| download: | droid4x.exe |
| Full analysis: | https://app.any.run/tasks/d5c28d12-0f21-474a-bd99-92f3779b4384 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2019, 18:53:42 |
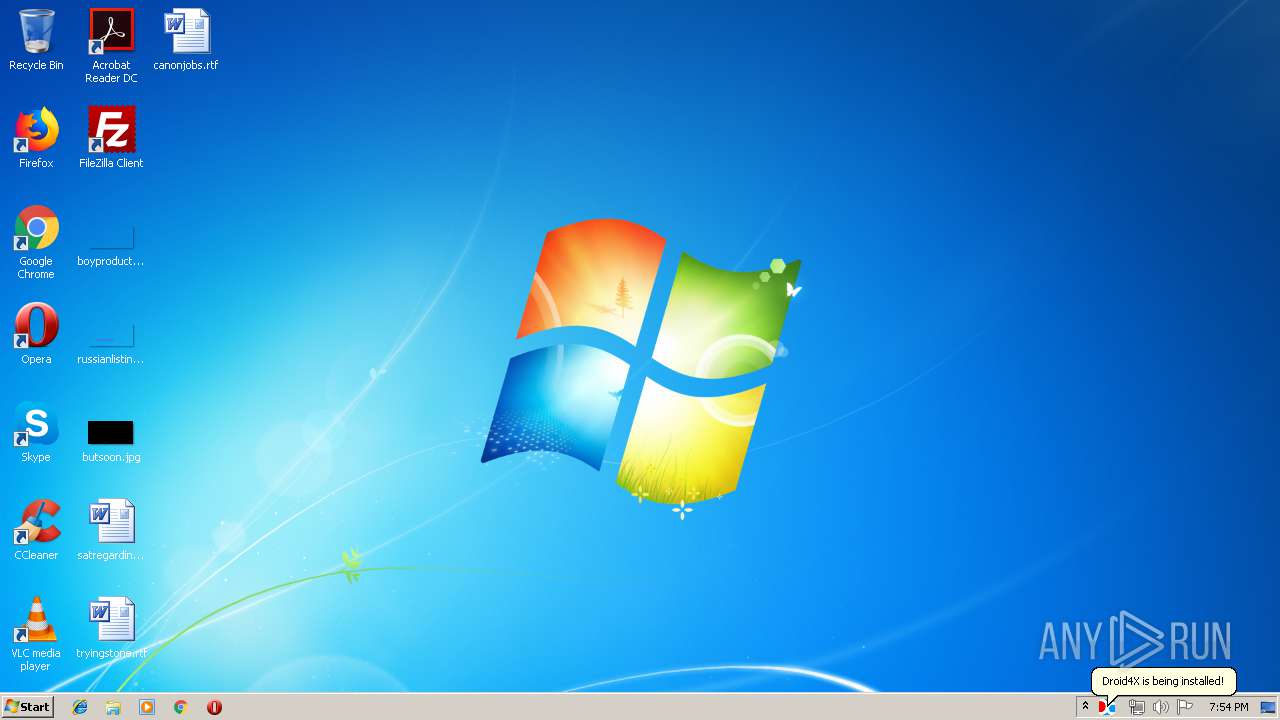
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F258A1BB7BD68D68CD0A5AA826FEF3B8 |
| SHA1: | 546428DA88A53BA68C24FE38EA14E6238AEB948D |
| SHA256: | ECB36D1A2B9DB95D49BA39C83495108CC2C5B2171FFBBCC887ED12AA53D64535 |
| SSDEEP: | 196608:RiCeZw7/ErVJP393fZHbRw85DYYCwHOgm+E:qHrVJRTj+wHE |
MALICIOUS
Loads dropped or rewritten executable
- droid4x.exe (PID: 2412)
- MiniThunderPlatform.exe (PID: 252)
Application was dropped or rewritten from another process
- MiniThunderPlatform.exe (PID: 252)
SUSPICIOUS
Executable content was dropped or overwritten
- droid4x.exe (PID: 2412)
- MiniThunderPlatform.exe (PID: 252)
Creates files in the program directory
- MiniThunderPlatform.exe (PID: 252)
Creates files in the user directory
- droid4x.exe (PID: 2412)
- MiniThunderPlatform.exe (PID: 252)
Low-level read access rights to disk partition
- MiniThunderPlatform.exe (PID: 252)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ax | | | DirectShow filter (54.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (11.2) |
| .exe | | | Win32 Executable (generic) (1.2) |
| .exe | | | Generic Win/DOS Executable (0.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:11 14:05:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 738816 |
| InitializedDataSize: | 8004096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x97323 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2015 13:05:54 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2015 13:05:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B4506 | 0x000B4600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49203 |
.rdata | 0x000B6000 | 0x000217CE | 0x00021800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.06346 |
.data | 0x000D8000 | 0x00005E5C | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.35566 |
.rsrc | 0x000DE000 | 0x00771BF0 | 0x00771C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.76971 |
.reloc | 0x00850000 | 0x00008CA4 | 0x00008E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58444 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.27441 | 2440 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 2.63843 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 2.57184 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 2.13514 | 16936 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 1.8542 | 67624 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 2.31718 | 88 | UNKNOWN | Chinese - PRC | RT_STRING |
8 | 3.26148 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 3.27441 | 2440 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 2.63843 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WLDAP32.dll |
WS2_32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
WMI_Exit | 1 | 0x0000AAB0 |
WMI_GetFirstHardwareInfo | 2 | 0x0000AAD0 |
WMI_GetNextHardwareInfo | 3 | 0x0000AB10 |
WMI_Init | 4 | 0x0000AB50 |
WMI_Install | 5 | 0x0000AB80 |
WMI_UnInstall | 6 | 0x0000AC90 |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Users\admin\AppData\Roaming\HaiYuInst\plugins\download\MiniThunderPlatform.exe" -StartTP | C:\Users\admin\AppData\Roaming\HaiYuInst\plugins\download\MiniThunderPlatform.exe | droid4x.exe | ||||||||||||
User: admin Company: 深圳市迅雷网络技术有限公司 Integrity Level: HIGH Description: 迅雷云加速开放平台 Exit code: 0 Version: 3.2.1.50 Modules
| |||||||||||||||
| 2412 | "C:\Users\admin\AppData\Local\Temp\droid4x.exe" | C:\Users\admin\AppData\Local\Temp\droid4x.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3464 | "C:\Users\admin\AppData\Local\Temp\droid4x.exe" | C:\Users\admin\AppData\Local\Temp\droid4x.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
94
Read events
65
Write events
29
Delete events
0
Modification events
| (PID) Process: | (2412) droid4x.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: droid4x.exe | |||
| (PID) Process: | (252) MiniThunderPlatform.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (252) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (252) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (252) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (252) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (252) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (252) MiniThunderPlatform.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\MiniThunderPlatform_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (252) MiniThunderPlatform.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (252) MiniThunderPlatform.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
12
Suspicious files
2
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 252 | MiniThunderPlatform.exe | C:\Users\admin\AppData\Roaming\HaiYuInst\DXInst\vbox32.msibk.td.cfg | — | |
MD5:— | SHA256:— | |||
| 252 | MiniThunderPlatform.exe | C:\Users\admin\AppData\Roaming\HaiYuInst\DXInst\vbox32.msibk | — | |
MD5:— | SHA256:— | |||
| 2412 | droid4x.exe | C:\Users\admin\AppData\Roaming\HaiYuInst\DXInst\vbox32.msi | — | |
MD5:— | SHA256:— | |||
| 252 | MiniThunderPlatform.exe | C:\Users\admin\AppData\Roaming\HaiYuInst\DXInst\Setup.exebk.td | — | |
MD5:— | SHA256:— | |||
| 2412 | droid4x.exe | C:\Users\admin\AppData\Roaming\HaiYuInst\plugins\download\id.dat | text | |
MD5:— | SHA256:— | |||
| 252 | MiniThunderPlatform.exe | C:\Users\Public\Thunder Network\Mini_downloadlib\ODAwMDA2MDA=\Version_3_2_1_50\Profiles\error.dat | text | |
MD5:— | SHA256:— | |||
| 2412 | droid4x.exe | C:\Users\admin\AppData\Roaming\HaiYuInst\plugins\download\dl_peer_id.dll | executable | |
MD5:DBA9A19752B52943A0850A7E19AC600A | SHA256:69A5E2A51094DC8F30788D63243B12A0EB2759A3F3C3A159B85FD422FC00AC26 | |||
| 2412 | droid4x.exe | C:\Users\admin\AppData\Roaming\HaiYuInst\plugins\download\zlib1.dll | executable | |
MD5:89F6488524EAA3E5A66C5F34F3B92405 | SHA256:BD29D2B1F930E4B660ADF71606D1B9634188B7160A704A8D140CADAFB46E1E56 | |||
| 2412 | droid4x.exe | C:\Users\admin\AppData\Roaming\HaiYuInst\plugins\download\XLBugHandler.dll | executable | |
MD5:92154E720998ACB6FA0F7BAD63309470 | SHA256:1845DF41DA539BCA264F59365BF7453B686B9098CC94CD0E2B9A20C74A561096 | |||
| 2412 | droid4x.exe | C:\Users\admin\AppData\Roaming\HaiYuInst\plugins\download\MiniThunderPlatform.exe | executable | |
MD5:DC62945C4E112BC3C3B043C8668A33DF | SHA256:C9B84B242479762DFCA7B707376FDE73CE99AA7BEFA74B9D4F18B4EC1967BD29 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
63
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
252 | MiniThunderPlatform.exe | GET | — | 223.99.254.231:80 | http://dl.haima.me/download/D4XU/win/0.10.7/bins/vbox32.msi?201507134c8c07db5d43d0ccb4de241a1250cf30 | CN | — | — | unknown |
252 | MiniThunderPlatform.exe | GET | — | 223.99.254.231:80 | http://dl.haima.me/download/D4XU/win/0.10.7/bins/vbox32.msi?201507134c8c07db5d43d0ccb4de241a1250cf30 | CN | — | — | unknown |
252 | MiniThunderPlatform.exe | GET | — | 223.99.254.231:80 | http://dl.haima.me/download/D4XU/win/0.10.7/bins/vbox32.msi?201507134c8c07db5d43d0ccb4de241a1250cf30 | CN | — | — | unknown |
252 | MiniThunderPlatform.exe | GET | — | 223.99.254.231:80 | http://dl.haima.me/download/D4XU/win/0.10.7/bins/vbox32.msi?201507134c8c07db5d43d0ccb4de241a1250cf30 | CN | — | — | unknown |
252 | MiniThunderPlatform.exe | GET | — | 223.99.254.231:80 | http://dl.haima.me/download/D4XU/win/0.10.7/bins/vbox32.msi?201507134c8c07db5d43d0ccb4de241a1250cf30 | CN | — | — | unknown |
252 | MiniThunderPlatform.exe | GET | — | 223.99.254.231:80 | http://dl.haima.me/download/D4XU/win/0.10.7/bins/vbox32.msi?201507134c8c07db5d43d0ccb4de241a1250cf30 | CN | — | — | unknown |
252 | MiniThunderPlatform.exe | GET | — | 223.99.254.231:80 | http://dl.haima.me/download/D4XU/win/0.10.7/bins/vbox32.msi?201507134c8c07db5d43d0ccb4de241a1250cf30 | CN | — | — | unknown |
252 | MiniThunderPlatform.exe | GET | — | 223.99.254.231:80 | http://dl.haima.me/download/D4XU/win/0.10.7/bins/vbox32.msi?201507134c8c07db5d43d0ccb4de241a1250cf30 | CN | — | — | unknown |
2412 | droid4x.exe | GET | 200 | 120.26.14.152:80 | http://config.droid4x.cn/update/win/D4XU.ini | CN | txt | 17.5 Kb | unknown |
2412 | droid4x.exe | GET | 463 | 69.172.201.153:80 | http://www.droid4x.com/dxadmin/operate.php?sys=Windows%207&type=0&sysver=6.1.7601&name=Installer&version=InstallerVersion&cpudes=&cpu=4&cpusn=1F8BFBFF000506E3&memory=3583&gpu=Standard%20VGA%20Graphics%20Adapter&gpudriver=vga.dll&vt=-1&sign=4631d5635c3a414cdc8812952c703a07&rand=14882&mac=52:54:00:4A:04:AF&hdsn=4d51303030302031202020202020202020202020&guid=90059c37-1320-41a4-b58d-2b75a9850d2f&step=DownloaderStart&interval=0&channel=Z001&time=2019:05:30_19:54:09&baifenbi=0&did=1755834a047e1cb34b644ddc0f52390a | US | html | 8.64 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
252 | MiniThunderPlatform.exe | 119.188.108.56:8000 | hub5pnc.hz.sandai.net | CHINA UNICOM China169 Backbone | CN | malicious |
2412 | droid4x.exe | 69.172.201.153:80 | www.droid4x.com | Dosarrest Internet Security LTD | US | malicious |
252 | MiniThunderPlatform.exe | 112.80.23.156:80 | pmap.hz.sandai.net | CHINA UNICOM China169 Backbone | CN | malicious |
252 | MiniThunderPlatform.exe | 123.129.242.221:80 | hub5c.hz.sandai.net | CHINA UNICOM China169 Backbone | CN | malicious |
— | — | 211.91.242.38:8000 | hub5pn.hz.sandai.net | — | CN | unknown |
252 | MiniThunderPlatform.exe | 119.188.108.14:80 | hub5pr.hz.sandai.net | CHINA UNICOM China169 Backbone | CN | unknown |
252 | MiniThunderPlatform.exe | 121.9.209.160:80 | imhub5pr.hz.sandai.net | CHINANET Guangdong province network | CN | unknown |
252 | MiniThunderPlatform.exe | 163.177.79.152:80 | score.phub.hz.sandai.net | China Unicom Guangdong IP network | CN | malicious |
— | — | 119.188.108.36:8000 | hub5u.hz.sandai.net | CHINA UNICOM China169 Backbone | CN | unknown |
252 | MiniThunderPlatform.exe | 123.129.242.179:80 | hubstat.hz.sandai.net | CHINA UNICOM China169 Backbone | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.droid4x.cn |
| unknown |
log.droid4x.cn |
| unknown |
www.droid4x.com |
| malicious |
hub5pnc.hz.sandai.net |
| malicious |
hub5pn.hz.sandai.net |
| unknown |
hub5u.hz.sandai.net |
| unknown |
relay.phub.hz.sandai.net |
| whitelisted |
hub5c.hz.sandai.net |
| malicious |
pmap.hz.sandai.net |
| malicious |
hub5pr.hz.sandai.net |
| unknown |
Threats
Process | Message |
|---|---|
droid4x.exe | C:\Users\admin\AppData\Roaming\droid4xinstaller.log |
droid4x.exe | |
droid4x.exe | |
droid4x.exe |