| File name: | snpvw.exe |
| Full analysis: | https://app.any.run/tasks/81728097-1d35-4046-8467-b20f66a1c032 |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2019, 13:25:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 2AEC4A3C7A1C928DEEB7D1E9B8779BB2 |
| SHA1: | 41A431279BF730C6EA0191C91370840DE38E5EBC |
| SHA256: | ED1B98952A38803166B76A526074F8928ED570B825BA048C310E3EC57079482C |
| SSDEEP: | 49152:qCf0Kv41pHlQ70bFJ0ap4m0iqxPhEjHIT:Tfr41pFTjOm07/a |
MALICIOUS
Changes the autorun value in the registry
- snpvw.exe (PID: 2876)
Application was dropped or rewritten from another process
- SNAPVIEW.EXE (PID: 1428)
- acmsetup.EXE (PID: 2992)
Loads dropped or rewritten executable
- acmsetup.EXE (PID: 2992)
SUSPICIOUS
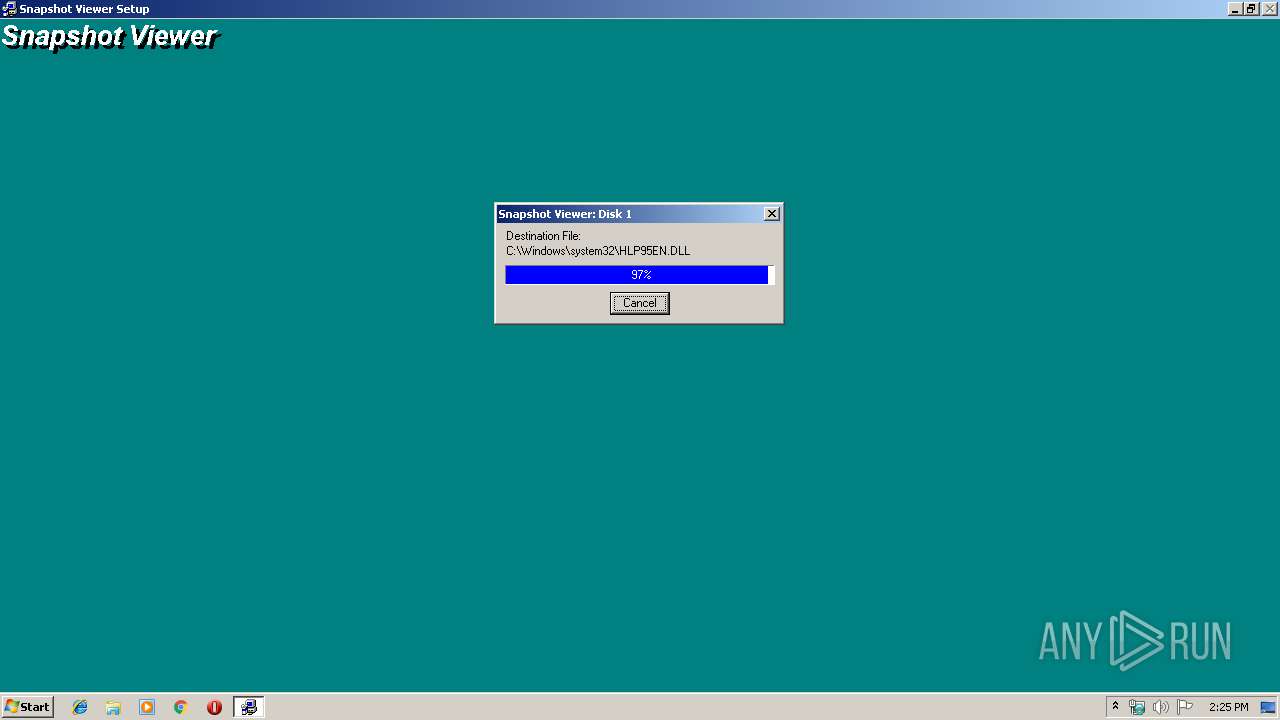
Executable content was dropped or overwritten
- snpvw.exe (PID: 2876)
- ntvdm.exe (PID: 3768)
- acmsetup.EXE (PID: 2992)
Executes application which crashes
- csrstub.exe (PID: 3748)
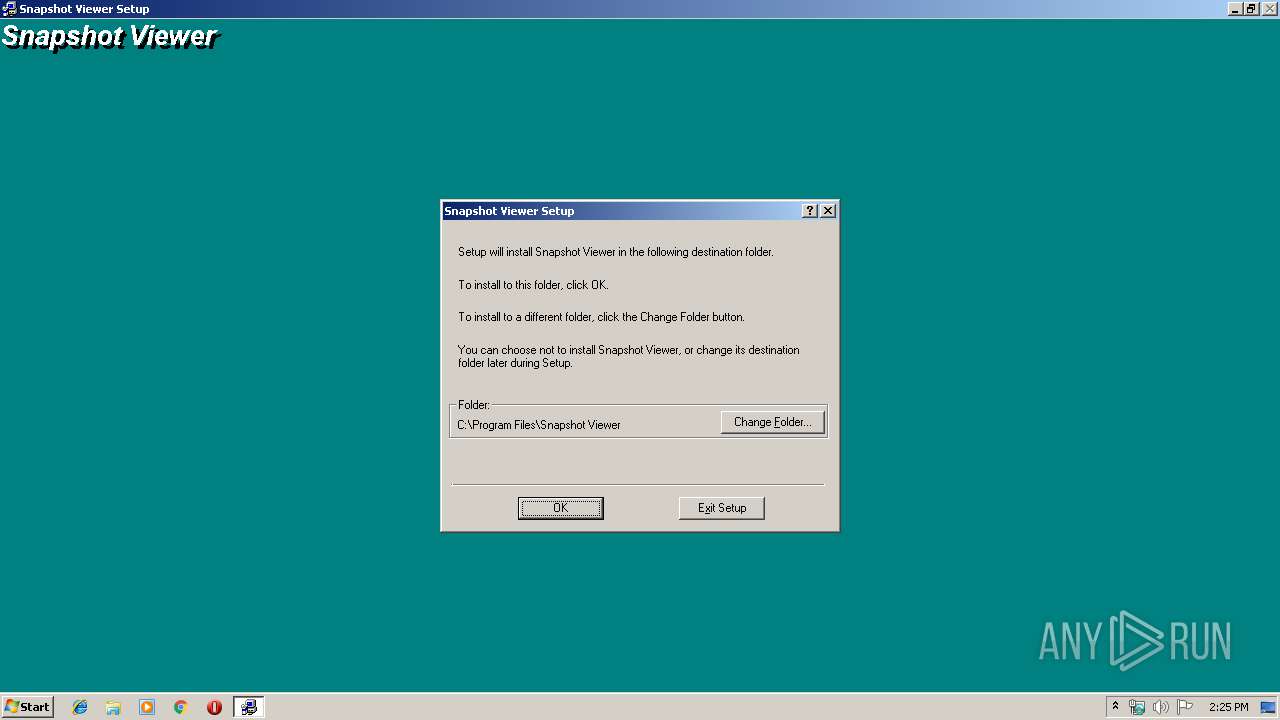
Creates files in the user directory
- acmsetup.EXE (PID: 2992)
Removes files from Windows directory
- acmsetup.EXE (PID: 2992)
Creates files in the program directory
- acmsetup.EXE (PID: 2992)
Modifies the open verb of a shell class
- acmsetup.EXE (PID: 2992)
- SNAPVIEW.EXE (PID: 1428)
Creates a software uninstall entry
- acmsetup.EXE (PID: 2992)
Creates files in the Windows directory
- acmsetup.EXE (PID: 2992)
INFO
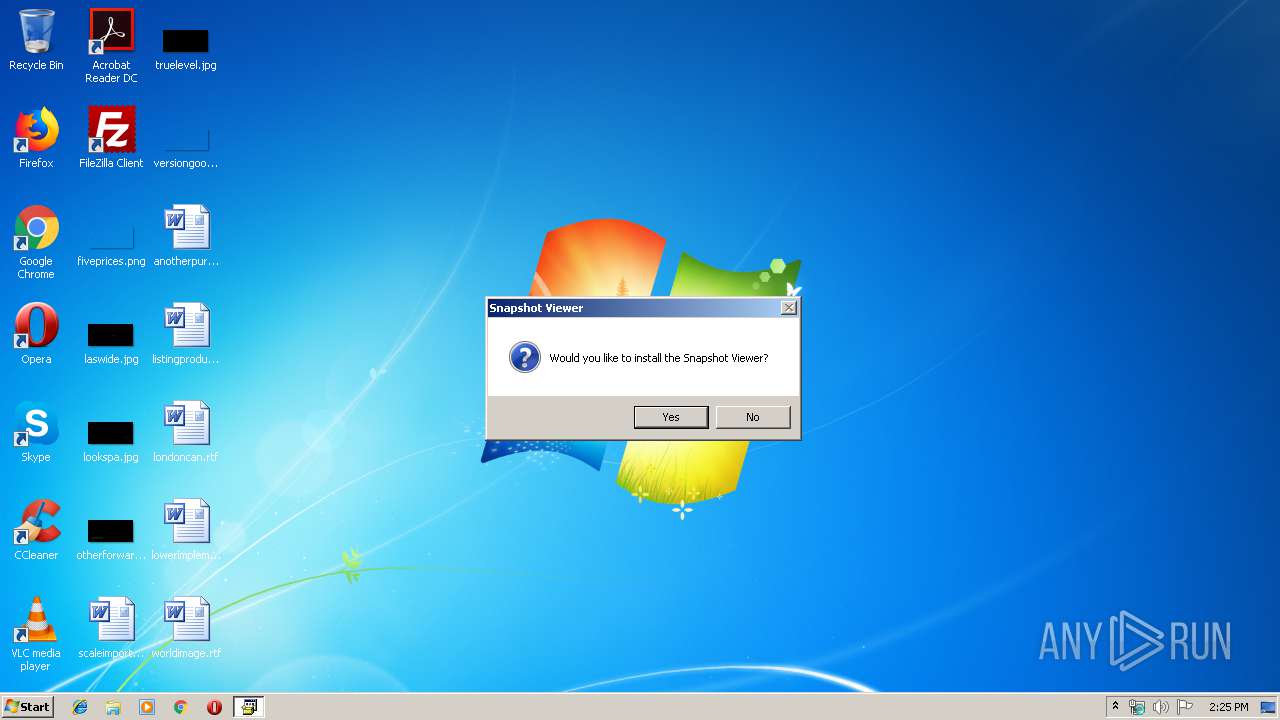
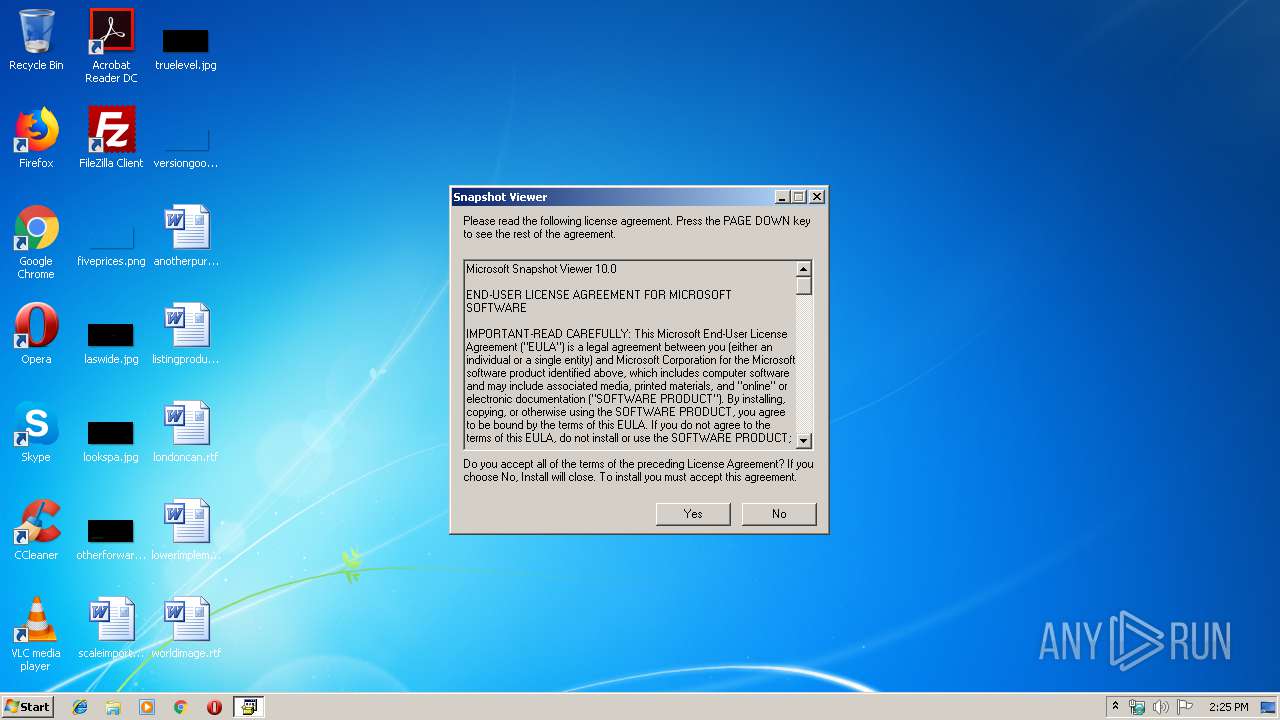
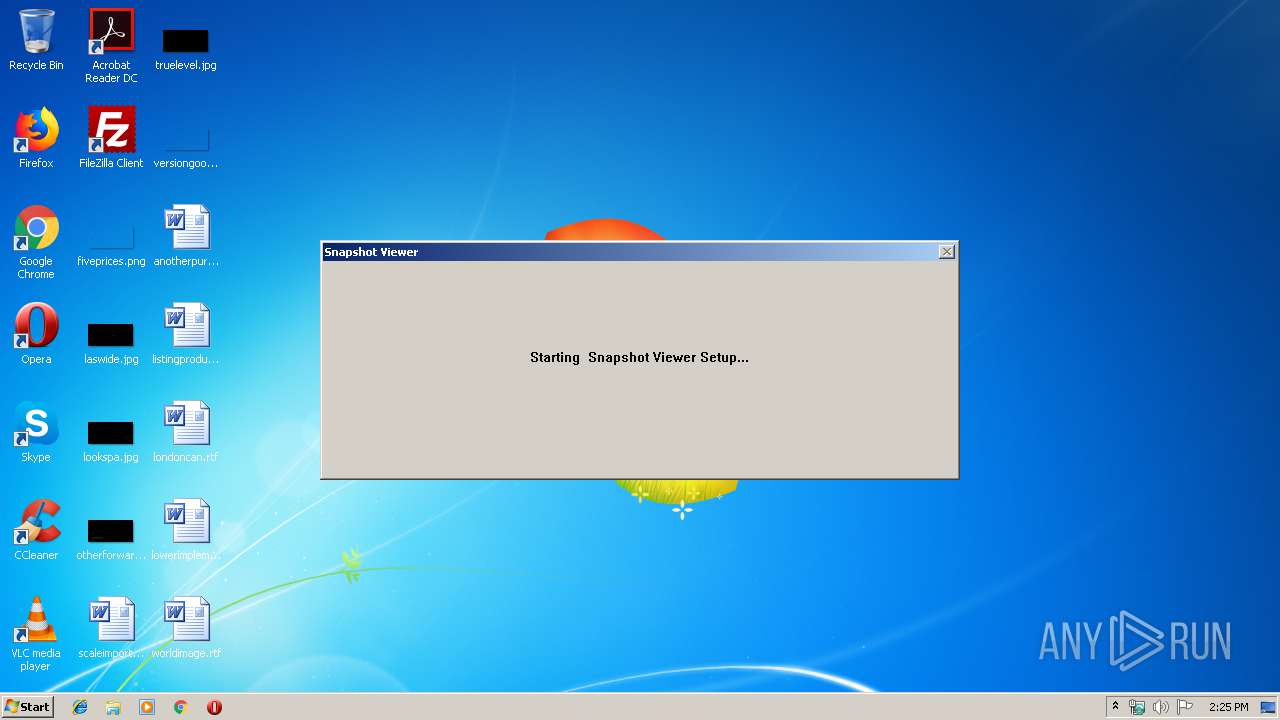
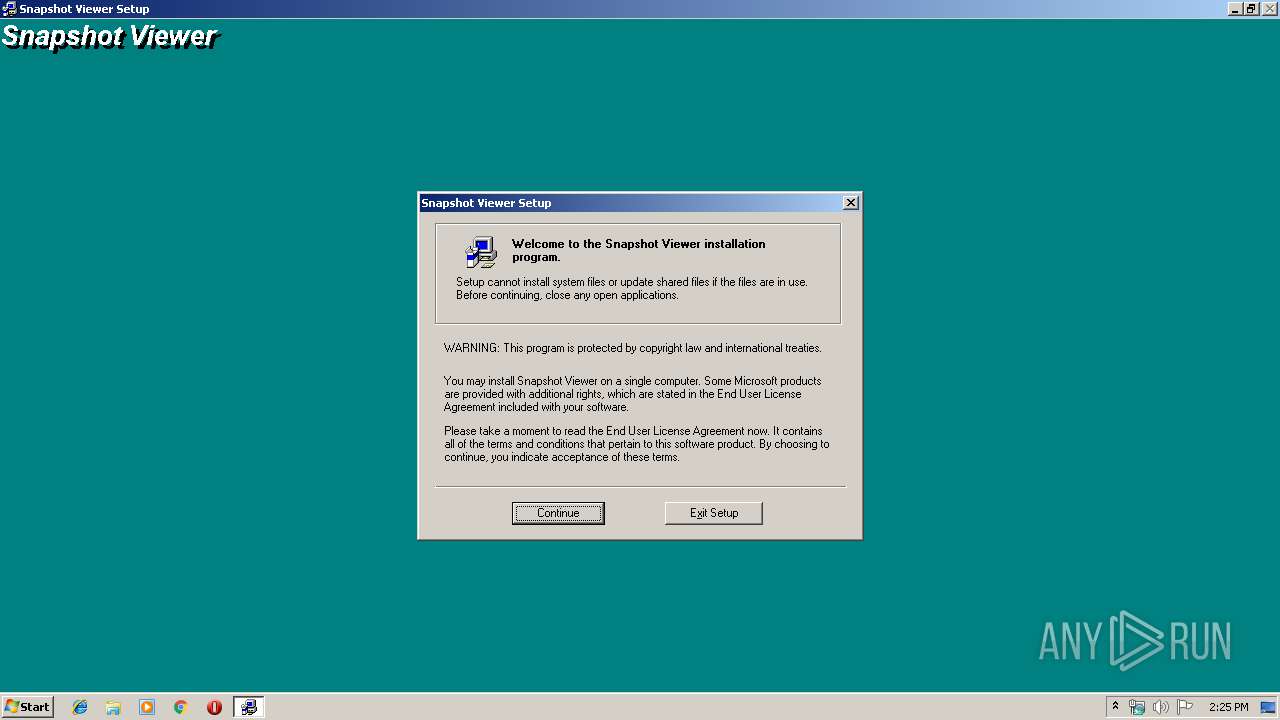
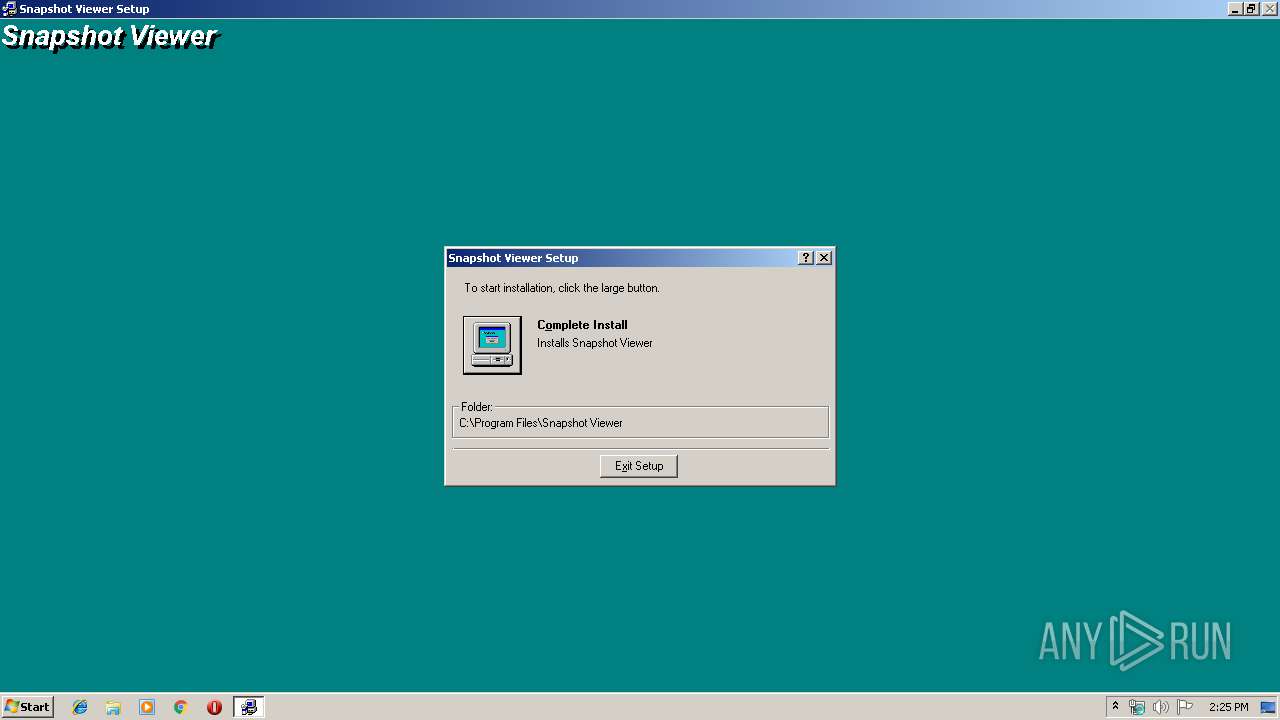
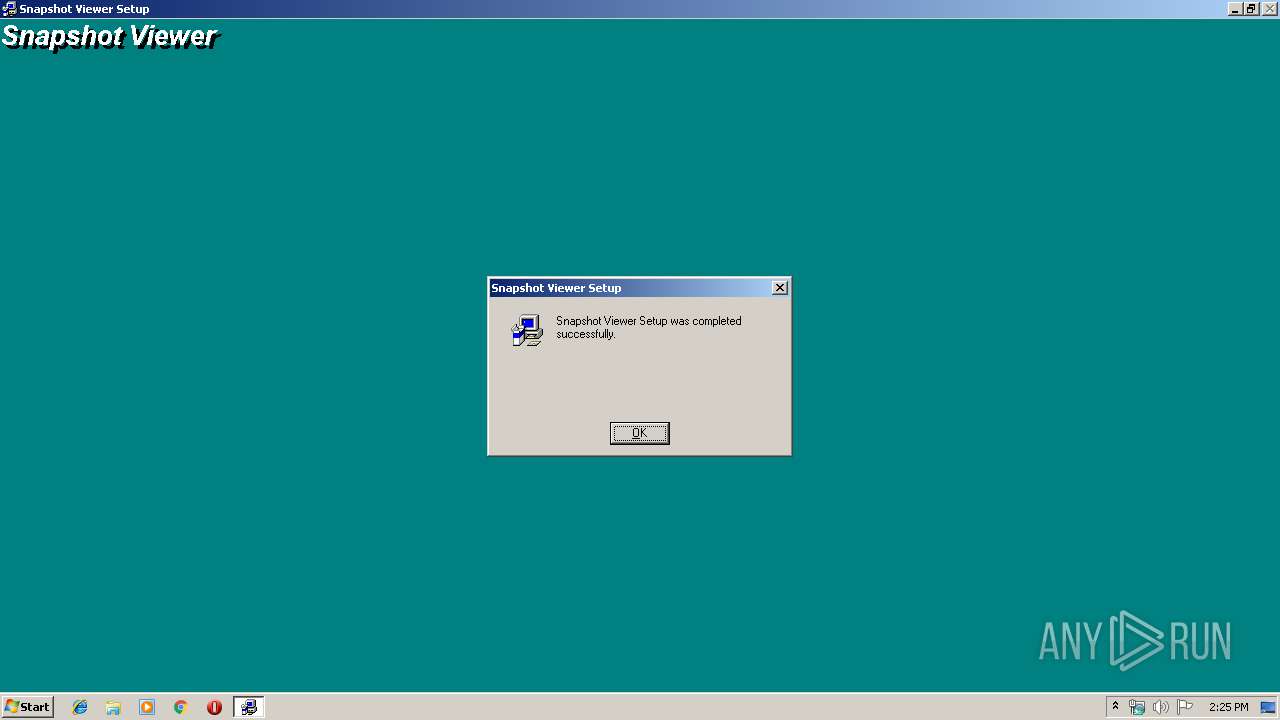
Manual execution by user
- SNAPVIEW.EXE (PID: 1428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Microsoft Update - Self Extracting Cabinet (38.1) |
|---|---|---|
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (34) |
| .exe | | | Win32 Executable MS Visual C++ 4.x (15.1) |
| .exe | | | InstallShield setup (4.8) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1997:01:10 14:11:29+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 3.1 |
| CodeSize: | 63488 |
| InitializedDataSize: | 1758720 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x65c0 |
| OSVersion: | 4 |
| ImageVersion: | 4 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.71.410.0 |
| ProductVersionNumber: | 4.71.410.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 4.71.0410.0 |
| InternalName: | Wextract |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1995 |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft(R) Windows NT(R) Operating System |
| ProductVersion: | 4.71.0410.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jan-1997 13:11:29 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 4.71.0410.0 |
| InternalName: | Wextract |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1995 |
| OriginalFilename: | WEXTRACT.EXE |
| ProductName: | Microsoft(R) Windows NT(R) Operating System |
| ProductVersion: | 4.71.0410.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 10-Jan-1997 13:11:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 2001 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F78C | 0x0000F800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50002 |
.data | 0x00011000 | 0x0000941C | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.89553 |
.rsrc | 0x0001B000 | 0x001A9000 | 0x001A8800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99241 |
.reloc | 0x001C4000 | 0x00001848 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.57693 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.40695 | 1000 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 3.53793 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 2.48958 | 140 | Latin 1 / Western European | English - United States | RT_STRING |
66 | 1.7646 | 64 | Latin 1 / Western European | English - United States | RT_STRING |
76 | 3.27164 | 1546 | Latin 1 / Western European | English - United States | RT_STRING |
77 | 3.30764 | 1524 | Latin 1 / Western European | English - United States | RT_STRING |
80 | 3.27174 | 1200 | Latin 1 / Western European | English - United States | RT_STRING |
82 | 3.24912 | 792 | Latin 1 / Western European | English - United States | RT_STRING |
83 | 3.26481 | 1272 | Latin 1 / Western European | English - United States | RT_STRING |
85 | 3.1621 | 1316 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
41
Monitored processes
5
Malicious processes
3
Suspicious processes
2
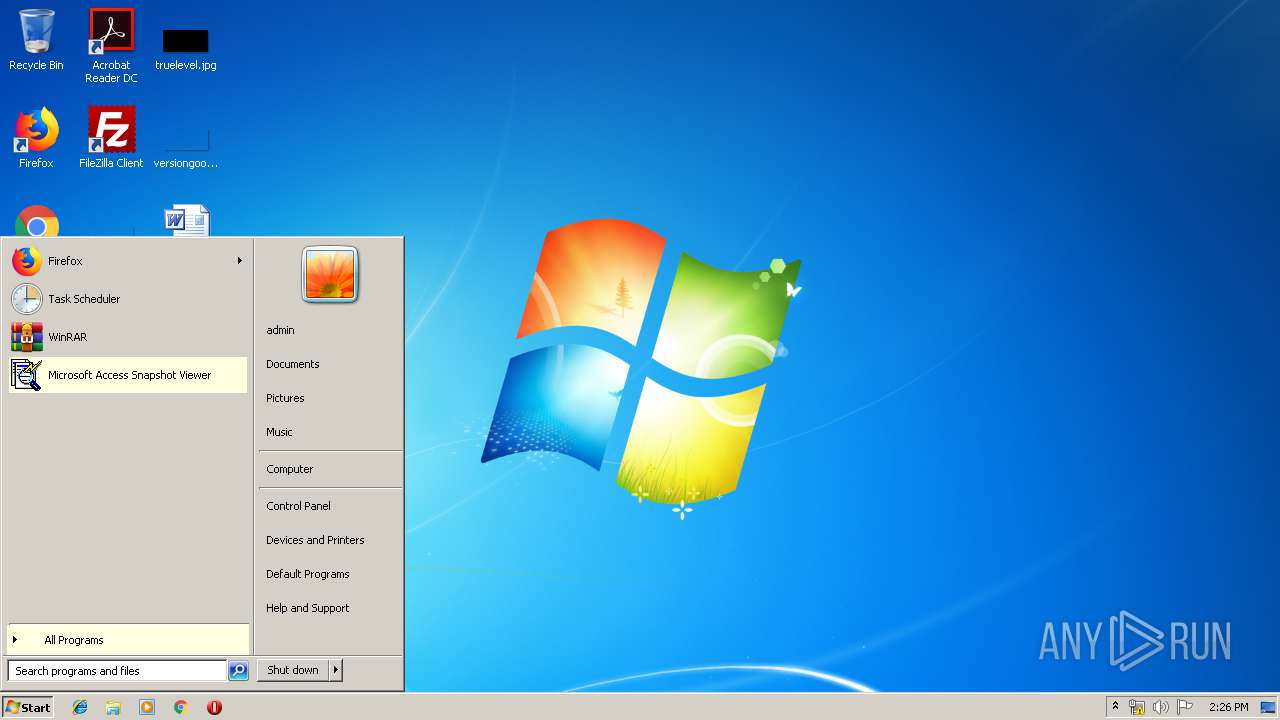
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | "C:\Program Files\Snapshot Viewer\SNAPVIEW.EXE" | C:\Program Files\Snapshot Viewer\SNAPVIEW.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Snapshot Viewer Application Exit code: 0 Version: 10.0.4622 Modules
| |||||||||||||||
| 2876 | "C:\Users\admin\AppData\Local\Temp\snpvw.exe" | C:\Users\admin\AppData\Local\Temp\snpvw.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.0410.0 Modules
| |||||||||||||||
| 2992 | C:\~MSSETUP.T\~msstfqf.t\acmsetup.EXE /T snap90.stf /S C:\USERS\ADMIN\APPDATA\LOCAL\TEMP\IXP000.TMP\ | C:\~MSSETUP.T\~msstfqf.t\acmsetup.EXE | ntvdm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Setup Tool Exit code: 0 Version: 3.01 Modules
| |||||||||||||||
| 3748 | csrstub.exe 525316 -P C:\Users\admin\AppData\Local\Temp\IXP000.TMP\setup.exe | C:\Windows\system32\csrstub.exe | snpvw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: allows lua to launch 16-bit applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3768 | "C:\Windows\system32\ntvdm.exe" -i1 -ws | C:\Windows\system32\ntvdm.exe | csrstub.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
275
Read events
174
Write events
91
Delete events
10
Modification events
| (PID) Process: | (2876) snpvw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: C:\Users\admin\AppData\Local\Temp\snpvw.exe /D:C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ | |||
| (PID) Process: | (2992) acmsetup.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MS Setup (ACME)\Bootstrapper\Exit Level |
| Operation: | write | Name: | |
Value: 2 | |||
| (PID) Process: | (2992) acmsetup.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MS Setup (ACME)\Bootstrapper\Exit Level |
| Operation: | write | Name: | |
Value: Running | |||
| (PID) Process: | (3768) ntvdm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MS Setup (ACME)\Bootstrapper\Exit Level |
| Operation: | write | Name: | |
Value: Running | |||
| (PID) Process: | (2992) acmsetup.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Snapshot Viewer |
| Operation: | write | Name: | DisplayName |
Value: Snapshot Viewer | |||
| (PID) Process: | (2992) acmsetup.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Snapshot Viewer |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Snapshot Viewer\Setup\Setup.exe /T snap90.stf | |||
| (PID) Process: | (2992) acmsetup.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Shared Tools\snapview.ocx |
| Operation: | write | Name: | Path |
Value: C:\Windows\system32\SNAPVIEW.OCX | |||
| (PID) Process: | (2992) acmsetup.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Shared Tools\snapview.ocx\Clients |
| Operation: | write | Name: | C:\Program Files\Snapshot Viewer\SNAPVIEW.EXE |
Value: | |||
| (PID) Process: | (2992) acmsetup.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\SNAPVIEW.OCX |
Value: 1 | |||
| (PID) Process: | (2992) acmsetup.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.SNP |
| Operation: | write | Name: | |
Value: SnapshotFile | |||
Executable files
15
Suspicious files
7
Text files
31
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsBAE8.tmp | — | |
MD5:— | SHA256:— | |||
| 3768 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsBAE9.tmp | — | |
MD5:— | SHA256:— | |||
| 3768 | ntvdm.exe | C:\~MSSETUP.T\~MSSTFQF.T\_MSSETUP._Q_ | text | |
MD5:— | SHA256:— | |||
| 2876 | snpvw.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\snap90.inf | text | |
MD5:4925D61CDF80CB2E07764A50AEFE7D4C | SHA256:491FB85A2E94FEA0E3C2C0778AA4B157F9FF4B0FBA561D966F5DA7717E7B0ECD | |||
| 2876 | snpvw.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\setup.exe | executable | |
MD5:D3F9F18A6FC60511CCF6E2D1EBDEE965 | SHA256:3F1F1431207DF98B3DB5D893624FC32B025271FE78BD73D94AB7BD60E4C30148 | |||
| 2876 | snpvw.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\setup.ini | binary | |
MD5:FA989EF5AC1BEF560EF661521311898A | SHA256:7DF27FA71D9F06E7FE45FA40D1D2BF8C9527ABE9D2F6DB281C1A249DCCA0F792 | |||
| 3768 | ntvdm.exe | C:\~MSSETUP.T\~MSSTFQF.T\LICENSE.TXT | text | |
MD5:261D27DCA015BA546B58997D5359FF11 | SHA256:493FC8403F45B45568DAB3AC80DCB785B9C97452C972C4DECDFFABDE01F0E238 | |||
| 2876 | snpvw.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\license.txt | text | |
MD5:261D27DCA015BA546B58997D5359FF11 | SHA256:493FC8403F45B45568DAB3AC80DCB785B9C97452C972C4DECDFFABDE01F0E238 | |||
| 2876 | snpvw.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\snap901.cab | compressed | |
MD5:7B258464C503E54375E201B3A6760C31 | SHA256:5F85963CDAC68C52DAF468EFB429D6B48F6E1453663DBC9EADEB274D69EB3220 | |||
| 3768 | ntvdm.exe | C:\~MSSETUP.T\~msstfqf.t\snap_bb.dll | executable | |
MD5:31FF6CA8527DA0AE00254BA96F19D213 | SHA256:0B60BB18A9F95BCF1D4DD7C818DC84A3260A52AACC6FDEB53E255B7A5A2DFED6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report