| File name: | dump1.bin |
| Full analysis: | https://app.any.run/tasks/cb08d70f-8c38-40a9-9e46-528f81f16a51 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 05:28:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | F0C97DCB65A030A214F6DD33CF4A8566 |
| SHA1: | B23175FA1D3989BAA2E3D8B5C7192554C24ABF18 |
| SHA256: | ED49B23DF7DEFAB3DF933C778183B12C019AB253330090F214F4BB5C2F89BCBC |
| SSDEEP: | 3072:AZPM0OGdUKV10OTed7/kBazzFbULOHOiPyH53ZV6:AZPMnGZVyO6F/M4qyPU53Z |
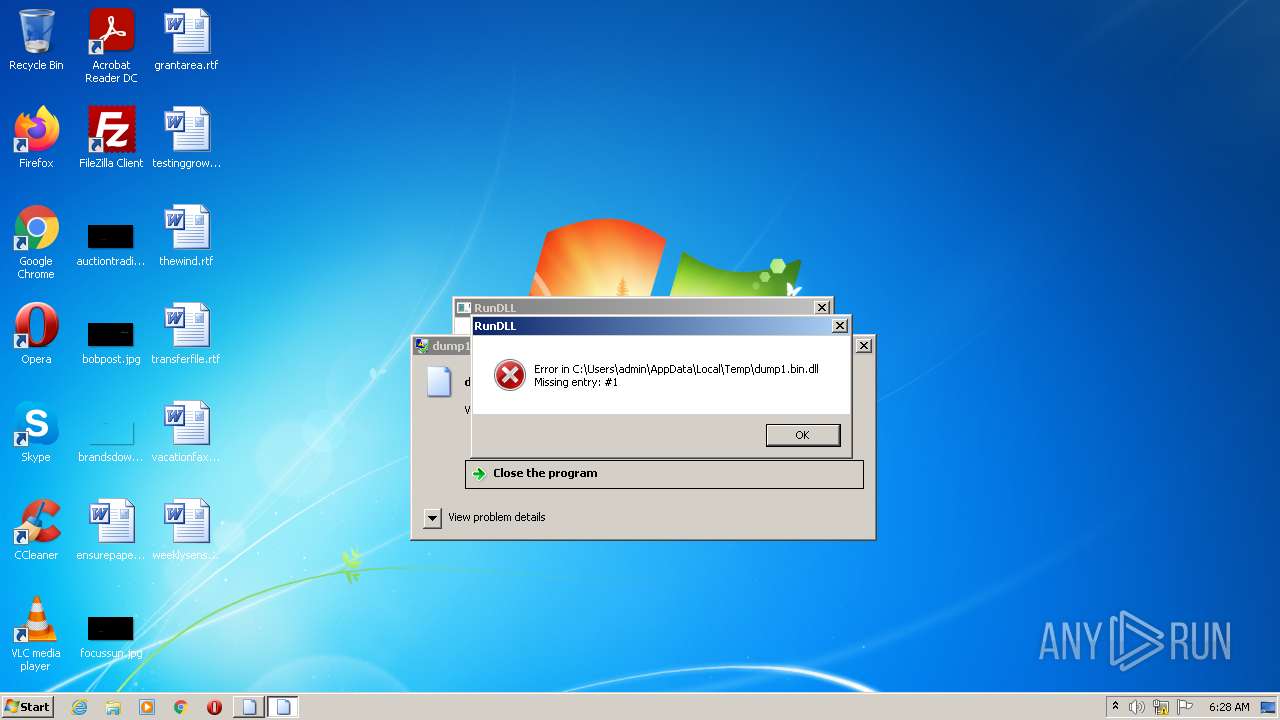
MALICIOUS
Loads dropped or rewritten executable
- WerFault.exe (PID: 1432)
- rundll32.exe (PID: 3768)
SUSPICIOUS
Application launched itself
- rundll32.exe (PID: 476)
INFO
Loads main object executable
- rundll32.exe (PID: 476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2019-Jul-08 14:33:00 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 248 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 5 |
| TimeDateStamp: | 2019-Jul-08 14:33:00 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 44100 | 44544 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54199 |
.rdata | 49152 | 11100 | 11264 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.89161 |
.data | 61440 | 59024 | 58368 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99241 |
.z4p395l | 122880 | 51200 | 51200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.06584 |
.reloc | 176128 | 1528 | 1536 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65359 |
Imports
KERNEL32.dll |
Total processes
52
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
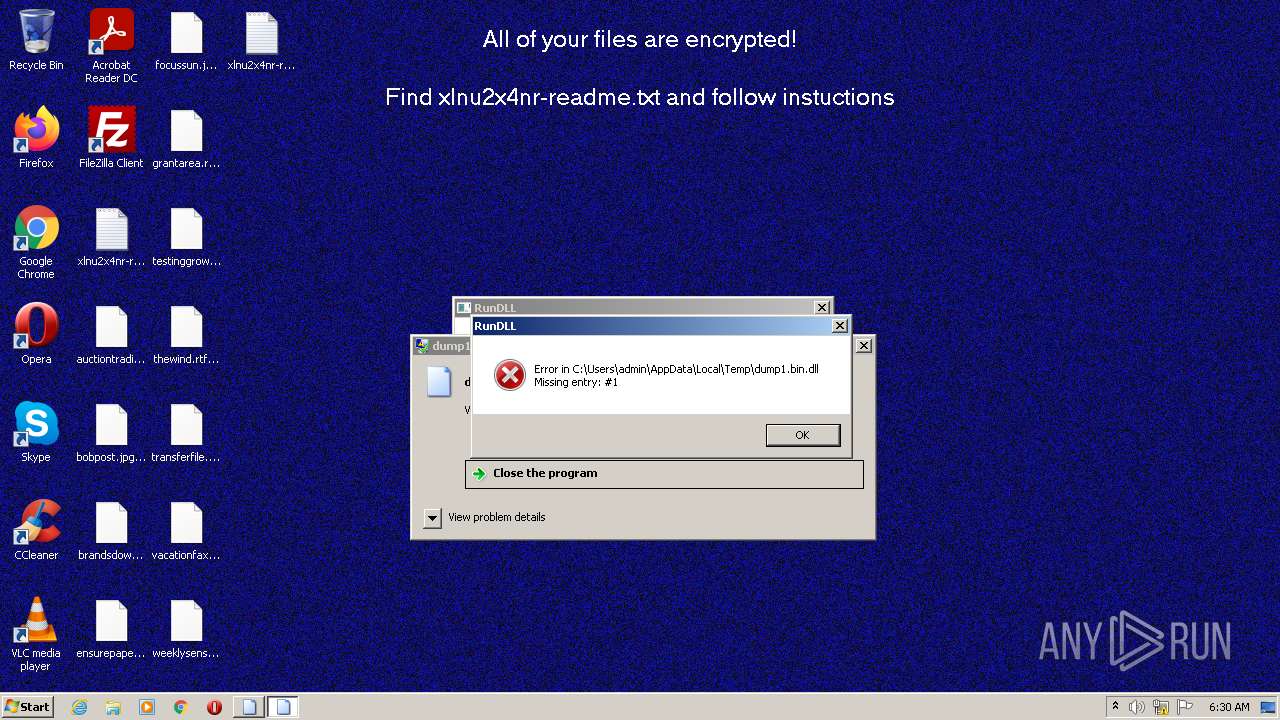
| 476 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\dump1.bin.dll", #1 | C:\Windows\System32\rundll32.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1100 | bcdedit /set {default} recoveryenabled No | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1252 | vssadmin.exe Delete Shadows /All /Quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1432 | C:\Windows\system32\WerFault.exe -u -p 476 -s 632 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
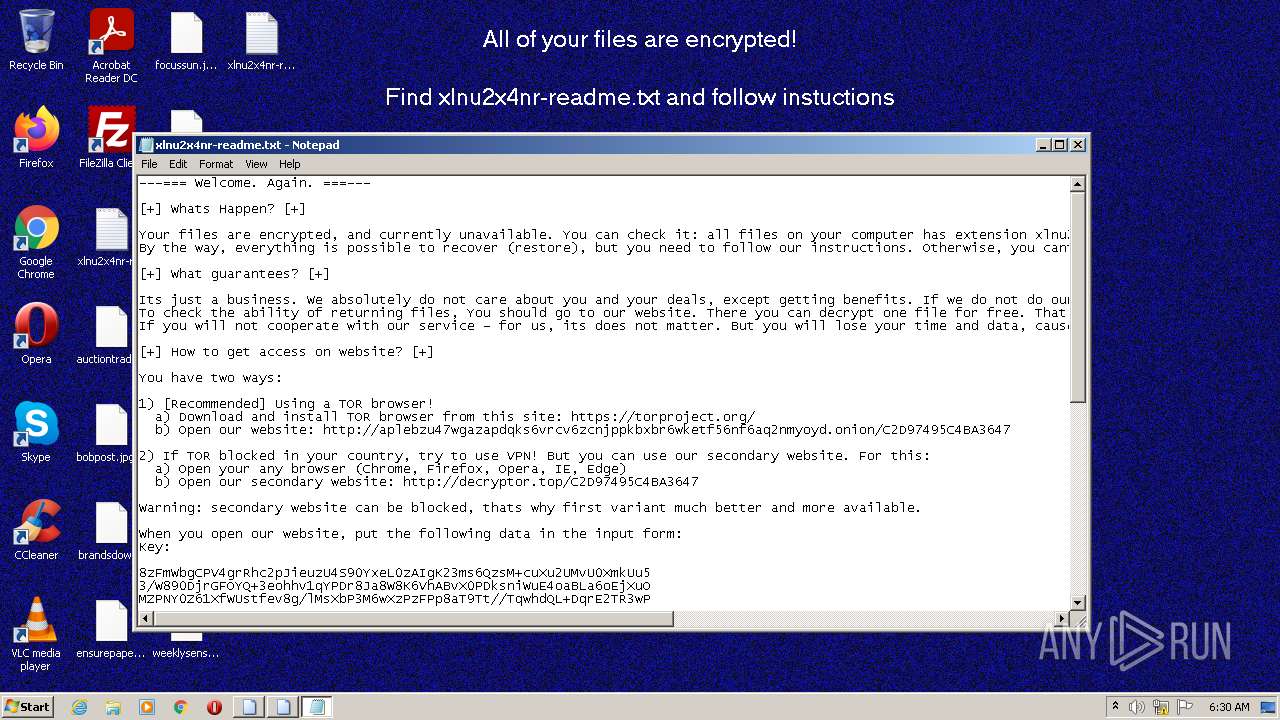
| 2392 | "C:\Windows\System32\cmd.exe" /c vssadmin.exe Delete Shadows /All /Quiet & bcdedit /set {default} recoveryenabled No & bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\cmd.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2536 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
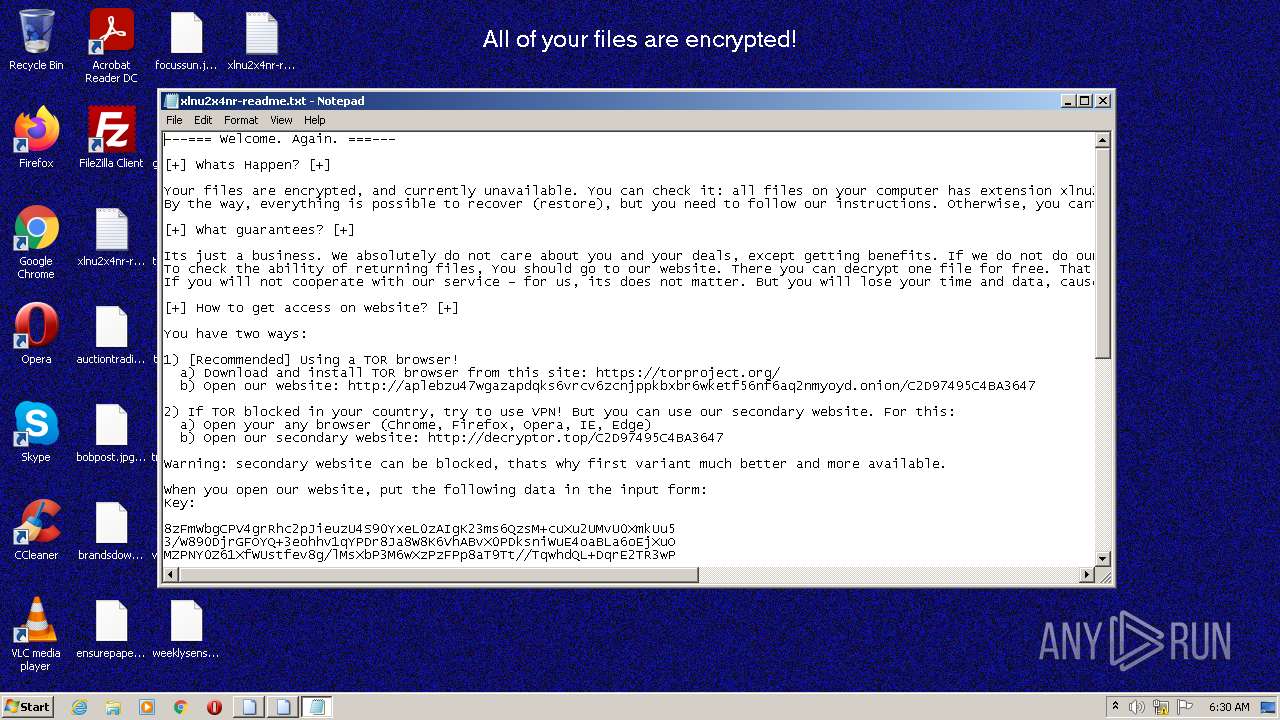
| 2684 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\Public\Desktop\xlnu2x4nr-readme.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3248 | C:\Windows\system32\wbem\unsecapp.exe -Embedding | C:\Windows\system32\wbem\unsecapp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Sink to receive asynchronous callbacks for WMI client application Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3768 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Local\Temp\dump1.bin.dll, #1 | C:\Windows\System32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4076 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 888
Read events
4 844
Write events
44
Delete events
0
Modification events
| (PID) Process: | (476) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (476) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (476) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (476) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3768) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\QtProject\OrganizationDefaults |
| Operation: | write | Name: | pvg |
Value: 84B6D6FA2B39341BA7265F47B9FF63DE6FC136A07E978CBCF88082E59367D41D | |||
| (PID) Process: | (3768) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\QtProject\OrganizationDefaults |
| Operation: | write | Name: | sxsP |
Value: 9ED4BDE233CAECC78FE25FE9A908CF9BD04CBD9A7EF8E78A7301B7123289CF70 | |||
| (PID) Process: | (3768) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\QtProject\OrganizationDefaults |
| Operation: | write | Name: | BDDC8 |
Value: 881C6673997138A972F3AAAEC12B67ED86D5B5E0BC8B40C54A62EC223F1EC61C3C5622390B0D280049F3E607CA9FBE8B7AE0911E28C091BE5999939B251A68590010BF09387A99D6A2DDC27BE248F258E4D140701DD0B7F8 | |||
| (PID) Process: | (3768) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\QtProject\OrganizationDefaults |
| Operation: | write | Name: | f7gVD7 |
Value: 5AEC26C93E112F645B1847624F765AF2B88B056F8729BB898BA79920953574C3D9C0C17D9623888EE800286040960C16F9167439B7F934C8A5A80777B1AB29EE0D6AB301354EF2171CB9CD52BDADCC4EA3EB51A15DA0F550 | |||
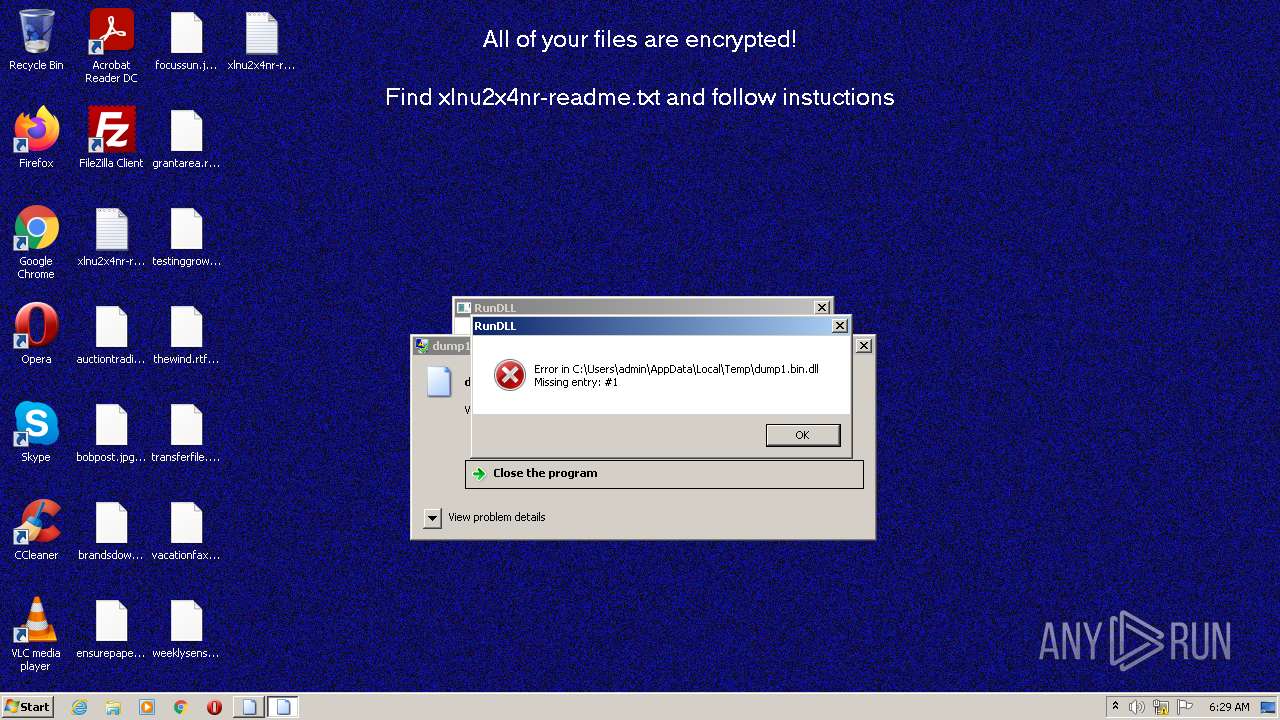
| (PID) Process: | (3768) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\QtProject\OrganizationDefaults |
| Operation: | write | Name: | Xu7Nnkd |
Value: .xlnu2x4nr | |||
| (PID) Process: | (3768) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\QtProject\OrganizationDefaults |
| Operation: | write | Name: | sMMnxpgk |
Value: F3316659B8023D5E20AD185CDA92627AECD4E12F7463178BD3300880ADB79ACE90CEC33E72E5EED9432F5345E6914BB9DFF5BCF740E3AC614E610FB77A8861BF5A983C3AFC25AF16F0AE9584006F5F43C392C9E25AE138A1A04B6BAA048D7B8E3193CD63467AD577D652CB5F7AFF20FE532C5DB3F733AC17CCFCC53E9F1A4FD4EDFFF4EAC217502FE0EAAC4D93477C0F59C461EAB1292B773161CED490B3B49F630894C30CFC33105D3FAAEAA1480E6894C00415F03521F490EC5B5C1769F710C1EC0F72561DA2241134420D2EEA8DA9E3367C4B37647148861210355A79B7CE9A1EFD37DD519536A5159A5648E65D821A82CD920673E12D60A9249E34531CAA84C72ABF5824A304139A9DE714AA688B78FB55FD2EE40FAC7C62F0301300D733BD8C8C44791B3D4E8B6D2677BB68075AFA58AB5747D481B0D259AD61AD1A85DB8007267984649C239C989E683149FCBCF1DC552FA0797AA2BC94FEBF4B357C2C2D6FFE37DE23651F8215461A099C9D26DA263B075983441D796D82C23C74CDF1E9F2294B517947216D6ADA2864F1166BEB8ABA674A373023B3A09AE14275CD92274BC0ABA6D8D0435AF536293E11770579BBC1AD96887329EA52152A3FC61CBA44B572445D66B829F598AF048EE695A11E4F526481BBF5F98A121C0F8FB74F4D6DA3244D1F6725B89221C867CDDE661ED0B67919D5F58BC28993FD60E2A01078AD9F41B4CC31206C140FA7F62A3CC532E535F805C7C3660AFE4262C29F7F69255D576E8FD72C32F93F0ACE83F07E434358ACD4003E014810B2C95B12BA9457EA3E3F5D5577CEF079F1BE867F7351ECC1D4829E1EAEDE6C9F21B4277CEE5B14CC474202749B1BF2D11CEFD5FD46A62E1479494BFDBB22E9B17A8D1D806A8FBB2147BD6920A6C2985407E71AA5CE1A7CD7C5D6CBD5B2B61E5D568DFC89089421B64F5848EDB71F32824542E6CD84B397A167C12414568D721E929DB8D4323736E95F09A59A570C0B755595B03A20B05206658F6C8425D825FDF49A51EEB259641FE70ED8A9CC54DB14523FB176543324E15308F764C33E1775F9C3B94435CA8B92B221DF83ADB2AC83E81F5D81A7269BB80A1958B1D31DED30EB5C25F3C950CFD728EC69281F6C7920DEA25AED0A56301A5F62DAB5D048ADE963E14473783F5F13E68B517BAB5E18899C4BBB4F88FDC688F707C19B95EB70E43D6BA8794594270E8885CA03493CEA098FC5C60C12E45068 | |||
Executable files
0
Suspicious files
258
Text files
4
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | rundll32.exe | C:\program files\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
| 3768 | rundll32.exe | C:\recovery\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
| 3768 | rundll32.exe | C:\users\admin\favorites\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
| 3768 | rundll32.exe | C:\users\admin\.oracle_jre_usage\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
| 3768 | rundll32.exe | C:\users\administrator\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
| 3768 | rundll32.exe | C:\users\default\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
| 3768 | rundll32.exe | C:\users\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
| 3768 | rundll32.exe | C:\users\admin\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
| 3768 | rundll32.exe | C:\recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
| 3768 | rundll32.exe | C:\users\public\xlnu2x4nr-readme.txt | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
36
DNS requests
30
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3768 | rundll32.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d1596c48ccff360f | US | compressed | 60.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3768 | rundll32.exe | 35.213.151.161:443 | trainiumacademy.com | GOOGLE | SG | suspicious |
3768 | rundll32.exe | 50.87.236.3:443 | mindsparkescape.com | UNIFIEDLAYER-AS-1 | US | suspicious |
3768 | rundll32.exe | 5.79.100.182:443 | molade.nl | LeaseWeb Netherlands B.V. | NL | suspicious |
— | — | 149.210.170.218:443 | artvark.nl | Signet B.V. | NL | suspicious |
3768 | rundll32.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
3768 | rundll32.exe | 77.72.4.226:443 | georgemuncey.com | Krystal Hosting Ltd | GB | malicious |
3768 | rundll32.exe | 172.67.193.13:443 | gaearoyals.com | CLOUDFLARENET | US | suspicious |
3768 | rundll32.exe | 94.231.103.59:443 | arthakapitalforvaltning.dk | team.blue Denmark A/S | DK | suspicious |
3768 | rundll32.exe | 162.241.244.73:443 | girlish.ae | UNIFIEDLAYER-AS-1 | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
gaearoyals.com |
| unknown |
georgemuncey.com |
| malicious |
arthakapitalforvaltning.dk |
| suspicious |
placermonticello.com |
| suspicious |
pourlabretagne.bzh |
| suspicious |
daveystownhouse.com |
| suspicious |
gavelmasters.com |
| whitelisted |
descargandoprogramas.com |
| malicious |
trainiumacademy.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3768 | rundll32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |