| File name: | Client-built-VM.exe |
| Full analysis: | https://app.any.run/tasks/00cbf892-acee-4035-b934-4853e7c86234 |
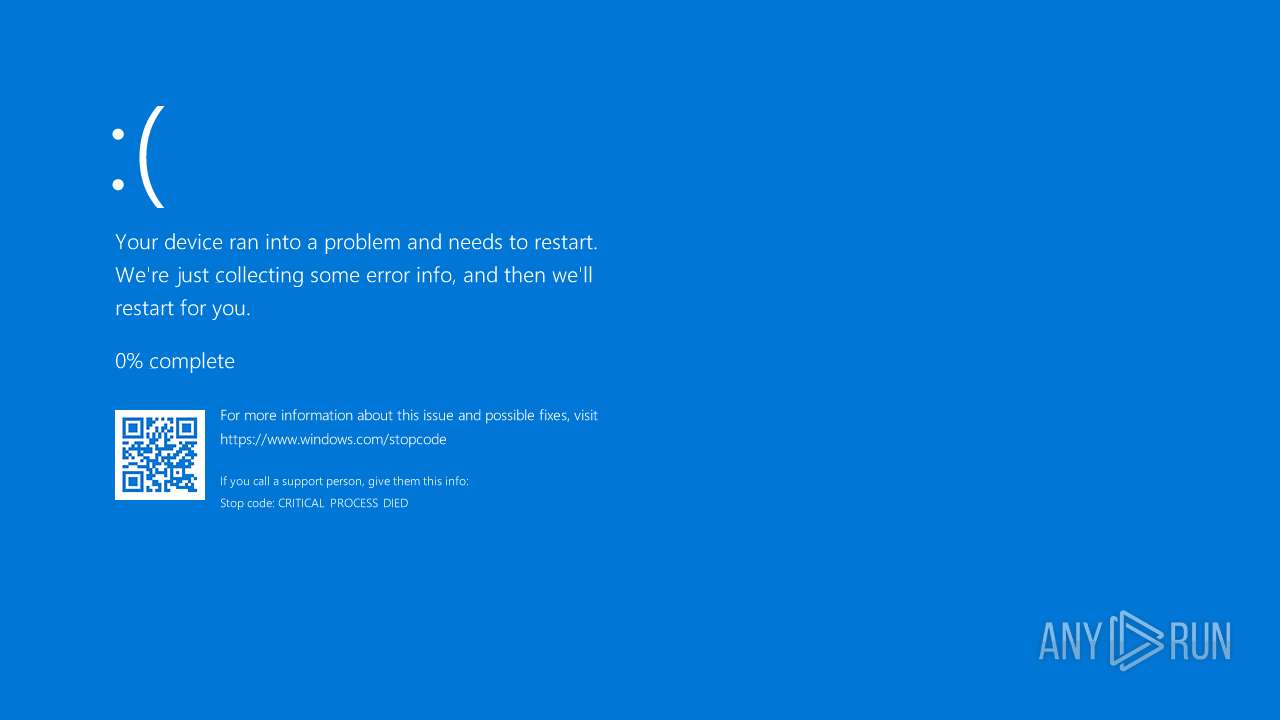
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 12:36:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | A663B7A30DDF67E392161B0806B0CDE1 |
| SHA1: | 9BD1413112C56C10CD28567118219C07E7A87C78 |
| SHA256: | ECD6E52C5038256CDB89DAE5915FDD774632EB65AF698FC941FEE7822712CB76 |
| SSDEEP: | 49152:eHDnwoERCSPvtJ+wQ3ROPBhgRJMWn+DXHzlSj4kn3ibMBvQWXS5XHNr6LK/Jsob+:iDnwsSPKwmOPnIakwH0j4W3iS5o9IK/S |
MALICIOUS
Bypass User Account Control (Modify registry)
- Client-built-VM.exe (PID: 4224)
Bypass User Account Control (fodhelper)
- fodhelper.exe (PID: 3800)
Execute application with conhost.exe as parent process
- cmd.exe (PID: 4648)
SUSPICIOUS
Changes default file association
- Client-built-VM.exe (PID: 4224)
Reads security settings of Internet Explorer
- Client-built-VM.exe (PID: 4224)
Reads the date of Windows installation
- Client-built-VM.exe (PID: 4224)
Starts CMD.EXE for commands execution
- conhost.exe (PID: 6656)
Executing commands from a ".bat" file
- conhost.exe (PID: 6656)
The executable file from the user directory is run by the CMD process
- Client-built-VM.exe (PID: 6336)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4648)
Executable content was dropped or overwritten
- Client-built-VM.exe (PID: 6336)
INFO
Reads the computer name
- Client-built-VM.exe (PID: 4224)
- Client-built-VM.exe (PID: 6336)
Reads the machine GUID from the registry
- Client-built-VM.exe (PID: 4224)
- Client-built-VM.exe (PID: 6336)
Reads Environment values
- Client-built-VM.exe (PID: 4224)
- Client-built-VM.exe (PID: 6336)
Create files in a temporary directory
- Client-built-VM.exe (PID: 4224)
Checks supported languages
- Client-built-VM.exe (PID: 4224)
- Client-built-VM.exe (PID: 6336)
Process checks computer location settings
- Client-built-VM.exe (PID: 4224)
Reads security settings of Internet Explorer
- fodhelper.exe (PID: 3800)
Uses Task Scheduler to autorun other applications (AUTOMATE)
- Client-built-VM.exe (PID: 6336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:21 12:35:09+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 1544192 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17ae6e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | temploader.exe |
| LegalCopyright: | |
| OriginalFileName: | temploader.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
137
Monitored processes
9
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3800 | "C:\Windows\System32\fodhelper.exe" | C:\Windows\System32\fodhelper.exe | Client-built-VM.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Features On Demand Helper Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4224 | "C:\Users\admin\AppData\Local\Temp\Client-built-VM.exe" | C:\Users\admin\AppData\Local\Temp\Client-built-VM.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 5 Version: 0.0.0.0 Modules
| |||||||||||||||
| 4648 | C:\WINDOWS\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\uacbypass.bat | C:\Windows\System32\cmd.exe | — | conhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4984 | timeout /t 4 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | "schtasks" /create /tn "ChromeUpdater" /sc ONLOGON /tr "C:\WINDOWS\system32\Updater\ChromeUpdater.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Client-built-VM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5616 | "C:\Windows\System32\fodhelper.exe" | C:\Windows\System32\fodhelper.exe | — | Client-built-VM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Features On Demand Helper Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6336 | "C:\Users\admin\AppData\Local\Temp\Client-built-VM.exe" | C:\Users\admin\AppData\Local\Temp\Client-built-VM.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 6404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6656 | "conhost.exe" --headless "C:\Users\admin\AppData\Local\Temp\uacbypass.bat" | C:\Windows\System32\conhost.exe | — | fodhelper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 386
Read events
1 378
Write events
4
Delete events
4
Modification events
| (PID) Process: | (3800) fodhelper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4224) Client-built-VM.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\Shell\Open\command |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4224) Client-built-VM.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\Shell\Open |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4224) Client-built-VM.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\Shell |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4224) Client-built-VM.exe | Key: | HKEY_CLASSES_ROOT\ms-settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4224) Client-built-VM.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\Shell\Open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
| (PID) Process: | (3800) fodhelper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3800) fodhelper.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4224 | Client-built-VM.exe | C:\Users\admin\AppData\Local\Temp\uacbypass.bat | text | |
MD5:620F94D73119109DB217D9E9E658B053 | SHA256:54C973ED3DD1D93D008106E7DBB613DC4AB673F78AFCBB8C16653B97EBEFB021 | |||
| 6336 | Client-built-VM.exe | C:\Windows\System32\Updater\ChromeUpdater.exe | executable | |
MD5:A663B7A30DDF67E392161B0806B0CDE1 | SHA256:ECD6E52C5038256CDB89DAE5915FDD774632EB65AF698FC941FEE7822712CB76 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
66
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:Cb7ID2pAz59RPP3YEhquW20GEYOZt71tQeMYOvDaqX0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5600 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 52.109.89.18:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |