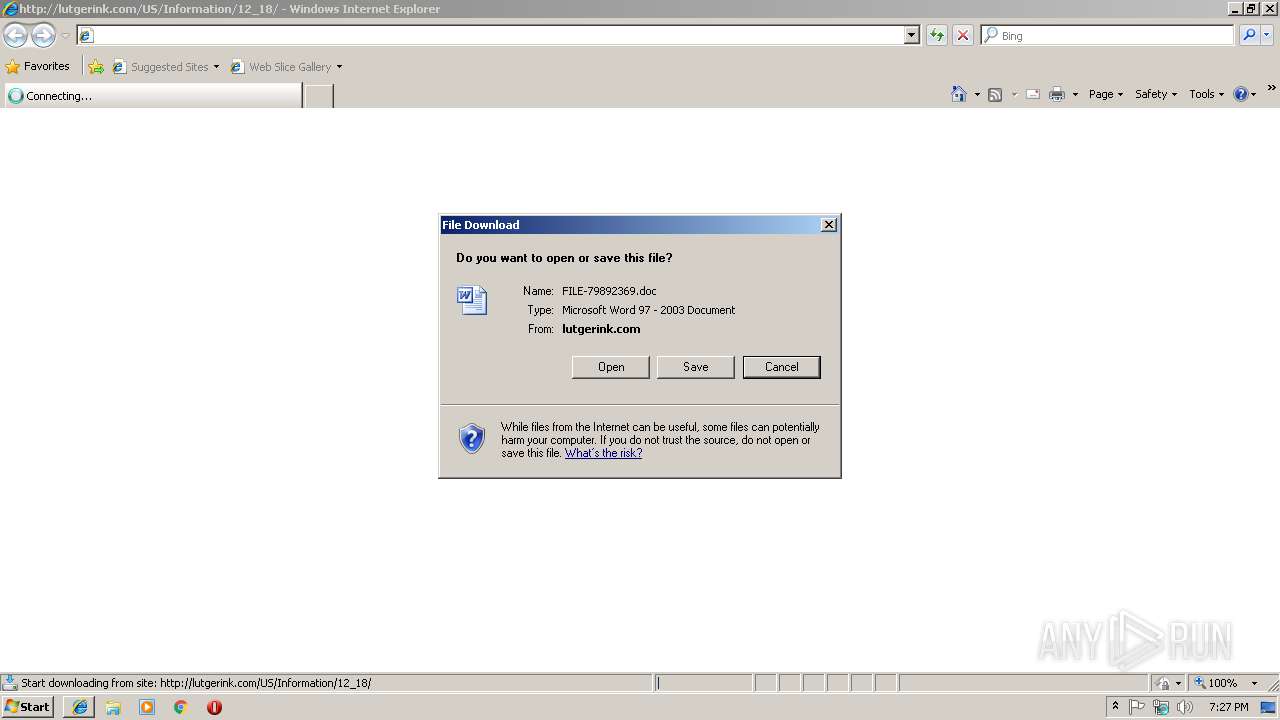
| URL: | http://lutgerink.com/US/Information/12_18 |
| Full analysis: | https://app.any.run/tasks/650afad8-5125-45cf-98cd-d4748e95c2bd |
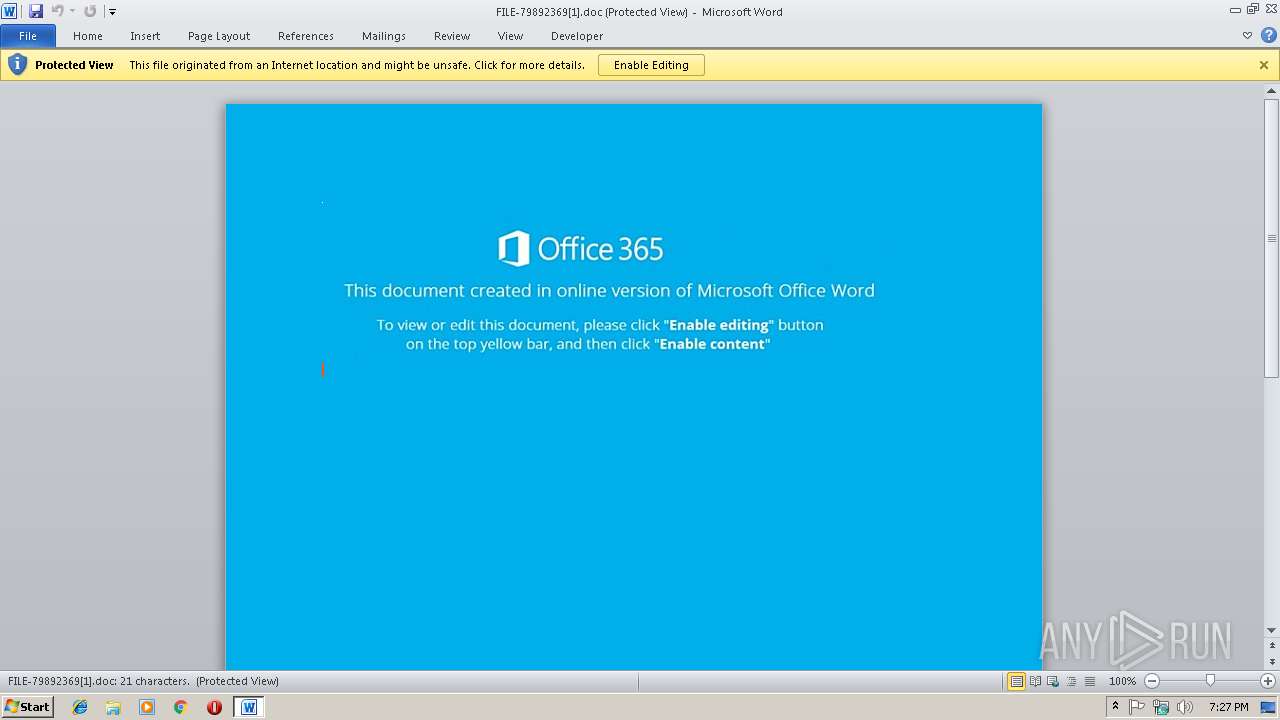
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 14, 2018, 19:27:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1F12FE8C775684F3EC49DCE4823D267E |
| SHA1: | 1241E63AB4FCDE77E406625A3407863802ED4A60 |
| SHA256: | ED548CD5BBB2228EB56F88B9B8D1EB35FFF7423100D6FB9E74B9DE5A0B399AC2 |
| SSDEEP: | 3:N1KSQy62KwB/MKLKin:CSjjB/MK+i |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 4020)
Executes PowerShell scripts
- cmd.exe (PID: 2784)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 2312)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 4020)
Application was dropped or rewritten from another process
- 749.exe (PID: 3944)
- 749.exe (PID: 2900)
- archivesymbol.exe (PID: 3316)
- archivesymbol.exe (PID: 2616)
- archivesymbol.exe (PID: 836)
- 2BOQZWOnI.exe (PID: 4044)
- 2COQZWOnJ.exe (PID: 1356)
Downloads executable files from the Internet
- powershell.exe (PID: 2312)
Connects to CnC server
- archivesymbol.exe (PID: 3316)
EMOTET was detected
- archivesymbol.exe (PID: 3316)
Changes the autorun value in the registry
- archivesymbol.exe (PID: 3316)
Actions looks like stealing of personal data
- archivesymbol.exe (PID: 836)
Stops/Deletes Windows Defender service
- cmd.exe (PID: 3764)
- cmd.exe (PID: 1416)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 3712)
Known privilege escalation attack
- DllHost.exe (PID: 2100)
Loads the Task Scheduler COM API
- 2COQZWOnJ.exe (PID: 1356)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 4020)
- cmd.exe (PID: 3852)
- 749.exe (PID: 3944)
- archivesymbol.exe (PID: 3316)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2784)
- cmd.exe (PID: 3228)
- cmd.exe (PID: 3852)
- cmd.exe (PID: 3476)
- 2BOQZWOnI.exe (PID: 4044)
- 2COQZWOnJ.exe (PID: 1356)
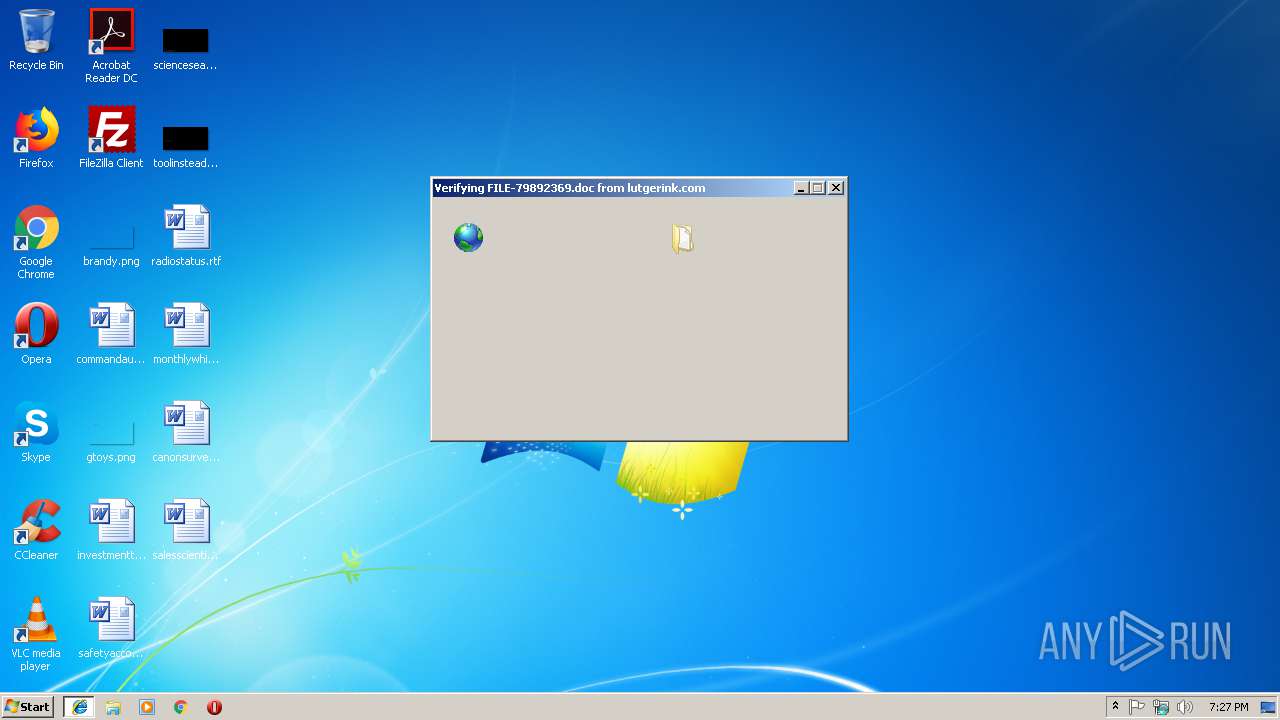
Starts Microsoft Office Application
- iexplore.exe (PID: 2980)
- WINWORD.EXE (PID: 4020)
Creates files in the user directory
- powershell.exe (PID: 2312)
- 2BOQZWOnI.exe (PID: 4044)
- powershell.exe (PID: 2560)
- powershell.exe (PID: 3428)
Executable content was dropped or overwritten
- powershell.exe (PID: 2312)
- 749.exe (PID: 2900)
- archivesymbol.exe (PID: 3316)
- 2BOQZWOnI.exe (PID: 4044)
Starts itself from another location
- 749.exe (PID: 2900)
Connects to unusual port
- archivesymbol.exe (PID: 3316)
Creates files in the program directory
- archivesymbol.exe (PID: 3316)
Loads DLL from Mozilla Firefox
- archivesymbol.exe (PID: 836)
Connects to SMTP port
- archivesymbol.exe (PID: 3316)
Executes PowerShell scripts
- cmd.exe (PID: 3192)
- cmd.exe (PID: 1476)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2980)
Reads internet explorer settings
- iexplore.exe (PID: 3144)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3320)
- WINWORD.EXE (PID: 4020)
Reads Internet Cache Settings
- iexplore.exe (PID: 3144)
Creates files in the user directory
- WINWORD.EXE (PID: 4020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
32
Malicious processes
13
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | "C:\Users\admin\AppData\Local\archivesymbol\archivesymbol.exe" /scomma "C:\Users\admin\AppData\Local\Temp\D095.tmp" | C:\Users\admin\AppData\Local\archivesymbol\archivesymbol.exe | archivesymbol.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 840 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1062 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1356 | "C:\Users\admin\AppData\Roaming\WinDefrag\2COQZWOnJ.exe" | C:\Users\admin\AppData\Roaming\WinDefrag\2COQZWOnJ.exe | — | DllHost.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Hotspot Client Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1416 | /c sc stop WinDefend | C:\Windows\system32\cmd.exe | — | 2BOQZWOnI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1476 | /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\system32\cmd.exe | — | 2COQZWOnJ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2100 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | powershell - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2444 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2560 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 908
Read events
3 267
Write events
631
Delete events
10
Modification events
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {49ECA593-FFD6-11E8-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070C0005000E0013001B001B007102 | |||
Executable files
4
Suspicious files
12
Text files
5
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2980 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2980 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD1EB19A4DAF14C45.TMP | — | |
MD5:— | SHA256:— | |||
| 4020 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7FCF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4020 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_75E6E0F6-8AB4-48F4-BB3D-FEBA32466816.0\9F6D67AF.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2980 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF87B8ADD1FB0037AF.TMP | — | |
MD5:— | SHA256:— | |||
| 2980 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{49ECA593-FFD6-11E8-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 4020 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F7DDBC95.wmf | — | |
MD5:— | SHA256:— | |||
| 4020 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F4D8706B.wmf | — | |
MD5:— | SHA256:— | |||
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_75E6E0F6-8AB4-48F4-BB3D-FEBA32466816.0\~DF4CCE46FAC3F7A04B.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
135
DNS requests
96
Threats
96
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3316 | archivesymbol.exe | GET | 200 | 181.15.92.18:80 | http://181.15.92.18/ | AR | binary | 148 b | malicious |
3316 | archivesymbol.exe | GET | — | 190.146.201.54:80 | http://190.146.201.54/ | CO | — | — | malicious |
3316 | archivesymbol.exe | GET | — | 190.152.12.86:80 | http://190.152.12.86/ | EC | — | — | malicious |
3316 | archivesymbol.exe | GET | — | 110.37.219.134:990 | http://110.37.219.134:990/ | PK | — | — | suspicious |
3316 | archivesymbol.exe | GET | — | 152.168.60.9:80 | http://152.168.60.9/ | AR | — | — | malicious |
3316 | archivesymbol.exe | GET | 200 | 181.15.92.18:80 | http://181.15.92.18/ | AR | binary | 148 b | malicious |
2312 | powershell.exe | GET | 200 | 162.220.162.40:80 | http://evihdaf.com/syXxoBHdX/ | US | executable | 156 Kb | malicious |
3144 | iexplore.exe | GET | 200 | 185.96.5.160:80 | http://lutgerink.com/US/Information/12_18/ | NL | document | 52.8 Kb | suspicious |
3144 | iexplore.exe | GET | 301 | 185.96.5.160:80 | http://lutgerink.com/US/Information/12_18 | NL | html | 250 b | suspicious |
3316 | archivesymbol.exe | GET | 200 | 181.15.92.18:80 | http://181.15.92.18/whoami.php | AR | text | 13 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3144 | iexplore.exe | 185.96.5.160:80 | lutgerink.com | CloudVPS B.V. | NL | suspicious |
2980 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2312 | powershell.exe | 162.220.162.40:80 | evihdaf.com | NEW JERSEY INTERNATIONAL INTERNET EXCHANGE LLC | US | malicious |
3316 | archivesymbol.exe | 190.152.12.86:80 | — | CORPORACION NACIONAL DE TELECOMUNICACIONES - CNT EP | EC | malicious |
3316 | archivesymbol.exe | 190.146.201.54:80 | — | Telmex Colombia S.A. | CO | malicious |
3316 | archivesymbol.exe | 152.168.60.9:80 | — | CABLEVISION S.A. | AR | malicious |
3316 | archivesymbol.exe | 110.37.219.134:990 | — | National WiMAX/IMS environment | PK | suspicious |
3316 | archivesymbol.exe | 181.15.92.18:80 | — | Telecom Argentina S.A. | AR | malicious |
3316 | archivesymbol.exe | 190.189.179.140:8080 | — | Prima S.A. | AR | malicious |
3316 | archivesymbol.exe | 192.185.120.146:587 | mail.skytravelsv.com | CyrusOne LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
lutgerink.com |
| suspicious |
evihdaf.com |
| malicious |
mail.reladi.com.mx |
| unknown |
imap.gmail.com |
| shared |
mail.grupoquimicocontreras.com.mx |
| unknown |
mail.ciemsa-mty.com.mx |
| unknown |
mail.ledneonchile.cl |
| suspicious |
watermelon.nocdirect.com |
| unknown |
a2plcpnl0344.prod.iad2.secureserver.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3144 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3144 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3144 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3144 | iexplore.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |
2312 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
2312 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
2312 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2312 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2312 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3316 | archivesymbol.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
7 ETPRO signatures available at the full report