| File name: | simboot.exe |
| Full analysis: | https://app.any.run/tasks/540da8b6-20c2-4c83-aa84-61d60ffd69ce |
| Verdict: | Malicious activity |
| Analysis date: | June 01, 2021, 05:33:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 6F2BECC820F905BF3873066293D88DC7 |
| SHA1: | 30C77985F3FA80B1D799EEE8AF8AF0E9862F820A |
| SHA256: | ED1F0C706E61FF8C386531172557DDADCE59C80CF08CA17D0FAE56A32D84EC94 |
| SSDEEP: | 98304:Ea8cwzeoVnnRwx1FQJorgDXVnNnVisW9Th+6B66nD0PWnEPdAN+oB9s/NDHYcSvC:OcwzeoVnnRwx1FQJorgWhD6kaWnEqN+v |
MALICIOUS
Application was dropped or rewritten from another process
- 7zr.exe (PID: 3576)
Drops executable file immediately after starts
- simboot.exe (PID: 1720)
- 7zr.exe (PID: 3576)
SUSPICIOUS
Executable content was dropped or overwritten
- 7zr.exe (PID: 3576)
- simboot.exe (PID: 1720)
Drops a file that was compiled in debug mode
- 7zr.exe (PID: 3576)
Drops a file with a compile date too recent
- 7zr.exe (PID: 3576)
Drops a file with too old compile date
- 7zr.exe (PID: 3576)
INFO
Dropped object may contain Bitcoin addresses
- 7zr.exe (PID: 3576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
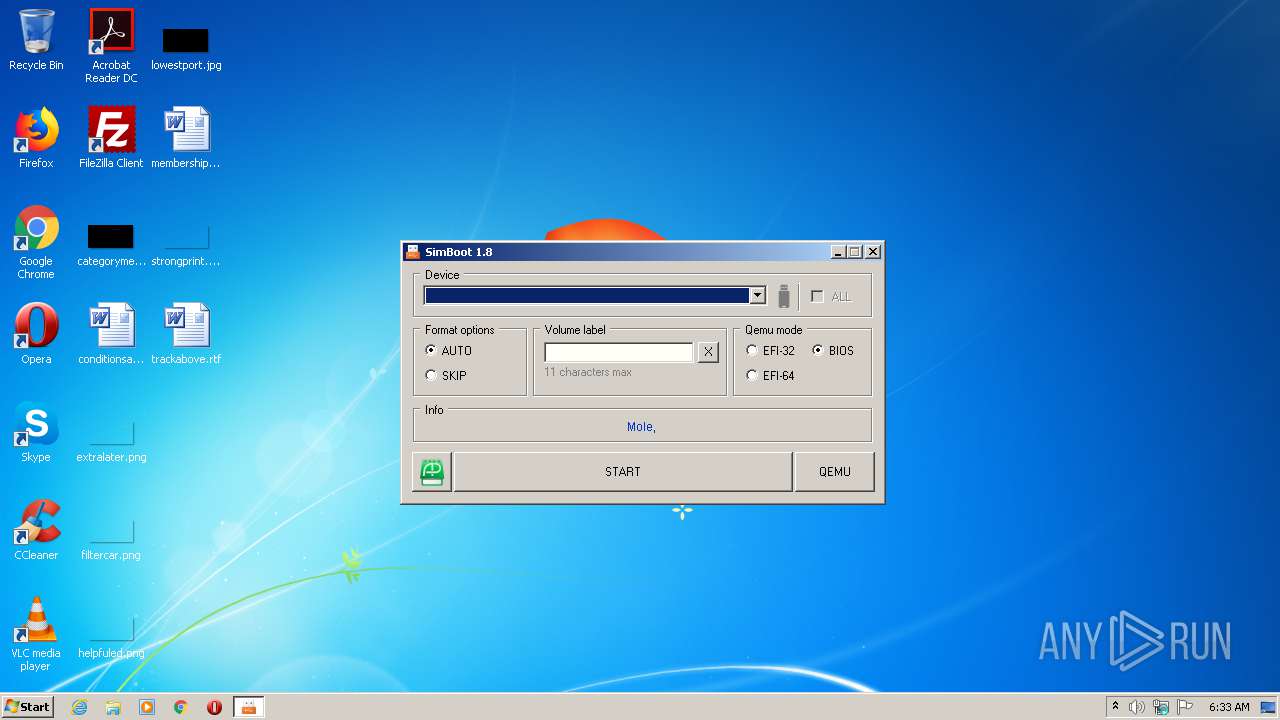
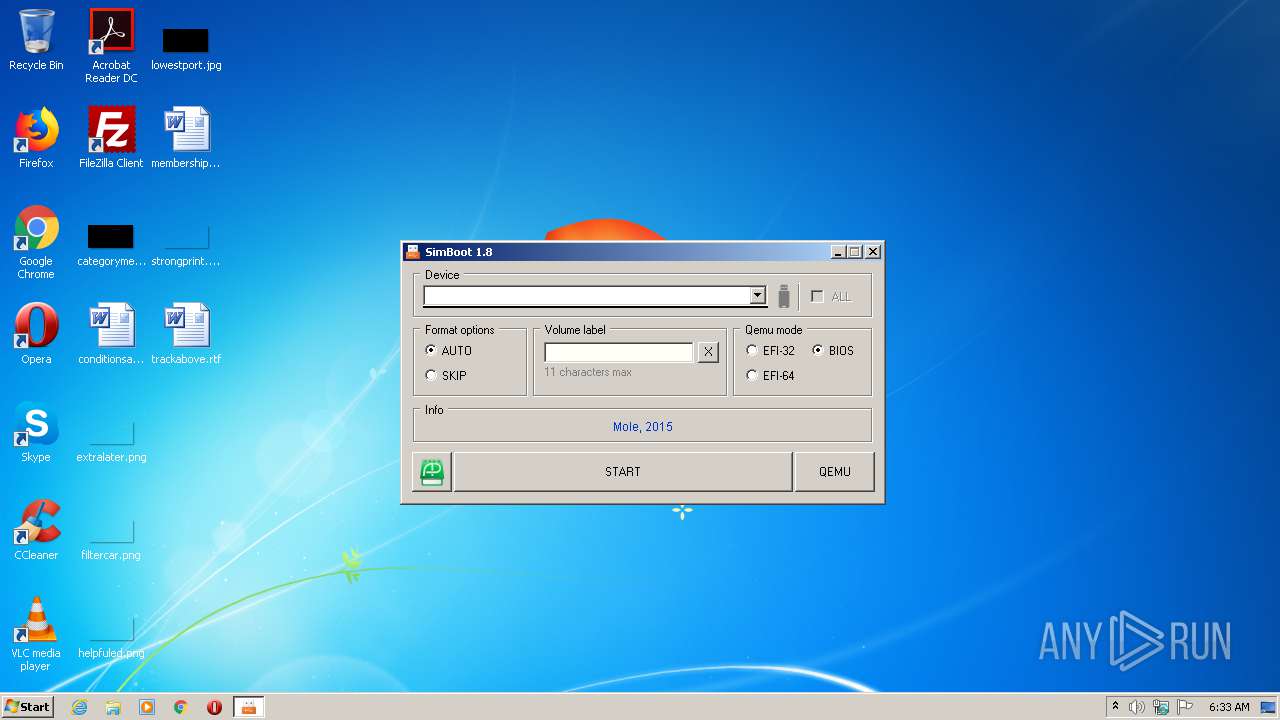
| ProductVersion: | 1.8 |
|---|---|
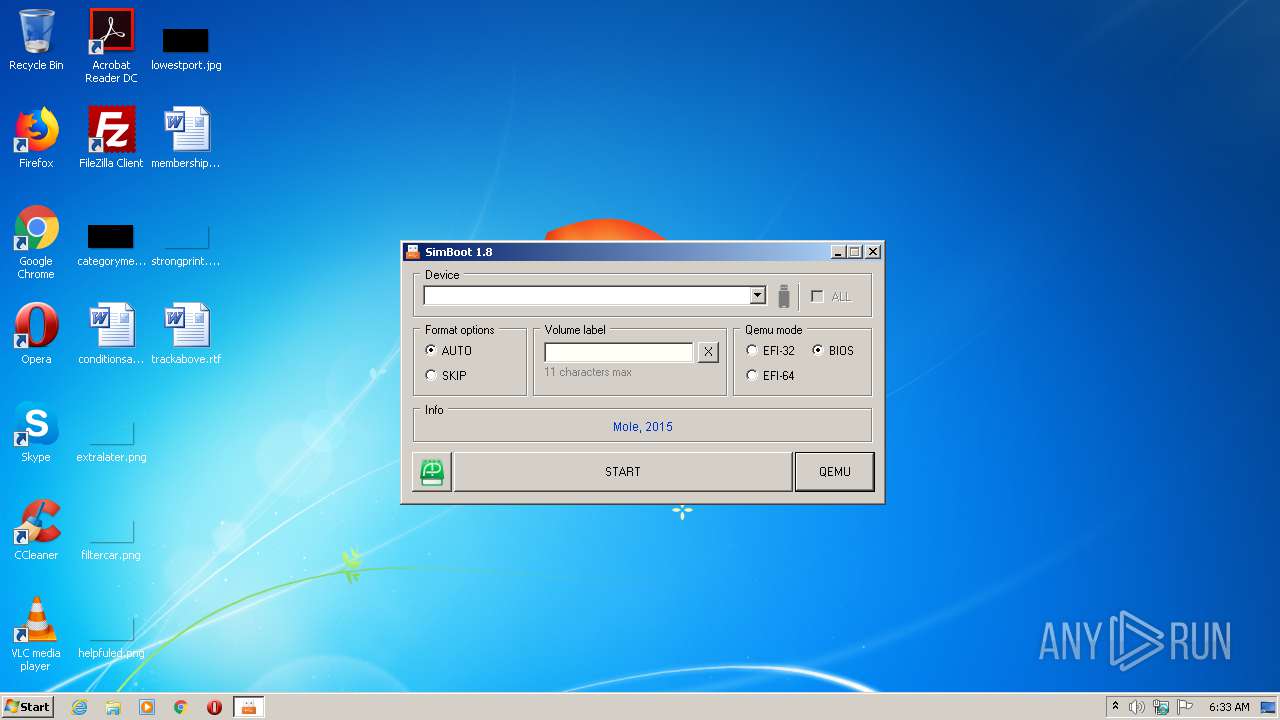
| ProductName: | SimBoot |
| OriginalFileName: | simboot.exe |
| LegalTrademarks: | Mole, 2015 |
| LegalCopyright: | © Mole, 2015 |
| InternalName: | simboot.exe |
| FileVersion: | 1.8.0.0 |
| FileDescription: | Simply Boot Flash Creator |
| CompanyName: | Mole, 2015 |
| CharacterSet: | Unicode |
| LanguageCode: | English (British) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.8.0.0 |
| FileVersionNumber: | 1.8.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x56bed0 |
| UninitializedDataSize: | 5337088 |
| InitializedDataSize: | 4812800 |
| CodeSize: | 348160 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2015:10:10 05:10:04+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Oct-2015 03:10:04 |
| Detected languages: |
|
| CompanyName: | Mole, 2015 |
| FileDescription: | Simply Boot Flash Creator |
| FileVersion: | 1.8.0.0 |
| InternalName: | simboot.exe |
| LegalCopyright: | © Mole, 2015 |
| LegalTrademarks: | Mole, 2015 |
| OriginalFilename: | simboot.exe |
| ProductName: | SimBoot |
| ProductVersion: | 1.8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 10-Oct-2015 03:10:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00517000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00518000 | 0x00055000 | 0x00054200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93455 |
.rsrc | 0x0056D000 | 0x00497000 | 0x00496200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99714 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.38312 | 944 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 5.4778 | 16936 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 5.41249 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 5.6347 | 4264 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 5.40245 | 2440 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 5.89476 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
35
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
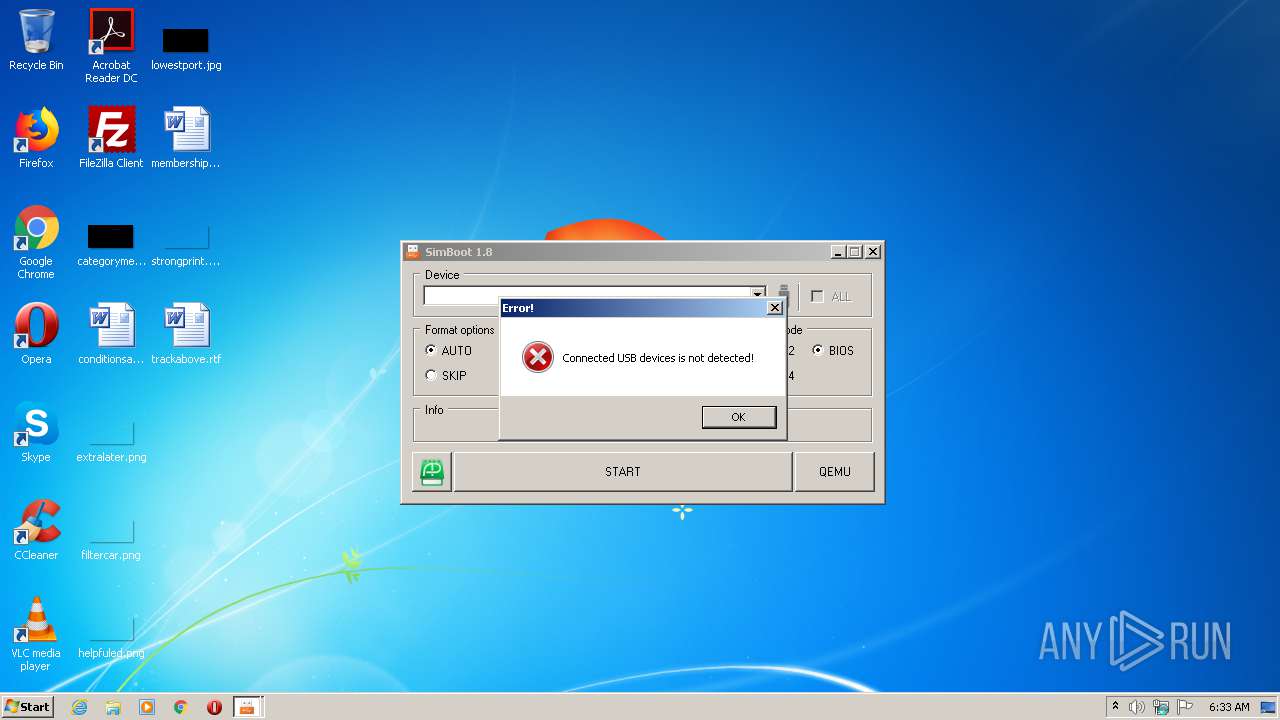
| 1720 | "C:\Users\admin\AppData\Local\Temp\simboot.exe" | C:\Users\admin\AppData\Local\Temp\simboot.exe | explorer.exe | ||||||||||||
User: admin Company: Mole, 2015 Integrity Level: MEDIUM Description: Simply Boot Flash Creator Exit code: 0 Version: 1.8.0.0 Modules
| |||||||||||||||
| 3576 | "C:\Users\admin\AppData\Local\Temp\5u0q0o9m\7zr.exe" x bin.7z -p20.9339868591621 -y | C:\Users\admin\AppData\Local\Temp\5u0q0o9m\7zr.exe | simboot.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Reduced Standalone Console Exit code: 0 Version: 15.08 beta Modules
| |||||||||||||||
Total events
1
Read events
1
Write events
0
Delete events
0
Modification events
Executable files
30
Suspicious files
1
Text files
14
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1720 | simboot.exe | C:\Users\admin\AppData\Local\Temp\aut3B8D.tmp | — | |
MD5:— | SHA256:— | |||
| 1720 | simboot.exe | C:\Users\admin\AppData\Local\Temp\aut3BAD.tmp | — | |
MD5:— | SHA256:— | |||
| 1720 | simboot.exe | C:\Users\admin\AppData\Local\Temp\5u0q0o9m\bin.7z | — | |
MD5:— | SHA256:— | |||
| 1720 | simboot.exe | C:\Users\admin\AppData\Local\Temp\5u0q0o9m\7zr.exe | executable | |
MD5:91C82DE1D6CCF7B5C1389B53FBC66B27 | SHA256:5115C095CD7F8884618252EB7CFDC3D34F85E8B6FA891CCFEFCC1183CEC710C6 | |||
| 3576 | 7zr.exe | C:\Users\admin\AppData\Local\Temp\5u0q0o9m\akelpad\AkelFiles\Docs\AkelHelp-Rus.htm | html | |
MD5:5CC29794A12AE27370880852F9307543 | SHA256:9BA6D99B2E26287FA090A18709DE5F084FEA93641D49CD673F6611651FFCCDDB | |||
| 3576 | 7zr.exe | C:\Users\admin\AppData\Local\Temp\5u0q0o9m\menu.lst | text | |
MD5:E5AFB18EAEC8DDB2AB27987B7DD16E6D | SHA256:69B3BFCA14065CAD11EF6C13A71910FA26B6D895BEFF8A3AEA8A80F23E0D92B3 | |||
| 3576 | 7zr.exe | C:\Users\admin\AppData\Local\Temp\5u0q0o9m\akelpad\AkelPad.ini | text | |
MD5:96FDDE692E98205585F36CD664253EDB | SHA256:57139DDD175A53591FC6A6DFD3F616D96F90805B2870E898BC98AD4DFDF1CE48 | |||
| 3576 | 7zr.exe | C:\Users\admin\AppData\Local\Temp\5u0q0o9m\akelpad\AkelFiles\Docs\AkelHelp-Eng.htm | html | |
MD5:9246B078DB096F6ACC77FA2F5262BC39 | SHA256:CE28B027E681AB640A3F095B19DAADA75DBC7CCB2DD37694962629586EE56727 | |||
| 3576 | 7zr.exe | C:\Users\admin\AppData\Local\Temp\5u0q0o9m\grldr | dsk | |
MD5:67C4D96145E5B54DA36D6F8D728F5ABB | SHA256:D61F672F052CAC3C09EE1233E8EE2F8708CC71A107A046BCCF6CE2DC802C2E26 | |||
| 3576 | 7zr.exe | C:\Users\admin\AppData\Local\Temp\5u0q0o9m\akelpad\AkelFiles\Plugs\Coder\grub4dos.coder | text | |
MD5:27931B6252BD392A47F92E8D4FC0632D | SHA256:BACA02F9ED72D3FC239291E46A1950BE770D9B20E943550508C2DCAA857EA186 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report