| File name: | ed34b6bea2aff6dcfb67dac2666c7e7c47224ca6b84b9e1b0372ce60ae1e37cd.rar |
| Full analysis: | https://app.any.run/tasks/22184b18-5cc2-465d-8f45-2149f65595c2 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 01:59:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
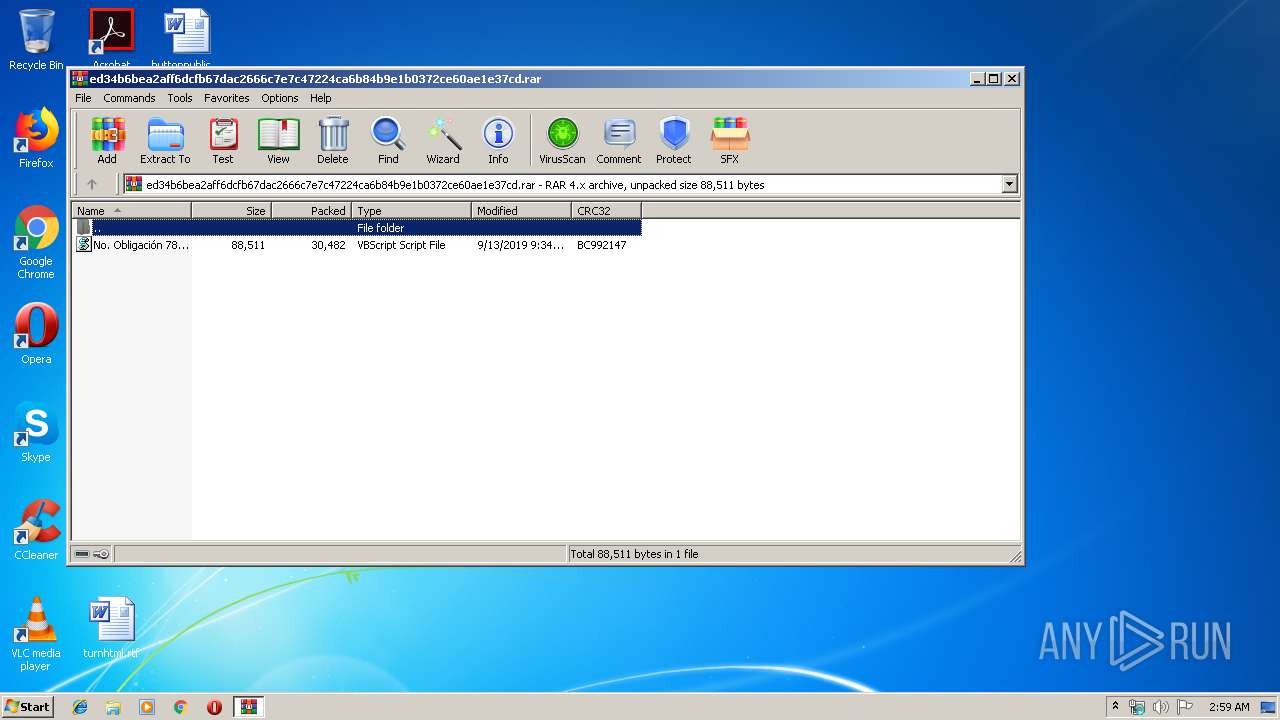
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 9521331F43984DC285394A975A3EA498 |
| SHA1: | E803D75AFA5485281BFD0CCD7AF7C4680EE38E4F |
| SHA256: | ED34B6BEA2AFF6DCFB67DAC2666C7E7C47224CA6B84B9E1B0372CE60AE1E37CD |
| SSDEEP: | 768:Cuh7eFahwk50KDXiDoLPibphmwGqf8ZP5Tp7rJ6W3TBnwy4ZKyiLe5qN:Cuh7eF+NDi0ebivqf8BVTuy4Z3Oe8N |
MALICIOUS
Writes to a start menu file
- wscript.exe (PID: 3132)
- WScript.exe (PID: 3456)
Changes the autorun value in the registry
- wscript.exe (PID: 3132)
- WScript.exe (PID: 3456)
SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 3456)
- wscript.exe (PID: 3132)
Executes scripts
- WScript.exe (PID: 3456)
Application launched itself
- WScript.exe (PID: 3456)
INFO
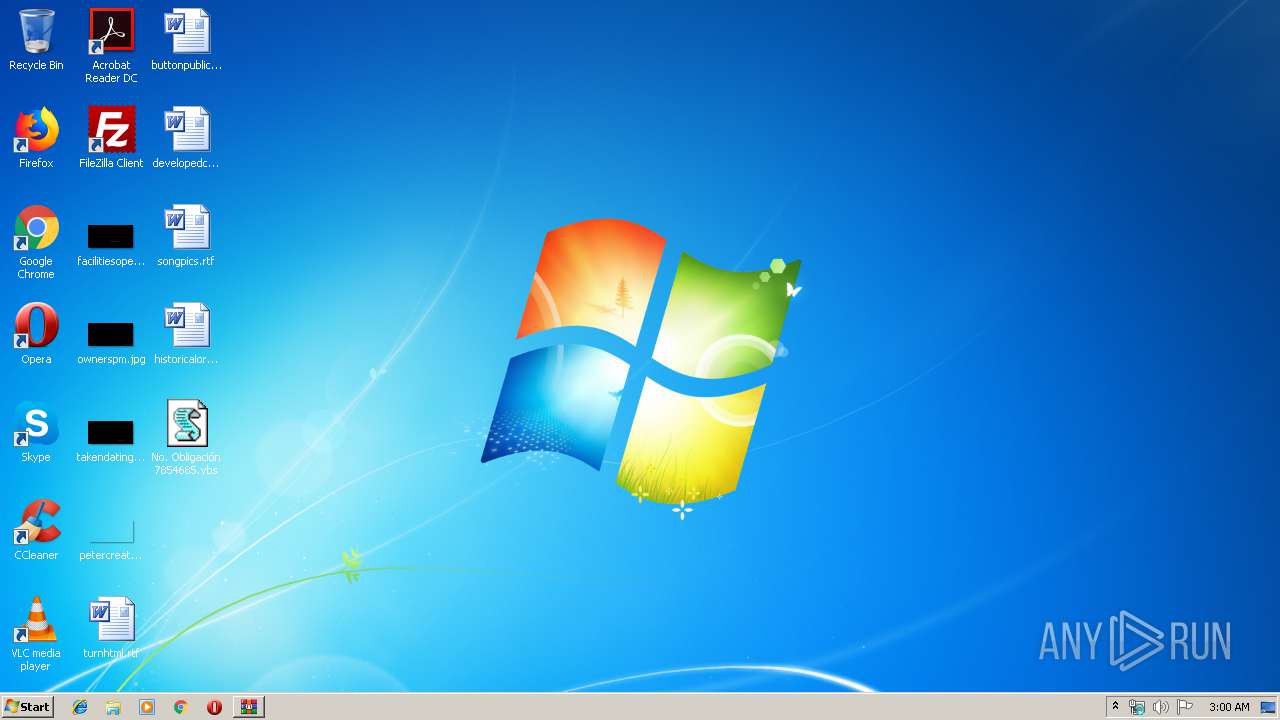
Manual execution by user
- WScript.exe (PID: 3456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 30540 |
|---|---|
| UncompressedSize: | 88511 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:09:13 09:34:25 |
| PackingMethod: | Normal |
| ArchivedFileName: | No. Obligaci?n 7854685.vbs |
Total processes
37
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2668 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\No. Obligación 7854685.vbs" | C:\Windows\System32\wscript.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3132 | "C:\Windows\System32\wscript.exe" //B "C:\Users\admin\AppData\Roaming\EoQJlUmqxx.vbs" | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3456 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\No. Obligación 7854685.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3484 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ed34b6bea2aff6dcfb67dac2666c7e7c47224ca6b84b9e1b0372ce60ae1e37cd.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
759
Read events
699
Write events
60
Delete events
0
Modification events
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ed34b6bea2aff6dcfb67dac2666c7e7c47224ca6b84b9e1b0372ce60ae1e37cd.rar | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (3484) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
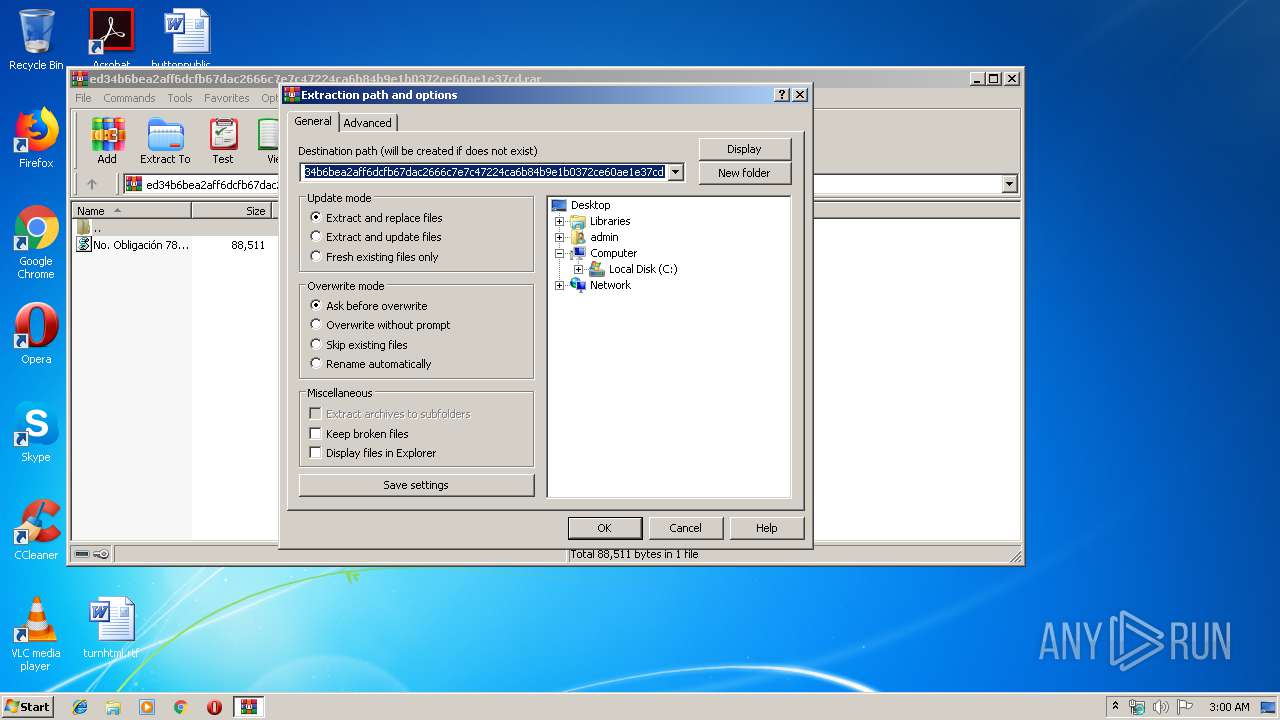
Value: C:\Users\admin\Desktop | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | WinRAR.exe | C:\Users\admin\Desktop\No. Obligación 7854685.vbs | text | |
MD5:— | SHA256:— | |||
| 3456 | WScript.exe | C:\Users\admin\AppData\Roaming\No. Obligación 7854685.vbs | text | |
MD5:— | SHA256:— | |||
| 3132 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\EoQJlUmqxx.vbs | text | |
MD5:— | SHA256:— | |||
| 3456 | WScript.exe | C:\Users\admin\AppData\Roaming\EoQJlUmqxx.vbs | text | |
MD5:— | SHA256:— | |||
| 3456 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\No. Obligación 7854685.vbs | text | |
MD5:— | SHA256:— | |||
| 3456 | WScript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3456 | WScript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3132 | wscript.exe | 79.134.225.73:3175 | britianica.uk.com | Andreas Fink trading as Fink Telecom Services | CH | malicious |
3456 | WScript.exe | 181.141.10.49:6660 | tocktekerickx32.duckdns.org | EPM Telecomunicaciones S.A. E.S.P. | CO | malicious |
— | — | 181.141.10.49:6660 | tocktekerickx32.duckdns.org | EPM Telecomunicaciones S.A. E.S.P. | CO | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
britianica.uk.com |
| unknown |
tocktekerickx32.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |