| download: | /MalwareTeam/WUDFHost/raw/main/WUDFHost.exe |
| Full analysis: | https://app.any.run/tasks/0454fd61-7180-459b-ac7d-e462e0da9d36 |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2023, 01:12:49 |
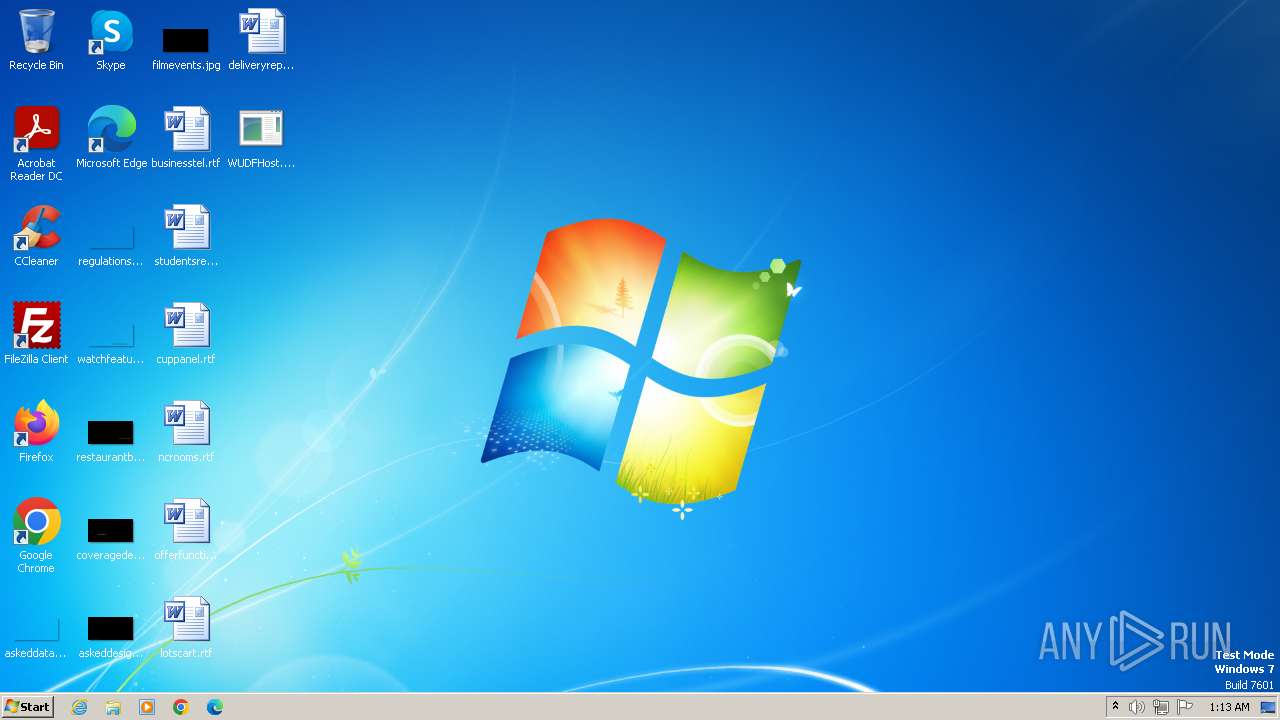
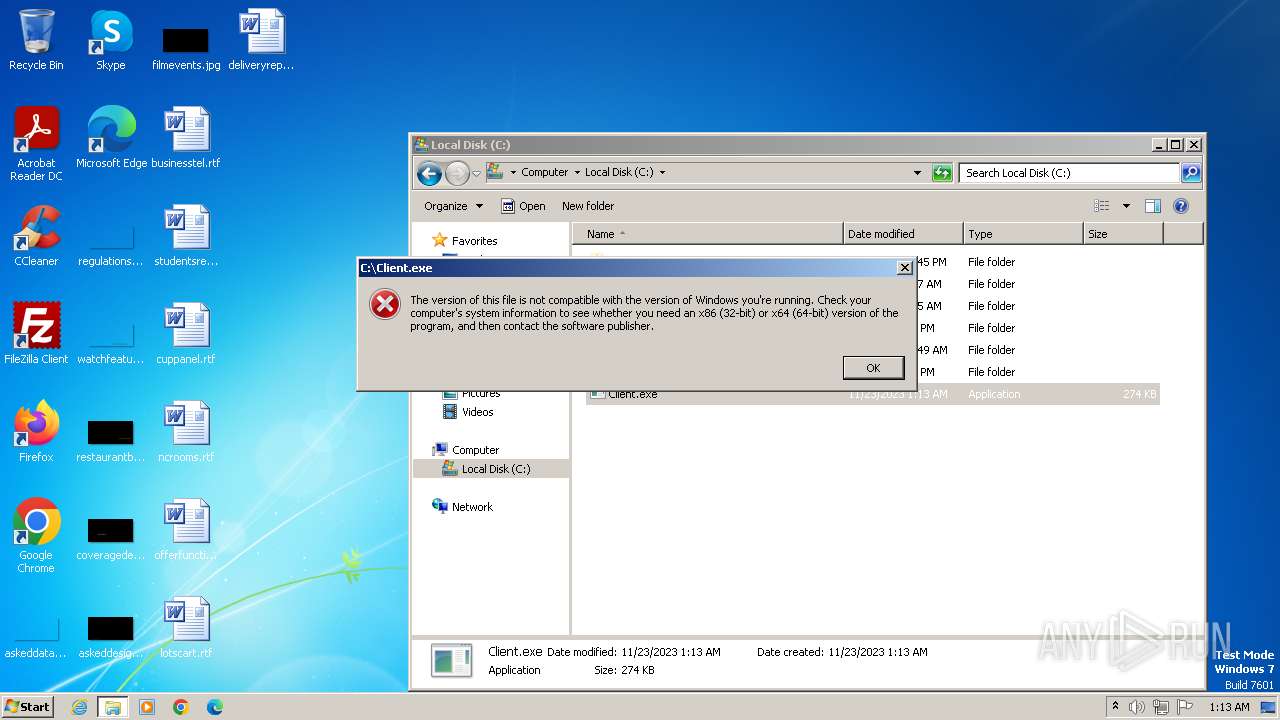
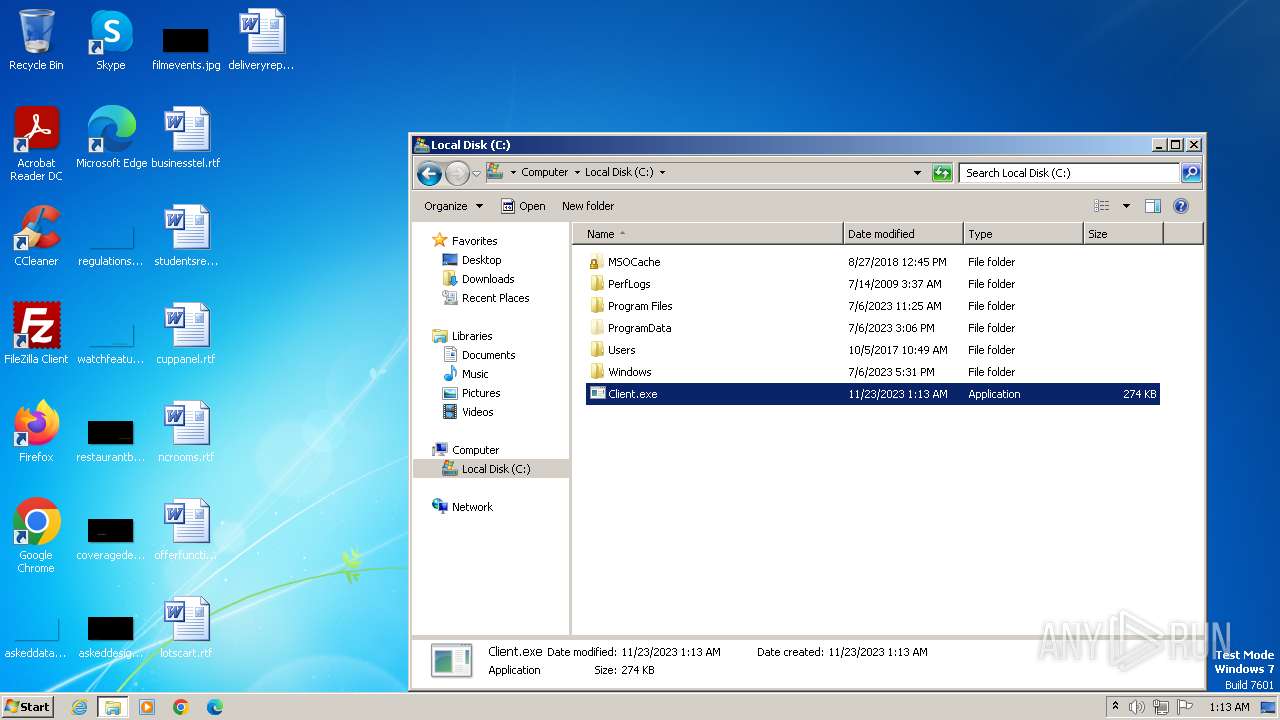
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | F6E138191D0684AE9ECC79340D1348E2 |
| SHA1: | D2671ECF43E1878369E181857C632ABDC80A4F09 |
| SHA256: | ECADF21CBD141C92DAC2CF0EFCFE66CCE87367916674AFA95693C3CAECB7606A |
| SSDEEP: | 12288:Y6aiiKODNZo2gL4OQEqhHVutjx6XIOKhir:Y69ODNZJgL4OZqVVutMIOKhe |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 3644)
Adds path to the Windows Defender exclusion list
- WUDFHost.exe (PID: 3776)
Uses Task Scheduler to autorun other applications
- WUDFHost.exe (PID: 3776)
Changes powershell execution policy (Bypass)
- WUDFHost.exe (PID: 3776)
Bypass execution policy to execute commands
- powershell.exe (PID: 3908)
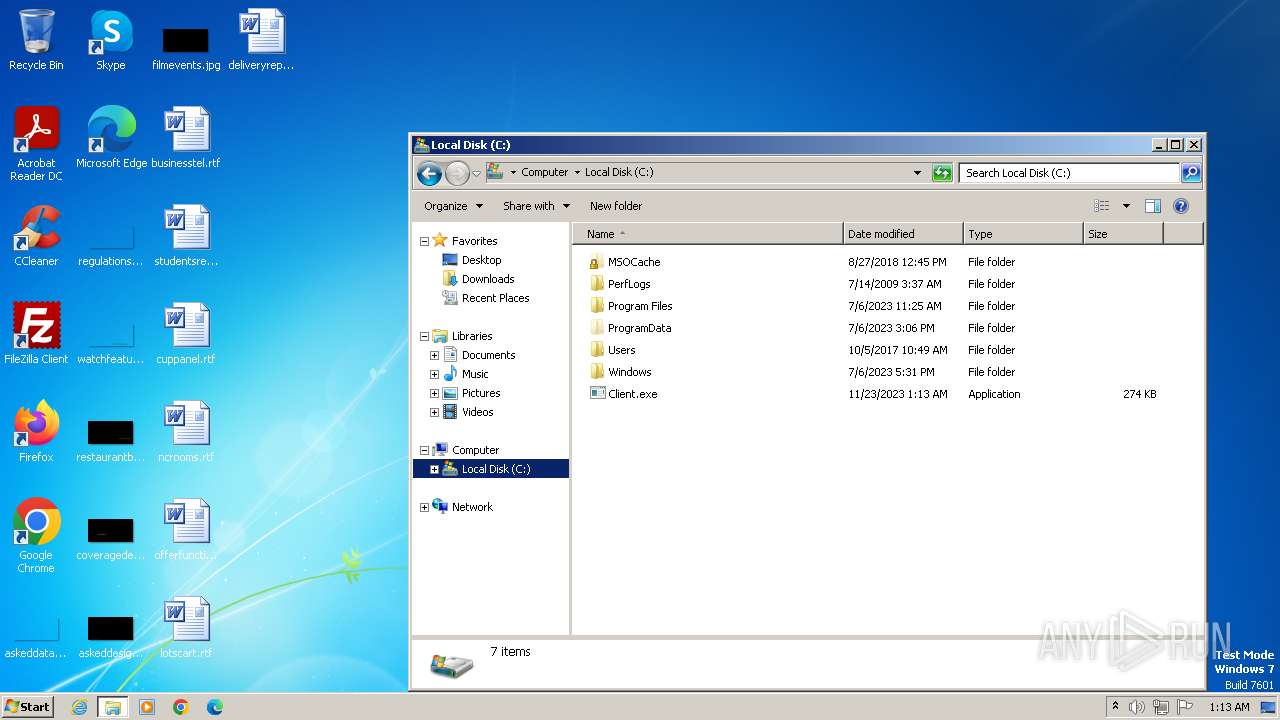
Drops the executable file immediately after the start
- WUDFHost.exe (PID: 3776)
SUSPICIOUS
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- WUDFHost.exe (PID: 3508)
Reads the Internet Settings
- WUDFHost.exe (PID: 3508)
- WUDFHost.exe (PID: 3776)
- mshta.exe (PID: 4056)
Script adds exclusion path to Windows Defender
- WUDFHost.exe (PID: 3776)
Starts CMD.EXE for commands execution
- WUDFHost.exe (PID: 3776)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4064)
Uses TASKKILL.EXE to kill process
- mshta.exe (PID: 4056)
Starts POWERSHELL.EXE for commands execution
- WUDFHost.exe (PID: 3776)
Powershell version downgrade attack
- powershell.exe (PID: 3908)
Process drops legitimate windows executable
- WUDFHost.exe (PID: 3776)
Executing commands from a ".bat" file
- WUDFHost.exe (PID: 3776)
Runs shell command (SCRIPT)
- mshta.exe (PID: 4056)
INFO
Reads the computer name
- WUDFHost.exe (PID: 3508)
- WUDFHost.exe (PID: 3776)
Checks supported languages
- WUDFHost.exe (PID: 3508)
- WUDFHost.exe (PID: 3776)
Reads the machine GUID from the registry
- WUDFHost.exe (PID: 3508)
- WUDFHost.exe (PID: 3776)
Checks transactions between databases Windows and Oracle
- cmstp.exe (PID: 3412)
Creates files in the program directory
- dllhost.exe (PID: 3644)
Create files in a temporary directory
- WUDFHost.exe (PID: 3776)
Reads Internet Explorer settings
- mshta.exe (PID: 4056)
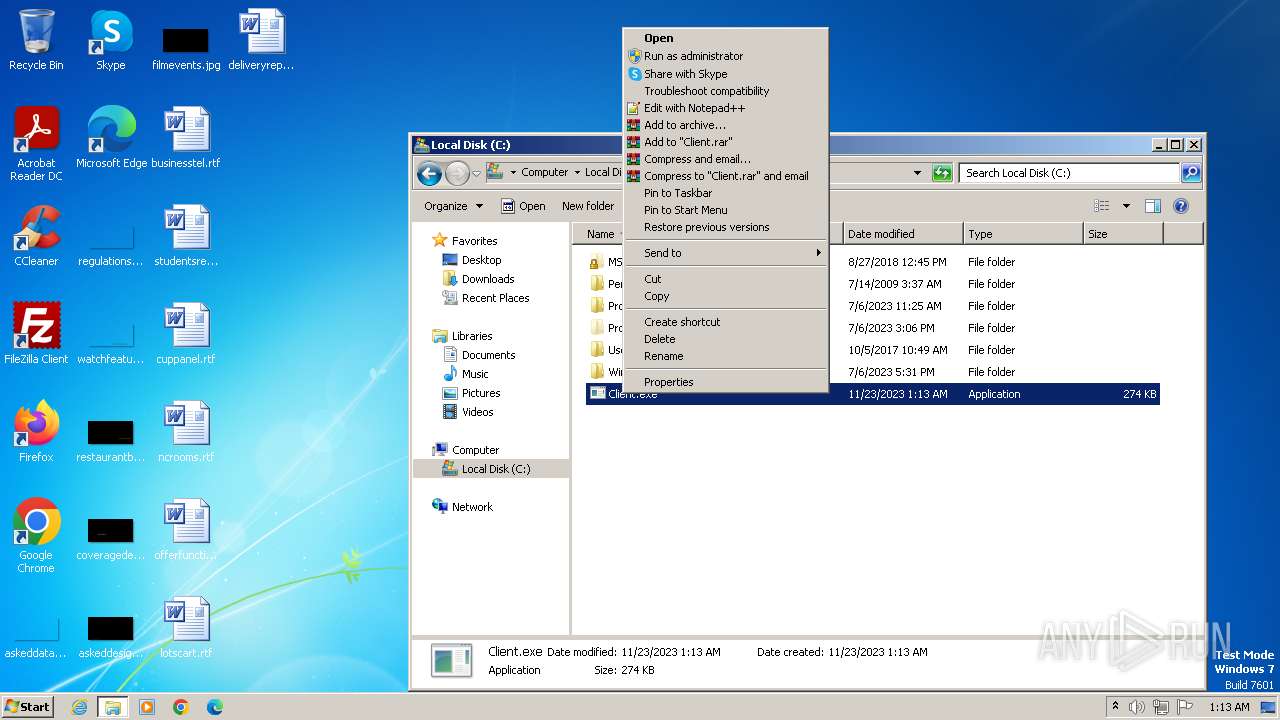
Manual execution by a user
- explorer.exe (PID: 1628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:11:15 12:39:08+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 259072 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4139e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.0.19041.3570 |
| ProductVersionNumber: | 10.0.19041.3570 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Driver Foundation - User-mode Driver Framework Host Process |
| FileVersion: | 10.0.19041.3570 |
| InternalName: | WUDFHost.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WUDFHost.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.19041.3570 |
| AssemblyVersion: | 10.0.19041.3570 |
Total processes
57
Monitored processes
11
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1628 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3412 | "C:\Windows\system32\cmstp.exe" /au C:\Windows\temp\2y4izjvu.inf | C:\Windows\System32\cmstp.exe | — | WUDFHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile Installer Exit code: 1 Version: 7.02.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3508 | "C:\Users\admin\Desktop\WUDFHost.exe" | C:\Users\admin\Desktop\WUDFHost.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Driver Foundation - User-mode Driver Framework Host Process Exit code: 0 Version: 10.0.19041.3570 Modules
| |||||||||||||||
| 3644 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3712 | "C:\Windows\System32\taskkill.exe" /IM cmstp.exe /F | C:\Windows\System32\taskkill.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3776 | "C:\Users\admin\Desktop\WUDFHost.exe" | C:\Users\admin\Desktop\WUDFHost.exe | dllhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Driver Foundation - User-mode Driver Framework Host Process Exit code: 0 Version: 10.0.19041.3570 Modules
| |||||||||||||||
| 3908 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Client.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WUDFHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4016 | "C:\Windows\System32\schtasks.exe" /Create /F /TN "Client" /SC ONLOGON /TR "C:\\Client.exe" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | WUDFHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4044 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4056 | mshta vbscript:Execute("CreateObject(""WScript.Shell"").Run ""taskkill /IM cmstp.exe /F"", 0, true:close") | C:\Windows\System32\mshta.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 232
Read events
2 152
Write events
80
Delete events
0
Modification events
| (PID) Process: | (3508) WUDFHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3508) WUDFHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3508) WUDFHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3508) WUDFHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3776) WUDFHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3776) WUDFHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3776) WUDFHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3776) WUDFHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3908) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4056) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | WUDFHost.exe | C:\Windows\temp\2y4izjvu.inf | text | |
MD5:532E324F2C705AF8A5E9221F1296D589 | SHA256:AE21AE2AB0B4DAE8BA0A62BB6BF928623B603B7CB3CAA4BCFC6DB5FECAC3E4C7 | |||
| 3776 | WUDFHost.exe | C:\Users\admin\AppData\Local\Temp\tmpC1FD.tmp.bat | text | |
MD5:76C8AE0F4EB6FB9F6ABAEBC2FBA069BE | SHA256:2E5107BD795FF505F455E532E8E29BD2CB00FD968FF12723BE673F3E87CD6856 | |||
| 3908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QJXA8CPWHPT0Z1TUYTAQ.temp | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF16be05.TMP | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3644 | dllhost.exe | C:\Windows\INF\setupapi.app.log | text | |
MD5:E8383940EC10581B447493C122173FA1 | SHA256:927B7D12FC97642FB293BB4A390C8DE4DC01F7C57D856477400CD35B01B503E8 | |||
| 3776 | WUDFHost.exe | C:\Client.exe | executable | |
MD5:AA9E905F440BED3444A993248AE3EB98 | SHA256:1135E8D09D64D468B986FE3E36F4CDF808551F8B541A09406E17B63B1E004B96 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |