| File name: | Instagram Get Phone Pro.exe |
| Full analysis: | https://app.any.run/tasks/0e01611e-c152-4449-9250-3ab009fabb29 |
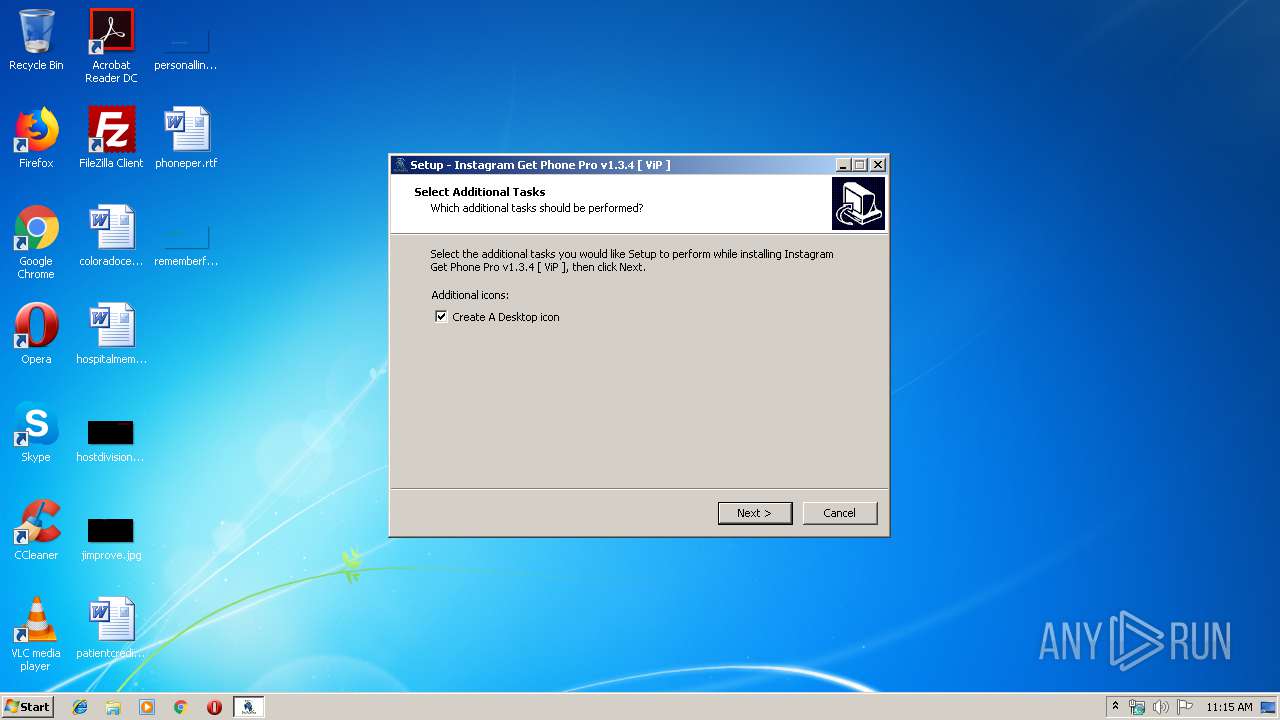
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 11:14:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E49FF0FF925124F181230B69426F24DF |
| SHA1: | FBB3447174B1233923A57F329EA117516945D467 |
| SHA256: | ED3CA404B99902DD21D95F11FE973405A8B0685070EFC460B60B50C203112835 |
| SSDEEP: | 49152:DyG3D1srArW8m4fedQdR5ZJcKc2g/broBS2Y3Ac2Hh4TZlT:+01chAzZTcZbeS2cqqPT |
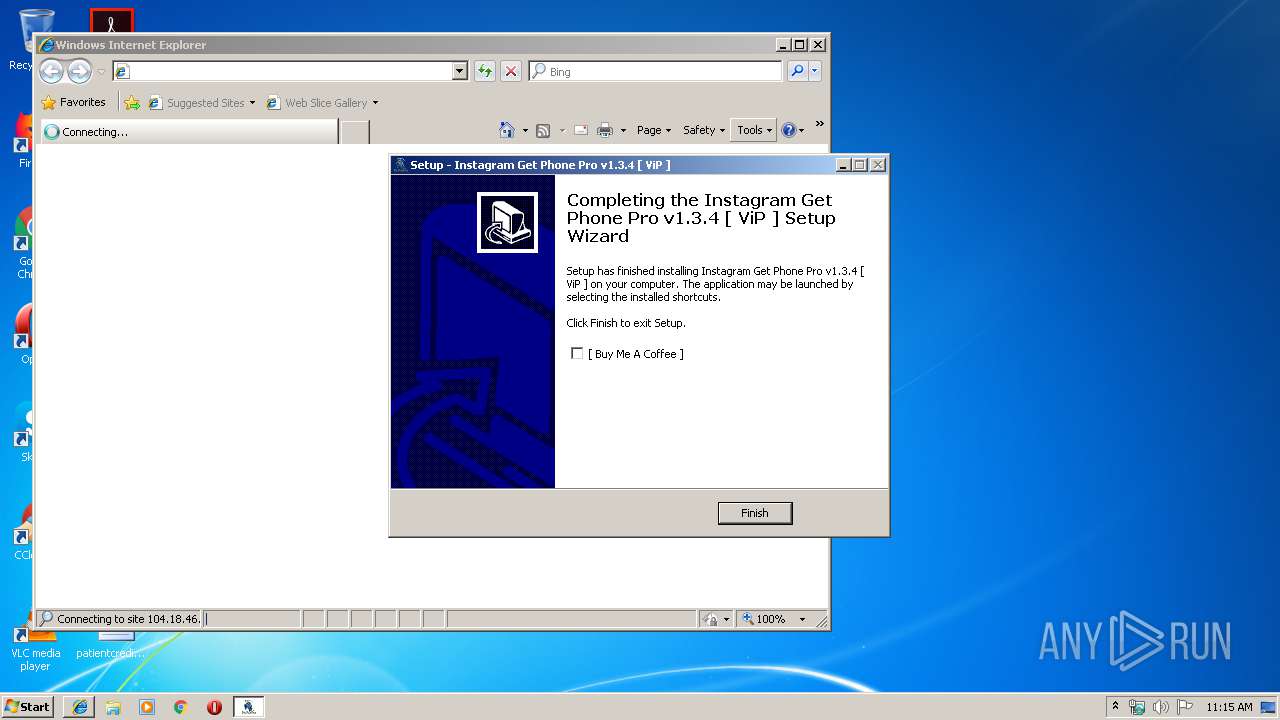
MALICIOUS
Application was dropped or rewritten from another process
- Instagram Get Phone Pro.exe (PID: 3632)
SUSPICIOUS
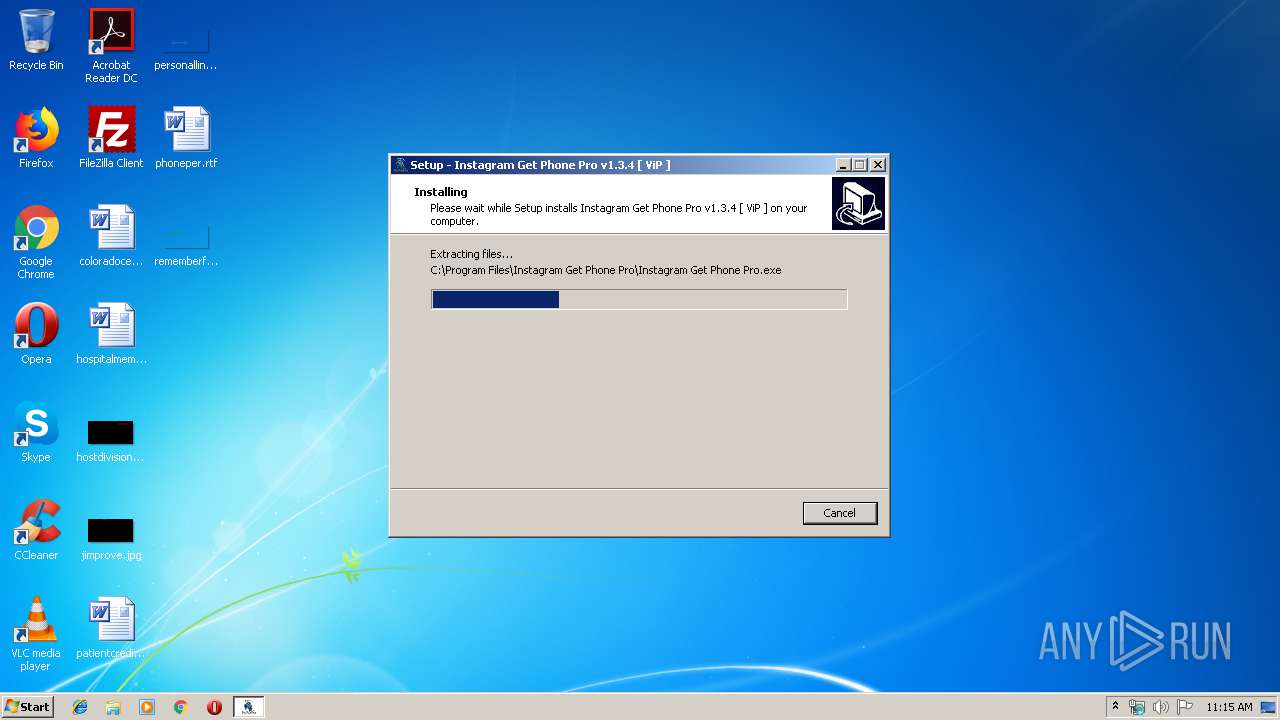
Executable content was dropped or overwritten
- Instagram Get Phone Pro.exe (PID: 3752)
- Instagram Get Phone Pro.tmp (PID: 1768)
- Instagram Get Phone Pro.exe (PID: 2772)
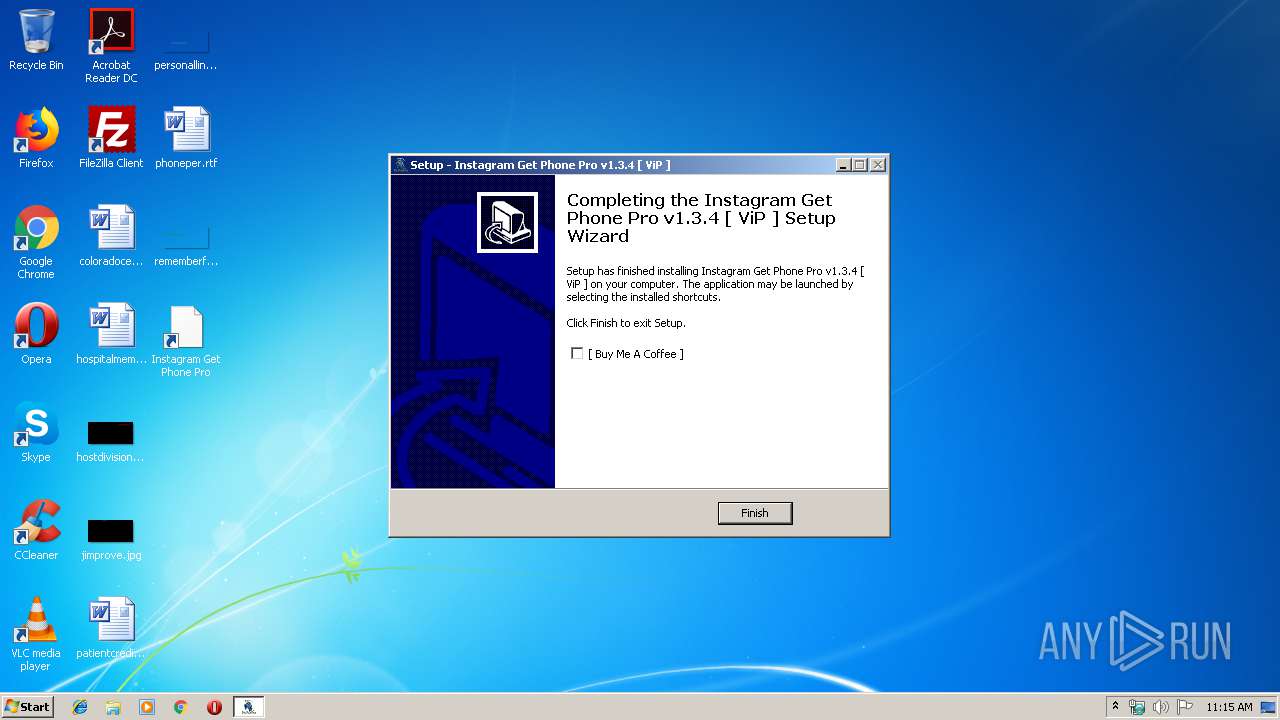
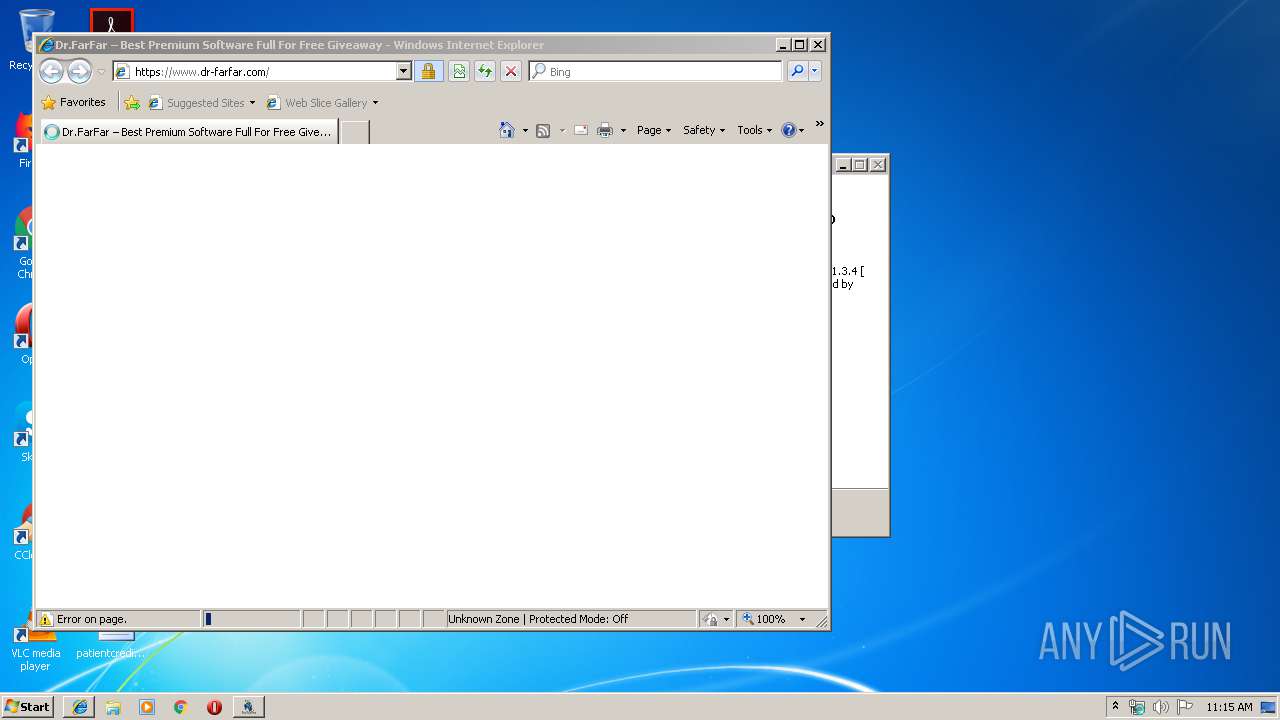
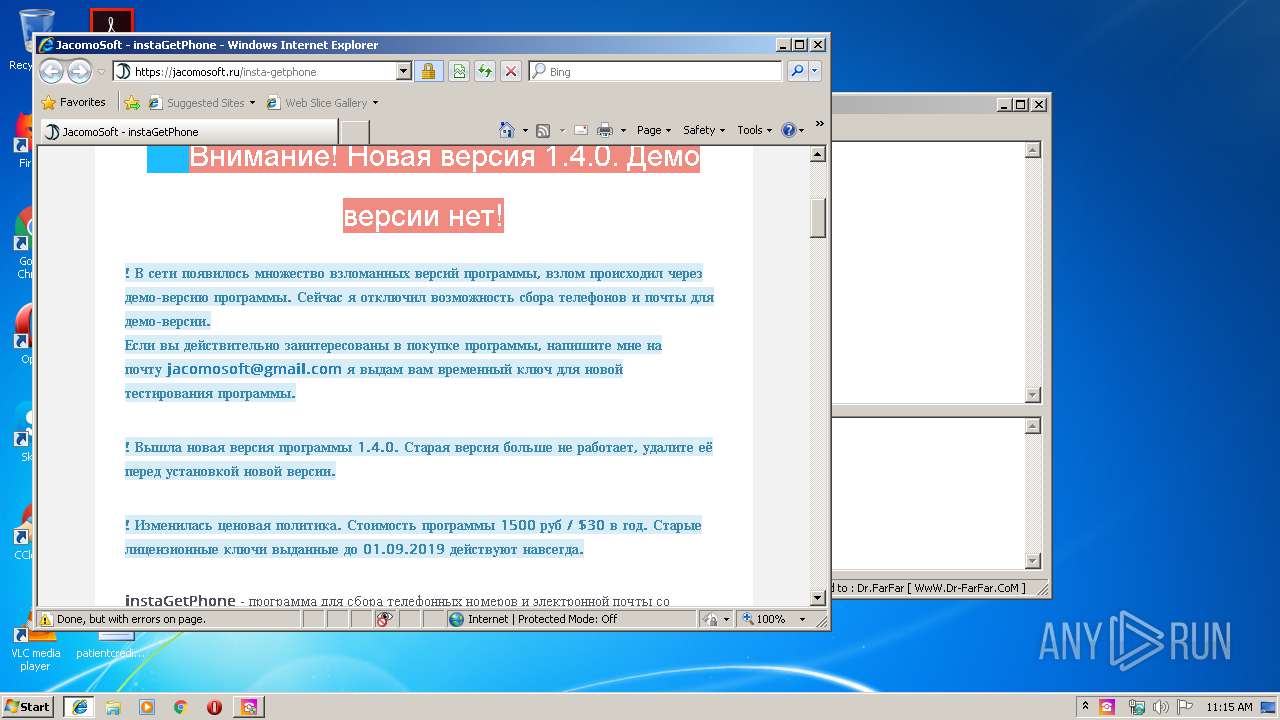
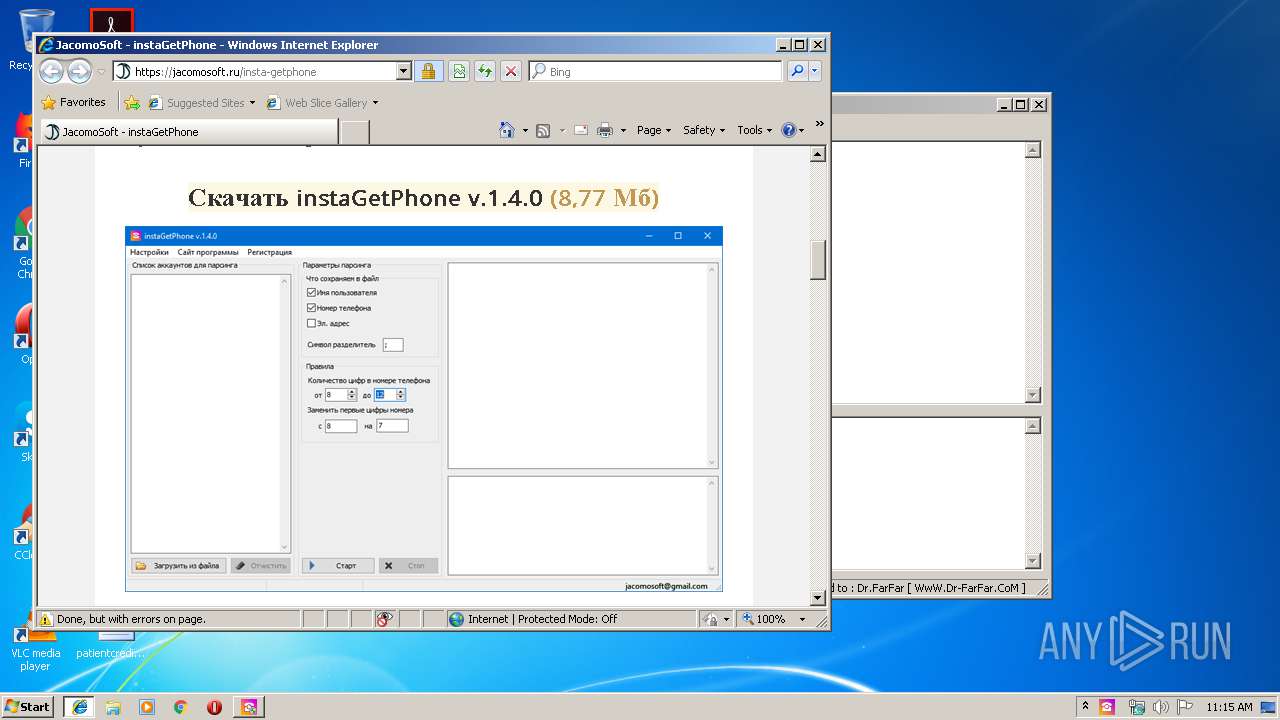
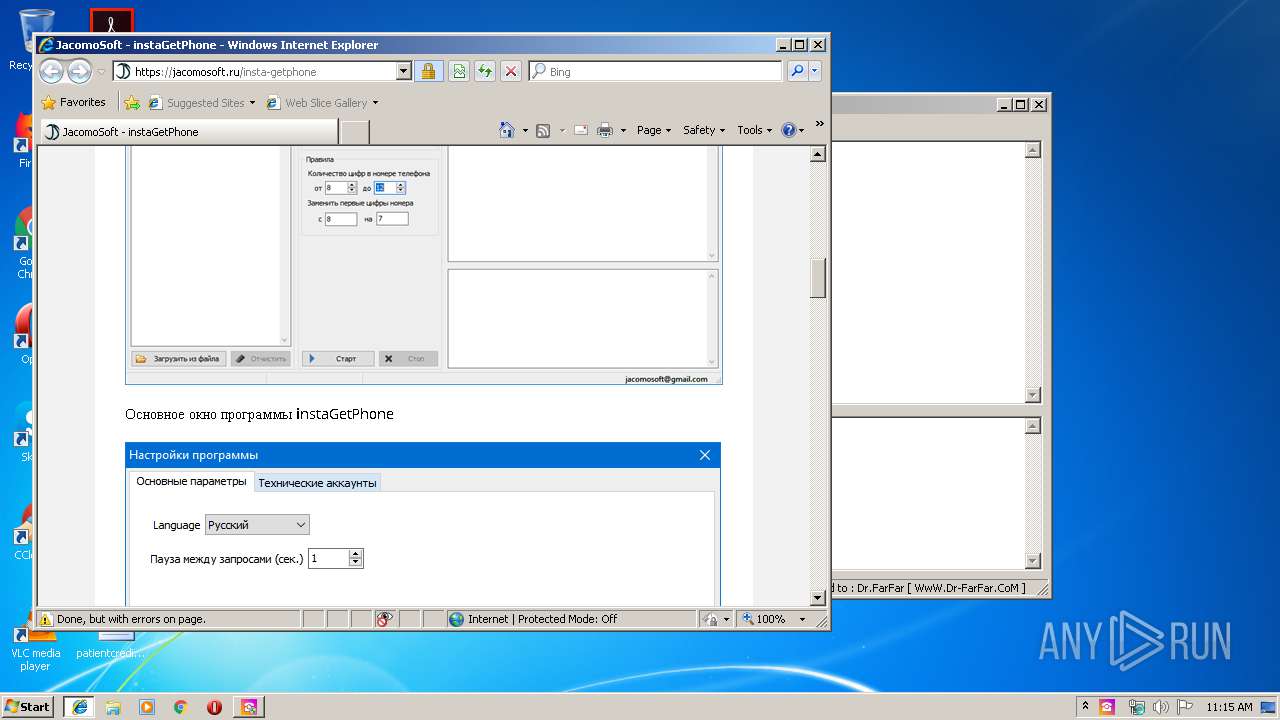
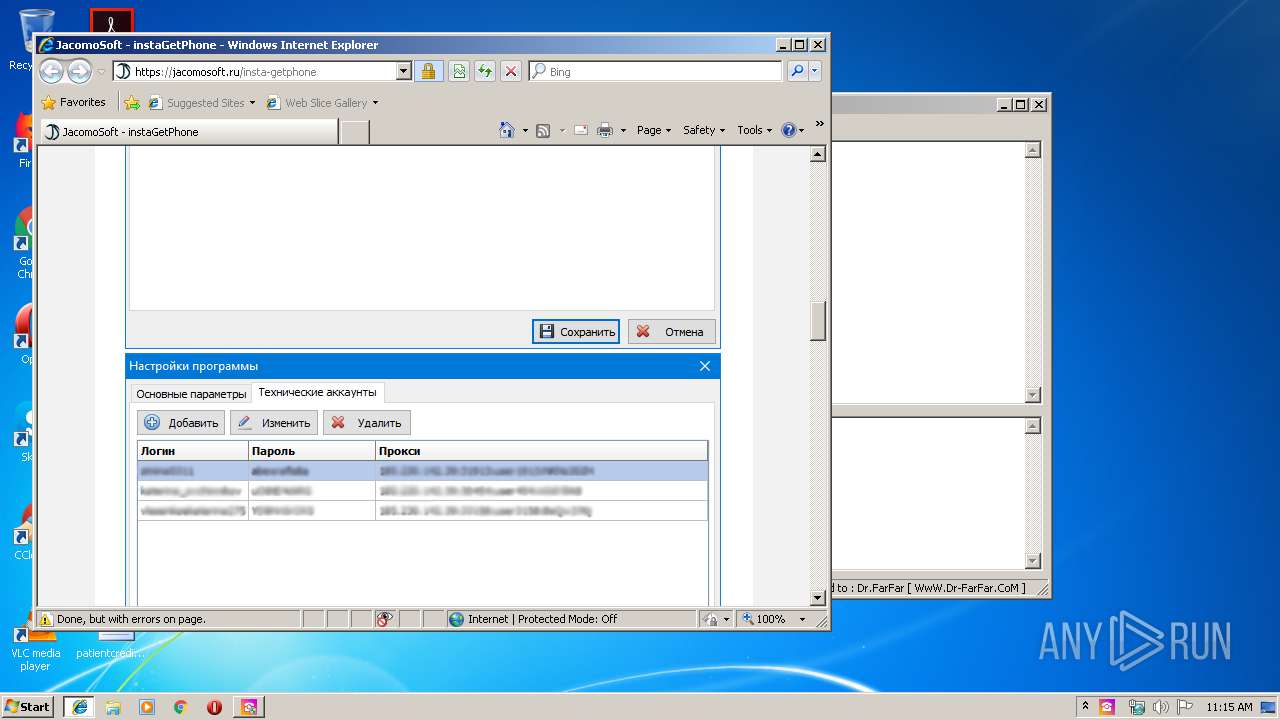
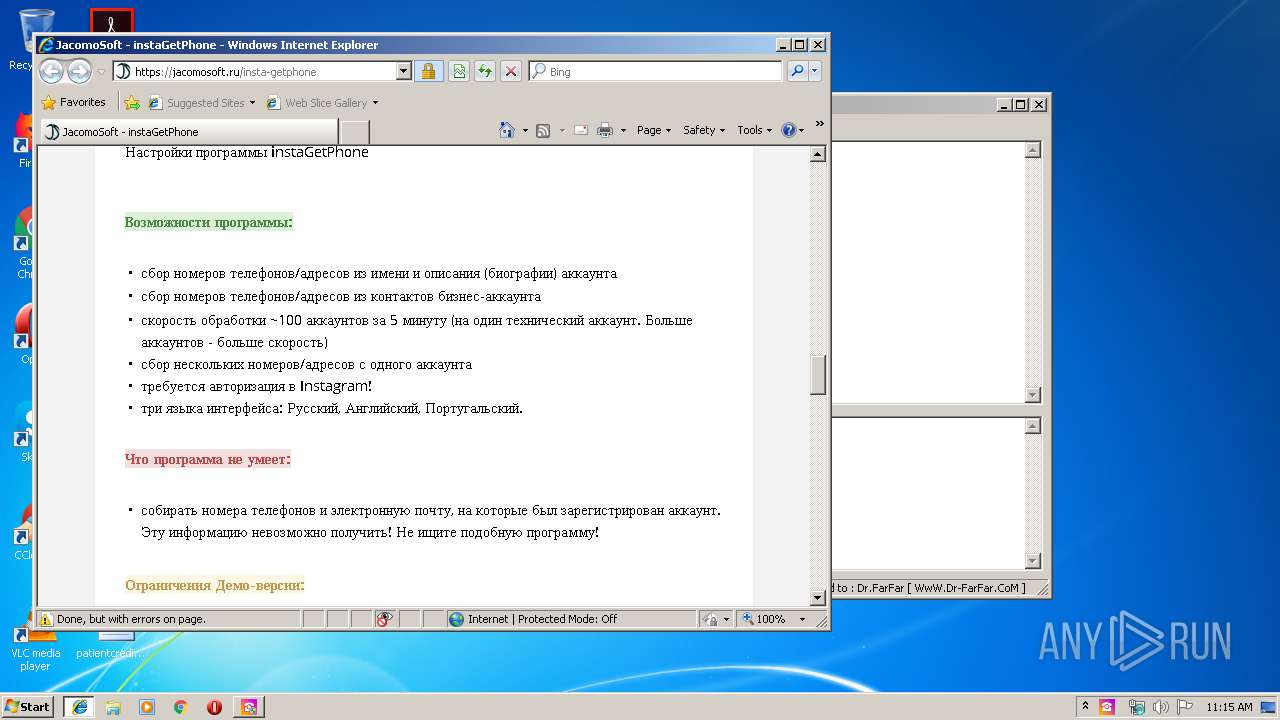
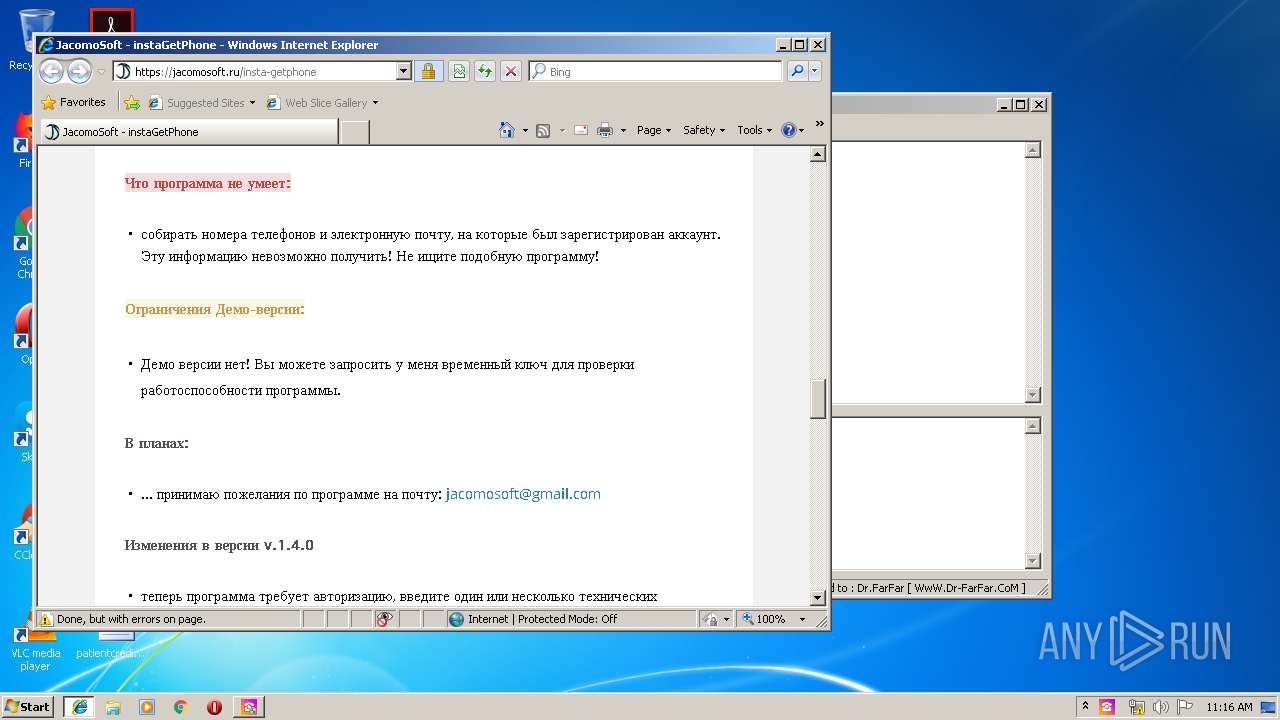
Starts Internet Explorer
- Instagram Get Phone Pro.tmp (PID: 1768)
- Instagram Get Phone Pro.exe (PID: 3632)
INFO
Application was dropped or rewritten from another process
- Instagram Get Phone Pro.tmp (PID: 1768)
- Instagram Get Phone Pro.tmp (PID: 2888)
Changes internet zones settings
- iexplore.exe (PID: 3464)
- iexplore.exe (PID: 3488)
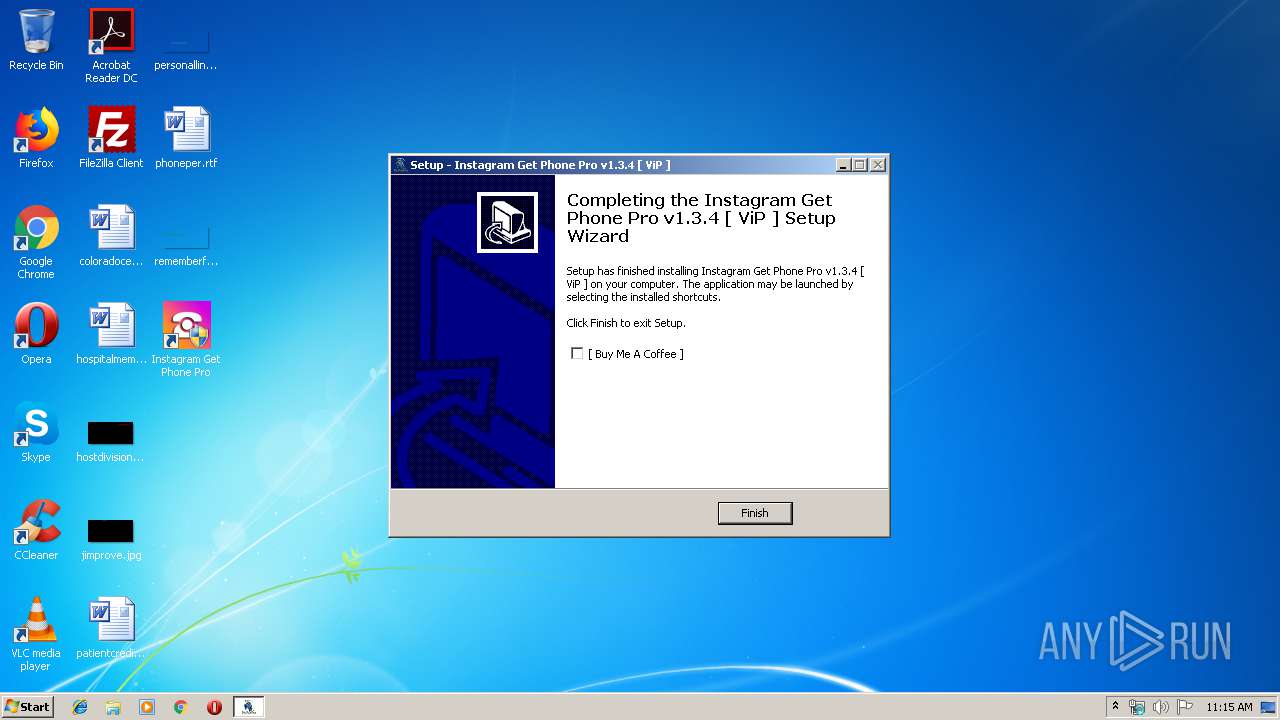
Creates a software uninstall entry
- Instagram Get Phone Pro.tmp (PID: 1768)
Changes settings of System certificates
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 4012)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 4012)
Reads internet explorer settings
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 4012)
Reads Internet Cache Settings
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 4012)
Creates files in the program directory
- Instagram Get Phone Pro.tmp (PID: 1768)
Manual execution by user
- Instagram Get Phone Pro.exe (PID: 3632)
Application launched itself
- iexplore.exe (PID: 3488)
Creates files in the user directory
- iexplore.exe (PID: 2372)
- iexplore.exe (PID: 4012)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41984 |
| InitializedDataSize: | 261632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaad0 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.4.0 |
| ProductVersionNumber: | 1.3.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
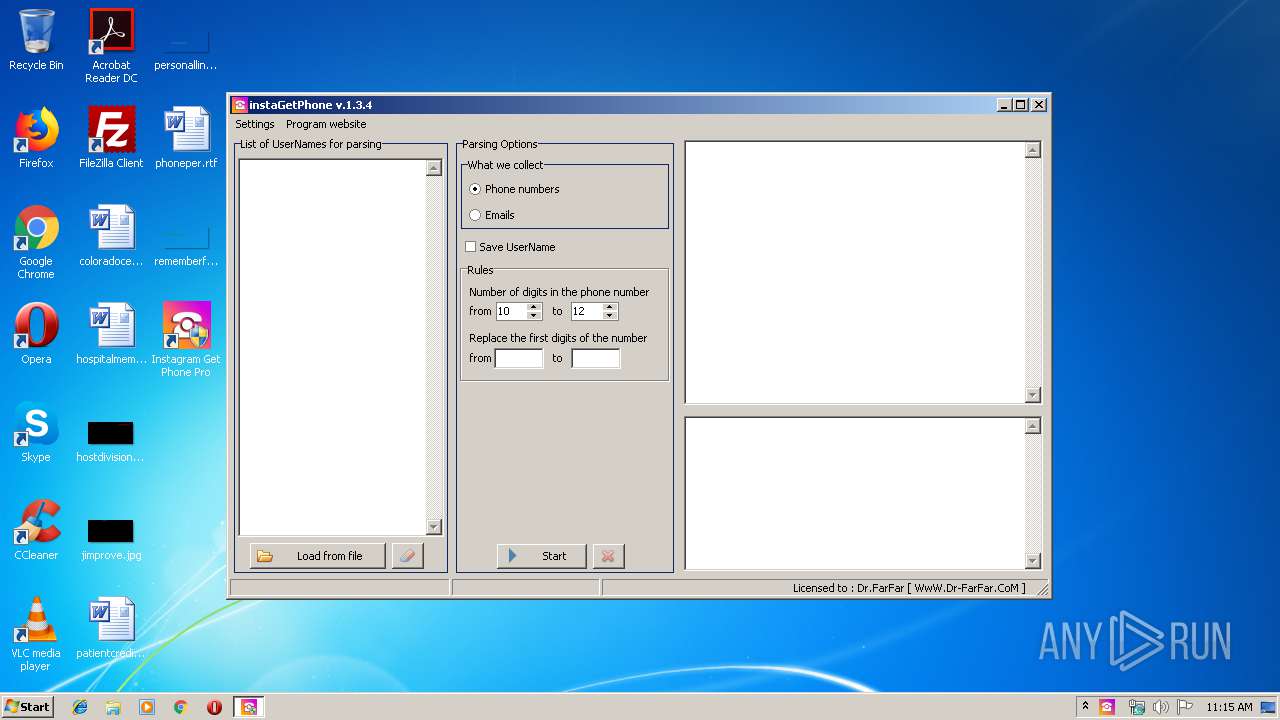
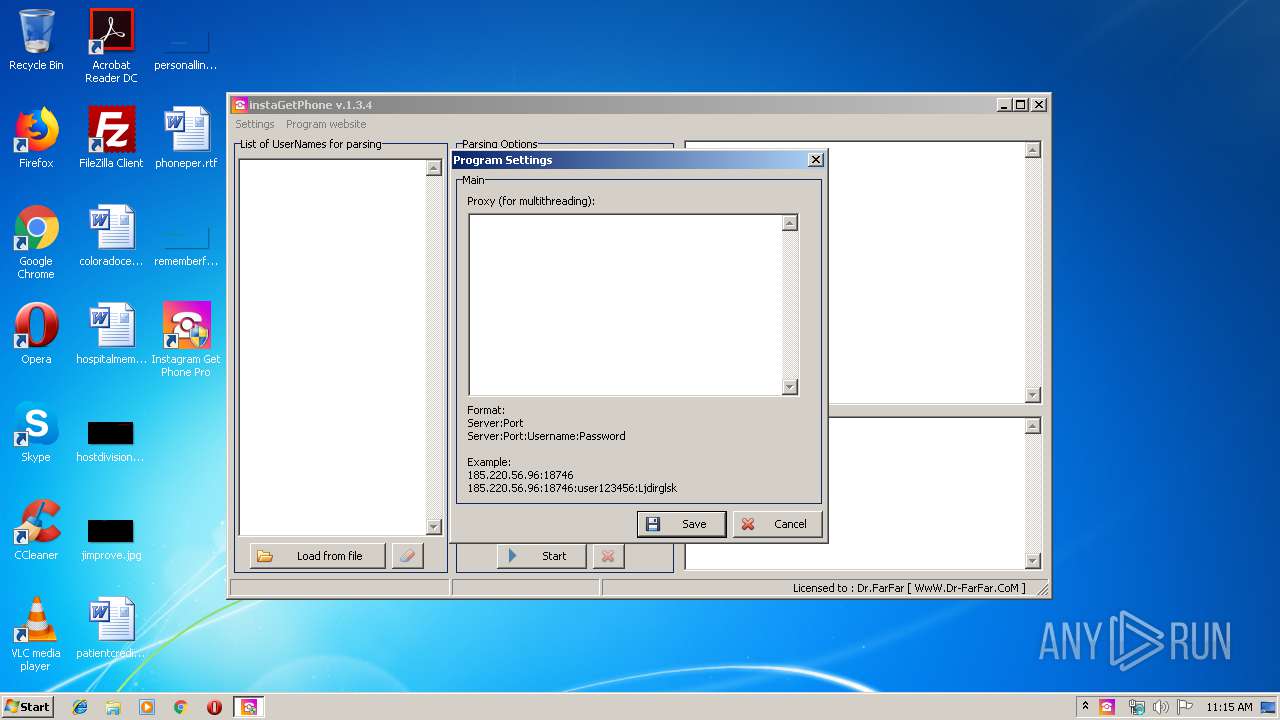
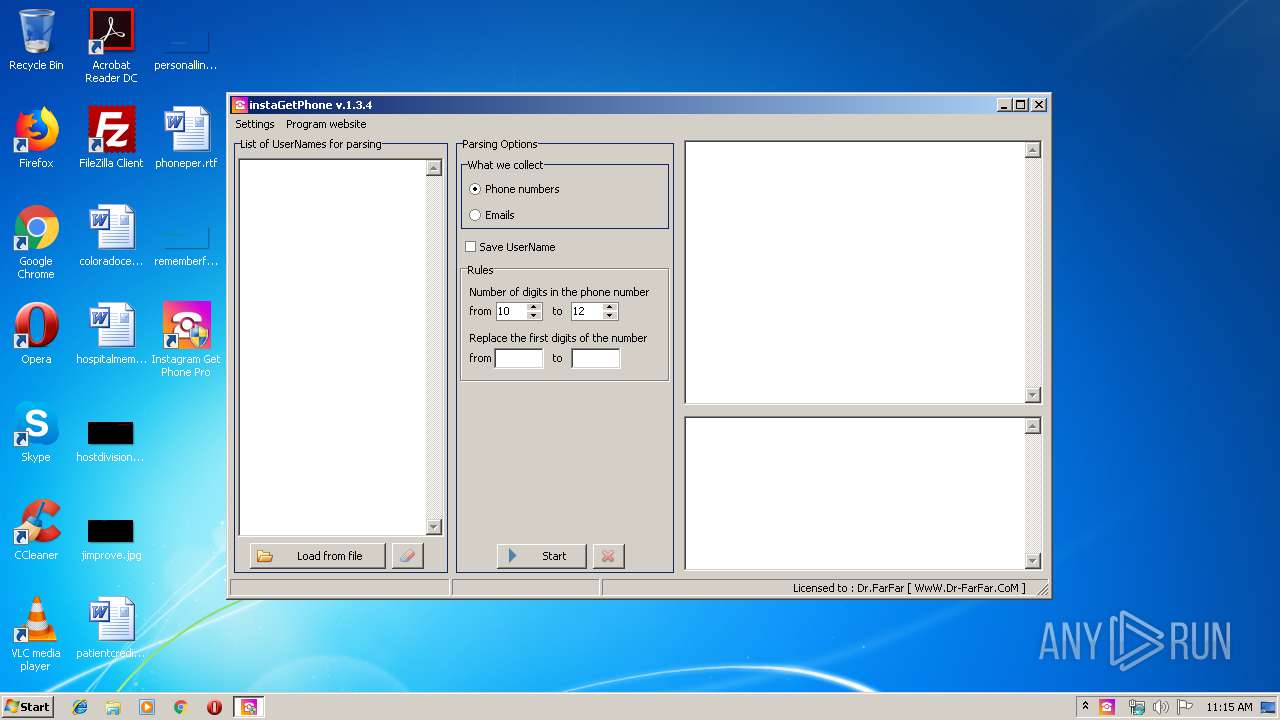
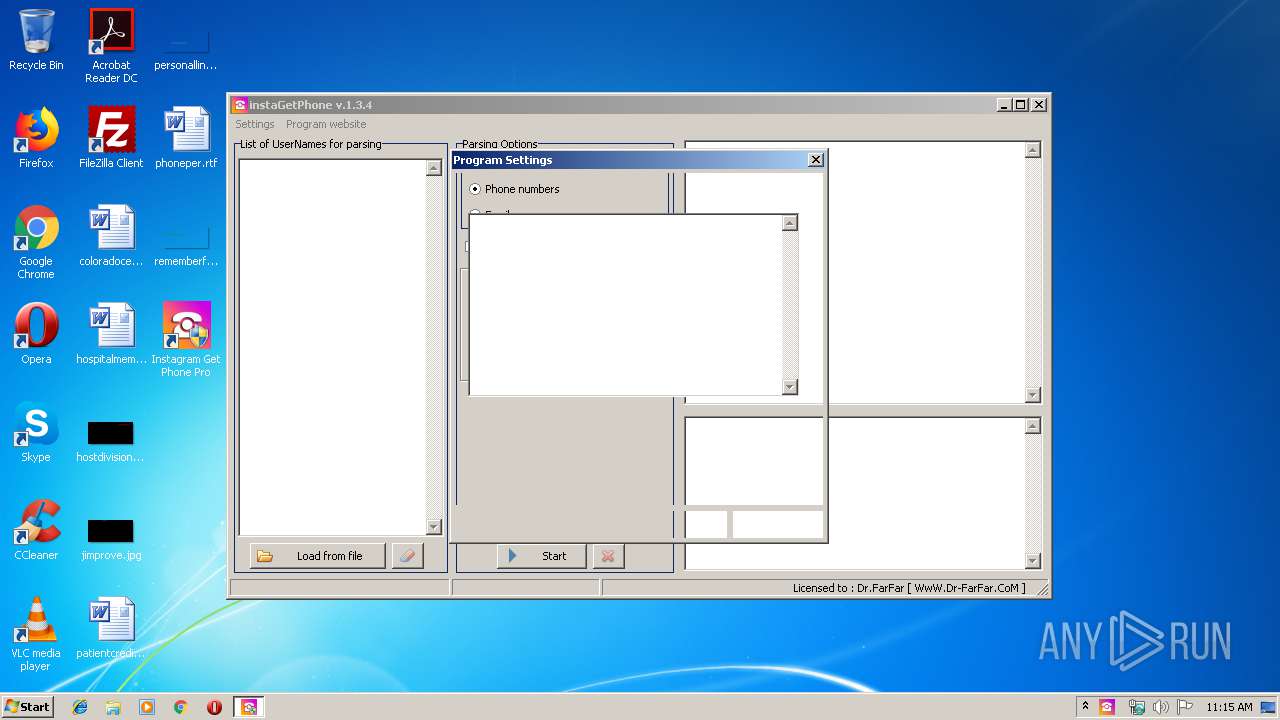
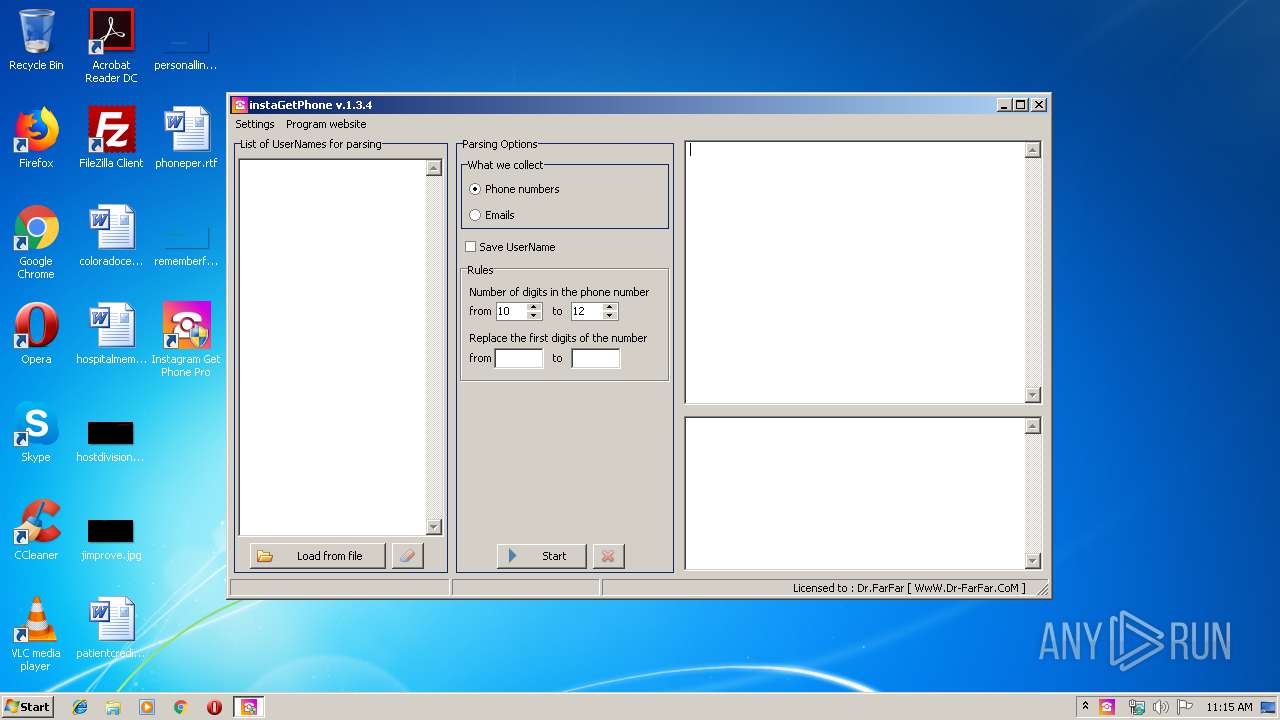
| CompanyName: | Dr.FarFar |
| FileDescription: | Instagram Get Phone Pro v1.3.4 [ ViP ] |
| FileVersion: | 1.3.4.0 |
| LegalCopyright: | Dr.FarFar |
| ProductName: | Instagram Get Phone Pro v1.3.4 [ ViP ] |
| ProductVersion: | 1.3.4.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Dr.FarFar |
| FileDescription: | Instagram Get Phone Pro v1.3.4 [ ViP ] |
| FileVersion: | 1.3.4.0 |
| LegalCopyright: | Dr.FarFar |
| ProductName: | Instagram Get Phone Pro v1.3.4 [ ViP ] |
| ProductVersion: | 1.3.4.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A208 | 0x0000A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60167 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.77135 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x00000920 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x0003EC0C | 0x0003EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.24687 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 7.99152 | 70906 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 7.99181 | 90866 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.9285 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.0339 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.36384 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.41268 | 12840 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.34364 | 7336 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.34738 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 3.0352 | 5672 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
49
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1768 | "C:\Users\admin\AppData\Local\Temp\is-8TAM1.tmp\Instagram Get Phone Pro.tmp" /SL5="$50126,2576470,304640,C:\Users\admin\AppData\Local\Temp\Instagram Get Phone Pro.exe" /SPAWNWND=$D011E /NOTIFYWND=$4012C | C:\Users\admin\AppData\Local\Temp\is-8TAM1.tmp\Instagram Get Phone Pro.tmp | Instagram Get Phone Pro.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3464 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | "C:\Users\admin\AppData\Local\Temp\Instagram Get Phone Pro.exe" | C:\Users\admin\AppData\Local\Temp\Instagram Get Phone Pro.exe | explorer.exe | ||||||||||||
User: admin Company: Dr.FarFar Integrity Level: MEDIUM Description: Instagram Get Phone Pro v1.3.4 [ ViP ] Exit code: 0 Version: 1.3.4.0 Modules
| |||||||||||||||
| 2888 | "C:\Users\admin\AppData\Local\Temp\is-IGO86.tmp\Instagram Get Phone Pro.tmp" /SL5="$4012C,2576470,304640,C:\Users\admin\AppData\Local\Temp\Instagram Get Phone Pro.exe" | C:\Users\admin\AppData\Local\Temp\is-IGO86.tmp\Instagram Get Phone Pro.tmp | — | Instagram Get Phone Pro.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3464 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Instagram Get Phone Pro.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3488 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | — | Instagram Get Phone Pro.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3632 | "C:\Program Files\Instagram Get Phone Pro\Instagram Get Phone Pro.exe" | C:\Program Files\Instagram Get Phone Pro\Instagram Get Phone Pro.exe | explorer.exe | ||||||||||||
User: admin Company: www.Dr-FarFar.com Integrity Level: HIGH Description: instagram Get Phone [ ViP ] Exit code: 0 Version: 1.3.4.0 Modules
| |||||||||||||||
| 3752 | "C:\Users\admin\AppData\Local\Temp\Instagram Get Phone Pro.exe" /SPAWNWND=$D011E /NOTIFYWND=$4012C | C:\Users\admin\AppData\Local\Temp\Instagram Get Phone Pro.exe | Instagram Get Phone Pro.tmp | ||||||||||||
User: admin Company: Dr.FarFar Integrity Level: HIGH Description: Instagram Get Phone Pro v1.3.4 [ ViP ] Exit code: 0 Version: 1.3.4.0 Modules
| |||||||||||||||
| 4012 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3488 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 676
Read events
1 419
Write events
250
Delete events
7
Modification events
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: E80600001062531B6F9CD501 | |||
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 32DDCBA654F2BCFC2E3E26FE24EC28B443F45E0EC1BD381C821BB60C573212EC | |||
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Instagram Get Phone Pro\Instagram Get Phone Pro.exe | |||
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: D89514D6A2181DE1BC92EE7F045E4FE02DA6693C17E4F51FD5AEC3944087E582 | |||
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files\Instagram Get Phone Pro\Instagram Get Phone Pro.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A6CBC04A-2C3E-42C7-8BD2-94C43ADFB7ED}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (a) | |||
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A6CBC04A-2C3E-42C7-8BD2-94C43ADFB7ED}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Instagram Get Phone Pro | |||
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A6CBC04A-2C3E-42C7-8BD2-94C43ADFB7ED}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Instagram Get Phone Pro\ | |||
| (PID) Process: | (1768) Instagram Get Phone Pro.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{A6CBC04A-2C3E-42C7-8BD2-94C43ADFB7ED}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Instagram Get Phone Pro v1.3.4 [ ViP ] | |||
Executable files
8
Suspicious files
3
Text files
103
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1768 | Instagram Get Phone Pro.tmp | C:\Program Files\Instagram Get Phone Pro\is-LLUD5.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | Instagram Get Phone Pro.tmp | C:\Program Files\Instagram Get Phone Pro\is-J4AJU.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | Instagram Get Phone Pro.tmp | C:\Program Files\Instagram Get Phone Pro\is-B0U75.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | Instagram Get Phone Pro.tmp | C:\Program Files\Instagram Get Phone Pro\is-LGOTD.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | Instagram Get Phone Pro.tmp | C:\Program Files\Instagram Get Phone Pro\is-S21RU.tmp | — | |
MD5:— | SHA256:— | |||
| 1768 | Instagram Get Phone Pro.tmp | C:\Program Files\Instagram Get Phone Pro\is-TQ80S.tmp | — | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\c16jg[2].css | — | |
MD5:— | SHA256:— | |||
| 2772 | Instagram Get Phone Pro.exe | C:\Users\admin\AppData\Local\Temp\is-IGO86.tmp\Instagram Get Phone Pro.tmp | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
33
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3464 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
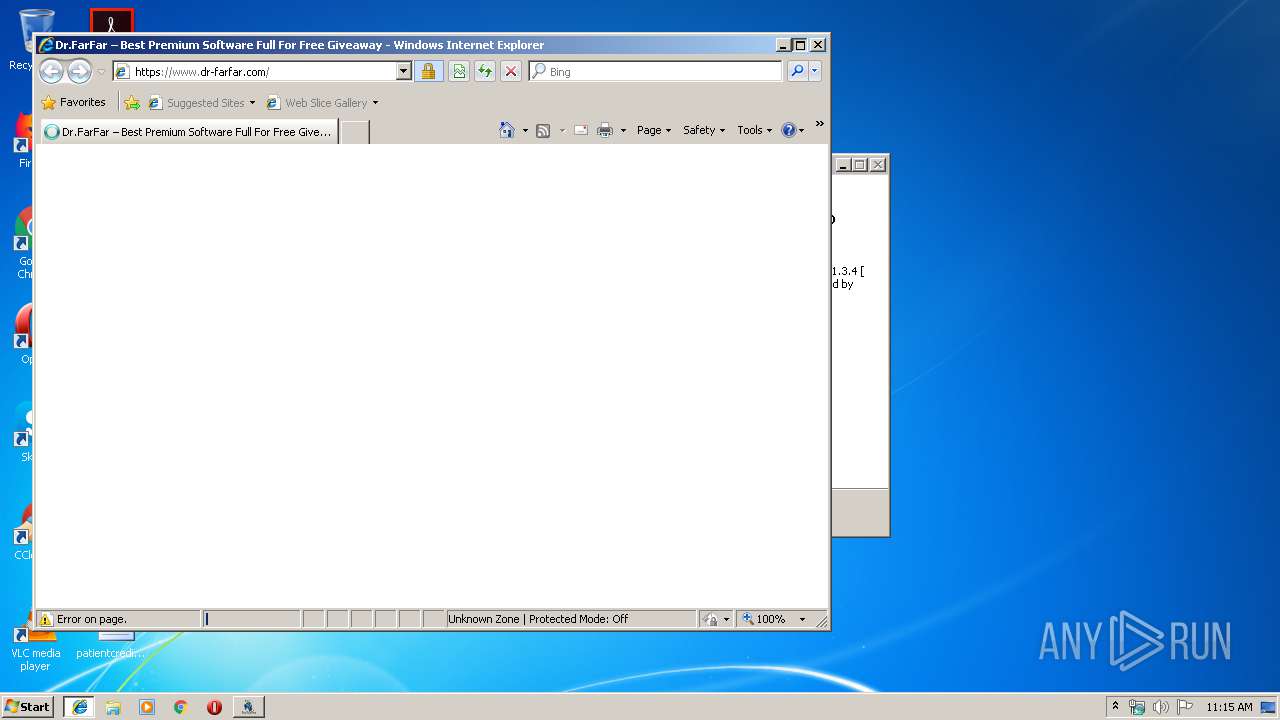
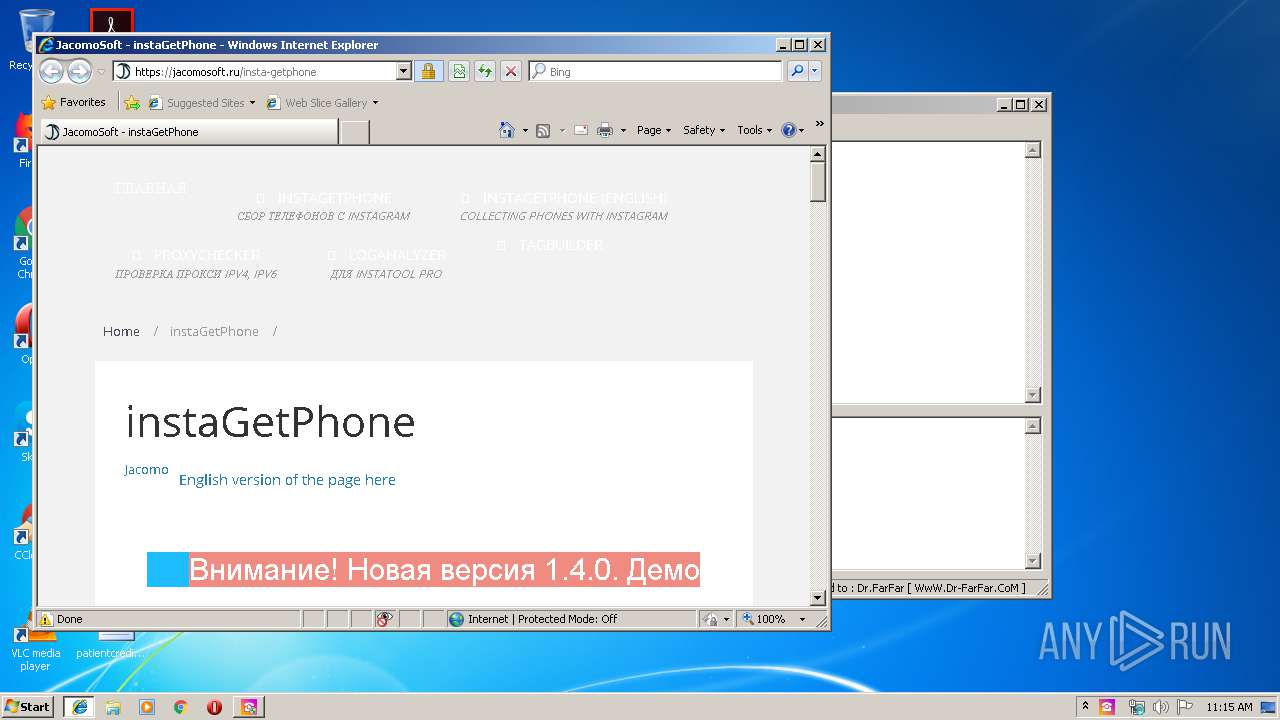
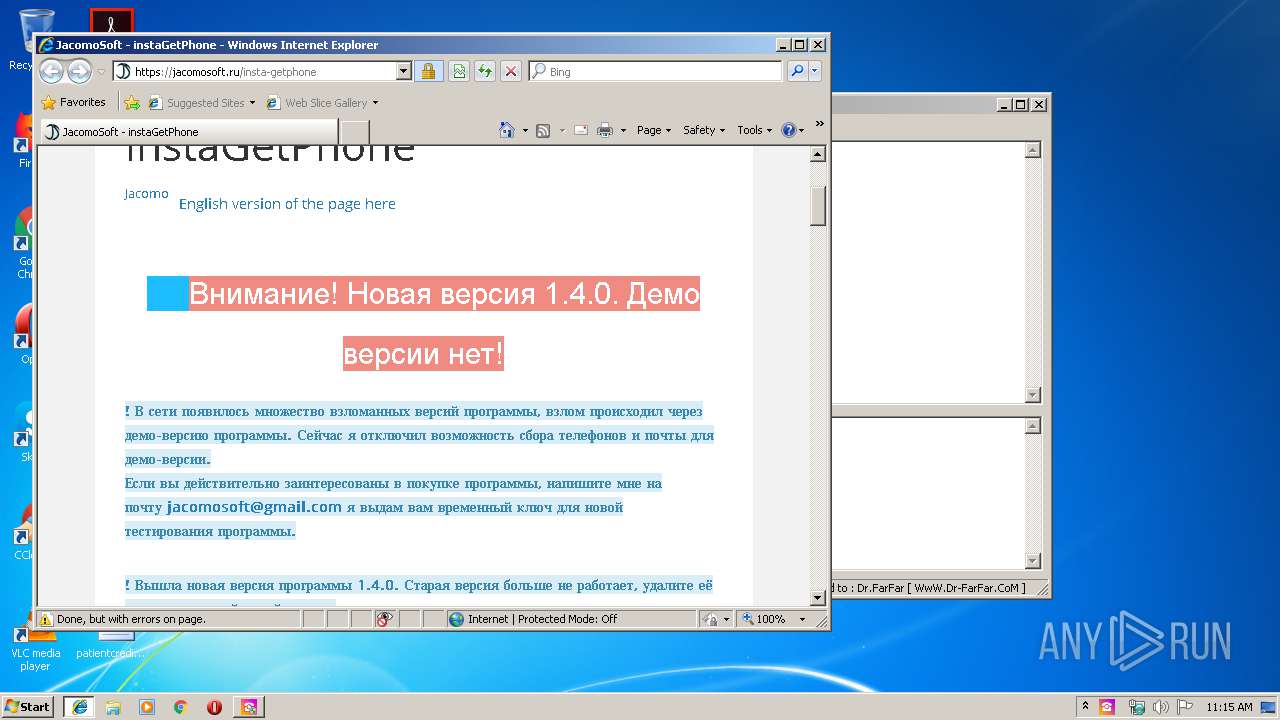
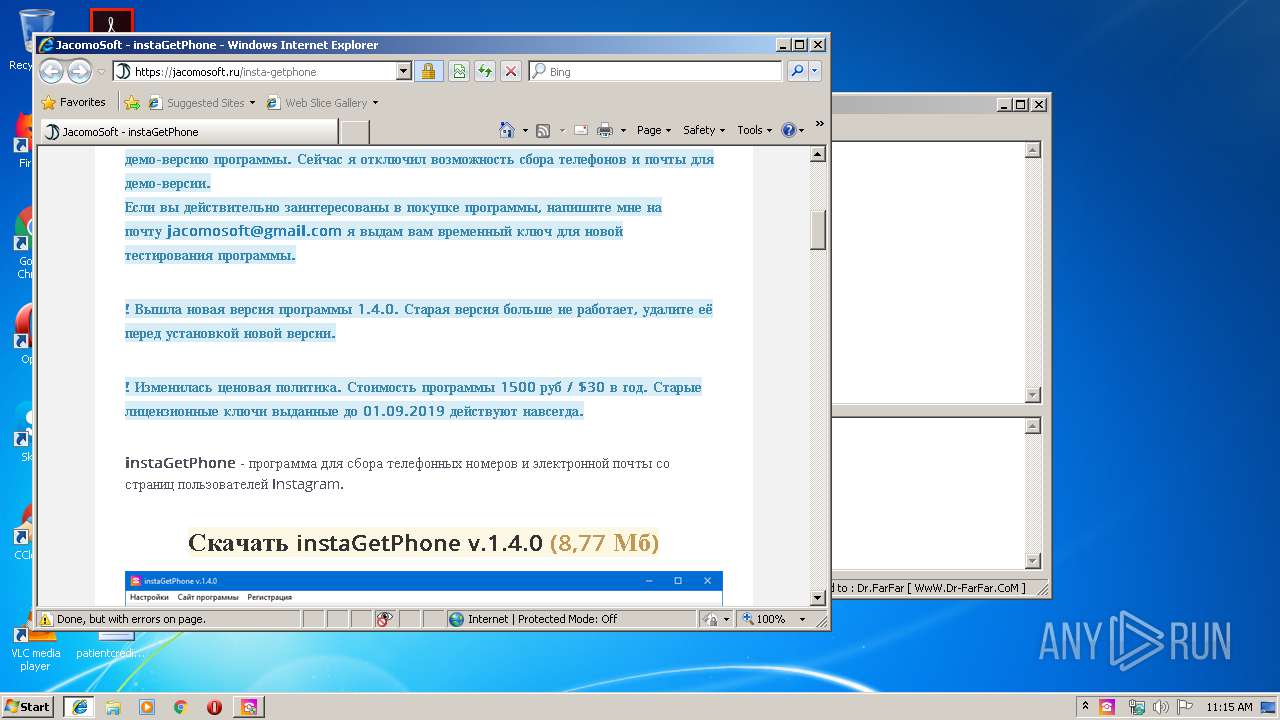
2372 | iexplore.exe | 104.18.46.165:443 | www.dr-farfar.com | Cloudflare Inc | US | shared |
3464 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2372 | iexplore.exe | 172.217.16.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2372 | iexplore.exe | 216.58.207.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2372 | iexplore.exe | 192.99.8.34:443 | s4is.histats.com | OVH SAS | CA | suspicious |
2372 | iexplore.exe | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
4012 | iexplore.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2372 | iexplore.exe | 74.125.206.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
4012 | iexplore.exe | 2.21.38.79:443 | www.paypalobjects.com | GTT Communications Inc. | FR | unknown |
4012 | iexplore.exe | 87.240.139.194:443 | vk.com | VKontakte Ltd | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dr-farfar.com |
| malicious |
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
i0.wp.com |
| whitelisted |
i2.wp.com |
| whitelisted |
i3.wp.com |
| whitelisted |
static.copyrighted.com |
| suspicious |
images.dmca.com |
| whitelisted |