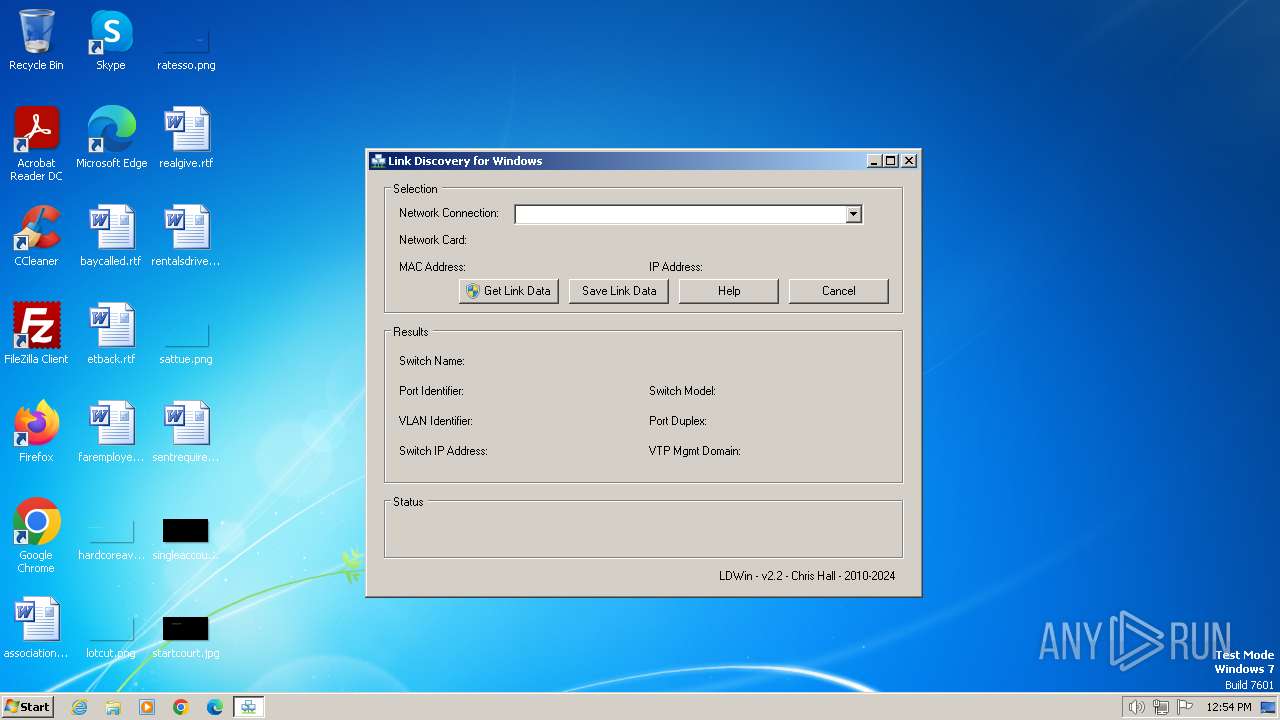
| File name: | LDWin.exe |
| Full analysis: | https://app.any.run/tasks/1cea9732-1e93-4c26-a46c-56a2d9504f0f |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2024, 12:54:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C8B91A236193BD8960F7B5C42FDCA3E5 |
| SHA1: | 0C4F632EC6F8EE80CBF539821645A0F5D3EA82BD |
| SHA256: | ED0BF3C3746FCAA8F4EFCF12AD26C590CBA709F229C0F4F8FC33E6DF227B1872 |
| SSDEEP: | 24576:WRmJkcoQricOIQxiZY1ia53Bb1Kid4ssIAZeQwVfjUqy:zJZoQrbTFZY1ia551V4ssIcdwVfA |
MALICIOUS
Drops the executable file immediately after the start
- LDWin.exe (PID: 3216)
- tcpdump.exe (PID: 4060)
Creates a writable file in the system directory
- tcpdump.exe (PID: 4060)
SUSPICIOUS
Executable content was dropped or overwritten
- LDWin.exe (PID: 3216)
- tcpdump.exe (PID: 4060)
Starts CMD.EXE for commands execution
- LDWin.exe (PID: 3216)
Drops a system driver (possible attempt to evade defenses)
- tcpdump.exe (PID: 4060)
The executable file from the user directory is run by the CMD process
- tcpdump.exe (PID: 4060)
Creates files in the driver directory
- tcpdump.exe (PID: 4060)
INFO
Checks supported languages
- LDWin.exe (PID: 3216)
- tcpdump.exe (PID: 4060)
Reads the computer name
- LDWin.exe (PID: 3216)
- tcpdump.exe (PID: 4060)
Process checks whether UAC notifications are on
- LDWin.exe (PID: 3216)
Reads mouse settings
- LDWin.exe (PID: 3216)
Reads the machine GUID from the registry
- LDWin.exe (PID: 3216)
Create files in a temporary directory
- LDWin.exe (PID: 3216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:01:29 21:32:28+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 526336 |
| InitializedDataSize: | 102912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x165c1 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 3.3.8.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 2.2.0.0 |
| FileDescription: | Link Discovery for Windows |
| LegalCopyright: | Chris Hall 2010-2015 |
| ProductName: | LDWin |
| ProductVersion: | 2.2 |
| OriginalFileName: | LDWin.exe |
Total processes
44
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2444 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\tcpdump.exe -i \Device\{4040CF00-1B3E-486A-B407-FA14C56B6FC0} -nn -v -s 1500 -c 1 (ether[12:2]==0x88cc or ether[20:2]==0x2000) >%temp%\Data_Out.txt | C:\Windows\System32\cmd.exe | — | LDWin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3216 | "C:\Users\admin\AppData\Local\Temp\LDWin.exe" | C:\Users\admin\AppData\Local\Temp\LDWin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Link Discovery for Windows Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
| 3672 | "C:\Users\admin\AppData\Local\Temp\LDWin.exe" | C:\Users\admin\AppData\Local\Temp\LDWin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Link Discovery for Windows Exit code: 3221226540 Version: 2.2.0.0 Modules
| |||||||||||||||
| 4060 | C:\Users\admin\AppData\Local\Temp\tcpdump.exe -i \Device\{4040CF00-1B3E-486A-B407-FA14C56B6FC0} -nn -v -s 1500 -c 1 (ether[12:2]==0x88cc or ether[20:2]==0x2000) | C:\Users\admin\AppData\Local\Temp\tcpdump.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
556
Read events
556
Write events
0
Delete events
0
Modification events
Executable files
4
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | tcpdump.exe | C:\Windows\system32\Drivers\pssdk50.sys | executable | |
MD5:2A2A5C1BDD41BE4C28350632ACD45B5F | SHA256:1D275CF166360B37F239ADC74248B23953A7A93240C984ABED1C10103306300C | |||
| 3216 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\autF6E3.tmp | executable | |
MD5:4AF745D8FB1CE63BC97CD7874EEDB613 | SHA256:99CFEFAF942BA679D08A17C07ABDBAFE99F8C156E5DB93A2F52F5E277830BB94 | |||
| 3216 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\tcpdump.exe | executable | |
MD5:4AF745D8FB1CE63BC97CD7874EEDB613 | SHA256:99CFEFAF942BA679D08A17C07ABDBAFE99F8C156E5DB93A2F52F5E277830BB94 | |||
| 3216 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\autF703.tmp | binary | |
MD5:9731F8533384DB70F219482BB4205AC6 | SHA256:E55A6A8A3456ADC2565E038D0E76B6FC56DAF090D637CB72D57FC7368B958863 | |||
| 3216 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\donate.ico | image | |
MD5:56D21E02150175332CB6D343ABADA53E | SHA256:23438154D279704EA70E335861E16B8D1EC930252221383EE70FEADEFAD896DA | |||
| 3216 | LDWin.exe | C:\Users\admin\AppData\Local\Temp\LinkData.txt | text | |
MD5:3C3894D567BBC6FA859C500CBA79E169 | SHA256:3E7A3AB429606B29C698F761BB48696598CF541EFA83F3D403195758F2BDD227 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |