| File name: | LDWin.exe |
| Full analysis: | https://app.any.run/tasks/7aa71469-5b40-4bf5-8f8a-e5fec66916ba |
| Verdict: | Malicious activity |
| Analysis date: | January 21, 2025, 10:22:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | C8B91A236193BD8960F7B5C42FDCA3E5 |
| SHA1: | 0C4F632EC6F8EE80CBF539821645A0F5D3EA82BD |
| SHA256: | ED0BF3C3746FCAA8F4EFCF12AD26C590CBA709F229C0F4F8FC33E6DF227B1872 |
| SSDEEP: | 24576:WRmJkcoQricOIQxiZY1ia53Bb1Kid4ssIAZeQwVfjUqy:zJZoQrbTFZY1ia551V4ssIcdwVfA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- LDWin.exe (PID: 5036)
- tcpdump.exe (PID: 6924)
Drops a system driver (possible attempt to evade defenses)
- tcpdump.exe (PID: 6924)
The executable file from the user directory is run by the CMD process
- tcpdump.exe (PID: 6924)
Starts CMD.EXE for commands execution
- LDWin.exe (PID: 5036)
There is functionality for taking screenshot (YARA)
- LDWin.exe (PID: 5036)
Creates files in the driver directory
- tcpdump.exe (PID: 6924)
INFO
The sample compiled with english language support
- LDWin.exe (PID: 5036)
- tcpdump.exe (PID: 6924)
Checks supported languages
- LDWin.exe (PID: 5036)
Reads mouse settings
- LDWin.exe (PID: 5036)
Process checks whether UAC notifications are on
- LDWin.exe (PID: 5036)
Reads the computer name
- LDWin.exe (PID: 5036)
The process uses AutoIt
- LDWin.exe (PID: 5036)
Create files in a temporary directory
- LDWin.exe (PID: 5036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:01:29 21:32:28+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 526336 |
| InitializedDataSize: | 102912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x165c1 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 3.3.8.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 2.2.0.0 |
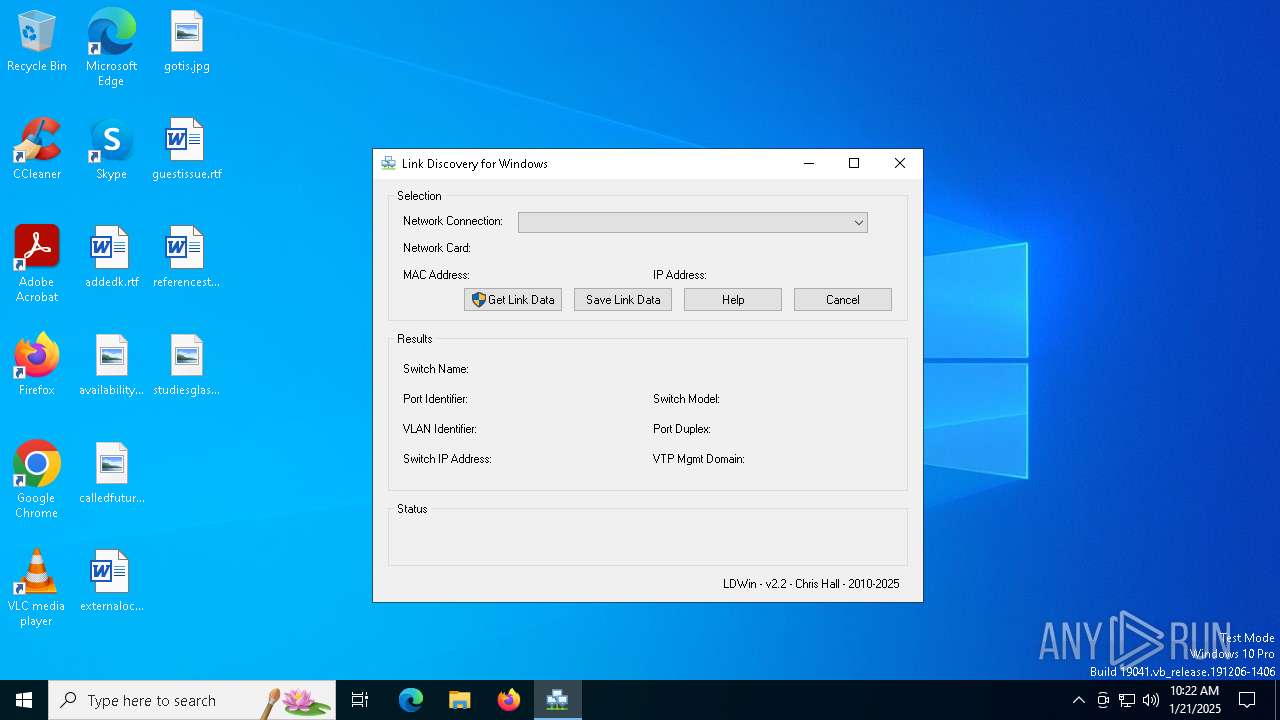
| FileDescription: | Link Discovery for Windows |
| LegalCopyright: | Chris Hall 2010-2015 |
| ProductName: | LDWin |
| ProductVersion: | 2.2 |
| OriginalFileName: | LDWin.exe |
Total processes
132
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3952 | "C:\Users\admin\AppData\Local\Temp\LDWin.exe" | C:\Users\admin\AppData\Local\Temp\LDWin.exe | — | explorer.exe | |||||||||||
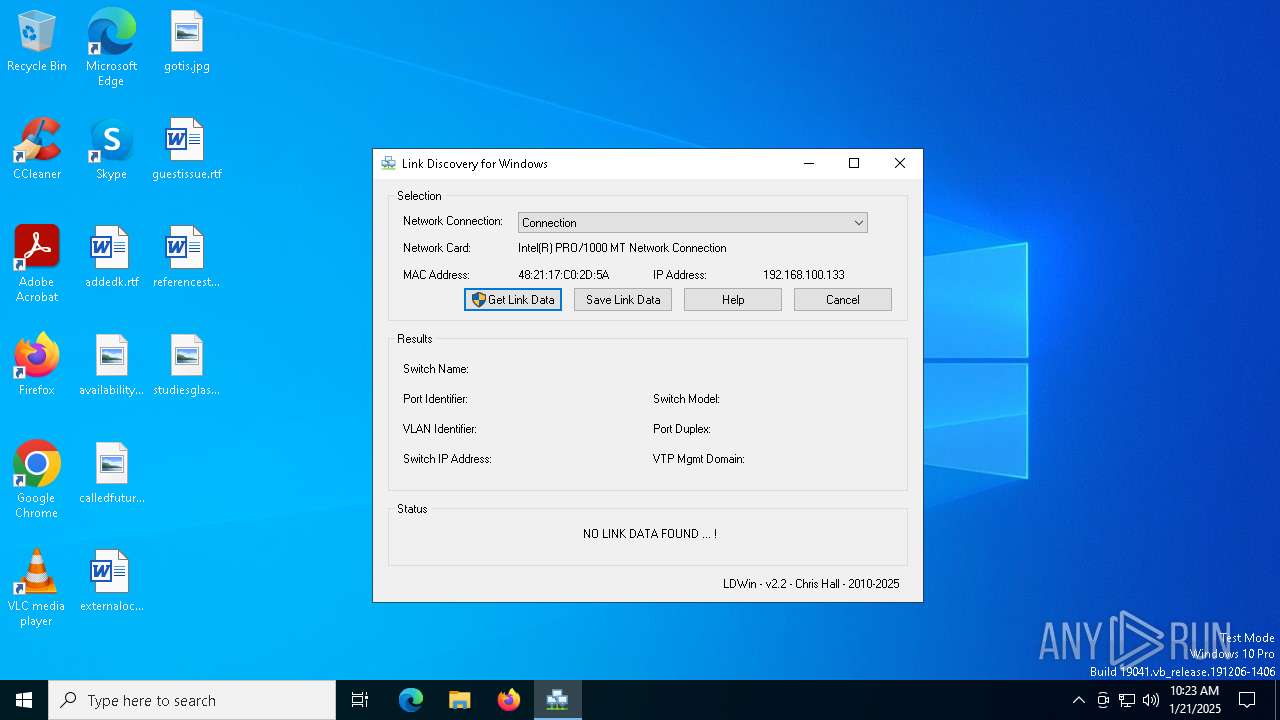
User: admin Integrity Level: MEDIUM Description: Link Discovery for Windows Exit code: 3221226540 Version: 2.2.0.0 Modules
| |||||||||||||||
| 5036 | "C:\Users\admin\AppData\Local\Temp\LDWin.exe" | C:\Users\admin\AppData\Local\Temp\LDWin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Link Discovery for Windows Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
| 6868 | C:\WINDOWS\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\tcpdump.exe -i \Device\{D950CA8D-448E-4CA2-89DE-A65A1AC2B2A6} -nn -v -s 1500 -c 1 (ether[12:2]==0x88cc or ether[20:2]==0x2000) >%temp%\Data_Out.txt | C:\Windows\SysWOW64\cmd.exe | — | LDWin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6924 | C:\Users\admin\AppData\Local\Temp\tcpdump.exe -i \Device\{D950CA8D-448E-4CA2-89DE-A65A1AC2B2A6} -nn -v -s 1500 -c 1 (ether[12:2]==0x88cc or ether[20:2]==0x2000) | C:\Users\admin\AppData\Local\Temp\tcpdump.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
603
Read events
603
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5036 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\donate.ico | image | |
MD5:56D21E02150175332CB6D343ABADA53E | SHA256:23438154D279704EA70E335861E16B8D1EC930252221383EE70FEADEFAD896DA | |||
| 5036 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\tcpdump.exe | executable | |
MD5:4AF745D8FB1CE63BC97CD7874EEDB613 | SHA256:99CFEFAF942BA679D08A17C07ABDBAFE99F8C156E5DB93A2F52F5E277830BB94 | |||
| 5036 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\aut83BA.tmp | executable | |
MD5:4AF745D8FB1CE63BC97CD7874EEDB613 | SHA256:99CFEFAF942BA679D08A17C07ABDBAFE99F8C156E5DB93A2F52F5E277830BB94 | |||
| 5036 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\aut8486.tmp | binary | |
MD5:9731F8533384DB70F219482BB4205AC6 | SHA256:E55A6A8A3456ADC2565E038D0E76B6FC56DAF090D637CB72D57FC7368B958863 | |||
| 5036 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\LinkData.txt | text | |
MD5:B4321300F1F8C991033A96796F5F4A21 | SHA256:74F87116FE44B117F1A348AC4211F2C5E6A4E6FC5841BC6CC8E837E6632D1E21 | |||
| 5036 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\SaveData.txt | text | |
MD5:EB17D0F892C3D58684D23FC26E7FE3C4 | SHA256:0E5ABE4C739EDB00A05D9E7E3465E60FC6B087589241D0A6A2365E3A46DBDE74 | |||
| 6924 | tcpdump.exe | C:\Windows\System32\drivers\pssdk50.sys | executable | |
MD5:58FA6D2EB56C08261240C0B881542AA5 | SHA256:CDF91222645FB4E172B8EC2421755DDF5ED2AEF263DFF485DA7639FC60C683EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
29
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7092 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7092 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6276 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.19.11.105:80 | — | Elisa Oyj | NL | unknown |
4712 | MoUsoCoreWorker.exe | 23.209.214.100:80 | www.microsoft.com | PT. Telekomunikasi Selular | ID | whitelisted |
— | — | 23.209.214.100:80 | www.microsoft.com | PT. Telekomunikasi Selular | ID | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.19.122.8:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2012 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 2.18.97.227:443 | go.microsoft.com | Akamai International B.V. | FR | whitelisted |
5064 | SearchApp.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |