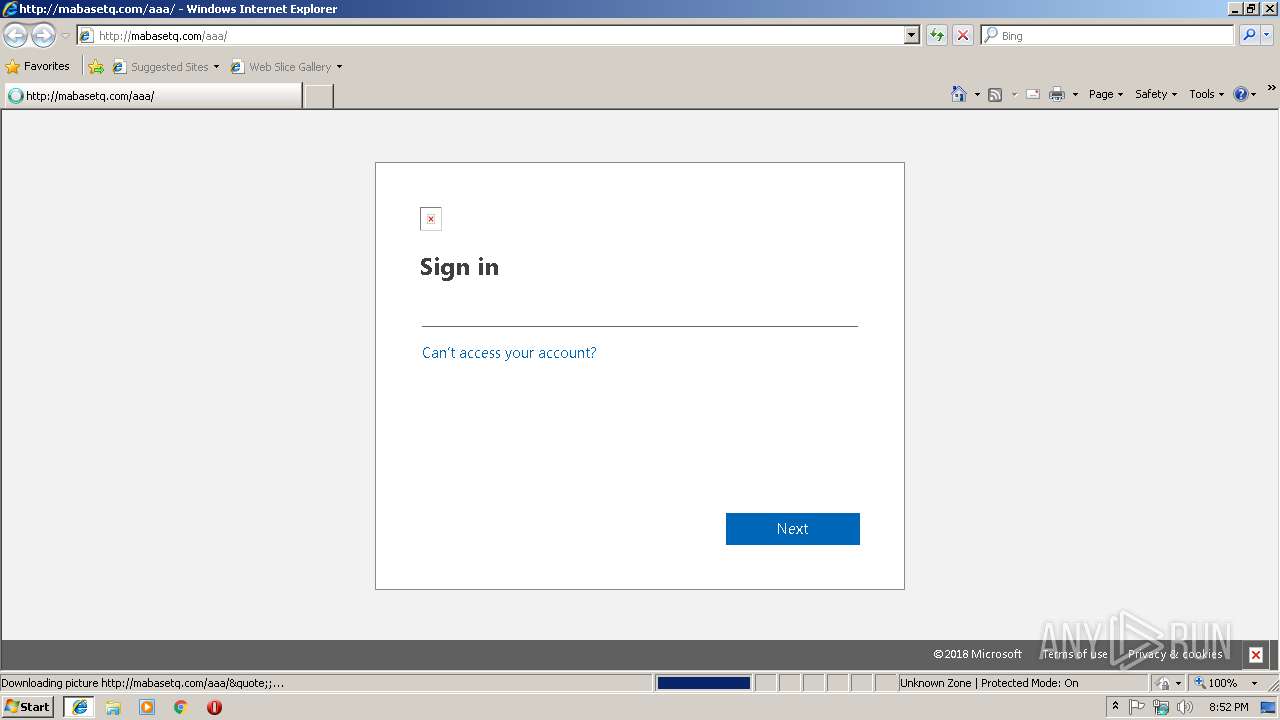
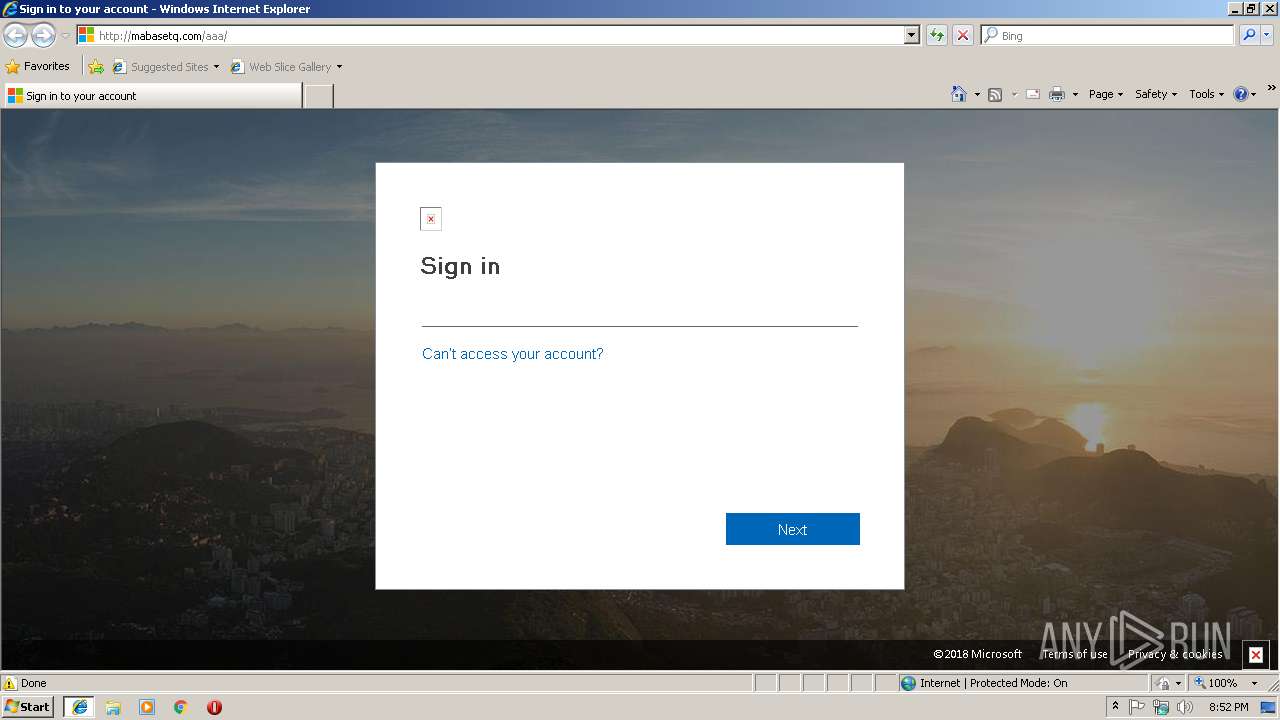
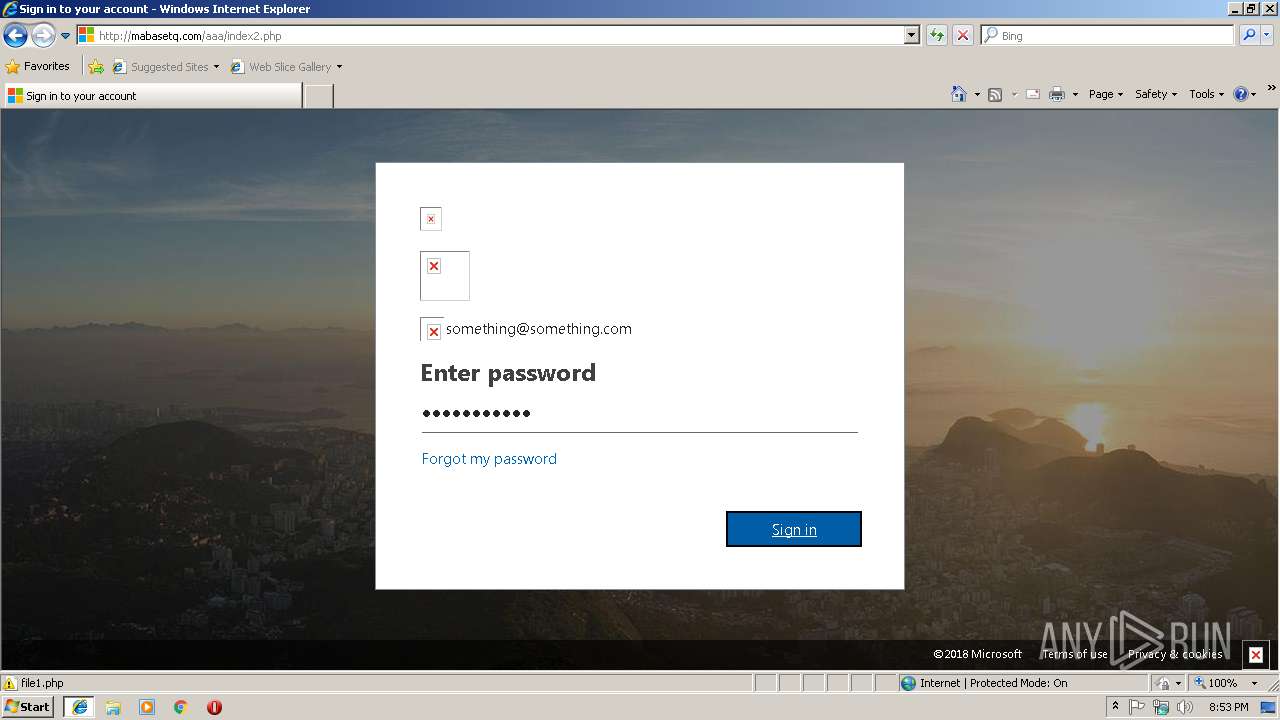
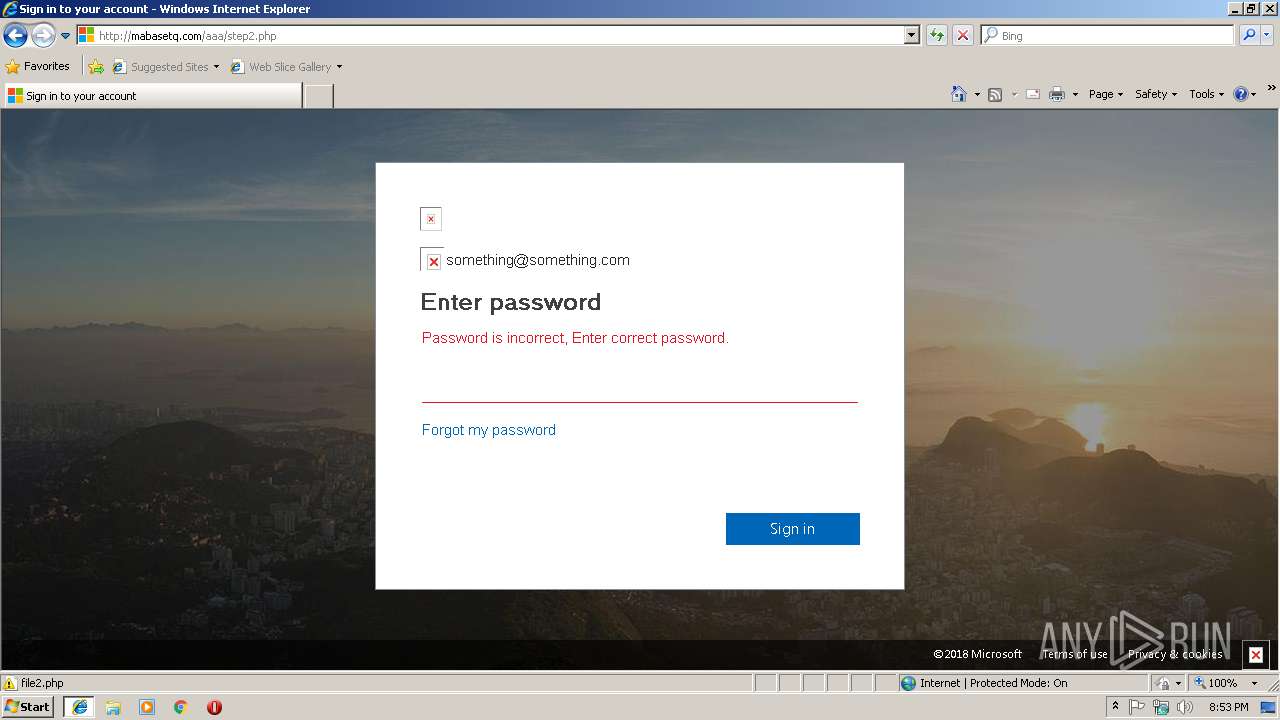
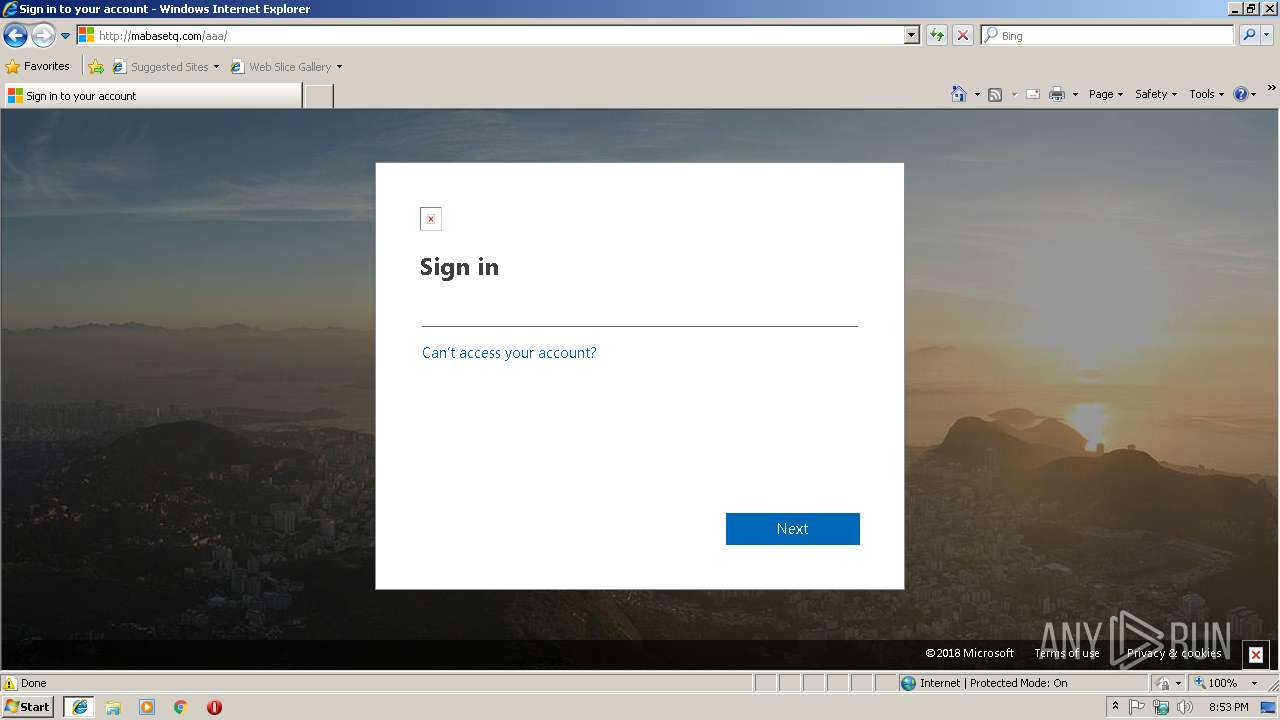
| URL: | http://mabasetq.com/aaa/ |
| Full analysis: | https://app.any.run/tasks/ac83eba4-89bc-4a7a-827c-c632b9054f30 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 20:52:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3F1A1ED847199BF973EE7A2A2AD5A170 |
| SHA1: | 9DCD3DE546C1B85E1DD502E27A69B0F4D23820E2 |
| SHA256: | ECCE78F5AFE968B9AA232BD80E540BD7DCC6824C09F094BE52993359DB66BA6F |
| SSDEEP: | 3:N1KTLx1Tf4:CvxJ4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3520)
Changes internet zones settings
- iexplore.exe (PID: 3520)
Reads settings of System Certificates
- iexplore.exe (PID: 2248)
Reads internet explorer settings
- iexplore.exe (PID: 2248)
Reads Internet Cache Settings
- iexplore.exe (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2248 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3520 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3520 | "C:\Program Files\Internet Explorer\iexplore.exe" http://mabasetq.com/aaa/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
445
Read events
381
Write events
61
Delete events
3
Modification events
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {B15550CF-1E87-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3520) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100020016001400340039000F00 | |||
Executable files
0
Suspicious files
1
Text files
33
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\aaa[1].txt | — | |
MD5:— | SHA256:— | |||
| 3520 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3520 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\index2[1].php | — | |
MD5:— | SHA256:— | |||
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\aaa[1].htm | html | |
MD5:— | SHA256:— | |||
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019012220190123\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3520 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019012220190123\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3520 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\NonCritical_iexplore.exe_12df8271b62395a348f102b12959f9768e2baf9_0dd98fb3\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\index2[1].htm | html | |
MD5:— | SHA256:— | |||
| 2248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\converged.v2.login.min[1].css | text | |
MD5:9B45F4084A4D9225B7A9C07888B86AF4 | SHA256:64570AC138A6D71E3880F0A50AE35192827C0D153B6484EF69D88CC1B92C4544 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
30
DNS requests
4
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
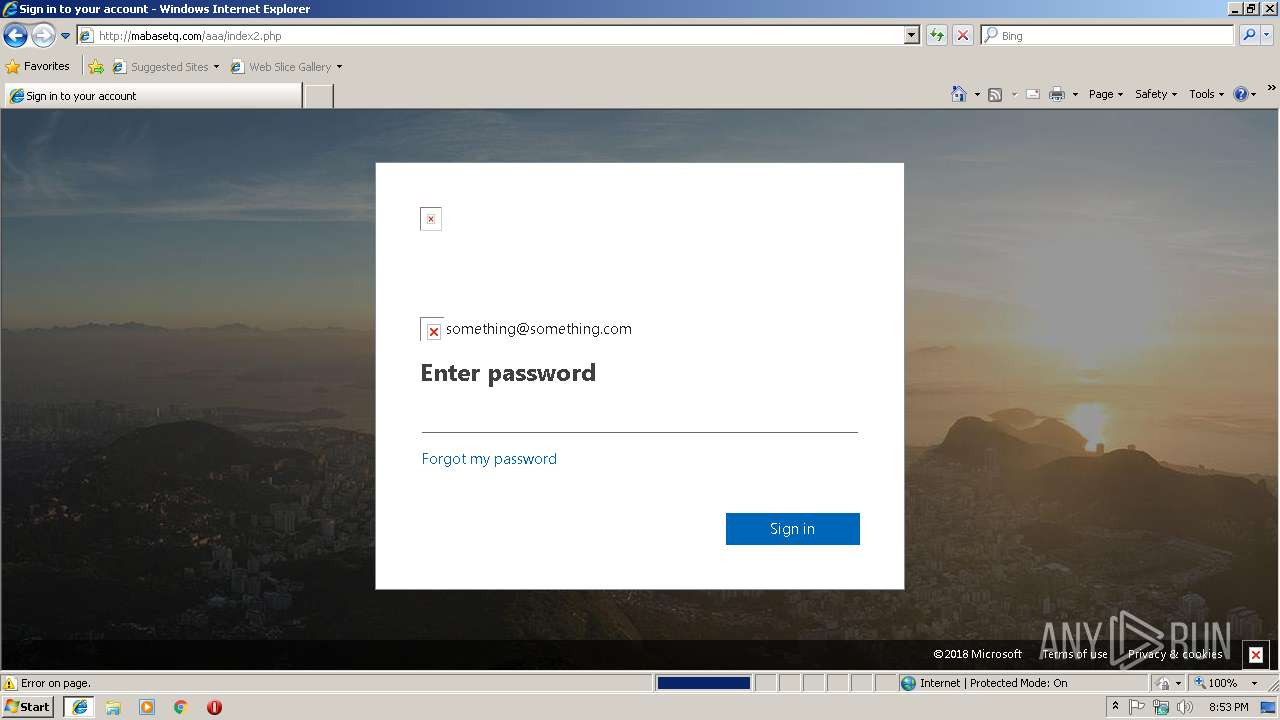
2248 | iexplore.exe | GET | 302 | 94.177.246.230:80 | http://mabasetq.com/aaa/s.php?mail=something@something.com&passwd=&ps=&psRNGCDefaultType=&psRNGCEntropy=&psRNGCSLK=&canary=4qQgTnDKNPGpFjIyyxWb%2BiZFSkaqH%2BYkJssPnR6gDy8%3D1%3A1&ctx=rQIIAdNiNtQztFIxgAAjXRCpa5CWZqibnApiIYEiIS6BRLtqhTc_brrMWmrusZ1l1cVVjPIZJSUFxVb6-vmlJTn5-dl6-Wlpmcmpesn5ufr55Yn6OxgZLzAyrmIyNzM2M7M0Mja1MDA3MrM0NLQ01rNMTjUxTTaz0E00NU7WNTE3TdG1SEux1DVMNk1OMzZOTDIyMr3FxO_vWFqSYQQi8osyq1I_MXGm5RflxhfkF5fMYk5wSS5xcst3THd2dAoq8kupCPYMc_SPNM1Iyikxig_LsjAKNXBOdzEs9owK9fRzDwvzNI1KdS_MC0vMq0wMME01Scmocs7KSQ3JjDD0K9ctysw0zksO8vLJDEjzMc9KK3dZxUxU6GxiZgN6OTc_7xQzW35Bal5mygUWxlcsPAasVhwcXAK8EmwKDD9YGBexAkNR4LtR2op8bde2TxX81-tZGE6x6psUBqaH5Ll4-wW4F7hleVZWVoQnaWdGuQVnJxZ6aEdmexUXB-QFmaW7VFrYGloZTmBjnMDG9oKN8QMbYwc7wy5OQtEAAA2&hpgrequestid=6632f710-6fa8-452b-86f2-780fd77f0400&flowToken=AQABAAEAAADXzZ3ifr-GRbDT45zNSEFEl-C_bh9vDXwBpmCPT_JVZD88DwuiI8QRin6Qiyu4ymKd6LEbBmslQA2QYDgiwq5XGFeRcQelzsfPL6GTvioEPgp2OLXK0dpe2APto9DukIKLbb_ofE3pXFwS503FZotevos6swUF0WECuZyXgvvco0NOuVd5i9CjMYsInmHzPQhiDHOZTnSrFh9YDRqxILdj3E9K9jOk882B3A2eXoEZ3Jl8apwMK8-UvQpmyCsRxmWJvbtRdPFxnypbmUaetCqgTCT-ZuHEdj7AuGVKOW3bvPMFsDXZZEBtaKv34Z9r2xw0TQ9OhzQJyFTyGTxogqVXDS2050RHj_ztjS66PzTuR6Ebt-8zY0-HV3R9mLLqOntYK9g5svb5rGub0YvQhX5WIAA&PPSX=&NewUser=1&FoundMSAs=&fspost=0&i21=0&CookieDisclosure=0&IsFidoSupported=1&i2=102&i17=&i18=&i19= | DE | — | — | malicious |
2248 | iexplore.exe | GET | 404 | 94.177.246.230:80 | http://mabasetq.com/aaa/fonts/office365icons.eot? | DE | html | 345 b | malicious |
2248 | iexplore.exe | GET | 200 | 94.177.246.230:80 | http://mabasetq.com/aaa/ | DE | html | 19.8 Kb | malicious |
2248 | iexplore.exe | GET | 404 | 94.177.246.230:80 | http://mabasetq.com/aaa/"e;; | DE | html | 333 b | malicious |
2248 | iexplore.exe | GET | 404 | 94.177.246.230:80 | http://mabasetq.com/aaa/index_files/boot.worldwide.1.mouse.js | DE | html | 358 b | malicious |
2248 | iexplore.exe | GET | 404 | 94.177.246.230:80 | http://mabasetq.com/aaa/index_files/boot.worldwide.0.mouse.js | DE | html | 358 b | malicious |
3520 | iexplore.exe | GET | 200 | 94.177.246.230:80 | http://mabasetq.com/aaa/index_files/favicon_a.ico | DE | image | 16.7 Kb | malicious |
2248 | iexplore.exe | GET | 200 | 94.177.246.230:80 | http://mabasetq.com/aaa/index_files/microsoft_logo.svg | DE | image | 3.57 Kb | malicious |
2248 | iexplore.exe | GET | 200 | 94.177.246.230:80 | http://mabasetq.com/aaa/index_files/ellipsis_grey.svg | DE | image | 915 b | malicious |
2248 | iexplore.exe | GET | 200 | 94.177.246.230:80 | http://mabasetq.com/aaa/index_files/converged.v2.login.min.css | DE | text | 93.2 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2248 | iexplore.exe | 94.177.246.230:80 | mabasetq.com | Aruba SAS | DE | suspicious |
3520 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2248 | iexplore.exe | 2.18.232.137:443 | r4.res.office365.com | Akamai International B.V. | — | whitelisted |
3520 | iexplore.exe | 94.177.246.230:80 | mabasetq.com | Aruba SAS | DE | suspicious |
2248 | iexplore.exe | 13.32.223.110:443 | logo.clearbit.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mabasetq.com |
| malicious |
www.bing.com |
| whitelisted |
r4.res.office365.com |
| whitelisted |
logo.clearbit.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2248 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
2248 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Phishing Microsoft Office365 |
3 ETPRO signatures available at the full report