| File name: | sample6.doc |
| Full analysis: | https://app.any.run/tasks/83ec1b67-5d45-4c8c-a90f-c512551e3370 |
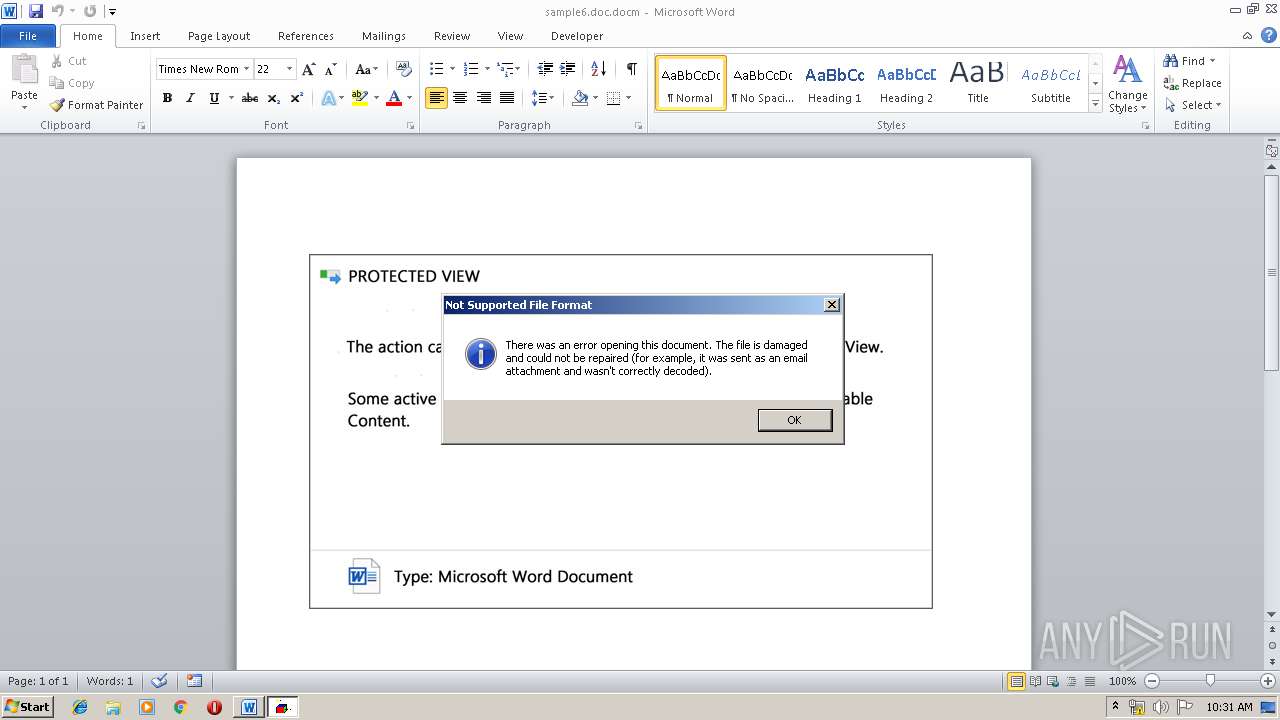
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 19, 2019, 09:27:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 41932B8B7A44A817F73E2B7C256768E2 |
| SHA1: | 17DEC293AA0942C3D0A3598541FACB3EB71FE769 |
| SHA256: | ECDB7767077CFA50958819F9912B5DDA680837CCCD95E7A4430341E97B847F50 |
| SSDEEP: | 3072:TZ1uxC2aghrksuWUYs65XpyTOIIAy/7WHkjdIqzWS:VqhrkvWU2iE1IEB |
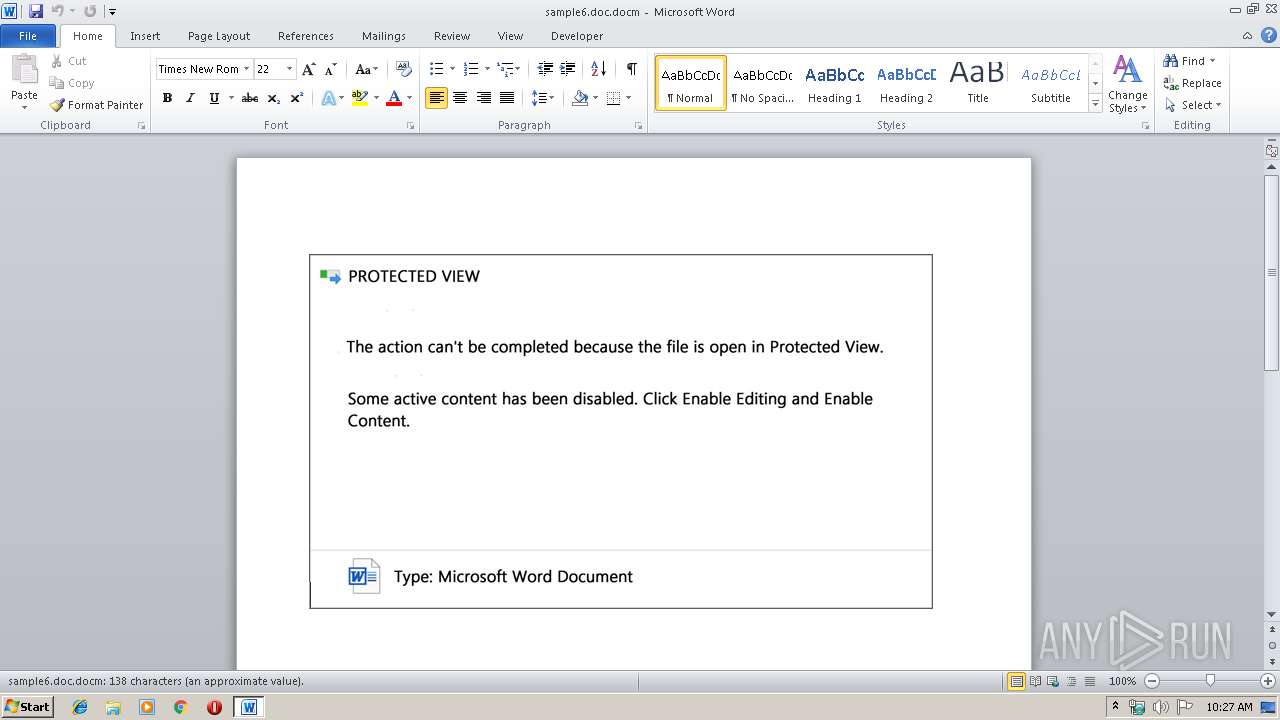
MALICIOUS
Executes scripts
- WINWORD.EXE (PID: 3392)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3392)
SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 2912)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3392)
Creates files in the user directory
- WINWORD.EXE (PID: 3392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x0c0cc35b |
| ZipCompressedSize: | 1505 |
| ZipUncompressedSize: | 1505 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | user |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | user |
| RevisionNumber: | 10 |
| CreateDate: | 2019:09:18 19:03:00Z |
| ModifyDate: | 2019:09:18 19:34:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 12 minutes |
| Pages: | 1 |
| Words: | 3 |
| Characters: | 21 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 23 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2912 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\0.7055475.jse" | C:\Windows\System32\WScript.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\sample6.doc.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 520
Read events
814
Write events
701
Delete events
5
Modification events
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ,# |
Value: 2C7F2300400D0000010000000000000000000000 | |||
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328742430 | |||
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742544 | |||
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742545 | |||
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 400D0000B05B0983CC6ED50100000000 | |||
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d`# |
Value: 64602300400D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | d`# |
Value: 64602300400D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3392) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9B0C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF80B4C1FCF8EB2133.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF031F970252F8A20F.TMP | — | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF2278CD13E21A1D54.TMP | — | |
MD5:— | SHA256:— | |||
| 2912 | WScript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\u9kh5at75ss[1].exe | — | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Forms\WINWORD.box | binary | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$mple6.doc.docm | pgc | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\0.7055475.jse | text | |
MD5:— | SHA256:— | |||
| 3392 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | WScript.exe | 39.106.43.41:443 | www.cityvisualization.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cityvisualization.com |
| unknown |