| File name: | Xworm 5.6.exe |
| Full analysis: | https://app.any.run/tasks/8ccbeb96-9027-4b31-91ee-7664bf46996e |
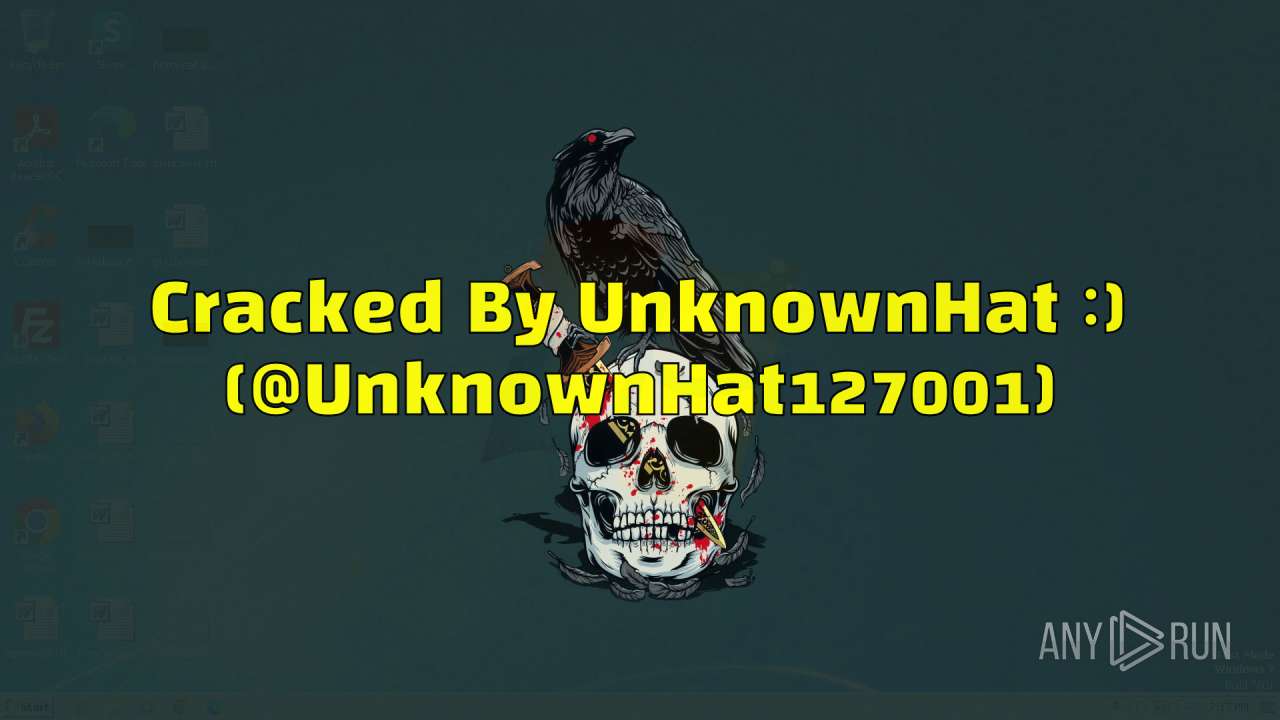
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2024, 18:16:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | C8195E17402EE6EE5F3265047233F27D |
| SHA1: | ED8D7A2CA3164C9905D9C53756E9FEE62B45FA9E |
| SHA256: | ECA582F0896B1164FEBF61620625A123E4E01E10DBEEDA0961E9A471BB85A898 |
| SSDEEP: | 98304:pdlXUKb2Zbx93qkTePdXCCPvbzZ9/2V1AyqgHr8uA6KtCng2uc2F5cyhJvFqg3xa:F9mIEhBhFESB0TXnqSHsyeBloHpj |
MALICIOUS
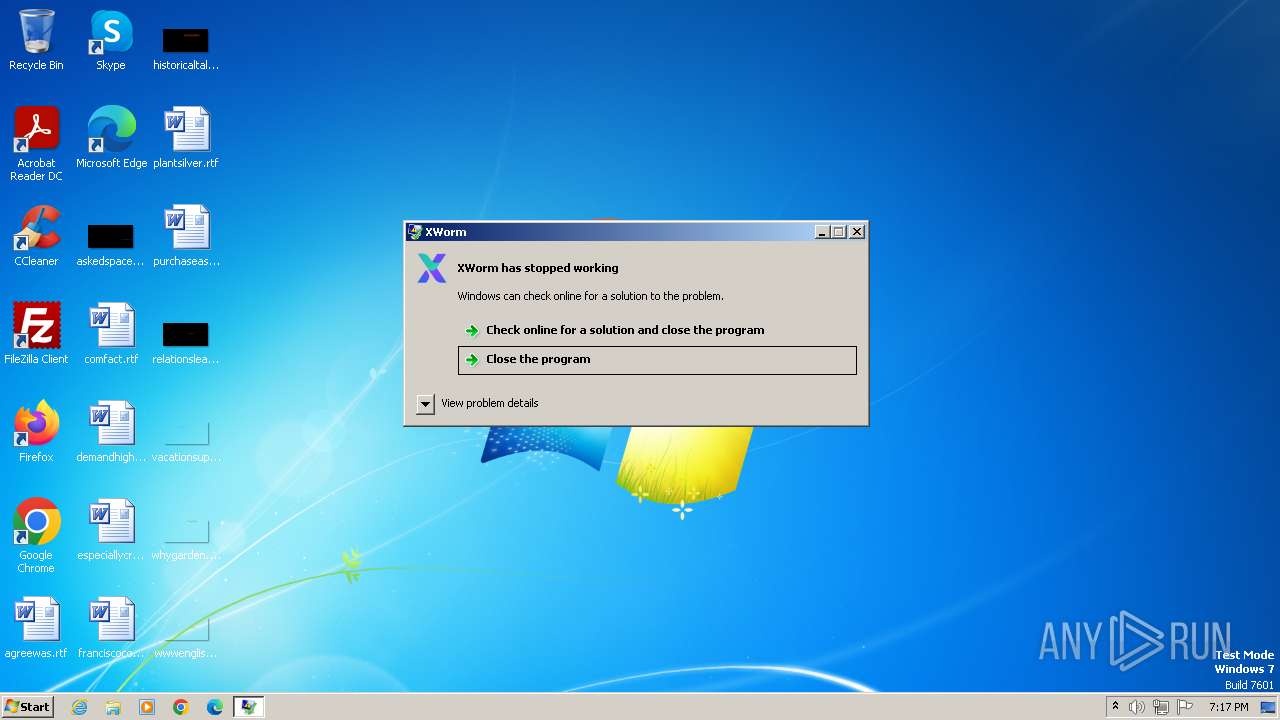
Drops the executable file immediately after the start
- Xworm 5.6.exe (PID: 3972)
- XClient.exe (PID: 4008)
Changes the autorun value in the registry
- XClient.exe (PID: 4008)
Create files in the Startup directory
- XClient.exe (PID: 4008)
SUSPICIOUS
Reads the Internet Settings
- Xworm 5.6.exe (PID: 3972)
- XClient.exe (PID: 4008)
Executable content was dropped or overwritten
- Xworm 5.6.exe (PID: 3972)
- XClient.exe (PID: 4008)
Reads security settings of Internet Explorer
- Xworm 5.6.exe (PID: 3972)
- XClient.exe (PID: 4008)
Potential Corporate Privacy Violation
- XClient.exe (PID: 4008)
Checks for external IP
- XClient.exe (PID: 4008)
Connects to unusual port
- XClient.exe (PID: 4008)
Device Retrieving External IP Address Detected
- XClient.exe (PID: 4008)
INFO
Reads the machine GUID from the registry
- Xworm 5.6.exe (PID: 3972)
- XClient.exe (PID: 4008)
- Xworm V5.6.exe (PID: 4032)
Checks supported languages
- Xworm 5.6.exe (PID: 3972)
- XClient.exe (PID: 4008)
- Xworm V5.6.exe (PID: 4032)
- wmpnscfg.exe (PID: 2028)
Reads the computer name
- Xworm 5.6.exe (PID: 3972)
- XClient.exe (PID: 4008)
- Xworm V5.6.exe (PID: 4032)
- wmpnscfg.exe (PID: 2028)
Creates files or folders in the user directory
- Xworm 5.6.exe (PID: 3972)
- XClient.exe (PID: 4008)
Reads Environment values
- XClient.exe (PID: 4008)
Manual execution by a user
- wmpnscfg.exe (PID: 2028)
Create files in a temporary directory
- XClient.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:05:04 17:26:06+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 15678976 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xef5c8e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 1.0.0.0 |
| InternalName: | output.exe |
| LegalCopyright: | |
| OriginalFileName: | output.exe |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
40
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2024 | "C:\Windows\System32\schtasks.exe" /create /f /sc minute /mo 1 /tn "update" /tr "C:\Users\admin\AppData\Local\Temp\update.exe" | C:\Windows\System32\schtasks.exe | — | XClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3972 | "C:\Users\admin\AppData\Local\Temp\Xworm 5.6.exe" | C:\Users\admin\AppData\Local\Temp\Xworm 5.6.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4008 | "C:\Users\admin\AppData\Roaming\XClient.exe" | C:\Users\admin\AppData\Roaming\XClient.exe | Xworm 5.6.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 1.0.0.0 Modules
| |||||||||||||||
| 4032 | "C:\Users\admin\AppData\Roaming\Xworm V5.6.exe" | C:\Users\admin\AppData\Roaming\Xworm V5.6.exe | Xworm 5.6.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: XWorm Version: 5.6.0.0 Modules
| |||||||||||||||
Total events
6 472
Read events
6 443
Write events
29
Delete events
0
Modification events
| (PID) Process: | (3972) Xworm 5.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3972) Xworm 5.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3972) Xworm 5.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3972) Xworm 5.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4008) XClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XClient_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4008) XClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XClient_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4008) XClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XClient_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4008) XClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XClient_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4008) XClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XClient_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4008) XClient.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\XClient_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | Xworm 5.6.exe | C:\Users\admin\AppData\Roaming\Xworm V5.6.exe | executable | |
MD5:56CCB739926A725E78A7ACF9AF52C4BB | SHA256:90F58865F265722AB007ABB25074B3FC4916E927402552C6BE17EF9AFAC96405 | |||
| 4008 | XClient.exe | C:\Users\admin\AppData\Local\Temp\update.exe | executable | |
MD5:B27CD8949BCF36369A6274DE80C95593 | SHA256:9BD7EEA5EAF0D6AE248F62A55D991AF01B726D7F6CA8E1907DB222B68F20EA70 | |||
| 3972 | Xworm 5.6.exe | C:\Users\admin\AppData\Roaming\XClient.exe | executable | |
MD5:B27CD8949BCF36369A6274DE80C95593 | SHA256:9BD7EEA5EAF0D6AE248F62A55D991AF01B726D7F6CA8E1907DB222B68F20EA70 | |||
| 4008 | XClient.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\update.lnk | binary | |
MD5:3D06728C6EB0BBAC5F5EA70CA22B6D6A | SHA256:86FF7DA3B82CF39F61E01DDCBA17AA86A65BA5CCF58A77EBF0CB49B143EA3712 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4008 | XClient.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4008 | XClient.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
4008 | XClient.exe | 147.185.221.19:13308 | existing-vincent.gl.at.ply.gg | PLAYIT-GG | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
existing-vincent.gl.at.ply.gg |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4008 | XClient.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
4008 | XClient.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
4008 | XClient.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1088 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |