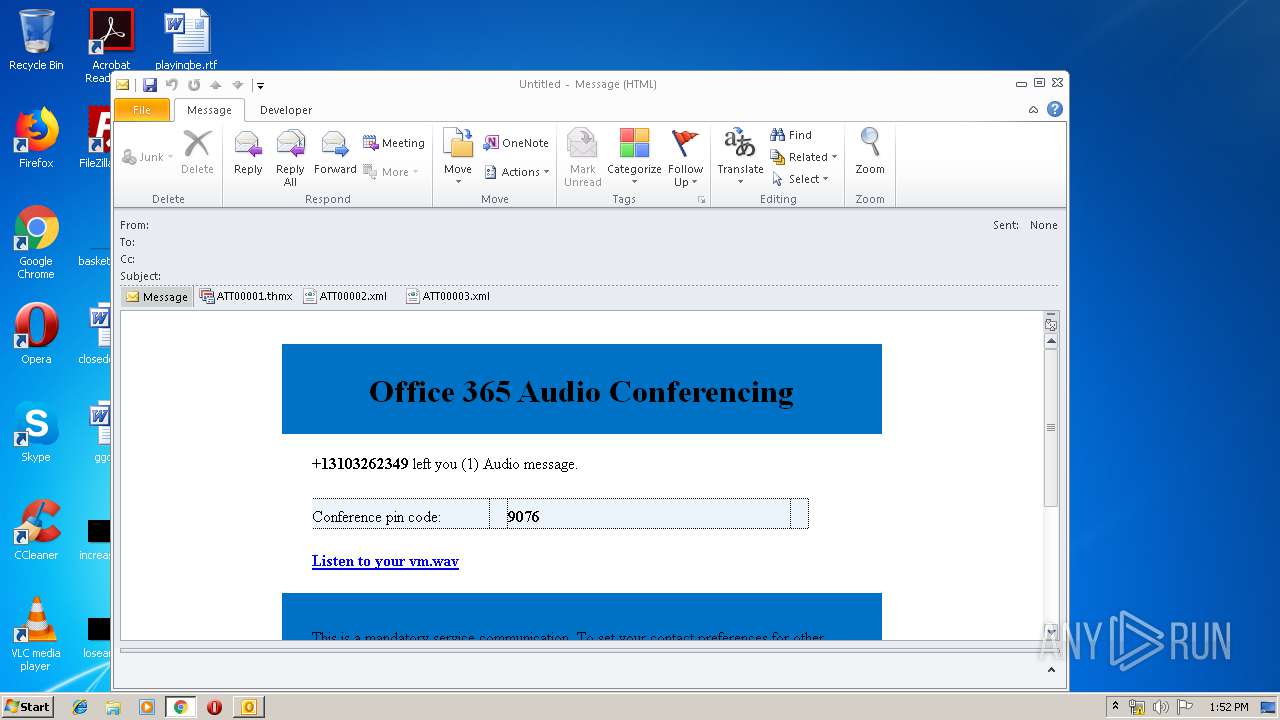
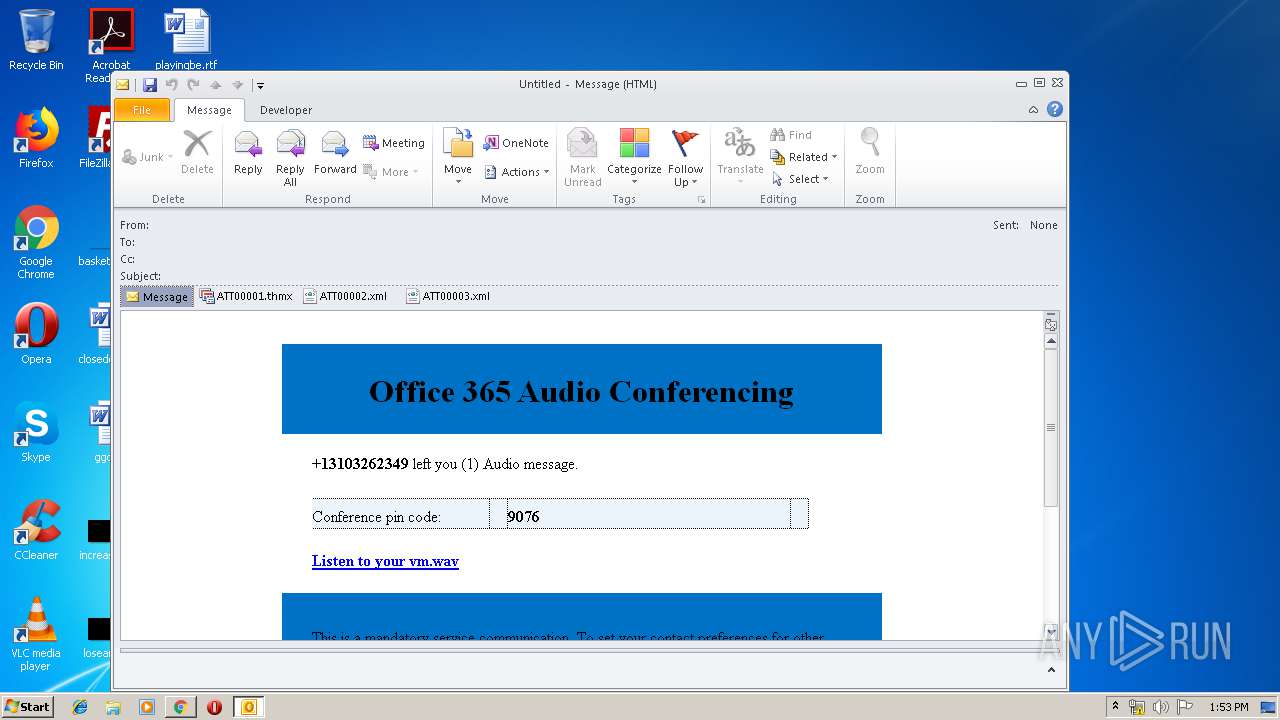
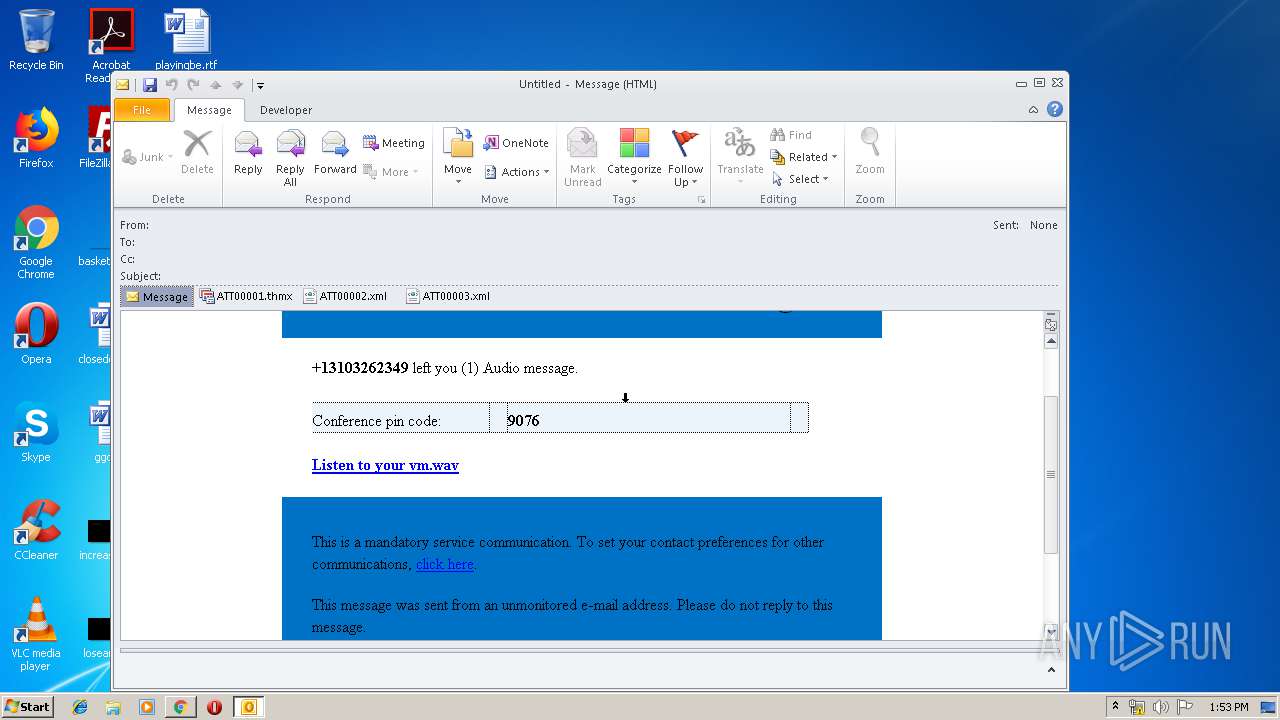
| File name: | e.msg |
| Full analysis: | https://app.any.run/tasks/3fc54b23-8af5-4eec-89f7-aa408bfc2a4e |
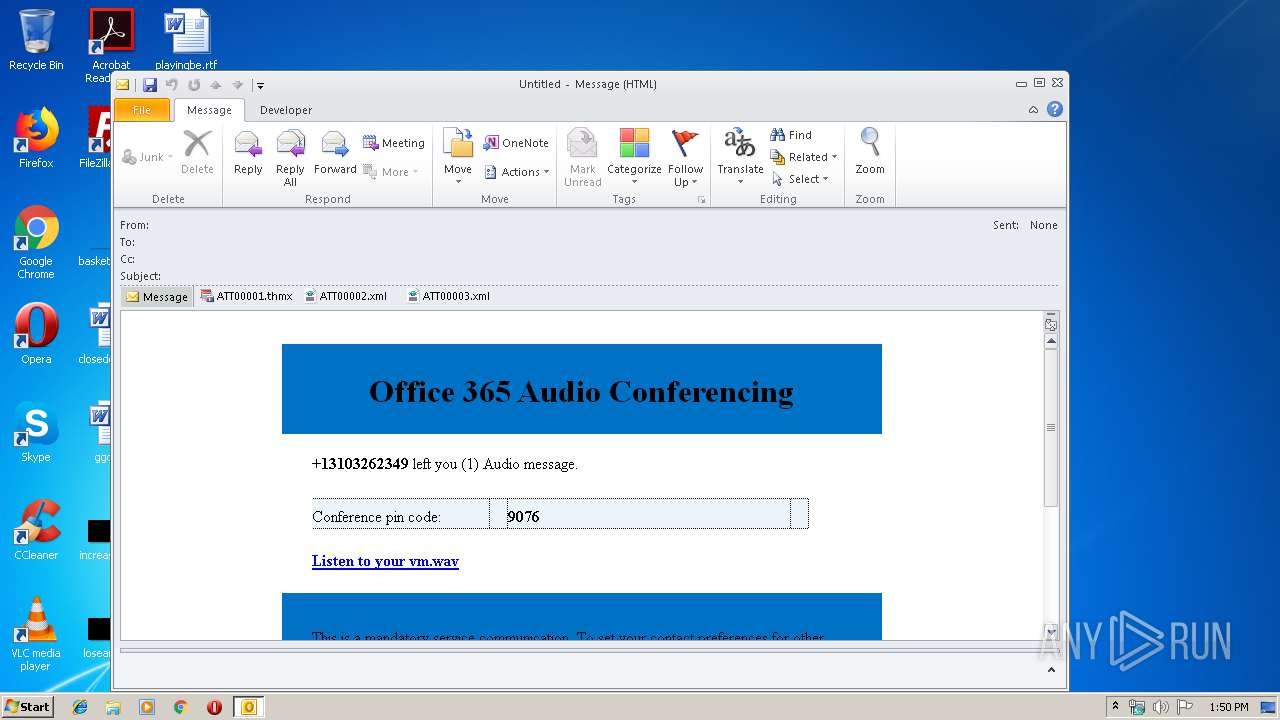
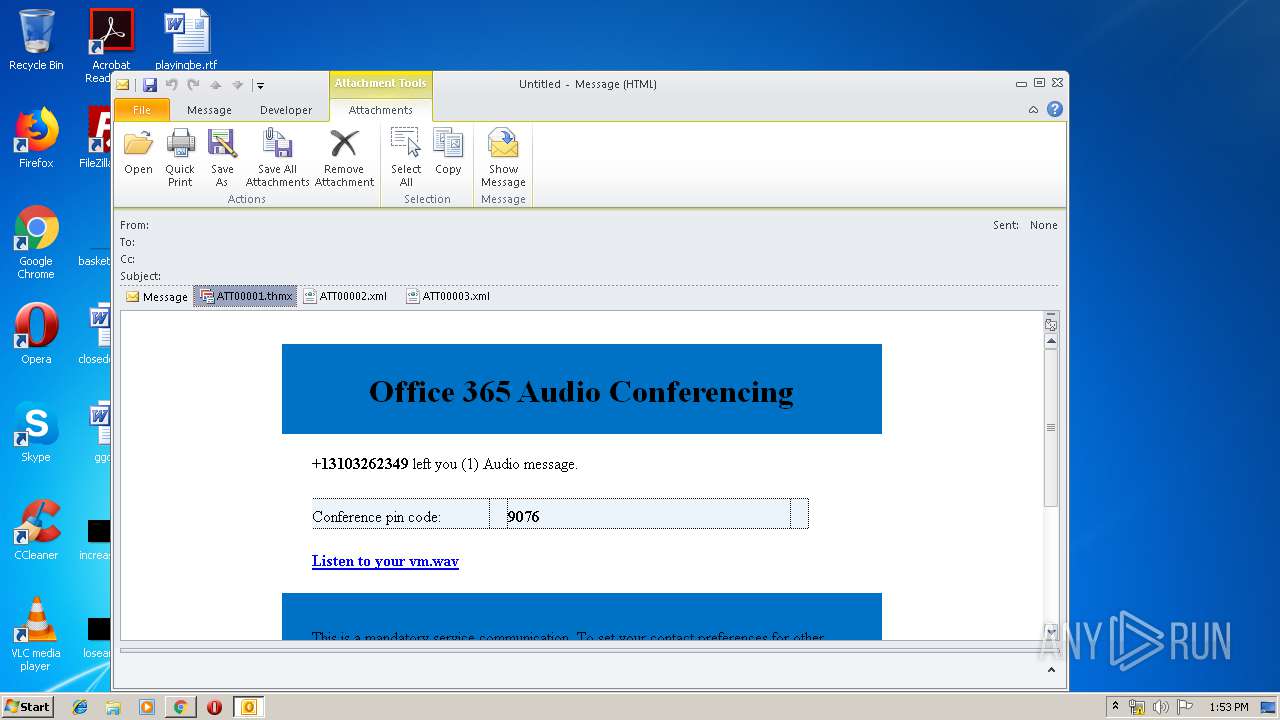
| Verdict: | Malicious activity |
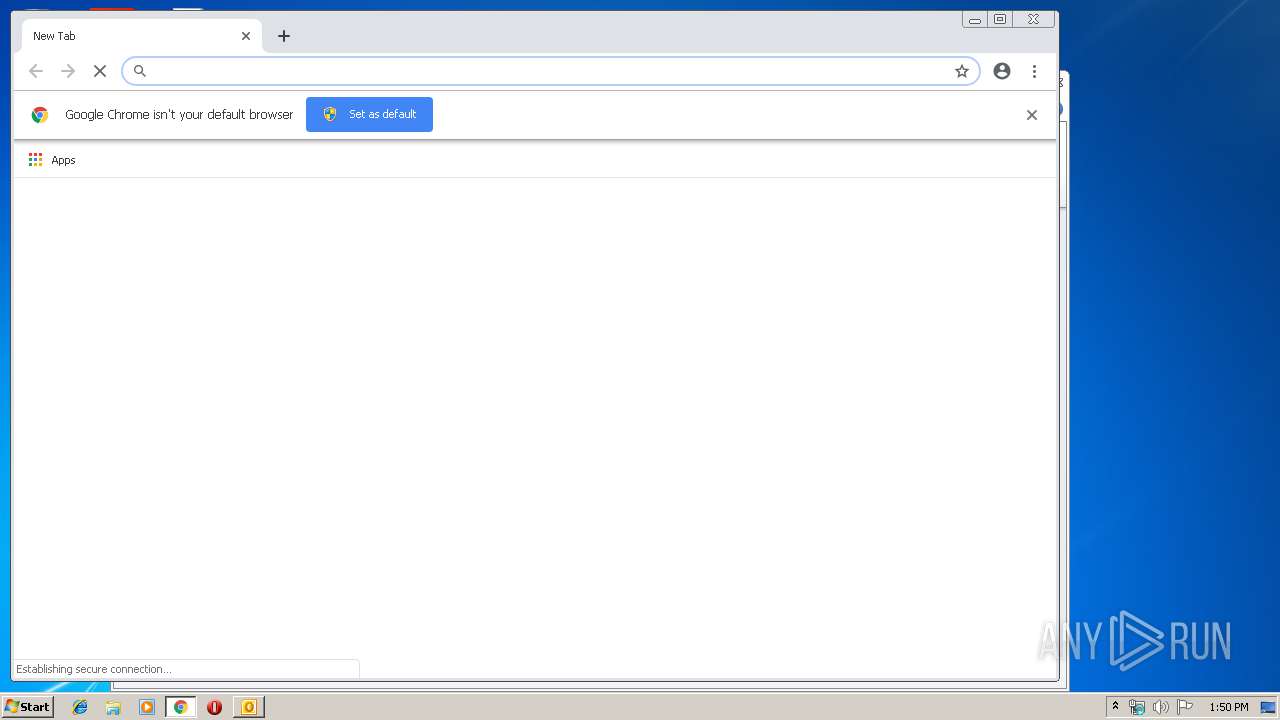
| Analysis date: | March 22, 2019, 13:50:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | E981EF4FD875E719F2EDC82B4C4131F1 |
| SHA1: | 0EBC7456B5A4A2A34E80DE0047BE8B30FD212516 |
| SHA256: | ED58912B3930C4835BDE9E30F035E27ECCE11EB707A3FBEC35FACBF1A907A127 |
| SSDEEP: | 384:T2CC3KyzE84xJeFypsLP30nHARorS4SYsKksKzsXv9w6FiS2k:qFbY84xQKekHAymYsKksKQ2n |
MALICIOUS
No malicious indicators.SUSPICIOUS
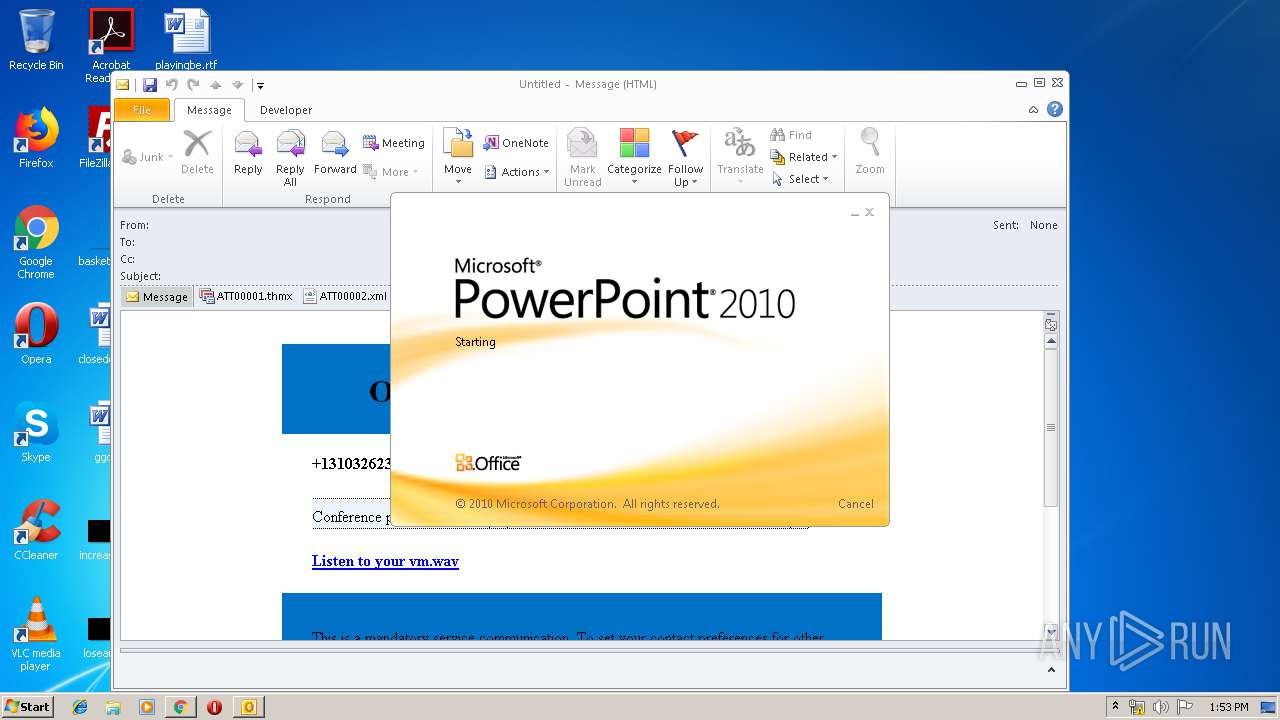
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 1484)
Checks supported languages
- POWERPNT.EXE (PID: 2676)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1484)
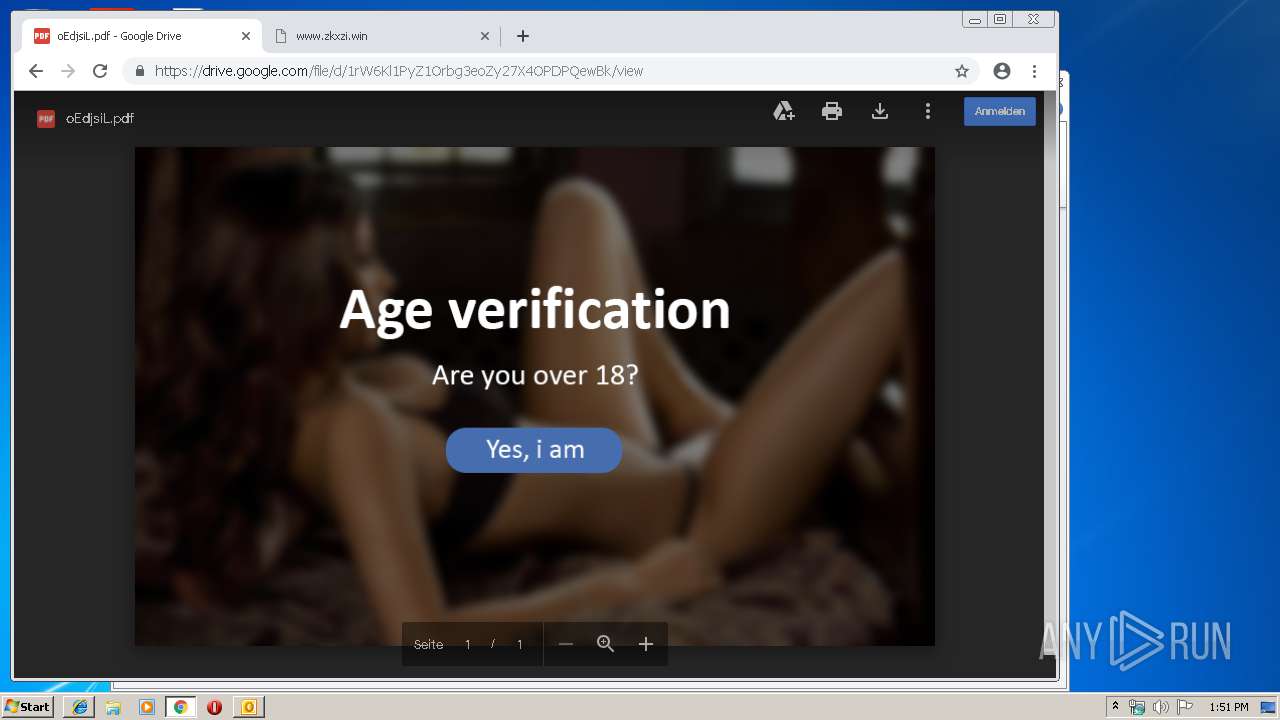
Modifies files in Chrome extension folder
- chrome.exe (PID: 2108)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1484)
- POWERPNT.EXE (PID: 2676)
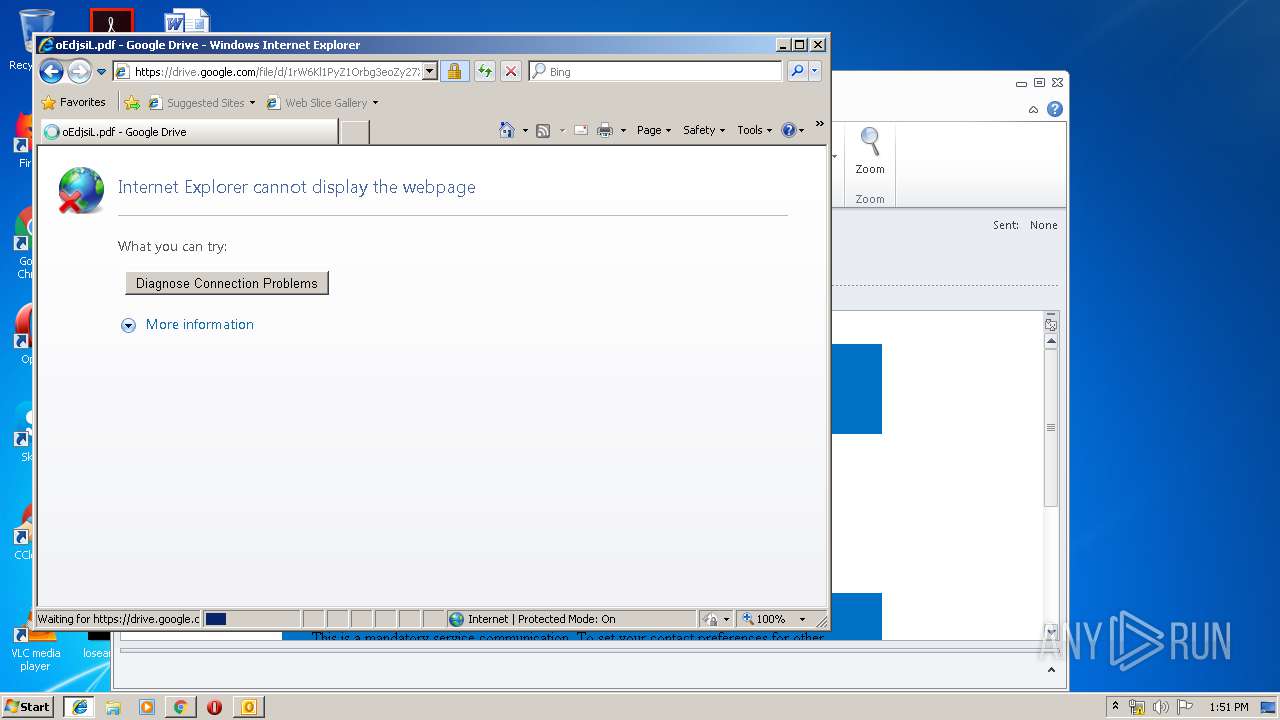
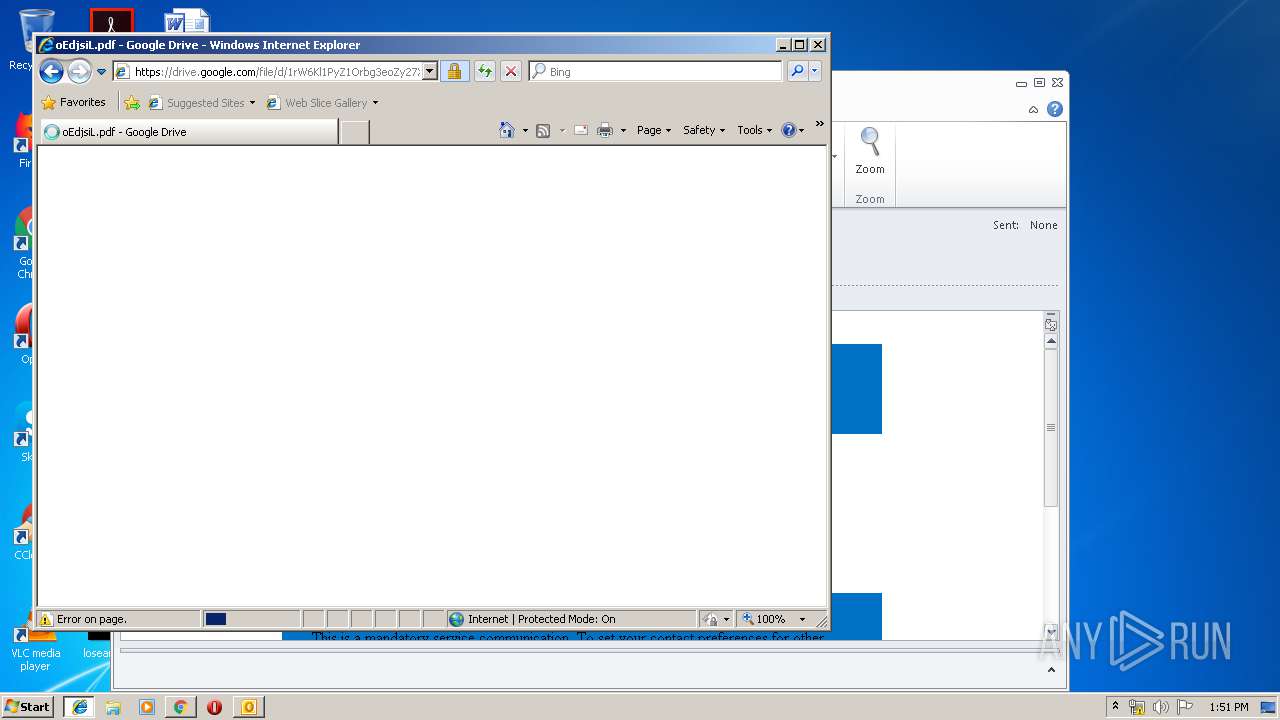
Changes settings of System certificates
- iexplore.exe (PID: 3300)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3300)
Creates files in the user directory
- iexplore.exe (PID: 3300)
- iexplore.exe (PID: 2760)
Application launched itself
- chrome.exe (PID: 2108)
Changes internet zones settings
- iexplore.exe (PID: 3300)
Reads internet explorer settings
- iexplore.exe (PID: 2760)
Reads settings of System Certificates
- iexplore.exe (PID: 3300)
- chrome.exe (PID: 3508)
Reads Internet Cache Settings
- iexplore.exe (PID: 2760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
61
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7137788658882723765,12189575154610852750,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8904032183441089547 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8904032183441089547 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7137788658882723765,12189575154610852750,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11422225976384574753 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11422225976384574753 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7137788658882723765,12189575154610852750,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3487927259972649425 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3487927259972649425 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7137788658882723765,12189575154610852750,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12229230899142136796 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12229230899142136796 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7137788658882723765,12189575154610852750,131072 --enable-features=PasswordImport --service-pipe-token=15915363440589865616 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15915363440589865616 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,7137788658882723765,12189575154610852750,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2194171533152685923 --mojo-platform-channel-handle=3292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\e.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2104 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x62360f18,0x62360f28,0x62360f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,7137788658882723765,12189575154610852750,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14797864586806246424 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14797864586806246424 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 042
Read events
2 363
Write events
643
Delete events
36
Modification events
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | ge1 |
Value: 67653100CC050000010000000000000000000000 | |||
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: CC050000CE2B1641B6E0D40100000000 | |||
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219961440 | |||
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (1484) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1316356117 | |||
Executable files
0
Suspicious files
72
Text files
218
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1484 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR89E7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\be88ba0a-6fe4-4303-9938-70bd02f9da6f.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
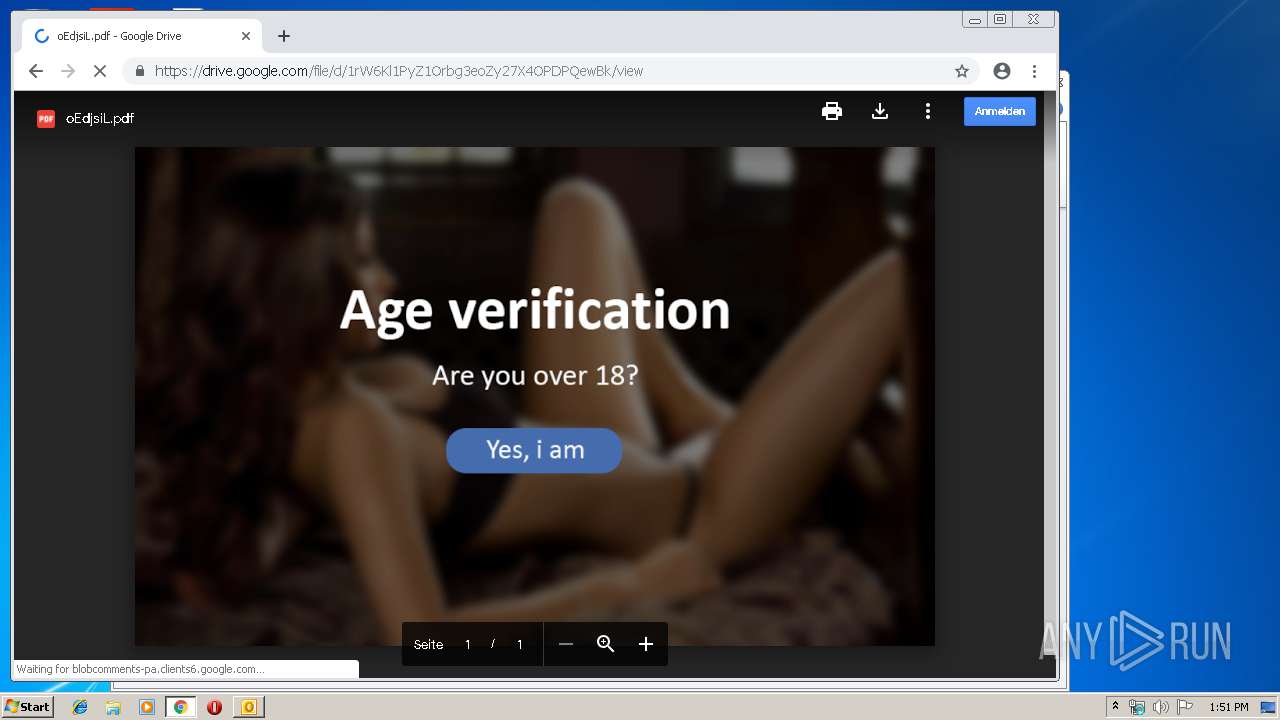
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
55
DNS requests
31
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
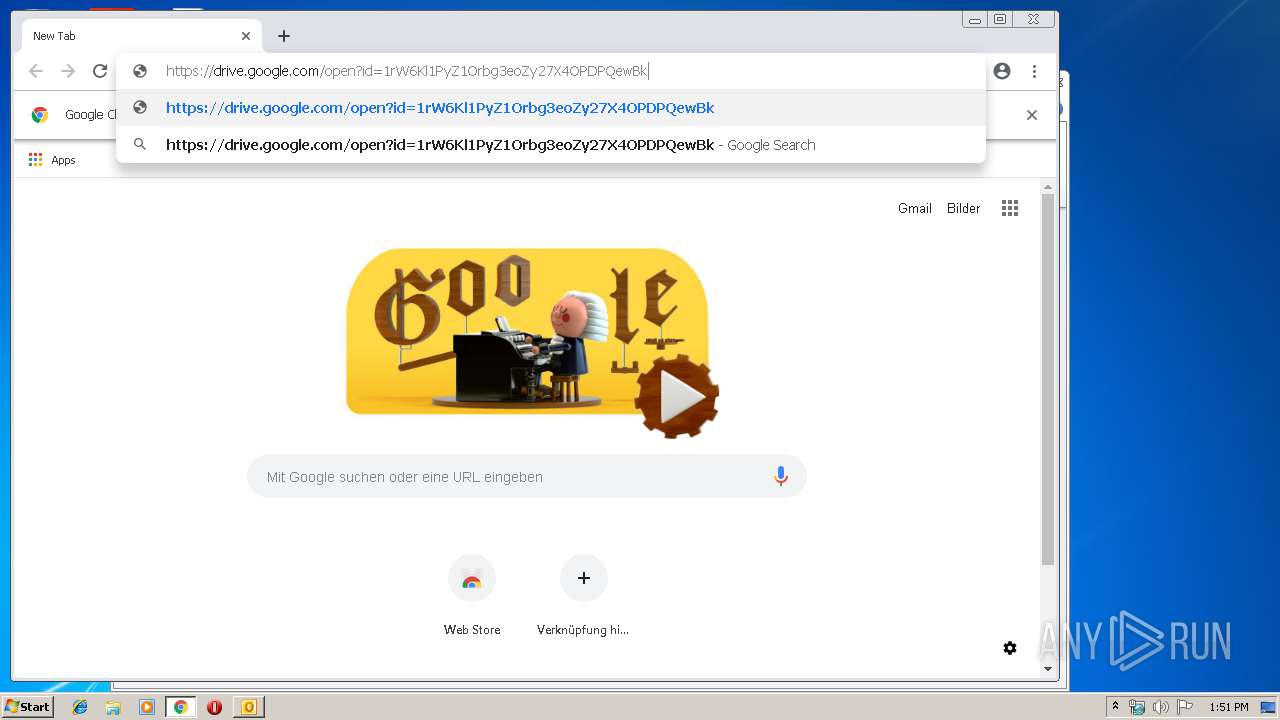
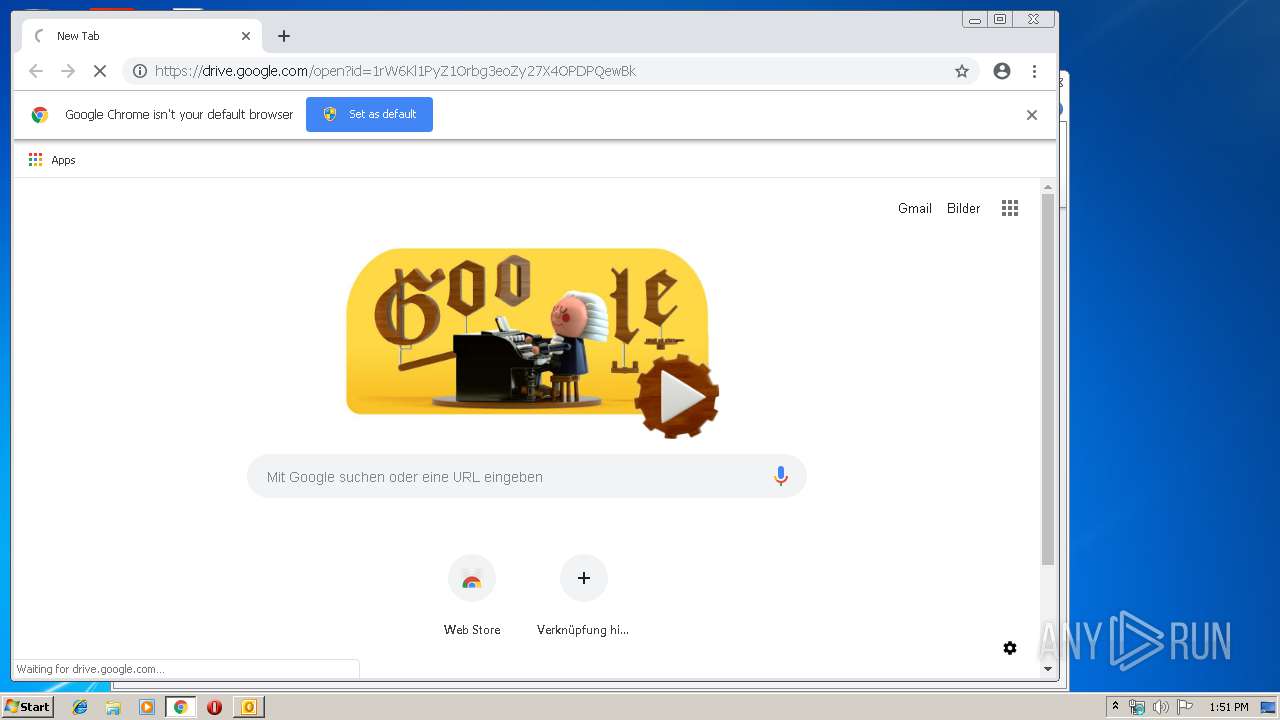
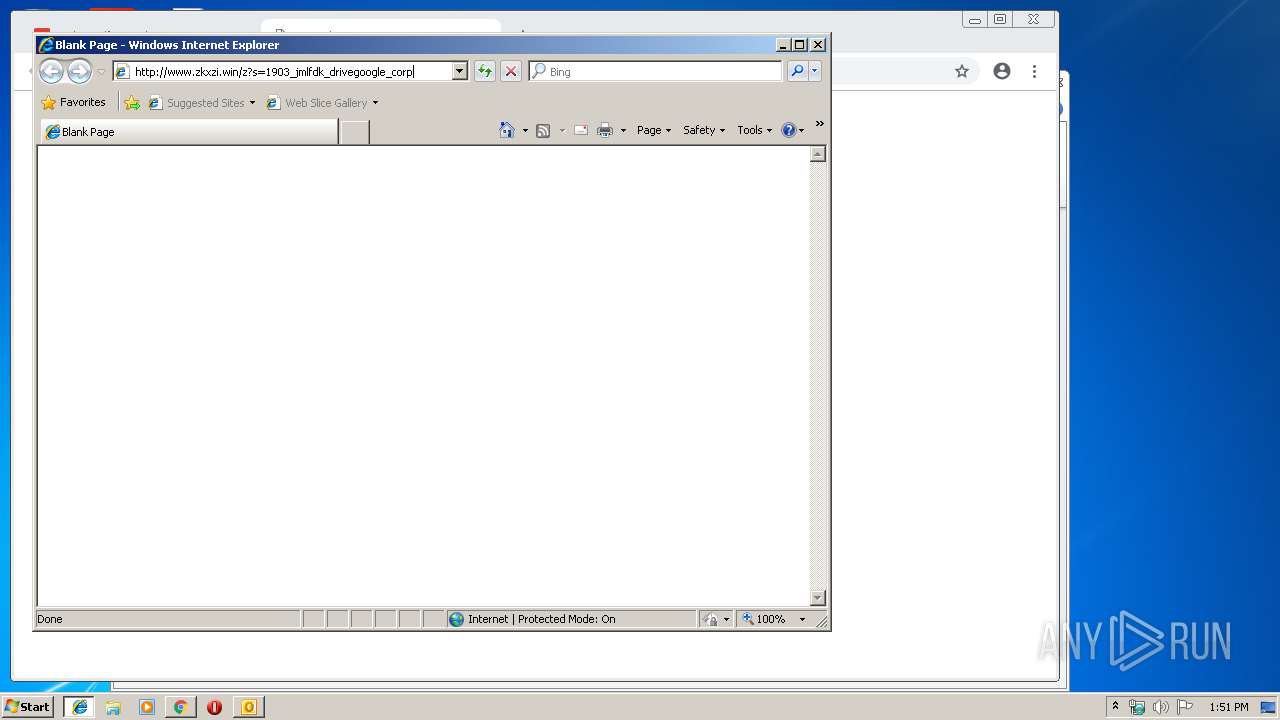
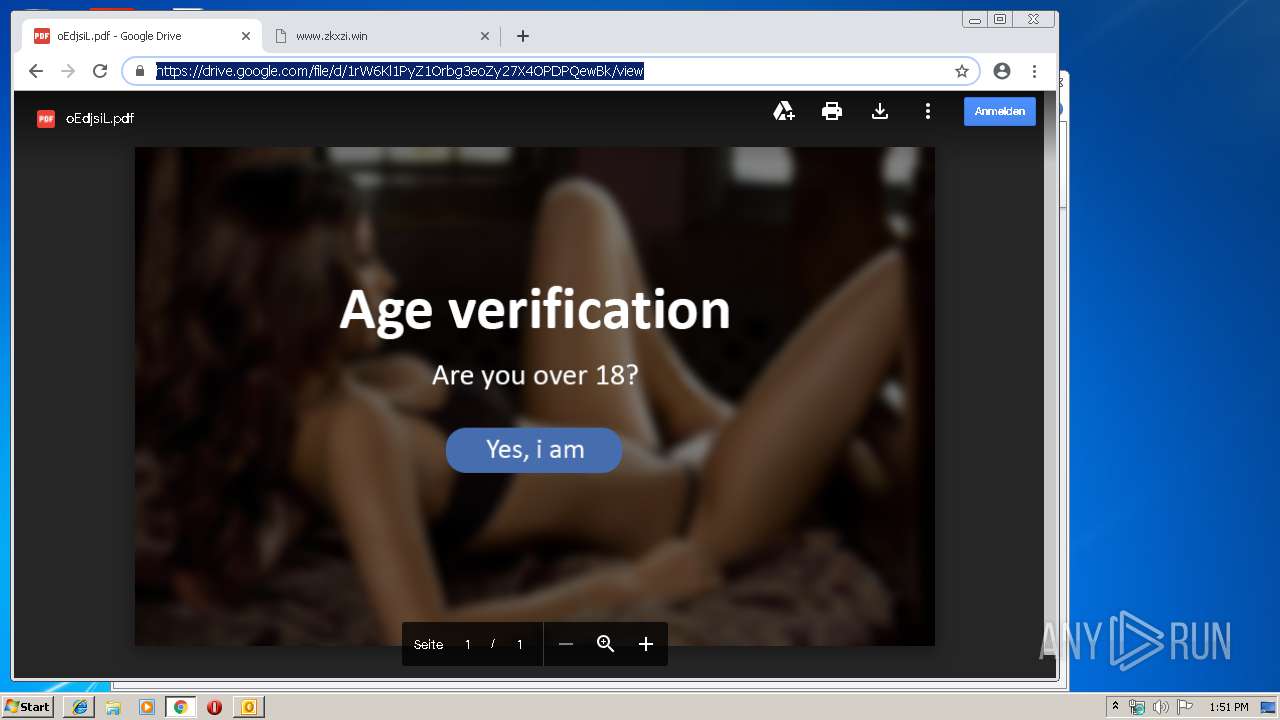
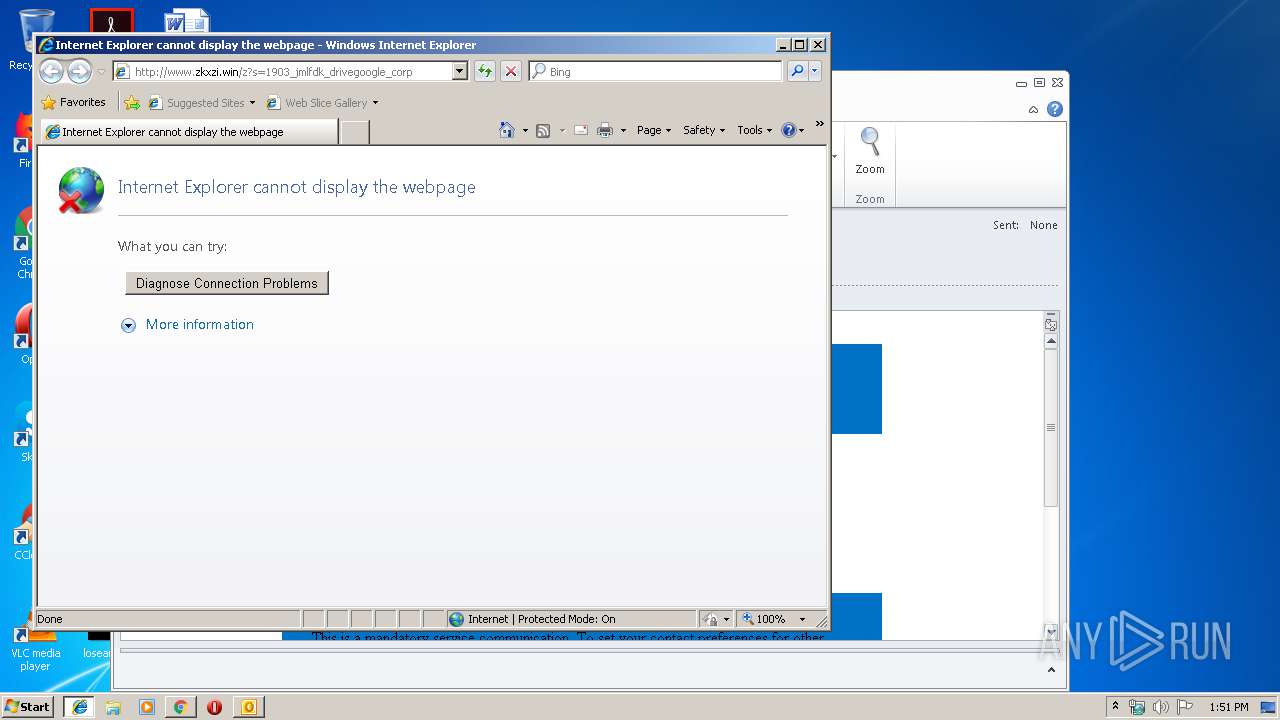
3508 | chrome.exe | GET | — | 198.54.117.210:80 | http://www.zkxzi.win/z?s=1903_jmlfdk_drivegoogle_corp | US | — | — | malicious |
3508 | chrome.exe | GET | — | 198.54.117.210:80 | http://www.zkxzi.win/z?s=1903_jmlfdk_drivegoogle_corp | US | — | — | malicious |
3508 | chrome.exe | GET | — | 198.54.117.210:80 | http://www.zkxzi.win/z?s=1903_jmlfdk_drivegoogle_corp | US | — | — | malicious |
3508 | chrome.exe | GET | — | 198.54.117.210:80 | http://www.zkxzi.win/z?s=1903_jmlfdk_drivegoogle_corp | US | — | — | malicious |
3508 | chrome.exe | GET | — | 198.54.117.210:80 | http://www.zkxzi.win/z?s=1903_jmlfdk_drivegoogle_corp | US | — | — | malicious |
2760 | iexplore.exe | GET | — | 198.54.117.216:80 | http://www.zkxzi.win/z?s=1903_jmlfdk_drivegoogle_corp | US | — | — | malicious |
3508 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
3508 | chrome.exe | GET | 200 | 217.146.165.205:80 | http://r2---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.150&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1553261727&mv=u&pl=20&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
3508 | chrome.exe | GET | 302 | 192.64.119.21:80 | http://zkxzi.win/z?s=1903_jmlfdk_drivegoogle_corp | US | html | 76 b | suspicious |
3300 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1484 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3508 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3508 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.22.74:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 216.58.205.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3508 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2760 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2760 | iexplore.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |