| URL: | http://alainghazal.com/Februar2019/PYORQFTPOS2153499/Rechnung/RECHNUNG |
| Full analysis: | https://app.any.run/tasks/6ecd787b-7b3d-4b38-a5a3-d4b59a00c05c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 18, 2019, 10:27:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 455F15700D88A73F8D53815E476A883D |
| SHA1: | 518C9AEC8DA86CC6A55FDE7B938C663C26C74D19 |
| SHA256: | EDB45EEB612E09EBD79D50BD9F02A2C2A43128EF40BE502ACFC469CD88EBEEBA |
| SSDEEP: | 3:N1KfHEJLKNHh+xz0FNcsA1L9:CvEJ2NHhdFt+ |
MALICIOUS
Application was dropped or rewritten from another process
- 540.exe (PID: 2900)
- 540.exe (PID: 3968)
- wabmetagen.exe (PID: 3972)
- wabmetagen.exe (PID: 2700)
Downloads executable files from the Internet
- poWersheLl.exe (PID: 3596)
Emotet process was detected
- wabmetagen.exe (PID: 3972)
EMOTET was detected
- wabmetagen.exe (PID: 2700)
Connects to CnC server
- wabmetagen.exe (PID: 2700)
SUSPICIOUS
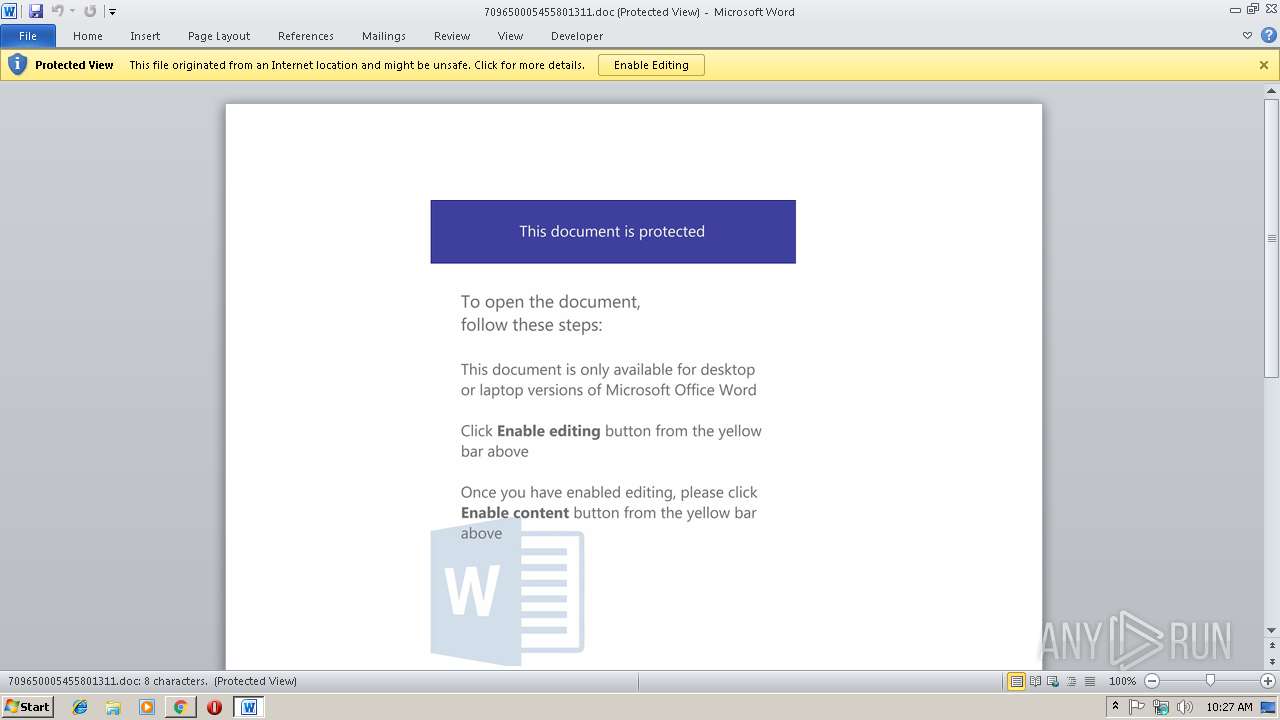
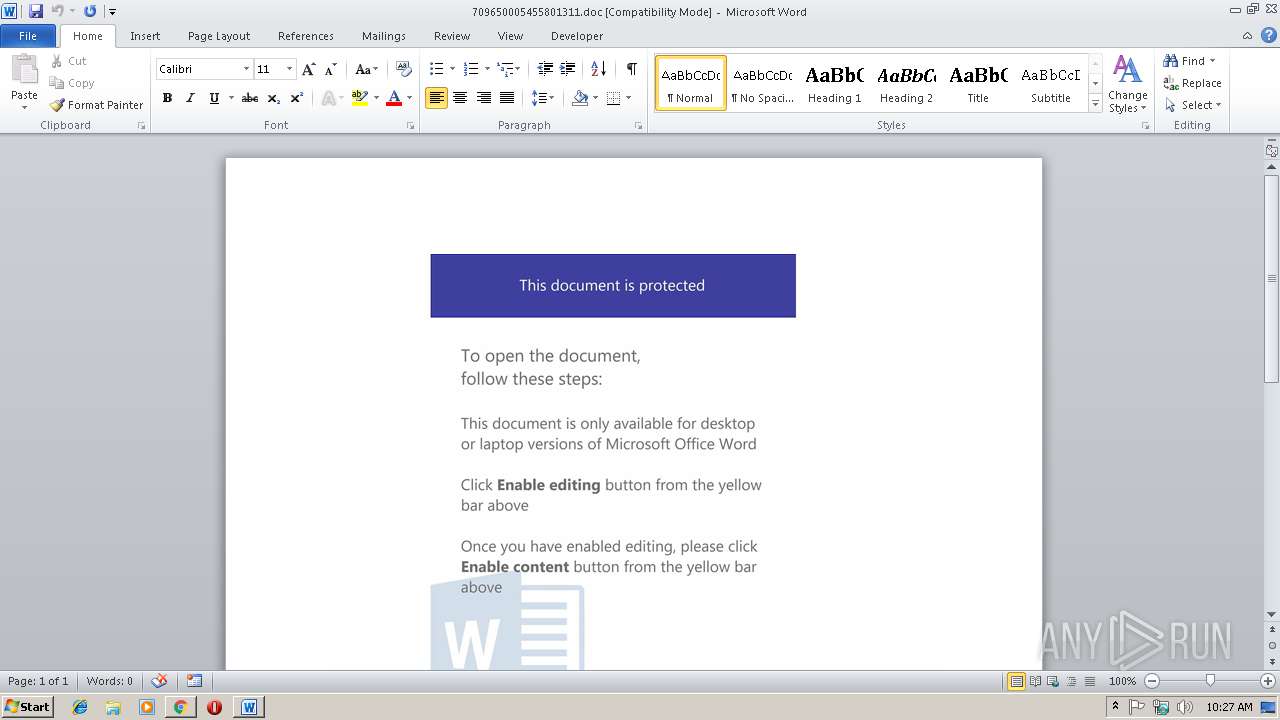
Application launched itself
- WINWORD.EXE (PID: 2352)
- wabmetagen.exe (PID: 3972)
Starts Microsoft Office Application
- chrome.exe (PID: 2964)
- WINWORD.EXE (PID: 2352)
Executable content was dropped or overwritten
- poWersheLl.exe (PID: 3596)
- 540.exe (PID: 3968)
Starts itself from another location
- 540.exe (PID: 3968)
Creates files in the user directory
- poWersheLl.exe (PID: 3596)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2964)
Reads Internet Cache Settings
- chrome.exe (PID: 2964)
Application launched itself
- chrome.exe (PID: 2964)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3532)
- WINWORD.EXE (PID: 2352)
Creates files in the user directory
- WINWORD.EXE (PID: 2352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
16
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=DA9F658DA4E17AD399641F2D624BA198 --mojo-platform-channel-handle=3944 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
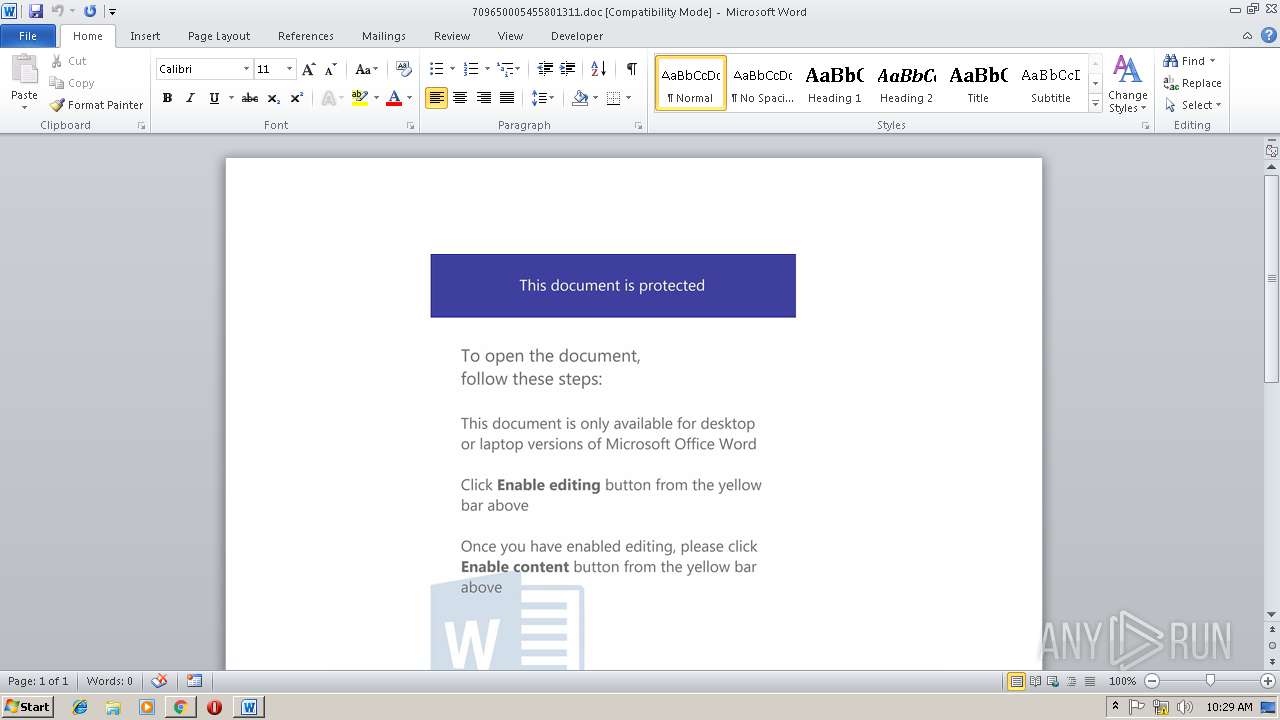
| 2352 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\709650005455801311.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=9FA4BEFECCF0649080EA9ECA35DF4D97 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9FA4BEFECCF0649080EA9ECA35DF4D97 --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS(r) DLL for Win32 Exit code: 0 Version: 13.0.0.047 Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\540.exe" | C:\Users\admin\540.exe | — | poWersheLl.exe | |||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS(r) DLL for Win32 Exit code: 0 Version: 13.0.0.047 Modules
| |||||||||||||||
| 2904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2968 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://alainghazal.com/Februar2019/PYORQFTPOS2153499/Rechnung/RECHNUNG | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=769FDDA9698DFE0AEF783368186449CB --mojo-platform-channel-handle=2308 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=9762D8DE2D11AB440BDA7049356F36C0 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9762D8DE2D11AB440BDA7049356F36C0 --renderer-client-id=3 --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=BC197797AAF2E4621706D37E78DFF847 --mojo-platform-channel-handle=1180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 179
Read events
2 698
Write events
467
Delete events
14
Modification events
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2964-13194959248213250 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2964-13194959248213250 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
17
Text files
61
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6b01bbe3-bb4f-42c5-b8c7-1875e44c0003.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ead74096-53ba-40ec-8ee5-a21531de873a.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\178e902d-ccd9-473d-a858-18afc0e249ce.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF199919.TMP | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\Downloads\709650005455801311.doc.crdownload | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF199958.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
12
DNS requests
8
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2700 | wabmetagen.exe | GET | — | 63.227.80.10:8080 | http://63.227.80.10:8080/ | US | — | — | malicious |
2964 | chrome.exe | GET | 301 | 46.182.5.20:80 | http://alainghazal.com/Februar2019/PYORQFTPOS2153499/Rechnung/RECHNUNG | FR | html | 269 b | malicious |
2964 | chrome.exe | GET | 200 | 46.182.5.20:80 | http://alainghazal.com/Februar2019/PYORQFTPOS2153499/Rechnung/RECHNUNG/ | FR | document | 311 Kb | malicious |
3596 | poWersheLl.exe | GET | 301 | 185.182.56.155:80 | http://masjidsolar.nl/xMPn6P4SWc_Nor4jjjBg | NL | html | 251 b | malicious |
2700 | wabmetagen.exe | GET | — | 70.184.86.103:8080 | http://70.184.86.103:8080/ | US | — | — | malicious |
3596 | poWersheLl.exe | GET | 200 | 185.182.56.155:80 | http://masjidsolar.nl/xMPn6P4SWc_Nor4jjjBg/ | NL | executable | 152 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | chrome.exe | 172.217.19.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3596 | poWersheLl.exe | 185.182.56.155:80 | masjidsolar.nl | Astralus B.V. | NL | malicious |
2700 | wabmetagen.exe | 70.184.86.103:8080 | — | Cox Communications Inc. | US | malicious |
2700 | wabmetagen.exe | 63.227.80.10:8080 | — | Qwest Communications Company, LLC | US | malicious |
2964 | chrome.exe | 46.182.5.20:80 | alainghazal.com | AlpineDC SA | FR | malicious |
2964 | chrome.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2964 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
alainghazal.com |
| malicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
masjidsolar.nl |
| malicious |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2964 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3596 | poWersheLl.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3596 | poWersheLl.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3596 | poWersheLl.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2700 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report