| URL: | https://ftp.vector.co.jp/46/52/1879/chorokuf128a.exe |
| Full analysis: | https://app.any.run/tasks/630bc6ea-3eb6-4f41-8691-39c8f4c0d327 |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2021, 06:12:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5AFF8B1439D3B7CBF1FE83ADE7CC70A6 |
| SHA1: | 2631F1A27A5262442C10F3BCF21232D7104618CD |
| SHA256: | ED58B7B7D084C3466DB8EDD12063471E7AAF8D09B3131DF403B99217F0457D73 |
| SSDEEP: | 3:N8pLMGsGQtK6E1YX6zL4A:2pLMhGejX4LN |
MALICIOUS
Application was dropped or rewritten from another process
- chorokuf128a.exe (PID: 3568)
- chorokuf128a.exe (PID: 2096)
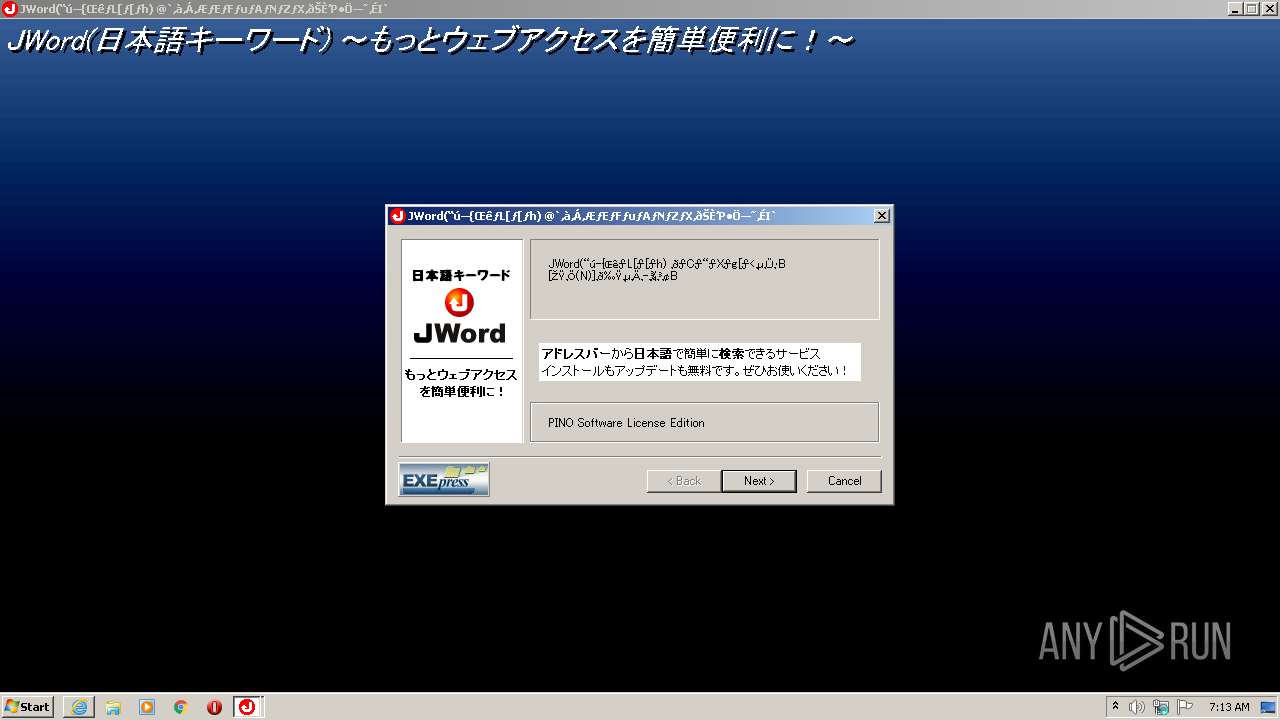
- jword_plugin.exe (PID: 1944)
- jword_plugin.exe (PID: 2340)
Loads dropped or rewritten executable
- CnsMinSetup_pino.exe (PID: 2268)
- NOTEPAD.EXE (PID: 1780)
- Rundll32.exe (PID: 2524)
- explorer.exe (PID: 376)
- jword_plugin.exe (PID: 1944)
- NOTEPAD.EXE (PID: 3004)
- EXECUTER.exe (PID: 2724)
- EXECUTER.exe (PID: 3728)
- CHoRoKuF.exe (PID: 3772)
Changes the autorun value in the registry
- CnsMinSetup_pino.exe (PID: 2268)
SUSPICIOUS
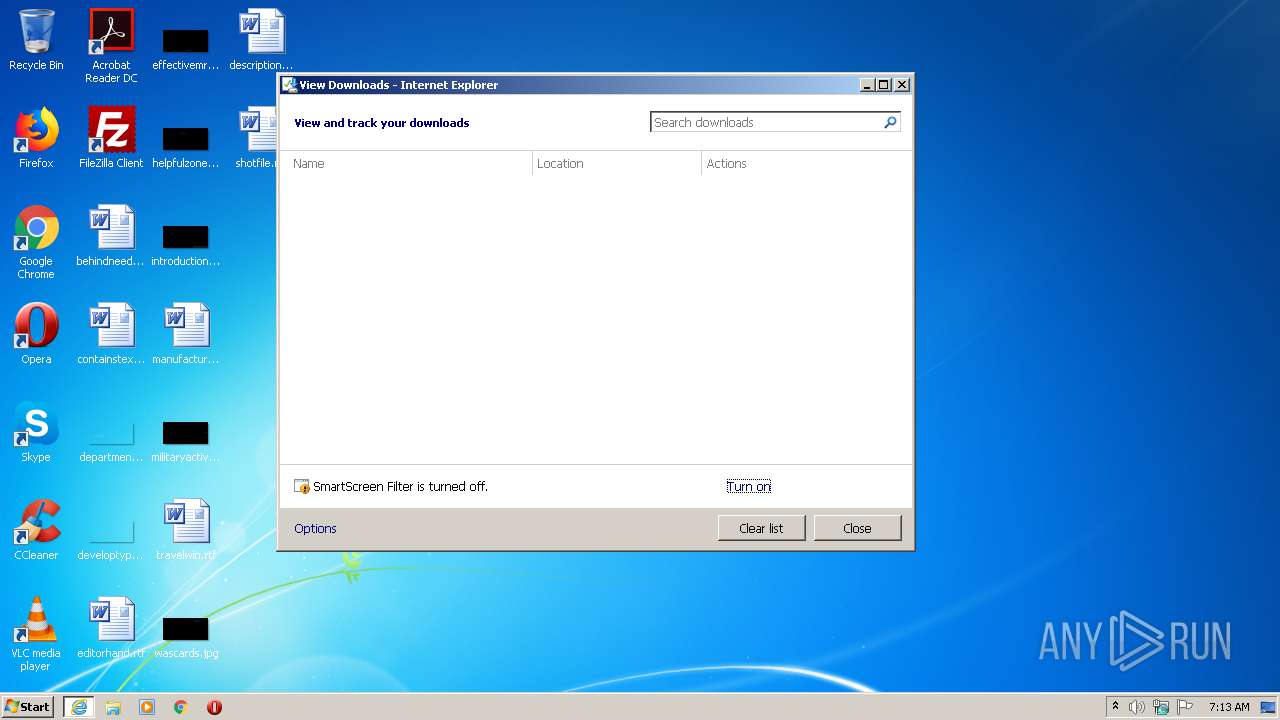
Starts Internet Explorer
- explorer.exe (PID: 376)
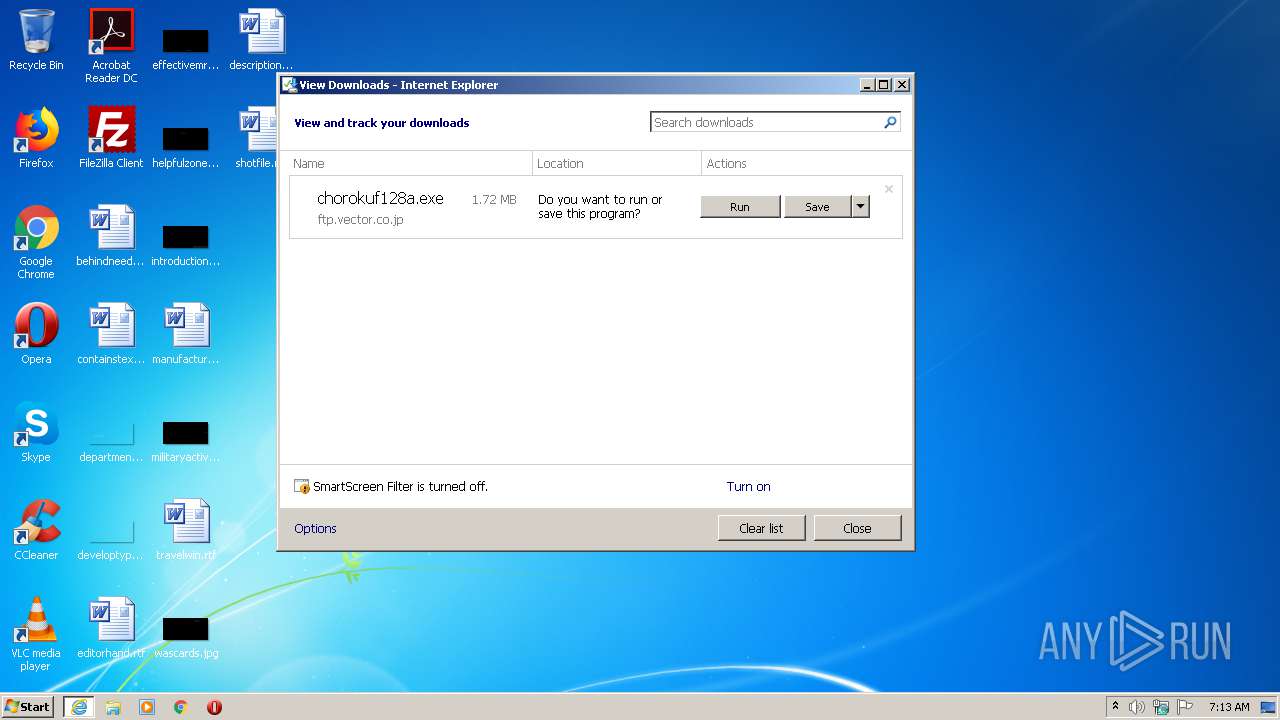
Executable content was dropped or overwritten
- iexplore.exe (PID: 820)
- chorokuf128a.exe (PID: 2096)
- CnsMinSetup_pino.exe (PID: 2268)
Drops a file with too old compile date
- iexplore.exe (PID: 820)
- chorokuf128a.exe (PID: 2096)
- CnsMinSetup_pino.exe (PID: 2268)
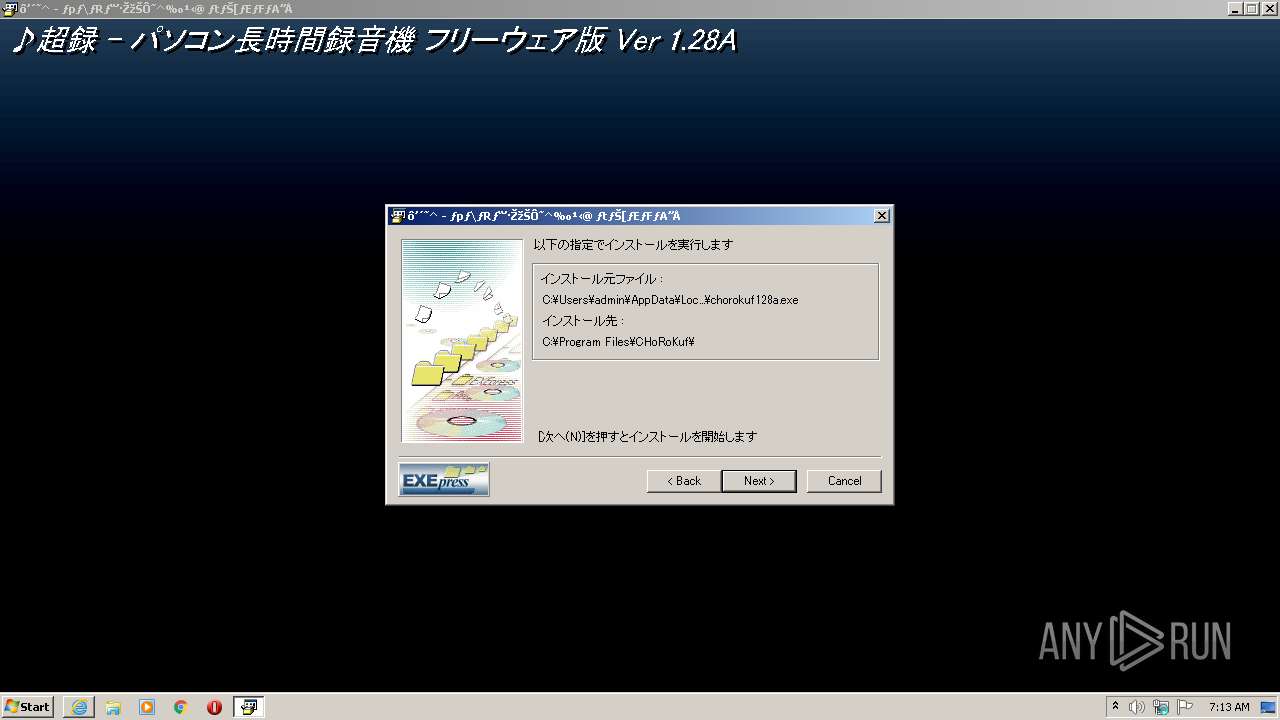
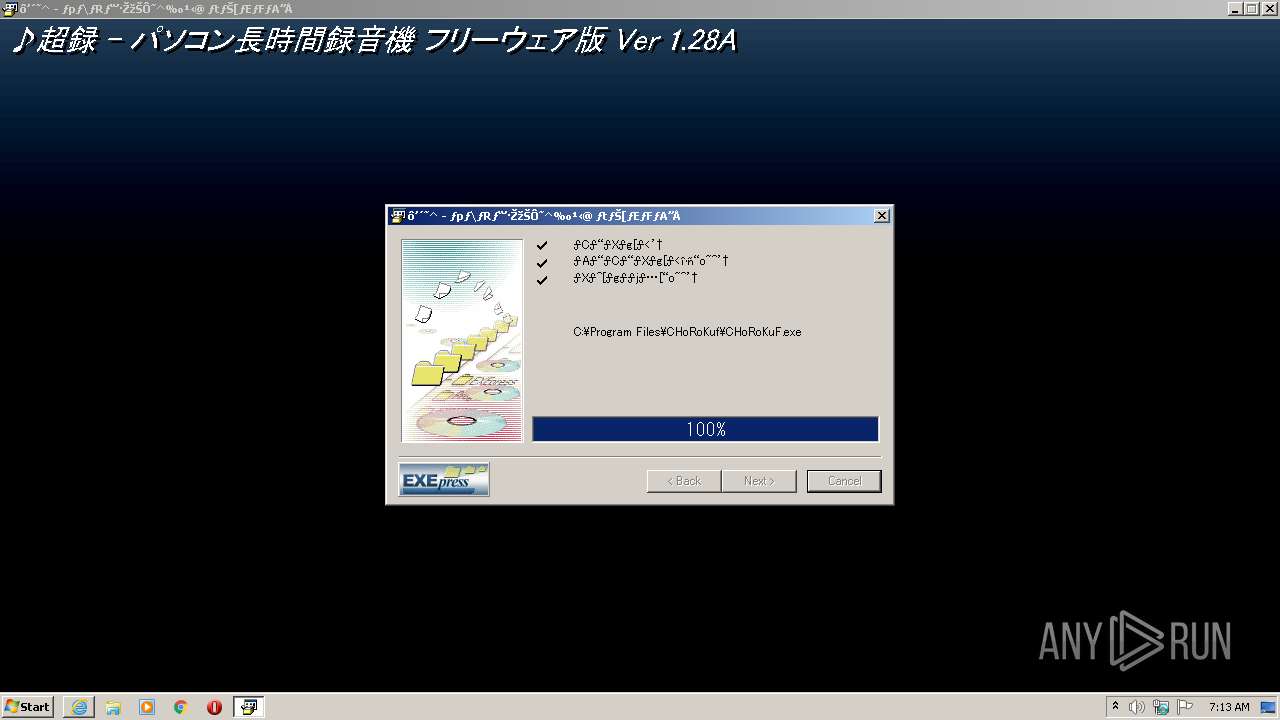
Creates a directory in Program Files
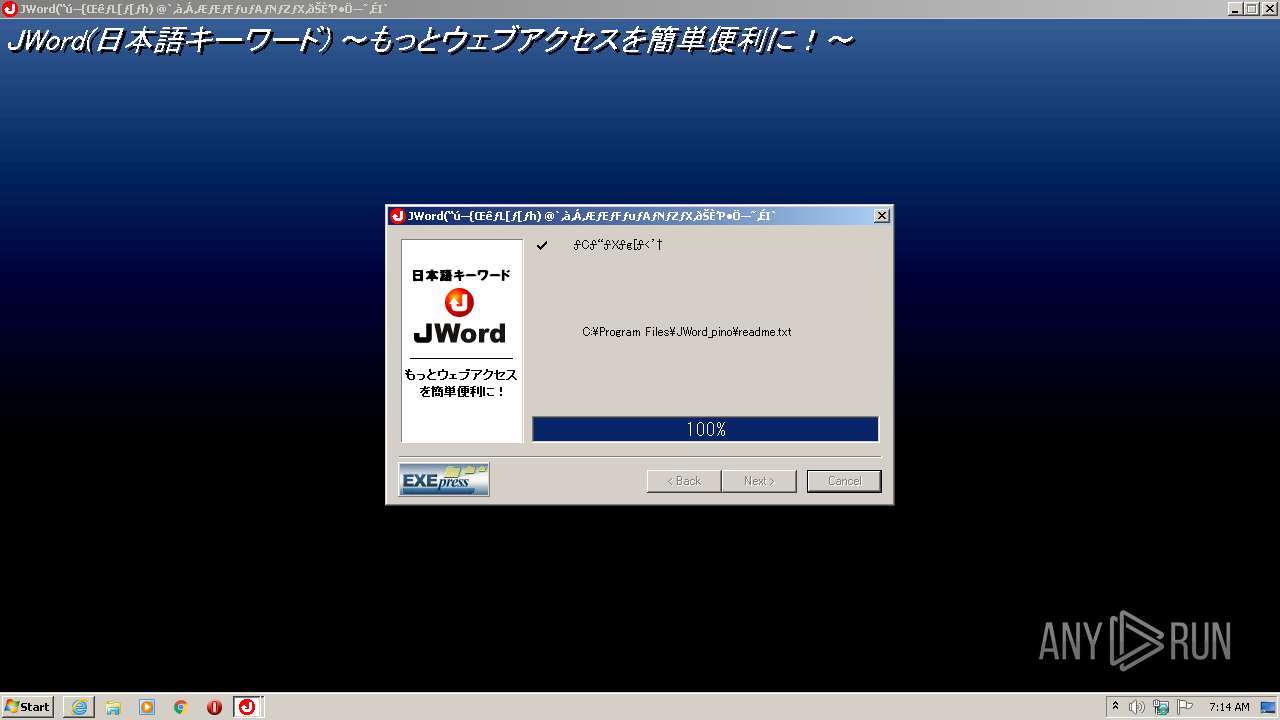
- chorokuf128a.exe (PID: 2096)
- jword_plugin.exe (PID: 2340)
Creates files in the program directory
- chorokuf128a.exe (PID: 2096)
- jword_plugin.exe (PID: 2340)
- CnsMinSetup_pino.exe (PID: 2268)
Creates a software uninstall entry
- chorokuf128a.exe (PID: 2096)
- CnsMinSetup_pino.exe (PID: 2268)
Uses RUNDLL32.EXE to load library
- CnsMinSetup_pino.exe (PID: 2268)
Creates files in the Windows directory
- CnsMinSetup_pino.exe (PID: 2268)
- jword_plugin.exe (PID: 1944)
- EXECUTER.exe (PID: 2724)
- NOTEPAD.EXE (PID: 3004)
- CHoRoKuF.exe (PID: 3772)
- EXECUTER.exe (PID: 3728)
Creates/Modifies COM task schedule object
- CnsMinSetup_pino.exe (PID: 2268)
Removes files from Windows directory
- EXECUTER.exe (PID: 2724)
- jword_plugin.exe (PID: 1944)
- NOTEPAD.EXE (PID: 3004)
- EXECUTER.exe (PID: 3728)
- CHoRoKuF.exe (PID: 3772)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 2184)
Changes internet zones settings
- iexplore.exe (PID: 820)
Application launched itself
- iexplore.exe (PID: 820)
Modifies the phishing filter of IE
- iexplore.exe (PID: 820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
15
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 820 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ftp.vector.co.jp/46/52/1879/chorokuf128a.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
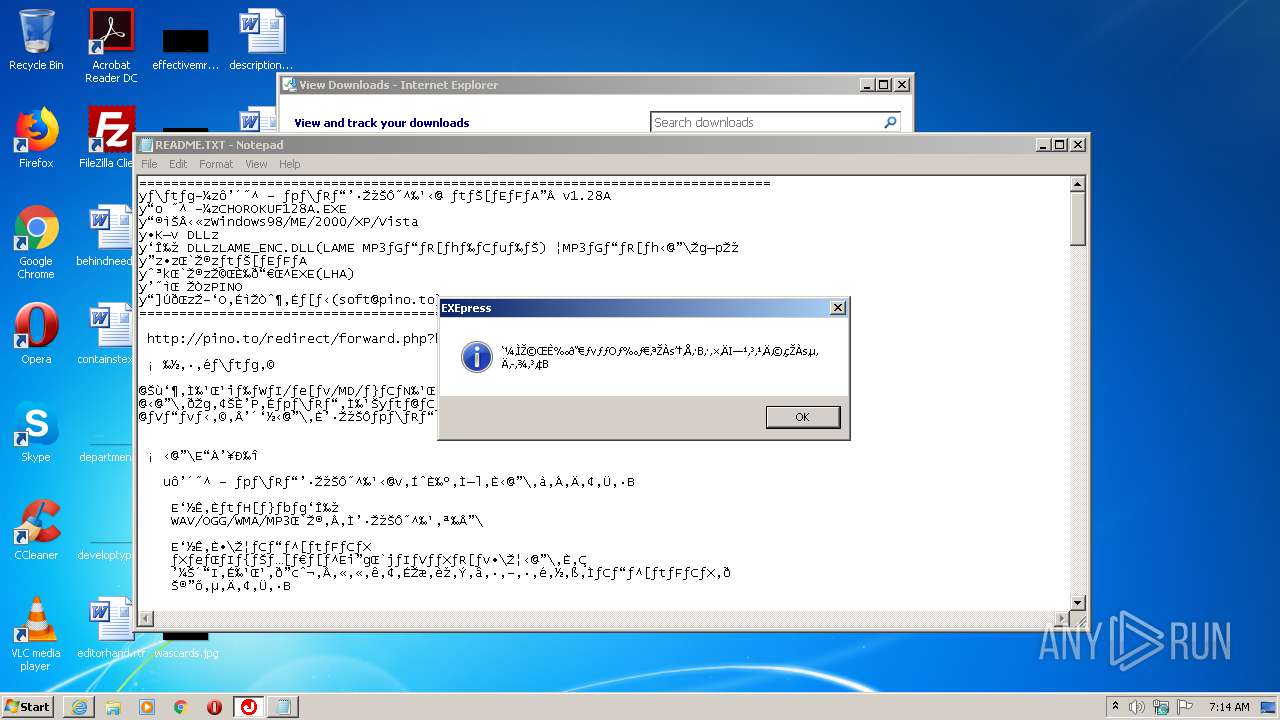
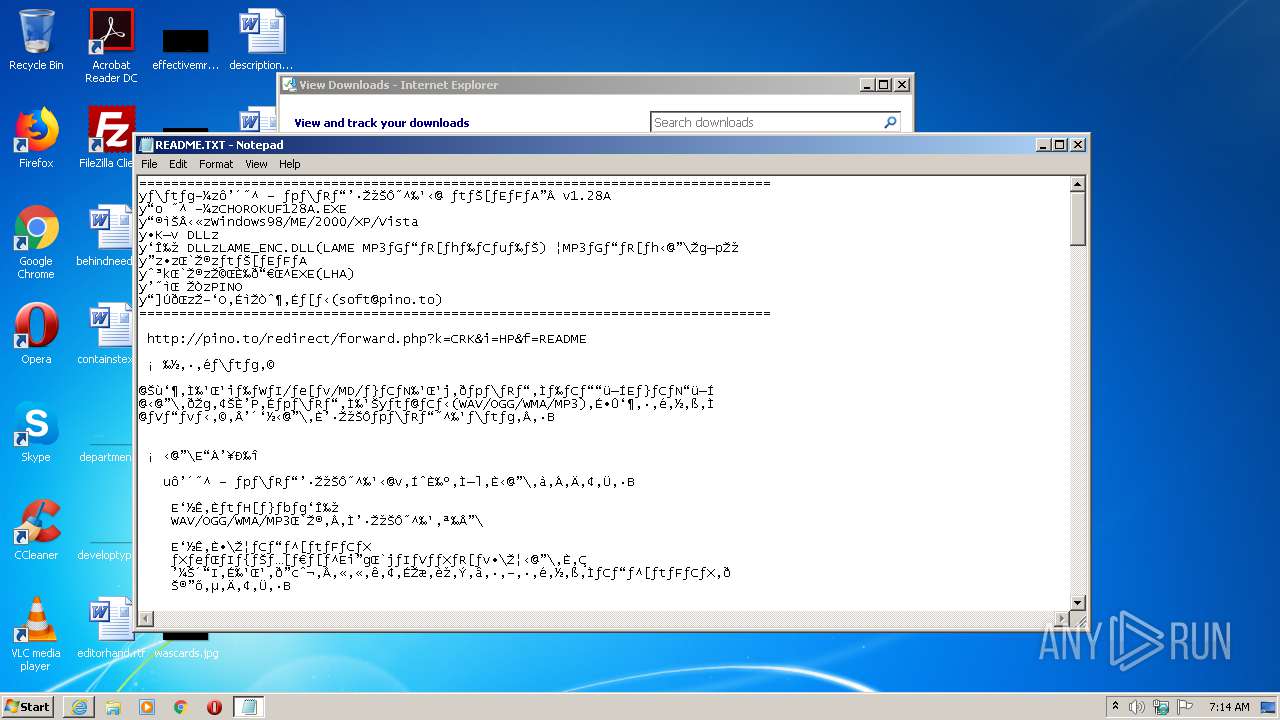
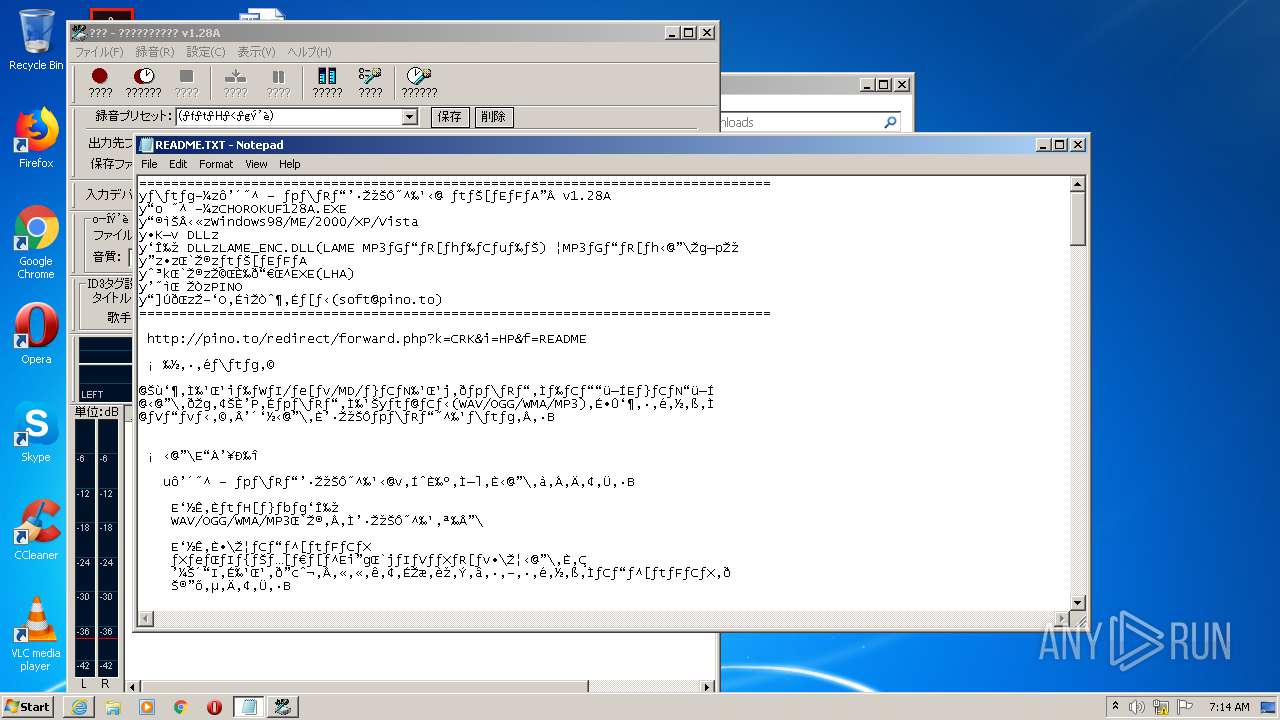
| 1780 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\CHoRoKuf\README.TXT | C:\Windows\system32\NOTEPAD.EXE | — | EXECUTER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
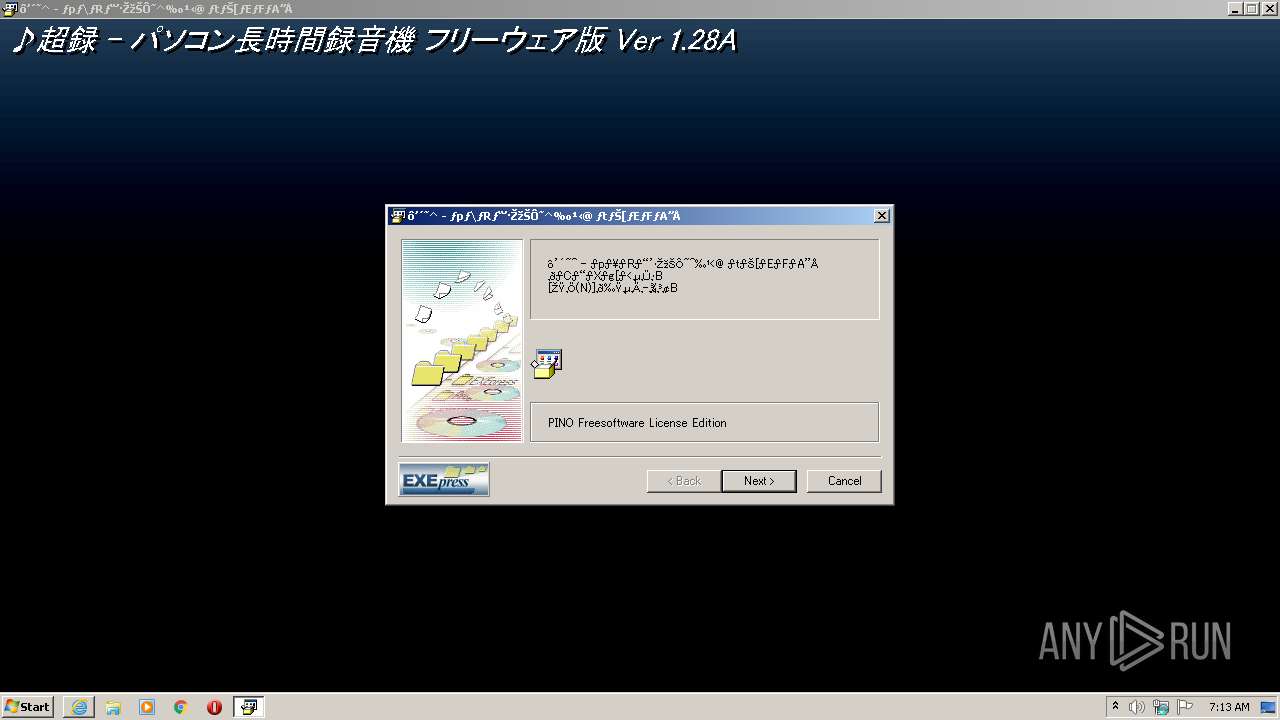
| 1944 | "C:\Program Files\CHoRoKuf\jword_plugin.exe" | C:\Program Files\CHoRoKuf\jword_plugin.exe | — | EXECUTER.exe | |||||||||||
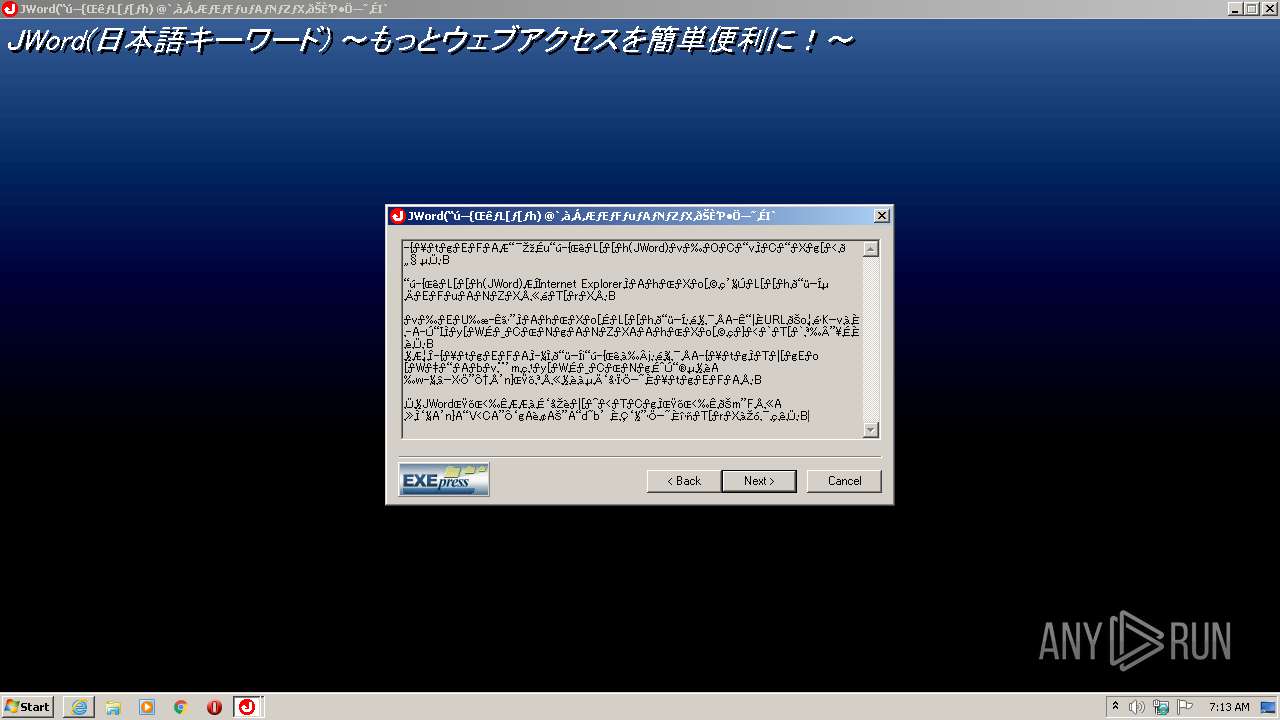
User: admin Company: web technology Corp.
http://www.webtech.co.jp/exepress/ Integrity Level: HIGH Description: Self Extractable Archive by EXEpress Exit code: 0 Version: 3.41 Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\chorokuf128a.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\chorokuf128a.exe | iexplore.exe | ||||||||||||
User: admin Company: web technology Corp.
http://www.webtech.co.jp/exepress/ Integrity Level: HIGH Description: Self Extractable Archive by EXEpress Exit code: 0 Version: 3.41 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:820 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2268 | "C:\Program Files\JWord_pino\CnsMinSetup_pino.exe" CnsMin.dll | C:\Program Files\JWord_pino\CnsMinSetup_pino.exe | jword_plugin.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\CHoRoKuf\jword_plugin.exe" | C:\Program Files\CHoRoKuf\jword_plugin.exe | — | EXECUTER.exe | |||||||||||
User: admin Company: web technology Corp.
http://www.webtech.co.jp/exepress/ Integrity Level: HIGH Description: Self Extractable Archive by EXEpress Exit code: 0 Version: 3.41 Modules
| |||||||||||||||
| 2524 | Rundll32.exe C:\Windows\DOWNLO~1\CnsMin.dll,Rundll32 | C:\Windows\system32\Rundll32.exe | — | CnsMinSetup_pino.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | "C:\Program Files\CHoRoKuf\EXECUTER.exe" installer.txt | C:\Program Files\CHoRoKuf\EXECUTER.exe | — | chorokuf128a.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
4 508
Read events
3 801
Write events
671
Delete events
36
Modification events
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2890356080 | |||
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30876770 | |||
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
4
Suspicious files
9
Text files
19
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9182.tmp | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9183.tmp | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\chorokuf128a[1].exe | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\chorokuf128a.exe.0w89vi0.partial | — | |
MD5:— | SHA256:— | |||
| 820 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFE8108DFD1A09A764.TMP | — | |
MD5:— | SHA256:— | |||
| 820 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\chorokuf128a.exe.0w89vi0.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 820 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{D803F031-9055-11EB-89FC-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B039FEA45CB4CC4BBACFC013C7C55604_50D7940D5D3FEDD8634D83074C7A46A3 | der | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\349D186F1CB5682FA0194D4F3754EF36_2C35055EF9BCF72B23077D62C20DDEB5 | binary | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\349D186F1CB5682FA0194D4F3754EF36_2C35055EF9BCF72B23077D62C20DDEB5 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2184 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | US | der | 1.48 Kb | whitelisted |
2184 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | US | der | 1.48 Kb | whitelisted |
2184 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFW6U5fLrDNi8a4PzA%3D%3D | US | der | 1.49 Kb | whitelisted |
2184 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFW6U5fLrDNi8a4PzA%3D%3D | US | der | 1.49 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2184 | iexplore.exe | 180.214.37.141:443 | ftp.vector.co.jp | Bit-isle Co.,Ltd. | JP | suspicious |
2184 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
2184 | iexplore.exe | 104.18.20.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ftp.vector.co.jp |
| malicious |
ocsp2.globalsign.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |