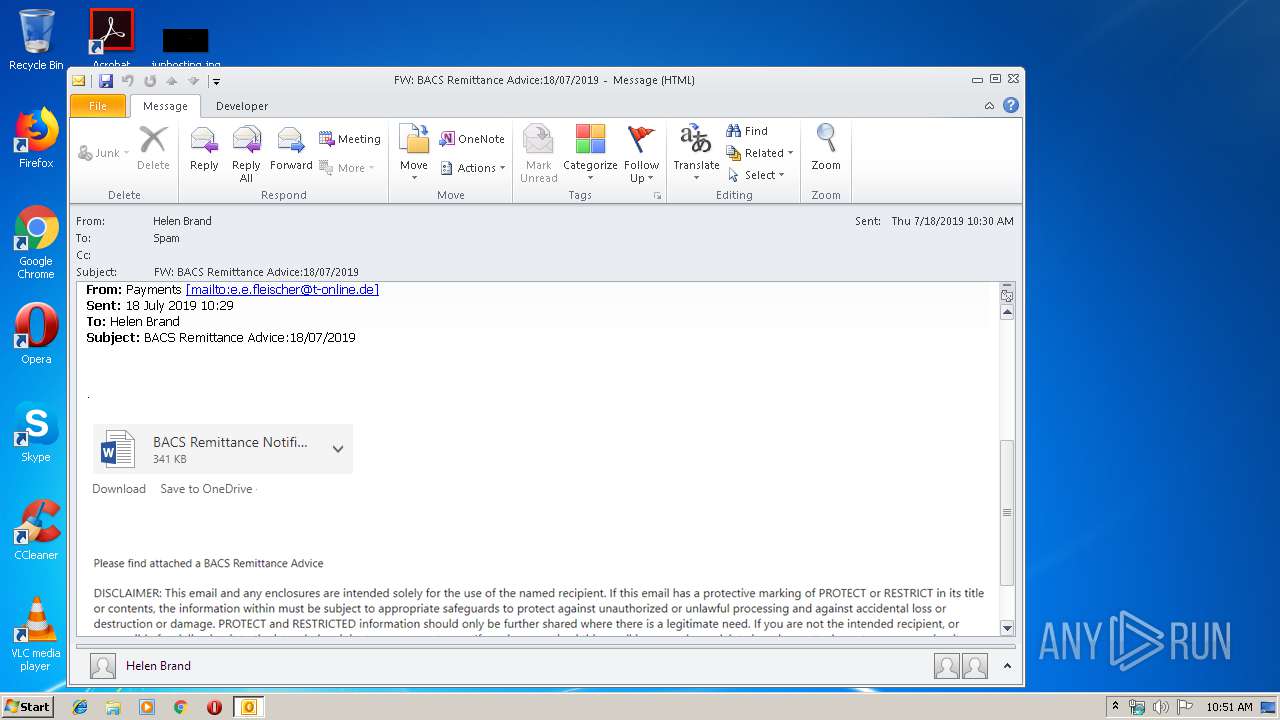
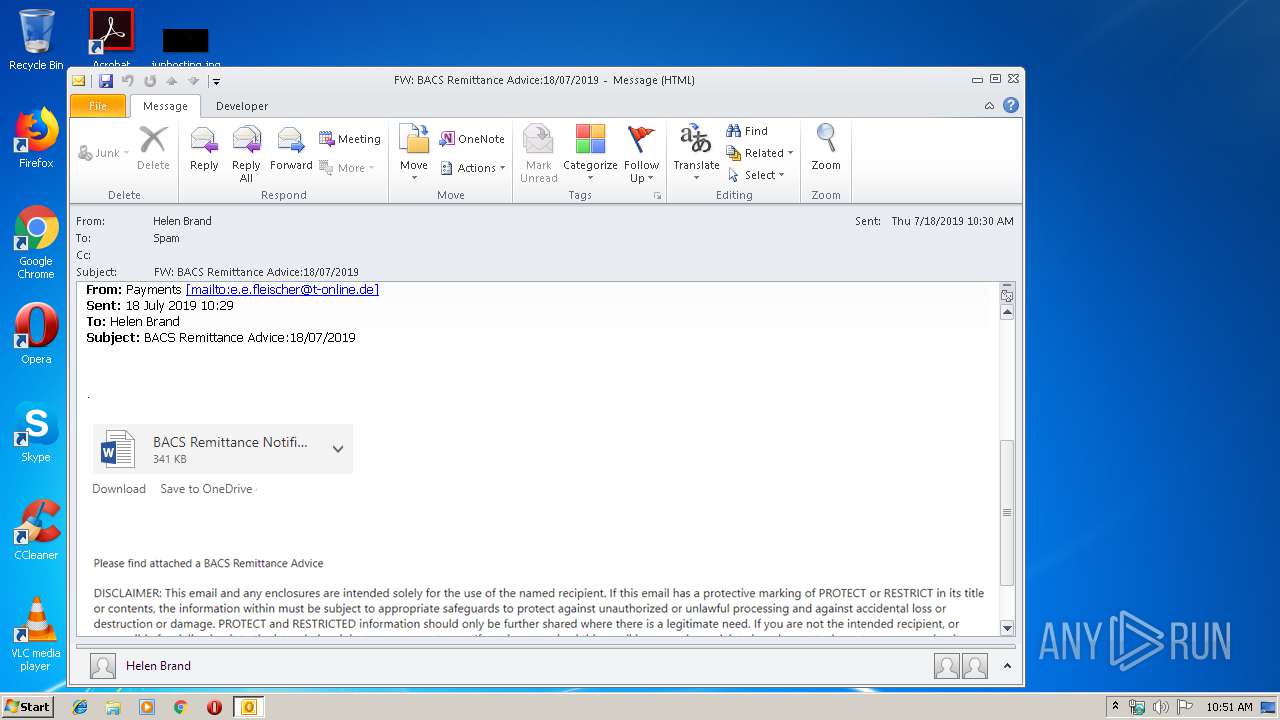
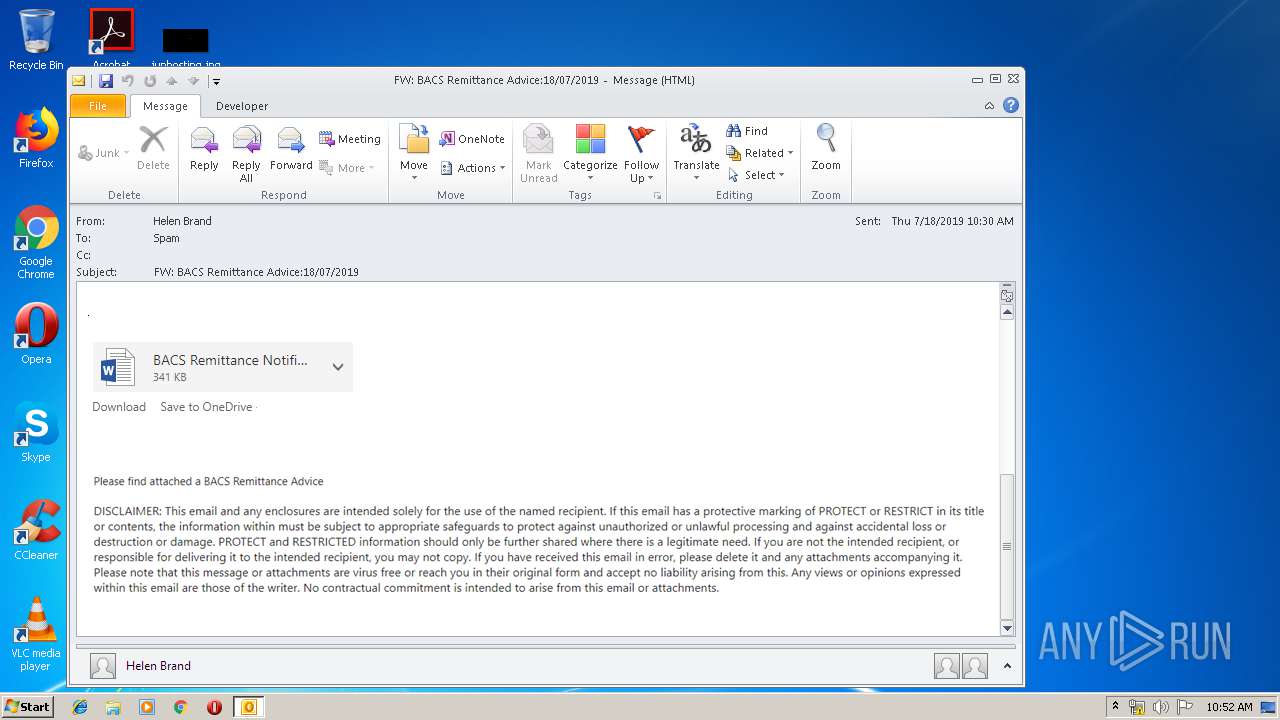
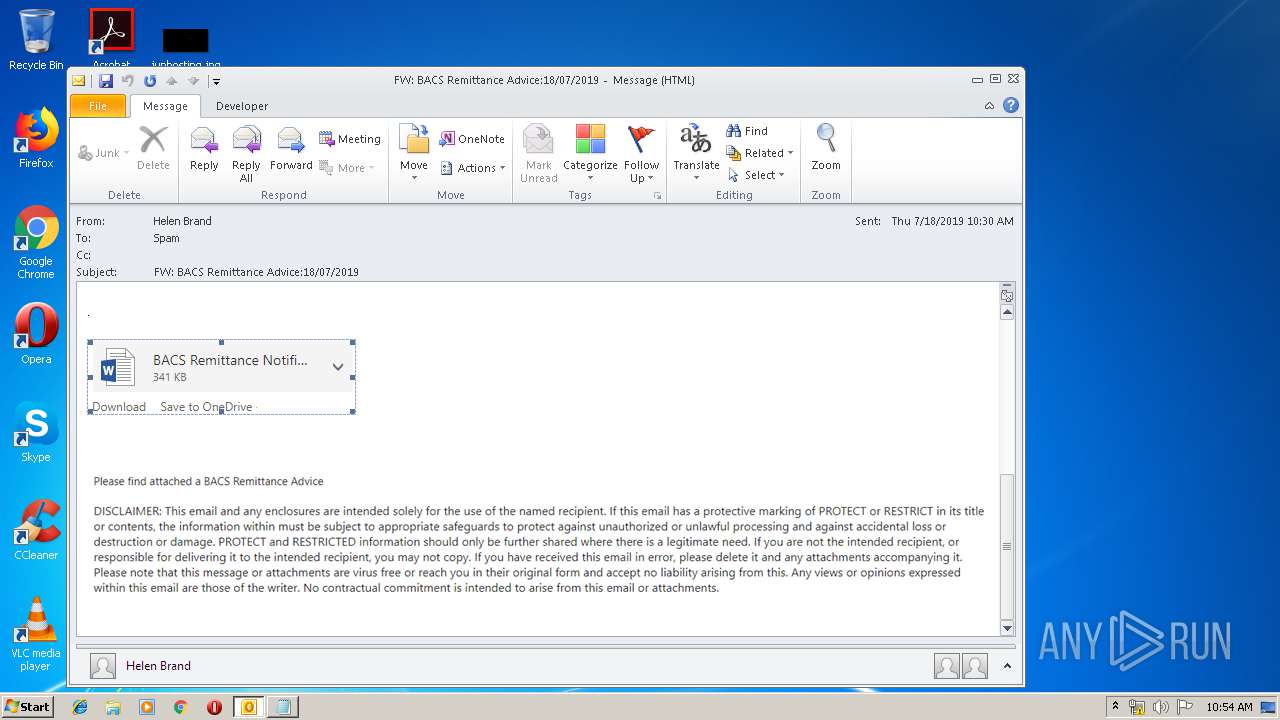
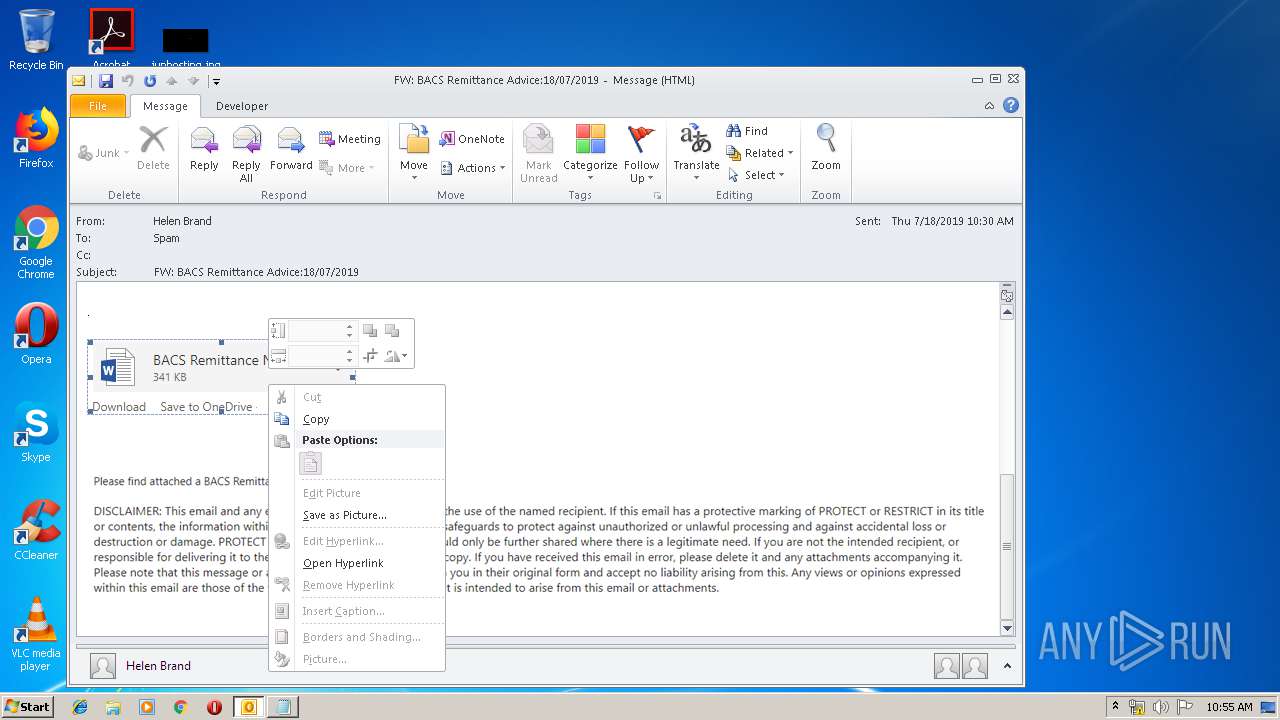
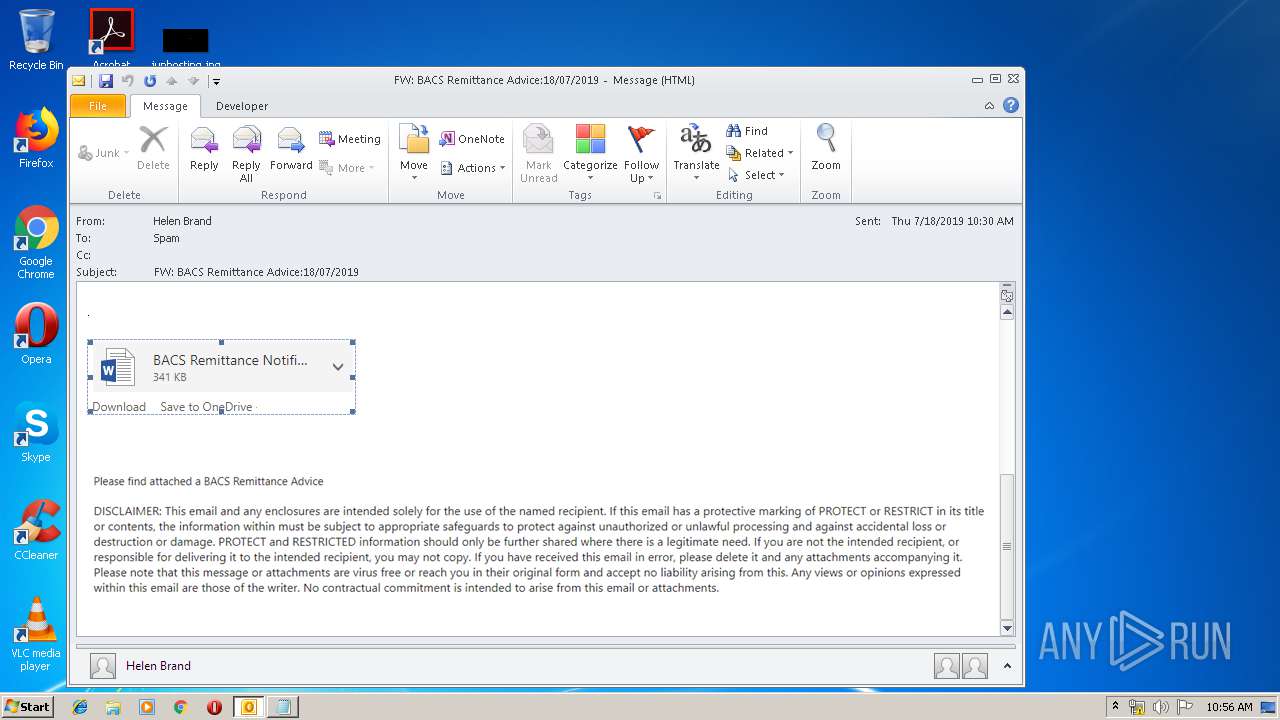
| File name: | FW BACS Remittance Advice18072019.msg |
| Full analysis: | https://app.any.run/tasks/eeed3451-2986-4133-bf89-f63c2b264de9 |
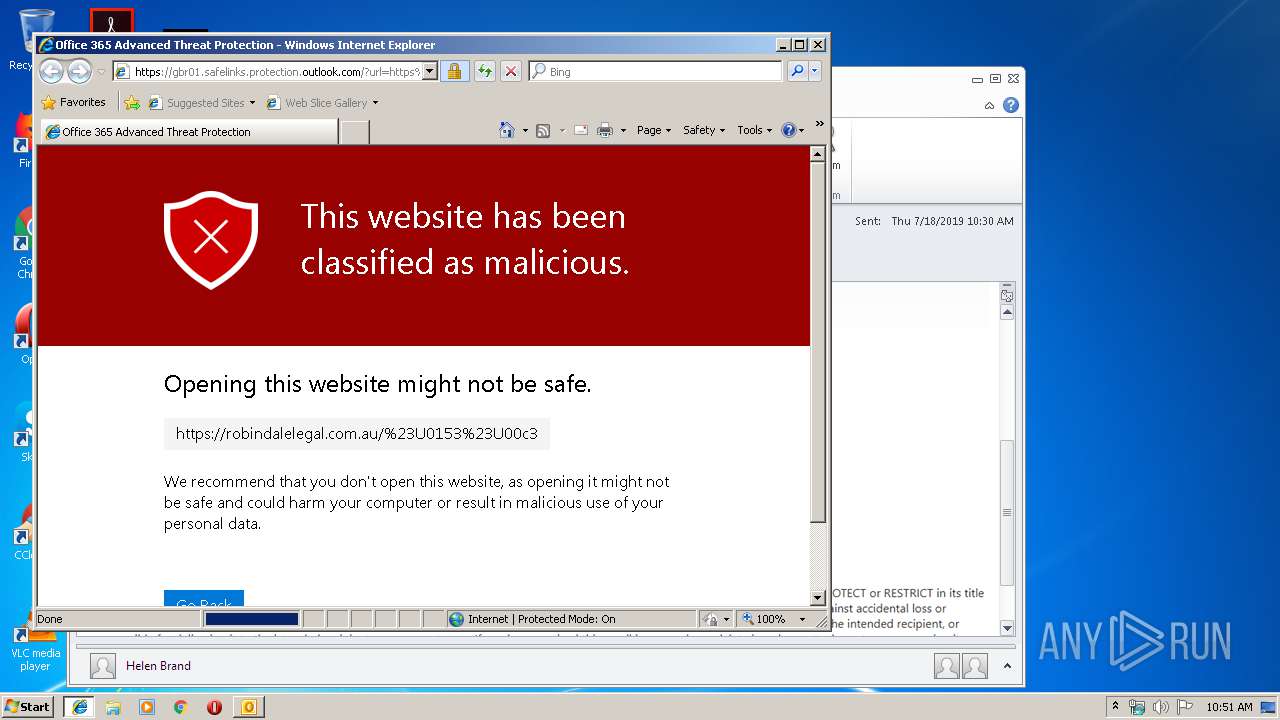
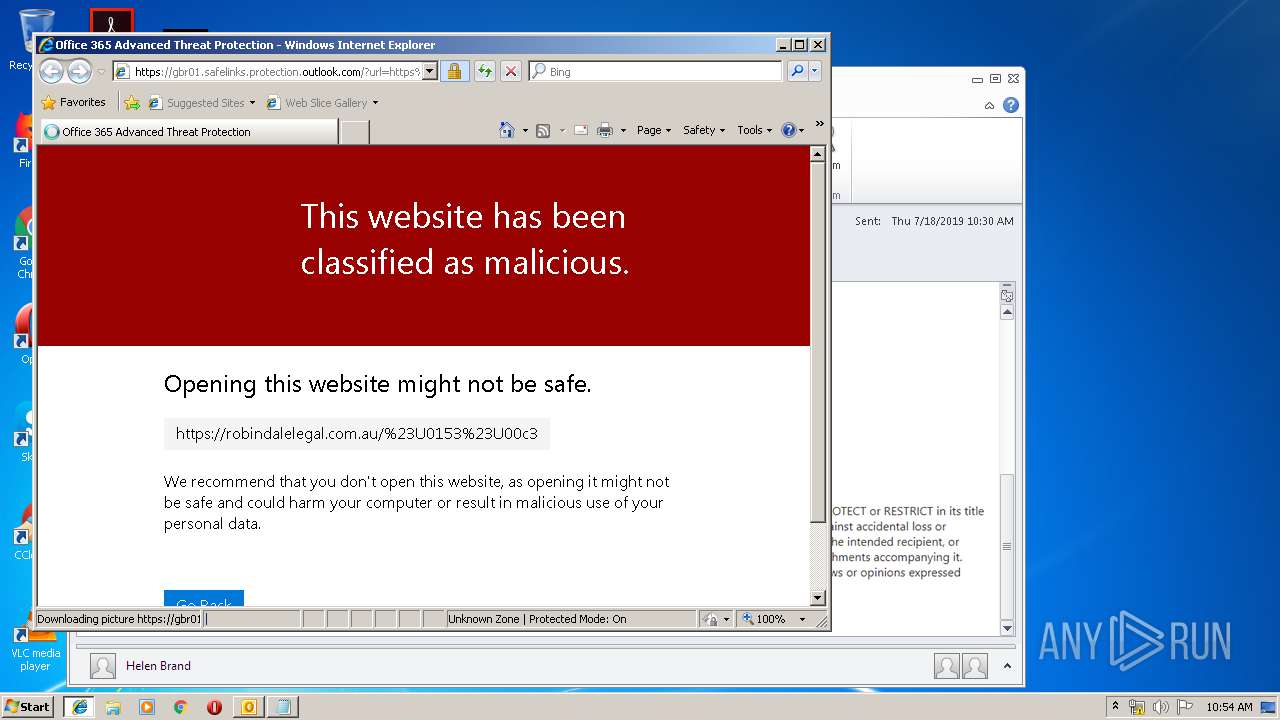
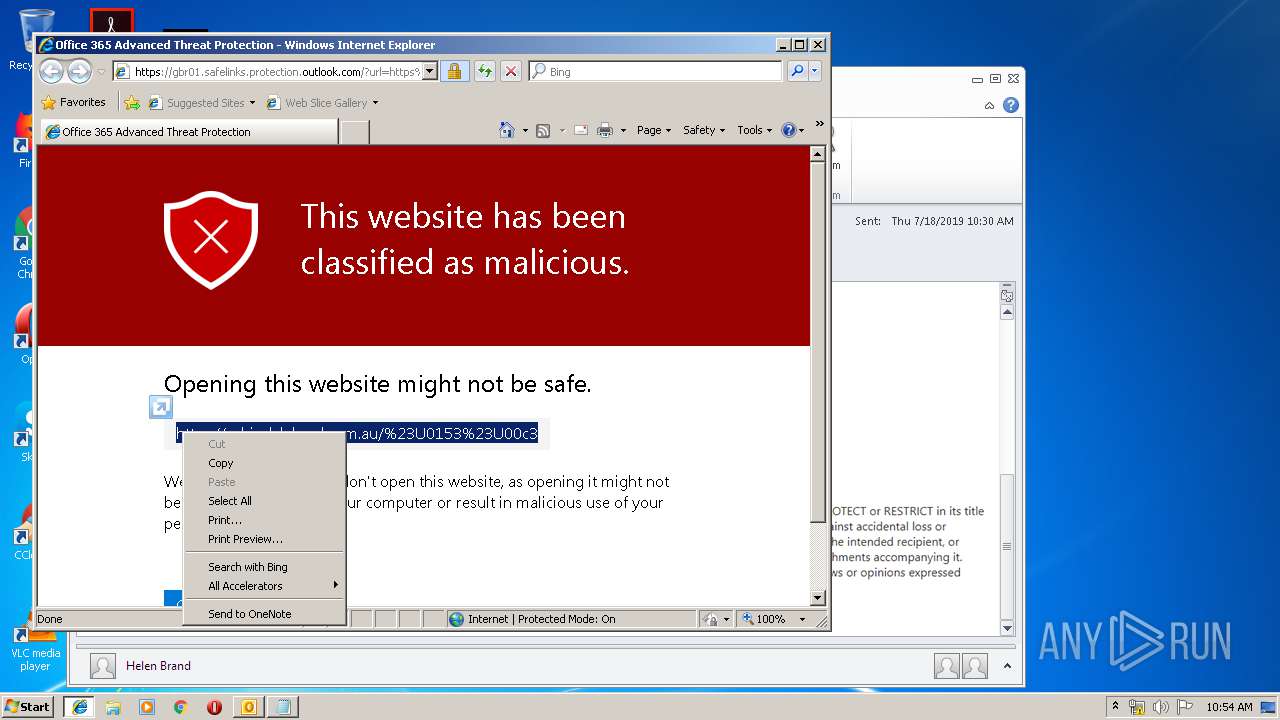
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 09:51:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 56EFB3D5618A082552F7337A9AD4E3F3 |
| SHA1: | 77BD25C2AAD670627B67C1FE68A1B2D5EAB5799D |
| SHA256: | EDE3DDFAA1604EEDF8882C3350E4B29722238133EEA0EACD62656CAF2D8AC6BE |
| SSDEEP: | 3072:PqRWzrNSeG8wySiSSEkEzz+qgqrH/fUDiDl3ML4D6/pqgQTZIeka:JJGLdcL24Sxk |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2960)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2960)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2960)
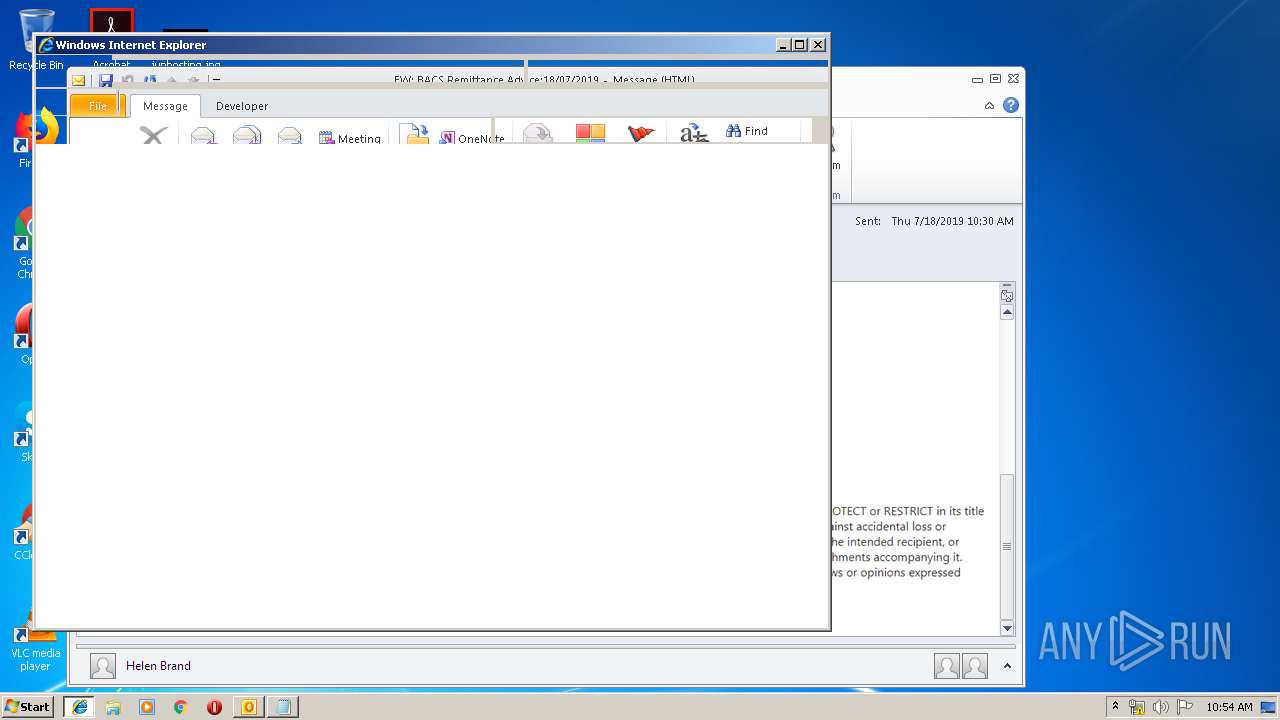
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2960)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3260)
- iexplore.exe (PID: 3736)
Application launched itself
- iexplore.exe (PID: 3260)
- iexplore.exe (PID: 3736)
Reads Internet Cache Settings
- iexplore.exe (PID: 3920)
- iexplore.exe (PID: 272)
Creates files in the user directory
- iexplore.exe (PID: 3920)
Reads settings of System Certificates
- iexplore.exe (PID: 3260)
- iexplore.exe (PID: 3736)
Reads internet explorer settings
- iexplore.exe (PID: 3920)
- iexplore.exe (PID: 272)
Changes settings of System certificates
- iexplore.exe (PID: 3260)
- iexplore.exe (PID: 3736)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3260)
- iexplore.exe (PID: 3736)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
40
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3736 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
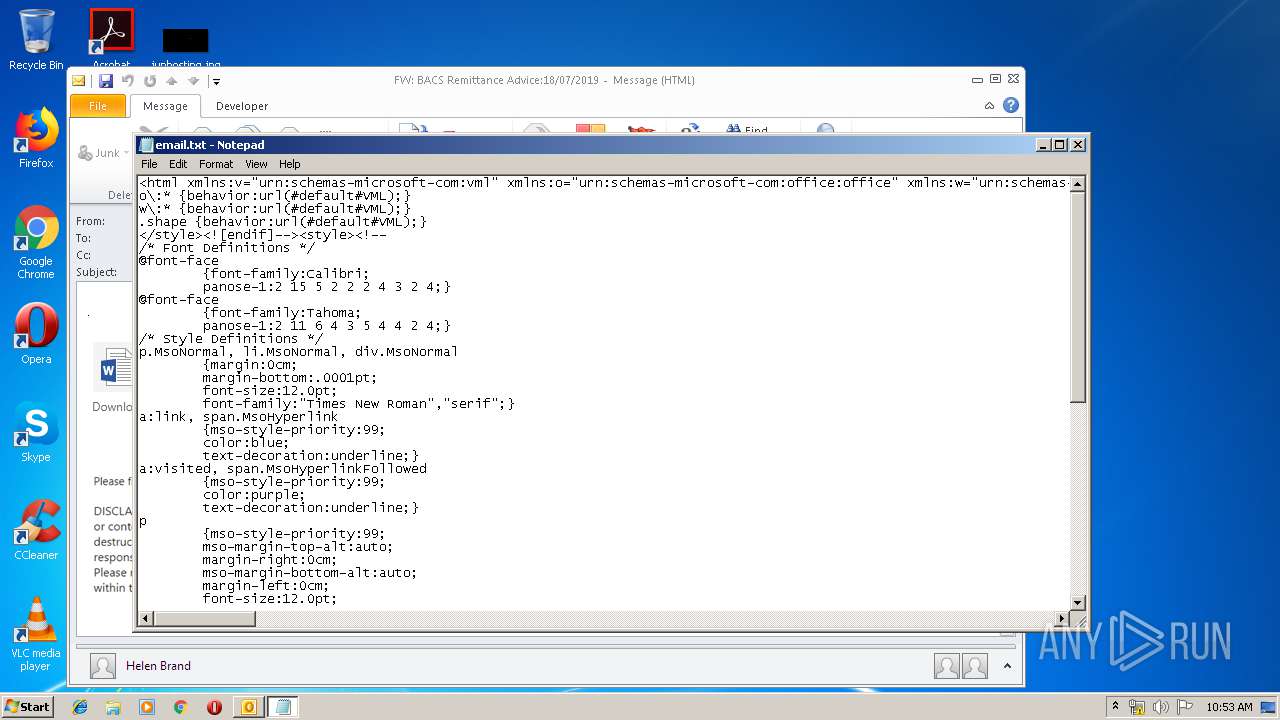
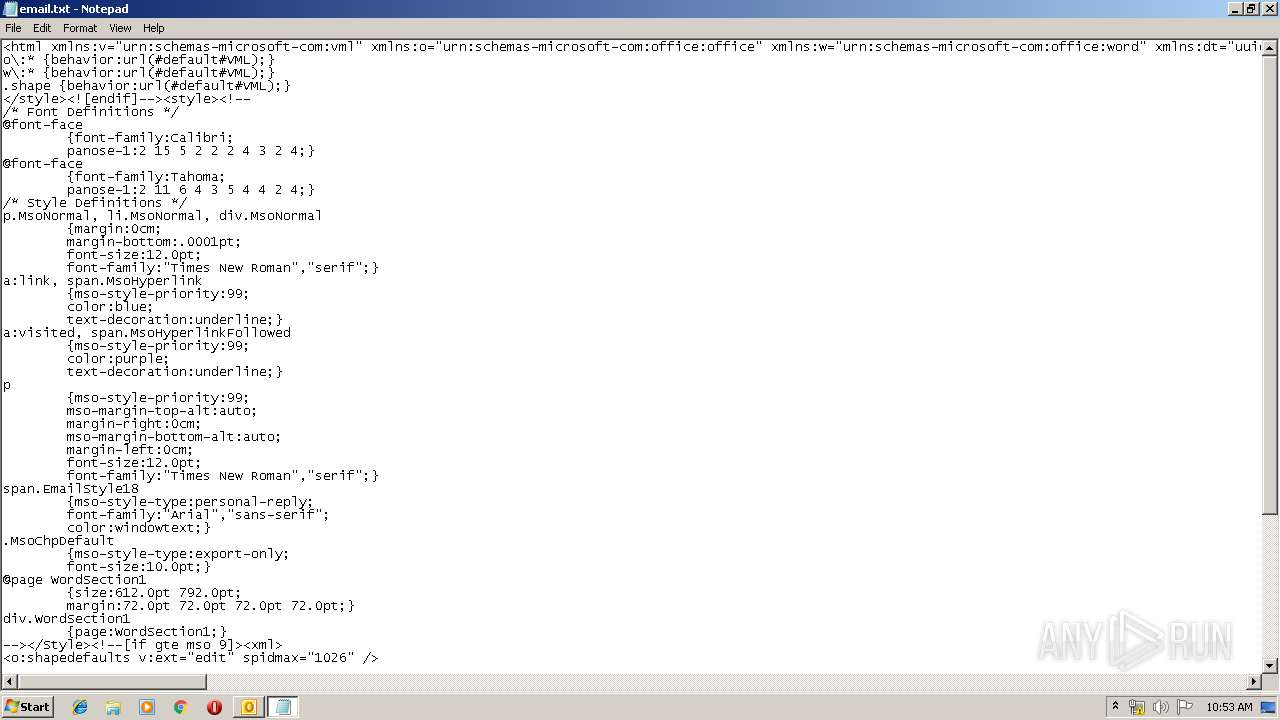
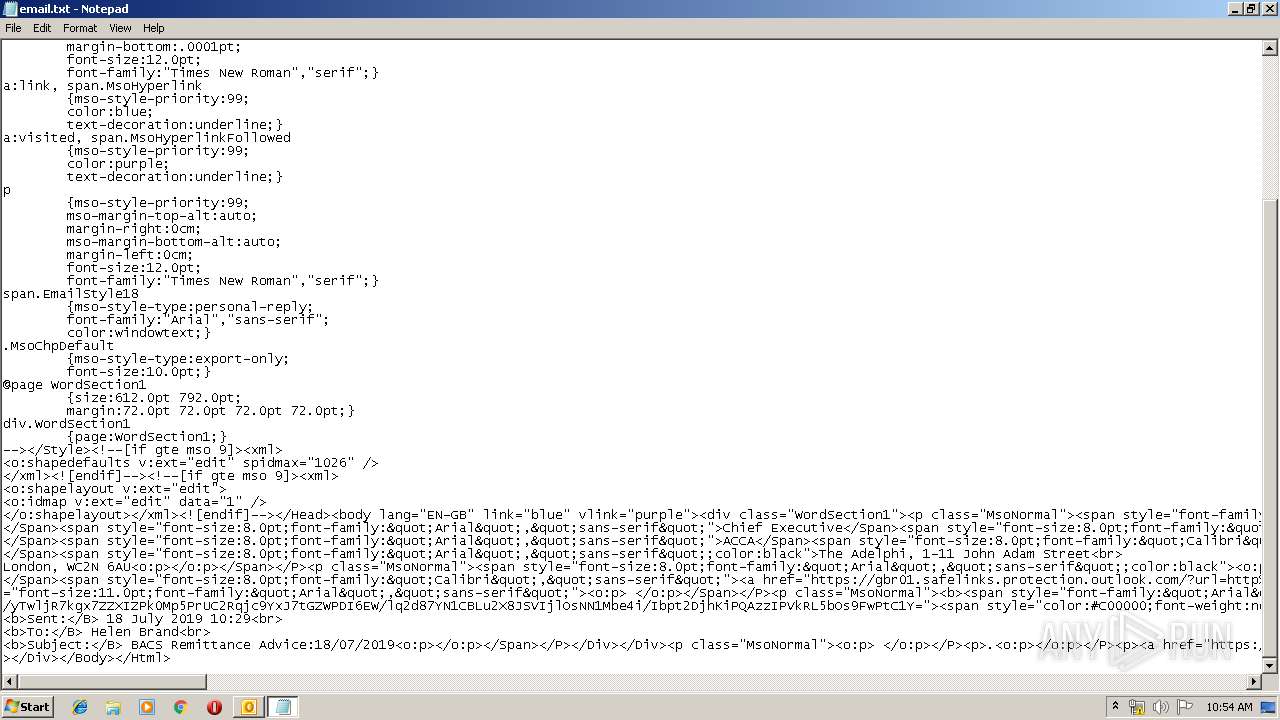
| 2524 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\MD2ZLD6I\email.txt | C:\Windows\system32\NOTEPAD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
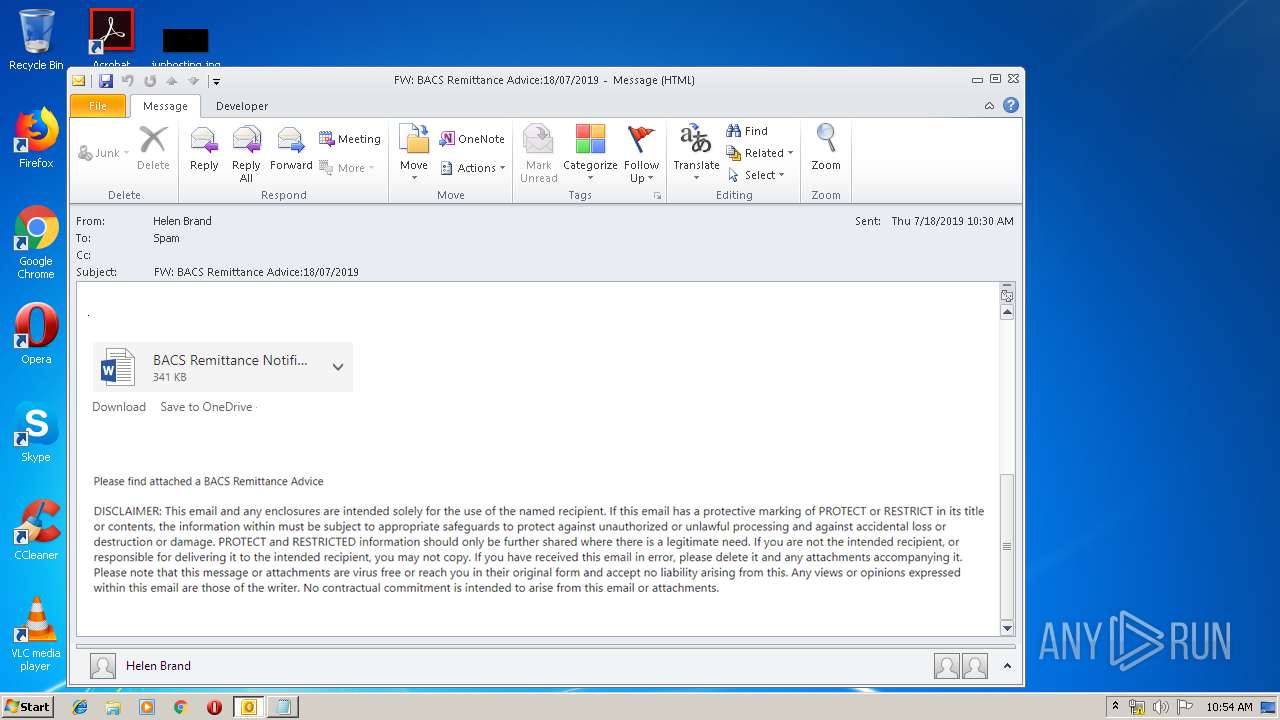
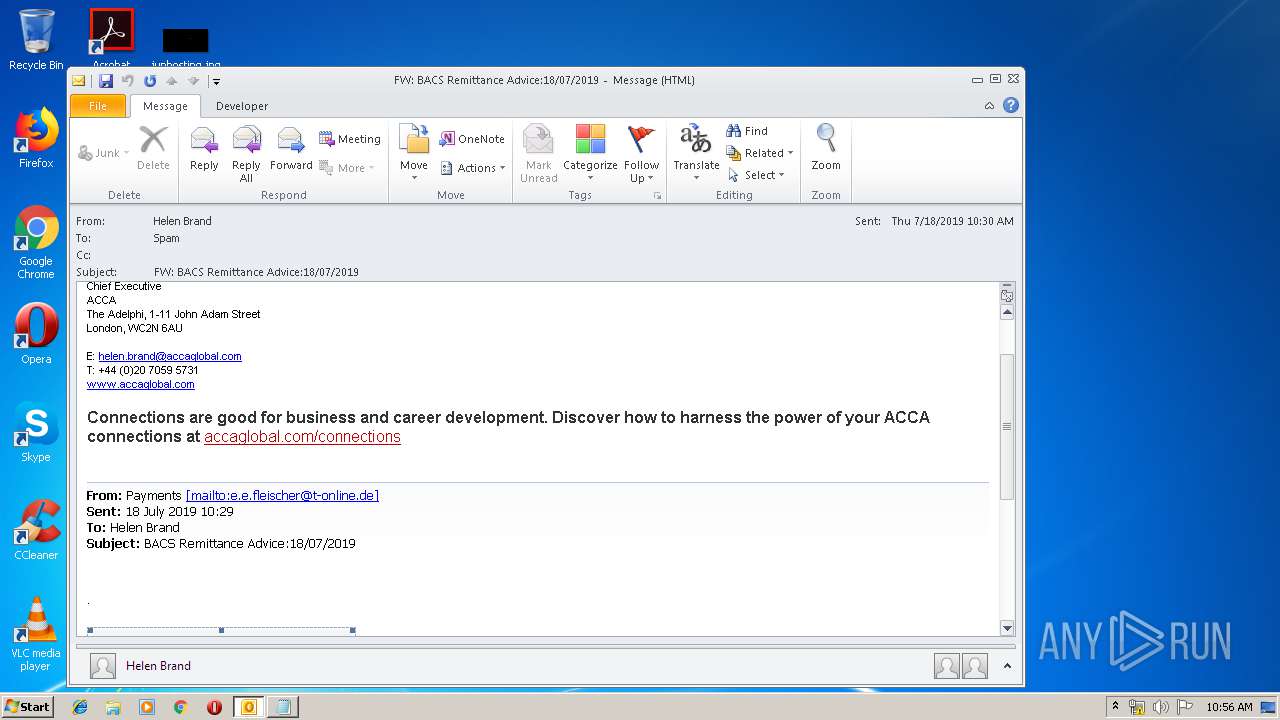
| 2960 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\FW BACS Remittance Advice18072019.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
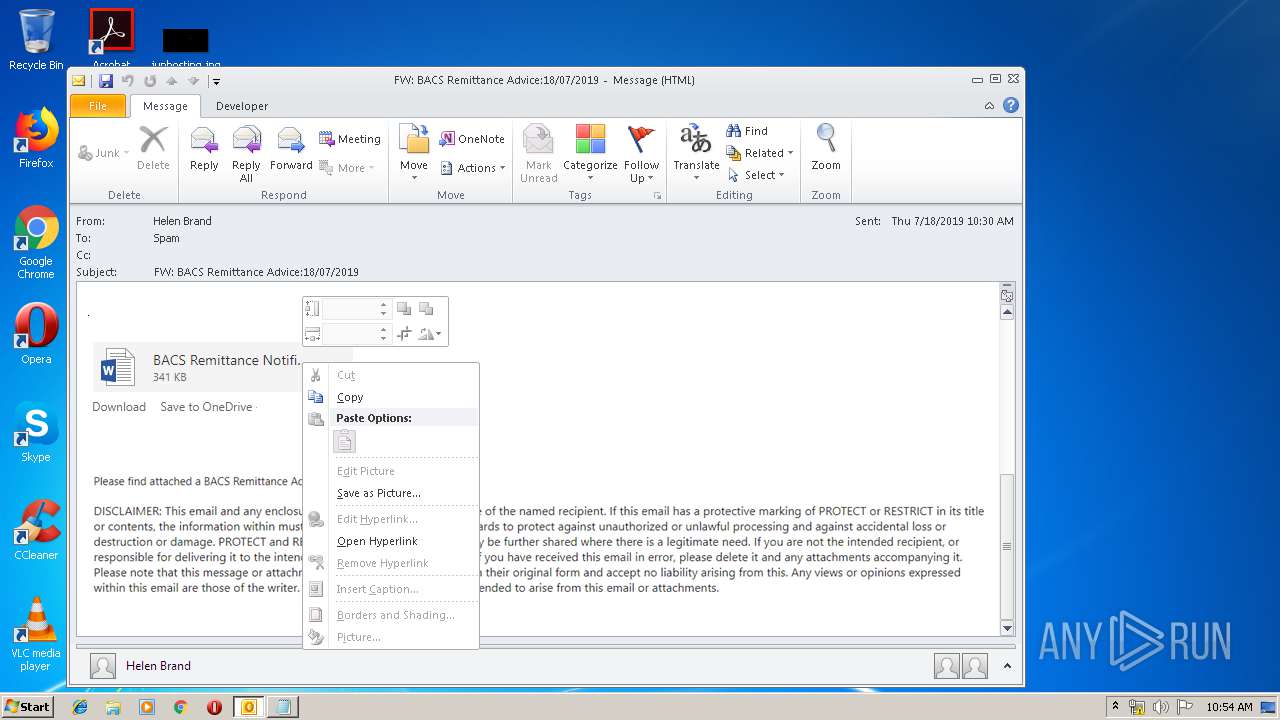
| 3260 | "C:\Program Files\Internet Explorer\iexplore.exe" https://gbr01.safelinks.protection.outlook.com/?url=https%3A%2F%2Frobindalelegal.com.au%2F%2523U0153%2523U00c3&data=02%7C01%7CSpam%40accaglobal.com%7Cf2f5f9e5d0cf4bad413508d70b628643%7Cf2e7de2c59ba49fe8c684cd333f96b01%7C0%7C0%7C636990390092058046&sdata=QnAPhihxkPRuFvk%2Bw3MxRXlK%2FPX7vk9Y24dHGPNPNAM%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3736 | "C:\Program Files\Internet Explorer\iexplore.exe" https://gbr01.safelinks.protection.outlook.com/?url=https%3A%2F%2Frobindalelegal.com.au%2F%2523U0153%2523U00c3&data=02%7C01%7CSpam%40accaglobal.com%7Cf2f5f9e5d0cf4bad413508d70b628643%7Cf2e7de2c59ba49fe8c684cd333f96b01%7C0%7C0%7C636990390092058046&sdata=QnAPhihxkPRuFvk%2Bw3MxRXlK%2FPX7vk9Y24dHGPNPNAM%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3260 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 373
Read events
1 831
Write events
517
Delete events
25
Modification events
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | {|< |
Value: 7B7C3C00900B0000010000000000000000000000 | |||
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 900B00006C788D584E3DD50100000000 | |||
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220131360 | |||
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2960) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1324482581 | |||
Executable files
0
Suspicious files
4
Text files
42
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE8CB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AC8194D6.dat | image | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\ECC7D2DF.dat | image | |
MD5:— | SHA256:— | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UR0OZV7L\gbr01_safelinks_protection_outlook_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 2960 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{8F0412AB-2E9E-4489-87D9-51B8C73D89FD}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:7D80C0A7E3849818695EAF4989186A3C | SHA256:72DC527D78A8E99331409803811CC2D287E812C008A1C869A6AEA69D7A44B597 | |||
| 2960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_8F094EA057A69A4D911F12068749A986.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 3920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
13
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2960 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3260 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3736 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3920 | iexplore.exe | 104.47.21.28:443 | gbr01.safelinks.protection.outlook.com | Microsoft Corporation | GB | unknown |
3736 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3736 | iexplore.exe | 104.47.20.28:443 | gbr01.safelinks.protection.outlook.com | Microsoft Corporation | GB | unknown |
272 | iexplore.exe | 104.47.20.28:443 | gbr01.safelinks.protection.outlook.com | Microsoft Corporation | GB | unknown |
3260 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2960 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3260 | iexplore.exe | 104.47.21.28:443 | gbr01.safelinks.protection.outlook.com | Microsoft Corporation | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
gbr01.safelinks.protection.outlook.com |
| whitelisted |
www.bing.com |
| whitelisted |