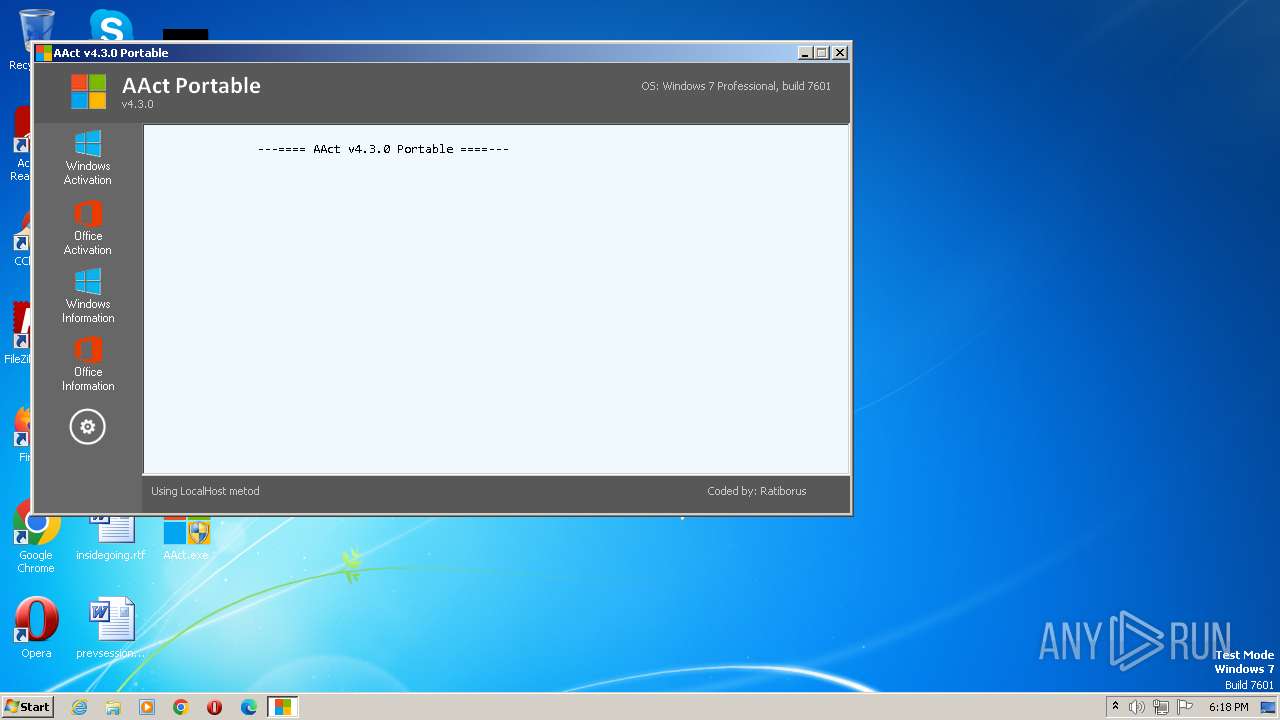
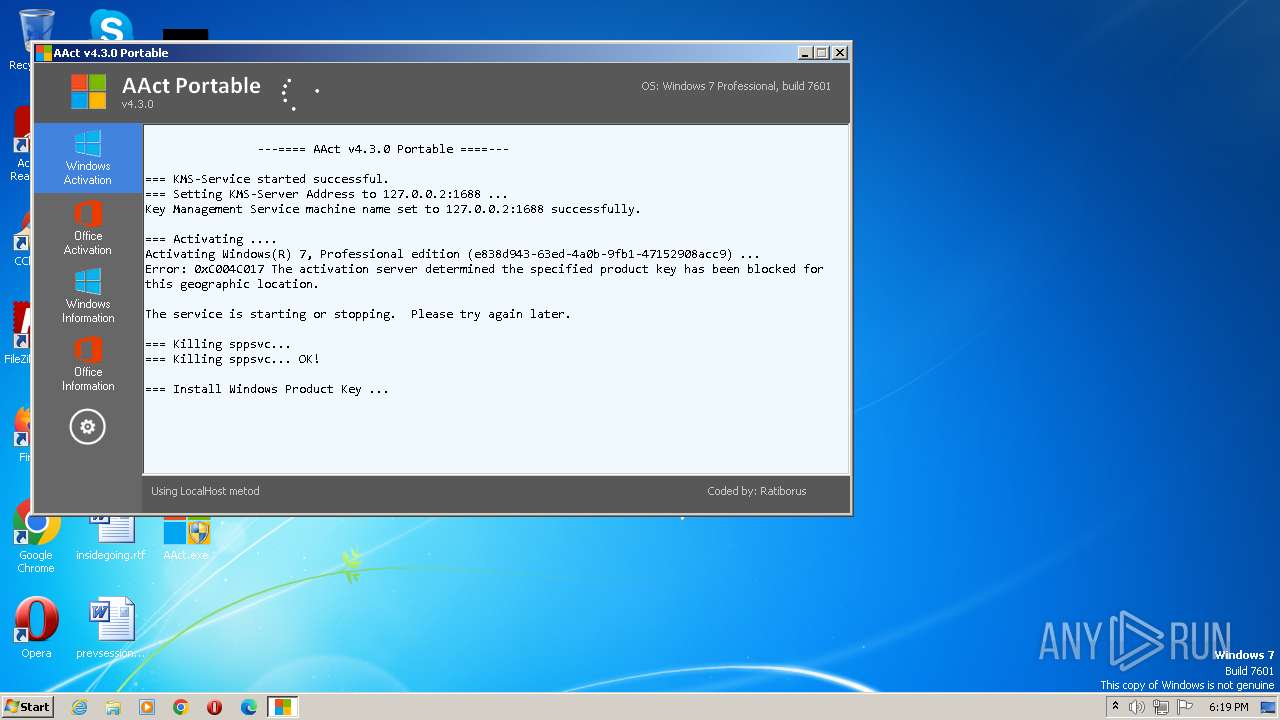
| File name: | AAct.exe |
| Full analysis: | https://app.any.run/tasks/29853880-c547-4123-88cd-de231a2b1c9b |
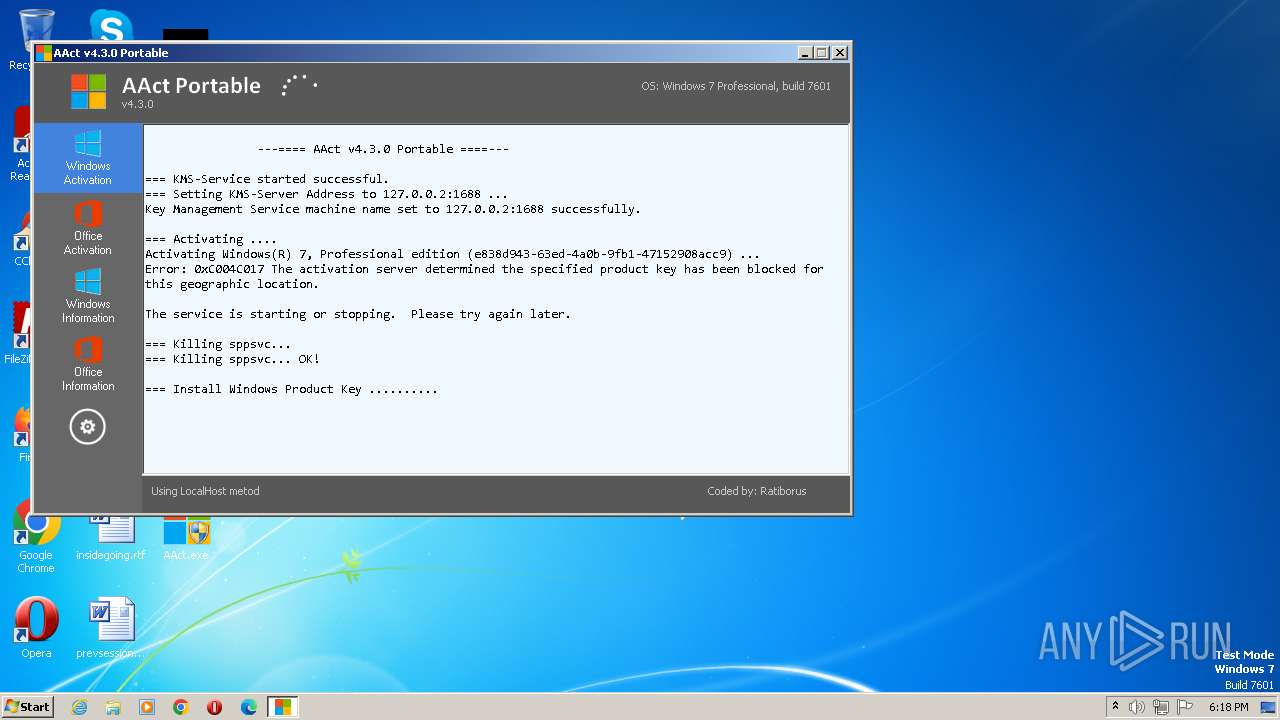
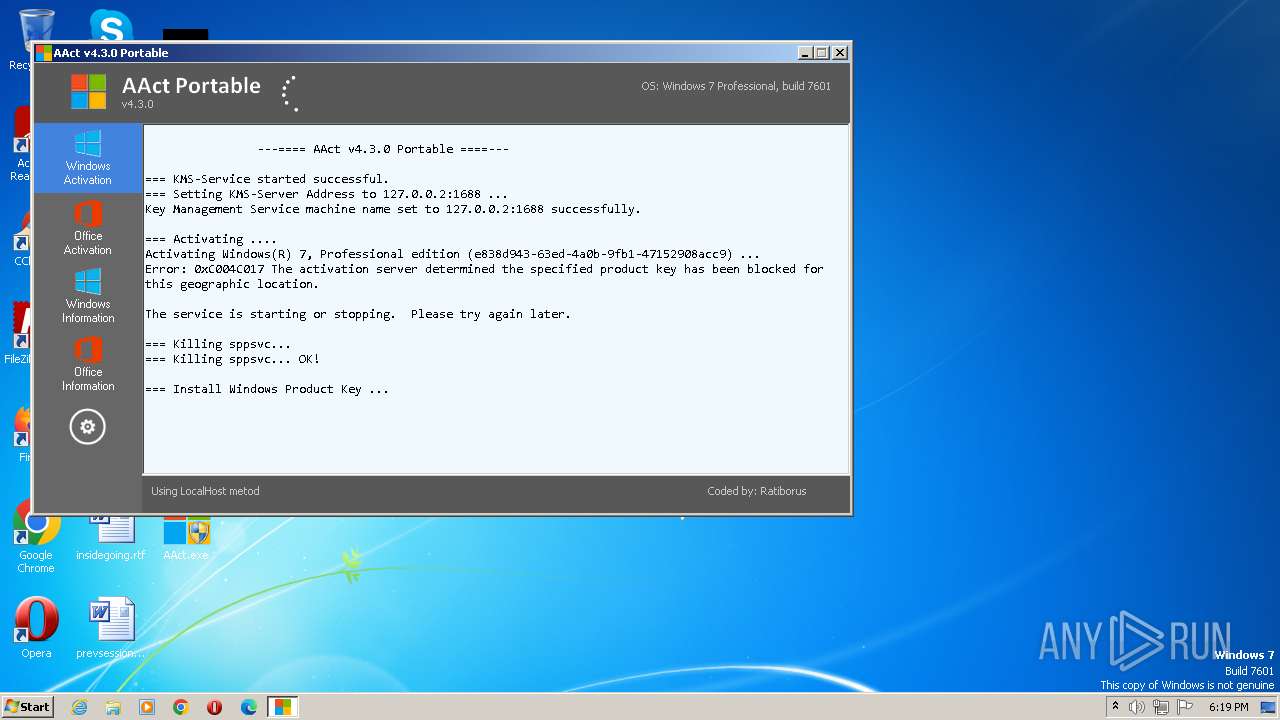
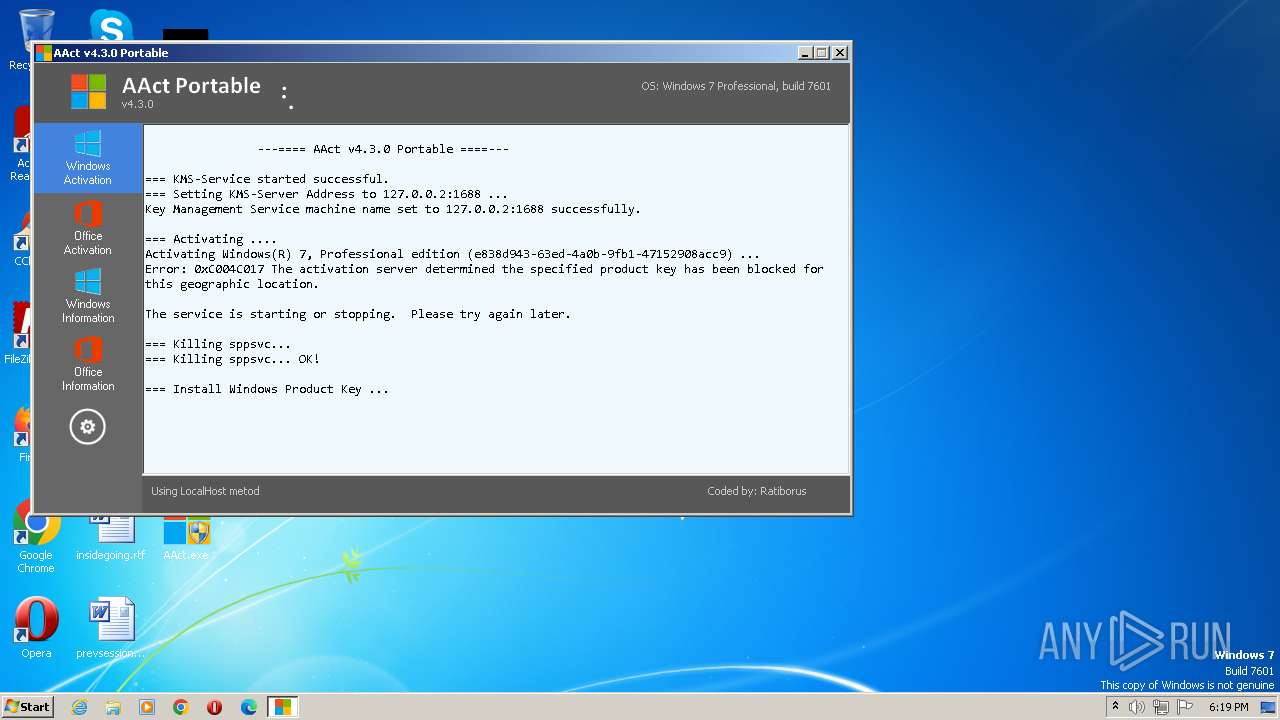
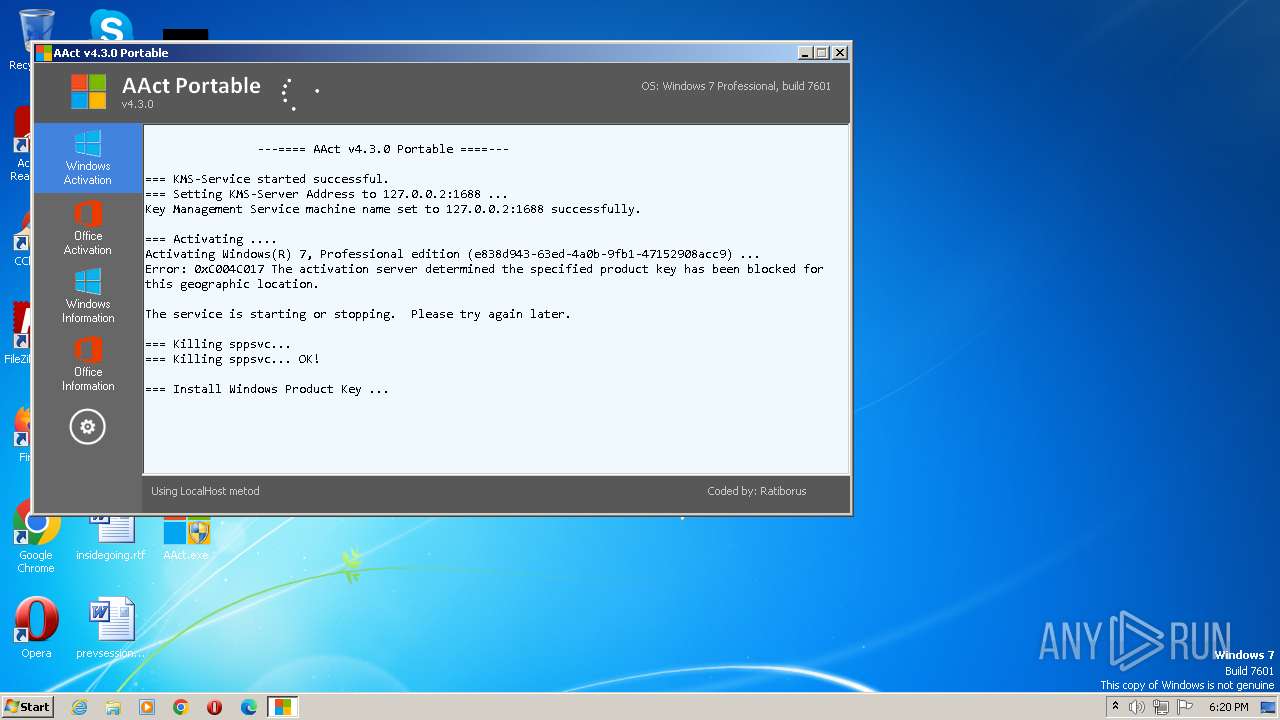
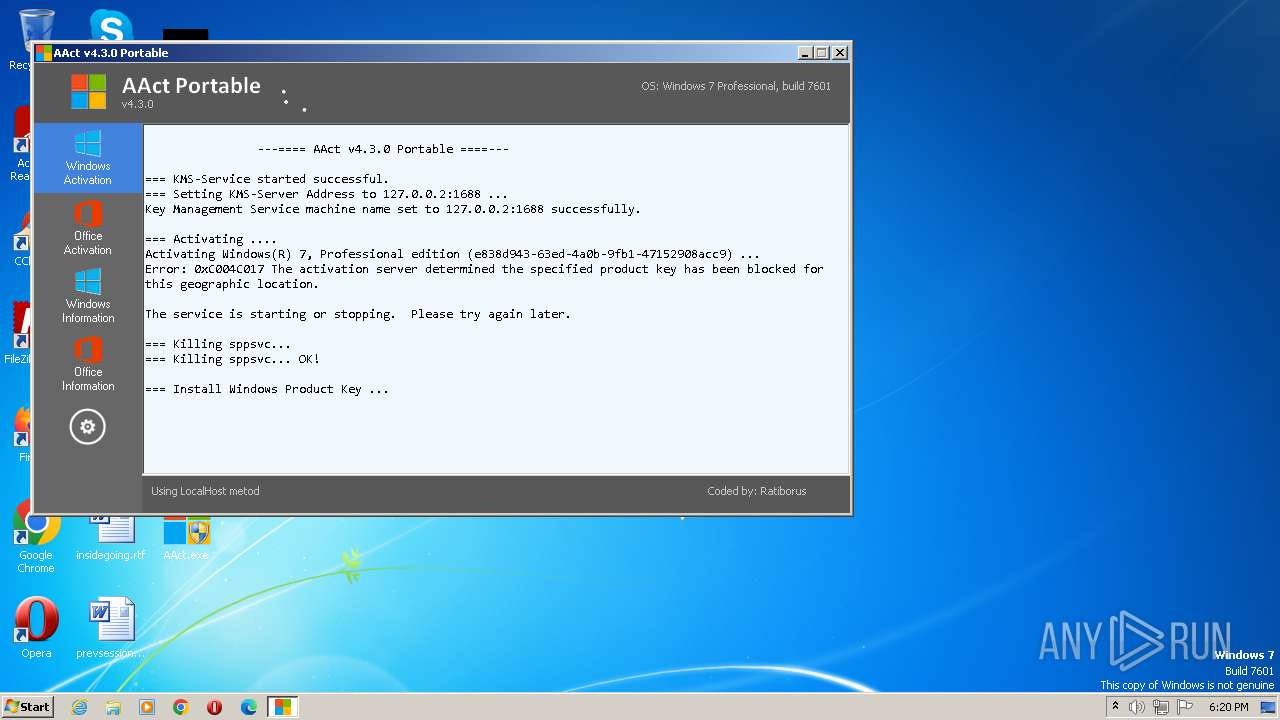
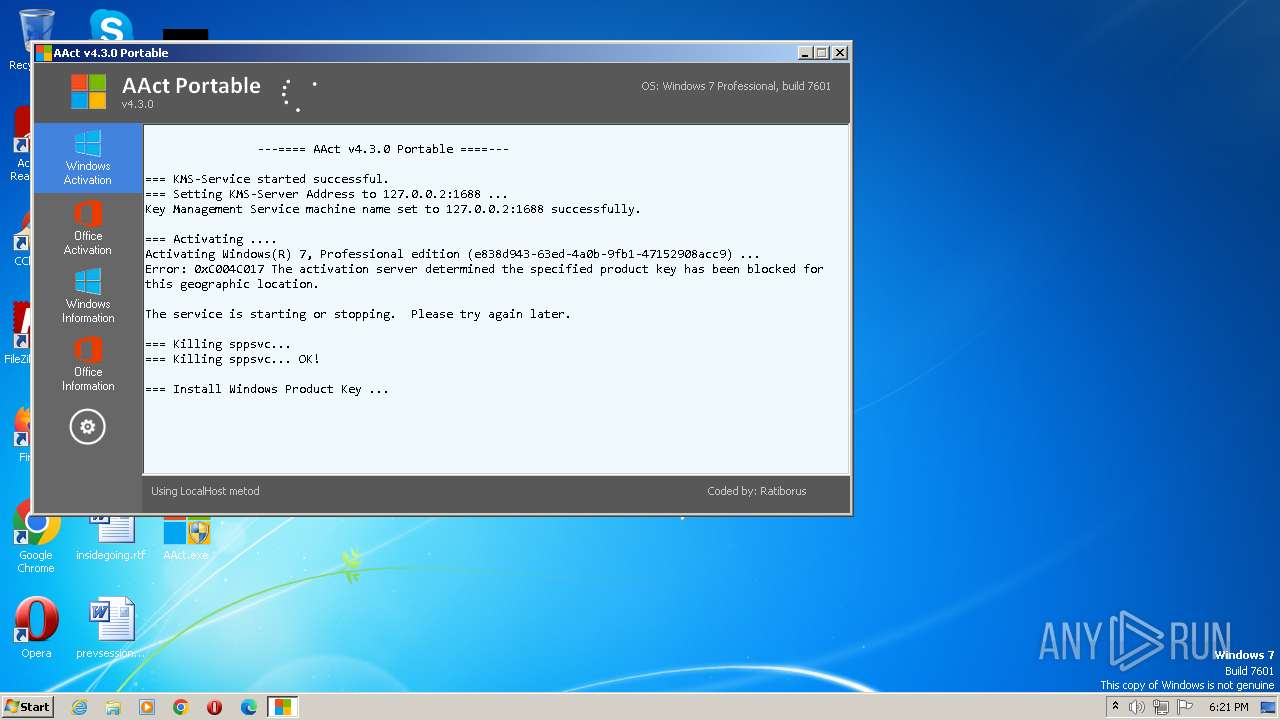
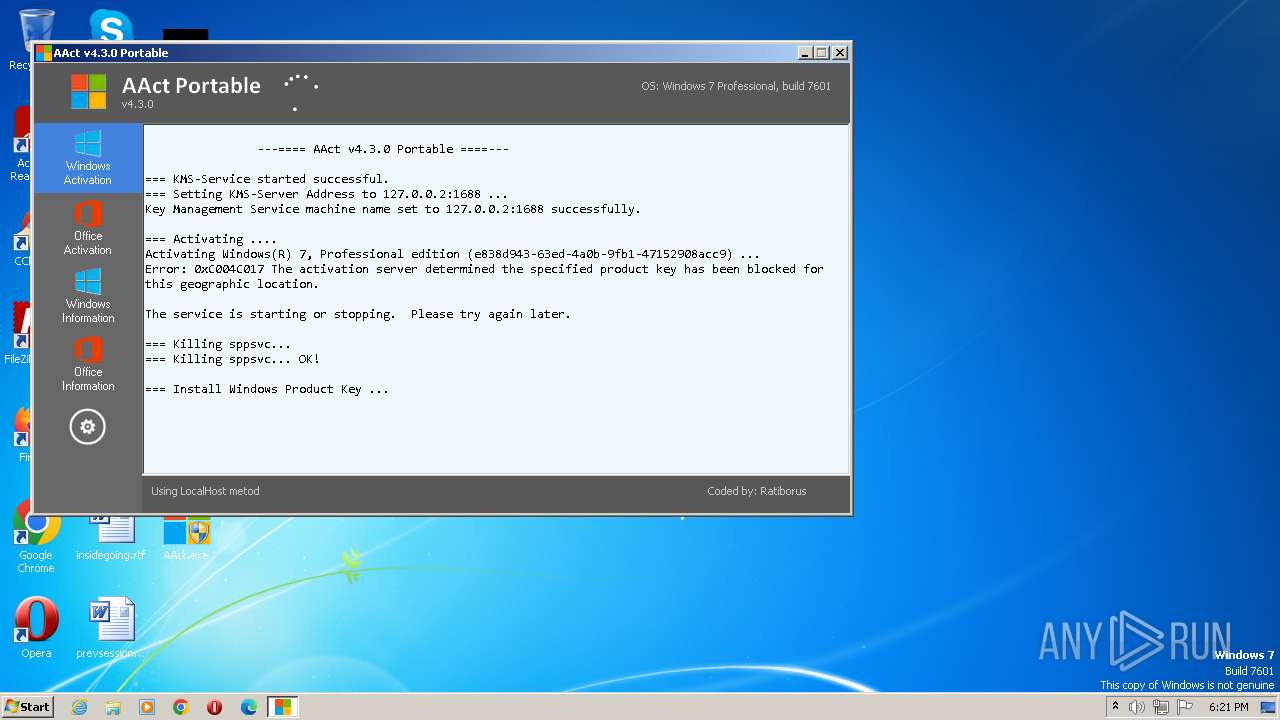
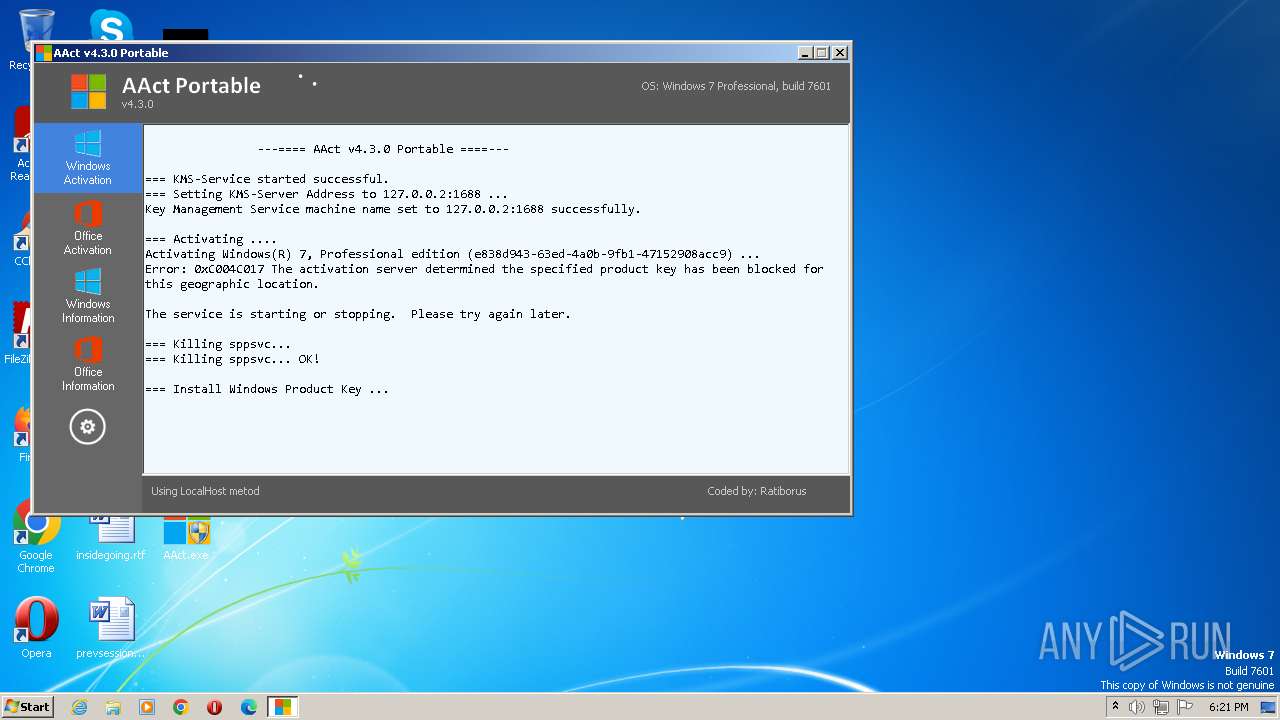
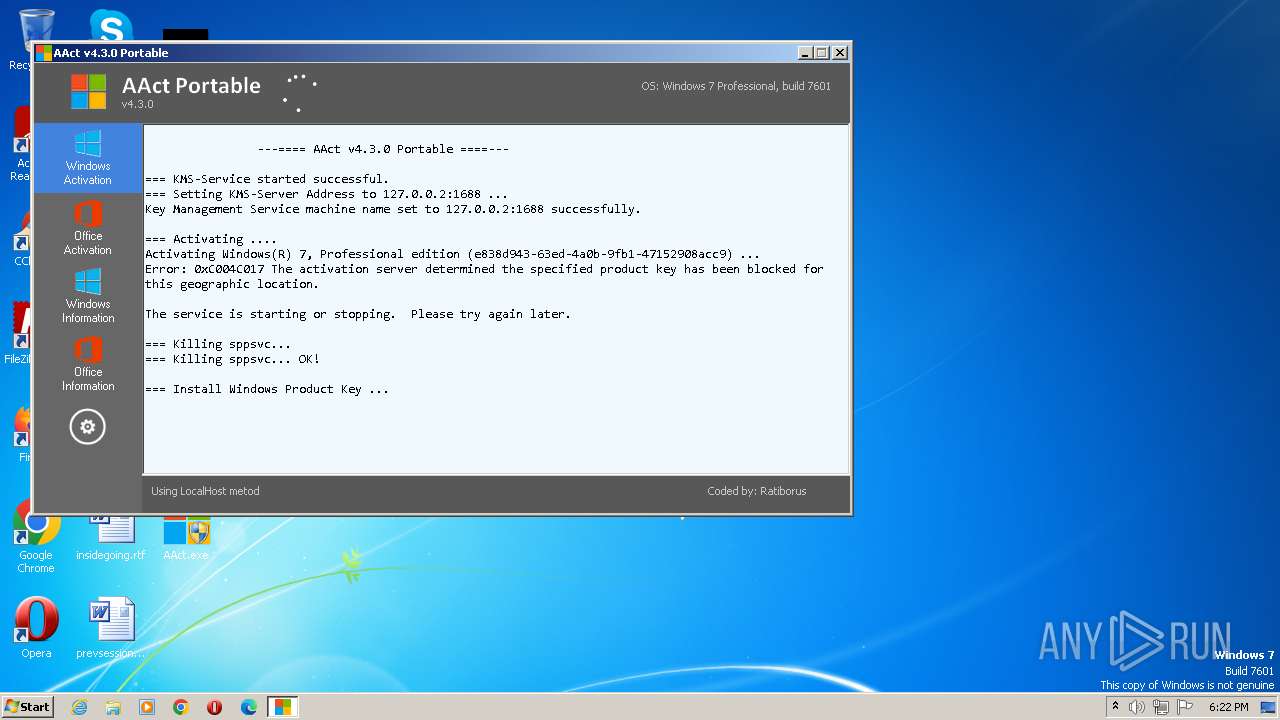
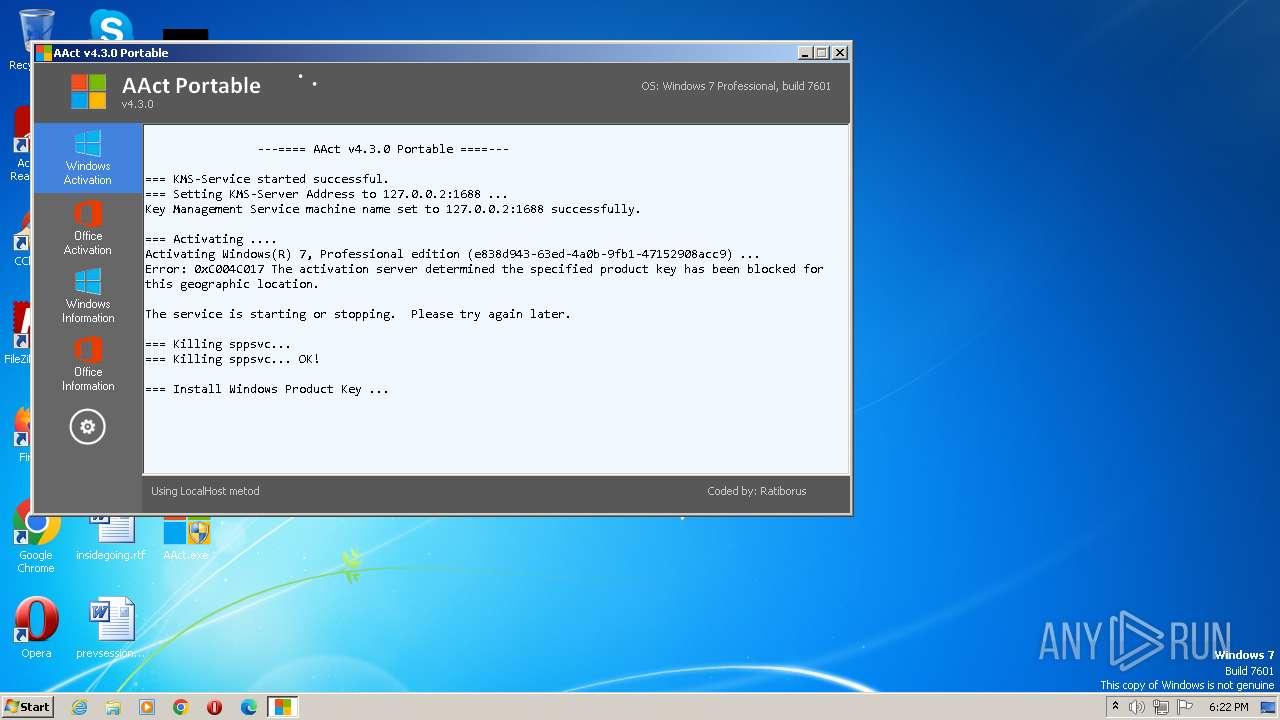
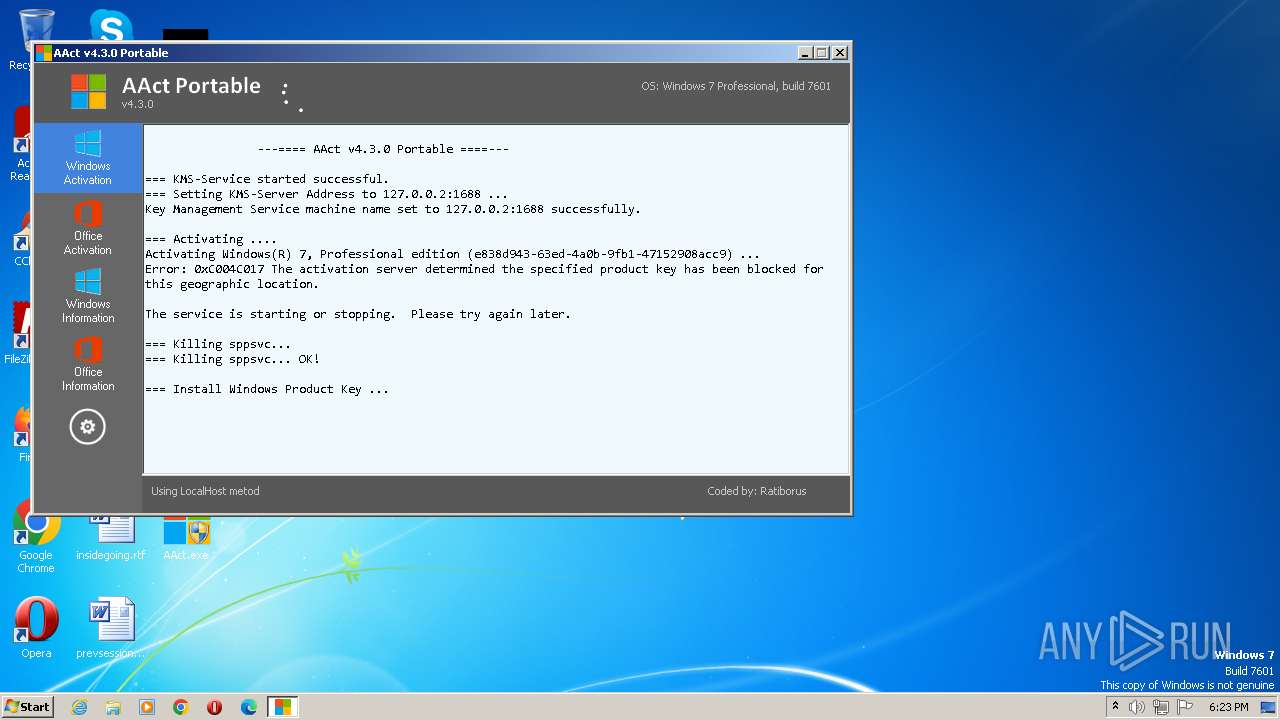
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2023, 17:18:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E41AE00985E350137DDD9C1280F04FC3 |
| SHA1: | D32A050B534F0AC5F8E6E9780E98F39E7AAF460A |
| SHA256: | ECD31E50FF35F41FBACF4B3C39901D5A2C9D4AE64B0C0385D661B1FD8B00481F |
| SSDEEP: | 49152:ENYemzlZ5Nnfto1LY8M11MvtKs5JcrKaVKaFq:aUZ5Nn6tY8GUgYEKoKaFq |
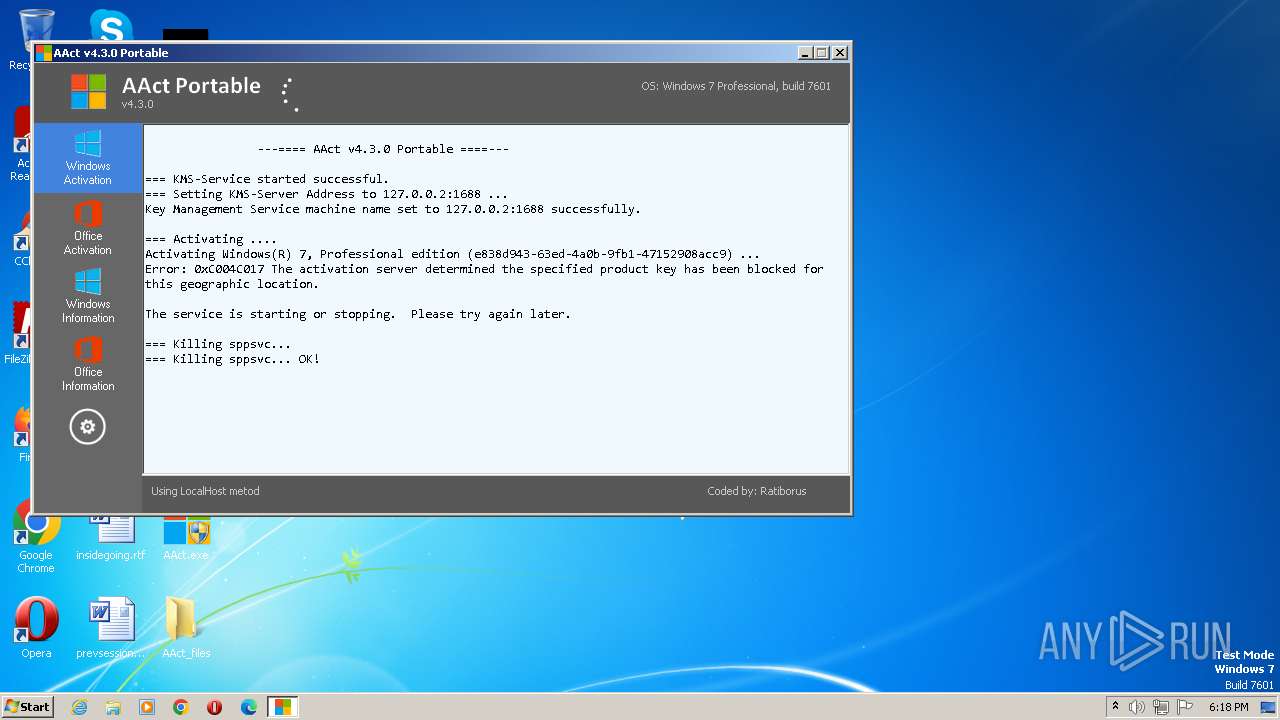
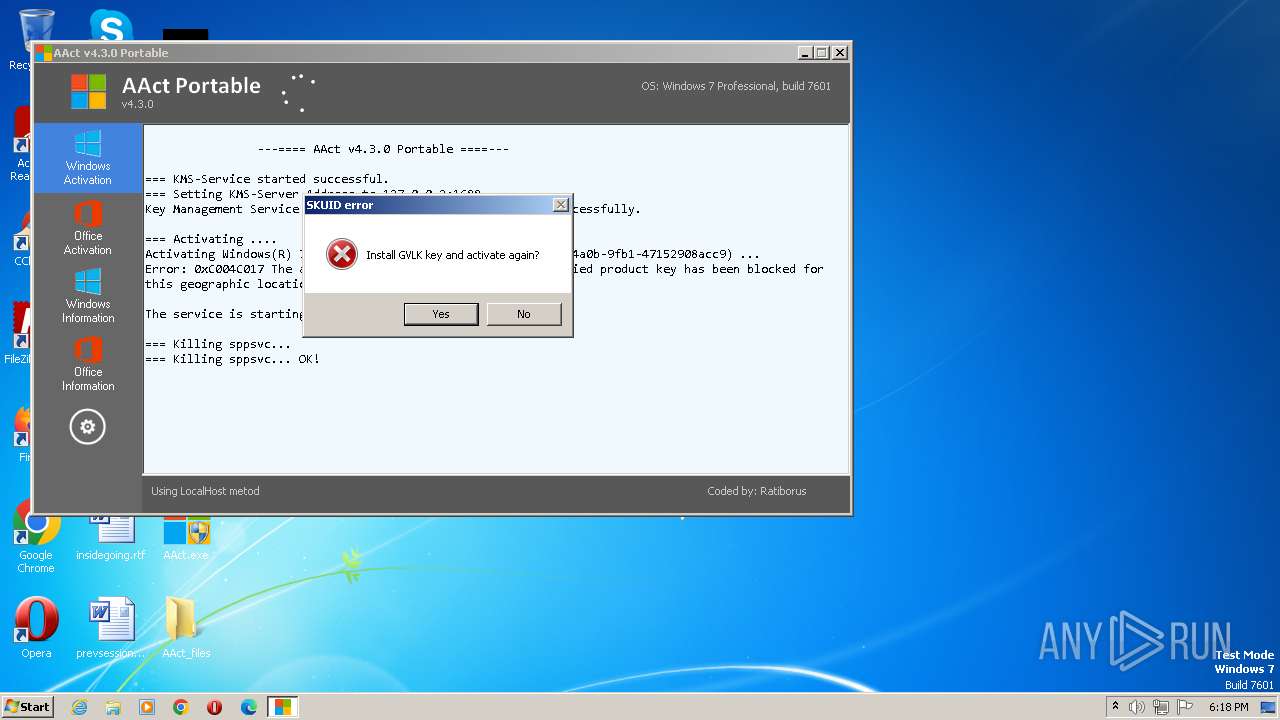
MALICIOUS
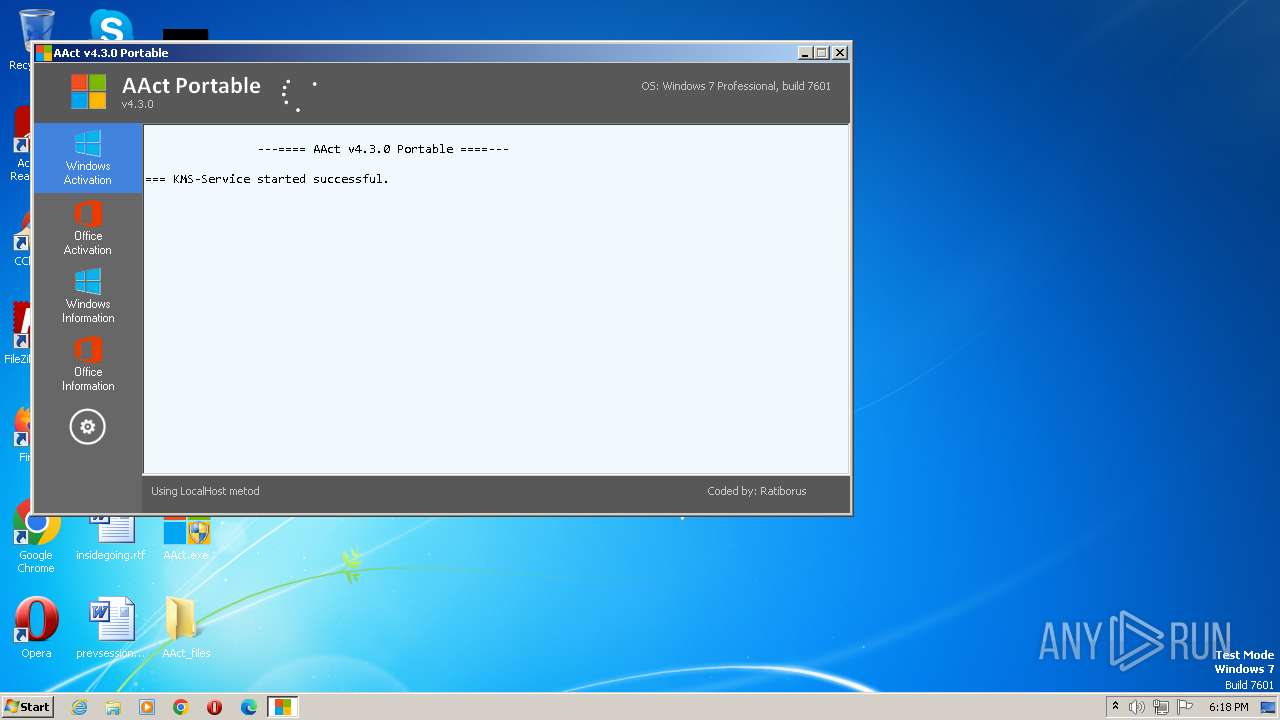
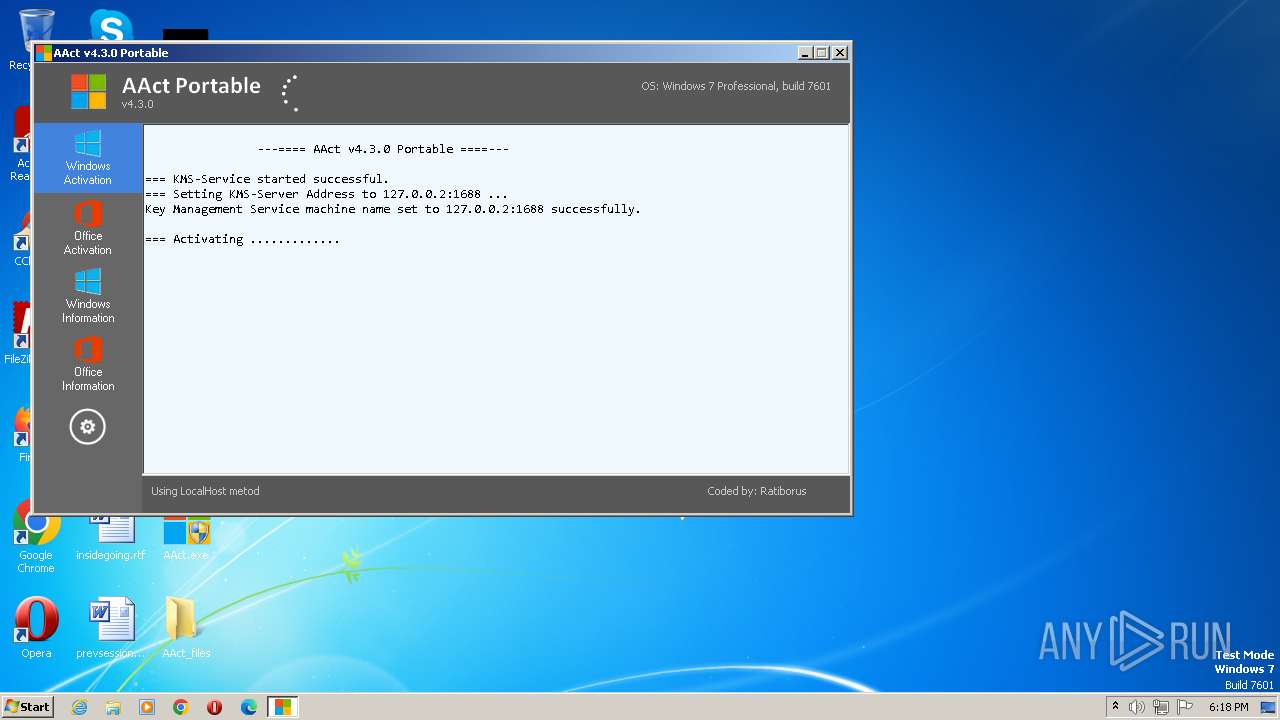
Application was dropped or rewritten from another process
- KMSSS.exe (PID: 2068)
Starts NET.EXE for service management
- cmd.exe (PID: 2820)
- net.exe (PID: 2664)
SUSPICIOUS
The process executes VB scripts
- cmd.exe (PID: 912)
- cmd.exe (PID: 2968)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 4028)
- cmd.exe (PID: 848)
- cmd.exe (PID: 328)
- cmd.exe (PID: 2460)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 3404)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 1768)
- cmd.exe (PID: 2492)
Starts CMD.EXE for commands execution
- AAct.exe (PID: 2740)
Uses REG/REGEDIT.EXE to modify registry
- AAct.exe (PID: 2740)
The process downloads a VBScript from the remote host
- cmd.exe (PID: 4028)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3116)
- cmd.exe (PID: 460)
Detected use of alternative data streams (AltDS)
- AAct.exe (PID: 2740)
Starts SC.EXE for service management
- cmd.exe (PID: 2468)
INFO
Checks supported languages
- AAct.exe (PID: 2740)
- KMSSS.exe (PID: 2068)
Reads product name
- AAct.exe (PID: 2740)
Reads the computer name
- KMSSS.exe (PID: 2068)
Reads the machine GUID from the registry
- KMSSS.exe (PID: 2068)
Reads Environment values
- AAct.exe (PID: 2740)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2404)
- cscript.exe (PID: 980)
- cscript.exe (PID: 2800)
- cscript.exe (PID: 956)
- cscript.exe (PID: 3892)
- cscript.exe (PID: 3676)
- cscript.exe (PID: 1000)
- cscript.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.5) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| FileDescription: | AAct x86 |
|---|---|
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Unknown (0) |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 4.3.0.0 |
| FileVersionNumber: | 4.3.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x2eabc0 |
| UninitializedDataSize: | 1507328 |
| InitializedDataSize: | 73728 |
| CodeSize: | 1548288 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2022:12:09 05:07:25+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Total processes
98
Monitored processes
37
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
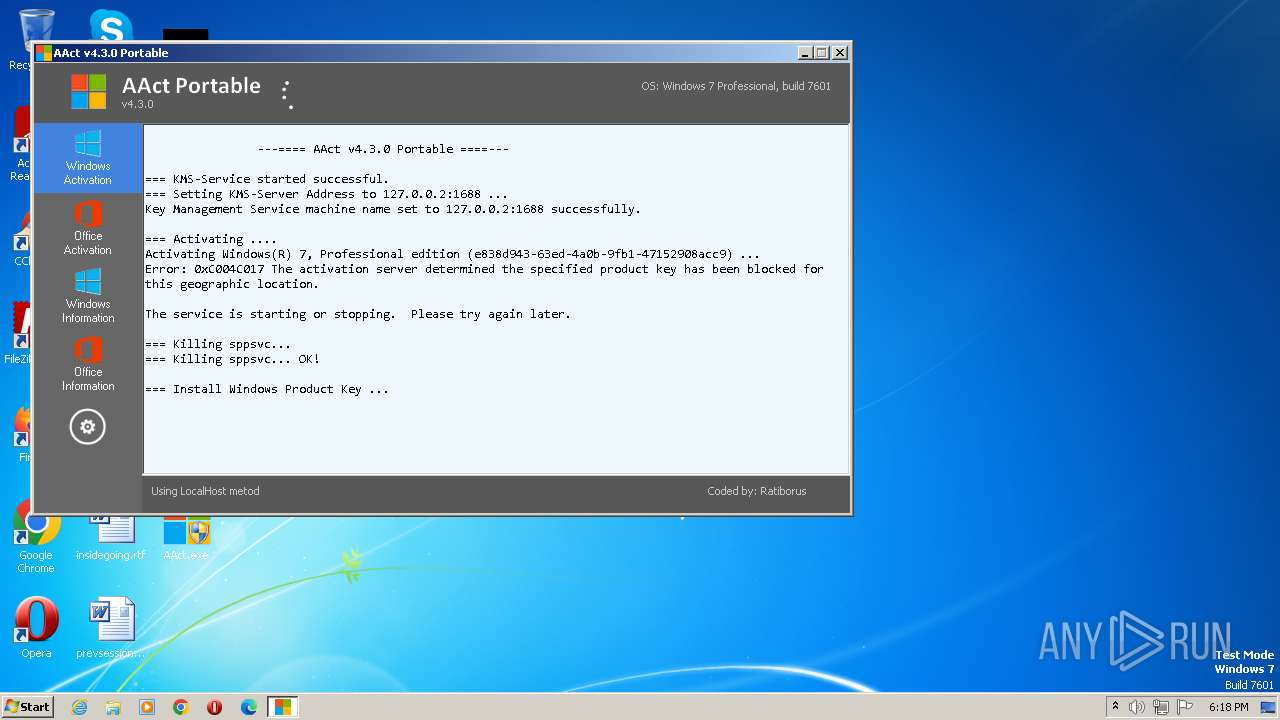
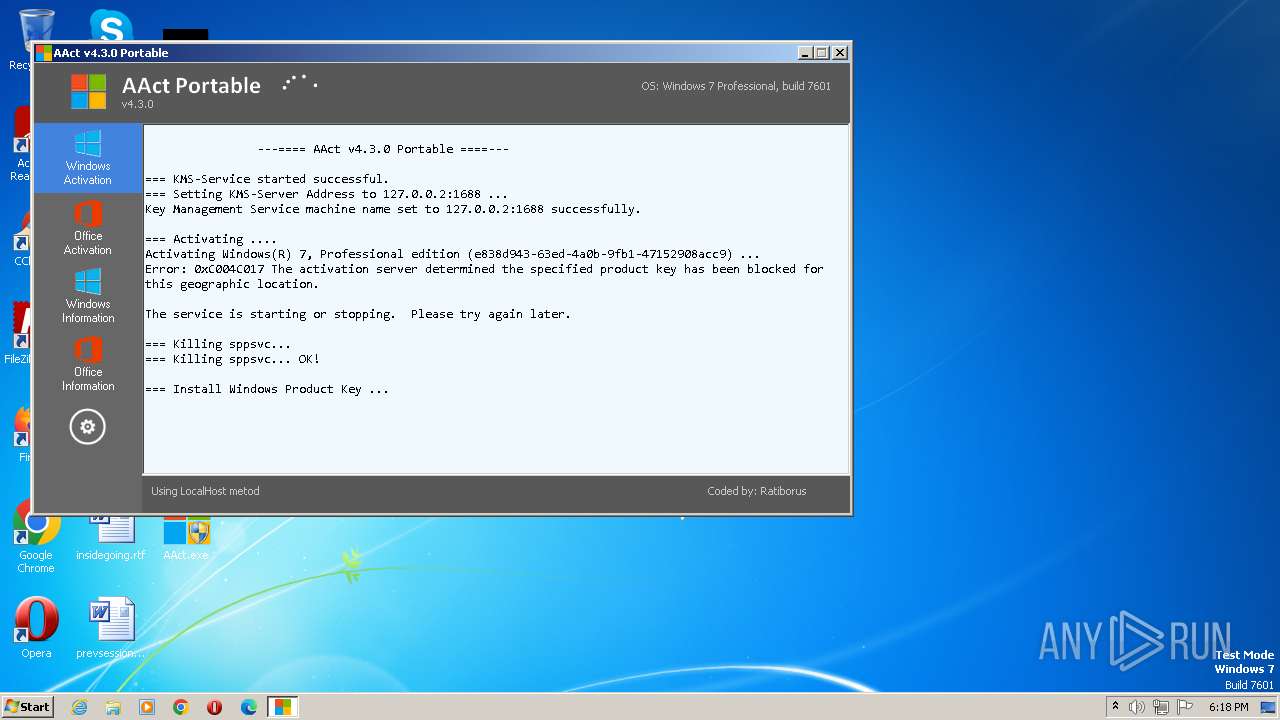
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /ipk FJ82H-XT6CR-J8D7P-XQJJ2-GPDD4 | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 460 | "C:\Windows\System32\cmd.exe" /c taskkill.exe /t /f /IM KMSSS.exe | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 848 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /dlv All | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 912 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /sdns | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /ckms-domain | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 980 | cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /act-type 0 | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1000 | cscript.exe C:\Windows\System32\slmgr.vbs //NoLogo /ato | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 3221536791 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1412 | Netsh.exe Advfirewall Firewall add rule name=0pen_Port_KMS dir=in action=allow protocol=TCP localport=1688 | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1576 | taskkill.exe /t /f /IM KMSSS.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1768 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\cmd.exe | — | AAct.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 730
Read events
2 598
Write events
132
Delete events
0
Modification events
| (PID) Process: | (3136) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1412) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3372) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
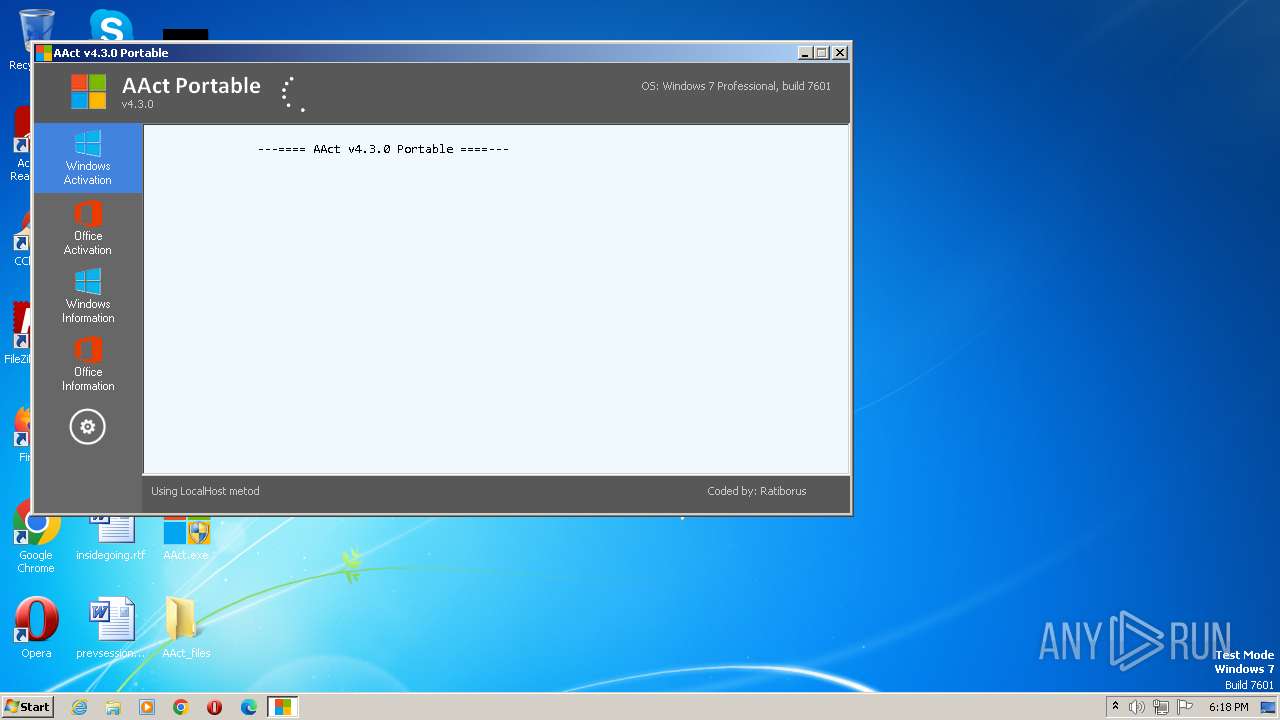
| 2740 | AAct.exe | C:\Users\admin\Desktop\AAct_files\KMSSS.exe | executable | |
MD5:01A80AAD5DABED1C1580F7E00213CF9D | SHA256:FD7499214ABAA13BF56D006AB7DE78EB8D6ADF17926C24ACE024D067049BC81D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3848 | WmiPrvSE.exe | POST | 302 | 23.56.204.161:80 | http://go.microsoft.com/fwlink/?LinkID=88340 | GB | — | — | unknown |
3848 | WmiPrvSE.exe | POST | 302 | 23.56.204.161:80 | http://go.microsoft.com/fwlink/?LinkID=88339 | GB | — | — | unknown |
3848 | WmiPrvSE.exe | POST | 302 | 23.56.204.161:80 | http://go.microsoft.com/fwlink/?LinkID=88341 | GB | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3848 | WmiPrvSE.exe | 23.56.204.161:80 | go.microsoft.com | AKAMAI-AS | GB | unknown |
3848 | WmiPrvSE.exe | 20.83.72.98:443 | activation.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |