| File name: | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe |
| Full analysis: | https://app.any.run/tasks/87c77258-aadf-4253-857a-858cbcb808a4 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 08:23:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E806D1194873FCFA4E31726710B75405 |
| SHA1: | 7D10BF42D901224BCE67249B590C0DFC4F350653 |
| SHA256: | ED37BB51AF01647FDE0A5B04A401FD278EBA50CF2D5D0678F86227D27AECBC62 |
| SSDEEP: | 3072:655tEdAOKlggqO3G0jPonfYnoFMIkcXo0fSUa:/W26QfweMILXoXU |
MALICIOUS
Deletes shadow copies
- cmd.exe (PID: 3208)
- cmd.exe (PID: 3920)
- cmd.exe (PID: 2408)
- cmd.exe (PID: 2400)
- cmd.exe (PID: 3716)
- cmd.exe (PID: 2168)
- cmd.exe (PID: 2180)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 1820)
- cmd.exe (PID: 2988)
- cmd.exe (PID: 2540)
- cmd.exe (PID: 3132)
- cmd.exe (PID: 1960)
- cmd.exe (PID: 1964)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 2372)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 3052)
- cmd.exe (PID: 3484)
- cmd.exe (PID: 3208)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 3816)
- cmd.exe (PID: 976)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 1540)
SUSPICIOUS
Reads the Internet Settings
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2752)
- WMIC.exe (PID: 3632)
- WMIC.exe (PID: 3760)
- WMIC.exe (PID: 3696)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1632)
- WMIC.exe (PID: 3000)
- WMIC.exe (PID: 1848)
- WMIC.exe (PID: 3452)
Executes as Windows Service
- VSSVC.exe (PID: 3404)
- wbengine.exe (PID: 3472)
- vds.exe (PID: 1472)
- VSSVC.exe (PID: 3720)
Starts CMD.EXE for commands execution
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2752)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1632)
Uses WEVTUTIL.EXE to cleanup log
- cmd.exe (PID: 1468)
- cmd.exe (PID: 3516)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 2012)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 3520)
- cmd.exe (PID: 1068)
- cmd.exe (PID: 3832)
- cmd.exe (PID: 3492)
- cmd.exe (PID: 3728)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 2148)
Uses WMIC.EXE to obtain shadow copy information
- cmd.exe (PID: 3364)
- cmd.exe (PID: 2472)
- cmd.exe (PID: 3208)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 1700)
- cmd.exe (PID: 3336)
Connects to unusual port
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2752)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1632)
Executable content was dropped or overwritten
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2752)
INFO
Reads the computer name
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2712)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2752)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1984)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1632)
Checks supported languages
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2712)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2752)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1632)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1984)
The process checks LSA protection
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2712)
- dllhost.exe (PID: 3604)
- dllhost.exe (PID: 2540)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2752)
- vssadmin.exe (PID: 3268)
- VSSVC.exe (PID: 3404)
- vssadmin.exe (PID: 2332)
- wbadmin.exe (PID: 3240)
- WMIC.exe (PID: 3632)
- vssadmin.exe (PID: 2444)
- wbadmin.exe (PID: 1736)
- wbadmin.exe (PID: 2220)
- vdsldr.exe (PID: 3648)
- WMIC.exe (PID: 3696)
- wbengine.exe (PID: 3472)
- vds.exe (PID: 1472)
- WMIC.exe (PID: 3760)
- wbadmin.exe (PID: 2664)
- dllhost.exe (PID: 3572)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1984)
- dllhost.exe (PID: 2512)
- wbadmin.exe (PID: 952)
- vssadmin.exe (PID: 3960)
- vssadmin.exe (PID: 2564)
- VSSVC.exe (PID: 3720)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1632)
- WMIC.exe (PID: 3000)
- vssadmin.exe (PID: 3468)
- wbadmin.exe (PID: 876)
- wbadmin.exe (PID: 4072)
- WMIC.exe (PID: 1848)
- wbadmin.exe (PID: 3056)
- wbadmin.exe (PID: 2340)
- WMIC.exe (PID: 3452)
Reads the machine GUID from the registry
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2712)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1984)
Checks transactions between databases Windows and Oracle
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2712)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1984)
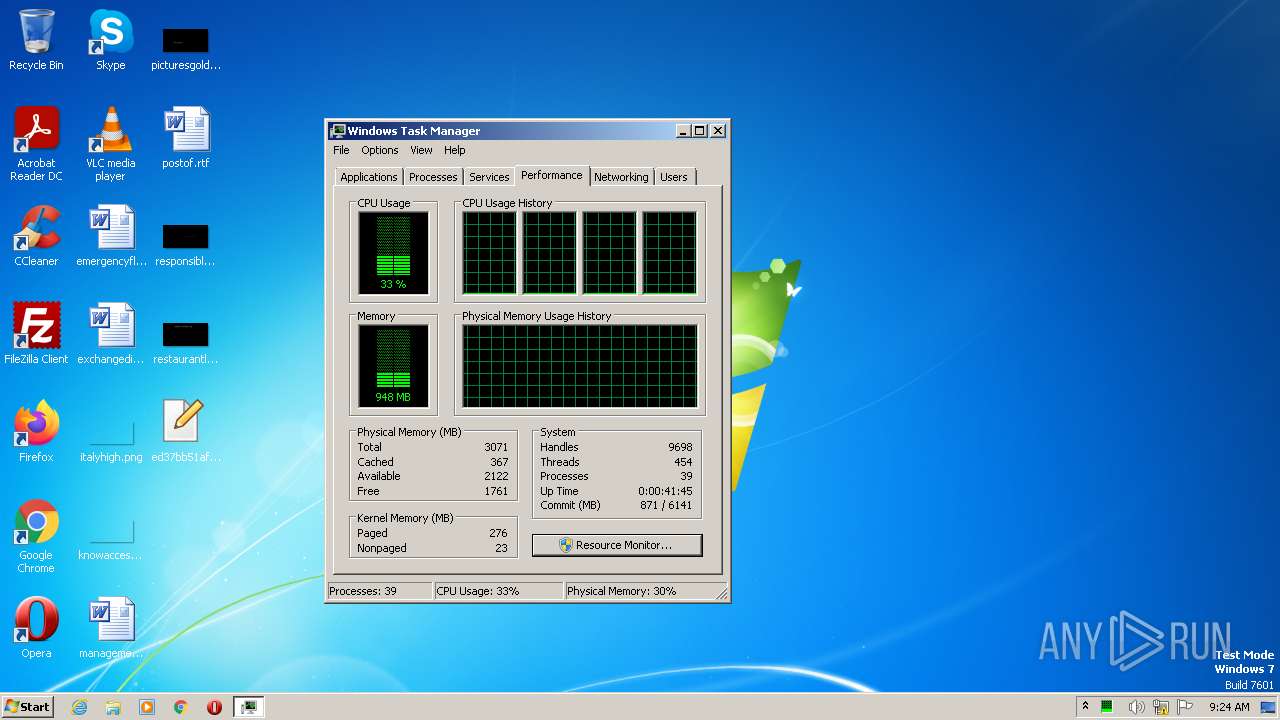
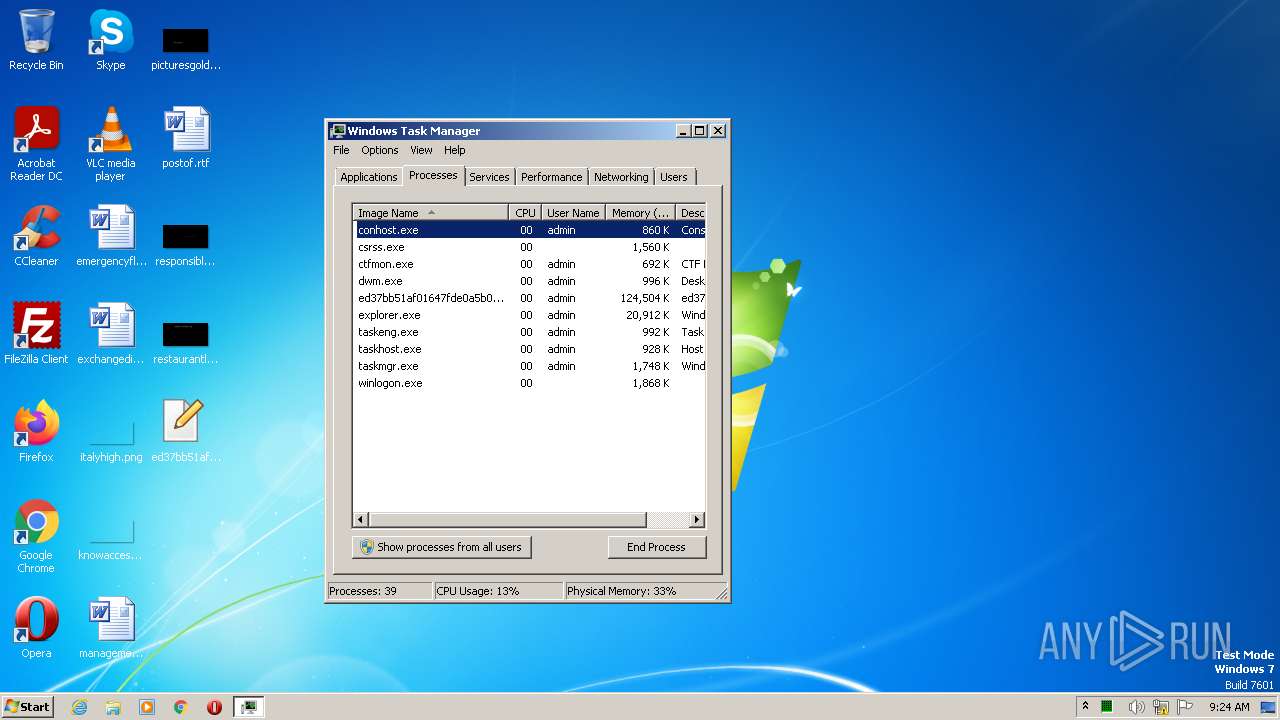
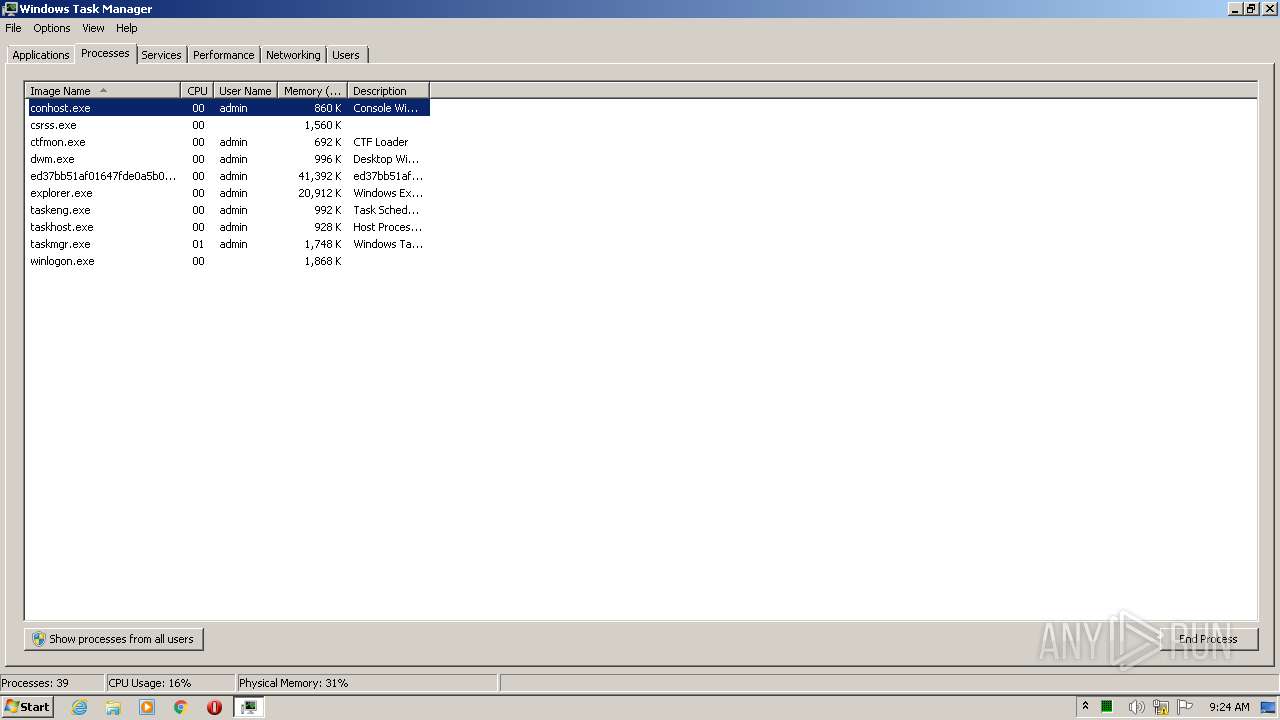
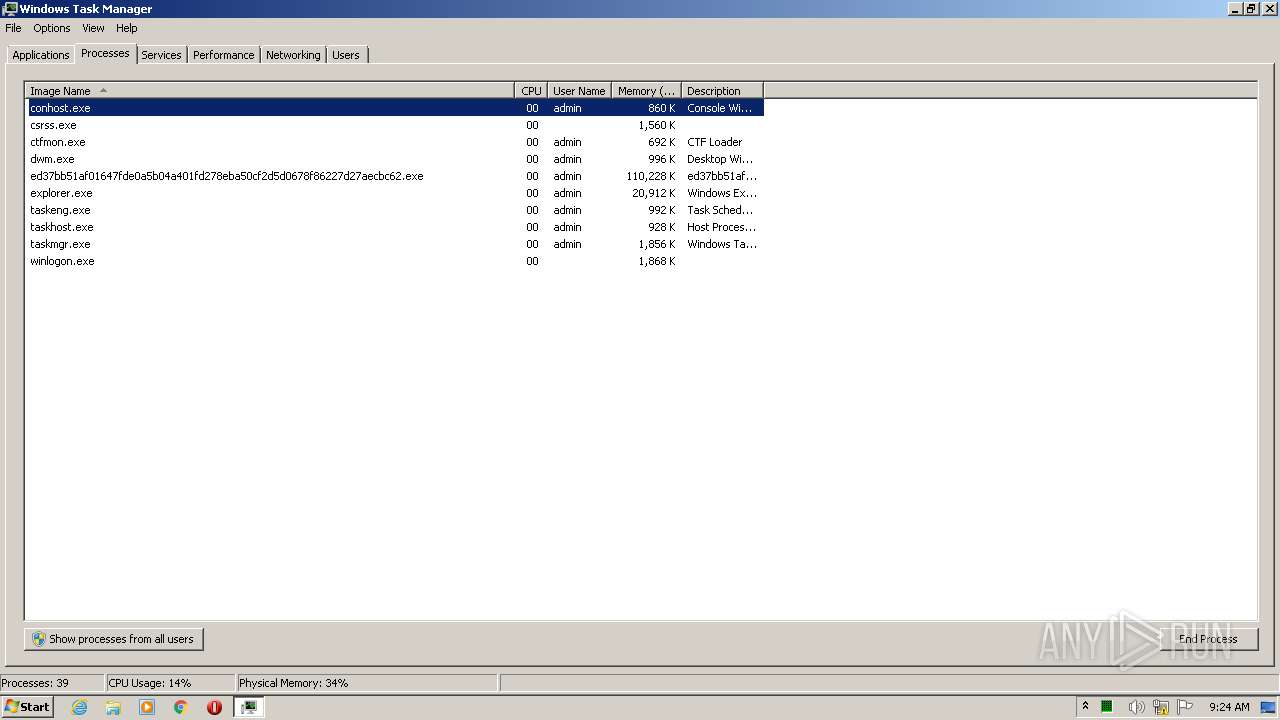
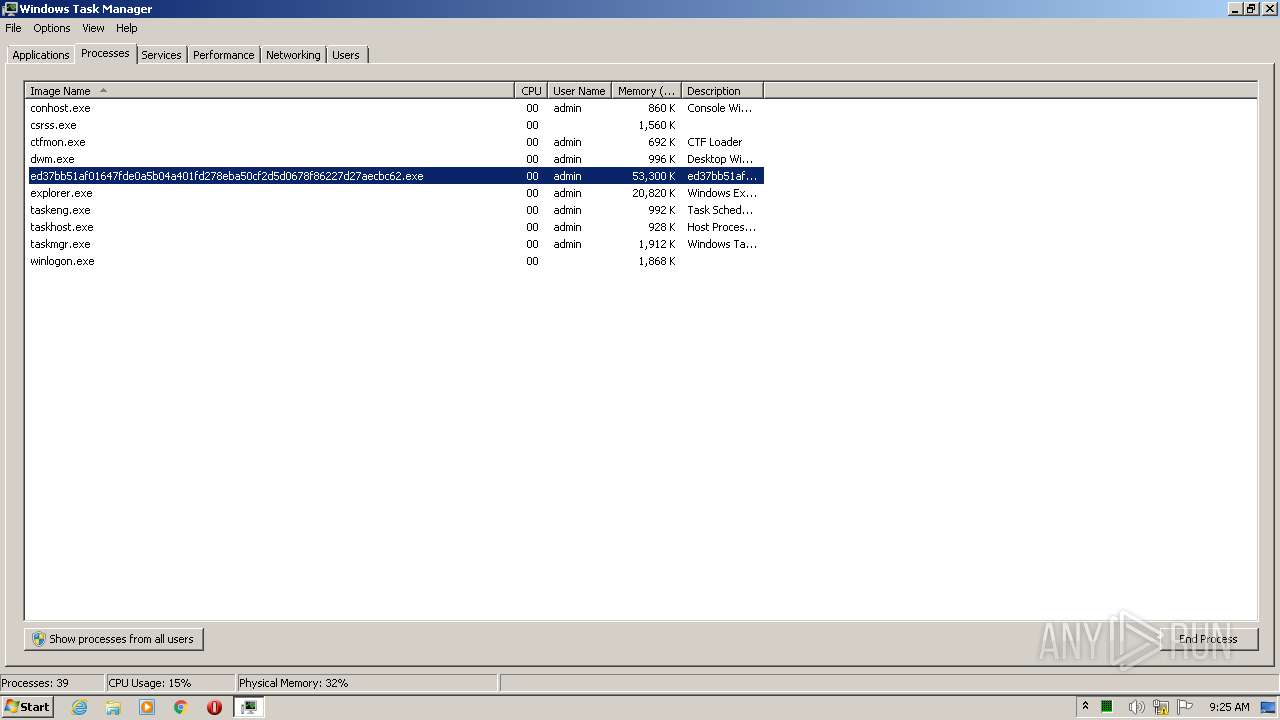
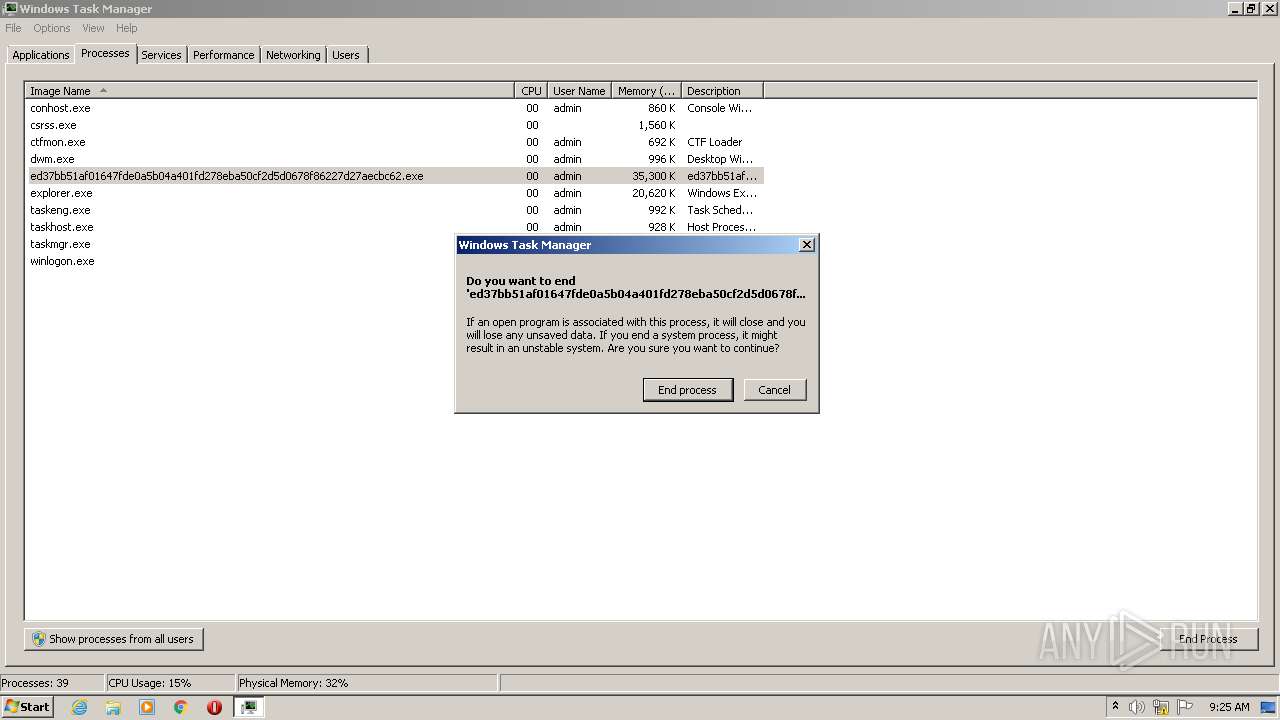
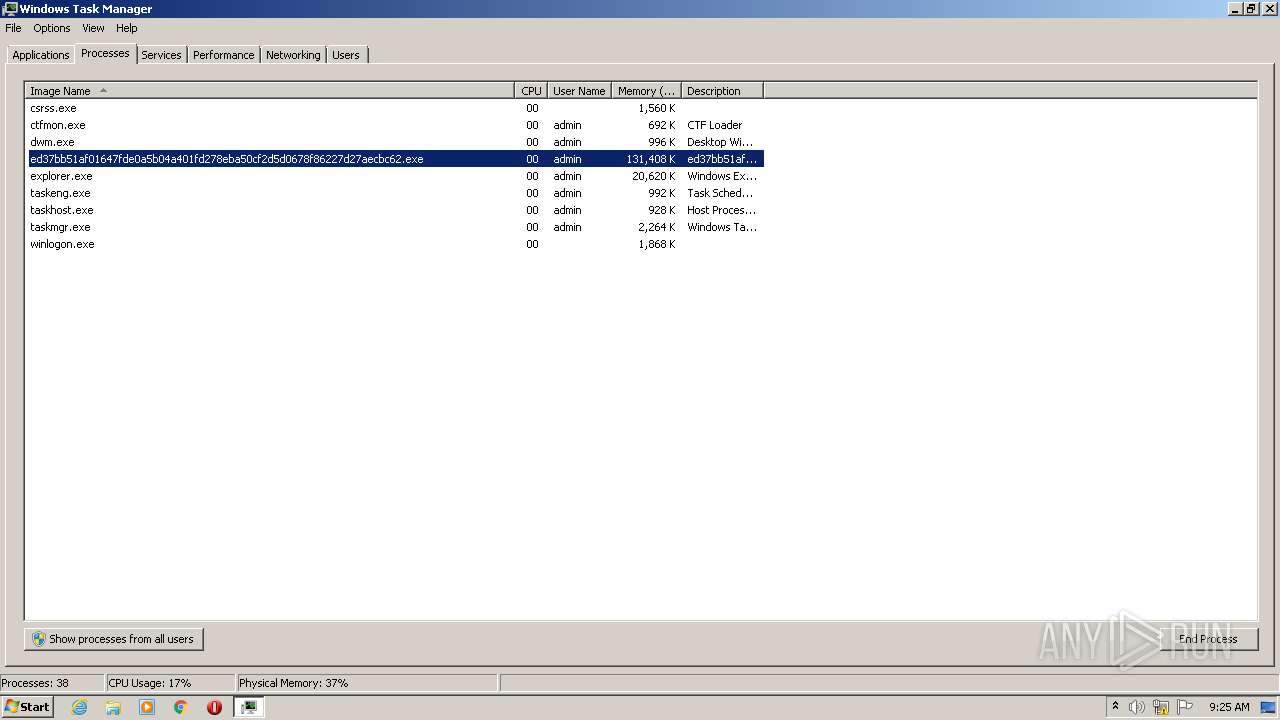
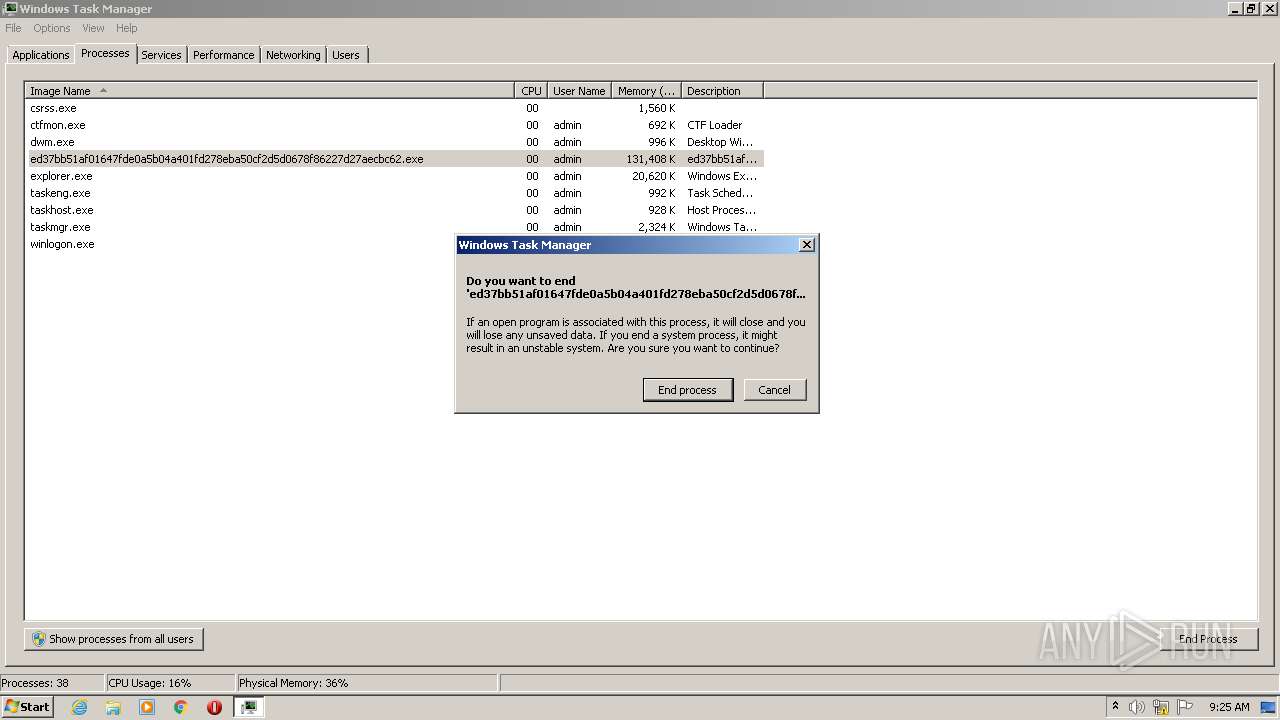
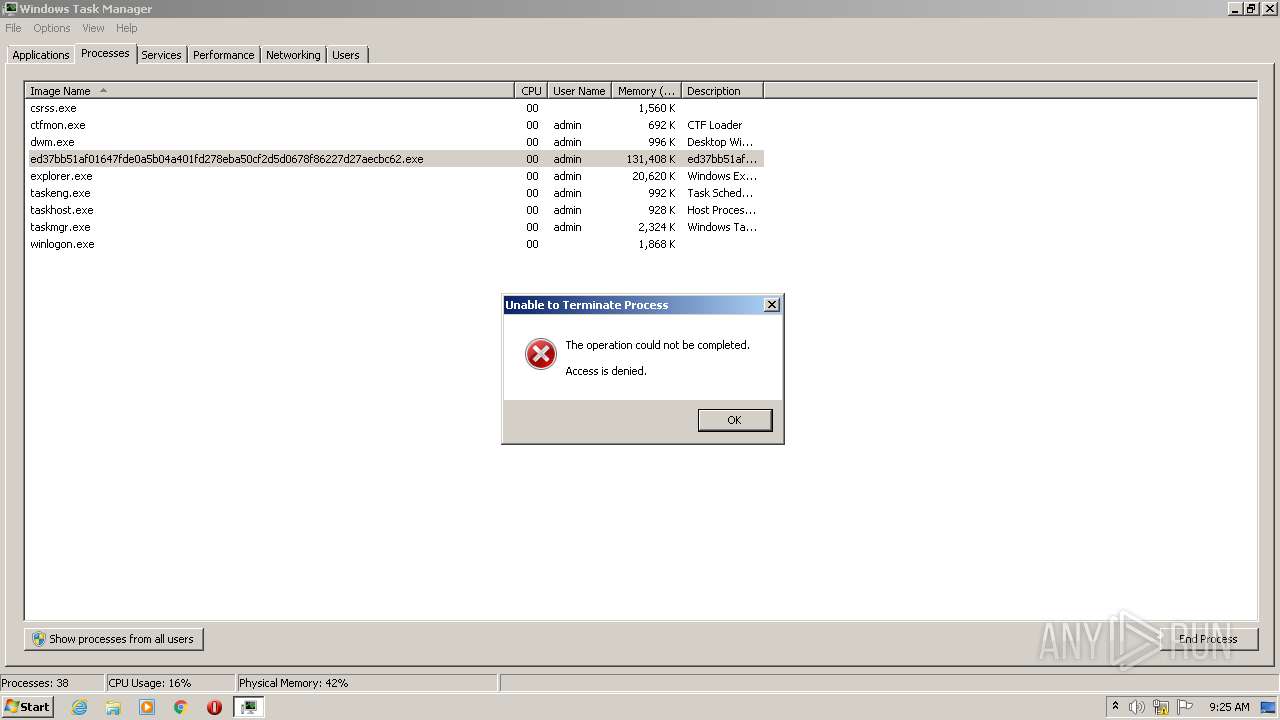
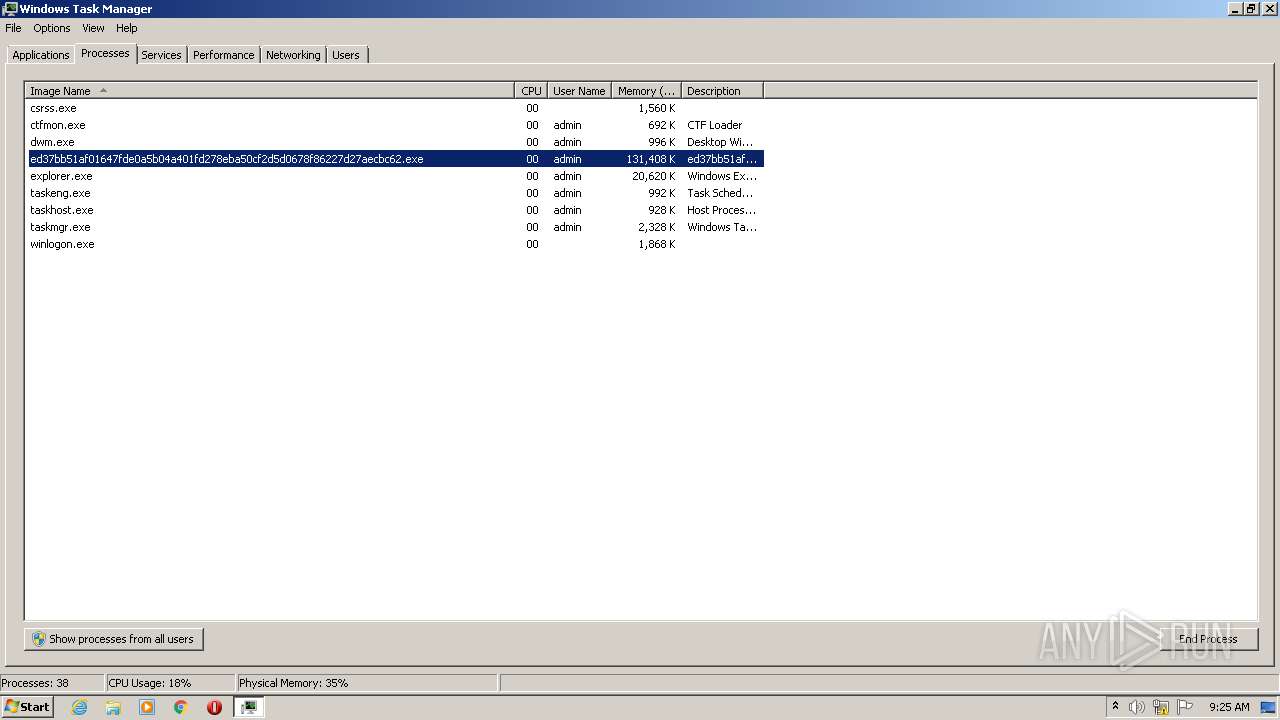
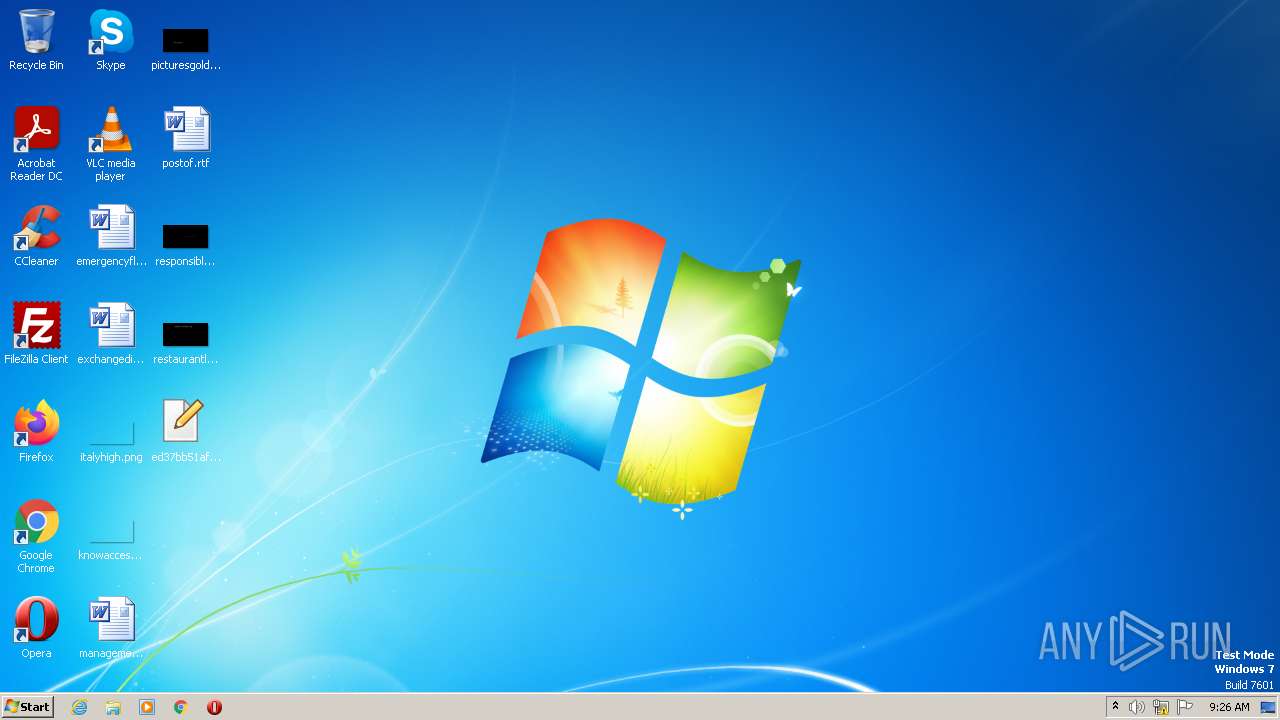
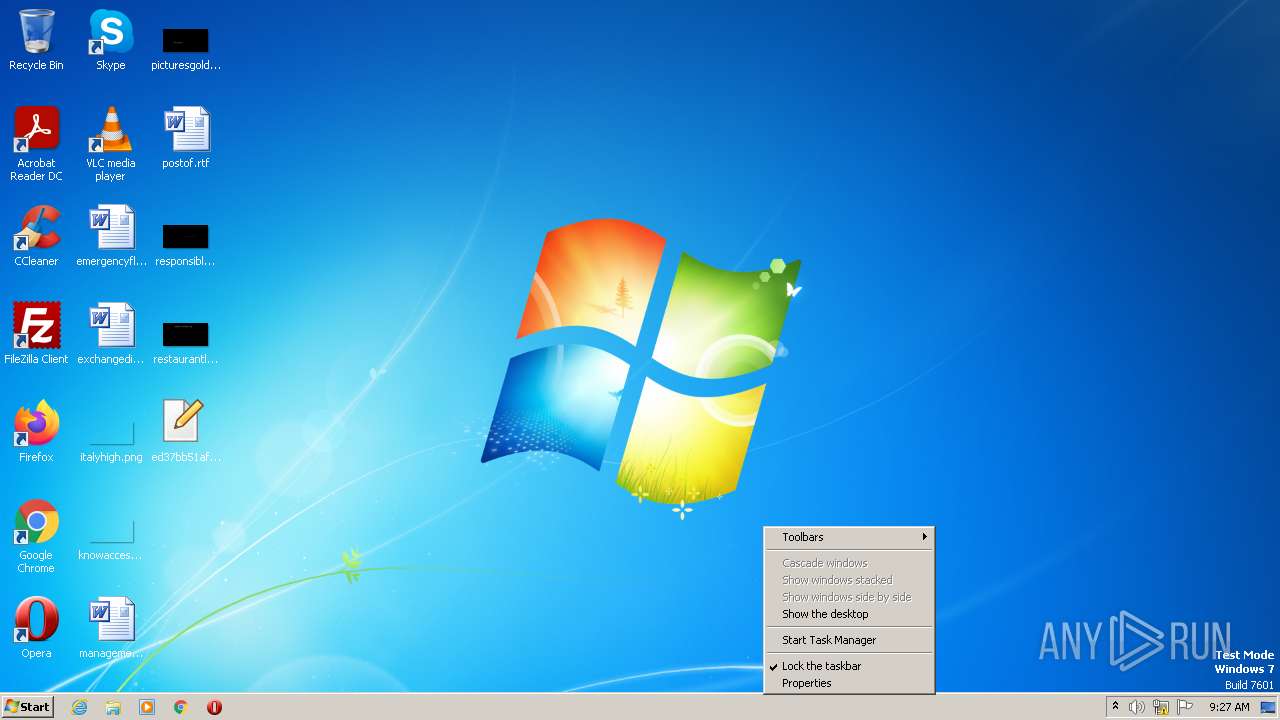
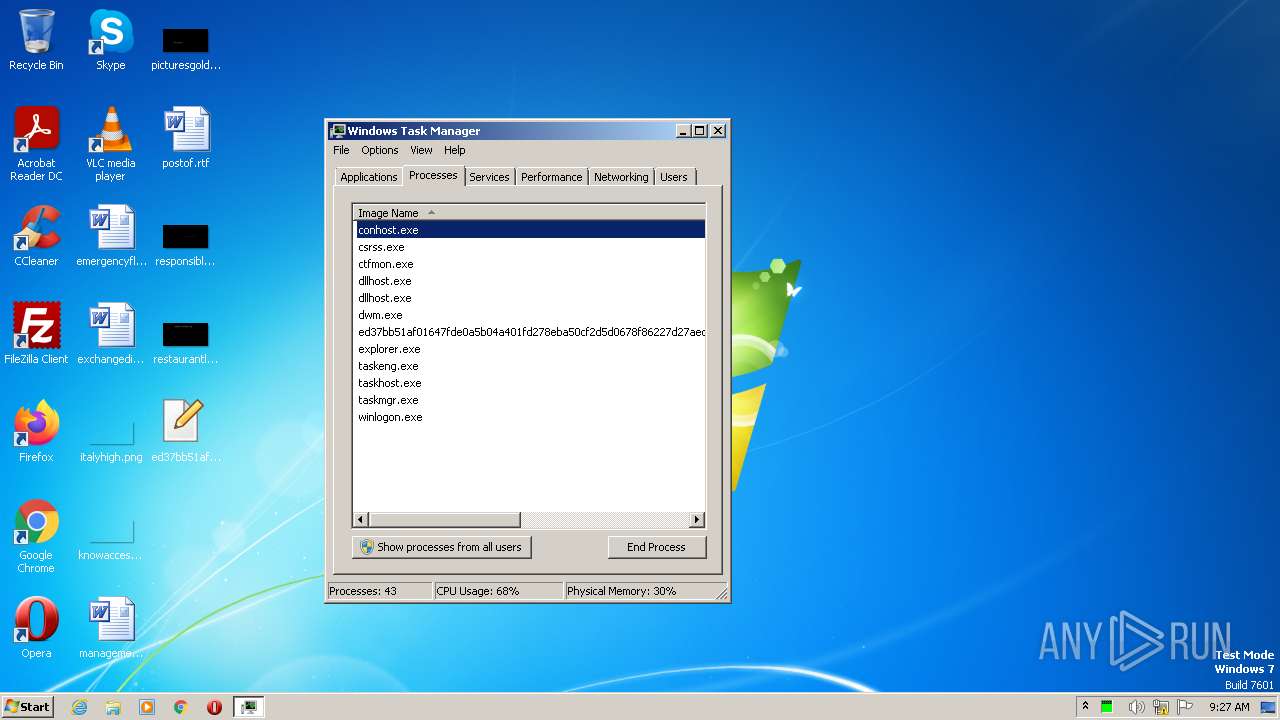
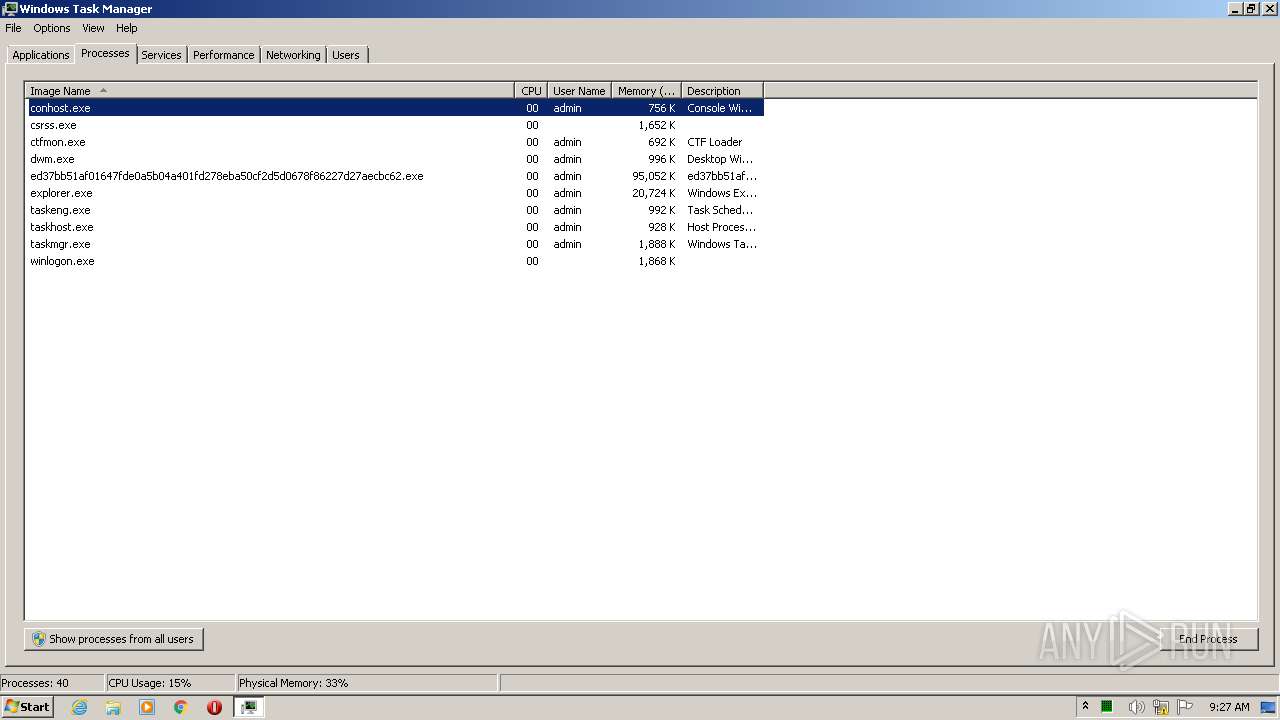
Manual execution by a user
- taskmgr.exe (PID: 2372)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1984)
- taskmgr.exe (PID: 2064)
Creates files in the program directory
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 1632)
- ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| ProductVer: | 2.0.9.29 |
|---|---|
| FileV: | 1.0.2.37 |
| CharacterSet: | Windows, Turkish |
| LanguageCode: | Russian |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | Special build |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 44.0.0.0 |
| FileVersionNumber: | 44.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x4cce90 |
| UninitializedDataSize: | 4894720 |
| InitializedDataSize: | 20480 |
| CodeSize: | 139264 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| TimeStamp: | 2019:08:02 16:08:23+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Aug-2019 16:08:23 |
| Detected languages: |
|
| FileV: | 1.0.2.37 |
| ProductVer: | 2.0.9.29 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 02-Aug-2019 16:08:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x004AB000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x004AC000 | 0x00022000 | 0x00021200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.78442 |
.rsrc | 0x004CE000 | 0x00005000 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.01714 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.99666 | 9640 | UNKNOWN | English - United States | RT_ICON |
2 | 3.94238 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 2.74199 | 304 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.33799 | 240 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 1.67607 | 4264 | UNKNOWN | UNKNOWN | RT_CURSOR |
25 | 3.27359 | 996 | UNKNOWN | UNKNOWN | RT_STRING |
26 | 3.18584 | 682 | UNKNOWN | UNKNOWN | RT_STRING |
124 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
2371 | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_CURSOR |
2374 | 2.51621 | 48 | UNKNOWN | UNKNOWN | RT_GROUP_CURSOR |
Imports
GDI32.dll |
KERNEL32.DLL |
Total processes
185
Monitored processes
99
Malicious processes
20
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | wevtutil cl application | C:\Windows\System32\wevtutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Eventing Command Line Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | wbadmin DELETE SYSTEMSTATEBACKUP | C:\Windows\System32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 4294967293 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | wbadmin delete catalog -quiet | C:\Windows\System32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 976 | /c bcdedit /set {default} recoveryenabled No | C:\Windows\System32\cmd.exe | — | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1068 | /c wevtutil cl security | C:\Windows\System32\cmd.exe | — | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1356 | bcdedit /set {default} recoveryenabled No | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1468 | /c wevtutil cl application | C:\Windows\System32\cmd.exe | — | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1472 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1540 | /c bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\cmd.exe | — | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1632 | "C:\Users\admin\Desktop\ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe" | C:\Users\admin\Desktop\ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
9 278
Read events
9 184
Write events
94
Delete events
0
Modification events
| (PID) Process: | (3604) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ICM\Calibration |
| Operation: | write | Name: | DisplayCalibrator |
Value: %SystemRoot%\System32\DCCW.exe | |||
| (PID) Process: | (2540) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2540) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2540) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2540) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2752) ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2752) ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2752) ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2752) ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1856) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\16000009 |
| Operation: | write | Name: | Element |
Value: 01 | |||
Executable files
6
Suspicious files
36 434
Text files
3 318
Unknown types
1 090
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\CollectSignatures.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\AppCenter_R.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\CollectSignatures.aapp | binary | |
MD5:— | SHA256:— | |||
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\Restore-My-Files.txt | text | |
MD5:— | SHA256:— | |||
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Restore-My-Files.txt | text | |
MD5:— | SHA256:— | |||
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\Accessibility_R_RHP.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\1494870C-9912-C184-4CC9-B401-A53F4D8DE290.pdf.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\Actions_R_RHP.aapp.lockbit | binary | |
MD5:— | SHA256:— | |||
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\1494870C-9912-C184-4CC9-B401-A53F4D8DE290.pdf | binary | |
MD5:— | SHA256:— | |||
| 2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroApp\ENU\Accessibility_R_RHP.aapp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
16
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | 192.168.100.1:135 | — | — | — | unknown |
1632 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | 192.168.100.1:445 | — | — | — | unknown |
1632 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | 192.168.100.2:135 | — | — | — | whitelisted |
2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | 192.168.100.1:445 | — | — | — | unknown |
2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | 192.168.100.2:135 | — | — | — | whitelisted |
1632 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | 192.168.100.1:135 | — | — | — | unknown |
2752 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | 192.168.100.2:445 | — | — | — | whitelisted |
1632 | ed37bb51af01647fde0a5b04a401fd278eba50cf2d5d0678f86227d27aecbc62.exe | 192.168.100.2:445 | — | — | — | whitelisted |