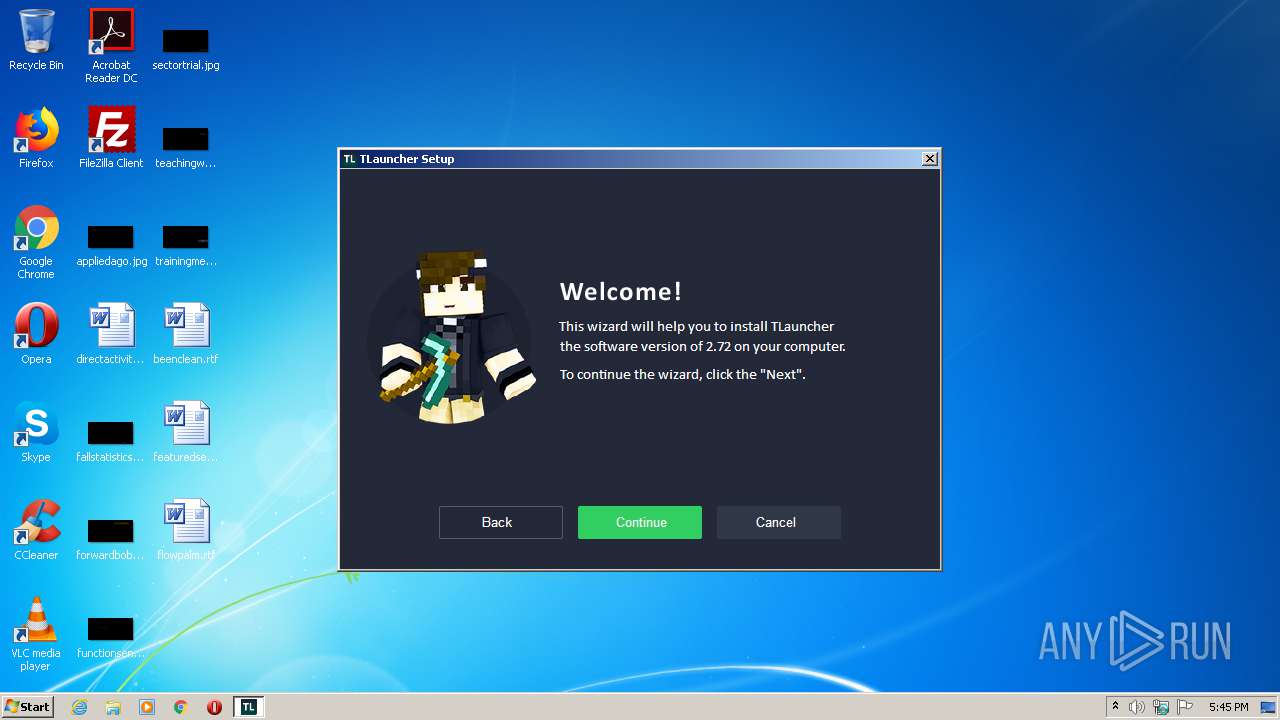
| File name: | TLauncher-2.72-Installer-0.5.2.exe |
| Full analysis: | https://app.any.run/tasks/f1f6d3f9-28ba-4905-aecd-a2ca772804df |
| Verdict: | Malicious activity |
| Analysis date: | September 04, 2020, 16:45:09 |
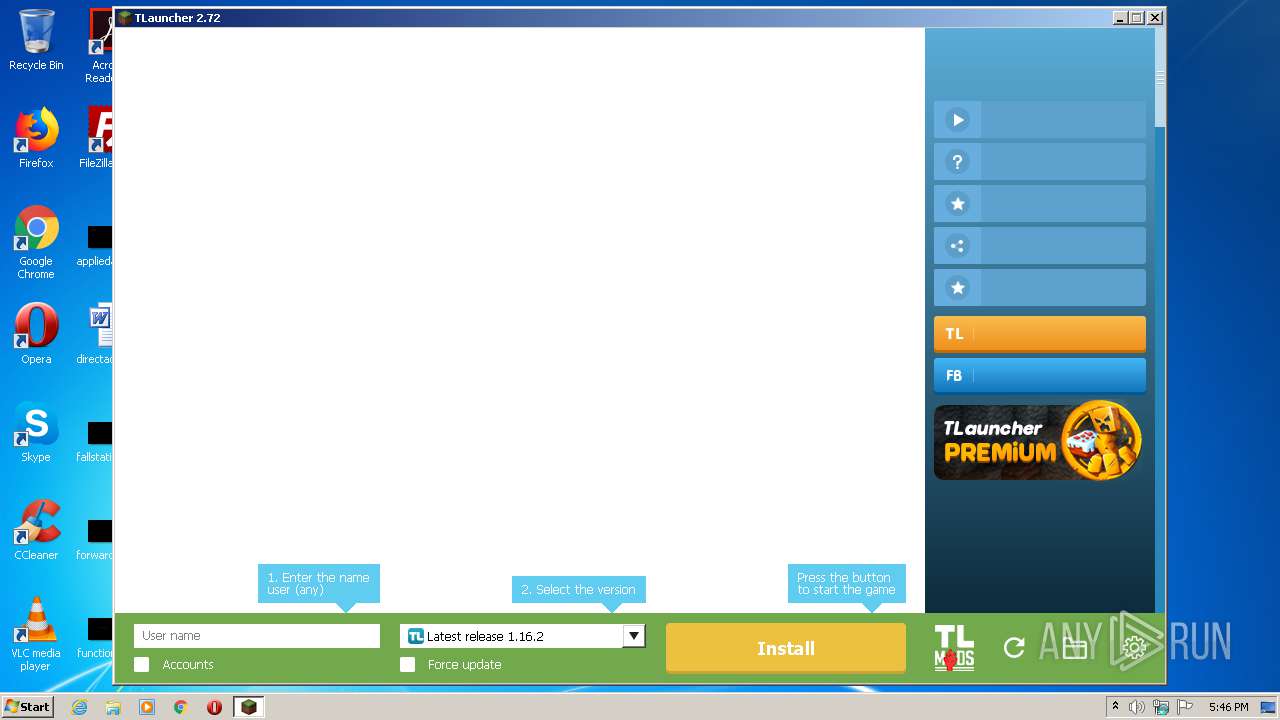
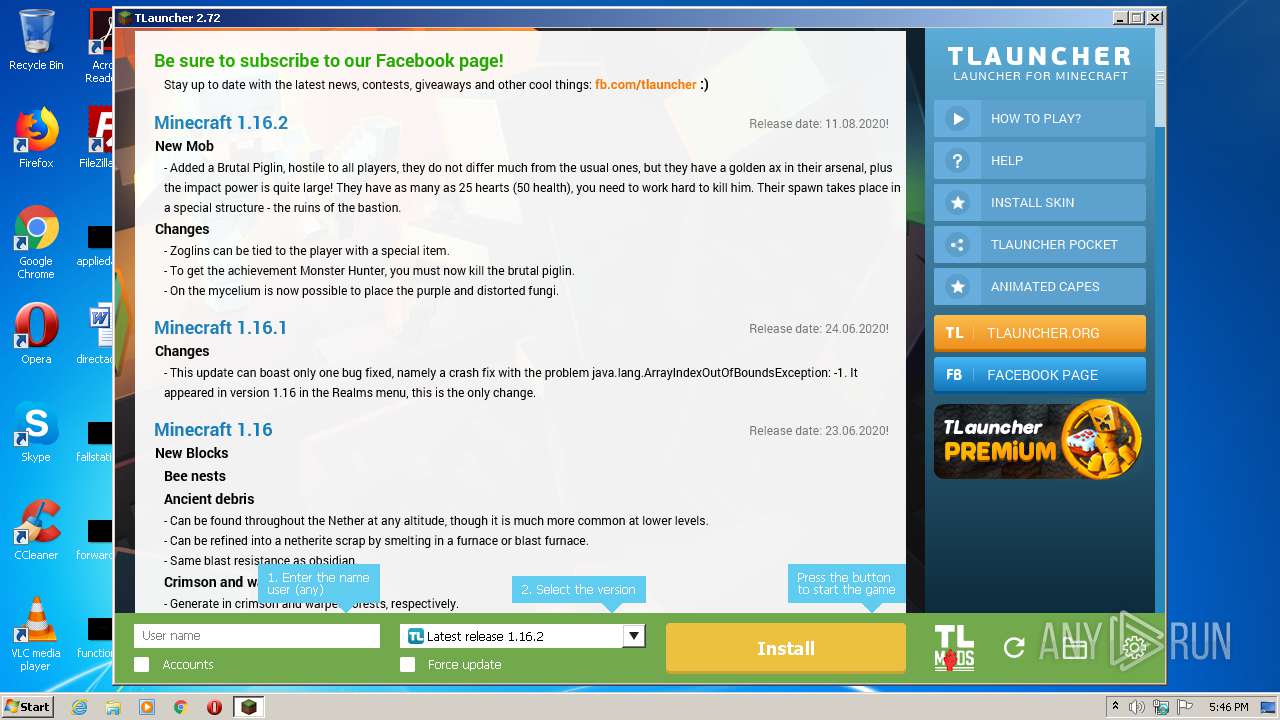
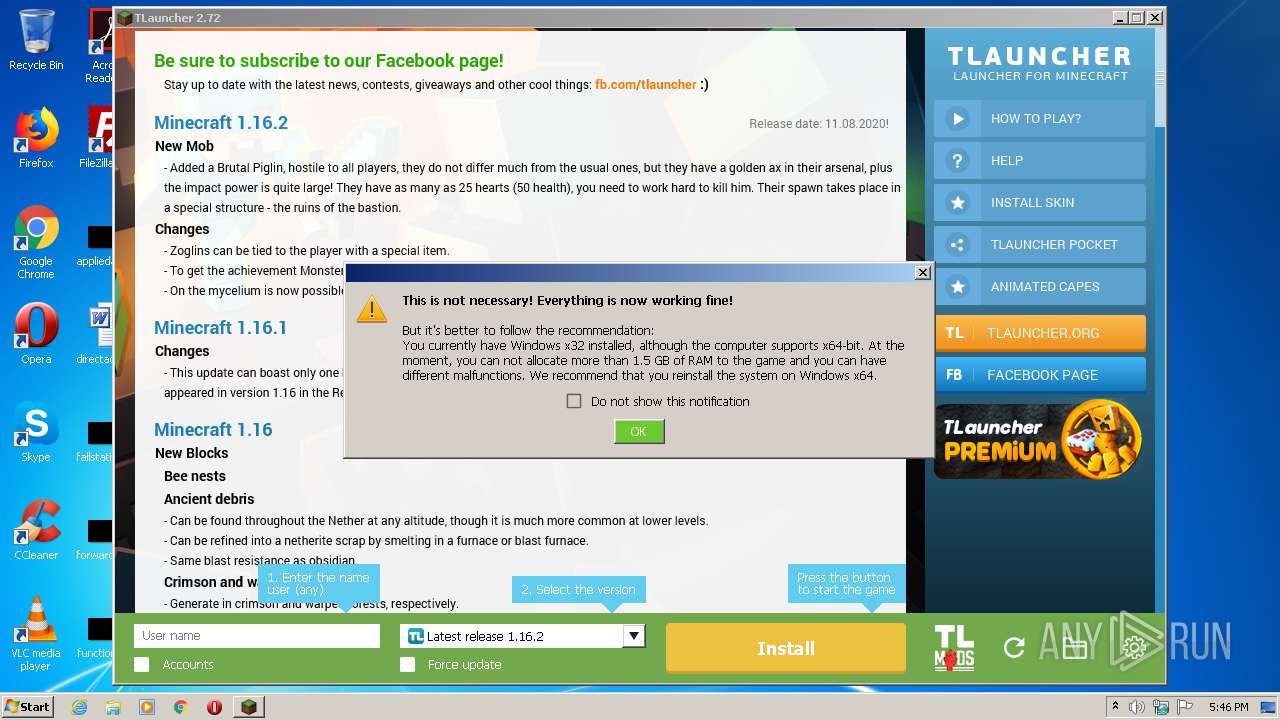
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 77CF6ABDC003148F0661C8C37BAE62C2 |
| SHA1: | 831EF726CA5AAF945CCEE509EEB6E5AFE0446059 |
| SHA256: | ED0F21AA98BBE5058C8E2E1AF33A1BB0BCBED8DC404BEA9215EBBB7C2EDAF25F |
| SSDEEP: | 393216:QXv7fsD441ffz4e4oQL14BIzAtdB7l9eN7r570hM:Q/7+1Hz4e4txzuB7l9o57eM |
MALICIOUS
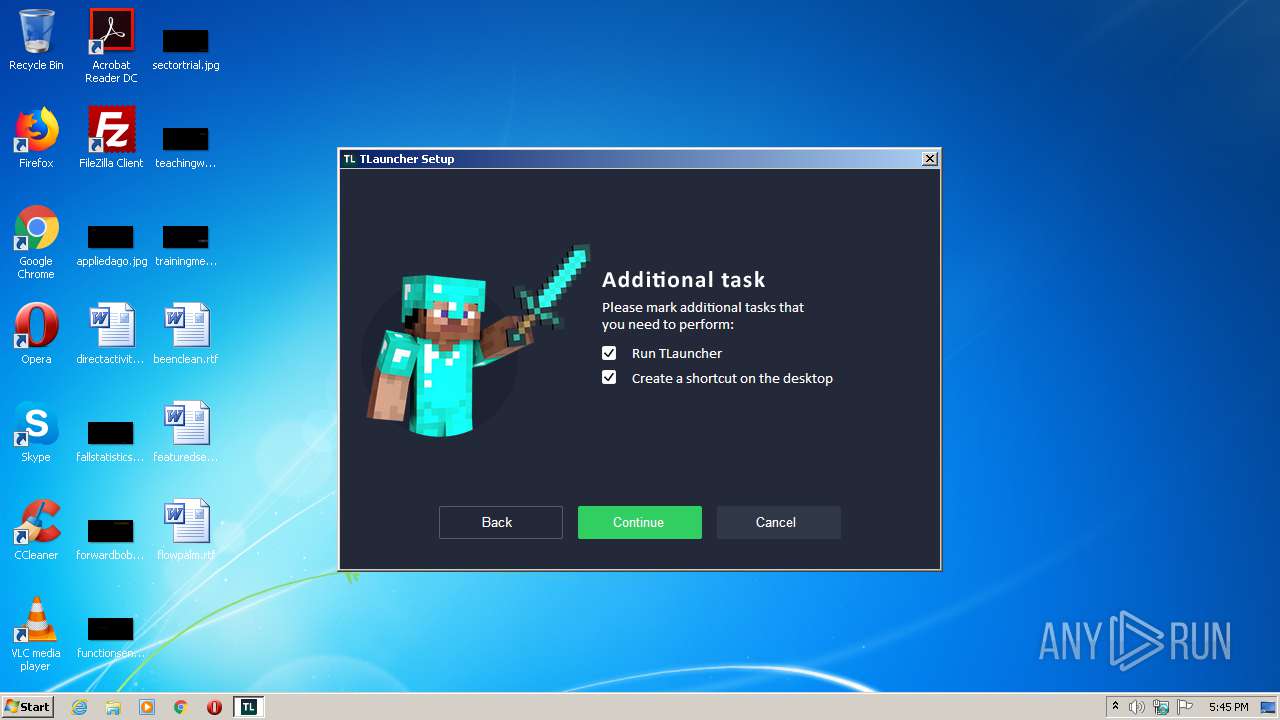
Application was dropped or rewritten from another process
- irsetup.exe (PID: 3964)
- TLauncher.exe (PID: 1936)
Loads dropped or rewritten executable
- irsetup.exe (PID: 3964)
SUSPICIOUS
Reads internet explorer settings
- irsetup.exe (PID: 3964)
Executable content was dropped or overwritten
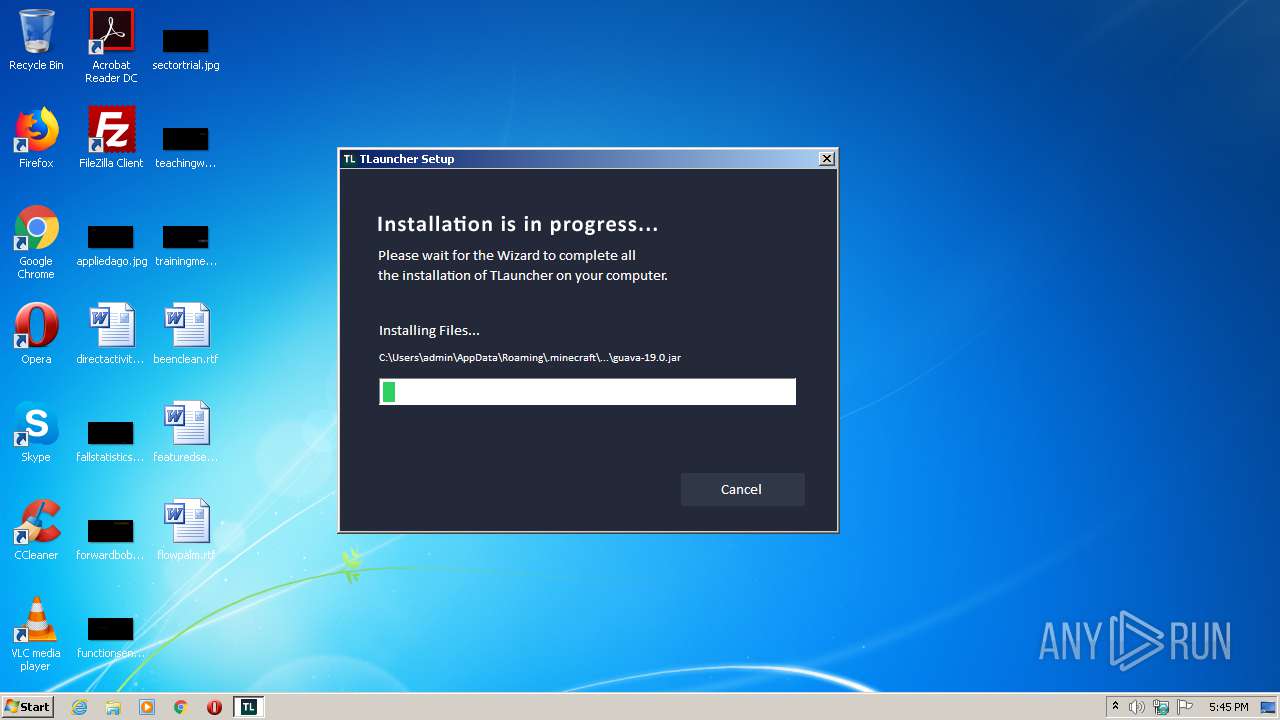
- TLauncher-2.72-Installer-0.5.2.exe (PID: 1876)
- irsetup.exe (PID: 3964)
Executes JAVA applets
- TLauncher.exe (PID: 1936)
- javaw.exe (PID: 2960)
Reads Internet Cache Settings
- irsetup.exe (PID: 3964)
Creates files in the user directory
- javaw.exe (PID: 2960)
- irsetup.exe (PID: 3964)
- dxdiag.exe (PID: 876)
- javaw.exe (PID: 4056)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 2960)
- javaw.exe (PID: 4056)
Starts application with an unusual extension
- cmd.exe (PID: 2592)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 2348)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2592)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 2348)
Application launched itself
- javaw.exe (PID: 2960)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 3152)
INFO
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 4056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.8) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (36.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (9) |
| .exe | | | Win32 Executable (generic) (6.1) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:03 20:13:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 23552 |
| InitializedDataSize: | 142336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2ce1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.5.2.0 |
| ProductVersionNumber: | 2.72.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | TLauncher Setup |
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher Setup |
| FileVersion: | 0.5.2.0 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Copyright © 2020 |
| LegalTrademarks: | TLauncher |
| OriginalFileName: | suf_launch.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.72.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jan-2019 19:13:08 |
| Detected languages: |
|
| Comments: | TLauncher Setup |
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher Setup |
| FileVersion: | 0.5.2.0 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Copyright © 2020 |
| LegalTrademarks: | TLauncher |
| OriginalFilename: | suf_launch.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.72.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Jan-2019 19:13:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A18 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40733 |
.rdata | 0x00007000 | 0x00002F54 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05968 |
.data | 0x0000A000 | 0x00001968 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.59807 |
.rsrc | 0x0000C000 | 0x0001DDCC | 0x0001DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.50313 |
.reloc | 0x0002A000 | 0x000010D0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.81847 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.37674 | 1413 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.87454 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.04321 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.10433 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.15069 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.24063 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.45174 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.39733 | 1720 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.52276 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.9892 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
74
Monitored processes
26
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | wmic qfe get HotFixID | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 464 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | dxdiag /whql:off /t C:\Users\admin\AppData\Roaming\.minecraft\logs\tlauncher\dxdiag.txt | C:\Windows\system32\dxdiag.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft DirectX Diagnostic Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | wmic CPU get NAME | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1492 | wmic os get osarchitecture | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1676 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
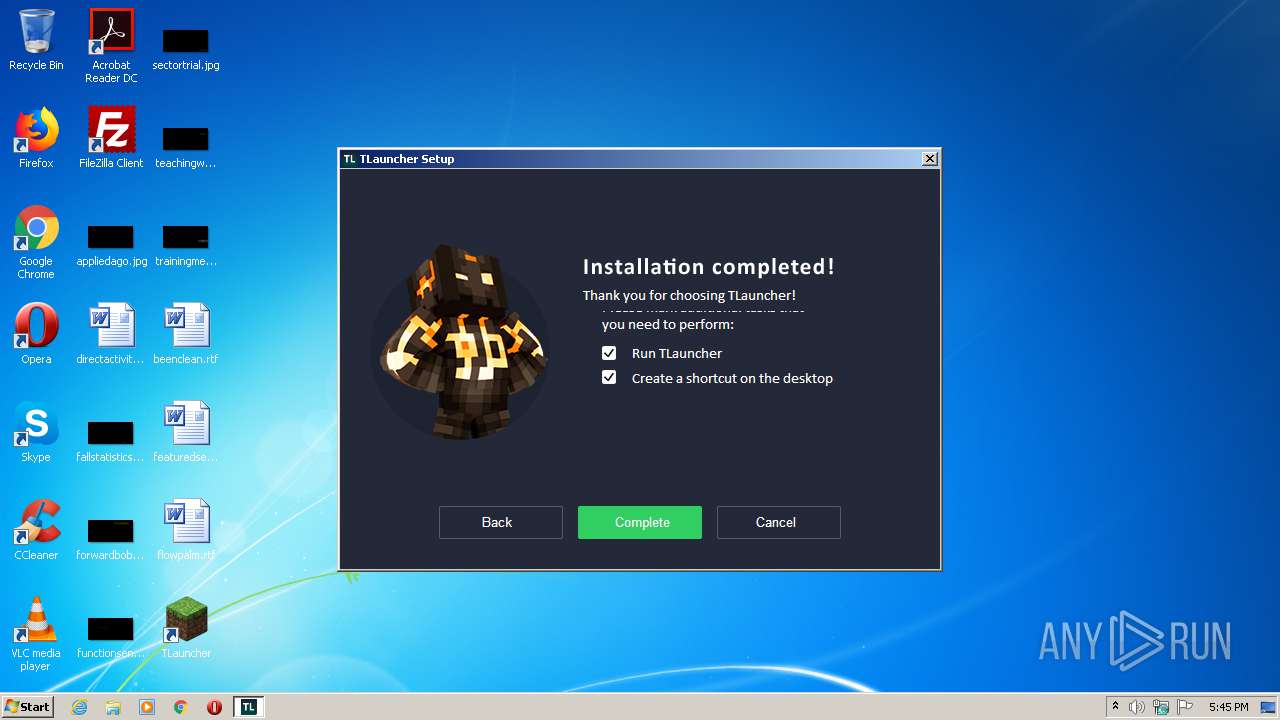
| 1876 | "C:\Users\admin\AppData\Local\Temp\TLauncher-2.72-Installer-0.5.2.exe" | C:\Users\admin\AppData\Local\Temp\TLauncher-2.72-Installer-0.5.2.exe | explorer.exe | ||||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Setup Exit code: 0 Version: 0.5.2.0 Modules
| |||||||||||||||
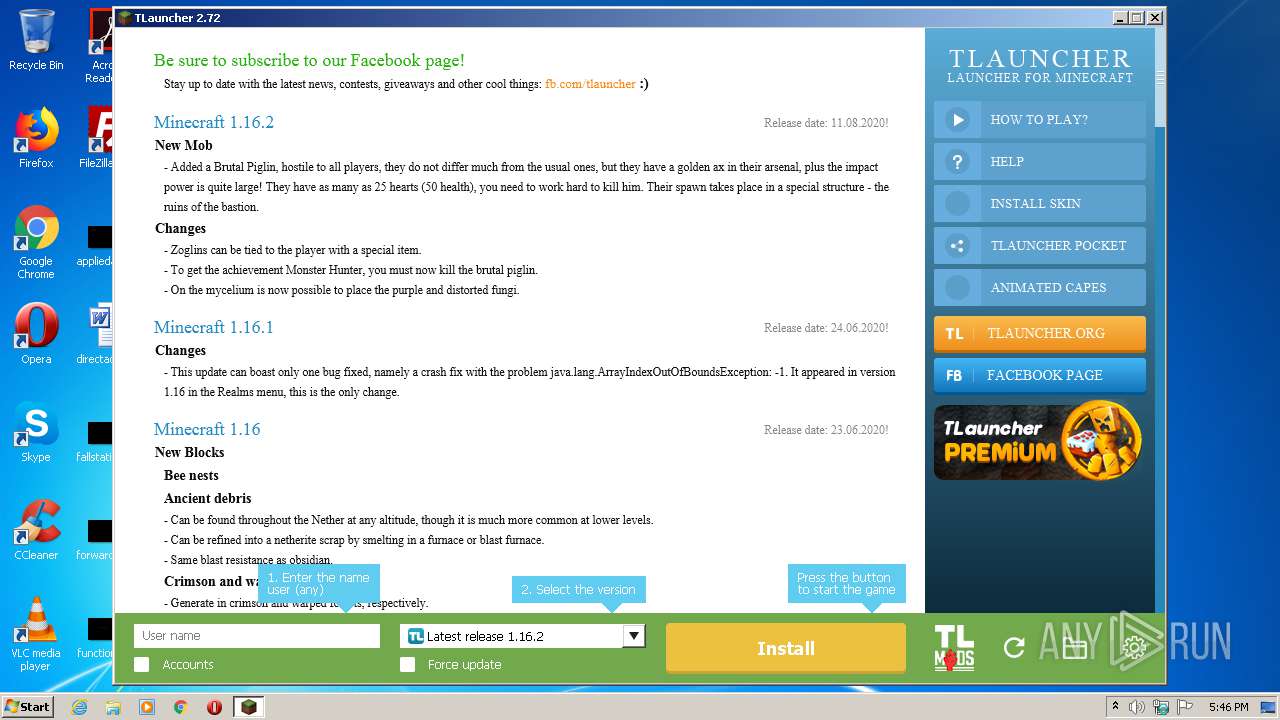
| 1936 | "C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe" | C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe | — | irsetup.exe | |||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Exit code: 0 Version: 2.72 Modules
| |||||||||||||||
| 2084 | cmd.exe /C chcp 437 & dxdiag /whql:off /t C:\Users\admin\AppData\Roaming\.minecraft\logs\tlauncher\dxdiag.txt | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2152 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 673
Read events
1 489
Write events
168
Delete events
16
Modification events
| (PID) Process: | (1876) TLauncher-2.72-Installer-0.5.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1876) TLauncher-2.72-Installer-0.5.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3964) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3964) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3964) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3964) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3964) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2960) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (4056) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4056) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
Executable files
10
Suspicious files
21
Text files
249
Unknown types
1 567
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG15.PNG | image | |
MD5:41BD19D49E2B1CA67523A06F565A4115 | SHA256:5F5CEBDAEB6911715E84293322281D4D1B400DB94F5F047C238E66B2312BA05B | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG17.PNG | image | |
MD5:867D39D8C43F6EDCDB19866EC05EC5FA | SHA256:DBDA640FDF9C9F5ABF97CD8AC33C11317E72448BFD79CDE124D877B0C34F7DA0 | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG11.PNG | image | |
MD5:4F7EE9256A02B1E219492BDF68DB9C67 | SHA256:A58F4BBC25BC0F7B10EE3201BFBB92CD6DFD27AD56F47B7F67AA8D4D3DAF12DF | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG14.PNG | image | |
MD5:0E2AADF17D0BC01F2AC22BF2A73F1EDA | SHA256:5435BA22F50A7CF9C6427A6E7B124A1D60436446BB9484A36FA07FAFD787DC61 | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG16.PNG | image | |
MD5:789613E319BA2649AF0D1F0D1398A10E | SHA256:8C70463E34BF7C8AA85A6B9366BE072E32547CD88A78B27B664C76C0546E436C | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG12.PNG | image | |
MD5:CABCC2139F639B0E355465EEFB80C62A | SHA256:D043C1BF944933CAC3401ED68386E1B5301DA8C9CA244FCCED2A77BD60C106B7 | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG10.PNG | image | |
MD5:478E9A6E6320B245268E3AF7603EAF91 | SHA256:9C76BDA2D5F5AF4C6BEE08696F419C25BDDDCF53C4E8136324B0E76DCD2A80E8 | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG2.PNG | image | |
MD5:3D4E6A58A77DEC97CB3011D9CFC9C414 | SHA256:4034EC229B72BE7E38B3E66A9A07CF1B192C28A92BA790E36CFD1FADD5880E81 | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG8.PNG | image | |
MD5:7E26B5D6E8FE479C2B4805E06B3F6324 | SHA256:B19494EF5CE0897E9FBD8C8765054B55661CD32A8ED910B8372B495259A81BA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 781
TCP/UDP connections
23
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4056 | javaw.exe | HEAD | 200 | 104.20.87.142:80 | http://page.tlauncher.org/ | US | — | — | malicious |
4056 | javaw.exe | HEAD | 200 | 104.20.87.142:80 | http://page.tlauncher.org/ | US | — | — | malicious |
4056 | javaw.exe | GET | 200 | 104.20.87.142:80 | http://repo.tlauncher.org/update/downloads/libraries/org/tlauncher/authlib/libraries-1.6.json | US | text | 108 Kb | whitelisted |
4056 | javaw.exe | GET | 200 | 104.20.87.142:80 | http://repo.tlauncher.org/update/lch/update_2.0.json?version=2.72&client=5f2c2f92-33fd-4cc9-a0b3-55ce0fae975f | US | text | 7.67 Kb | whitelisted |
4056 | javaw.exe | GET | 200 | 104.20.86.142:80 | http://img.tlauncher.org/update/downloads/configs/client/style_new_bes_fontov.css | US | text | 5.76 Kb | malicious |
4056 | javaw.exe | GET | 200 | 104.20.86.142:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn1.png | US | image | 160 b | malicious |
4056 | javaw.exe | GET | 200 | 104.20.86.142:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn2.png | US | image | 193 b | malicious |
4056 | javaw.exe | GET | 200 | 104.20.86.142:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn4.png | US | image | 205 b | malicious |
4056 | javaw.exe | GET | 200 | 104.20.86.142:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/tl2.png | US | image | 114 b | malicious |
4056 | javaw.exe | GET | 200 | 104.20.86.142:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/fb.png | US | image | 167 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4056 | javaw.exe | 104.20.87.142:80 | page.tlauncher.org | Cloudflare Inc | US | shared |
4056 | javaw.exe | 104.20.86.142:80 | page.tlauncher.org | Cloudflare Inc | US | shared |
4056 | javaw.exe | 104.16.168.35:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
4056 | javaw.exe | 99.86.7.139:443 | launchermeta.mojang.com | AT&T Services, Inc. | US | unknown |
4056 | javaw.exe | 176.9.83.82:8092 | stat.tlrepo.com | Hetzner Online GmbH | DE | suspicious |
4056 | javaw.exe | 104.20.86.142:443 | page.tlauncher.org | Cloudflare Inc | US | shared |
4056 | javaw.exe | 176.9.83.82:443 | stat.tlrepo.com | Hetzner Online GmbH | DE | suspicious |
4056 | javaw.exe | 143.204.201.32:80 | resources.download.minecraft.net | — | US | suspicious |
4056 | javaw.exe | 143.204.201.30:80 | resources.download.minecraft.net | — | US | suspicious |
4056 | javaw.exe | 46.4.112.226:443 | resource.tlrepo.com | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
page.tlauncher.org |
| malicious |
repo.tlauncher.org |
| whitelisted |
img.tlauncher.org |
| malicious |
ajax.cloudflare.com |
| whitelisted |
launchermeta.mojang.com |
| whitelisted |
stat.tlrepo.com |
| suspicious |
tlauncher.org |
| malicious |
dl2.tlrepo.com |
| suspicious |
resources.download.minecraft.net |
| shared |
resource.tlrepo.com |
| malicious |