| File name: | mipony pro 3.0.6_365225.exe |
| Full analysis: | https://app.any.run/tasks/4d3e3441-2f28-4ac2-b065-c8b245ce6b08 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2020, 11:46:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 4727856145B7F2B9C4DA44CDAD95DD0B |
| SHA1: | 9943F28EE3B8DC8D5A87279B41191DECCCD9A5F8 |
| SHA256: | ED876095280EA0F26C95B545E241091DA5D1F6DC4B4F3825D607FB6475290A31 |
| SSDEEP: | 98304:y4H32qvSA/Rz1+4pf5/S2a07PjJZBdNiF013mBdWDKO9kz8u:b1vH/X+ESw1LdQF4QnhJ |
MALICIOUS
Connects to CnC server
- mipony pro 3.0.6_365225.exe (PID: 3336)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:28 15:40:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 3760128 |
| InitializedDataSize: | 204800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x60e177 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.1.26 |
| ProductVersionNumber: | 2.7.1.26 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | German |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Buldagon Solf |
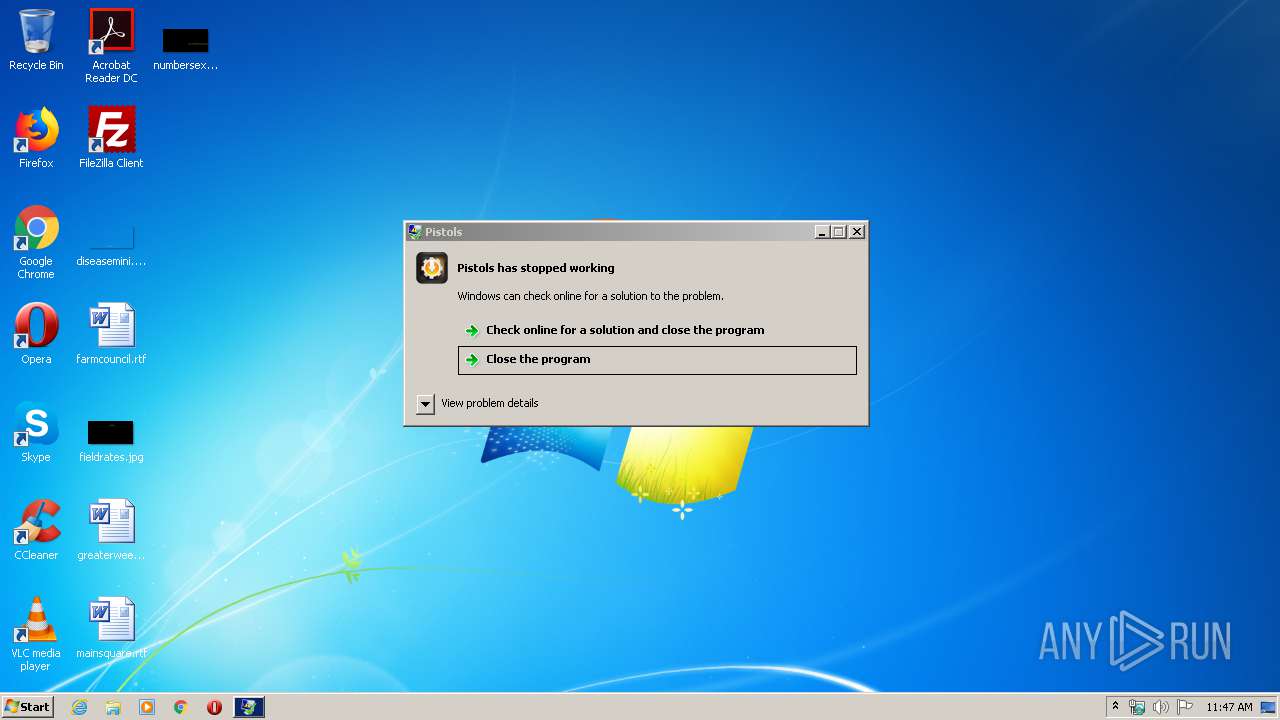
| FileDescription: | Pistols |
| FileVersion: | 2.7.1.26 |
| ProductName: | Pistols |
| ProductVersion: | 2.7.1.26 |
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1800 | "C:\Users\admin\AppData\Local\Temp\mipony pro 3.0.6_365225.exe" | C:\Users\admin\AppData\Local\Temp\mipony pro 3.0.6_365225.exe | — | explorer.exe | |||||||||||
User: admin Company: Buldagon Solf Integrity Level: MEDIUM Description: Pistols Exit code: 3221226540 Version: 2.7.1.26 Modules
| |||||||||||||||
| 3336 | "C:\Users\admin\AppData\Local\Temp\mipony pro 3.0.6_365225.exe" | C:\Users\admin\AppData\Local\Temp\mipony pro 3.0.6_365225.exe | explorer.exe | ||||||||||||
User: admin Company: Buldagon Solf Integrity Level: HIGH Description: Pistols Exit code: 0 Version: 2.7.1.26 Modules
| |||||||||||||||
Total events
18
Read events
18
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3336 | mipony pro 3.0.6_365225.exe | POST | 200 | 104.18.45.18:80 | http://giliafundation.life/v2/events | US | html | 6.53 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3336 | mipony pro 3.0.6_365225.exe | 104.18.45.18:80 | giliafundation.life | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
giliafundation.life |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
3336 | mipony pro 3.0.6_365225.exe | A Network Trojan was detected | ET MALWARE Win32/DownloadAssistant.Q Variant Checkin |
3336 | mipony pro 3.0.6_365225.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |