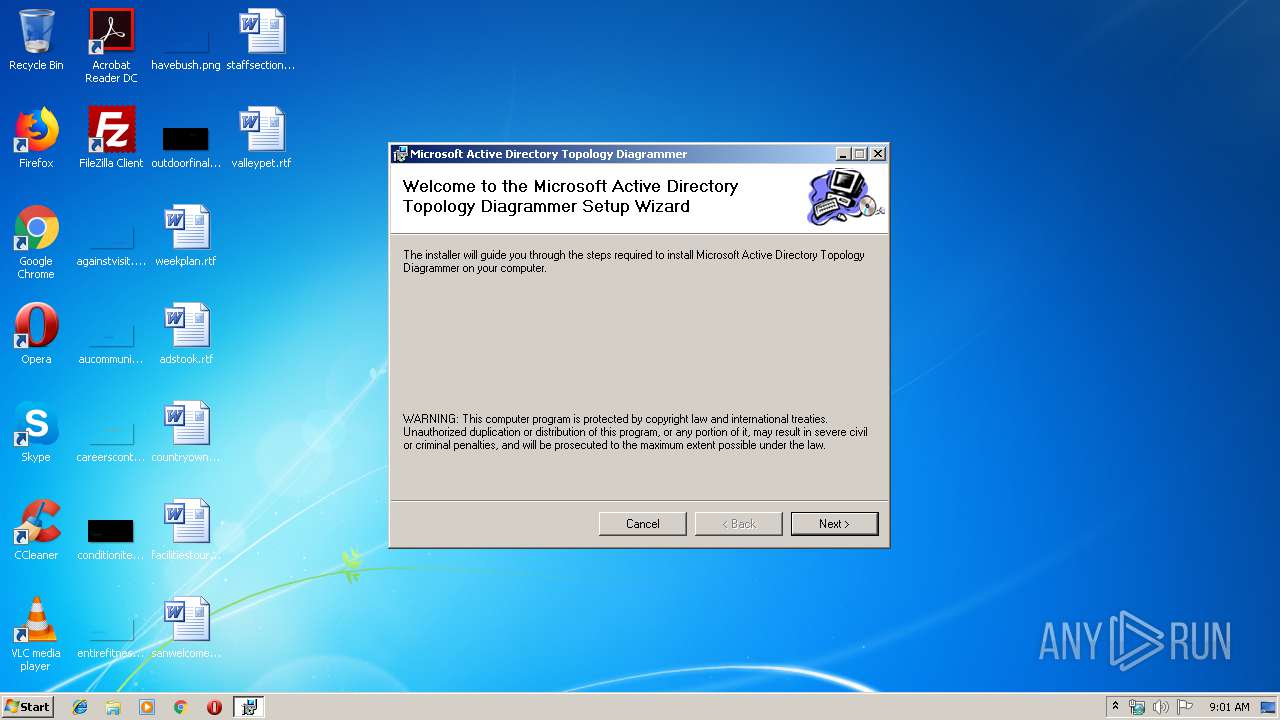
| File name: | ADTD.Net Setup.msi |
| Full analysis: | https://app.any.run/tasks/3277daa4-076a-4d18-ad62-df5c793851a6 |
| Verdict: | Malicious activity |
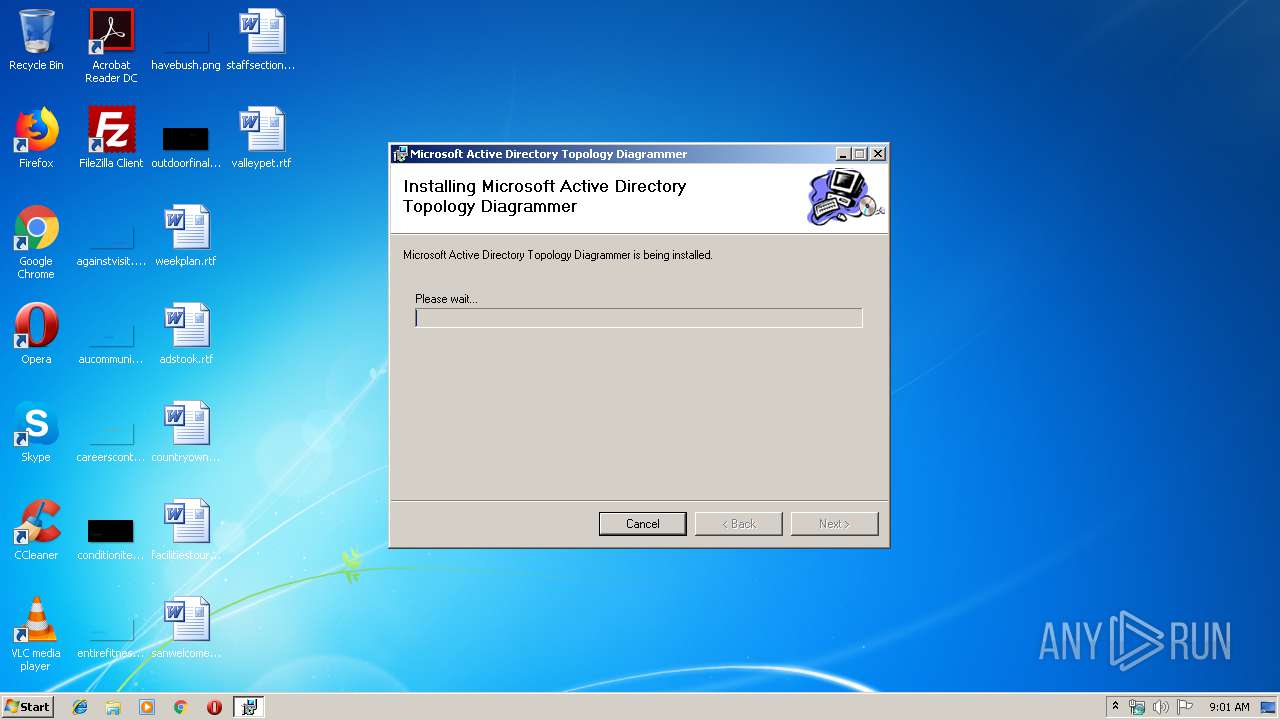
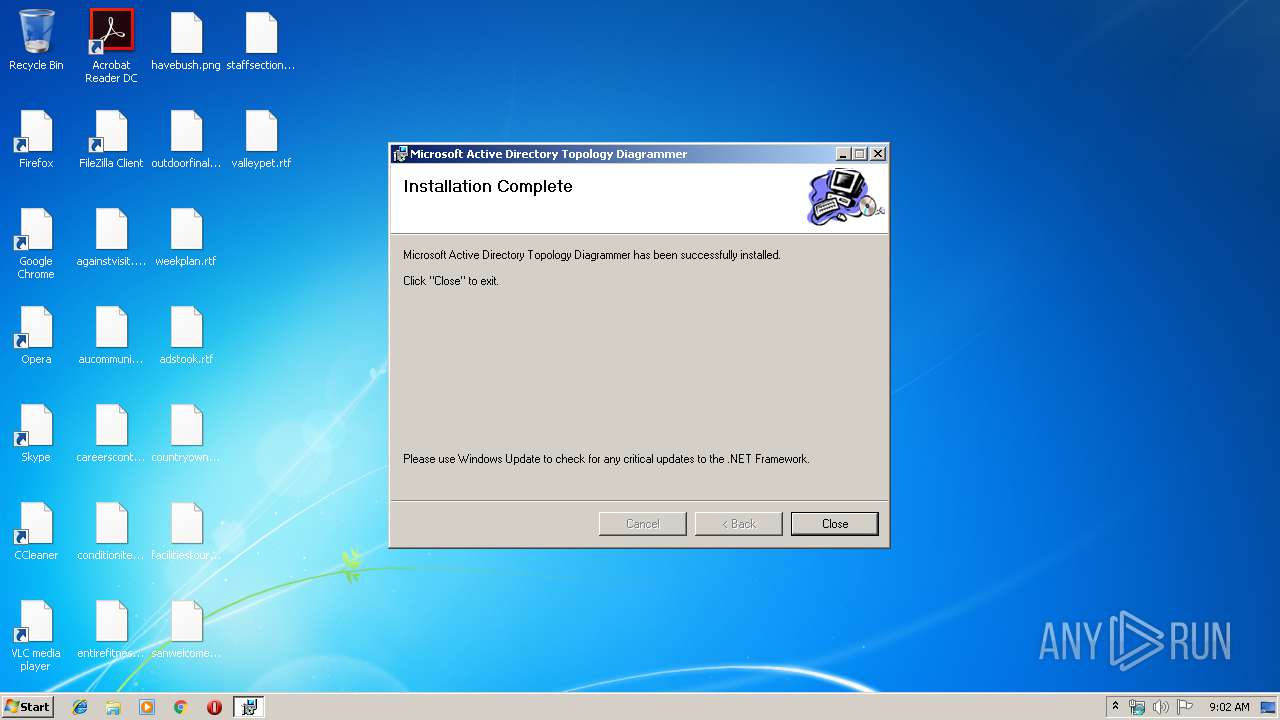
| Analysis date: | March 21, 2019, 09:01:07 |
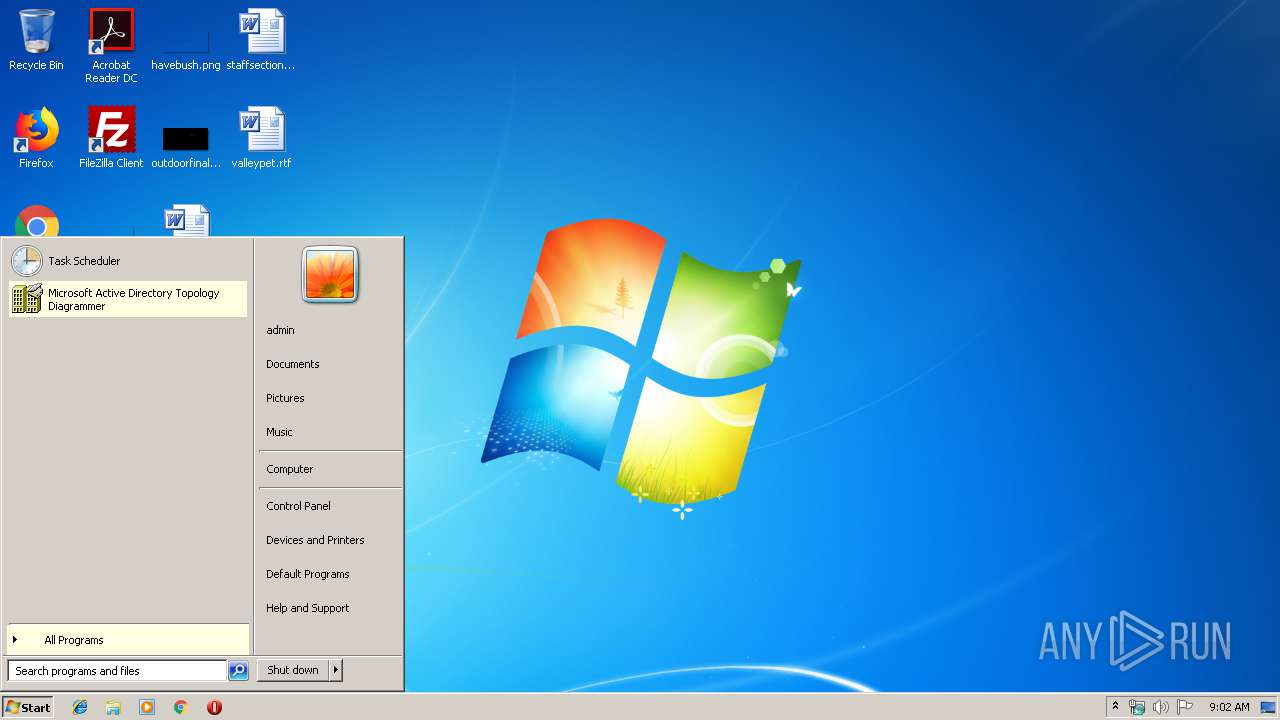
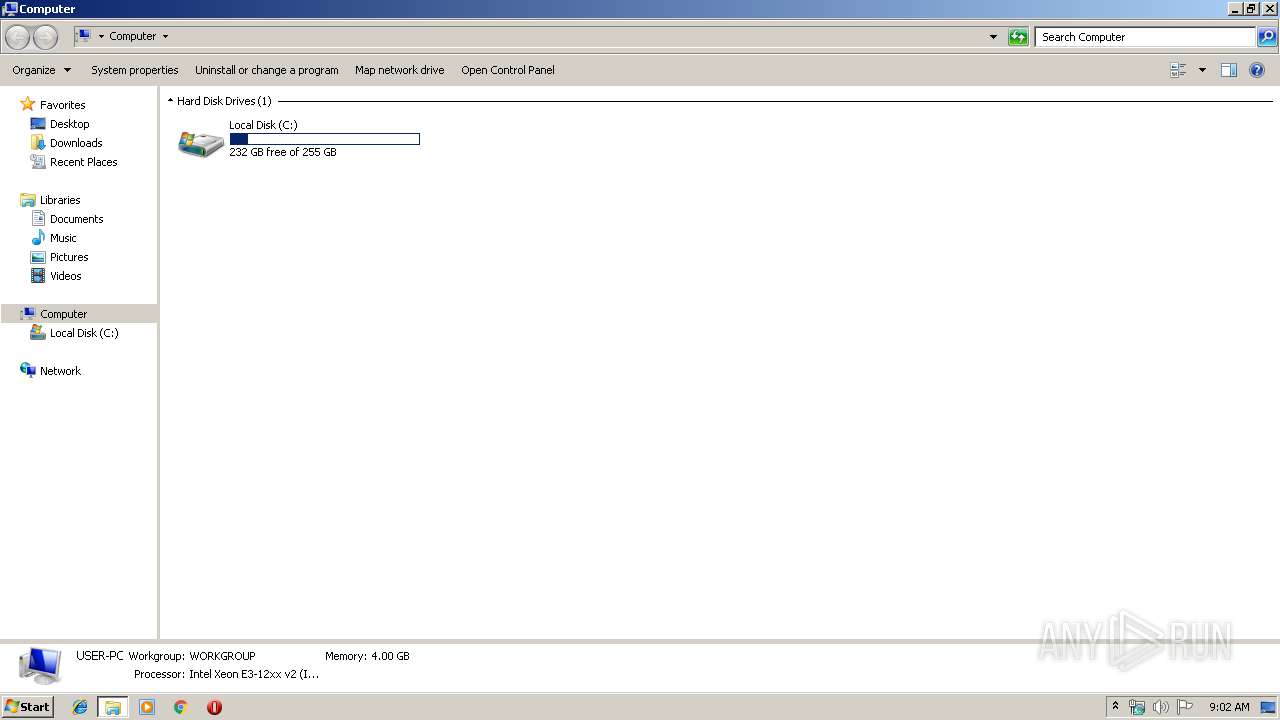
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
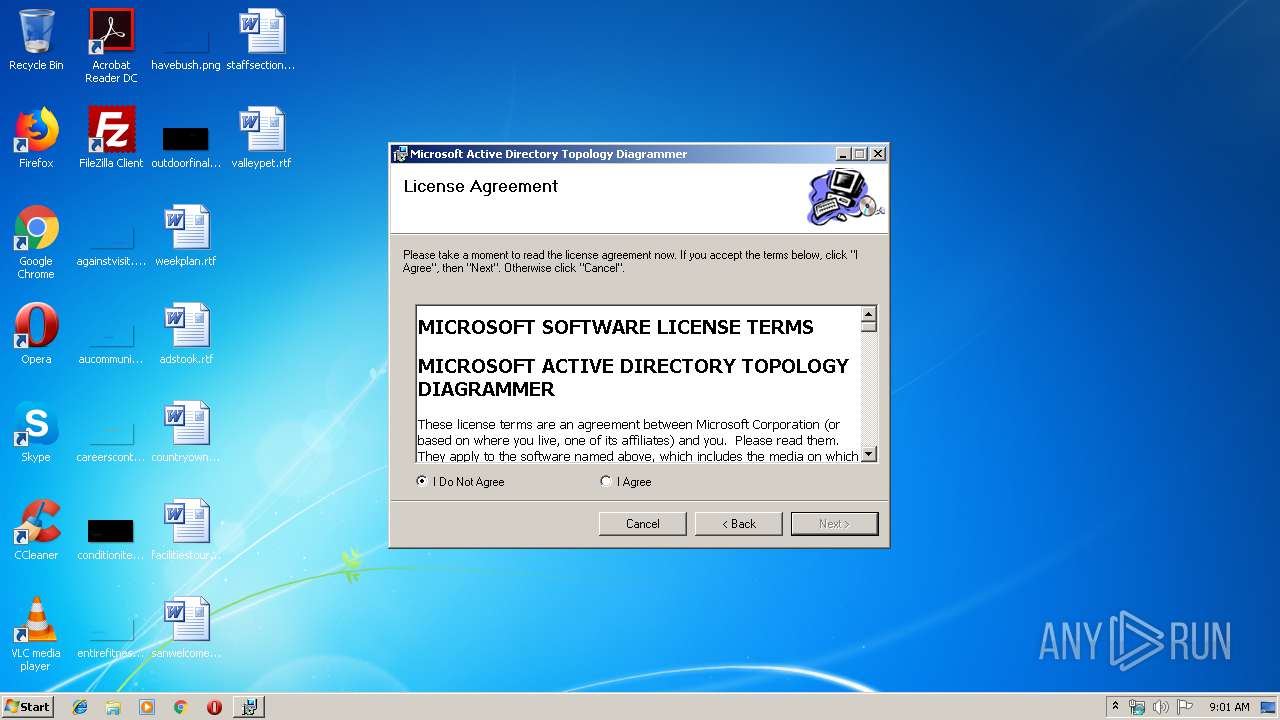
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 5.2, MSI Installer, Create Time/Date: Mon Jun 21 08:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: Intel;1033, Number of Pages: 200, Revision Number: {E635A1BC-3A3D-4CDB-828B-FA8E922A0833}, Title: Active Directory Topology Diagrammer, Author: Microsoft Corporation, Keywords: ADTD, Comments: Make your Microsoft Active Directory configuration visible in Microsoft Visio, Number of Words: 2, Last Saved Time/Date: Tue May 10 10:41:19 2011, Last Printed: Tue May 10 10:41:19 2011 |
| MD5: | EF9A1ACA99082FA0970095A150B9B55A |
| SHA1: | C5D51F2B400FD41EC13905ABAA08A41E9B842CD7 |
| SHA256: | ED3F6222704691F8E826F63334EA161E1316FE78E38EB594286BF2DFD16895FF |
| SSDEEP: | 24576:lpFG1n9AGyKfeefIN8bYtSF1A8BV0gmaIPFlL:lpFG19zfe8IMY8Fy8B5MF1 |
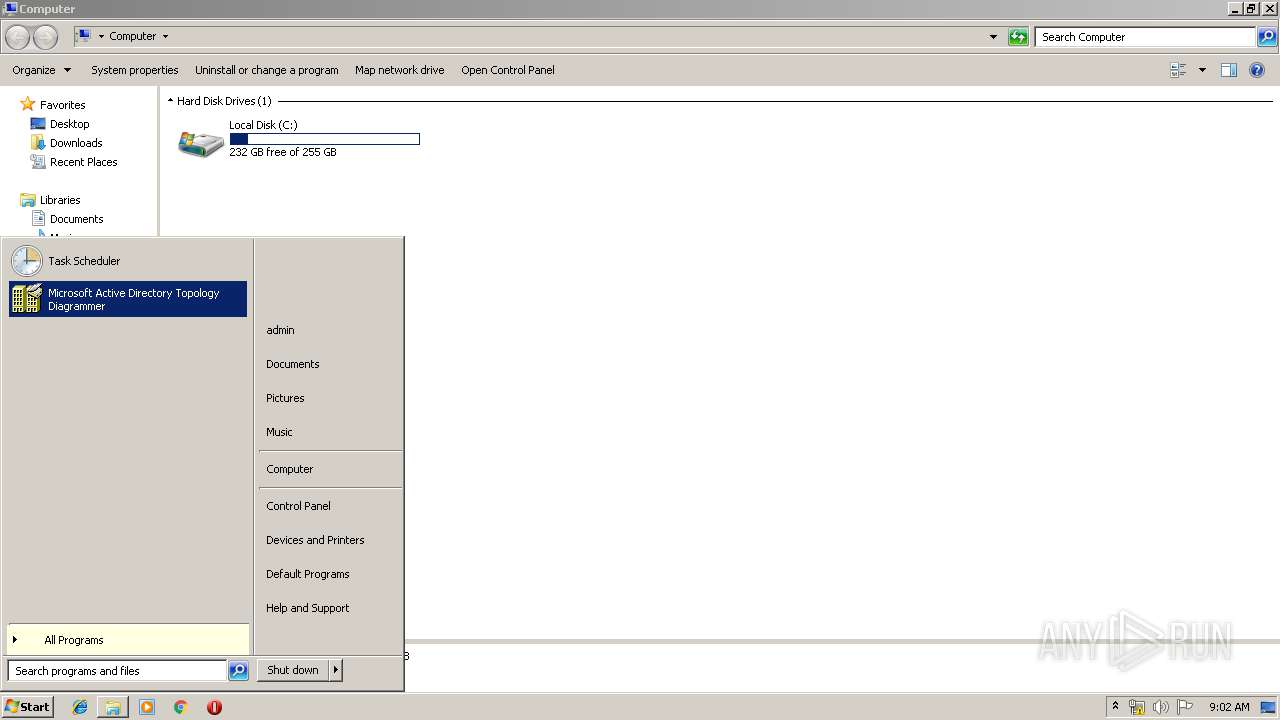
MALICIOUS
Application was dropped or rewritten from another process
- ADTD.exe (PID: 3272)
- ADTD.exe (PID: 3412)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 2096)
INFO
Searches for installed software
- msiexec.exe (PID: 2096)
Application launched itself
- msiexec.exe (PID: 2096)
Low-level read access rights to disk partition
- vssvc.exe (PID: 396)
Changes settings of System certificates
- DrvInst.exe (PID: 332)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 332)
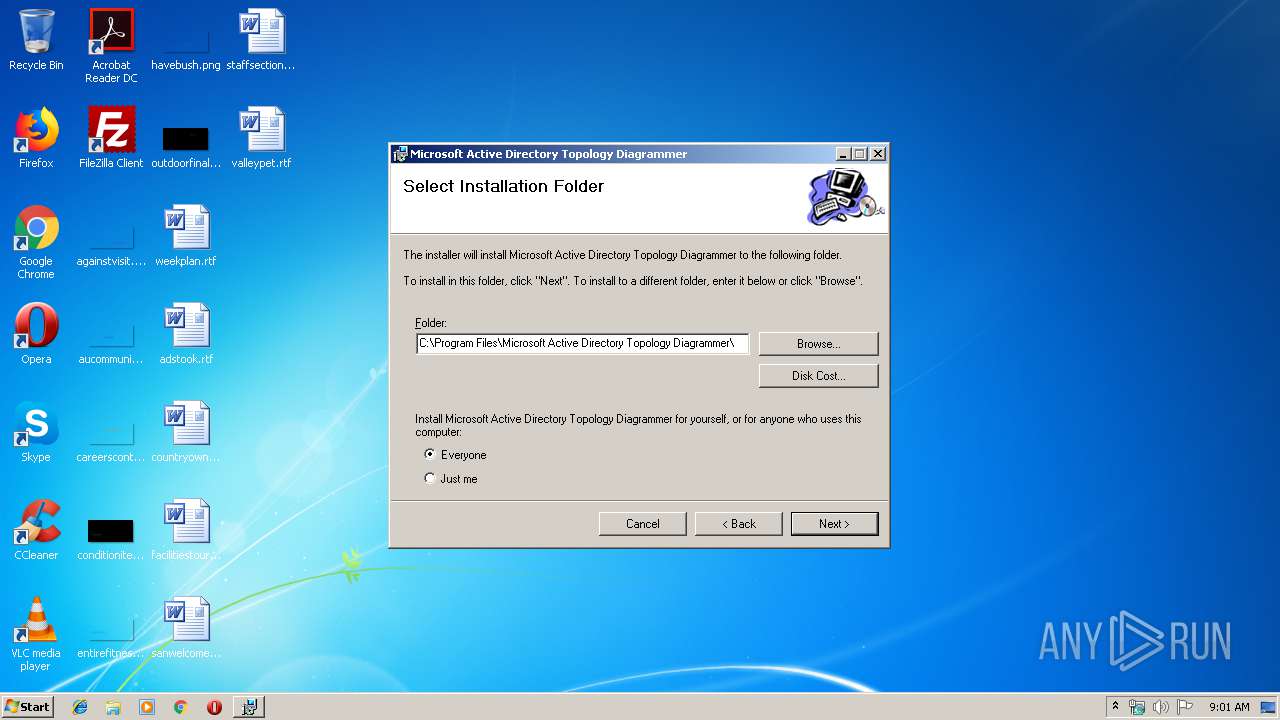
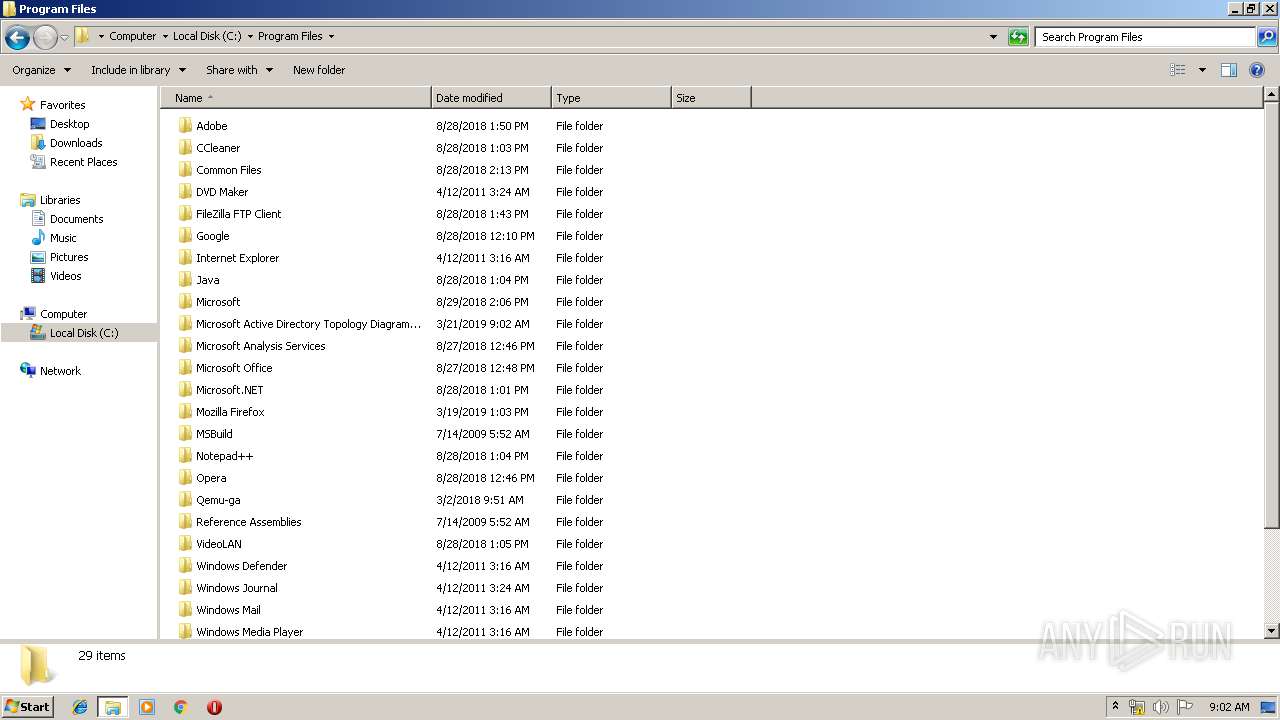
Creates files in the program directory
- msiexec.exe (PID: 2096)
Creates a software uninstall entry
- msiexec.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
| Pages: | 200 |
| RevisionNumber: | {E635A1BC-3A3D-4CDB-828B-FA8E922A0833} |
| Title: | Active Directory Topology Diagrammer |
| Subject: | - |
| Author: | Microsoft Corporation |
| Keywords: | ADTD |
| Comments: | Make your Microsoft Active Directory configuration visible in Microsoft Visio |
| Words: | 2 |
| ModifyDate: | 2011:05:10 09:41:19 |
| LastPrinted: | 2011:05:10 09:41:19 |
Total processes
41
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "00000398" "000005C4" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 360 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ADTD.Net Setup.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 396 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
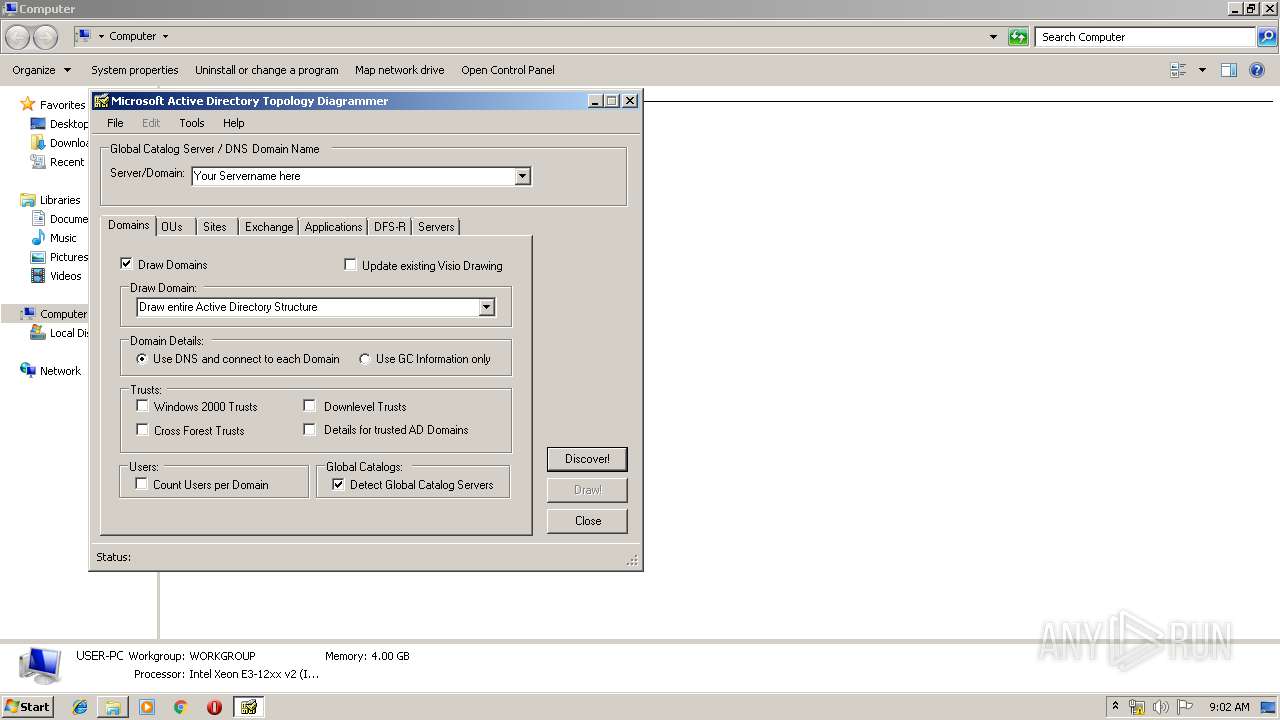
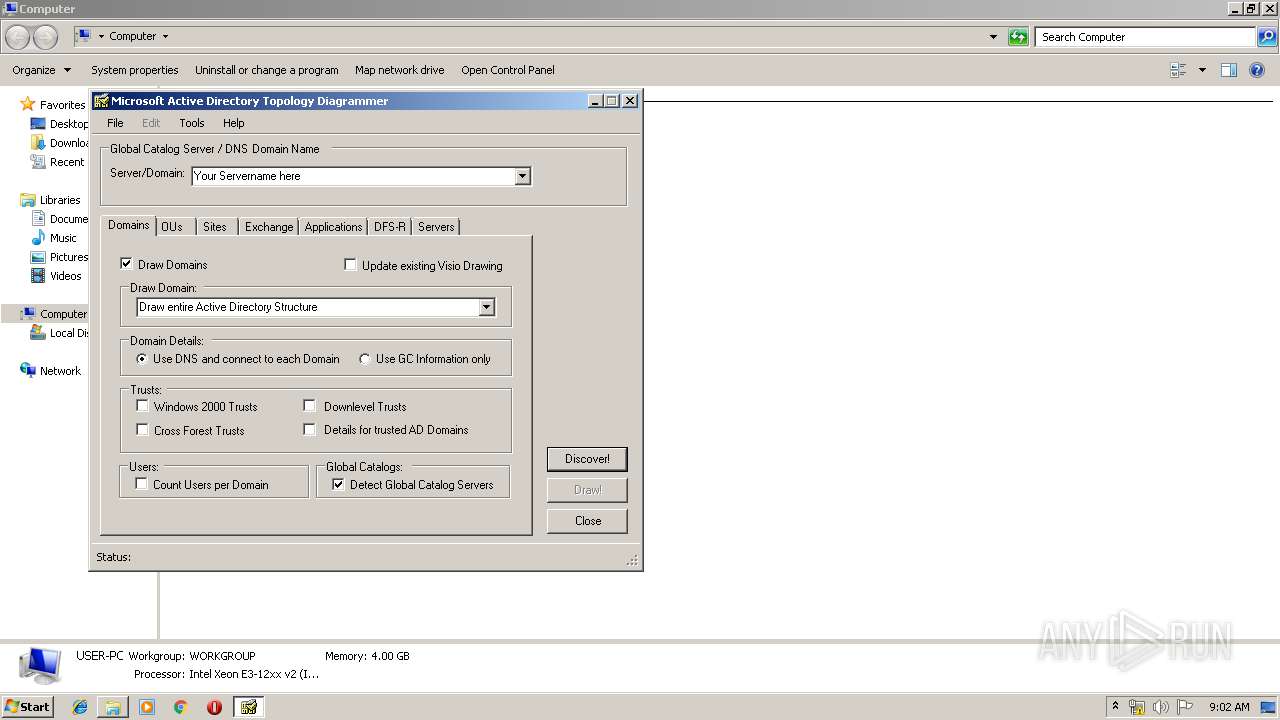
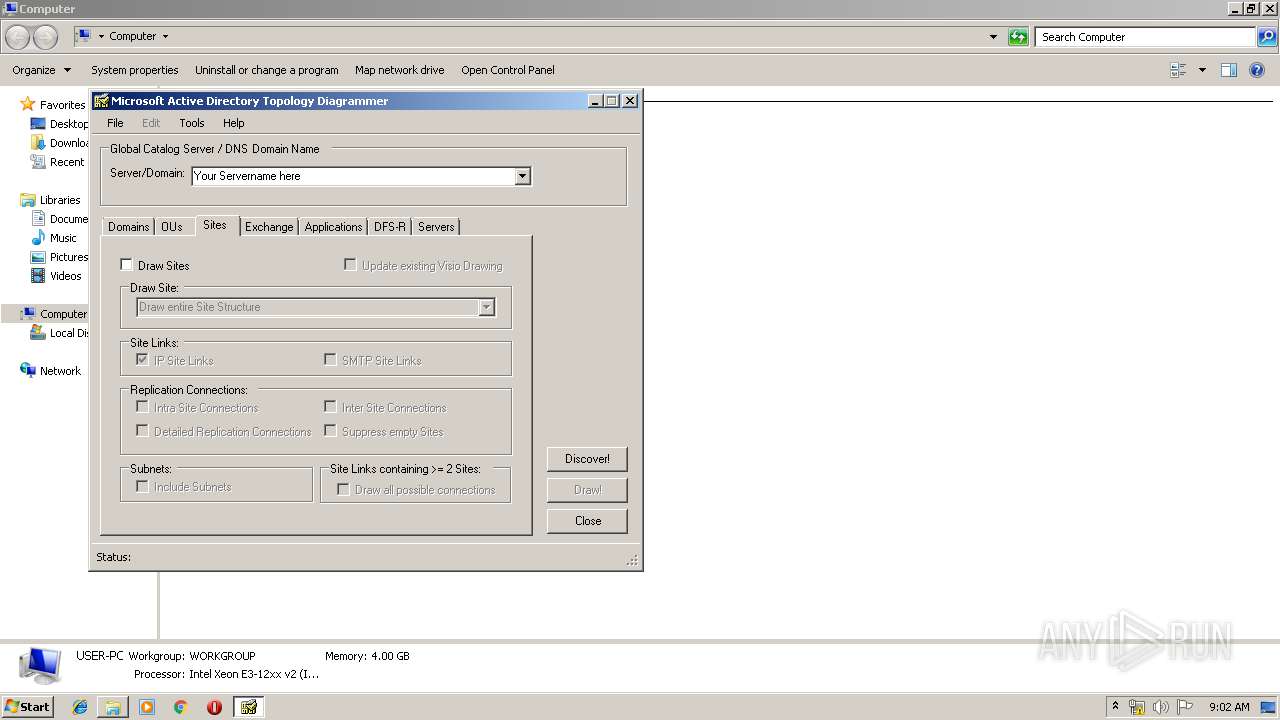
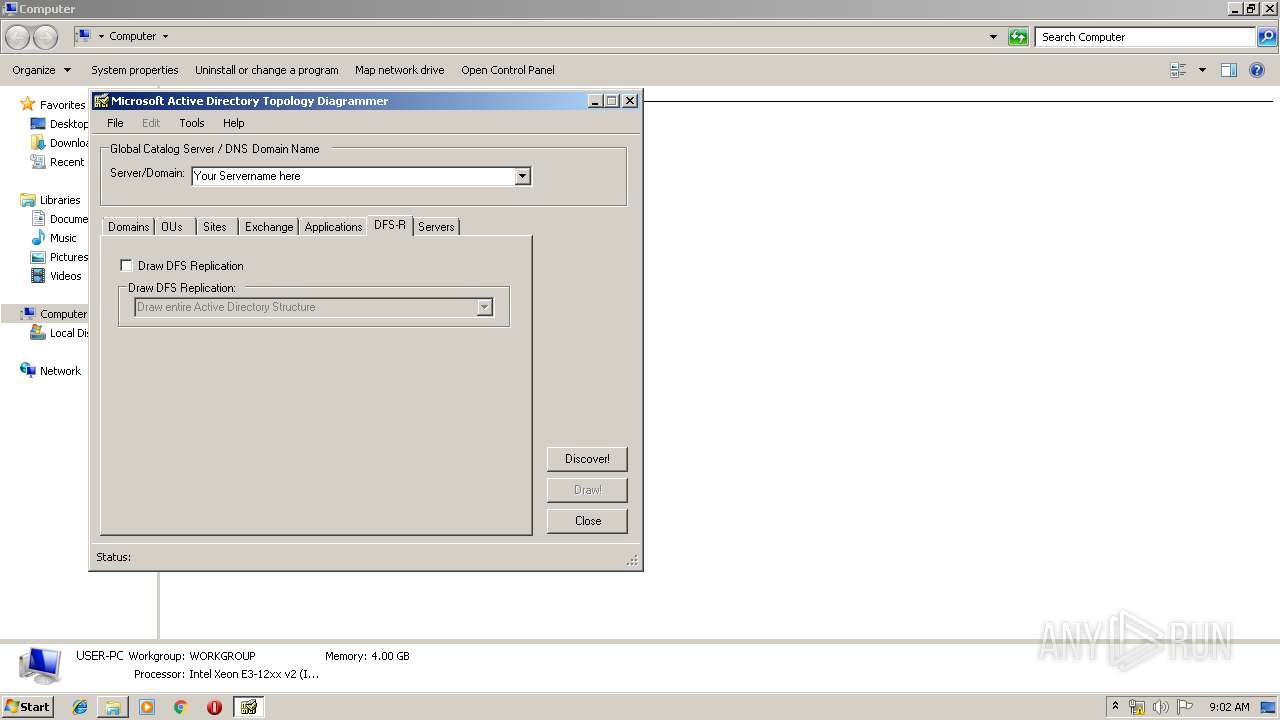
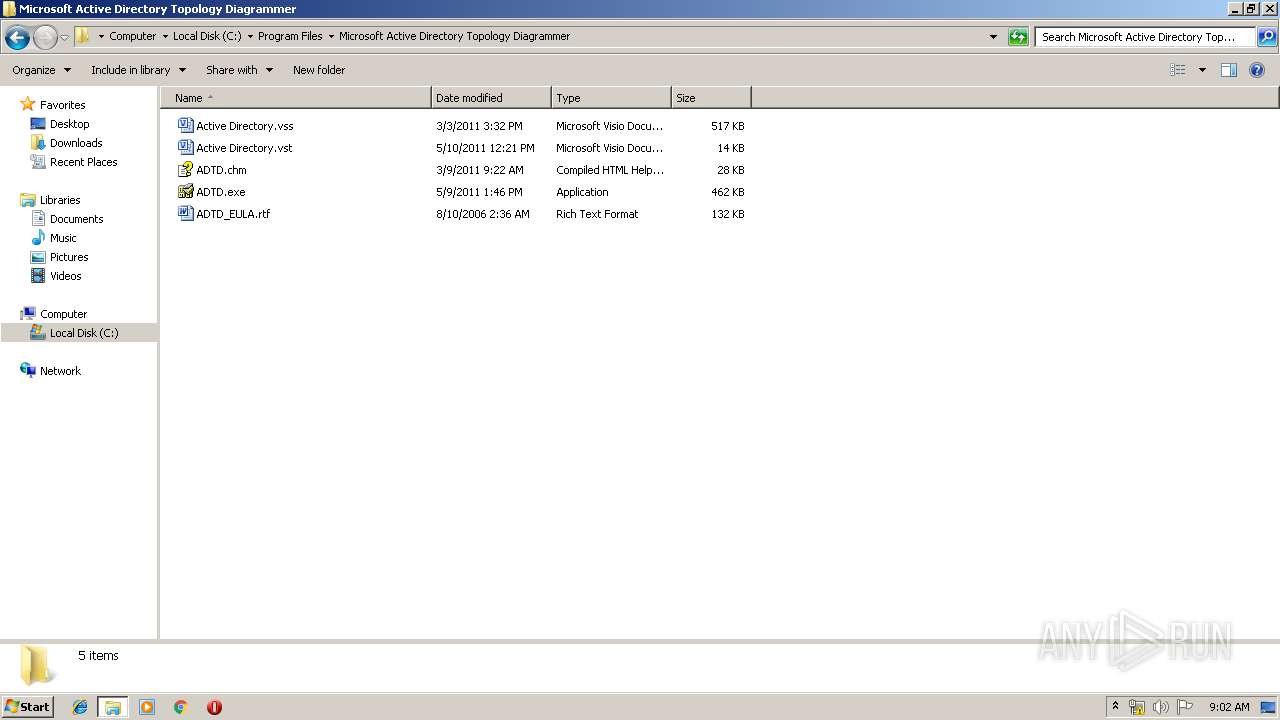
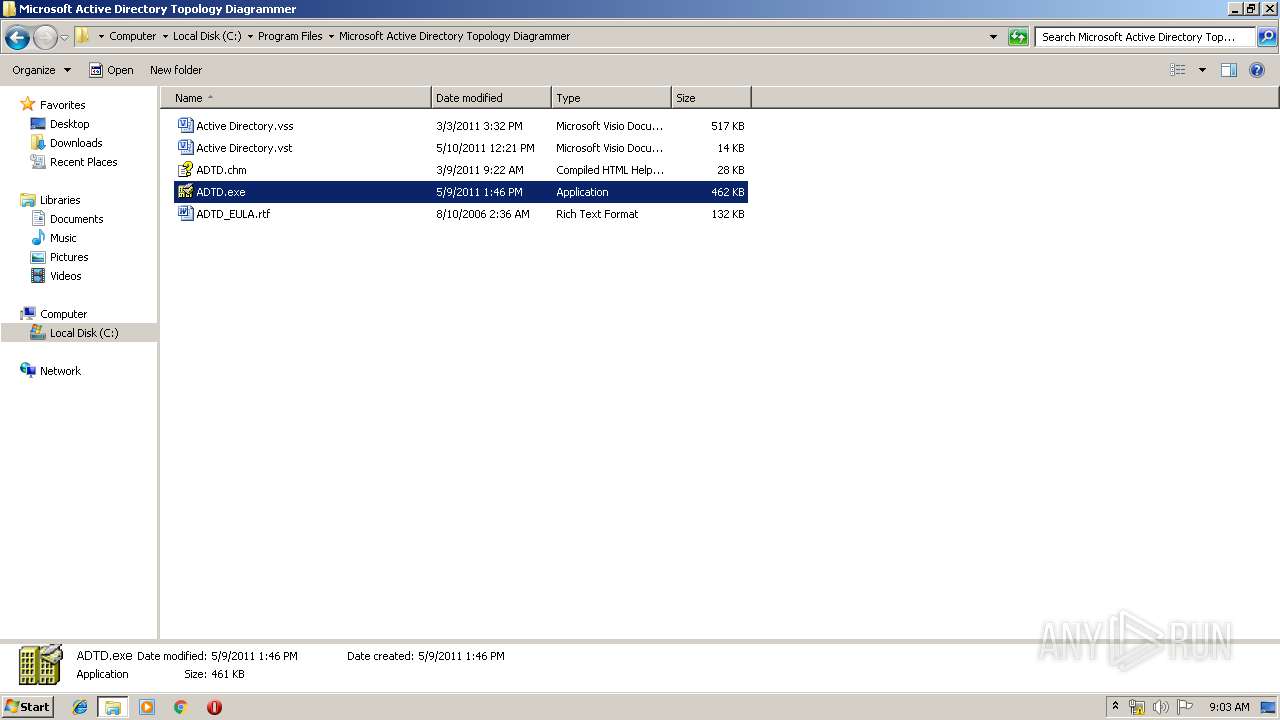
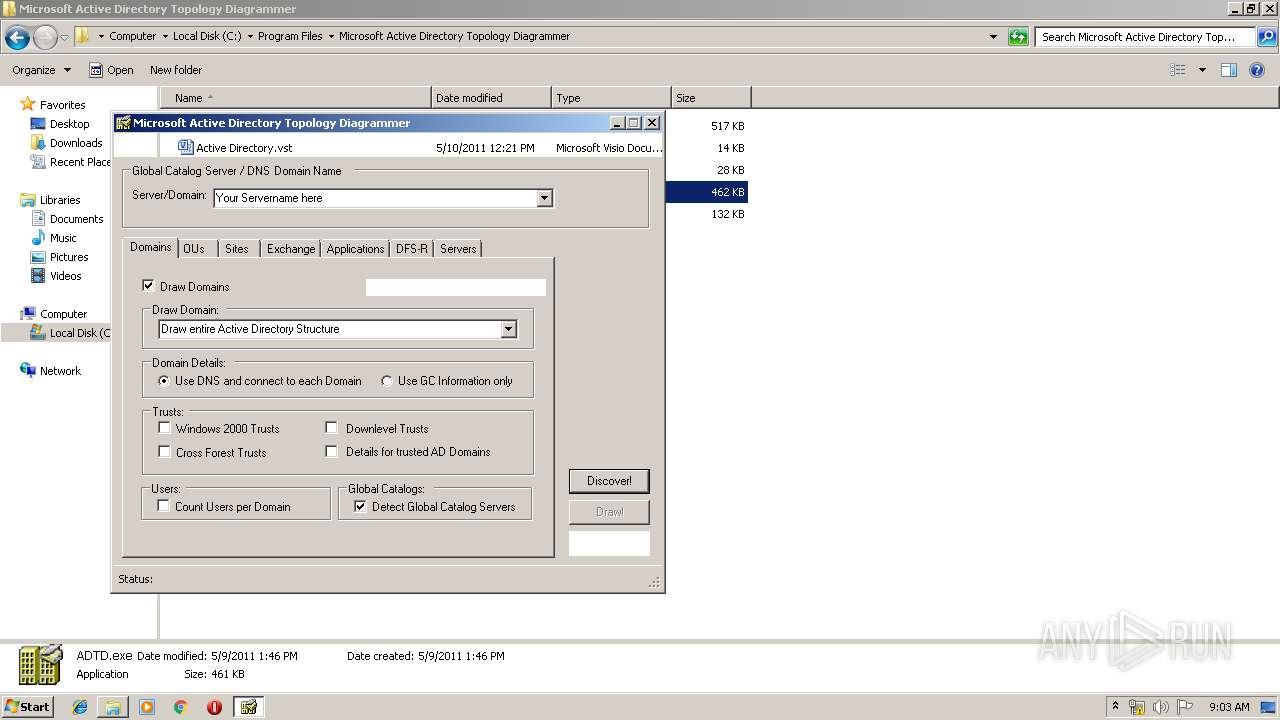
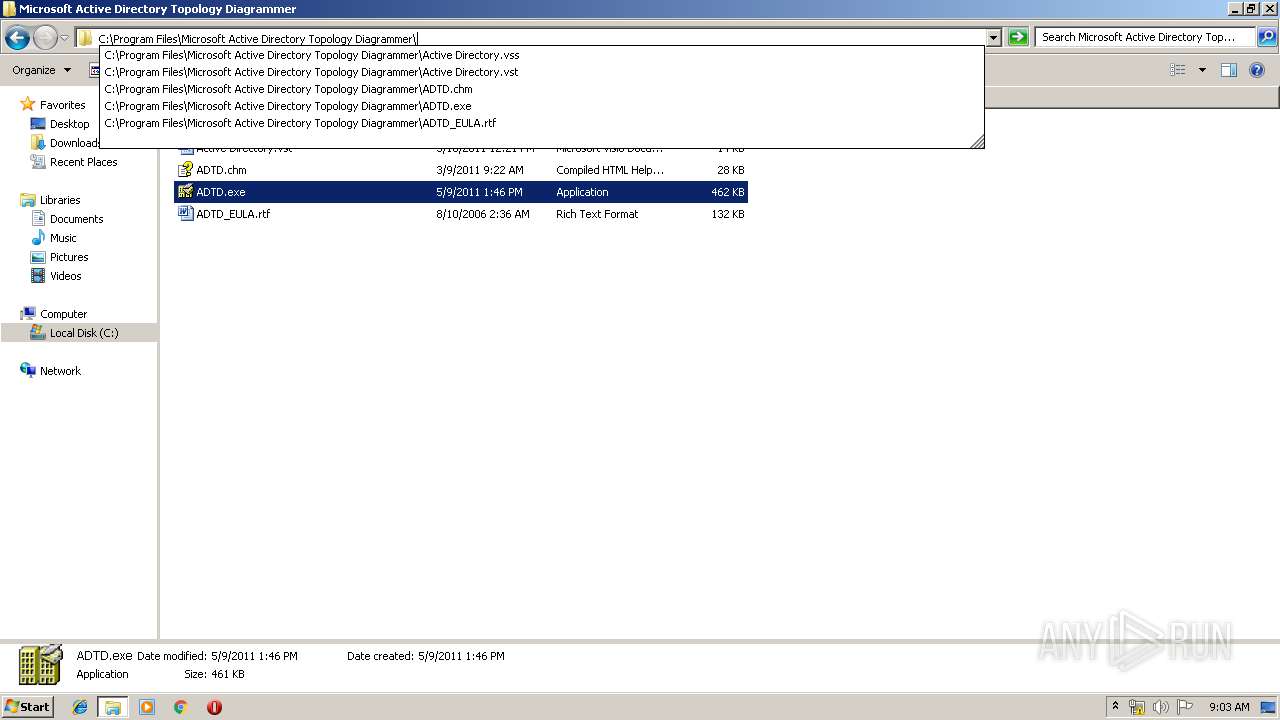
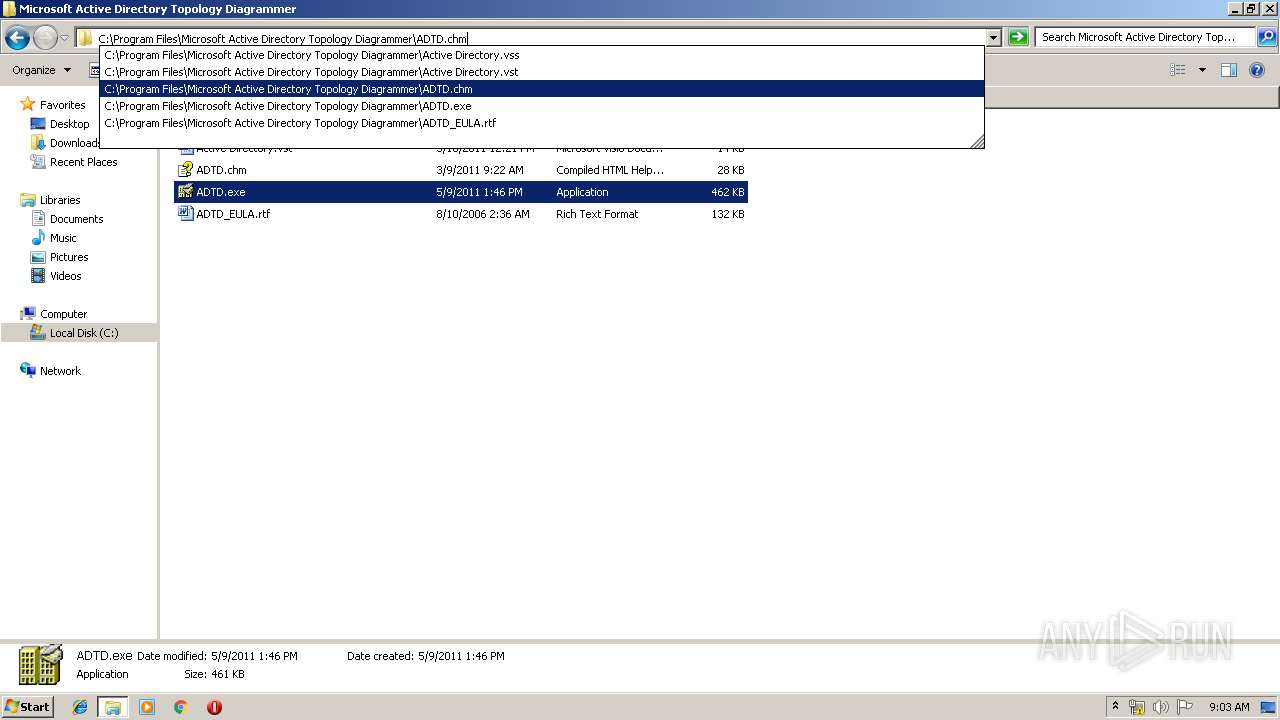
| 3272 | "C:\Program Files\Microsoft Active Directory Topology Diagrammer\ADTD.exe" | C:\Program Files\Microsoft Active Directory Topology Diagrammer\ADTD.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Active Directory Topology Diagrammer Exit code: 0 Version: 2.2.4146.20801 Modules
| |||||||||||||||
| 3316 | C:\Windows\system32\MsiExec.exe -Embedding A754C127F4D7A58C495920AA57DC81D9 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3412 | "C:\Program Files\Microsoft Active Directory Topology Diagrammer\ADTD.exe" | C:\Program Files\Microsoft Active Directory Topology Diagrammer\ADTD.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Active Directory Topology Diagrammer Exit code: 0 Version: 2.2.4146.20801 Modules
| |||||||||||||||
| 3760 | C:\Windows\system32\MsiExec.exe -Embedding 5FAD641CDFE9F8A8C2037D995FF3D991 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
731
Read events
435
Write events
284
Delete events
12
Modification events
| (PID) Process: | (360) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2096) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000007CE42FB8C4DFD40130080000F0050000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2096) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000D64632B8C4DFD40130080000F0050000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2096) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (2096) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000005C55A2B8C4DFD40130080000F0050000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2096) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B6B7A4B8C4DFD401300800007C070000E80300000100000000000000000000003296C224BCA17D418A82675FB92E1B900000000000000000 | |||
| (PID) Process: | (396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D205B3B8C4DFD4018C0100004C070000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D205B3B8C4DFD4018C010000380B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D205B3B8C4DFD4018C010000A8070000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D205B3B8C4DFD4018C0100003C0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
7
Text files
96
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 360 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIA128.tmp | — | |
MD5:— | SHA256:— | |||
| 360 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIA1D5.tmp | — | |
MD5:— | SHA256:— | |||
| 2096 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2096 | msiexec.exe | C:\Windows\Installer\MSI2146.tmp | — | |
MD5:— | SHA256:— | |||
| 2096 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFA217458AEDEC7197.TMP | — | |
MD5:— | SHA256:— | |||
| 2096 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 396 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2096 | msiexec.exe | C:\Config.Msi\101b2d.rbs | — | |
MD5:— | SHA256:— | |||
| 2096 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFC6275F4300E15C9D.TMP | — | |
MD5:— | SHA256:— | |||
| 332 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report