| File name: | meeting.exe |
| Full analysis: | https://app.any.run/tasks/20b320a9-25f6-4961-abe5-76f8d9b362c8 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2023, 06:50:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 94AEA5A8C7F08CB7C7A8ED9CC781488E |
| SHA1: | 66172B9C4C4928B40C737C3BBE4AD3A045646B8B |
| SHA256: | EDB76A6159243C4E0694C4273123EB2A399D9F60BDB2A8FD0C660BDB845500CD |
| SSDEEP: | 12288:E4v5plrnRYe/FuIEZ8B3RODp2o0MF/ynn68GUBPNBoEq:VJqe/Y2mQozW68GUBboE |
MALICIOUS
Starts CMD.EXE for self-deleting
- meeting.exe (PID: 3936)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1016)
Actions looks like stealing of personal data
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
SUSPICIOUS
Executable content was dropped or overwritten
- meeting.exe (PID: 3936)
Reads the Internet Settings
- meeting.exe (PID: 3936)
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
Starts application with an unusual extension
- cmd.exe (PID: 1016)
Starts CMD.EXE for commands execution
- meeting.exe (PID: 3936)
The process executes via Task Scheduler
- meeting.exe (PID: 1964)
Reads settings of System Certificates
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
Accesses Microsoft Outlook profiles
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
Checks for external IP
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- meeting.exe (PID: 332)
Process requests binary or script from the Internet
- meeting.exe (PID: 332)
Reads browser cookies
- meeting.exe (PID: 332)
Connects to the server without a host name
- meeting.exe (PID: 332)
Searches for installed software
- meeting.exe (PID: 332)
INFO
Checks supported languages
- meeting.exe (PID: 3936)
- chcp.com (PID: 3784)
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
The process checks LSA protection
- meeting.exe (PID: 3936)
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
Reads the computer name
- meeting.exe (PID: 3936)
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
Reads the machine GUID from the registry
- meeting.exe (PID: 3936)
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
Reads Environment values
- meeting.exe (PID: 3936)
- meeting.exe (PID: 1964)
- meeting.exe (PID: 332)
Creates files or folders in the user directory
- meeting.exe (PID: 3936)
- meeting.exe (PID: 332)
The executable file from the user directory is run by the CMD process
- meeting.exe (PID: 332)
Create files in a temporary directory
- meeting.exe (PID: 332)
- meeting.exe (PID: 1964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.2.0.0 |
|---|---|
| ProductVersion: | 1.1.0.0 |
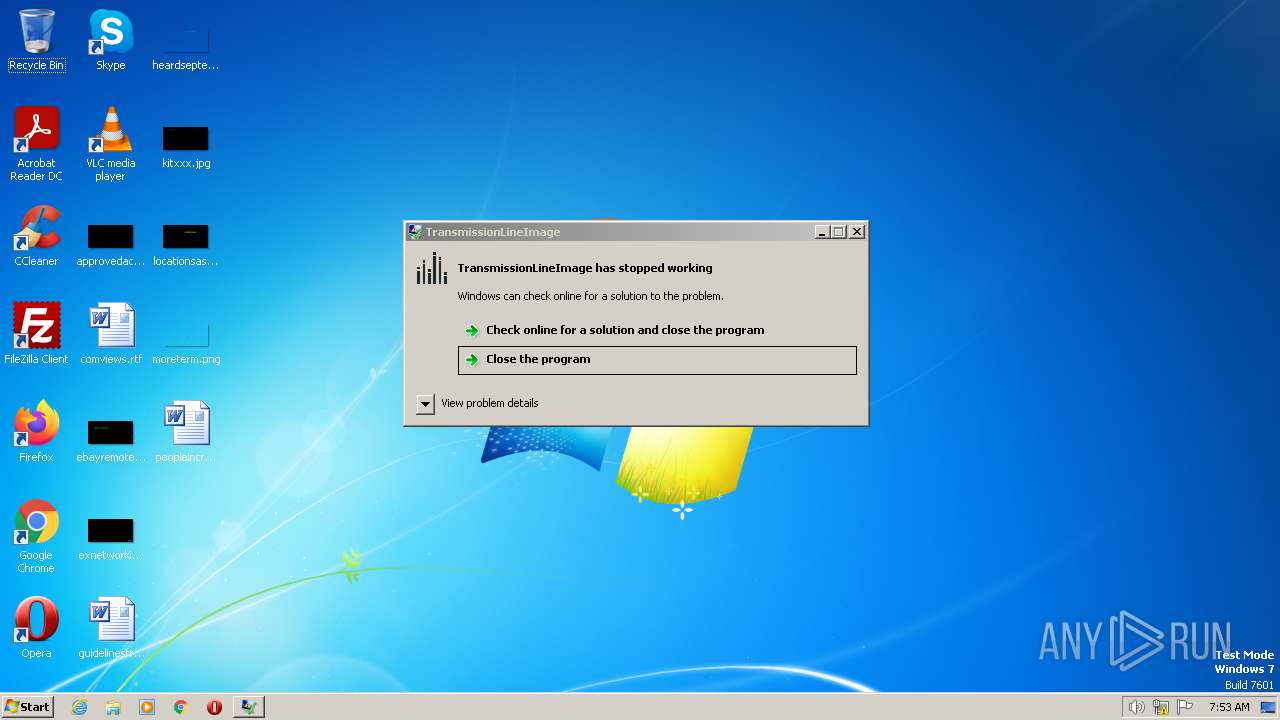
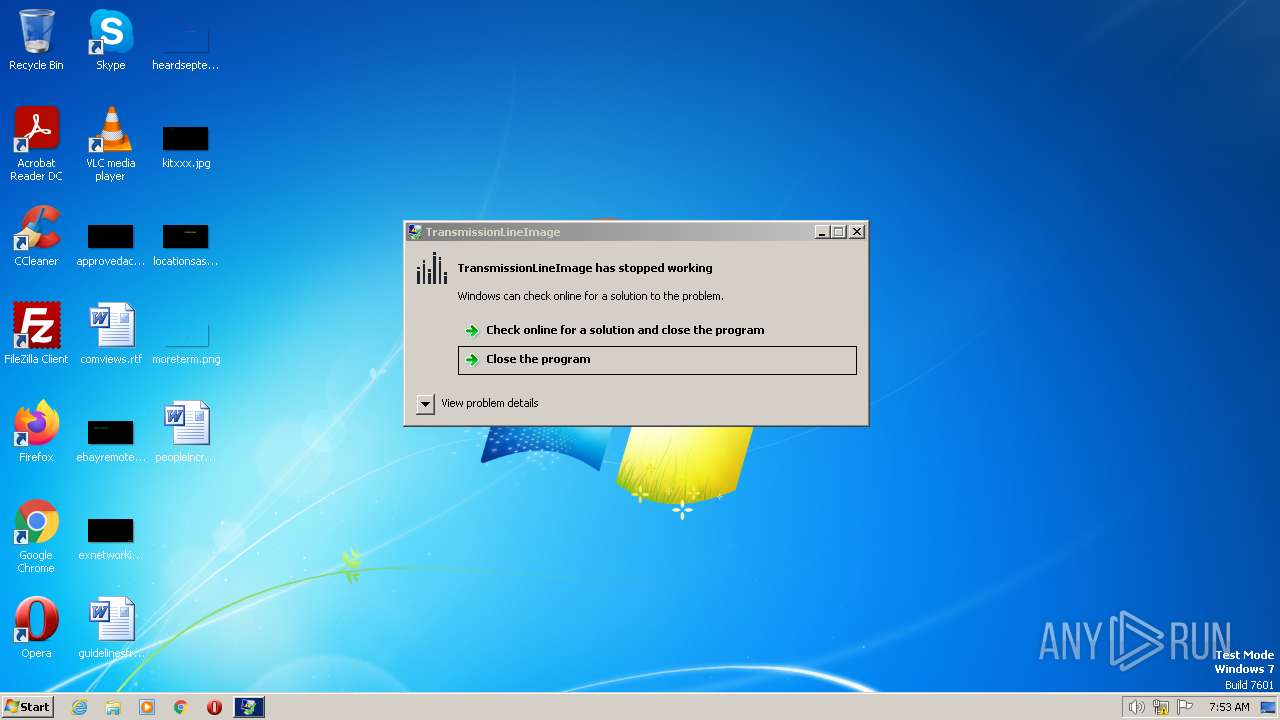
| ProductName: | TransmissionLineImage |
| OriginalFileName: | TtDk.exe |
| LegalTrademarks: | Handyman |
| LegalCopyright: | - |
| InternalName: | TtDk.exe |
| FileVersion: | 1.1.0.0 |
| FileDescription: | TransmissionLineImage |
| CompanyName: | Handyman |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.1.0.0 |
| FileVersionNumber: | 1.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xb52d2 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4096 |
| CodeSize: | 734208 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2023:05:16 01:17:20+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-May-2023 01:17:20 |
| Comments: | - |
| CompanyName: | Handyman |
| FileDescription: | TransmissionLineImage |
| FileVersion: | 1.1.0.0 |
| InternalName: | TtDk.exe |
| LegalCopyright: | - |
| LegalTrademarks: | Handyman |
| OriginalFilename: | TtDk.exe |
| ProductName: | TransmissionLineImage |
| ProductVersion: | 1.1.0.0 |
| Assembly Version: | 1.2.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-May-2023 01:17:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000B32D8 | 0x000B3400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.77391 |
.rsrc | 0x000B6000 | 0x00000D10 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.79674 |
.reloc | 0x000B8000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94168 | 436 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
32512 | 1.51664 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
46
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Users\admin\AppData\Local\Nvidia\meeting.exe" | C:\Users\admin\AppData\Local\Nvidia\meeting.exe | cmd.exe | ||||||||||||
User: admin Company: Handyman Integrity Level: MEDIUM Description: TransmissionLineImage Exit code: 3762504530 Version: 1.1.0.0 Modules
| |||||||||||||||
| 1016 | "C:\Windows\System32\cmd.exe" /C chcp 65001 && ping 127.0.0.1 && schtasks /create /tn "meeting" /sc MINUTE /tr "C:\Users\admin\AppData\Local\Nvidia\meeting.exe" /rl LIMITED /f && DEL /F /S /Q /A "C:\Users\admin\AppData\Local\Temp\meeting.exe" &&START "" "C:\Users\admin\AppData\Local\Nvidia\meeting.exe" | C:\Windows\System32\cmd.exe | — | meeting.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1964 | C:\Users\admin\AppData\Local\Nvidia\meeting.exe | C:\Users\admin\AppData\Local\Nvidia\meeting.exe | taskeng.exe | ||||||||||||
User: admin Company: Handyman Integrity Level: MEDIUM Description: TransmissionLineImage Exit code: 3762504530 Version: 1.1.0.0 Modules
| |||||||||||||||
| 2896 | ping 127.0.0.1 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3784 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3936 | "C:\Users\admin\AppData\Local\Temp\meeting.exe" | C:\Users\admin\AppData\Local\Temp\meeting.exe | explorer.exe | ||||||||||||
User: admin Company: Handyman Integrity Level: MEDIUM Description: TransmissionLineImage Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 4028 | schtasks /create /tn "meeting" /sc MINUTE /tr "C:\Users\admin\AppData\Local\Nvidia\meeting.exe" /rl LIMITED /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 096
Read events
10 060
Write events
36
Delete events
0
Modification events
| (PID) Process: | (3936) meeting.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3936) meeting.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3936) meeting.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3936) meeting.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (332) meeting.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1964) meeting.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
4
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 332 | meeting.exe | C:\Users\admin\AppData\Local\Temp\tmp6F8B.tmp | — | |
MD5:— | SHA256:— | |||
| 1964 | meeting.exe | C:\Users\admin\AppData\Local\Temp\tmpC56B.tmp | — | |
MD5:— | SHA256:— | |||
| 3936 | meeting.exe | C:\Users\admin\AppData\Local\Nvidia\meeting.exe | executable | |
MD5:94AEA5A8C7F08CB7C7A8ED9CC781488E | SHA256:EDB76A6159243C4E0694C4273123EB2A399D9F60BDB2A8FD0C660BDB845500CD | |||
| 332 | meeting.exe | C:\Users\admin\AppData\Local\Temp\Cab744E.tmp | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 332 | meeting.exe | C:\Users\admin\AppData\Local\dc2hvbfa3x\port.dat | text | |
MD5:9A02387B02CE7DE2DAC4B925892F68FB | SHA256:914302698973596F3CC6FC14206D81A13B9D08ADA96B4E22FE9A6209087C42ED | |||
| 332 | meeting.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:3AC860860707BAAF32469FA7CC7C0192 | SHA256:D015145D551ECD14916270EFAD773BBC9FD57FAD2228D2C24559F696C961D904 | |||
| 332 | meeting.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:1155D7058D092D9C2135F040F0E33825 | SHA256:066F4A7D138AC6627E06023F97EA351DA2EF7A85FBCA8ED1C3EFEA8BD0B32126 | |||
| 332 | meeting.exe | C:\Users\admin\AppData\Local\Temp\Tar744F.tmp | cat | |
MD5:4FF65AD929CD9A367680E0E5B1C08166 | SHA256:C8733C93CC5AAF5CA206D06AF22EE8DBDEC764FB5085019A6A9181FEB9DFDEE6 | |||
| 332 | meeting.exe | C:\Users\admin\AppData\Local\dc2hvbfa3x\report.lock | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
94
DNS requests
18
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
332 | meeting.exe | POST | 400 | 142.250.186.110:80 | http://youtube.com/Ep3hnbR6IC?q=0 | US | html | 7.32 Kb | whitelisted |
332 | meeting.exe | POST | 400 | 142.250.186.110:80 | http://youtube.com/wsVZjAbAO0?q=2 | US | html | 7.32 Kb | whitelisted |
332 | meeting.exe | POST | 400 | 142.250.186.110:80 | http://youtube.com/Ep3hnbR6IC?q=0 | US | html | 7.32 Kb | whitelisted |
332 | meeting.exe | POST | 400 | 142.250.186.110:80 | http://youtube.com/Ep3hnbR6IC?q=0 | US | html | 7.32 Kb | whitelisted |
332 | meeting.exe | POST | 400 | 142.250.186.110:80 | http://youtube.com/Ep3hnbR6IC?q=0 | US | html | 7.32 Kb | whitelisted |
332 | meeting.exe | POST | 301 | 104.16.156.132:80 | http://blockchain.com/GjMLkoZqDj?q=1 | US | — | — | suspicious |
332 | meeting.exe | POST | 400 | 142.250.186.110:80 | http://youtube.com/Ep3hnbR6IC?q=0 | US | html | 7.32 Kb | whitelisted |
332 | meeting.exe | POST | 301 | 104.16.156.132:80 | http://blockchain.com/GjMLkoZqDj?q=1 | US | — | — | suspicious |
332 | meeting.exe | POST | 400 | 142.250.186.110:80 | http://youtube.com/Ep3hnbR6IC?q=0 | US | html | 7.32 Kb | whitelisted |
332 | meeting.exe | POST | 301 | 104.16.156.132:80 | http://blockchain.com/GjMLkoZqDj?q=1 | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3416 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
332 | meeting.exe | 142.250.186.110:80 | youtube.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
332 | meeting.exe | 104.16.156.132:80 | blockchain.com | CLOUDFLARENET | — | suspicious |
332 | meeting.exe | 159.69.63.226:443 | archive.torproject.org | Hetzner Online GmbH | DE | suspicious |
332 | meeting.exe | 104.16.157.132:443 | blockchain.com | CLOUDFLARENET | — | unknown |
332 | meeting.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
332 | meeting.exe | 142.250.185.142:80 | google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
archive.torproject.org |
| shared |
youtube.com |
| whitelisted |
blockchain.com |
| suspicious |
www.blockchain.com |
| suspicious |
google.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
pornhub.com |
| whitelisted |
github.com |
| malicious |
telegram.org |
| whitelisted |
ip-api.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
332 | meeting.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
332 | meeting.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1964 | meeting.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1964 | meeting.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1076 | svchost.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to File Transfer Service Domain (transfer .sh) |
1076 | svchost.exe | Misc activity | ET INFO Commonly Abused File Sharing Site Domain Observed (transfer .sh in DNS Lookup) |
332 | meeting.exe | Misc activity | ET INFO Commonly Abused File Sharing Site Domain Observed (transfer .sh in TLS SNI) |
332 | meeting.exe | Potential Corporate Privacy Violation | ET POLICY Observed File Transfer Service SSL/TLS Certificate (transfer .sh) |
1076 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
332 | meeting.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |