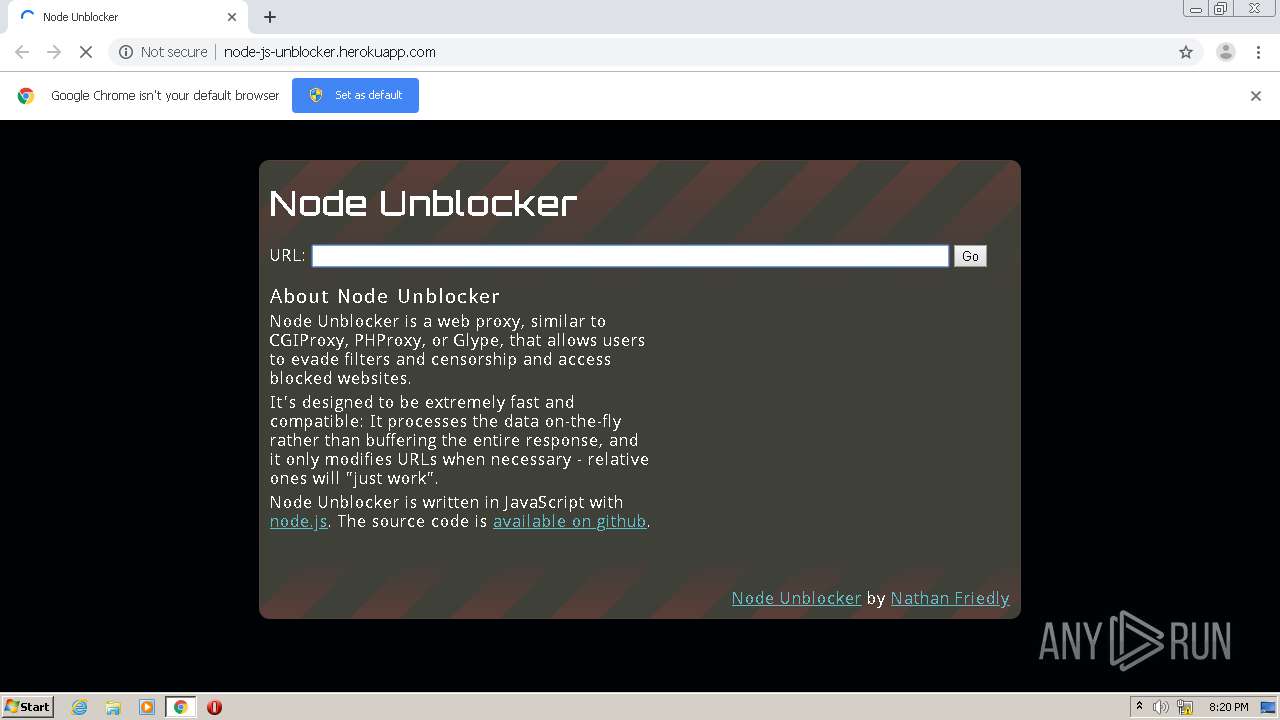
| URL: | http://node-js-unblocker.herokuapp.com |
| Full analysis: | https://app.any.run/tasks/6f1c9b55-2d13-43d0-94d7-bdf897db7fd2 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2020, 20:20:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 967344AFBCFA5E78332D6D4D955E6F7A |
| SHA1: | F2963EE0DA710DFE8A796D15BA8F507A20CBF296 |
| SHA256: | ECD469FAF101E32DF3B774226134F848927E54283F63520BBF173B221477983B |
| SSDEEP: | 3:N1KQLyap:CQG2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3256)
Reads the hosts file
- chrome.exe (PID: 3256)
- chrome.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,10721774673278614258,12686001423654617875,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16642239964041423854 --mojo-platform-channel-handle=1092 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,10721774673278614258,12686001423654617875,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13172826429643200523 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,10721774673278614258,12686001423654617875,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3583350308345581021 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,10721774673278614258,12686001423654617875,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8246075517249750955 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,10721774673278614258,12686001423654617875,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13764950890184608899 --mojo-platform-channel-handle=3388 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,10721774673278614258,12686001423654617875,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3519574542804885499 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,10721774673278614258,12686001423654617875,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10145726380759210051 --mojo-platform-channel-handle=1464 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://node-js-unblocker.herokuapp.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3260 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,10721774673278614258,12686001423654617875,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1700311733792065695 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
566
Read events
515
Write events
48
Delete events
3
Modification events
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3256-13252796444115125 |
Value: 259 | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3256) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
32
Text files
60
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FDD0F1C-CB8.pma | — | |
MD5:— | SHA256:— | |||
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ea728f77-30e8-4197-bf14-b6f433471921.tmp | — | |
MD5:— | SHA256:— | |||
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe2af.TMP | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe2be.TMP | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3256 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe510.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
142
TCP/UDP connections
48
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
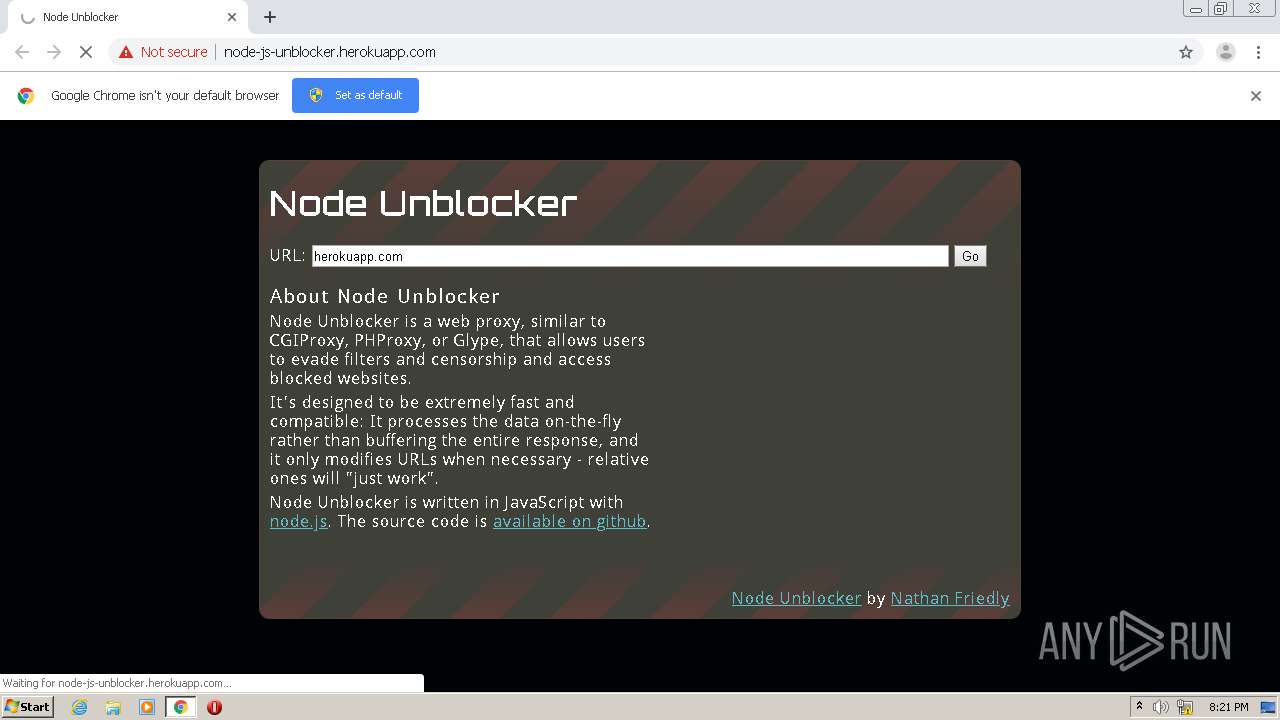
3228 | chrome.exe | GET | 200 | 34.199.176.68:80 | http://node-js-unblocker.herokuapp.com/ | US | html | 6.64 Kb | malicious |
3228 | chrome.exe | GET | 404 | 34.199.176.68:80 | http://node-js-unblocker.herokuapp.com/favicon.ico | US | html | 150 b | malicious |
3228 | chrome.exe | GET | 307 | 34.199.176.68:80 | http://node-js-unblocker.herokuapp.com/proxy/http://herokuapp.com | US | html | 150 b | malicious |
3228 | chrome.exe | GET | 200 | 216.58.212.130:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 46.0 Kb | whitelisted |
3228 | chrome.exe | GET | 301 | 34.199.176.68:80 | http://node-js-unblocker.herokuapp.com/proxy/http://herokuapp.com/ | US | html | 150 b | malicious |
3228 | chrome.exe | GET | 301 | 34.199.176.68:80 | http://node-js-unblocker.herokuapp.com/proxy/https://herokuapp.com/ | US | html | 92 b | malicious |
3228 | chrome.exe | GET | 301 | 34.199.176.68:80 | http://node-js-unblocker.herokuapp.com/proxy/https://heroku.com/ | US | html | 143 b | malicious |
3228 | chrome.exe | GET | 307 | 34.199.176.68:80 | http://node-js-unblocker.herokuapp.com/proxy/https://www.heroku.com/assets/application-0da31d424c04b78cb3ddf9370cfece6b95199d06e0a20a431de4968cb7a7abec.css?__proxy_cookies_to=https%3A%2F%2Fwww2.assets.heroku.com%2Fassets%2Fapplication-0da31d424c04b78cb3ddf9370cfece6b95199d06e0a20a431de4968cb7a7abec.css | US | — | — | malicious |
3228 | chrome.exe | GET | 307 | 34.199.176.68:80 | http://node-js-unblocker.herokuapp.com/proxy/https://www.heroku.com/app.js?__proxy_cookies_to=https%3A%2F%2Fdoppler.heroku.com%2Fapp.js | US | — | — | malicious |
3228 | chrome.exe | GET | 200 | 34.199.176.68:80 | http://node-js-unblocker.herokuapp.com/proxy/https://developer.salesforce.com/shared-components/css/index.css | US | text | 14.0 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3228 | chrome.exe | 216.58.212.130:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3228 | chrome.exe | 172.217.18.2:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 172.217.23.162:443 | partner.googleadservices.com | Google Inc. | US | whitelisted |
— | — | 216.58.206.2:443 | adservice.google.co.uk | Google Inc. | US | whitelisted |
3228 | chrome.exe | 34.199.176.68:80 | node-js-unblocker.herokuapp.com | Amazon.com, Inc. | US | unknown |
3228 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3228 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 216.58.212.130:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3228 | chrome.exe | 74.125.205.157:443 | adservice.google.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
node-js-unblocker.herokuapp.com |
| unknown |
accounts.google.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
github.com |
| malicious |
nodejs.org |
| whitelisted |
www.nfriedly.com |
| malicious |
googleads.g.doubleclick.net |
| whitelisted |