| File name: | LockerGoga ransomware |
| Full analysis: | https://app.any.run/tasks/43ae54ec-da9c-4d7f-9928-af9b66b086eb |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 01:26:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 16BCC3B7F32C41E7C7222BF37FE39FE6 |
| SHA1: | A25BC5442C86BDEB0DEC6583F0E80E241745FB73 |
| SHA256: | EDA26A1CD80AAC1C42CDBBA9AF813D9C4BC81F6052080BC33435D1E076E75AA0 |
| SSDEEP: | 24576:uj/6CtkHRos9l+zan4Q6eQqF5ZgQibE2zkMiJHic9OuTw258tox6T9G0SKoRl:A/NtkHRos9l+zan4QTB/2zkPtBq2itoP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- yxugwjud2378.exe (PID: 868)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:02 20:41:12+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 935936 |
| InitializedDataSize: | 322560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9a42c |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.2.0 |
| ProductVersionNumber: | 1.3.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
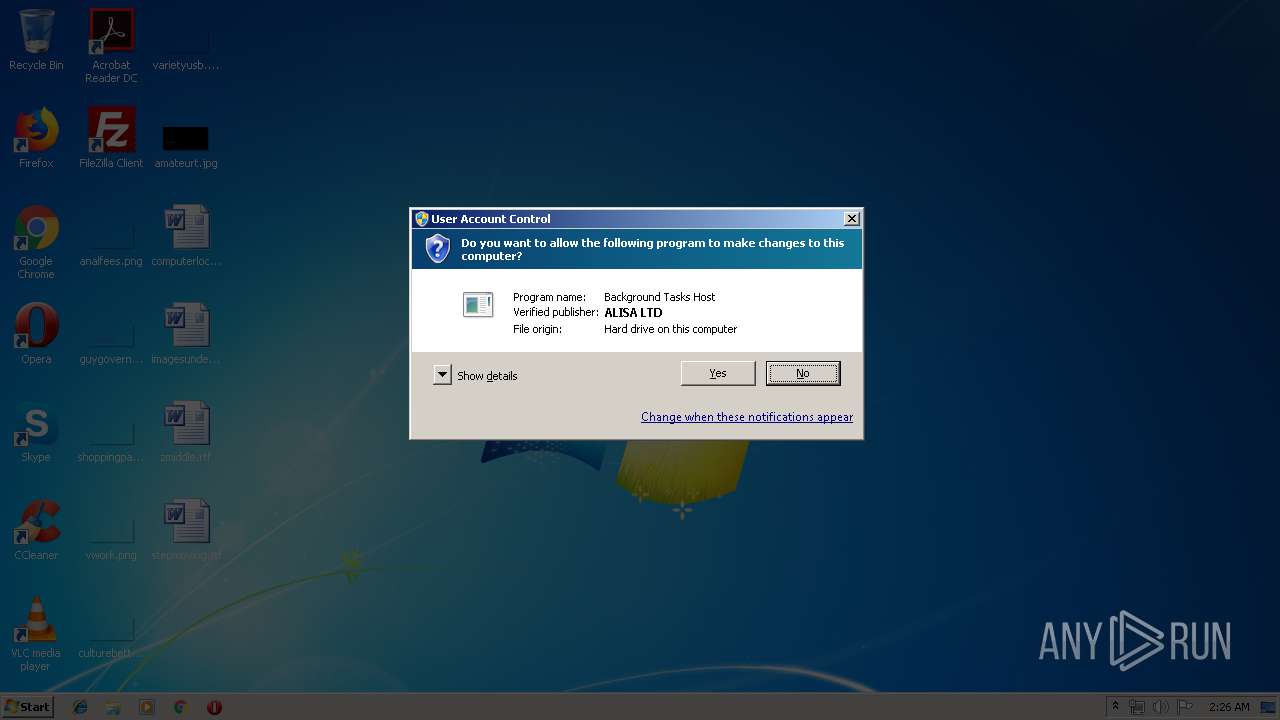
| CompanyName: | ALISA LTD |
| FileDescription: | Background Tasks Host |
| FileVersion: | 1.3.2.0 |
| InternalName: | yxugwjud |
| LegalCopyright: | Copyright (C) ALISA LTD 2019 |
| OriginalFileName: | yxugwjud |
| ProductName: | Service yxugwjud |
| ProductVersion: | 1.3.2.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Mar-2019 19:41:12 |
| Detected languages: |
|
| CompanyName: | ALISA LTD |
| FileDescription: | Background Tasks Host |
| FileVersion: | 1.3.2.0 |
| InternalName: | yxugwjud |
| LegalCopyright: | Copyright (C) ALISA LTD 2019 |
| OriginalFilename: | yxugwjud |
| ProductName: | Service yxugwjud |
| ProductVersion: | 1.3.2.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Mar-2019 19:41:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000E47A2 | 0x000E4800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66182 |
.rdata | 0x000E6000 | 0x000346F8 | 0x00034800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.005 |
.data | 0x0011B000 | 0x0000B9D8 | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98592 |
.rsrc | 0x00127000 | 0x00000508 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.73664 |
.reloc | 0x00128000 | 0x0000E2B8 | 0x0000E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55369 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
WS2_32.dll |
ole32.dll |
Total processes
76
Monitored processes
38
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -i Global\SM-yxugwjud -s | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | yxugwjud2378.exe | ||||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 644 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -i Global\SM-yxugwjud -s | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | yxugwjud2378.exe | ||||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 712 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -i Global\SM-yxugwjud -s | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | yxugwjud2378.exe | ||||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 836 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -i Global\SM-yxugwjud -s | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | yxugwjud2378.exe | ||||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 856 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -i Global\SM-yxugwjud -s | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | yxugwjud2378.exe | ||||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 868 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -m | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | — | LockerGoga ransomware.exe | |||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 908 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -i Global\SM-yxugwjud -s | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | yxugwjud2378.exe | ||||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 980 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -i Global\SM-yxugwjud -s | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | yxugwjud2378.exe | ||||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 1012 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -i Global\SM-yxugwjud -s | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | yxugwjud2378.exe | ||||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
| 1352 | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe -i Global\SM-yxugwjud -s | C:\Users\admin\AppData\Local\Temp\yxugwjud2378.exe | yxugwjud2378.exe | ||||||||||||
User: admin Company: ALISA LTD Integrity Level: HIGH Description: Background Tasks Host Exit code: 0 Version: 1.3.2.0 Modules
| |||||||||||||||
Total events
3 051
Read events
136
Write events
1 610
Delete events
1 305
Modification events
| (PID) Process: | (2168) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: 78080000A521BC0F3E26D501 | |||
| (PID) Process: | (2168) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: 9F2B7D682BB03D452AF54D15170B06897B14416FE5A01FBB860607EA1119107C | |||
| (PID) Process: | (2168) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2168) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\SIWW2.cab | |||
| (PID) Process: | (2168) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFilesHash |
Value: 3F9F6AEE77E8248C2DC67448D78D1CBE411D379B04B3CC27645495BE972BBC09 | |||
| (PID) Process: | (3612) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 1C0E000059E6C00F3E26D501 | |||
| (PID) Process: | (3612) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: B58DA76ABB1BFA5F779DDEFBFF7D9E58498CE49F45478C673FD95050C5D849D8 | |||
| (PID) Process: | (3612) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3612) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\PptLR.cab | |||
| (PID) Process: | (3612) yxugwjud2378.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: DA75D73794C93184C4C03DBB9E7FE7400A4E0AAC0373D54CD2DFC4AB2F39CD4F | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\SIWW.cab |
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\PptLR.cab |
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-001B-0409-0000-0000000FF1CE}-C\WordLR.cab |
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\SIWW2.cab |
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-0117-0409-0000-0000000FF1CE}-C\Access.en-us\AccLR.cab |
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\SingleImageWW.msi |
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-003D-0000-0000-0000000FF1CE}-C\OWOW64WW.cab |
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-002C-0409-0000-0000000FF1CE}-C\Proof.fr\Proof.cab |
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-00A1-0409-0000-0000000FF1CE}-C\OnoteLR.cab |
yxugwjud2378.exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\ExcelLR.cab |